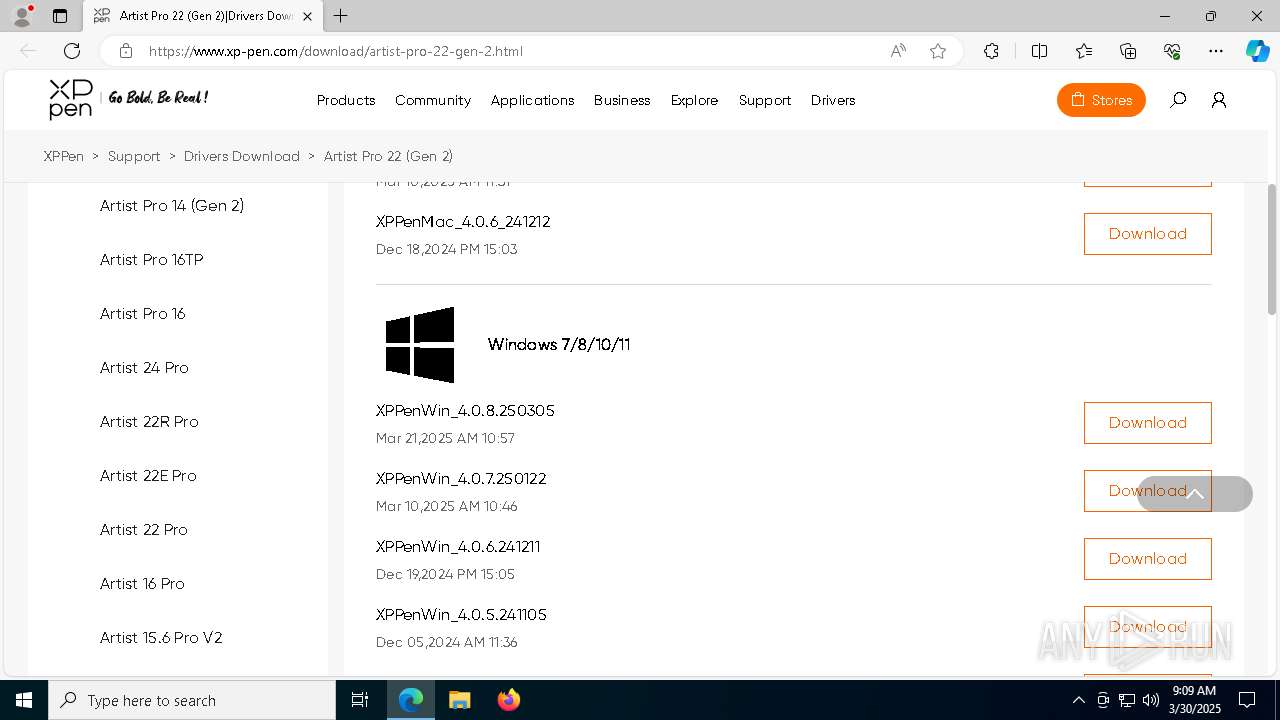
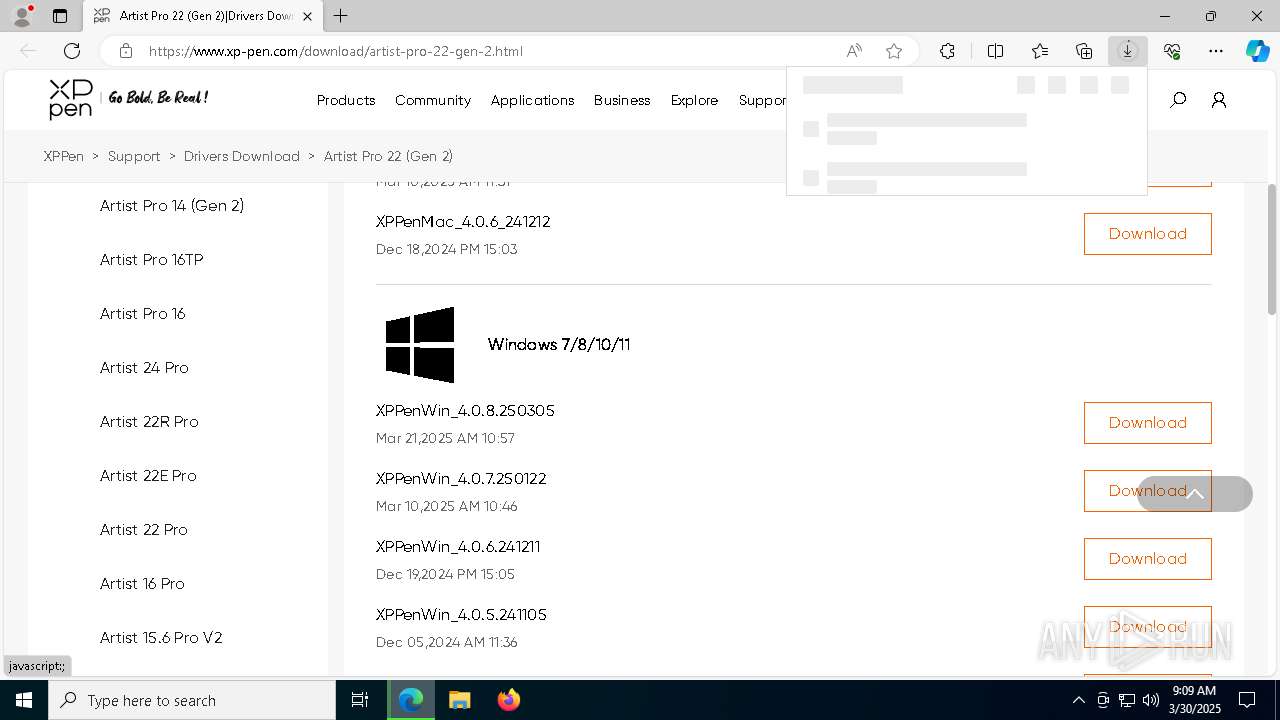
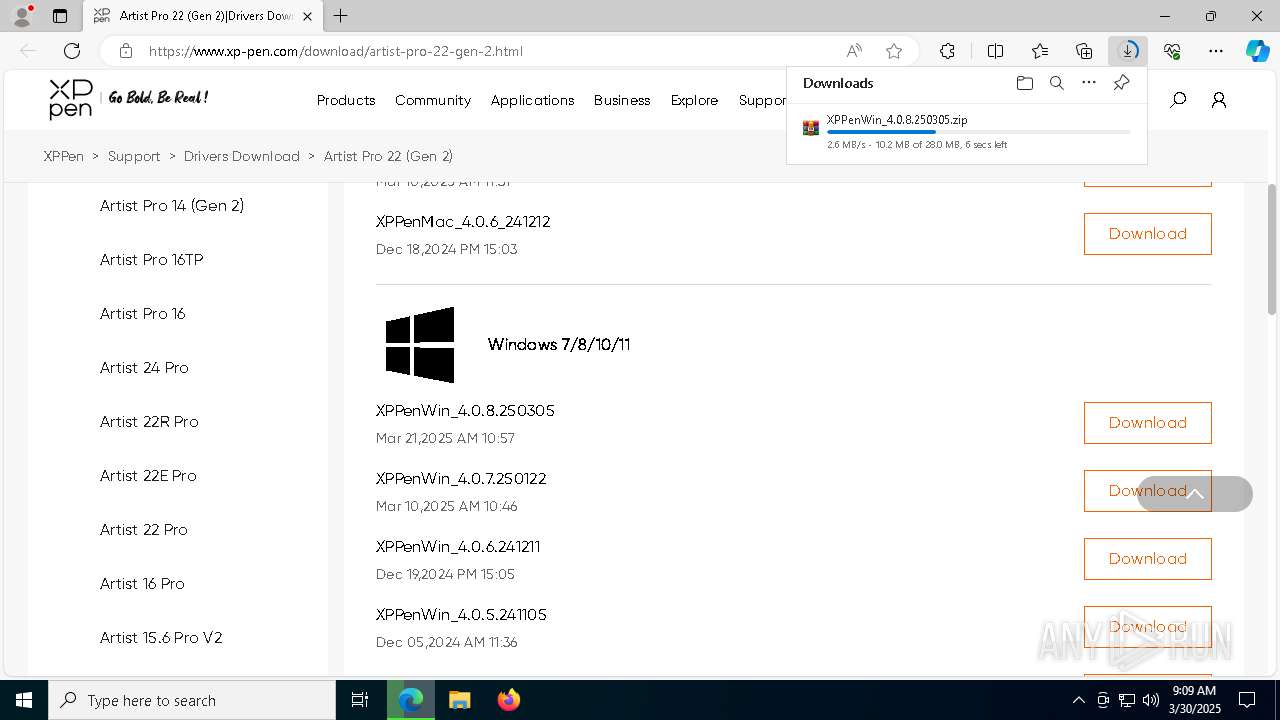
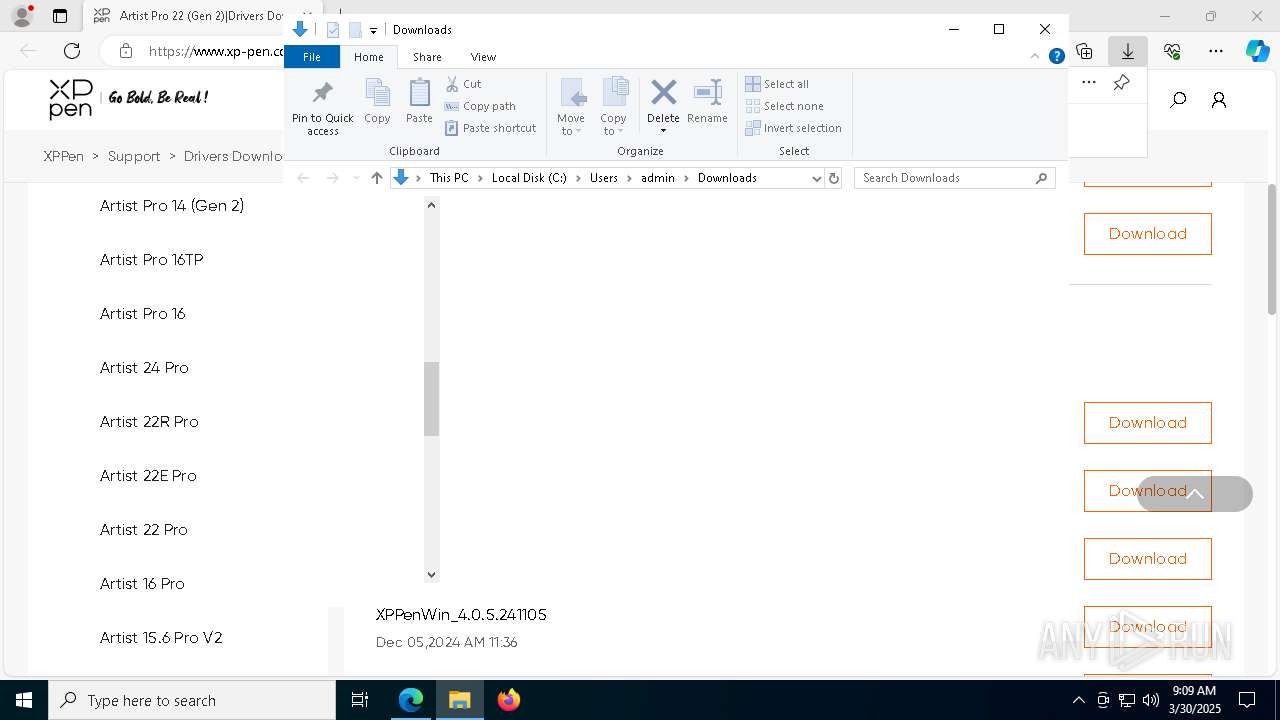
| URL: | https://www.xp-pen.com/download/artist-pro-22-gen-2.html |
| Full analysis: | https://app.any.run/tasks/91a7ba49-db55-4b8e-93b6-4bb293d0ed55 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2025, 09:08:45 |
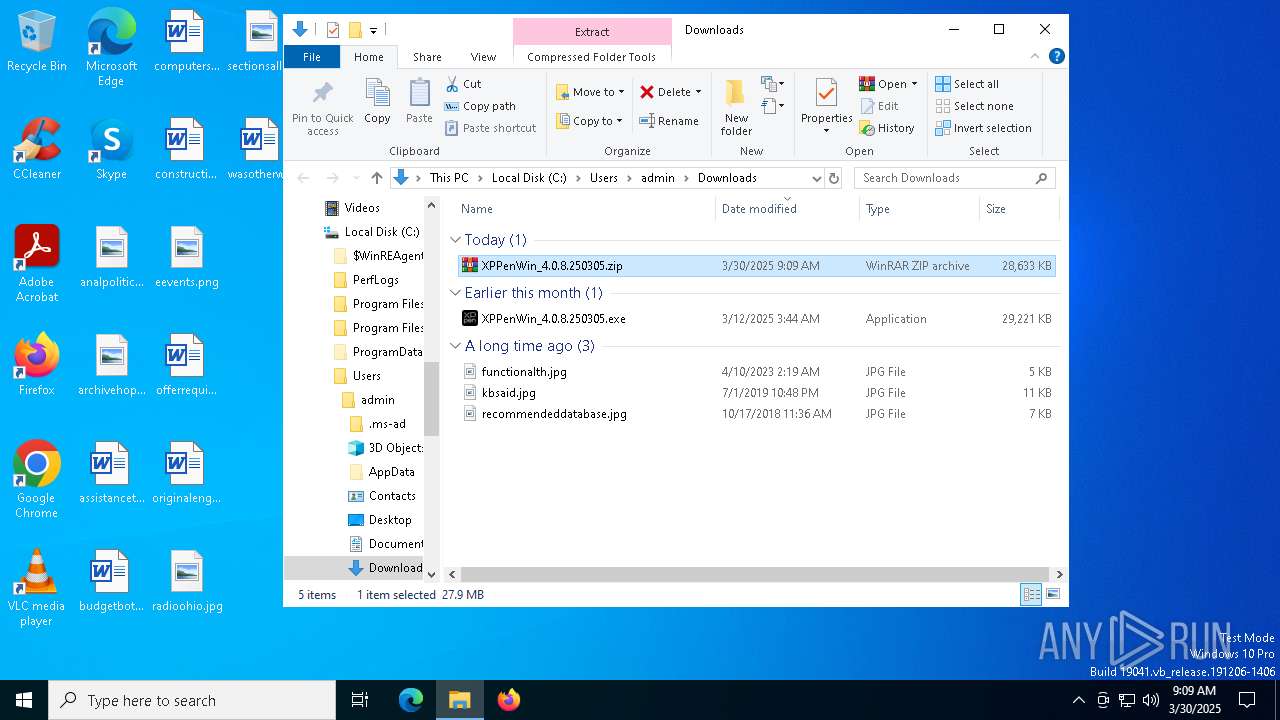
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9C6376903272B251DC50B423BA1F2DB3 |
| SHA1: | 601A64D250E82EF6CC748F00C985A07D28576E24 |
| SHA256: | 37BFBFFF4B802994301CBA3A16FDE411BA4C0EE6CF75DE357B9F867D52CFDE2E |
| SSDEEP: | 3:N8DSL4SIaKL+RXaXkIG:2OL8B+cQ |
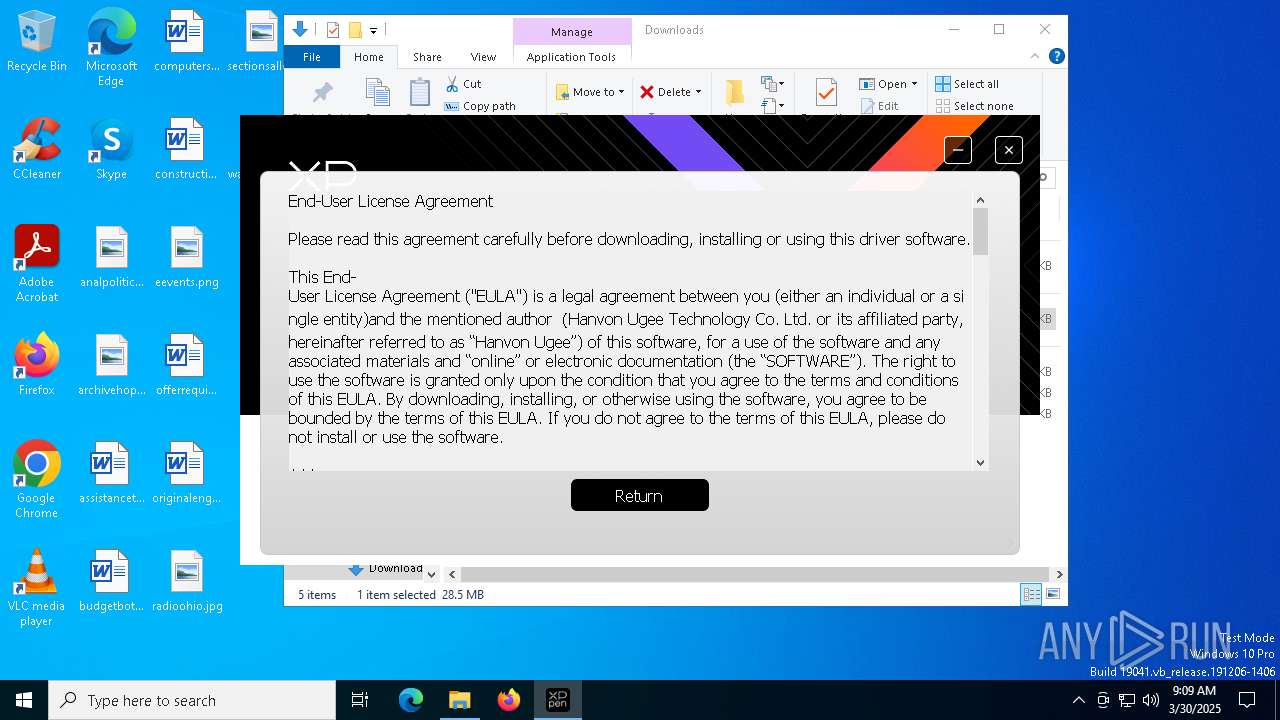
MALICIOUS
Executing a file with an untrusted certificate
- Listdlls.exe (PID: 7352)
- Listdlls64.exe (PID: 5576)
- dpinst.exe (PID: 7396)
Changes the autorun value in the registry
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
SUSPICIOUS
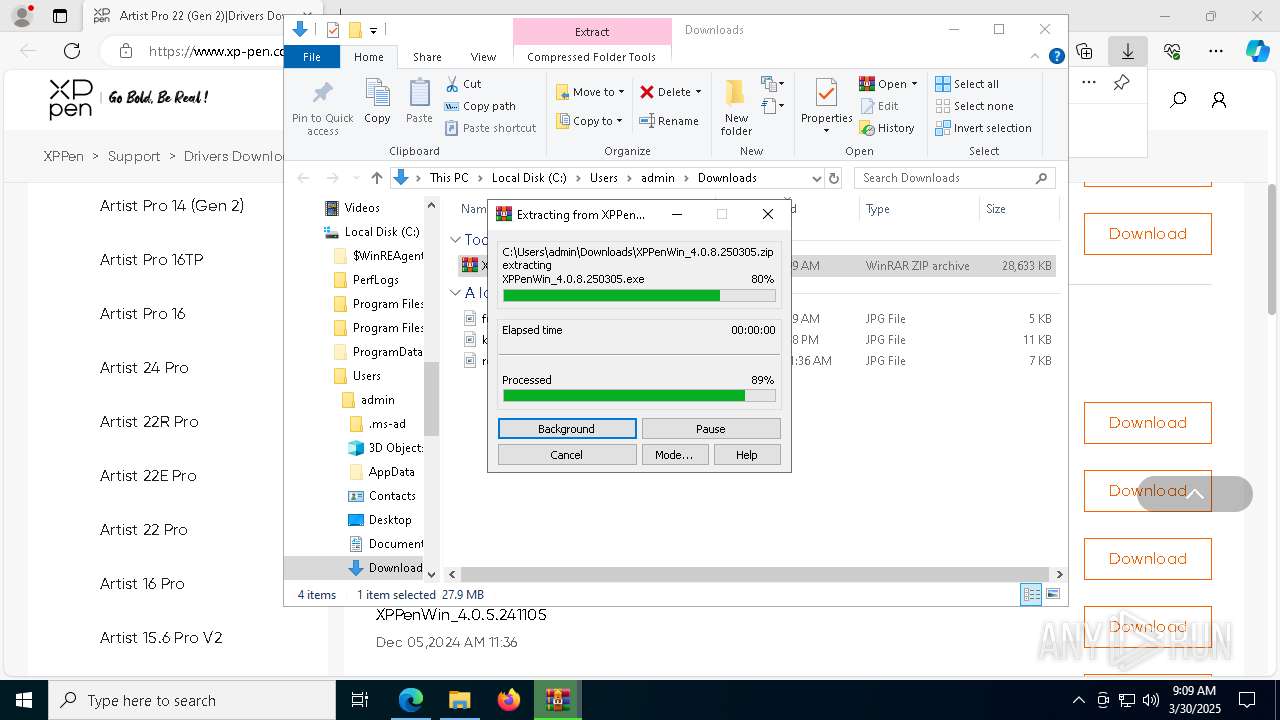
Executable content was dropped or overwritten
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- XPPenWin_4.0.8.250305.exe (PID: 7968)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- Listdlls.exe (PID: 7352)
- devcon.exe (PID: 496)
- drvinst.exe (PID: 6768)
- drvinst.exe (PID: 2040)
- dpinst.exe (PID: 7396)
- drvinst.exe (PID: 7564)
- drvinst.exe (PID: 7404)
Reads security settings of Internet Explorer
- XPPenWin_4.0.8.250305.tmp (PID: 7592)
- devcon.exe (PID: 496)
Starts CMD.EXE for commands execution
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- cmd.exe (PID: 7432)
Reads the Windows owner or organization settings
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Application launched itself
- cmd.exe (PID: 7432)
Executing commands from a ".bat" file
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7432)
Drops a system driver (possible attempt to evade defenses)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- devcon.exe (PID: 496)
- drvinst.exe (PID: 6768)
- drvinst.exe (PID: 2040)
- dpinst.exe (PID: 7396)
- drvinst.exe (PID: 7564)
- drvinst.exe (PID: 7404)
There is functionality for taking screenshot (YARA)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Process drops legitimate windows executable
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- devcon.exe (PID: 496)
- drvinst.exe (PID: 6768)
- dpinst.exe (PID: 7396)
- drvinst.exe (PID: 7564)
- drvinst.exe (PID: 7404)
Creates or modifies Windows services
- drvinst.exe (PID: 2040)
- drvinst.exe (PID: 7404)
Creates files in the driver directory
- drvinst.exe (PID: 2040)
- drvinst.exe (PID: 7564)
- drvinst.exe (PID: 7404)
- drvinst.exe (PID: 6768)
The executable file from the user directory is run by the CMD process
- Listdlls.exe (PID: 7352)
The process drops C-runtime libraries
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4236)
Searches for installed software
- PenTablet.exe (PID: 7024)
INFO
Reads Environment values
- identity_helper.exe (PID: 5772)
- identity_helper.exe (PID: 7784)
Application launched itself
- msedge.exe (PID: 3268)
- msedge.exe (PID: 6372)
Checks supported languages
- identity_helper.exe (PID: 5772)
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- identity_helper.exe (PID: 7784)
- XPPenWin_4.0.8.250305.tmp (PID: 7592)
- XPPenWin_4.0.8.250305.exe (PID: 7968)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- Listdlls.exe (PID: 7352)
- Listdlls64.exe (PID: 5576)
- devcon.exe (PID: 496)
- drvinst.exe (PID: 6768)
- drvinst.exe (PID: 2040)
- dpinst.exe (PID: 7396)
- drvinst.exe (PID: 7564)
- PLUGScheduler.exe (PID: 4236)
- PenTablet.exe (PID: 7024)
- PenTablet.exe (PID: 968)
- drvinst.exe (PID: 7404)
Reads the computer name
- identity_helper.exe (PID: 5772)
- identity_helper.exe (PID: 7784)
- XPPenWin_4.0.8.250305.tmp (PID: 7592)
- XPPenWin_4.0.8.250305.exe (PID: 7968)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- Listdlls64.exe (PID: 5576)
- devcon.exe (PID: 496)
- drvinst.exe (PID: 2040)
- drvinst.exe (PID: 6768)
- dpinst.exe (PID: 7396)
- drvinst.exe (PID: 7404)
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- PLUGScheduler.exe (PID: 4236)
- PenTablet.exe (PID: 7024)
- drvinst.exe (PID: 7564)
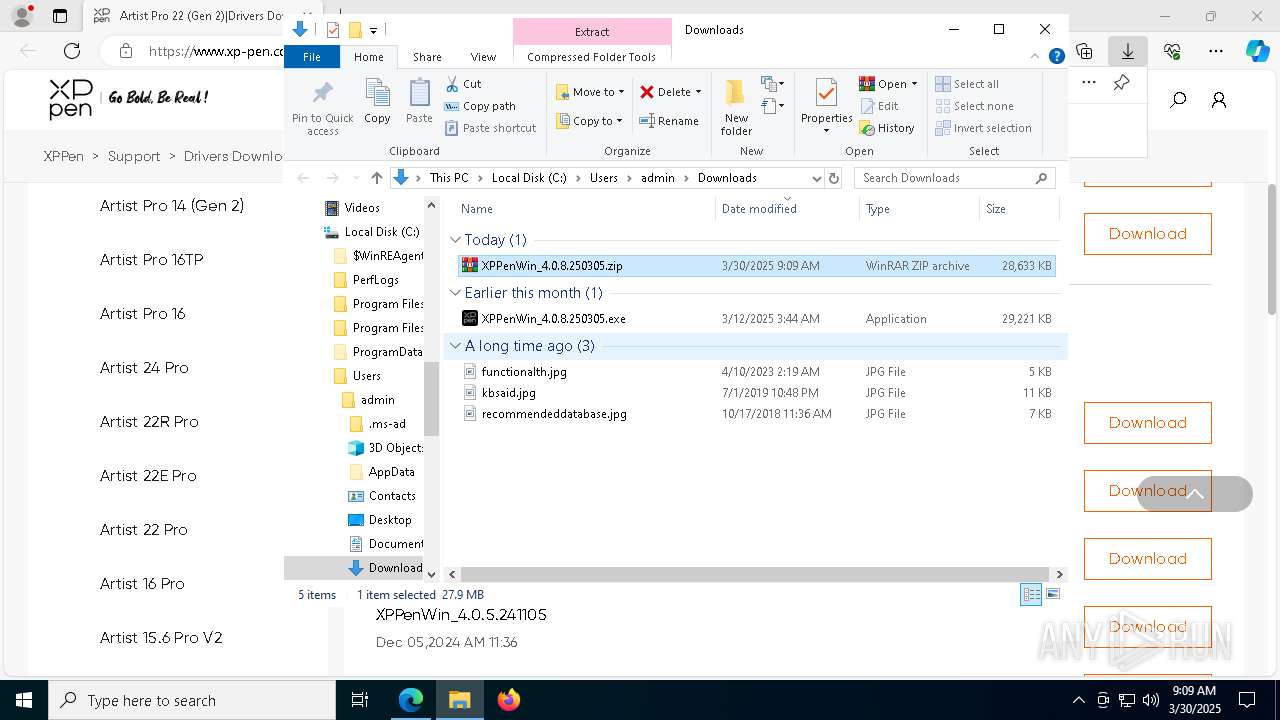
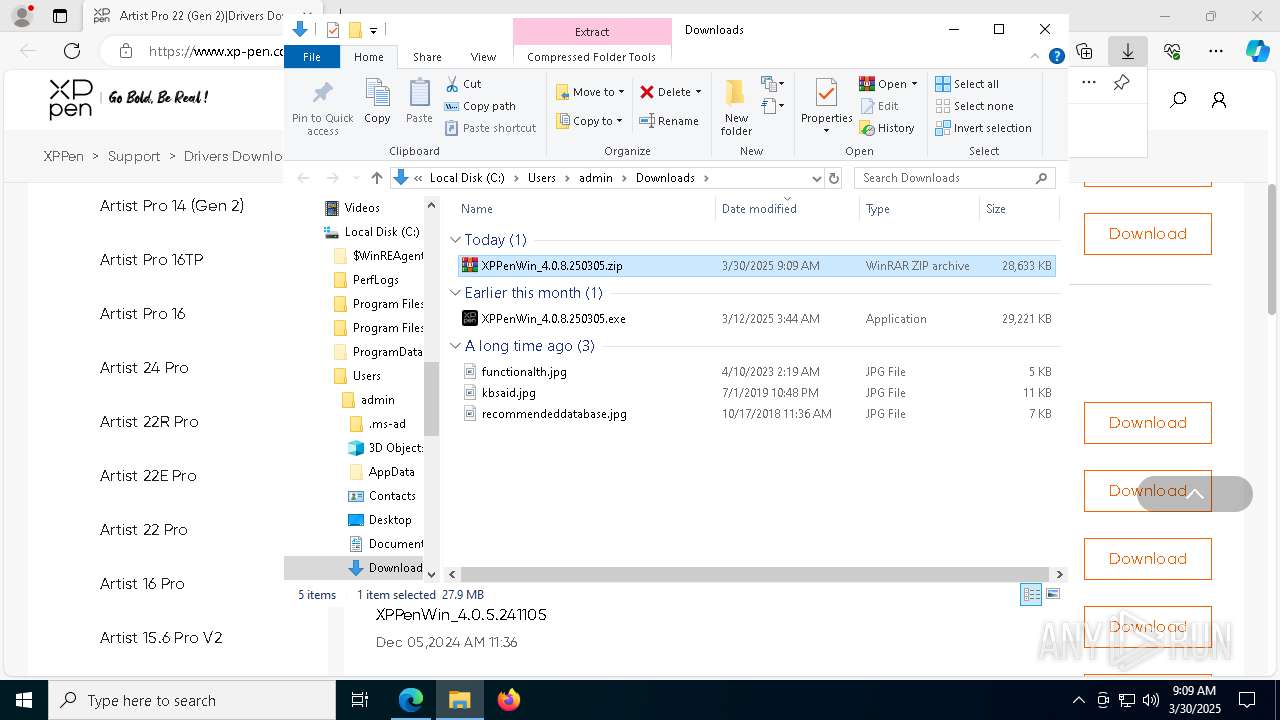
Autorun file from Downloads
- msedge.exe (PID: 3240)
- msedge.exe (PID: 6372)
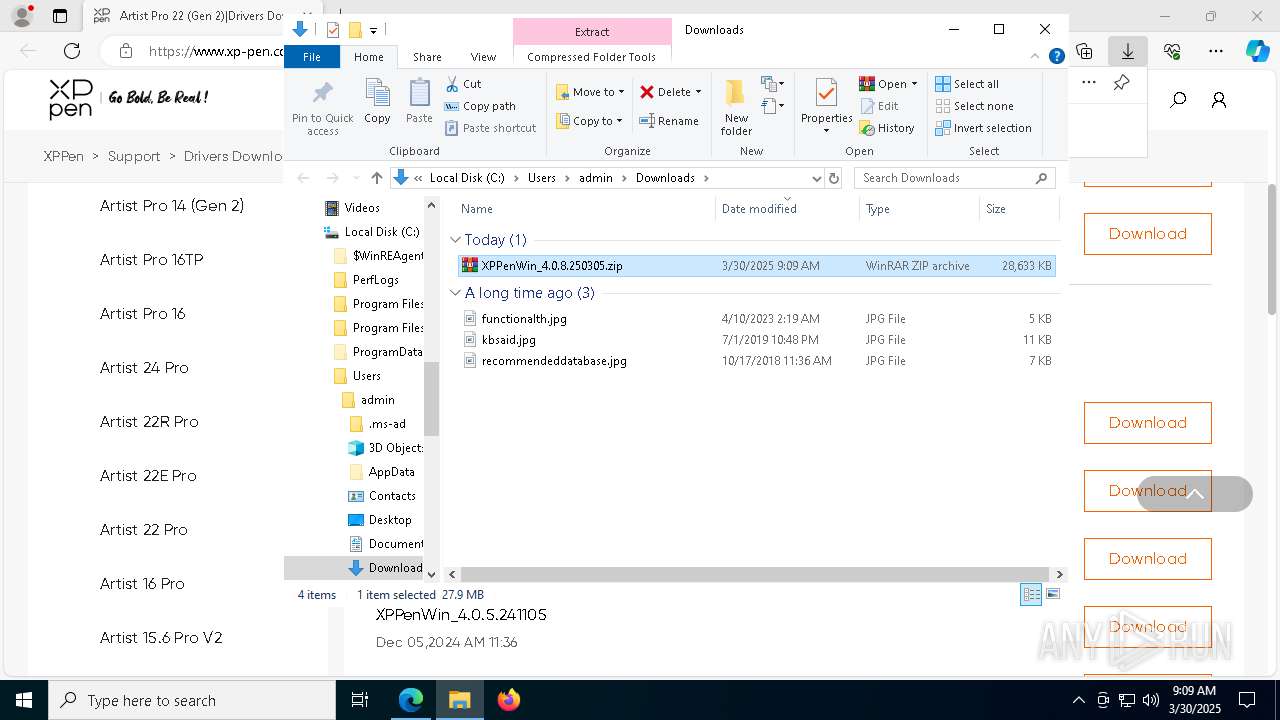
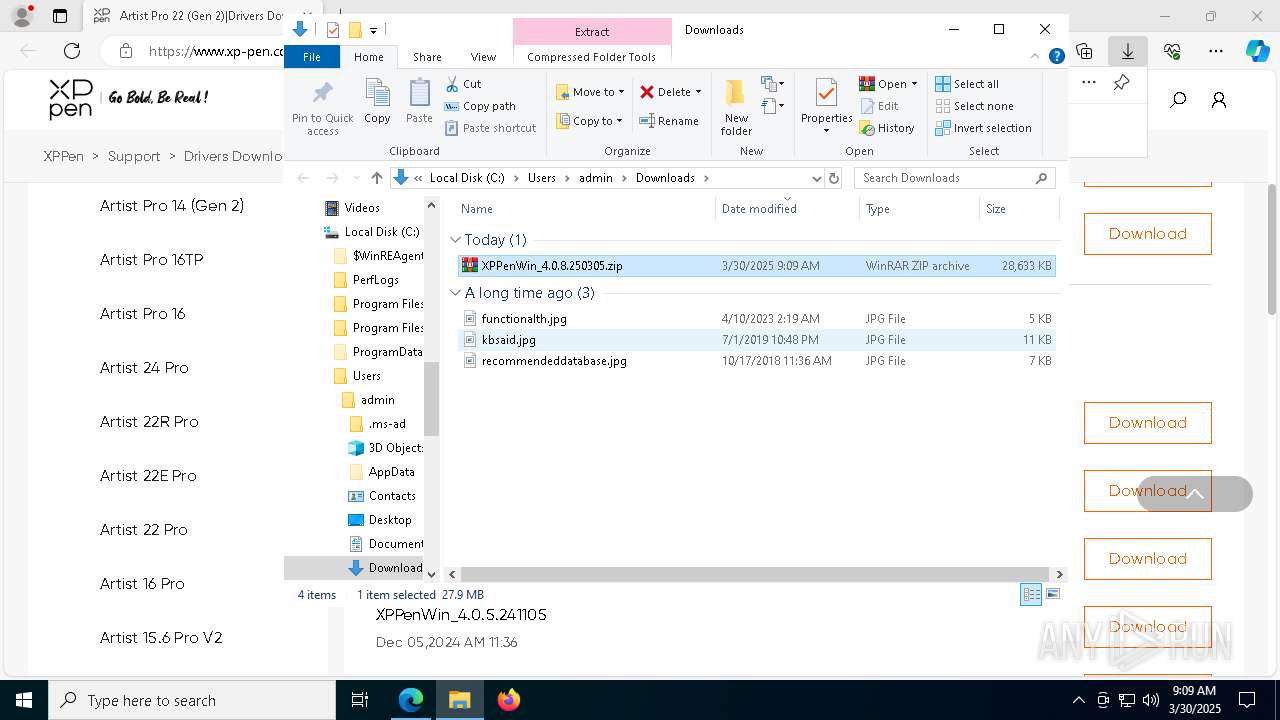
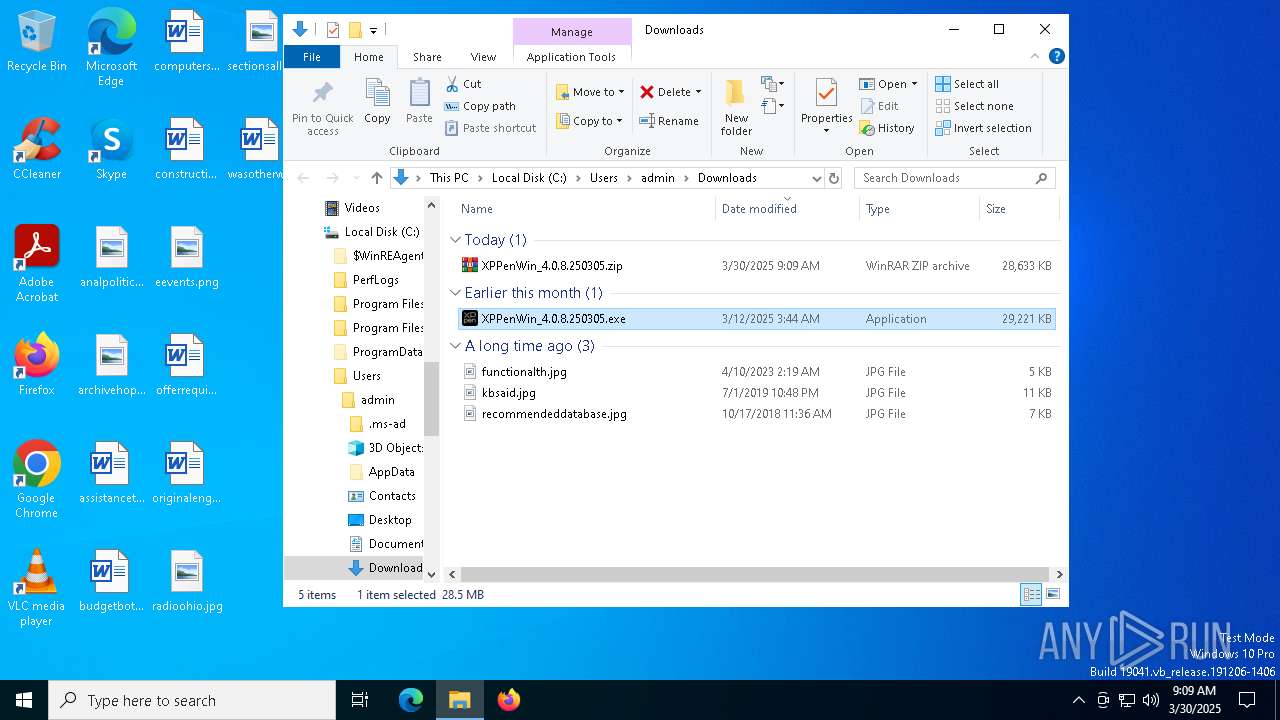
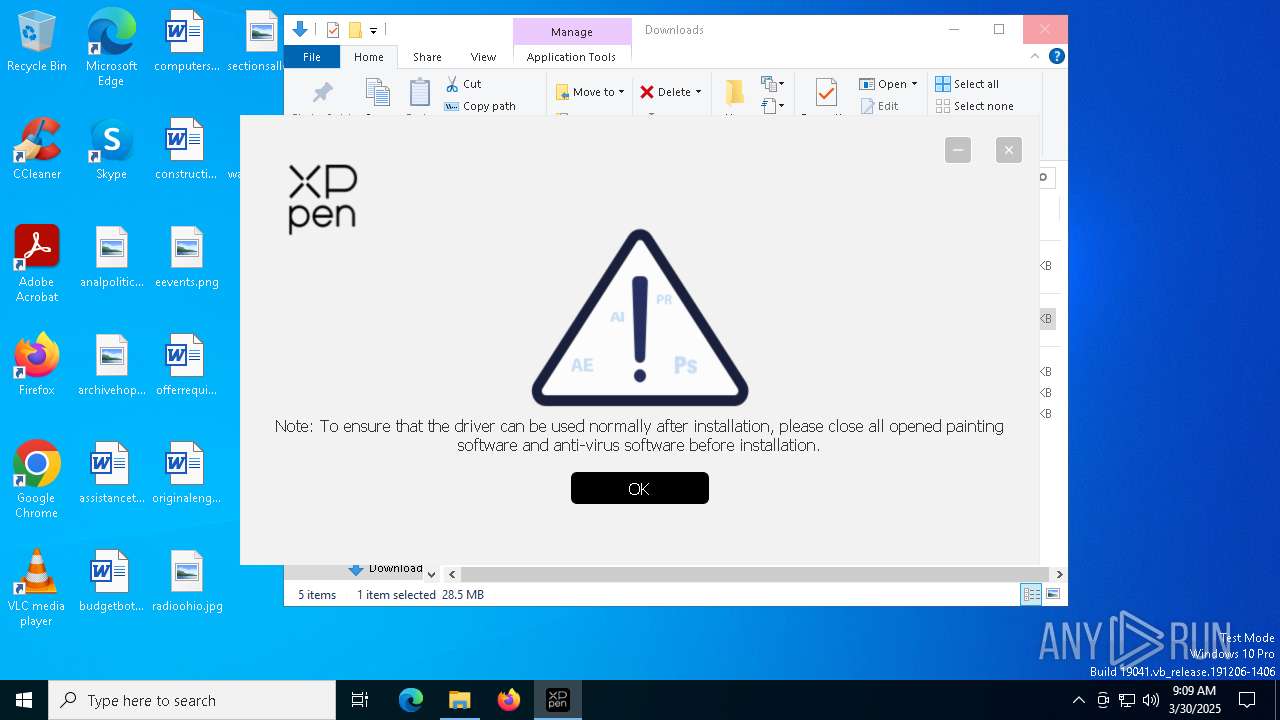
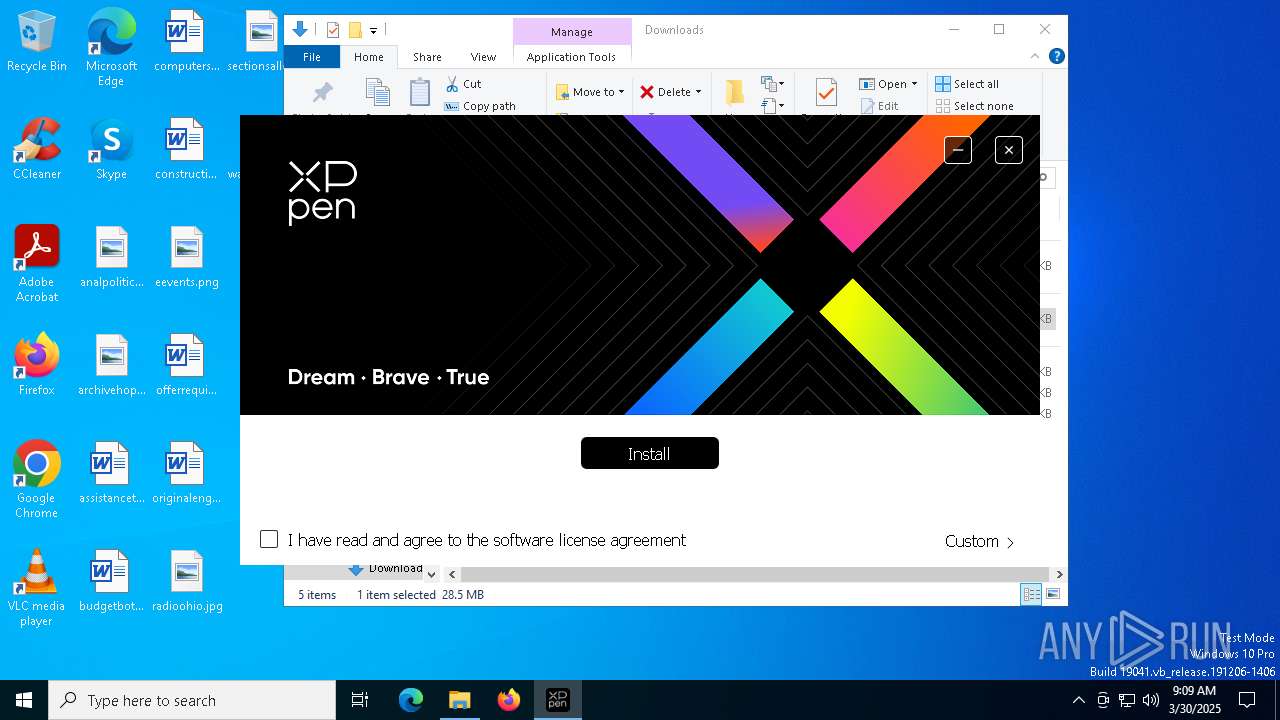
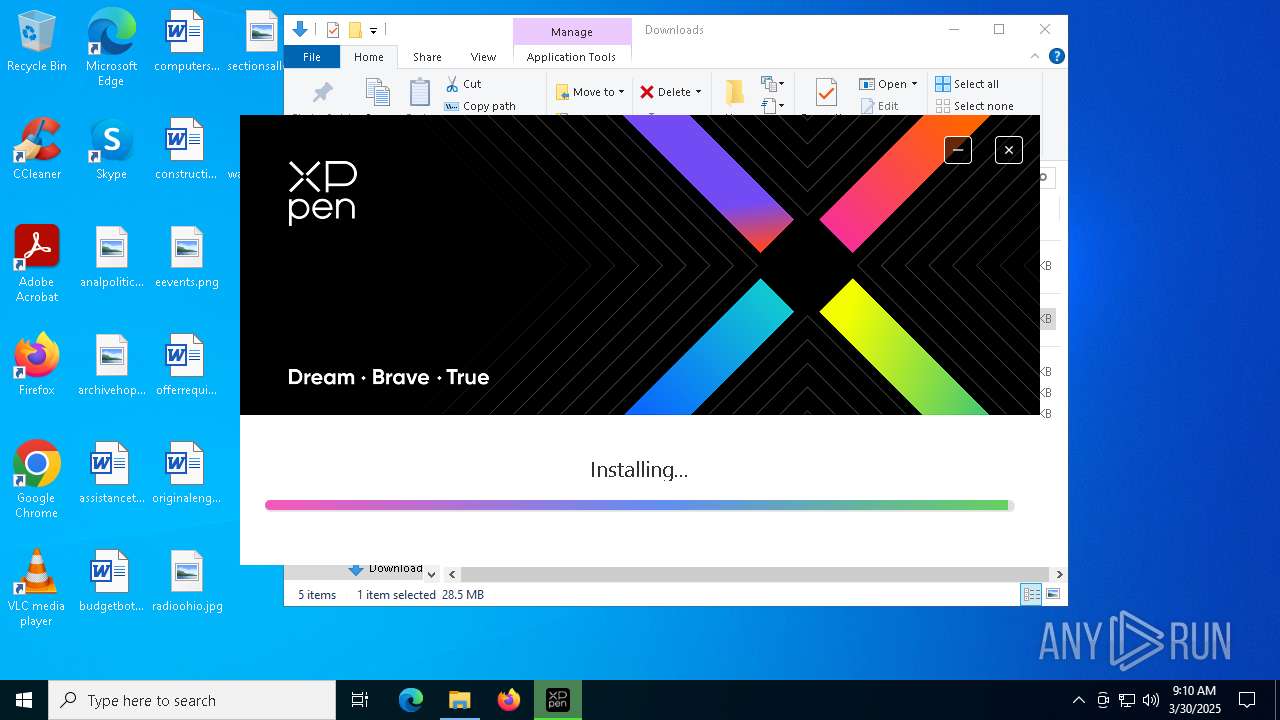
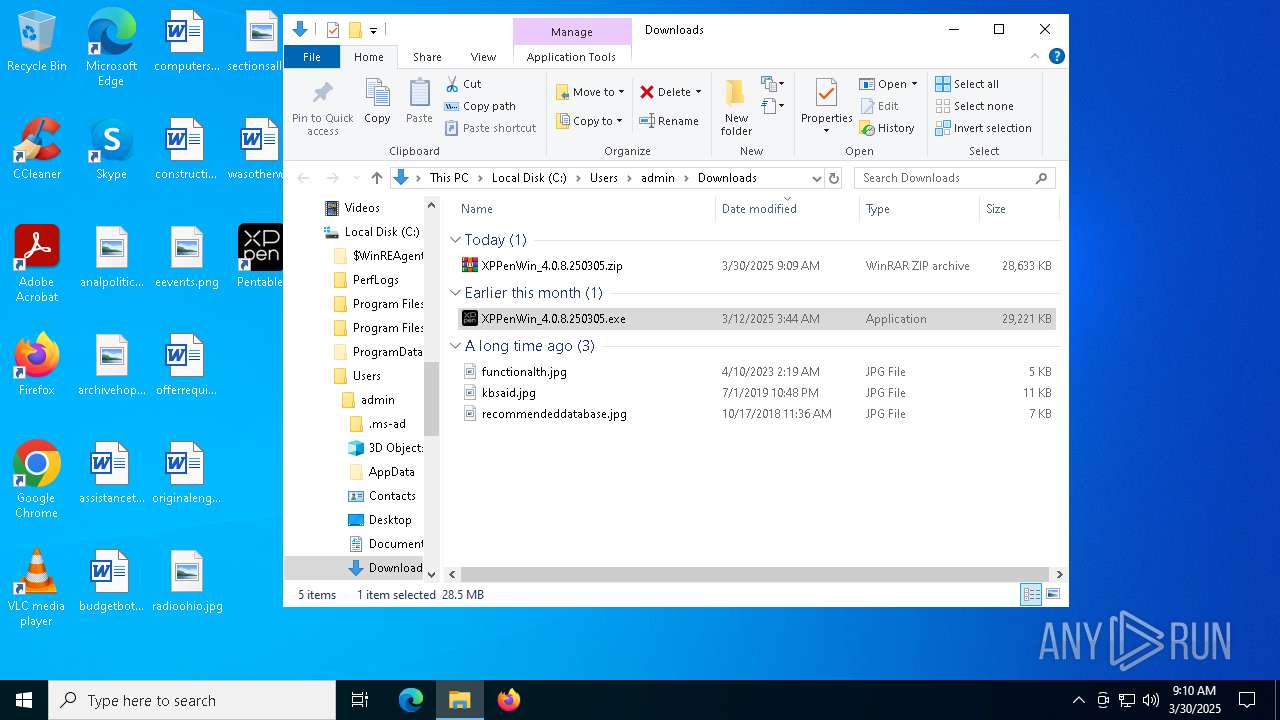
Manual execution by a user
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- WinRAR.exe (PID: 4448)
- PenTablet.exe (PID: 7024)
- PenTablet.exe (PID: 968)
Create files in a temporary directory
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- XPPenWin_4.0.8.250305.exe (PID: 7968)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- Listdlls.exe (PID: 7352)
- devcon.exe (PID: 496)
- dpinst.exe (PID: 7396)
- PenTablet.exe (PID: 7024)
Process checks computer location settings
- XPPenWin_4.0.8.250305.tmp (PID: 7592)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4448)
The sample compiled with russian language support
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
The sample compiled with english language support
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- Listdlls.exe (PID: 7352)
- devcon.exe (PID: 496)
- drvinst.exe (PID: 6768)
- drvinst.exe (PID: 2040)
- dpinst.exe (PID: 7396)
- drvinst.exe (PID: 7564)
- drvinst.exe (PID: 7404)
Detects InnoSetup installer (YARA)
- XPPenWin_4.0.8.250305.tmp (PID: 7592)
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- XPPenWin_4.0.8.250305.exe (PID: 7968)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Compiled with Borland Delphi (YARA)
- XPPenWin_4.0.8.250305.exe (PID: 7968)
- XPPenWin_4.0.8.250305.exe (PID: 7560)
- XPPenWin_4.0.8.250305.tmp (PID: 7592)
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Creates files in the program directory
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- PLUGScheduler.exe (PID: 4236)
The sample compiled with chinese language support
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Reads the software policy settings
- devcon.exe (PID: 496)
- slui.exe (PID: 7852)
- drvinst.exe (PID: 6768)
- drvinst.exe (PID: 7564)
Creates files or folders in the user directory
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
- PenTablet.exe (PID: 7024)
Reads the machine GUID from the registry
- devcon.exe (PID: 496)
- drvinst.exe (PID: 6768)
- drvinst.exe (PID: 7564)
Creates a software uninstall entry
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Qt framework related mutex has been found
- PenTablet.exe (PID: 7024)
- PenTablet.exe (PID: 968)
The sample compiled with arabic language support
- XPPenWin_4.0.8.250305.tmp (PID: 7368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
426
Monitored processes
143
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files\XPPen\64\devcon.exe" install XPPenTablet.inf XPPen\PenTablet | C:\Program Files\XPPen\64\devcon.exe | XPPenWin_4.0.8.250305.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Error opening smss.exe(412): " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6876 --field-trial-handle=2436,i,4929463220373035164,10985549147742201347,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4180 --field-trial-handle=2304,i,6622228087991341297,17820250608970145857,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files\XPPen\PenTablet.exe" | C:\Program Files\XPPen\PenTablet.exe | — | explorer.exe | |||||||||||
User: admin Company: XPPEN TECHNOLOGY CO. Integrity Level: MEDIUM Description: Pentablet Exit code: 0 Version: 4.0.8.0 Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Access is denied. " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5036 --field-trial-handle=2304,i,6622228087991341297,17820250608970145857,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc881d5fd8,0x7ffc881d5fe4,0x7ffc881d5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7752 --field-trial-handle=2436,i,4929463220373035164,10985549147742201347,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 057
Read events
19 901
Write events
137
Delete events
19
Modification events
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 248264EF21902F00 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 71AC8AEF21902F00 | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3C294360-6AB3-43BD-8DA3-19CB1BA664D2} | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FEDC2C5F-C8BD-425C-9176-E550B12E6A69} | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B15C061C-5BF7-4012-8355-E9887C7B62F2} | |||
| (PID) Process: | (6372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C0BCEA63-A8A7-421D-A494-150B899C890F} | |||
Executable files
158
Suspicious files
556
Text files
111
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c361.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c352.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c361.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c371.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c381.TMP | — | |
MD5:— | SHA256:— | |||
| 6372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
153
DNS requests
131
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
6800 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
7316 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743608916&P2=404&P3=2&P4=EsKD56rR2ZlGIKwL6pGsLN3B2VV%2ftQNTzNyWWXpMhQh8lnnuPTrOBesF865psup52%2f4Q%2bMILlTXOx1s2VsUnVg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6372 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7276 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7276 | msedge.exe | 23.48.23.26:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.xp-pen.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |