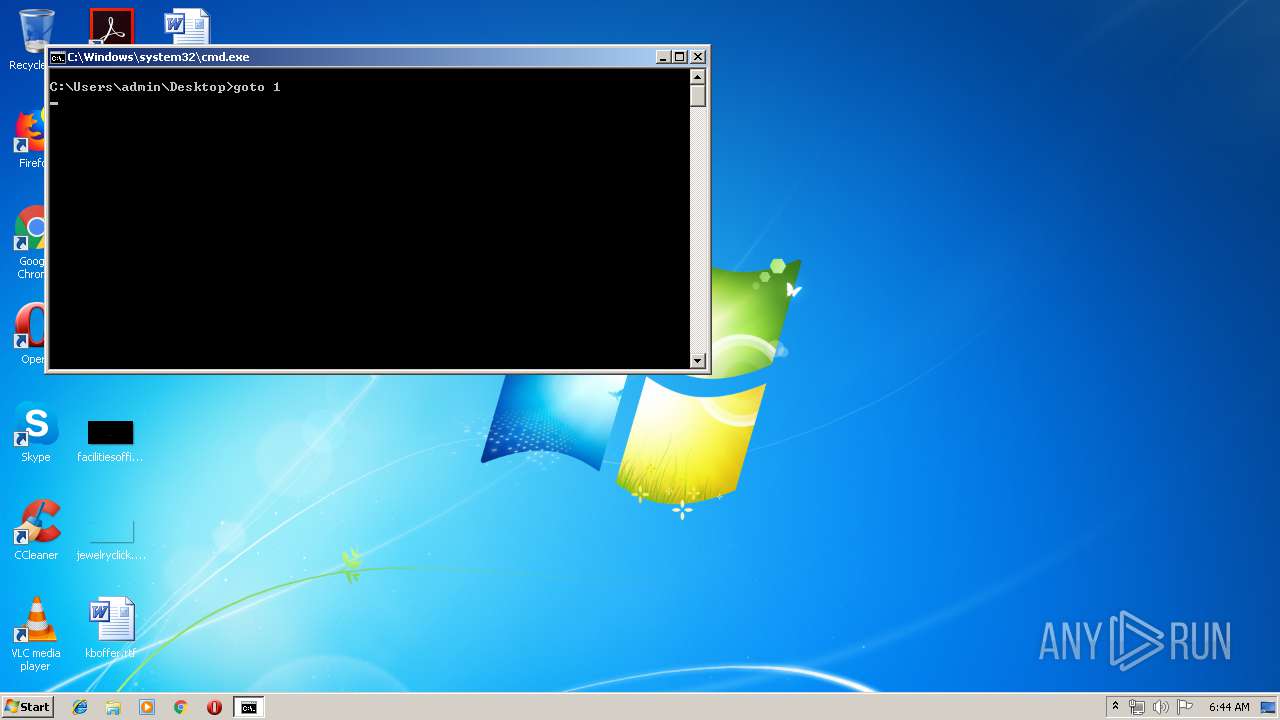
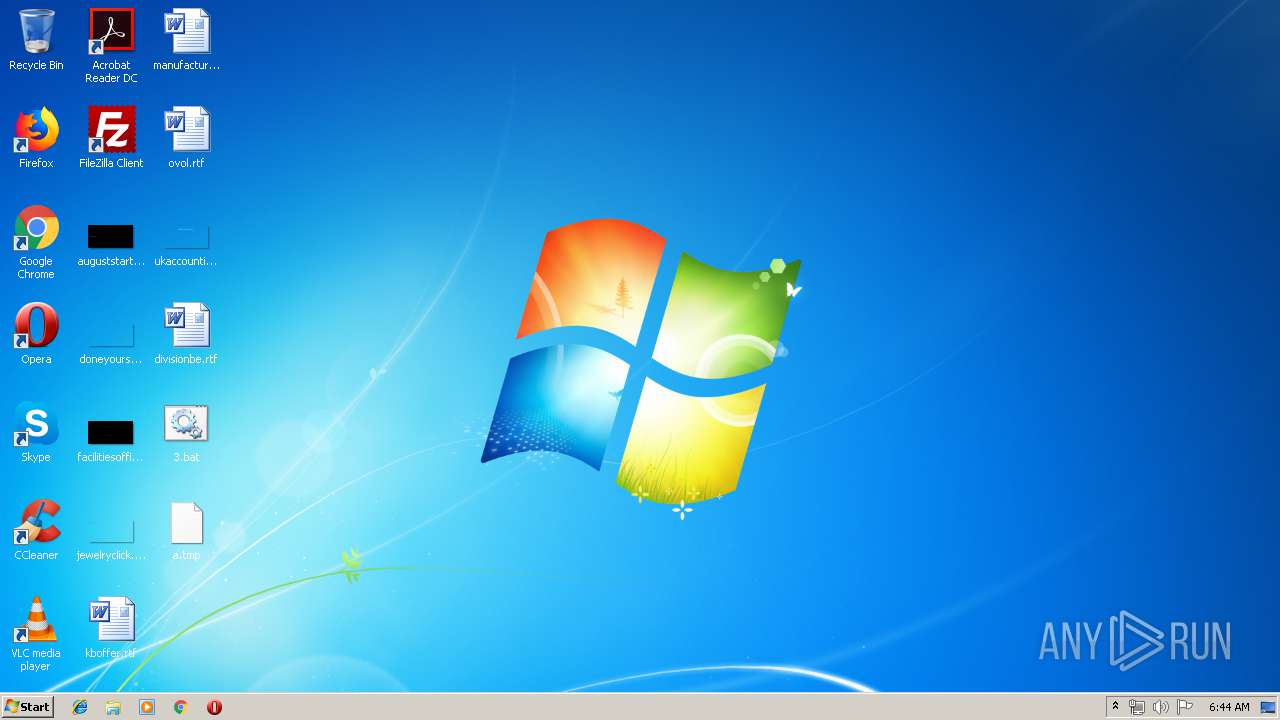
| File name: | 3.bat |
| Full analysis: | https://app.any.run/tasks/3352fb5f-2951-4e77-a2c6-381b41b800ed |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 05:43:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 35F4B666420956A2F0B890A349909037 |
| SHA1: | 8CB482CF4ABB9720C1ADAF80FD752A6D959E85B2 |
| SHA256: | 3768C2AFB2804DD3A795D8238A4CC2851AD56C99A03821C9FCD097235E5FEEC1 |
| SSDEEP: | 24:2YZLRyMtZF/6RK1f6uSXeGxs6uSXeGxQuDA1wY6XjN5SBllYHlV/W01RVp/UPA7o:L7y4qK9TweGaTweGOveCBHcf/BmpP9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3948)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3352)
- cmd.exe (PID: 2748)
Application launched itself
- cmd.exe (PID: 2748)
Executable content was dropped or overwritten
- cmd.exe (PID: 2748)
Starts application with an unusual extension
- cmd.exe (PID: 2748)
- cmd.exe (PID: 3948)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2104 | C:\Windows\system32\cmd.exe /c "dir /a/s/b/on *.exe *.jpg" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2128 | more +1 2.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Windows\System32\cmd.exe" /c 1.bat | C:\Windows\System32\cmd.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2840 | more +1 3.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | more +1 2.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | more +1 *.bat | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3312 | more +1 1.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3352 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\11.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3444 | more +1 2.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3512 | more +1 3.txt | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
133
Read events
125
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3352) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3352) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3948) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3948) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | cmd.exe | C:\Users\admin\Desktop\11.txt | — | |
MD5:— | SHA256:— | |||
| 2748 | cmd.exe | C:\Users\admin\Desktop\a.tmp | — | |
MD5:— | SHA256:— | |||
| 3948 | cmd.exe | C:\Users\admin\Desktop\a.tmp | text | |
MD5:— | SHA256:— | |||
| 2748 | cmd.exe | C:\Users\admin\Desktop\4.txt | text | |
MD5:— | SHA256:— | |||
| 2748 | cmd.exe | C:\Users\admin\Desktop\2.txt | text | |
MD5:— | SHA256:— | |||
| 2748 | cmd.exe | C:\Users\admin\Desktop\3.txt | text | |
MD5:— | SHA256:— | |||
| 3948 | cmd.exe | C:\Users\admin\Desktop\1.bat | text | |
MD5:— | SHA256:— | |||
| 3948 | cmd.exe | C:\Users\admin\Desktop\11.vbs | text | |
MD5:— | SHA256:— | |||
| 2748 | cmd.exe | C:\Users\admin\Desktop\1.txt | text | |
MD5:— | SHA256:— | |||
| 2748 | cmd.exe | C:\Users\admin\Desktop\Rar.exe | executable | |
MD5:FD5EFD73394BA1B411C356FA849BF3F1 | SHA256:8014C516D154A6E17FDF3C40806B775F75B21E18E4047BF1D898A072EE4E3311 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report