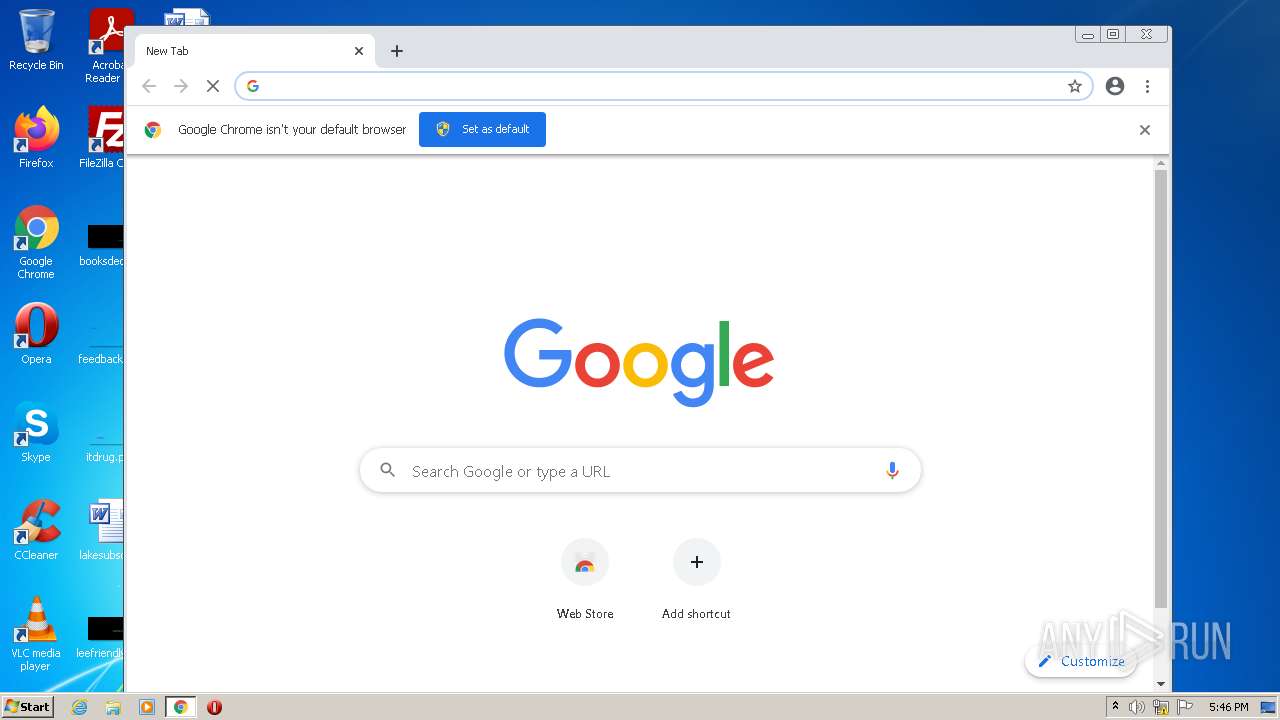
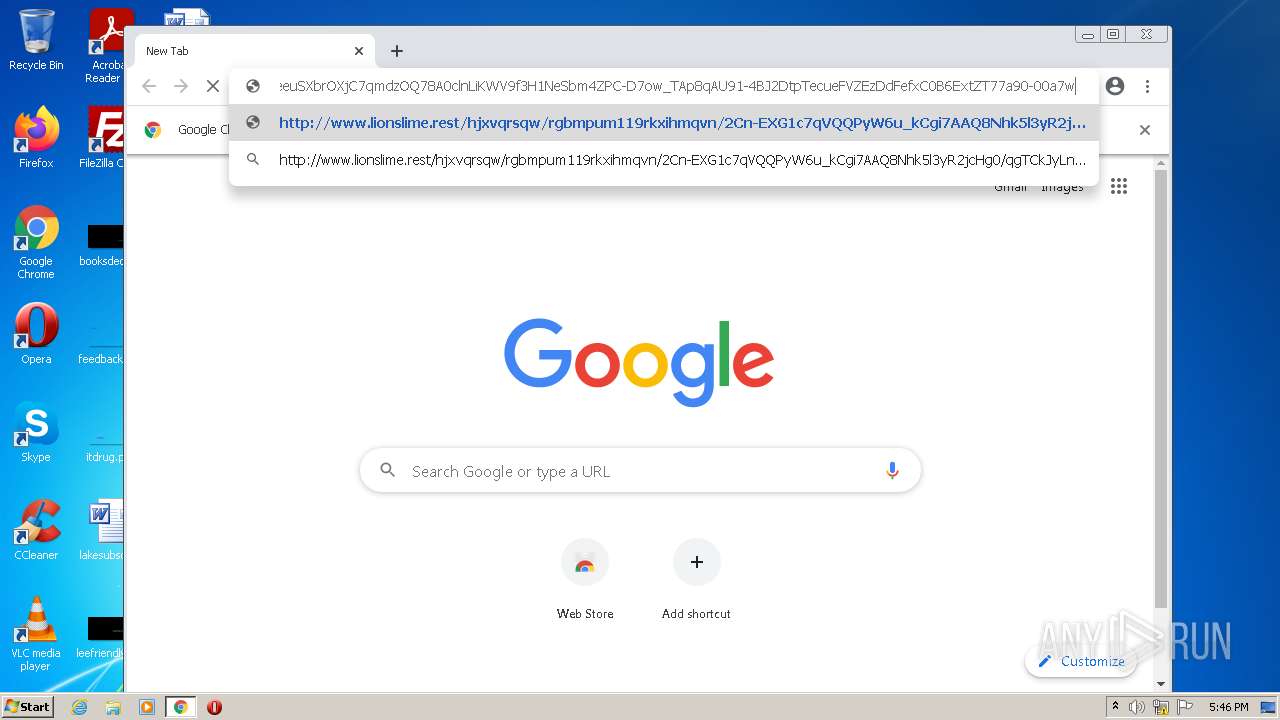
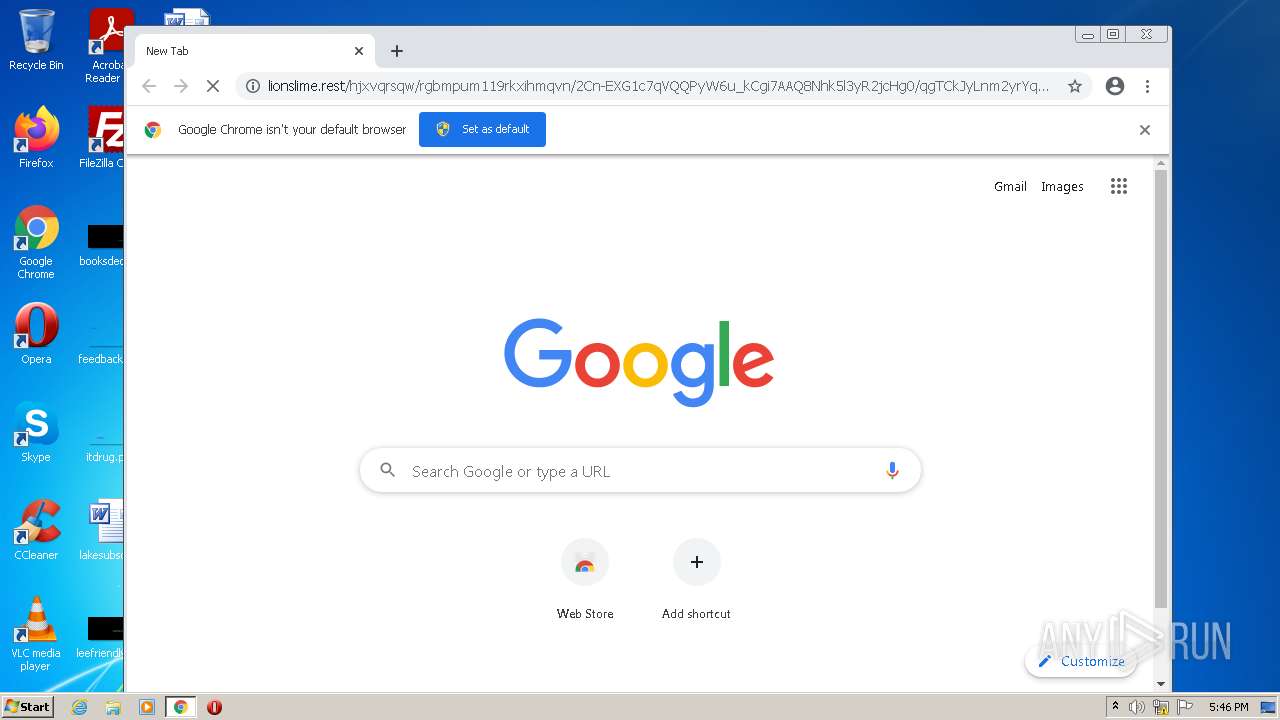
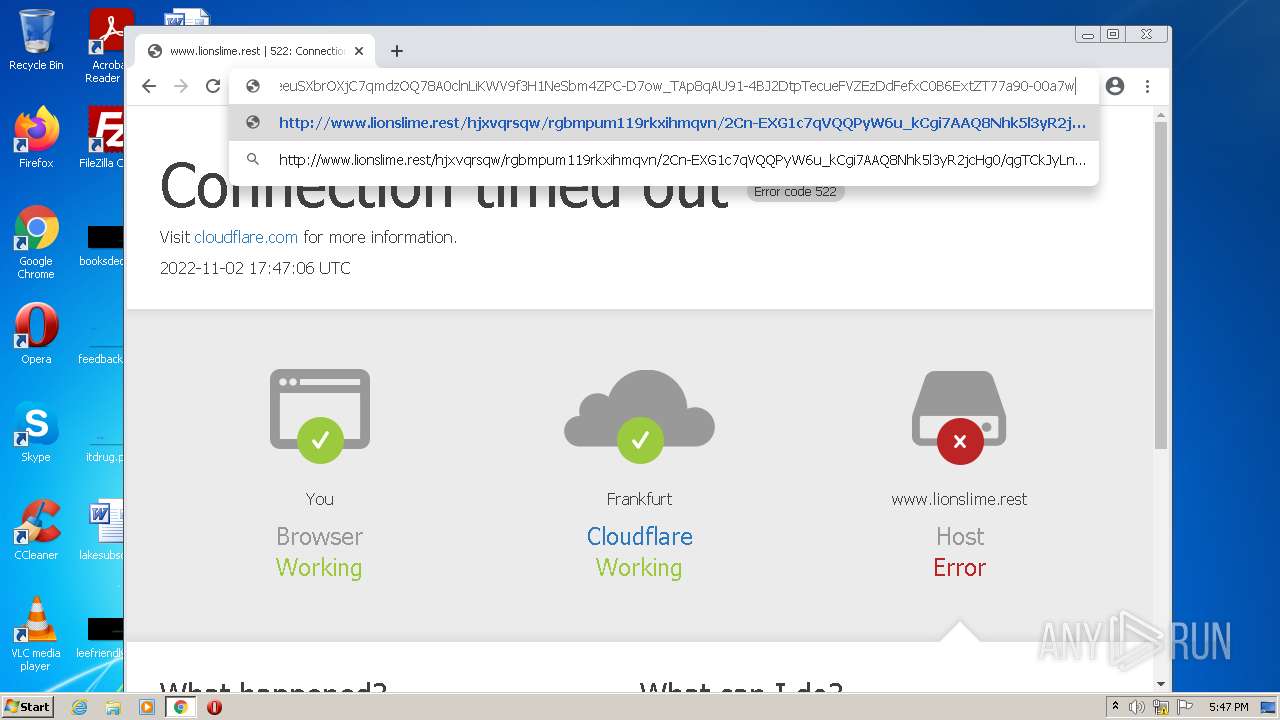
| URL: | http://www.lionslime.rest/hjxvqrsqw/rgbmpum119rkxihmqvn/2Cn-EXG1c7qVQQPyW6u_kCgi7AAQ8Nhk5l3yR2jcHg0/qgTCkJyLnm2yrYqYJbYnx6HcelvjyGF2KIlEejXnWtQc45OeeuSXbrOXjC7qmdzOQ78A0clnLiKWV9f3H1NeSbm4ZPC-D7ow_TAp8qAU91-4BJ2DtpTecueFVZEzDdFefxC0B6ExtZT77a90-00a7w |
| Full analysis: | https://app.any.run/tasks/996c4b13-55c8-4e5c-9cf8-f271213e53bb |
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2022, 17:45:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F1BA16981C5429AF2D29DBCD5A5C6264 |
| SHA1: | D18E0452174336884BB7E58F5EA91619BADBCB1F |
| SHA256: | 37691447D126A2C9618BEBD2CD09BC29B2302E603BC8CF41E6DABADC8B3196AA |
| SSDEEP: | 6:Cc4JZxCNXOrKXi70n6O1mXkxYjThKPaSTqUPf5VyEh:ETCFSai7o6OoXSQ0PaSbpVyEh |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Manual execution by user
- chrome.exe (PID: 3056)
Application launched itself
- iexplore.exe (PID: 2968)
- chrome.exe (PID: 3056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f40d988,0x6f40d998,0x6f40d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3296 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3280 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
12 960
Read events
12 736
Write events
221
Delete events
3
Modification events
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30994146 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30994146 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
144
Text files
133
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{323A2B0C-5AD6-11ED-9A81-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6362ACF2-BF0.pma | — | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3080DAA1157E6A10.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{44491ABA-5AD6-11ED-9A81-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{28C63839-5AD6-11ED-9A81-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
47
DNS requests
23
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
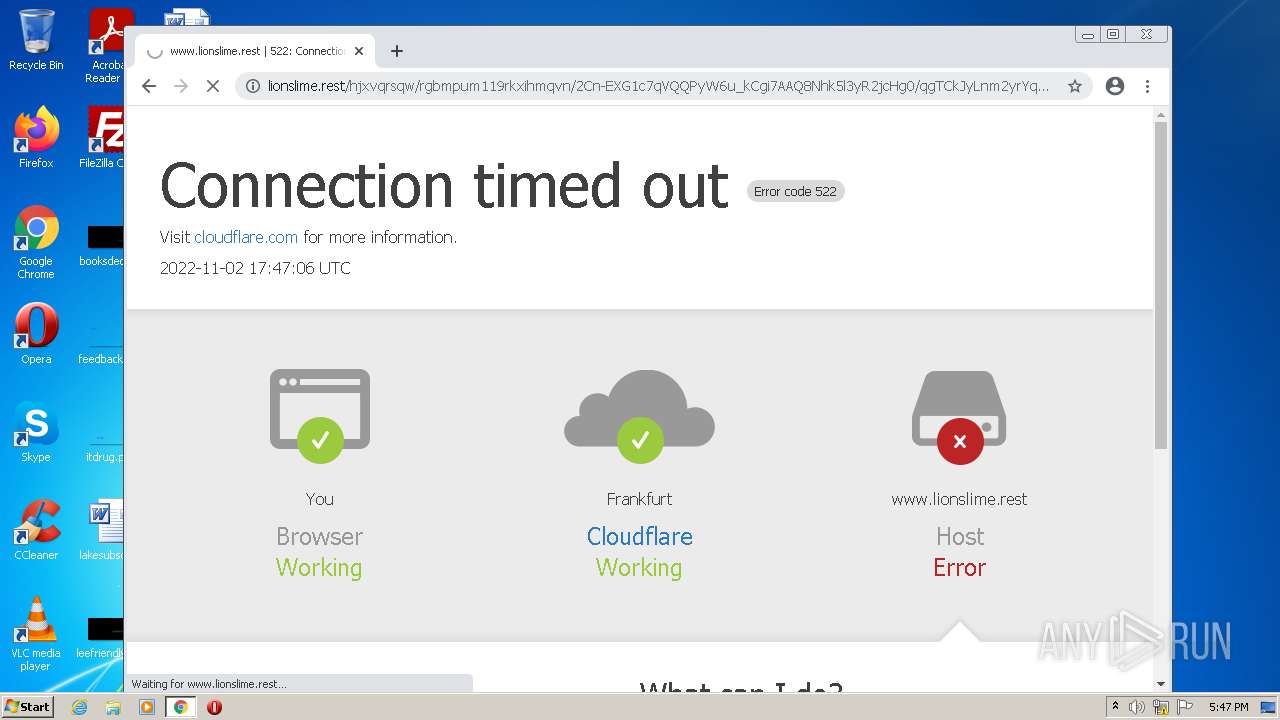
3396 | iexplore.exe | GET | — | 172.67.153.176:80 | http://www.lionslime.rest/hjxvqrsqw/rgbmpum119rkxihmqvn/2Cn-EXG1c7qVQQPyW6u_kCgi7AAQ8Nhk5l3yR2jcHg0/qgTCkJyLnm2yrYqYJbYnx6HcelvjyGF2KIlEejXnWtQc45OeeuSXbrOXjC7qmdzOQ78A0clnLiKWV9f3H1NeSbm4ZPC-D7ow_TAp8qAU91-4BJ2DtpTecueFVZEzDdFefxC0B6ExtZT77a90-00a7w | US | — | — | suspicious |
4060 | chrome.exe | GET | 522 | 172.67.153.176:80 | http://www.lionslime.rest/hjxvqrsqw/rgbmpum119rkxihmqvn/2Cn-EXG1c7qVQQPyW6u_kCgi7AAQ8Nhk5l3yR2jcHg0/qgTCkJyLnm2yrYqYJbYnx6HcelvjyGF2KIlEejXnWtQc45OeeuSXbrOXjC7qmdzOQ78A0clnLiKWV9f3H1NeSbm4ZPC-D7ow_TAp8qAU91-4BJ2DtpTecueFVZEzDdFefxC0B6ExtZT77a90-00a7w | US | html | 7.01 Kb | suspicious |
2968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
4060 | chrome.exe | GET | — | 172.67.153.176:80 | http://www.lionslime.rest/hjxvqrsqw/rgbmpum119rkxihmqvn/2Cn-EXG1c7qVQQPyW6u_kCgi7AAQ8Nhk5l3yR2jcHg0/qgTCkJyLnm2yrYqYJbYnx6HcelvjyGF2KIlEejXnWtQc45OeeuSXbrOXjC7qmdzOQ78A0clnLiKWV9f3H1NeSbm4ZPC-D7ow_TAp8qAU91-4BJ2DtpTecueFVZEzDdFefxC0B6ExtZT77a90-00a7w | US | — | — | suspicious |
2968 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9e1261ca3c431a52 | US | compressed | 4.70 Kb | whitelisted |
4060 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
4060 | chrome.exe | GET | 200 | 172.67.153.176:80 | http://www.lionslime.rest/cdn-cgi/styles/main.css | US | text | 2.13 Kb | suspicious |
4060 | chrome.exe | GET | 200 | 172.67.153.176:80 | http://www.lionslime.rest/cdn-cgi/images/cf-icon-ok.png | US | image | 946 b | suspicious |
4060 | chrome.exe | GET | 200 | 172.67.153.176:80 | http://www.lionslime.rest/cdn-cgi/images/cf-icon-error.png | US | image | 854 b | suspicious |
4060 | chrome.exe | GET | 200 | 172.67.153.176:80 | http://www.lionslime.rest/favicon.ico | US | image | 69 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3396 | iexplore.exe | 104.21.32.186:80 | www.lionslime.rest | CLOUDFLARENET | — | whitelisted |
2968 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2968 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3396 | iexplore.exe | 172.67.153.176:80 | www.lionslime.rest | CLOUDFLARENET | US | suspicious |
4060 | chrome.exe | 142.250.186.109:443 | accounts.google.com | GOOGLE | US | whitelisted |
2968 | iexplore.exe | 23.36.162.87:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
— | — | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
4060 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
4060 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
4060 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.lionslime.rest |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3396 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |
4060 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.rest Domain |