| File name: | SentinelCleaner.exe |
| Full analysis: | https://app.any.run/tasks/b4798bbb-a1d7-45df-812f-a55986497b5f |
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2020, 01:53:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 13CCE65582D94BB6E9ED6A6A350923D4 |
| SHA1: | 019B9AE7F1AA1F461110ED81C5D18922C1CFED71 |
| SHA256: | 37AE785DE99140C0DBAFAAF27CDECB68CF68B499DF0B835E1B9C6D0001E9B5E2 |
| SSDEEP: | 768:A2j/f+HNIqBAkV2m/uzcPbvVOP6Zq/OPw33qKPR5XjOpFL3gbWl:A2rW4wXPJOP9/8wHNXjOpFgU |
MALICIOUS
No malicious indicators.SUSPICIOUS
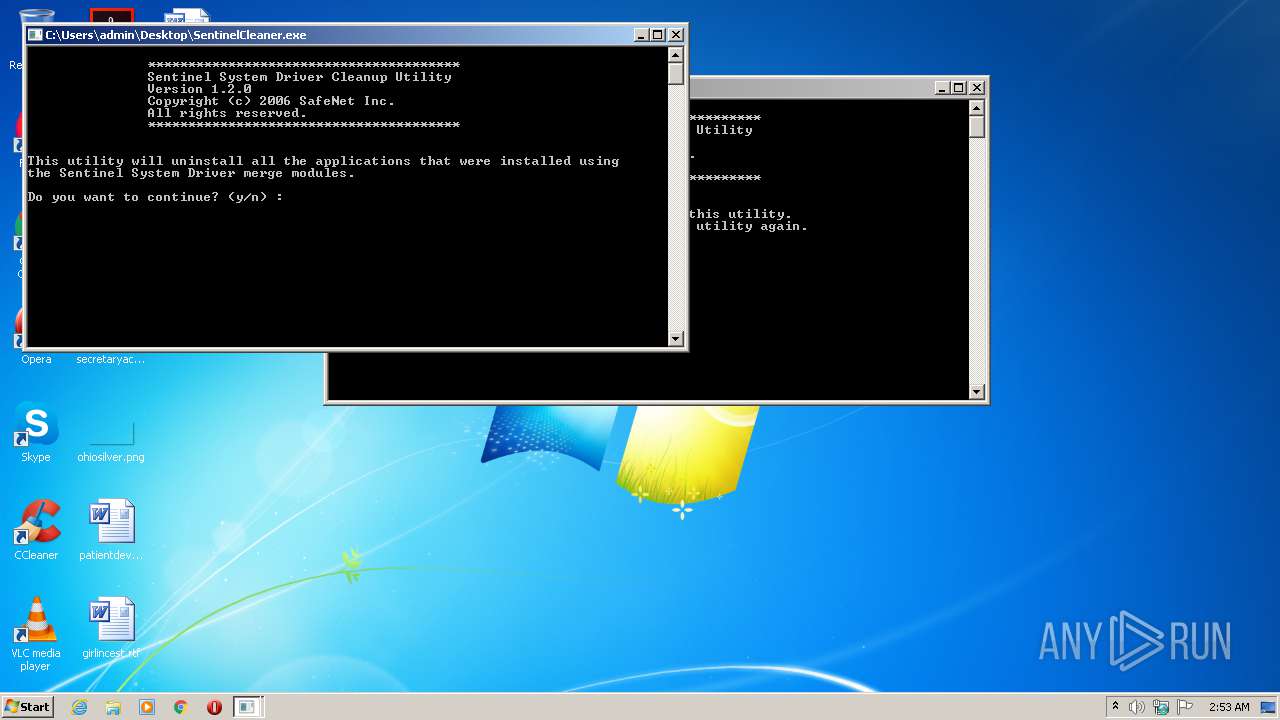
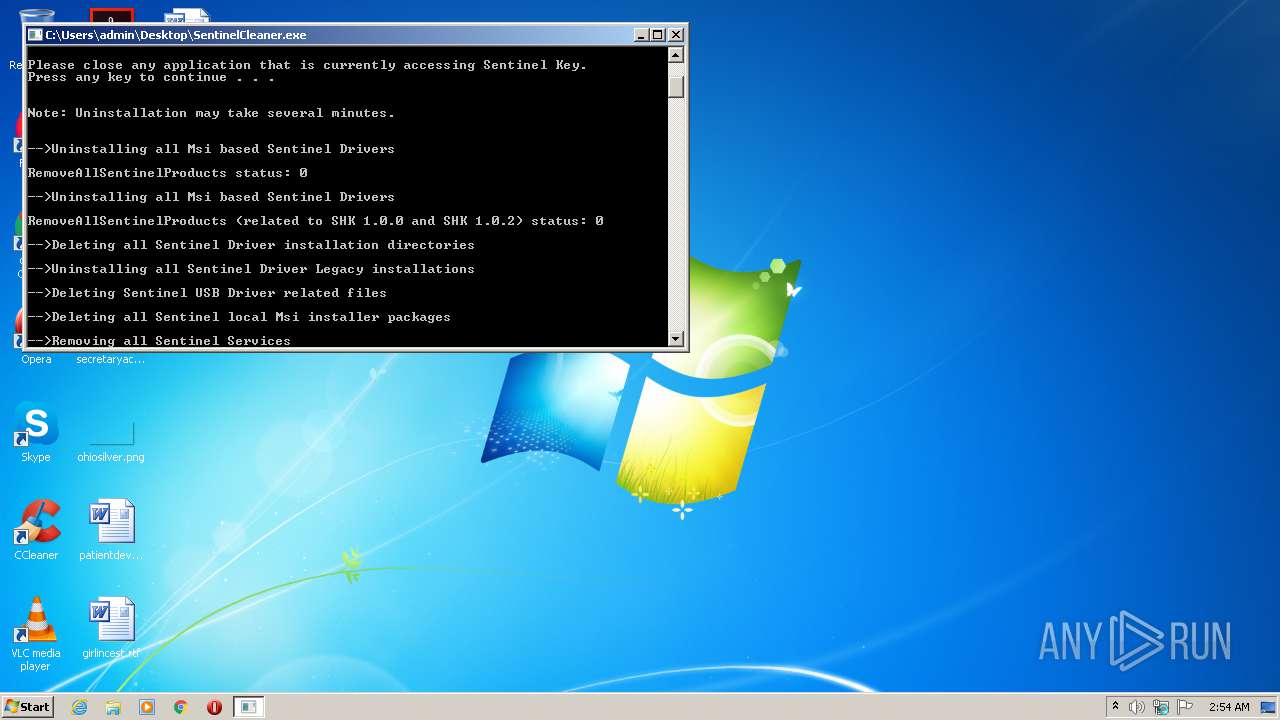
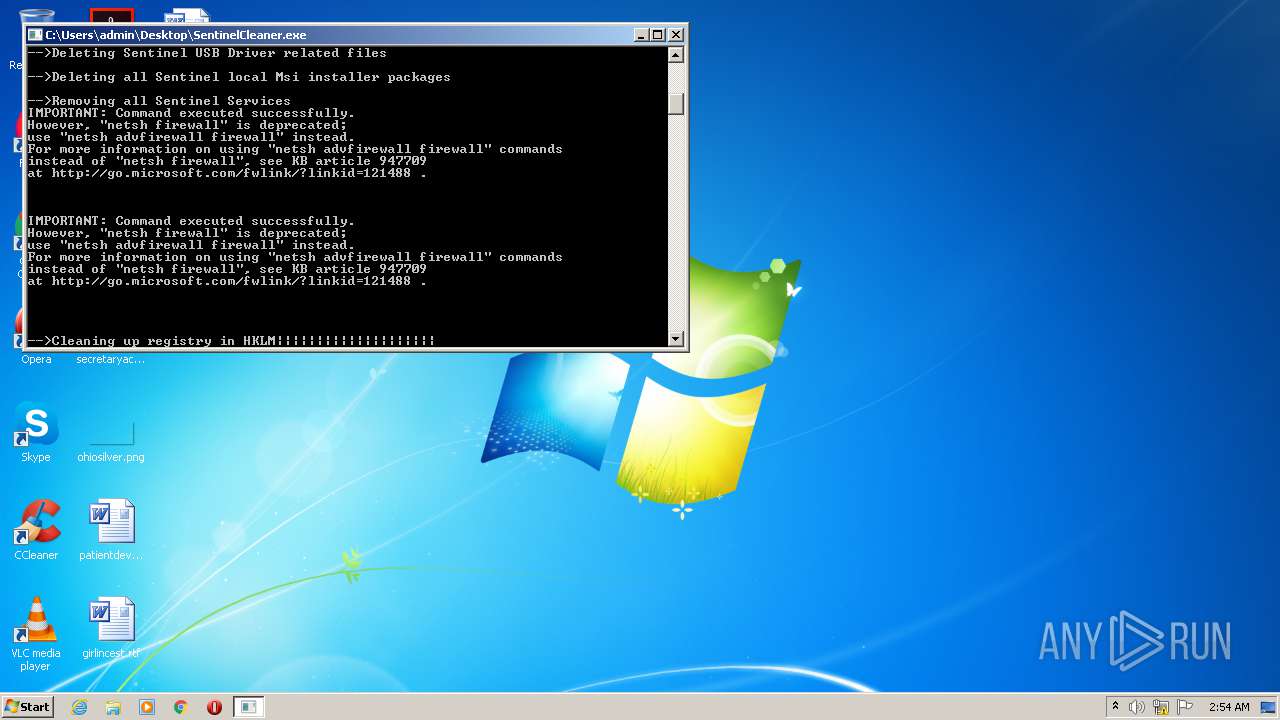
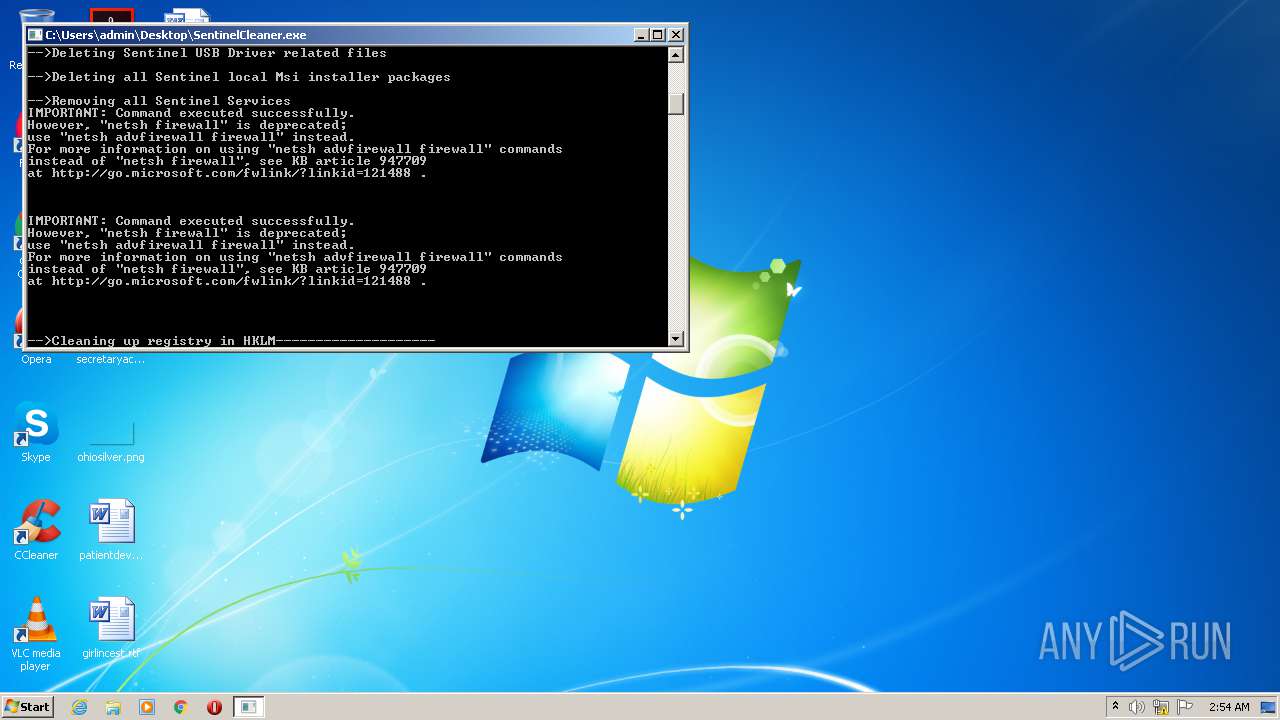
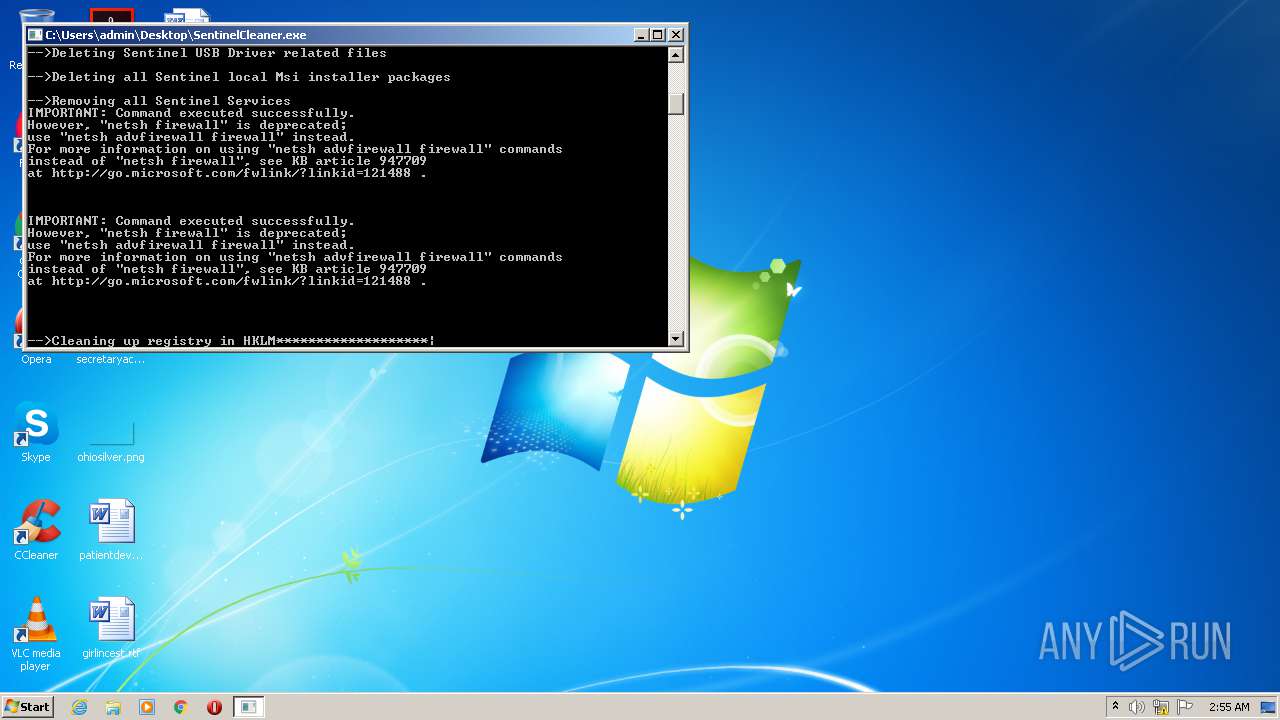
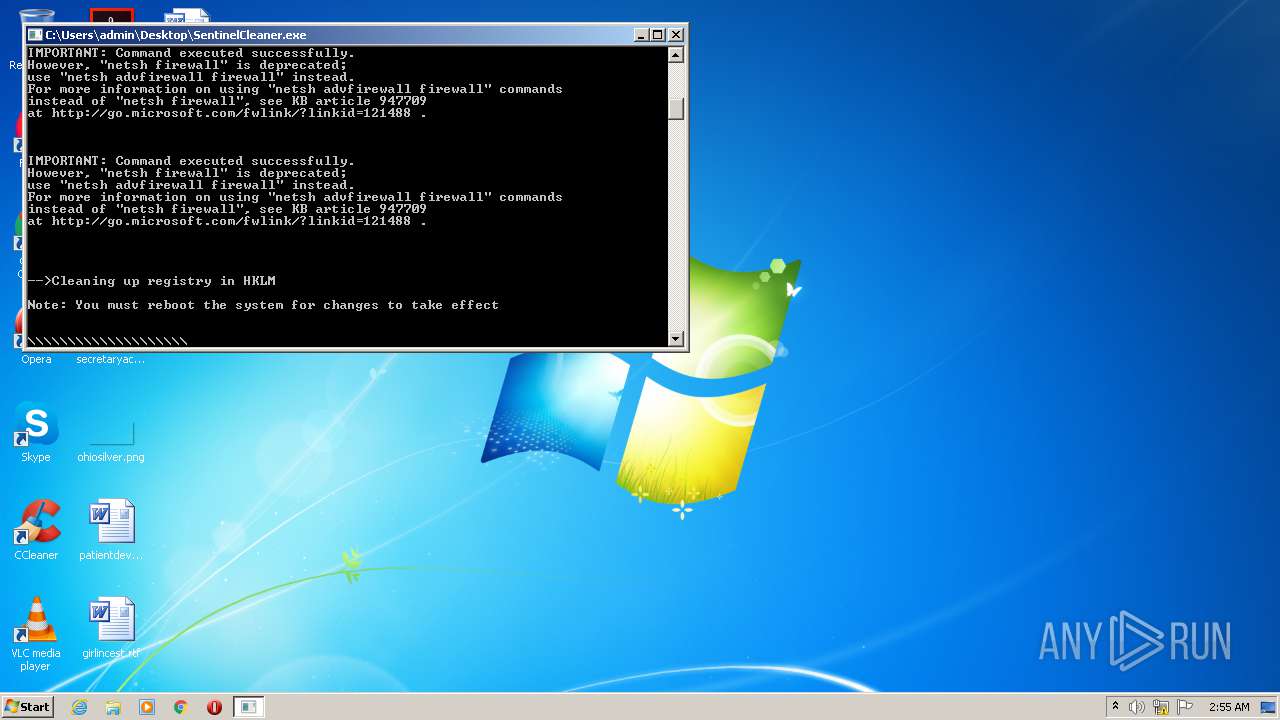
Creates files in the Windows directory
- SentinelCleaner.exe (PID: 2472)
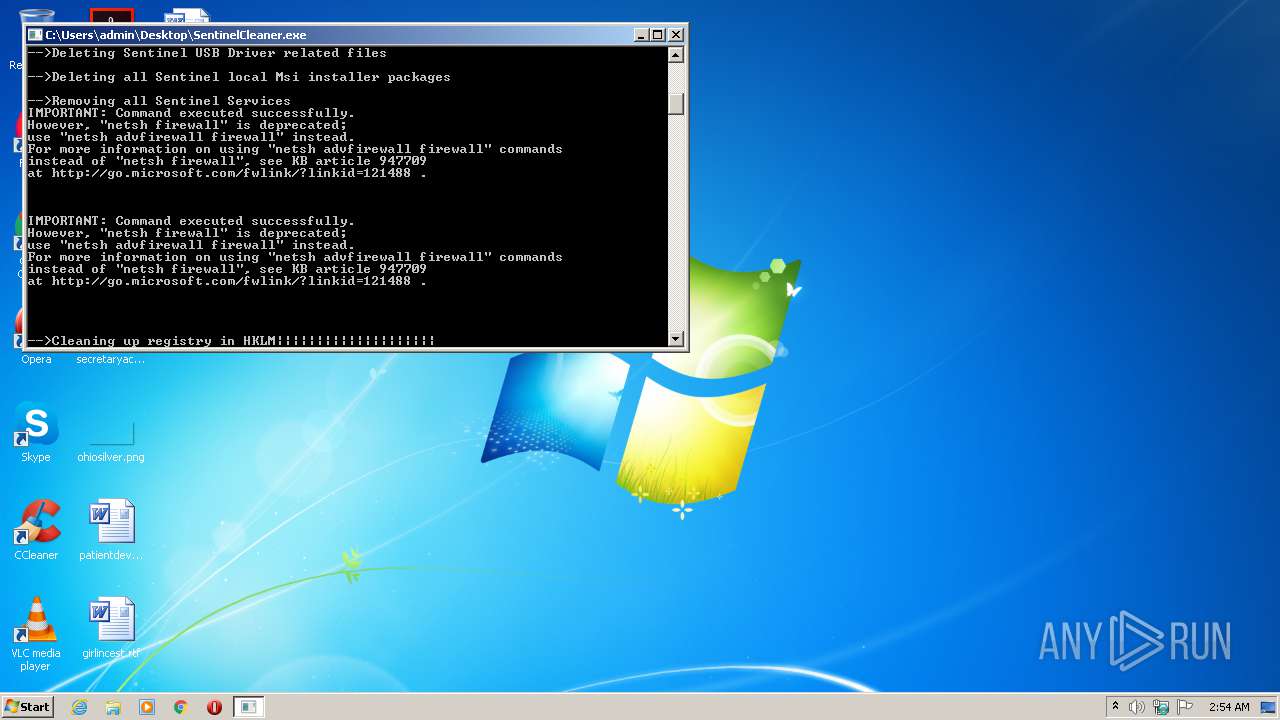
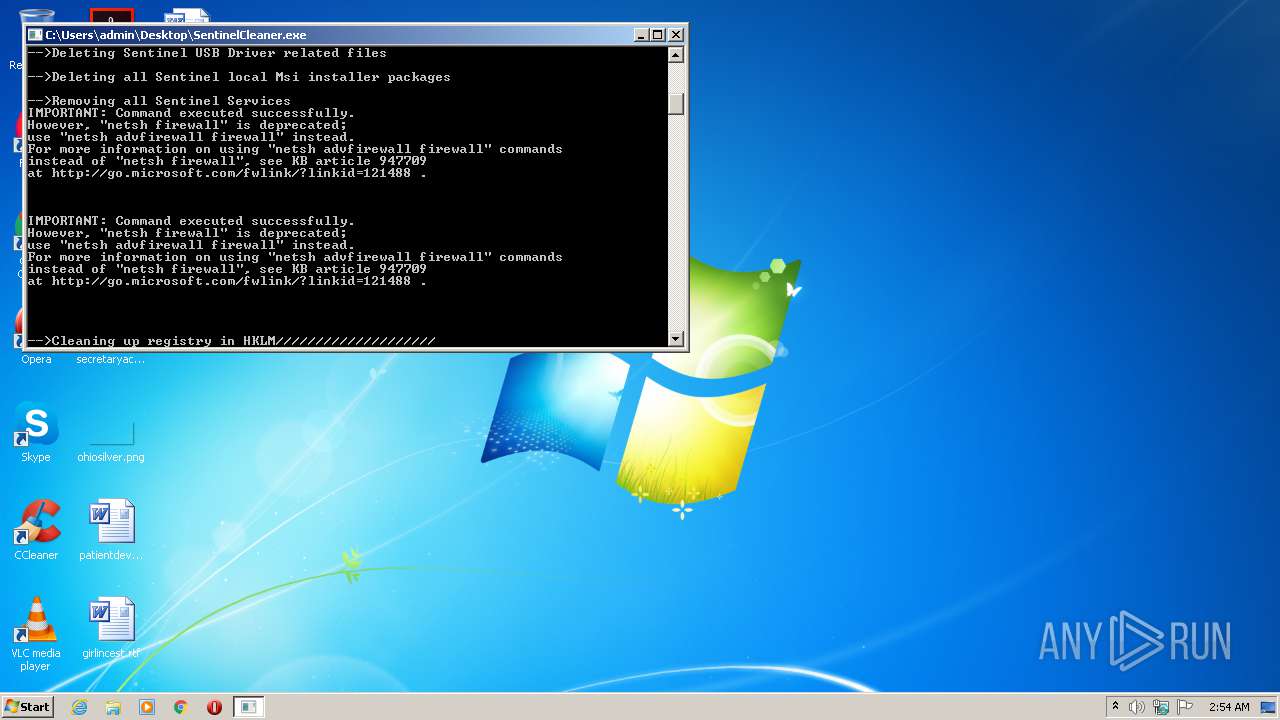
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3704)
- cmd.exe (PID: 2320)
Starts CMD.EXE for commands execution
- SentinelCleaner.exe (PID: 2472)
INFO
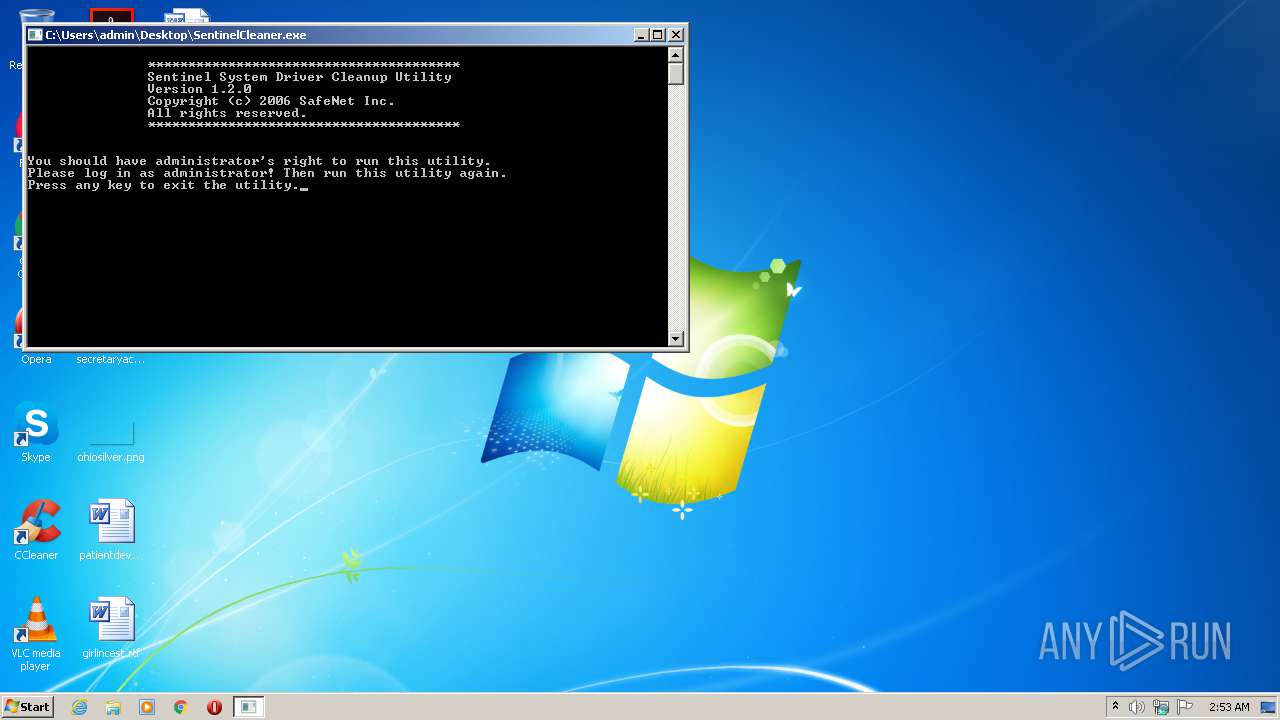
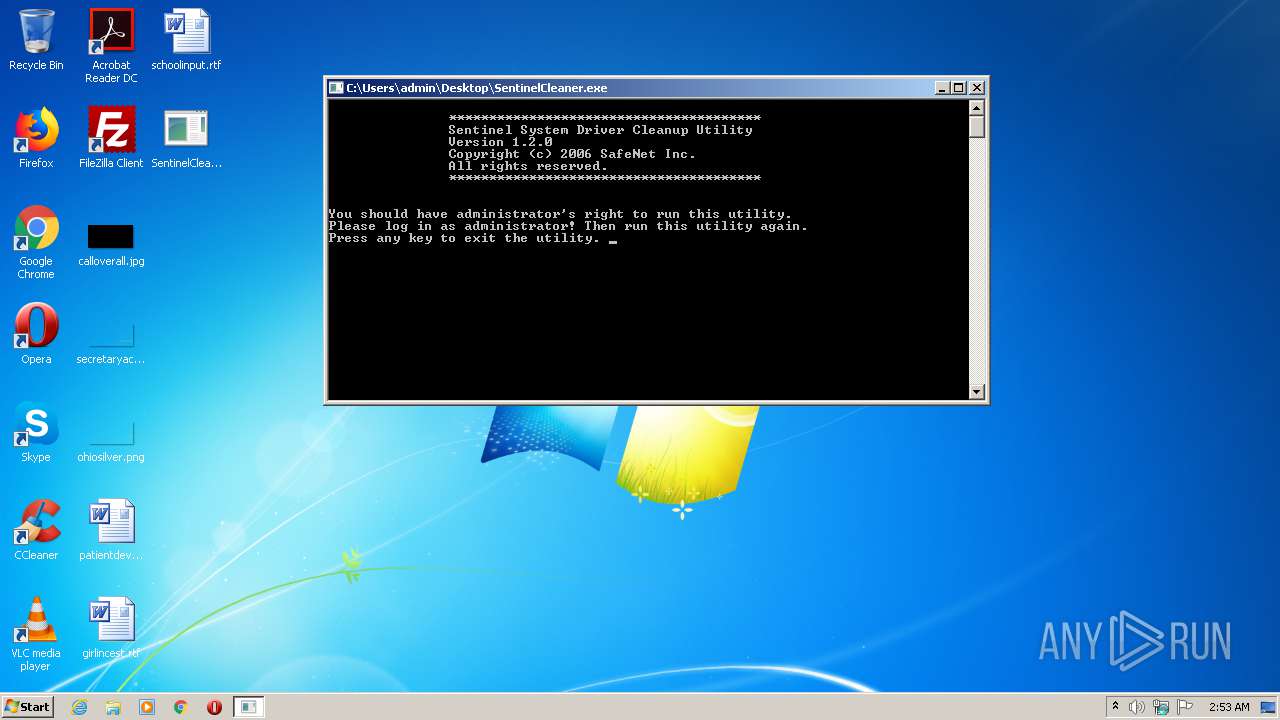
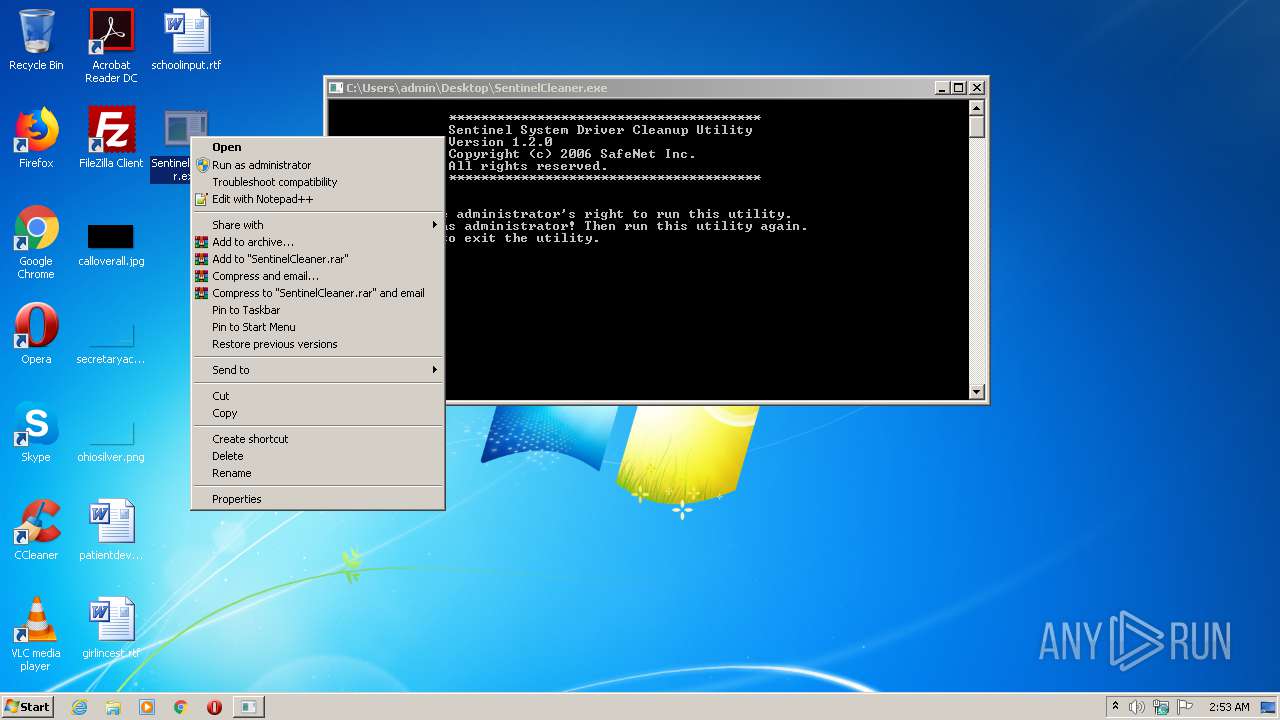
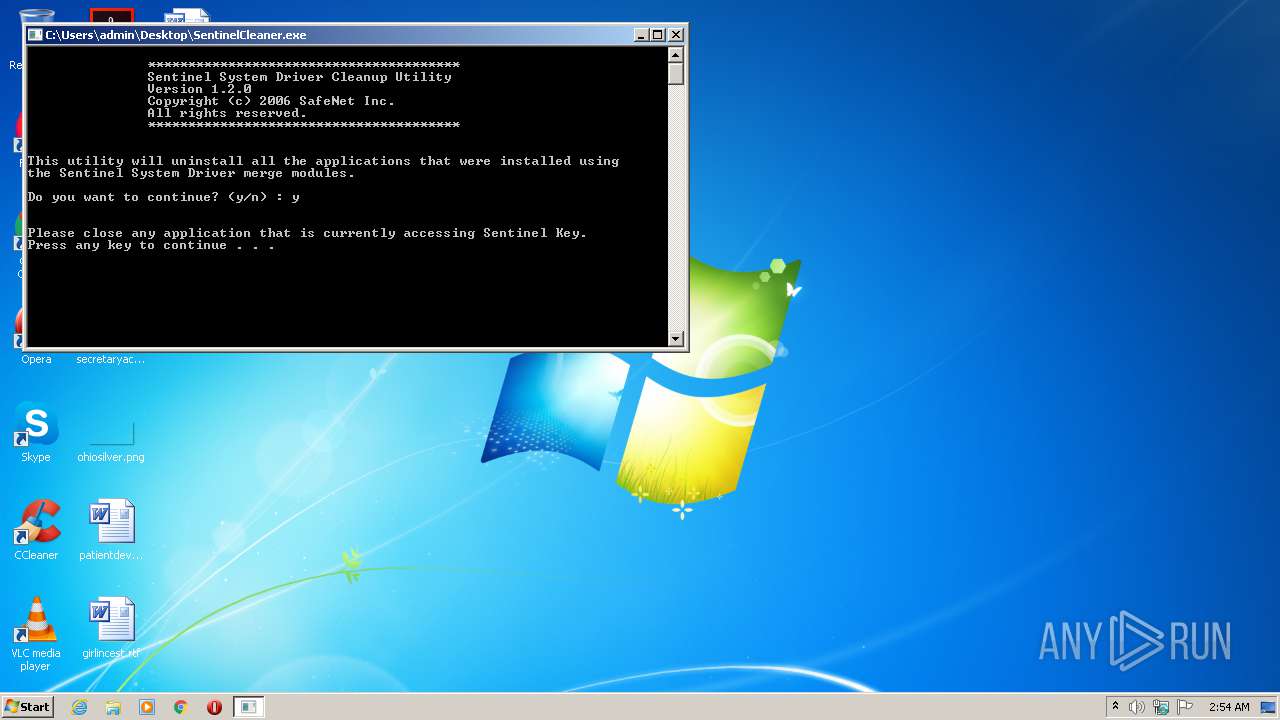
Manual execution by user
- SentinelCleaner.exe (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:12:29 08:06:11+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28672 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6eda |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.2.0.3 |
| ProductVersionNumber: | 1.2.0.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | SafeNet Inc. |
| FileDescription: | Sentinel Cleanup Utility |
| FileVersion: | 1, 2, 0, 3 |
| InternalName: | SSDCleanup |
| LegalCopyright: | Copyright (C) 2006 SafeNet Inc. |
| LegalTrademarks: | - |
| OriginalFileName: | SSDCleanup.exe |
| PrivateBuild: | - |
| ProductName: | SafeNet SSDCleanup |
| ProductVersion: | 1, 2, 0, 3 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 29-Dec-2006 07:06:11 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | SafeNet Inc. |
| FileDescription: | Sentinel Cleanup Utility |
| FileVersion: | 1, 2, 0, 3 |
| InternalName: | SSDCleanup |
| LegalCopyright: | Copyright (C) 2006 SafeNet Inc. |
| LegalTrademarks: | - |
| OriginalFilename: | SSDCleanup.exe |
| PrivateBuild: | - |
| ProductName: | SafeNet SSDCleanup |
| ProductVersion: | 1, 2, 0, 3 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 29-Dec-2006 07:06:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000064C6 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.86267 |
.rdata | 0x00008000 | 0x00001226 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.34214 |
.data | 0x0000A000 | 0x000021F8 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.30307 |
.rsrc | 0x0000D000 | 0x00000478 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.10816 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.36362 | 916 | UNKNOWN | Chinese - PRC | RT_VERSION |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MFC42.DLL |
MSVCP60.dll |
MSVCRT.dll |
SHLWAPI.dll |
USER32.dll |
msi.dll |
Total processes
49
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | C:\Windows\system32\cmd.exe /c PAUSE | C:\Windows\system32\cmd.exe | — | SentinelCleaner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2320 | C:\Windows\system32\cmd.exe /c netsh exec C:\Users\admin\AppData\Local\Temp\\script.dat | C:\Windows\system32\cmd.exe | — | SentinelCleaner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2380 | netsh exec C:\Users\admin\AppData\Local\Temp\\script.dat | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\Desktop\SentinelCleaner.exe" | C:\Users\admin\Desktop\SentinelCleaner.exe | explorer.exe | ||||||||||||
User: admin Company: SafeNet Inc. Integrity Level: HIGH Description: Sentinel Cleanup Utility Exit code: 0 Version: 1, 2, 0, 3 Modules
| |||||||||||||||
| 2480 | C:\Windows\system32\cmd.exe /c PAUSE | C:\Windows\system32\cmd.exe | — | SentinelCleaner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\Desktop\SentinelCleaner.exe" | C:\Users\admin\Desktop\SentinelCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: SafeNet Inc. Integrity Level: MEDIUM Description: Sentinel Cleanup Utility Exit code: 3221225547 Version: 1, 2, 0, 3 Modules
| |||||||||||||||
| 3704 | C:\Windows\system32\cmd.exe /c netsh exec C:\Users\admin\AppData\Local\Temp\\script.dat | C:\Windows\system32\cmd.exe | — | SentinelCleaner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3960 | netsh exec C:\Users\admin\AppData\Local\Temp\\script.dat | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
138
Read events
34
Write events
104
Delete events
0
Modification events
| (PID) Process: | (2472) SentinelCleaner.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Program Files\Common Files\SafeNet Sentinel\Sentinel Keys Driver | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2380) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | SentinelCleaner.exe | C:\Users\admin\AppData\Local\Temp\script.dat | text | |
MD5:— | SHA256:— | |||
| 2472 | SentinelCleaner.exe | C:\Windows\INF\oem0.PNF | pnf | |
MD5:DAE7BA9175551BFA796D7B45ED700C7E | SHA256:EC9D17406F5D7F041E6C2BD21931A20527D2DD4DB340C22876B25DBC4BD90D00 | |||
| 2472 | SentinelCleaner.exe | C:\Windows\INF\oem1.PNF | pnf | |
MD5:8504B83F275B392AF5AB6E4D54BCBF37 | SHA256:07DB433C8335935F9933A2C7CC056B6573670A4E4950220103C546D5718870BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report