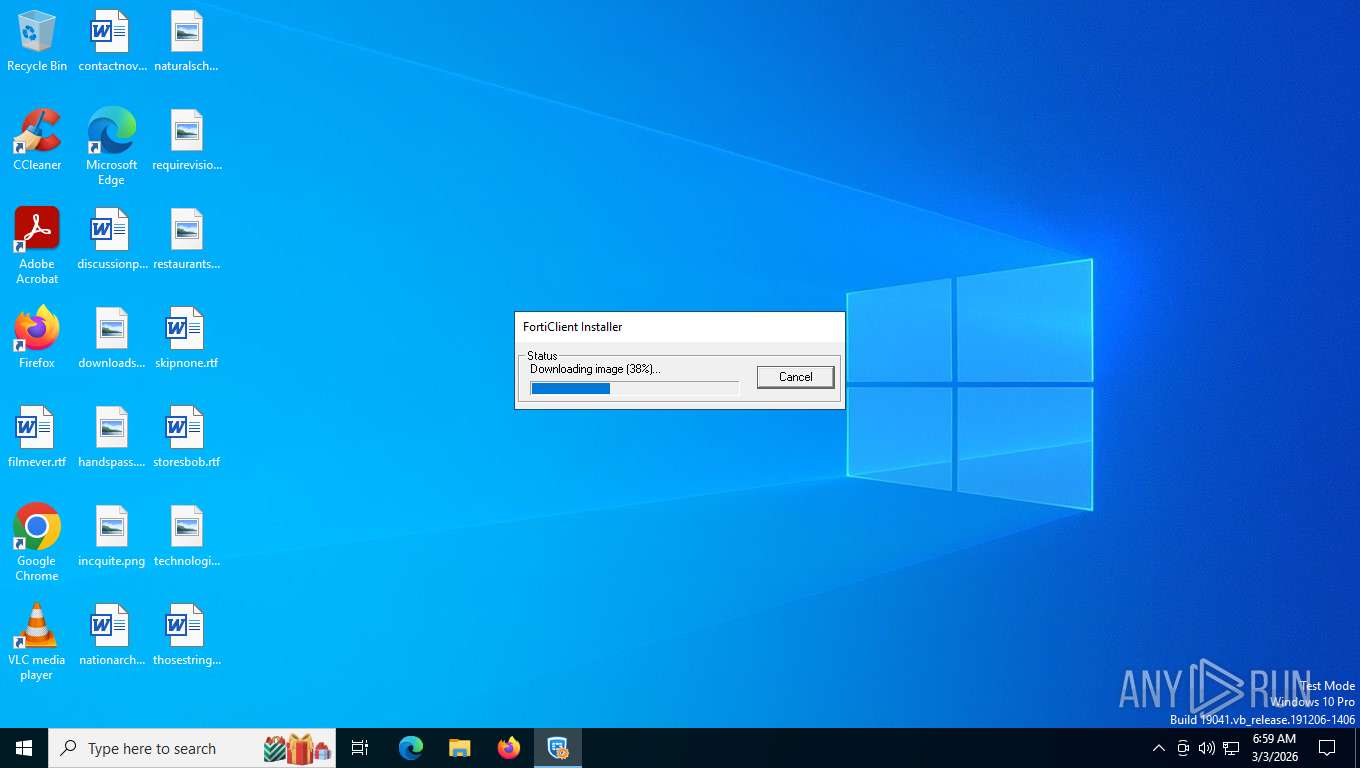
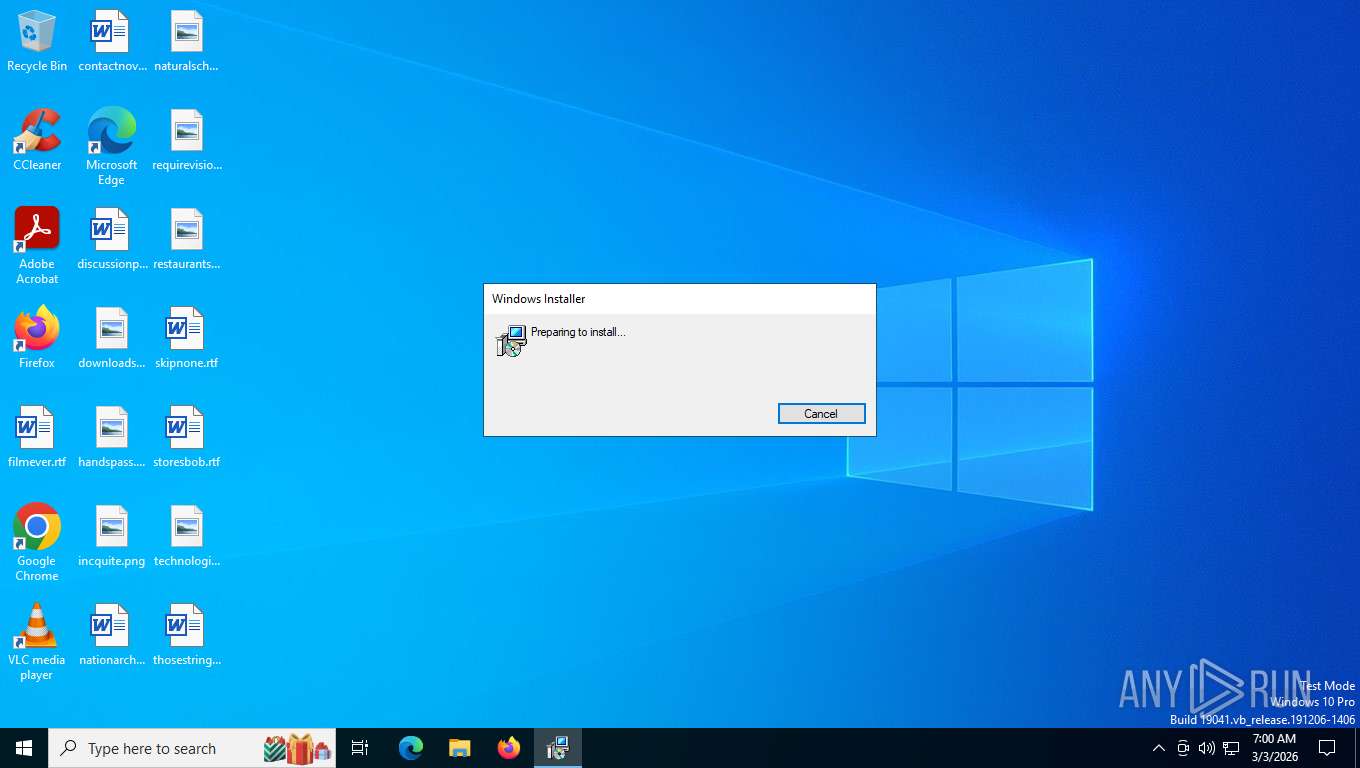
| File name: | FortiClientInstaller.exe |
| Full analysis: | https://app.any.run/tasks/db88c485-5833-4470-9971-c69adc431175 |
| Verdict: | Malicious activity |
| Analysis date: | March 03, 2026, 11:58:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | C58F681123BB38F54CD968DB3867B78F |
| SHA1: | 2815DE01F07B098789F22896E0D33C387311D974 |
| SHA256: | 379D3A4BC348C5BCB0802A9FCFCD7450D99FA310DB1CB7D66ACEA3C400FE1D43 |
| SSDEEP: | 98304:hHs0zaf5xFyk2ABZZDTlAl1n5sS9Mm41m9nPEwU8Ed9qs4YBOvKQx+wJimWyTRRF:uHQZ4Q |
MALICIOUS
Potential DLL hijacking behavior detected
- regsvr32.exe (PID: 5524)
- regsvr32.exe (PID: 476)
- VSSVC.exe (PID: 9196)
Registers / Runs the DLL via REGSVR32.EXE
- msiexec.exe (PID: 3552)
- scheduler.exe (PID: 3096)
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x86.exe (PID: 6392)
Starts NET.EXE for service management
- net.exe (PID: 8080)
- FortiSSLVPNdaemon.exe (PID: 7308)
SUSPICIOUS
Executable content was dropped or overwritten
- FortiClientInstaller.exe (PID: 8820)
- FortiClientInstaller.exe (PID: 412)
- VC_redist.x64.exe (PID: 4060)
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x64.exe (PID: 2280)
- VC_redist.x64.exe (PID: 9108)
- VC_redist.x86.exe (PID: 8376)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 8052)
- VC_redist.x86.exe (PID: 6392)
- VC_redist.x86.exe (PID: 4816)
- update_task.exe (PID: 6580)
Starts itself from another location
- FortiClientInstaller.exe (PID: 8820)
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x86.exe (PID: 3544)
Creates/Modifies COM task schedule object
- FortiClientInstaller.exe (PID: 412)
- regsvr32.exe (PID: 5524)
- regsvr32.exe (PID: 476)
- msiexec.exe (PID: 8780)
- regsvr32.exe (PID: 4544)
Reads the Windows owner or organization settings
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 8780)
Application launched itself
- msiexec.exe (PID: 8780)
- VC_redist.x64.exe (PID: 9076)
- VC_redist.x64.exe (PID: 2280)
- VC_redist.x86.exe (PID: 4196)
- VC_redist.x86.exe (PID: 8052)
- FortiClient.exe (PID: 5896)
Creates files in the driver directory
- msiexec.exe (PID: 8780)
- msiexec.exe (PID: 3552)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 8780)
- msiexec.exe (PID: 3552)
- drvinst.exe (PID: 3664)
- drvinst.exe (PID: 9152)
- drvinst.exe (PID: 7824)
The process creates files with name similar to system file names
- msiexec.exe (PID: 8780)
Executes as Windows Service
- Fct_SecSvr.exe (PID: 7600)
- scheduler.exe (PID: 3096)
- VSSVC.exe (PID: 9196)
Reads the date of Windows installation
- msiexec.exe (PID: 3552)
- scheduler.exe (PID: 3096)
- FortiElevate.exe (PID: 1092)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 6392)
The process drops C-runtime libraries
- msiexec.exe (PID: 8780)
Searches for installed software
- dllhost.exe (PID: 8272)
- VC_redist.x64.exe (PID: 2280)
- VC_redist.x64.exe (PID: 9108)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 6392)
- VC_redist.x86.exe (PID: 8052)
- VC_redist.x86.exe (PID: 4816)
- update_task.exe (PID: 6580)
Modifies hosts file to alter network resolution
- FCDBLog.exe (PID: 8580)
Reads Mozilla Firefox installation path
- FCDBLog.exe (PID: 8580)
Checks for external IP
- FortiESNAC.exe (PID: 8468)
INFO
The sample compiled with english language support
- FortiClientInstaller.exe (PID: 8820)
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 8780)
- msiexec.exe (PID: 3552)
- drvinst.exe (PID: 3664)
- drvinst.exe (PID: 7660)
- VC_redist.x64.exe (PID: 4060)
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x64.exe (PID: 2280)
- VC_redist.x64.exe (PID: 9108)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 8376)
- VC_redist.x86.exe (PID: 8052)
- VC_redist.x86.exe (PID: 6392)
- VC_redist.x86.exe (PID: 4816)
- update_task.exe (PID: 6580)
Reads the computer name
- FortiClientInstaller.exe (PID: 8820)
- msiexec.exe (PID: 8780)
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 7696)
- msiexec.exe (PID: 4964)
- msiexec.exe (PID: 3552)
- drvinst.exe (PID: 9152)
- drvinst.exe (PID: 7832)
- drvinst.exe (PID: 7824)
- Fct_SecSvr.exe (PID: 7600)
- scheduler.exe (PID: 3096)
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x64.exe (PID: 7088)
- drvinst.exe (PID: 3664)
- VC_redist.x64.exe (PID: 2280)
- drvinst.exe (PID: 6468)
- VC_redist.x64.exe (PID: 9108)
- drvinst.exe (PID: 7660)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 6392)
- VC_redist.x86.exe (PID: 8052)
- VC_redist.x86.exe (PID: 4816)
- FCDBLog.exe (PID: 8580)
- FcVpnSched.exe (PID: 5408)
- fcappdb.exe (PID: 3332)
- FortiTray.exe (PID: 1656)
- FortiESNAC.exe (PID: 8468)
- FortiSSLVPNdaemon.exe (PID: 7308)
- FortiSettings.exe (PID: 8760)
- FortiVPN.exe (PID: 8436)
- FortiClient.exe (PID: 5896)
- EPCUserAvatar.exe (PID: 7672)
- FortiClient.exe (PID: 7516)
- FortiElevate.exe (PID: 1092)
- FortiClient.exe (PID: 7604)
- FortiClient.exe (PID: 8256)
- FortiClientSecurity.exe (PID: 9072)
- FortiClient.exe (PID: 5336)
- update_task.exe (PID: 6580)
Checks supported languages
- FortiClientInstaller.exe (PID: 8820)
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 8780)
- msiexec.exe (PID: 7696)
- msiexec.exe (PID: 4964)
- msiexec.exe (PID: 3552)
- drvinst.exe (PID: 3664)
- drvinst.exe (PID: 7832)
- drvinst.exe (PID: 7824)
- drvinst.exe (PID: 6468)
- Fct_SecSvr.exe (PID: 7600)
- scheduler.exe (PID: 3096)
- VC_redist.x64.exe (PID: 4060)
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x64.exe (PID: 2280)
- VC_redist.x64.exe (PID: 9108)
- VC_redist.x86.exe (PID: 8376)
- drvinst.exe (PID: 7660)
- drvinst.exe (PID: 9152)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 6392)
- VC_redist.x86.exe (PID: 4196)
- VC_redist.x86.exe (PID: 8052)
- VC_redist.x86.exe (PID: 4816)
- FCDBLog.exe (PID: 8580)
- FcVpnSched.exe (PID: 5408)
- fcappdb.exe (PID: 3332)
- FortiVPN.exe (PID: 8436)
- FortiTray.exe (PID: 1656)
- FortiESNAC.exe (PID: 8468)
- FortiSSLVPNdaemon.exe (PID: 7308)
- FortiSettings.exe (PID: 8760)
- FortiClient.exe (PID: 5896)
- EPCUserAvatar.exe (PID: 7672)
- FortiClient.exe (PID: 7516)
- FortiClient.exe (PID: 7604)
- FortiClient.exe (PID: 8256)
- VC_redist.x64.exe (PID: 9076)
- FortiClient.exe (PID: 8972)
- FortiElevate.exe (PID: 1092)
- FortiClientSecurity.exe (PID: 9072)
- FortiClient.exe (PID: 5336)
- update_task.exe (PID: 6580)
- FortiClient.exe (PID: 1916)
- vcm2.exe (PID: 5516)
Process checks whether UAC notifications are on
- FortiClientInstaller.exe (PID: 8820)
Process checks computer location settings
- FortiClientInstaller.exe (PID: 8820)
- msiexec.exe (PID: 3552)
- FCDBLog.exe (PID: 8580)
- FortiClient.exe (PID: 5896)
- FortiClient.exe (PID: 5336)
- update_task.exe (PID: 6580)
- FortiElevate.exe (PID: 1092)
Reads security settings of Internet Explorer
- FortiClientInstaller.exe (PID: 8820)
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 3552)
- VC_redist.x64.exe (PID: 1988)
- VC_redist.x64.exe (PID: 2280)
- VC_redist.x86.exe (PID: 3544)
- VC_redist.x86.exe (PID: 8052)
- scheduler.exe (PID: 3096)
- FCDBLog.exe (PID: 8580)
- FortiElevate.exe (PID: 1092)
- update_task.exe (PID: 6580)
Creates files in the program directory
- FortiClientInstaller.exe (PID: 412)
- scheduler.exe (PID: 3096)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x86.exe (PID: 6392)
- FCDBLog.exe (PID: 8580)
- FcVpnSched.exe (PID: 5408)
- fcappdb.exe (PID: 3332)
- FortiVPN.exe (PID: 8436)
- FortiSettings.exe (PID: 8760)
- FortiSSLVPNdaemon.exe (PID: 7308)
- FortiESNAC.exe (PID: 8468)
- update_task.exe (PID: 6580)
Create files in a temporary directory
- FortiClientInstaller.exe (PID: 8820)
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 4964)
- msiexec.exe (PID: 3552)
- EPCUserAvatar.exe (PID: 7672)
Reads the machine GUID from the registry
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 8780)
- drvinst.exe (PID: 3664)
- drvinst.exe (PID: 9152)
- drvinst.exe (PID: 7824)
- scheduler.exe (PID: 3096)
- msiexec.exe (PID: 3552)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x86.exe (PID: 6392)
- FortiClient.exe (PID: 5896)
Creates files or folders in the user directory
- FortiClientInstaller.exe (PID: 412)
- FortiTray.exe (PID: 1656)
- FortiClient.exe (PID: 5896)
- EPCUserAvatar.exe (PID: 7672)
- FortiClient.exe (PID: 7604)
Checks proxy server information
- FortiClientInstaller.exe (PID: 412)
- slui.exe (PID: 8584)
- FortiClient.exe (PID: 5896)
Reads Environment values
- msiexec.exe (PID: 7696)
- msiexec.exe (PID: 4964)
- Fct_SecSvr.exe (PID: 7600)
- scheduler.exe (PID: 3096)
- FCDBLog.exe (PID: 8580)
- FortiTray.exe (PID: 1656)
- FortiSSLVPNdaemon.exe (PID: 7308)
- FortiVPN.exe (PID: 8436)
- FortiESNAC.exe (PID: 8468)
- EPCUserAvatar.exe (PID: 7672)
- FortiClient.exe (PID: 5896)
- FortiElevate.exe (PID: 1092)
- FortiClientSecurity.exe (PID: 9072)
- FortiClient.exe (PID: 5336)
- update_task.exe (PID: 6580)
Drops script file
- FortiClientInstaller.exe (PID: 412)
- msiexec.exe (PID: 8780)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8780)
- msiexec.exe (PID: 3552)
Creates a software uninstall entry
- msiexec.exe (PID: 3552)
- msiexec.exe (PID: 8780)
- VC_redist.x64.exe (PID: 7088)
- FortiESNAC.exe (PID: 8468)
- VC_redist.x86.exe (PID: 6392)
Manages system restore points
- SrTasks.exe (PID: 8048)
Launching a file from a Registry key
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x86.exe (PID: 6392)
Creating file in SysWOW64
- msiexec.exe (PID: 8780)
Manual execution by a user
- FortiClient.exe (PID: 5896)
Reads product name
- FortiClient.exe (PID: 5896)
- FortiClient.exe (PID: 5336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:12:10 21:28:03+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.44 |
| CodeSize: | 3811328 |
| InitializedDataSize: | 1363968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11adb0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.4.5.1949 |
| ProductVersionNumber: | 7.4.5.1949 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Fortinet Inc. |
| FileDescription: | FortiClient Online Installation |
| FileVersion: | 7.4.5.1949 |
| InternalName: | FortiClientInstaller |
| LegalCopyright: | 2025 Fortinet Inc. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | FortiClientInstaller.exe |
| PrivateBuild: | - |
| ProductName: | FortiClient Online Installation |
| ProductVersion: | 7.4.5.1949 |
| SpecialBuild: | - |
Total processes
222
Monitored processes
63
Malicious processes
6
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Users\admin\AppData\Local\Temp\{C7724024-482F-416C-96DD-C5285E480B01}\FortiClientInstaller.exe" | C:\Users\admin\AppData\Local\Temp\{C7724024-482F-416C-96DD-C5285E480B01}\FortiClientInstaller.exe | FortiClientInstaller.exe | ||||||||||||
User: admin Company: Fortinet Inc. Integrity Level: HIGH Description: FortiClient Online Installation Exit code: 0 Version: 7.4.5.1949 Modules
| |||||||||||||||
| 476 | /s "C:\Program Files\Fortinet\FortiClient\x86\FortiAmsi.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1092 | ./FortiElevate.exe | C:\Program Files\Fortinet\FortiClient\FortiElevate.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Elevation Exit code: 0 Version: 7.4.5.1949 Modules
| |||||||||||||||
| 1656 | -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000008 | C:\Program Files\Fortinet\FortiClient\FortiTray.exe | scheduler.exe | ||||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient System Tray Controller Version: 7.4.5.1949 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Local\FortiClient" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAABgAAAAAAAAAGAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --mojo-platform-channel-handle=2700 --field-trial-handle=1992,i,7887140896904790758,17754544549930831496,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: LOW Description: FortiClient Console Version: 7.4.5.1949 Modules
| |||||||||||||||
| 1988 | "C:\WINDOWS\Temp\{328D8A6C-3B77-4A36-B921-BF2F22DD720E}\.cr\VC_redist.x64.exe" -burn.clean.room="C:\Program Files\Common Files\Fortinet\FortiClient\VC_redist.x64.exe" -burn.filehandle.attached=708 -burn.filehandle.self=712 /install /quiet /norestart | C:\Windows\Temp\{328D8A6C-3B77-4A36-B921-BF2F22DD720E}\.cr\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 3010 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 2260 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\Fortinet\FortiClient\x86\FortiAmsi.dll" | C:\Windows\System32\regsvr32.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.clean.room="C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.filehandle.attached=520 -burn.filehandle.self=548 -uninstall -quiet -burn.related.upgrade -burn.ancestors={5af95fd8-a22e-458f-acee-c61bd787178e} -burn.filehandle.self=1016 -burn.embedded BurnPipe.{815938CC-1249-4B43-BF68-8830BDD731A8} {B73FA142-DDB2-47BE-A7CC-91B1D2AF0792} 7088 | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 2620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | EPCUserAvatar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
70 948
Read events
67 352
Write events
2 856
Delete events
740
Modification events
| (PID) Process: | (412) FortiClientInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{8052F904-874D-4d28-9380-AA9BDBF13AFD}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: diskcopy.dll | |||
| (PID) Process: | (412) FortiClientInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{8052F904-874D-4d28-9380-AA9BDBF13AFD}\InProcServer32 |
| Operation: | write | Name: | AppID |
Value: {E4174709-1380-4BA8-AED7-FB6A7772E751} | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\20c5a7.rbs |
Value: 31238875 | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\20c5a7.rbsLow |
Value: | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\0853336E0ACA9F7459F6A63C4693343C |
| Operation: | write | Name: | 3AAB47B602F9E6F4482D210349E505B3 |
Value: C:\Program Files\Common Files\Fortinet\FortiClient\VC_redist.x86.exe | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\54E05C2EB36152F4CA01265EF0DB30D7 |
| Operation: | write | Name: | 3AAB47B602F9E6F4482D210349E505B3 |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\BAE2BC2062E17A349A4992D1428C964C |
| Operation: | write | Name: | 3AAB47B602F9E6F4482D210349E505B3 |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\2D32B215BCF6E554BB28AB2F4D4C0723 |
| Operation: | write | Name: | 3AAB47B602F9E6F4482D210349E505B3 |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
| (PID) Process: | (8780) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\C715147F8E1E0C04680EAA2133FCFEC9 |
| Operation: | write | Name: | 3AAB47B602F9E6F4482D210349E505B3 |
Value: C:\Program Files\Fortinet\FortiClient\FCDBLog.exe | |||
Executable files
356
Suspicious files
539
Text files
179
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\Local\Temp\FortiClient.msi | — | |
MD5:— | SHA256:— | |||
| 412 | FortiClientInstaller.exe | C:\ProgramData\Applications\Cache\{6B74BAA3-9F20-4F6E-84D2-1230945E503B}\7.4.5.1949\FortiClient.msi | — | |
MD5:— | SHA256:— | |||
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\Local\Temp\obj_1_a08412 | binary | |
MD5:A37A5D8A2D57149772C9B968D5B1E359 | SHA256:212D46F7BDACDFB1529786D1D7E20E2F75C5D09D72A2167DC1D5FA1A8036F6C9 | |||
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:3D41C9F18076553BAFB2A9ADC5CAF089 | SHA256:443C840A317B8AC567EE0D0839E219CDF79E6B4112E0959F8DF46E52284AE13F | |||
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:1C004E27F642E25F97A60F8E303C472C | SHA256:25B7AF36868F57211E3D7E40AB21EF7A5D39B74407E6F37C7E28F9FC8E20770B | |||
| 8780 | msiexec.exe | C:\Windows\Installer\20c5a6.msi | — | |
MD5:— | SHA256:— | |||
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\Local\Temp\FCTInstall.log | text | |
MD5:654EA852E663F21C8700AFED19AA3DC7 | SHA256:9AB1993965F0C6A6621BA412A5C855CE347D134D6E051A384F5205DFFA36AF64 | |||
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\Local\Temp\MSIFF2A.tmp | executable | |
MD5:0311280AEA566D19893730D587A34FE1 | SHA256:6CA8F540A433217F4B62689C79D0564032AFA6F1FCD4D131D88DC7587AEB04FD | |||
| 412 | FortiClientInstaller.exe | C:\Users\admin\AppData\Local\Temp\MSI28A.tmp | executable | |
MD5:0311280AEA566D19893730D587A34FE1 | SHA256:6CA8F540A433217F4B62689C79D0564032AFA6F1FCD4D131D88DC7587AEB04FD | |||
| 8820 | FortiClientInstaller.exe | C:\Users\admin\AppData\Local\Temp\{C7724024-482F-416C-96DD-C5285E480B01}\FortiClientInstaller.exe | executable | |
MD5:C58F681123BB38F54CD968DB3867B78F | SHA256:379D3A4BC348C5BCB0802A9FCFCD7450D99FA310DB1CB7D66ACEA3C400FE1D43 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
53
DNS requests
30
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
8628 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
5392 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
5392 | SIHClient.exe | GET | 200 | 135.232.92.97:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
5392 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
5392 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
5568 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
412 | FortiClientInstaller.exe | POST | 200 | 209.40.106.66:80 | http://209.40.106.66/fdsupdate | unknown | — | — | unknown |
412 | FortiClientInstaller.exe | POST | 200 | 209.40.106.66:80 | http://209.40.106.66/fdsupdate | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8628 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5180 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 92.123.104.49:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
412 | FortiClientInstaller.exe | 209.40.106.66:80 | forticlient.fortinet.net | FORTINET | US | unknown |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
forticlient.fortinet.net |
| unknown |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8628 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
8468 | FortiESNAC.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
8468 | FortiESNAC.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
8468 | FortiESNAC.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
8468 | FortiESNAC.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
8468 | FortiESNAC.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
8468 | FortiESNAC.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
Fct_SecSvr.exe | {FCT}"C:\Program Files\Fortinet\FortiClient\Fct_SecSvr.exe"
|
Fct_SecSvr.exe | {FCT}WscRegisterAvProduct(), Register() returned 0x0, err=2, bstrRemediationExePath=C:\Program Files\Fortinet\FortiClient\FortiClientConsole.exe, strDisplayName=FortiClient
|
Fct_SecSvr.exe | {FCT}C:\Program Files\Fortinet\FortiClient\Fct_SecSvr.exe
|
msiexec.exe | Failed to release Service
|
FcVpnSched.exe | ---> 62
|
FortiTray.exe | ---> 78
|
FortiClient.exe | ---> 46
|
FortiClient.exe | [0303/070253.572:ERROR:crash_report_database_win.cc(614)] CreateDirectory C:\Users\admin\AppData\Roaming\FortiClient\logs\trace: The system cannot find the path specified. (0x3)
|