| URL: | https://2n8w.app.link/?~channel=Email&~feature=ConfirmationEmail--AtocETicket&~campaign=WebToApp&~tags=locale%3Den_GB&~tags=version%3D1&~tags=marketing_code%3DBSH3675&$android_url=https%3A%2F%2Fplay.google.com%2Fstore%2Fapps%2Fdetails%3Fid%3Dcom.thetrainline%26hl%3Den-GB&$android_deepview=false&$android_passive_deepview=false&$ios_url=https%3A%2F%2Fitunes.apple.com%2FGB%2Fapp%2Fthetrainline%2Fid334235181&$ios_deepview=false&$ios_passive_deepview=false&$fallback_url=https://thegurlonthego.com/tangotango/mangoxxxmanoxxx/.filepage/vivi///cm9iZXJ0LmRhbnRvbmlvQHRveW90YS5jb20= |
| Full analysis: | https://app.any.run/tasks/712a3b13-7027-4cb4-a0b0-51915e713a82 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2024, 21:03:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7478FB9126732D580888BB22DE396886 |
| SHA1: | 2CCBEA978775A399B36AD12207AE1A595A30EABB |
| SHA256: | 37919ECF33E5A0E4FC5010334755DFA40068282BCA383BCDF8D03F6D99343BBA |
| SSDEEP: | 12:2TScoHFMkd2KAEKIjSjA86x2KAZEYxt+1fYxiEYx4UPCGbZFY:2TwL/pSjt6xtKxgdYxKx6Uc |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2588 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2640 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://2n8w.app.link/?~channel=Email&~feature=ConfirmationEmail--AtocETicket&~campaign=WebToApp&~tags=locale%3Den_GB&~tags=version%3D1&~tags=marketing_code%3DBSH3675&$android_url=https%3A%2F%2Fplay.google.com%2Fstore%2Fapps%2Fdetails%3Fid%3Dcom.thetrainline%26hl%3Den-GB&$android_deepview=false&$android_passive_deepview=false&$ios_url=https%3A%2F%2Fitunes.apple.com%2FGB%2Fapp%2Fthetrainline%2Fid334235181&$ios_deepview=false&$ios_passive_deepview=false&$fallback_url=https://thegurlonthego.com/tangotango/mangoxxxmanoxxx/.filepage/vivi///cm9iZXJ0LmRhbnRvbmlvQHRveW90YS5jb20=" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 351
Read events
16 244
Write events
99
Delete events
8
Modification events
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
21
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:2393762B02BD693F6DBBD84FCB3B351D | SHA256:18B0C2507C038C8F786A801649C9F04F46C098B812253480334C7527A28C3AA8 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:1279D835F78EF23F49A5EE668BA7AC82 | SHA256:FB16CE9EBF79E14F5F378783408CE34D594806EBFD7CC1CF2CFB0B18F6ADE5D0 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | binary | |
MD5:4560214AEB0413935A8FDCDEDEA8DF2D | SHA256:DB7CFDB54B71FA150669EF4241CC709335D54836B35656EF5F62F93FF0AA21D3 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:598F78BCC55DB4EFBB2B8C22731615AA | SHA256:36BE264730FCE9E941D0ABE9040E461A9CEC49BAB576D21D09AC1083BE056177 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:967CEDEC9A4EC7E270590D5B6ABB5463 | SHA256:BA0813057AE688E6E304B6A6F5BDDE9BE0DA3D51705979F15407AD07302714BD | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\S070X2J8.txt | text | |
MD5:245AF67B635C33949D37B4C68A50003C | SHA256:FF489657F306A763937C017761E1893C9EE86BB55423AF462461A04FEDE80305 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:DA5929785777C8F48E42DF59118B7B26 | SHA256:95F7D138239A9884861ED122CA083311943F41C6534F8BF6B7C932D9DDC6A05B | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:02141ADA5B2DA4B9C18E86A3D87322FB | SHA256:C8C541A97371C2F7A19F85D70DB50D819CD97546B5BA879F509641ADFC8F76FB | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | binary | |
MD5:7F4B2060E9EBDCC558A9C1116BEBCF4A | SHA256:E4A6122B02BAF41CC7A7EE421649C24A1B0FAEE6FC27DCA32C53F875AD2946D2 | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
32
DNS requests
17
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2588 | iexplore.exe | GET | 304 | 184.24.77.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?09ca35c5e0844a72 | DE | — | — | unknown |
2640 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 313 b | unknown |
2588 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | unknown |
2588 | iexplore.exe | GET | 304 | 184.24.77.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a0aa2a2858c872c9 | DE | — | — | unknown |
2588 | iexplore.exe | GET | 200 | 108.138.2.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 2.02 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | binary | 1.49 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.37 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 184.24.77.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d66bcfdf10b71413 | DE | compressed | 65.2 Kb | unknown |
2588 | iexplore.exe | GET | 200 | 184.24.77.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?bdf45b2858d38473 | DE | compressed | 65.2 Kb | unknown |
2640 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | iexplore.exe | 18.66.196.19:443 | 2n8w.app.link | — | US | unknown |
2588 | iexplore.exe | 184.24.77.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2588 | iexplore.exe | 108.138.2.195:80 | o.ss2.us | AMAZON-02 | US | unknown |
2588 | iexplore.exe | 18.245.39.64:80 | ocsp.rootg2.amazontrust.com | — | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | iexplore.exe | 162.241.120.242:443 | thegurlonthego.com | UNIFIEDLAYER-AS-1 | US | unknown |
2588 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2640 | iexplore.exe | 162.241.120.242:443 | thegurlonthego.com | UNIFIEDLAYER-AS-1 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2n8w.app.link |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
thegurlonthego.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
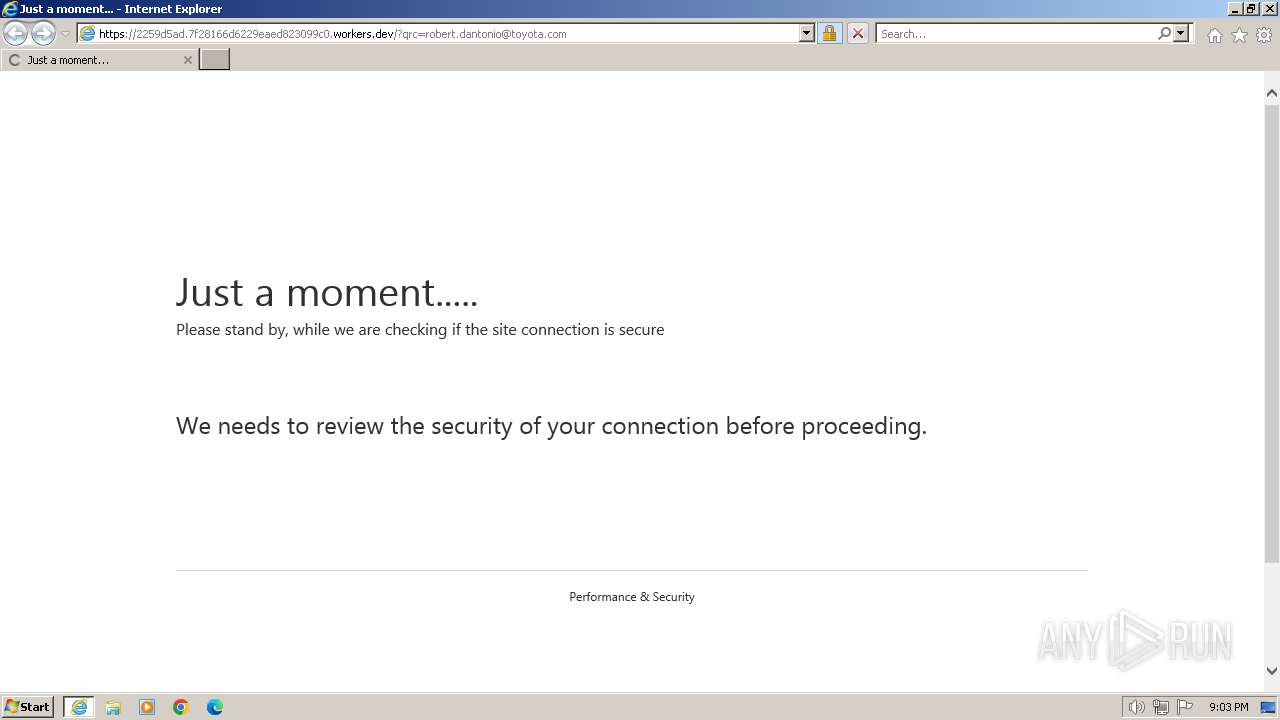
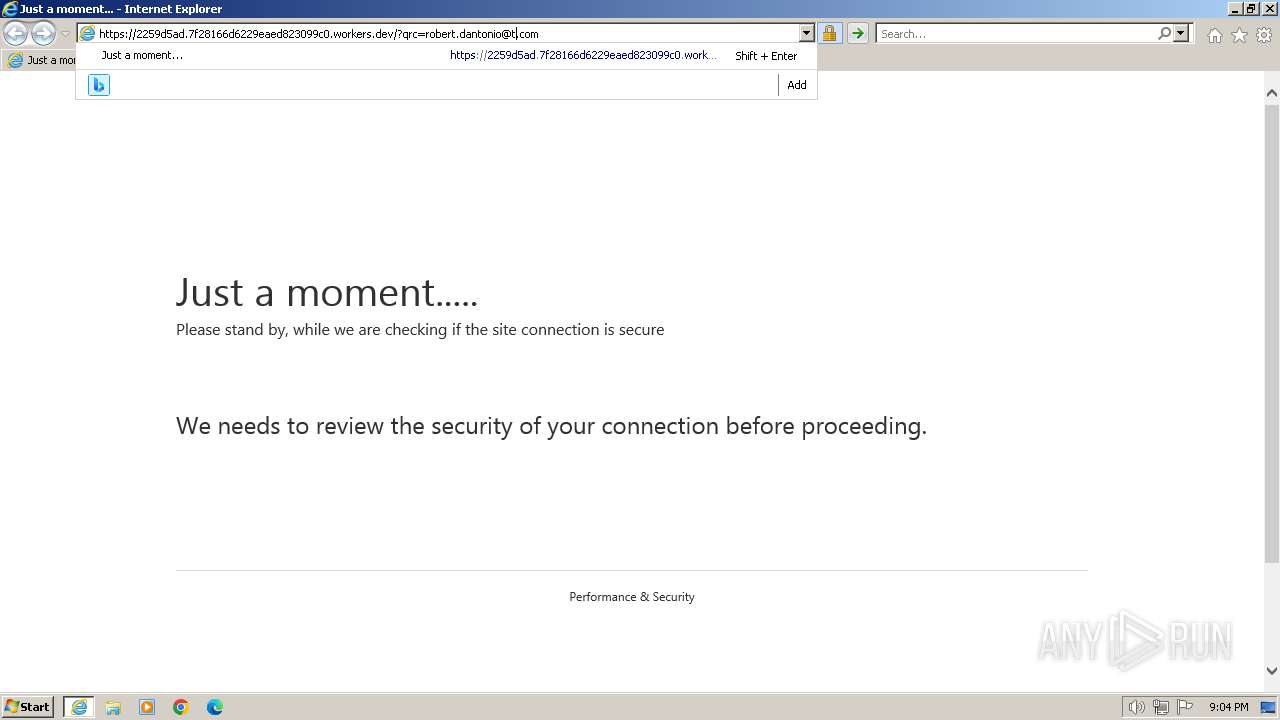
2259d5ad.7f28166d6229eaed823099c0.workers.dev |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2588 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Worker App observed TLS SNI |
2588 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspicious Cloudflare Worker Name observed in Phishing (TLS SNI) |
2588 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2588 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |