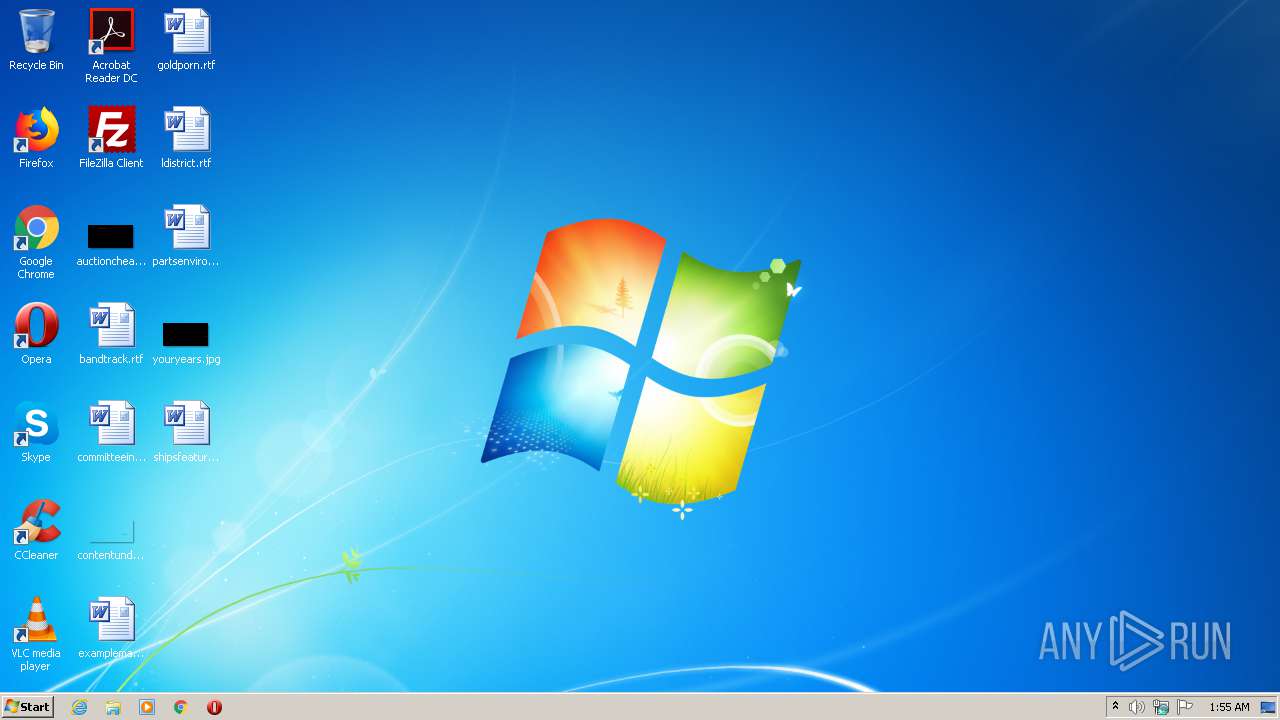
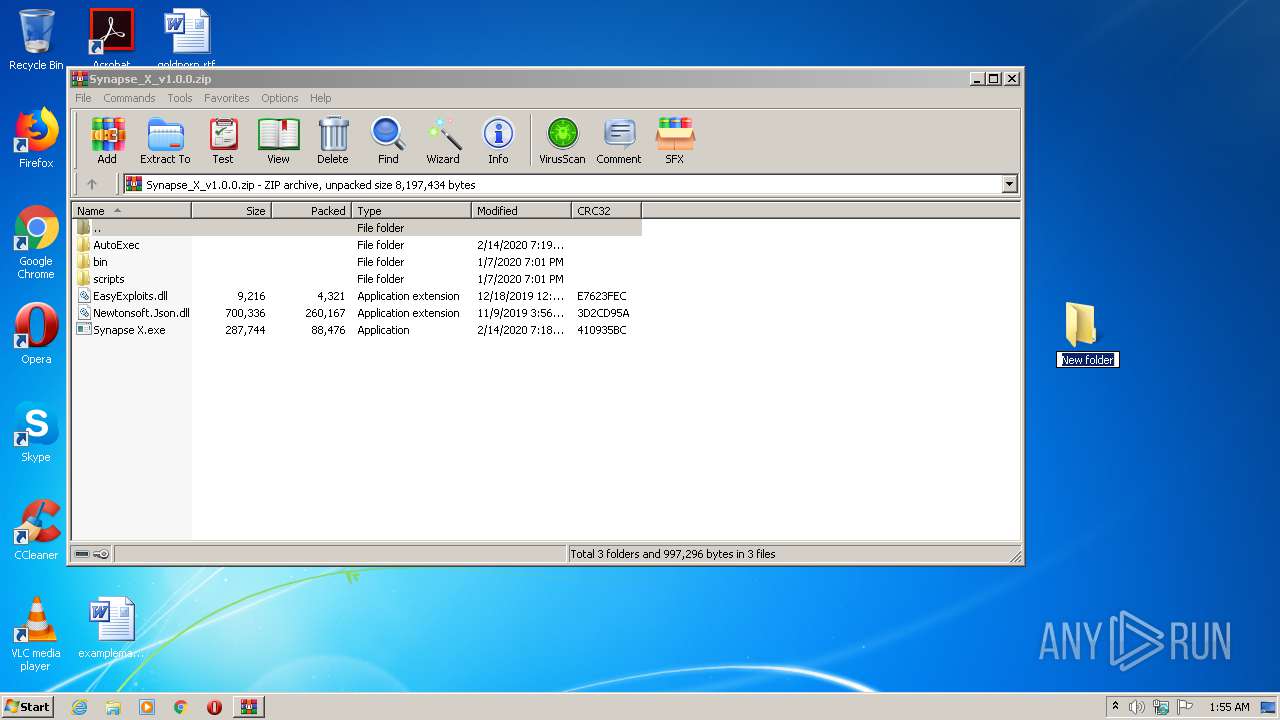
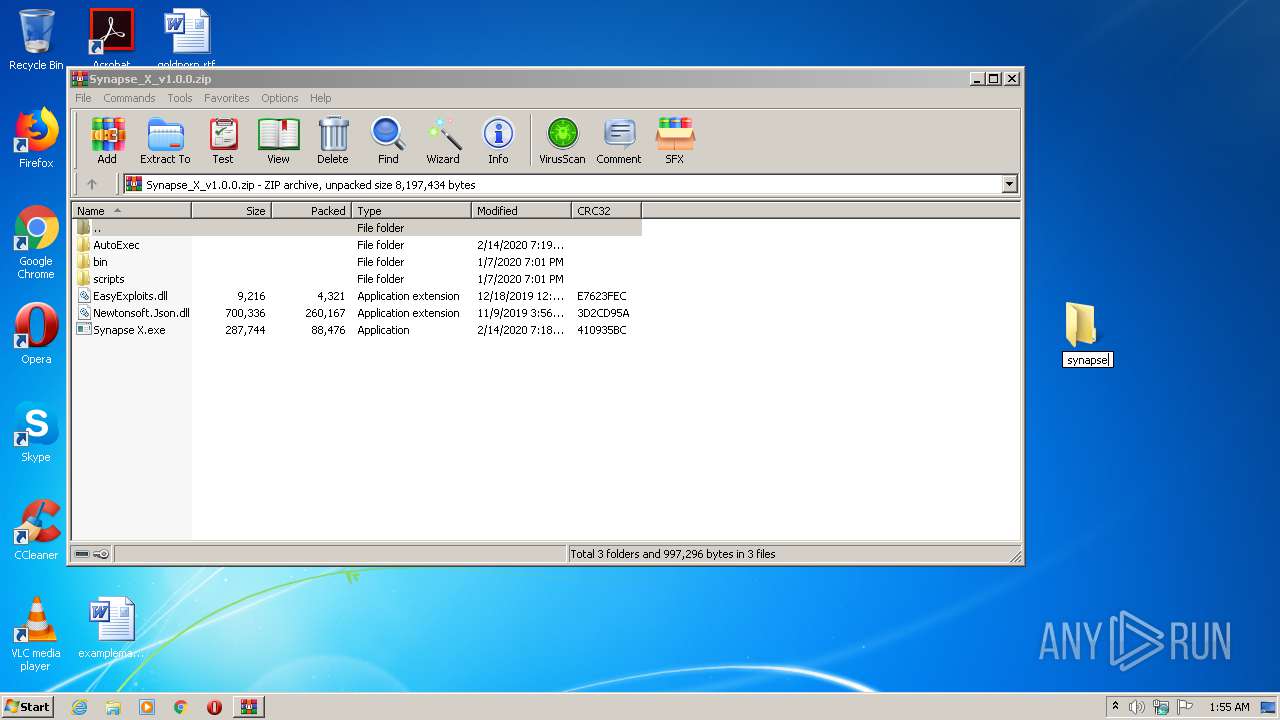
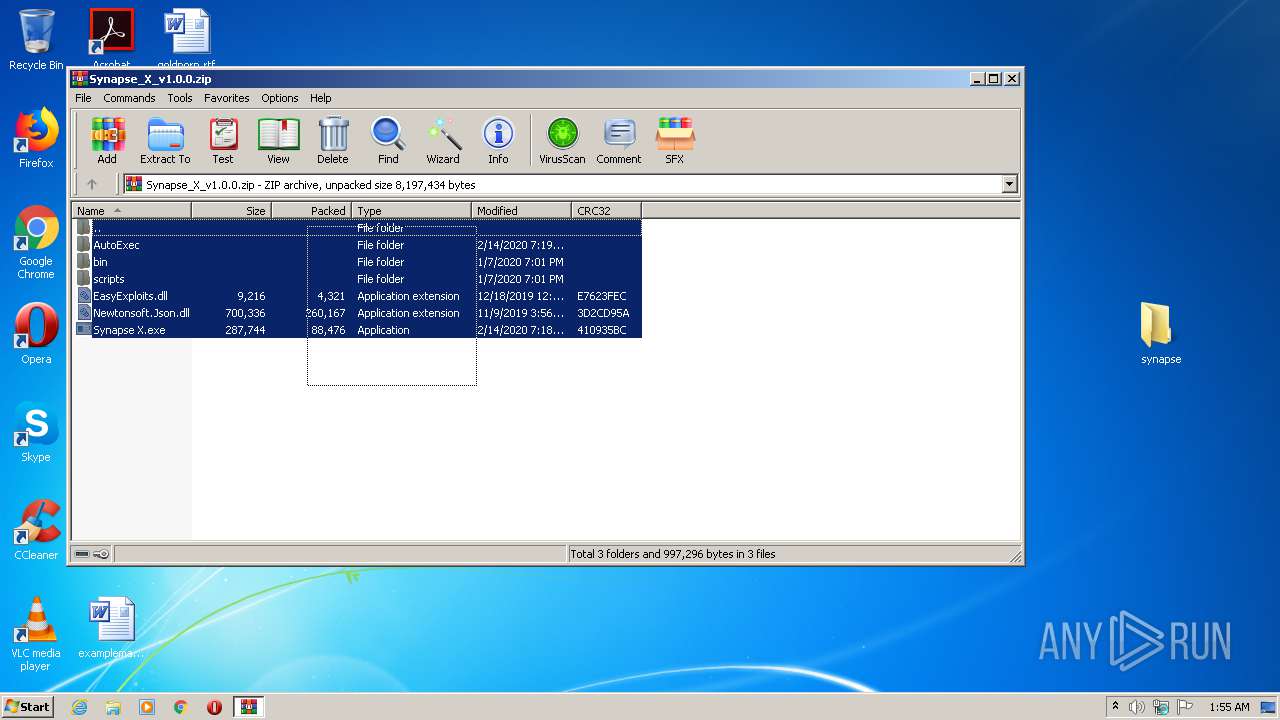
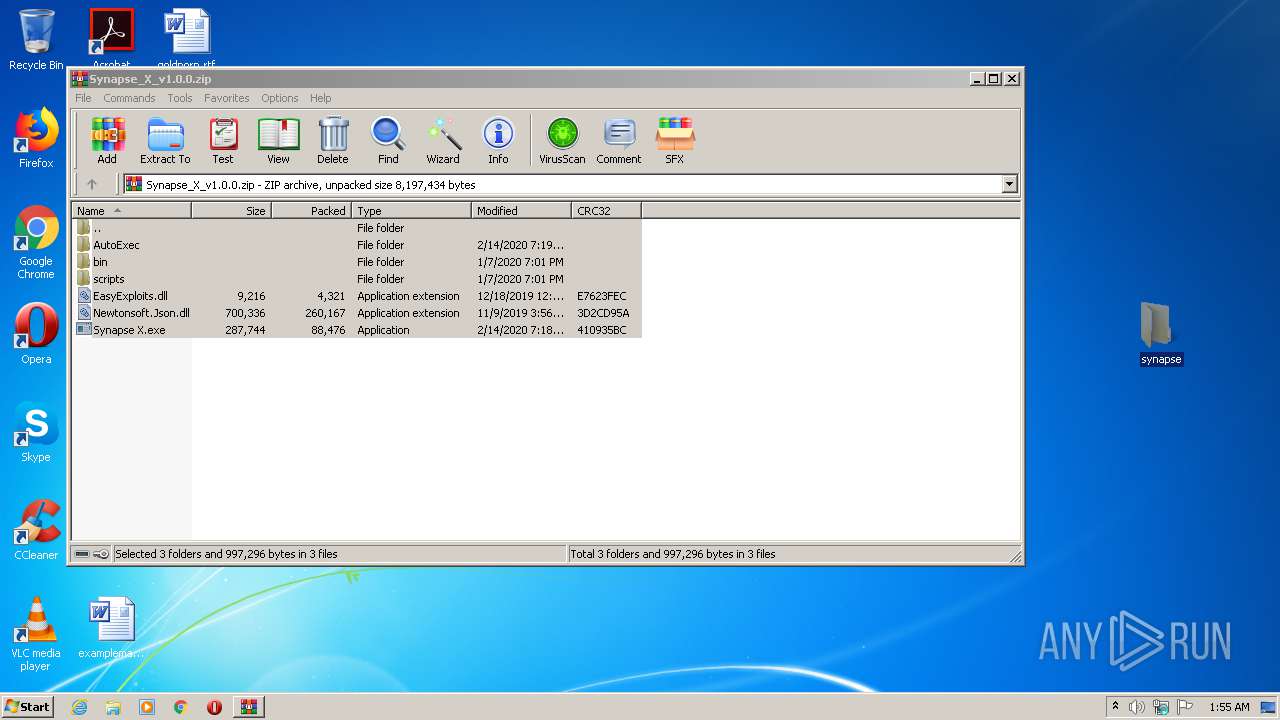
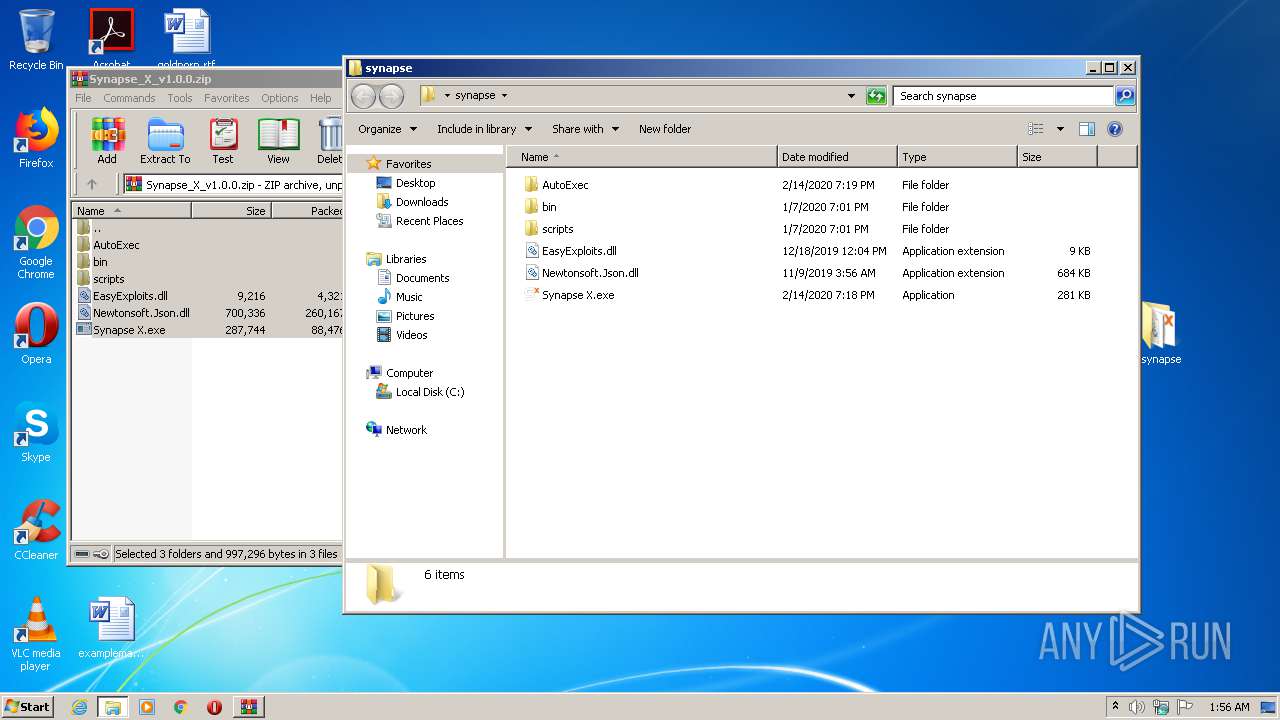
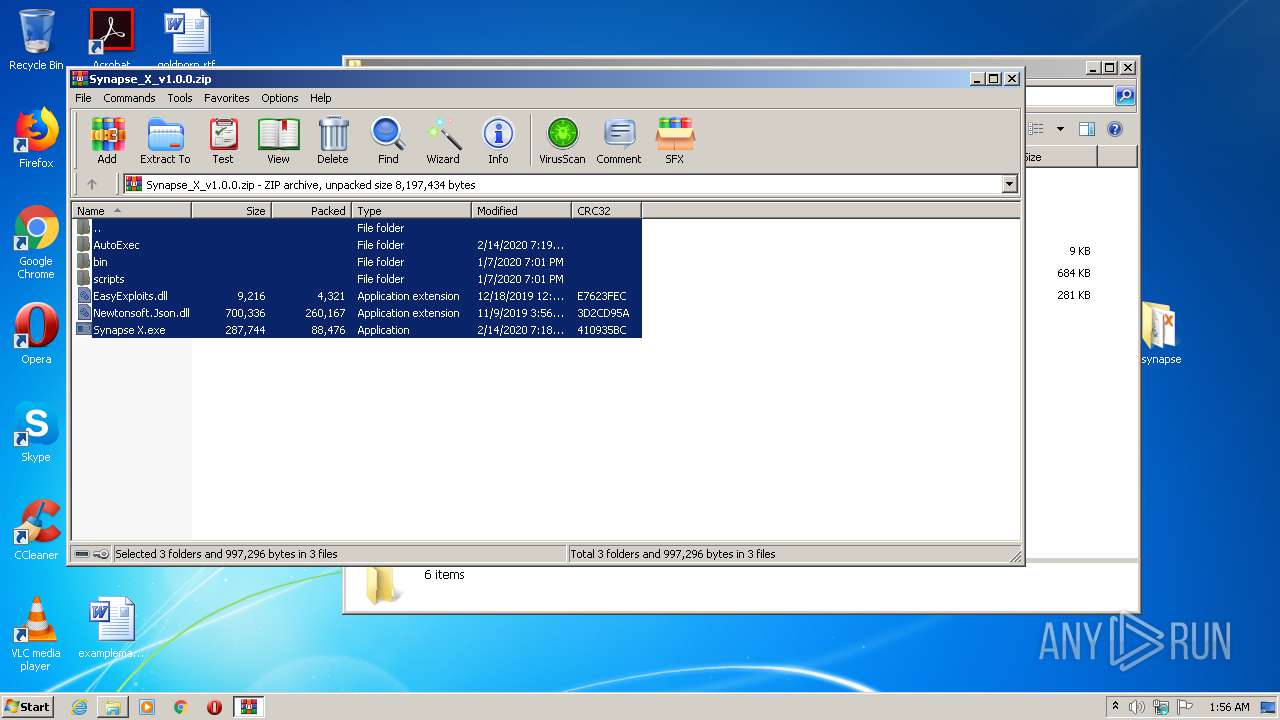
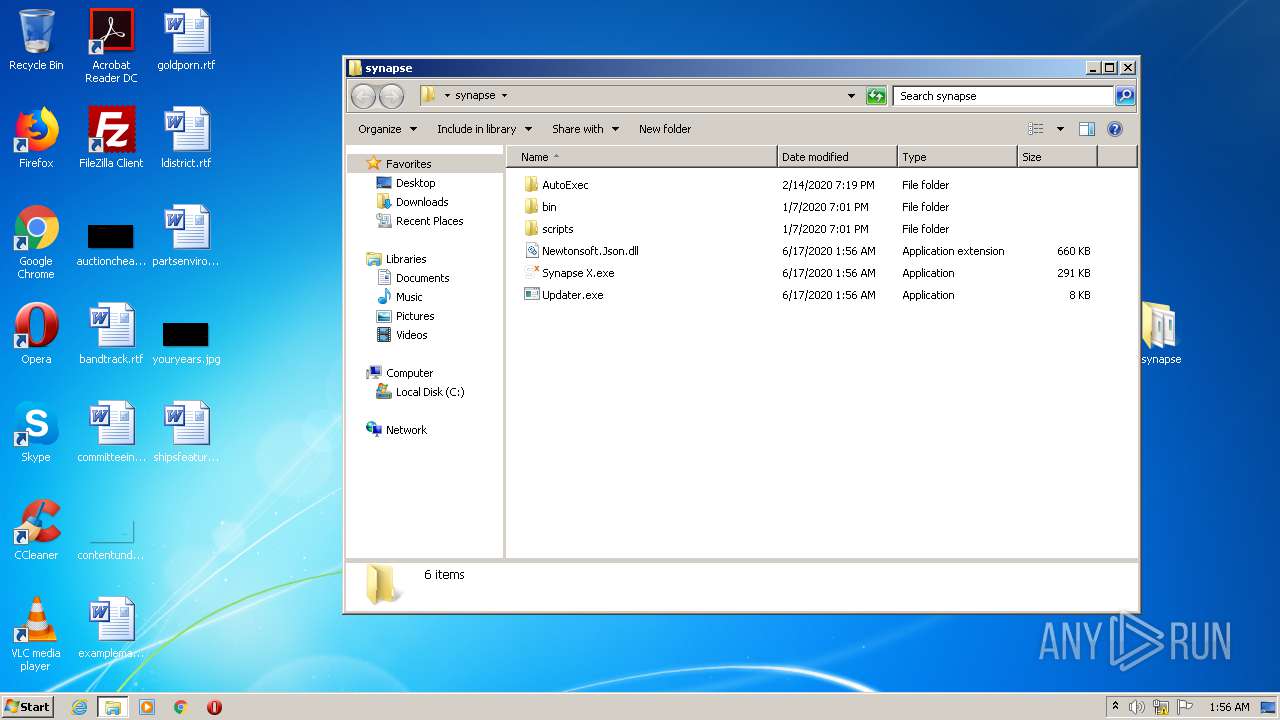
| download: | Synapse_X_v1.0.0.zip |
| Full analysis: | https://app.any.run/tasks/fddd9eec-8101-4718-9f3a-adcac8c6c907 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2020, 00:55:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CD4615BD3B7F479B1235E8694F4296D8 |
| SHA1: | 748E81099C714522A99E1E733514FEFC75F60098 |
| SHA256: | 375D5E7BDA3A968719D43172BC8E6A5CECB8E30D56A68081586DE1F4D759FBD3 |
| SSDEEP: | 49152:vtRE8SSiHU3n4aa5GkiyImT69JmdxMcecfL:lRE5SXn4aa+FmT69JmqcfL |
MALICIOUS
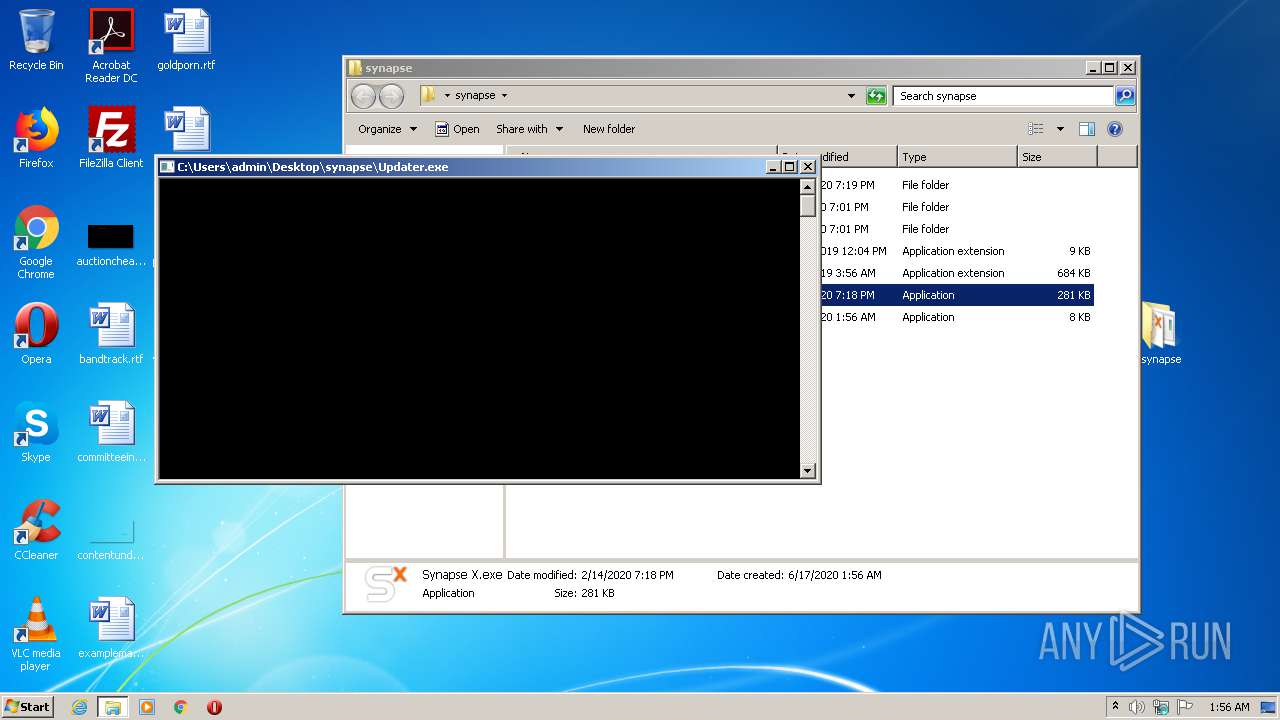
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3536)
Application was dropped or rewritten from another process
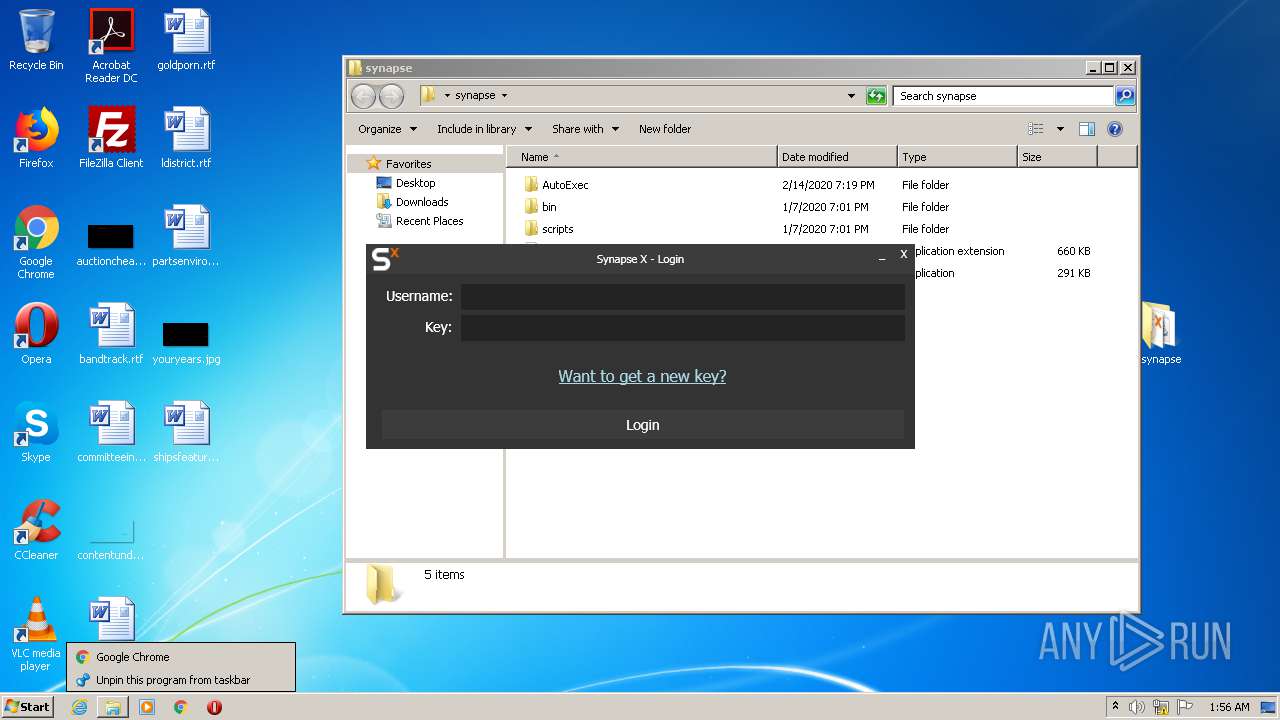
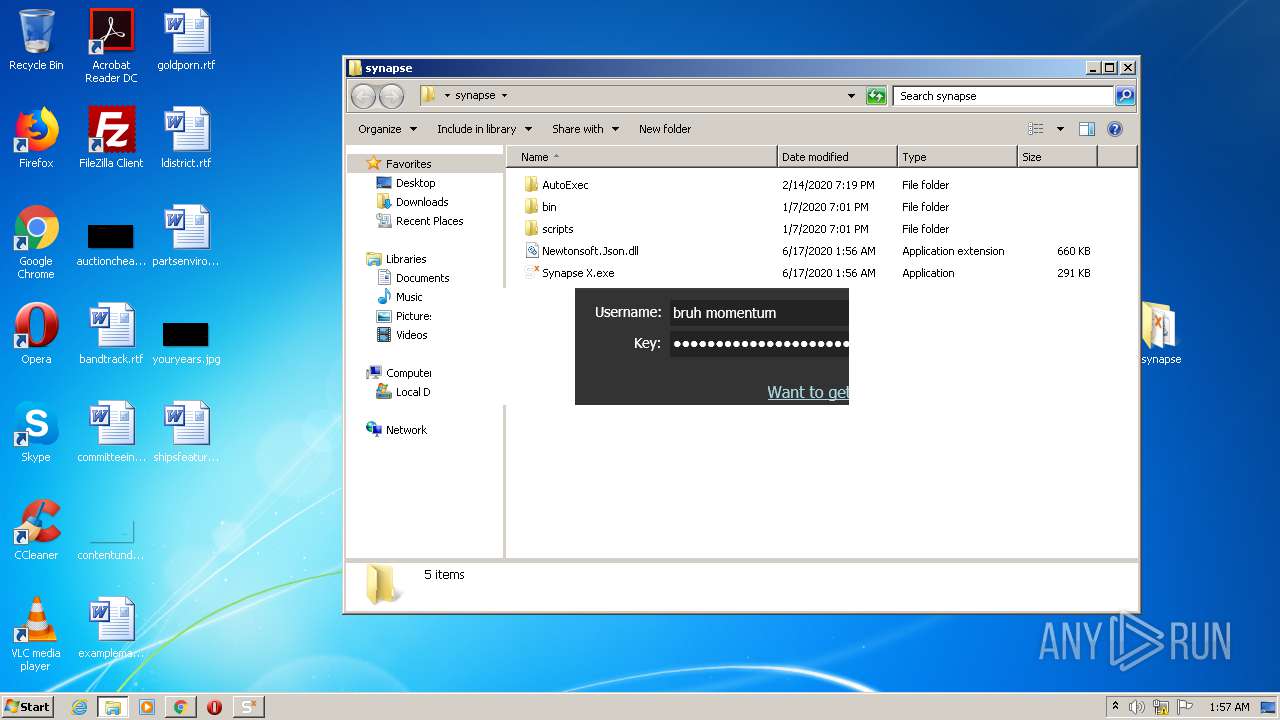
- Synapse X.exe (PID: 2724)
- Updater.exe (PID: 2452)
- Synapse X.exe (PID: 2288)
SUSPICIOUS
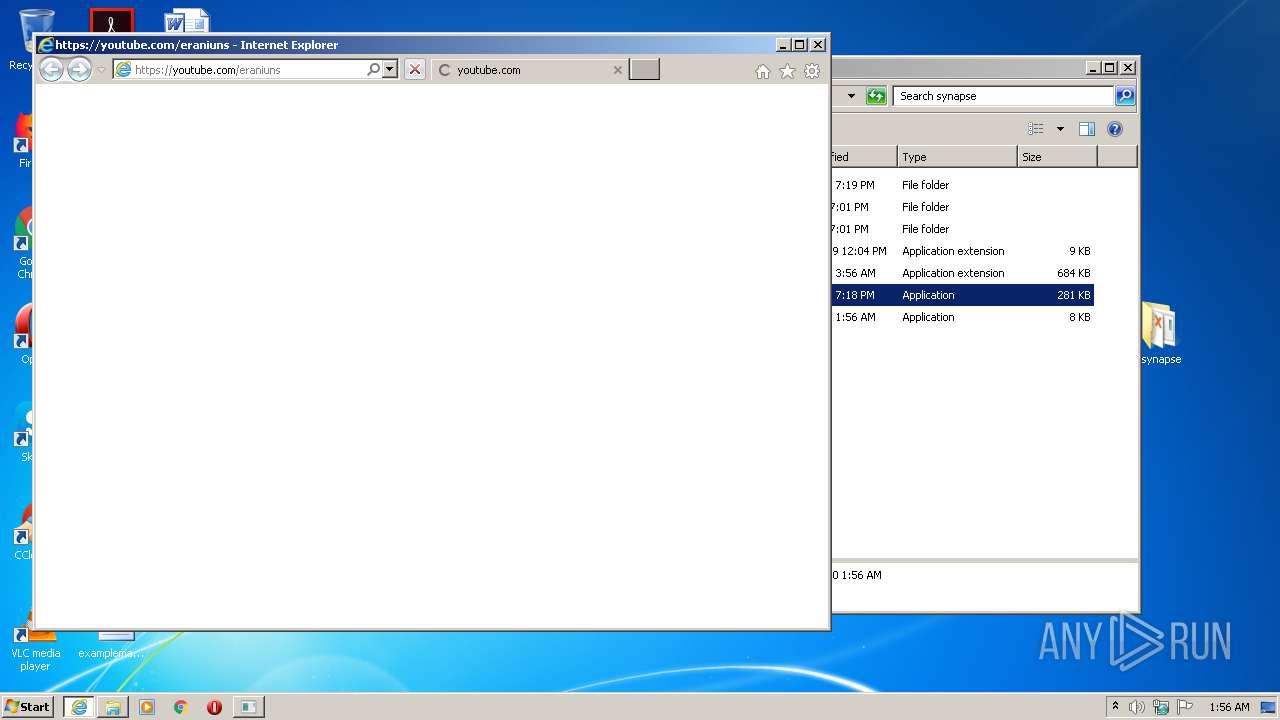
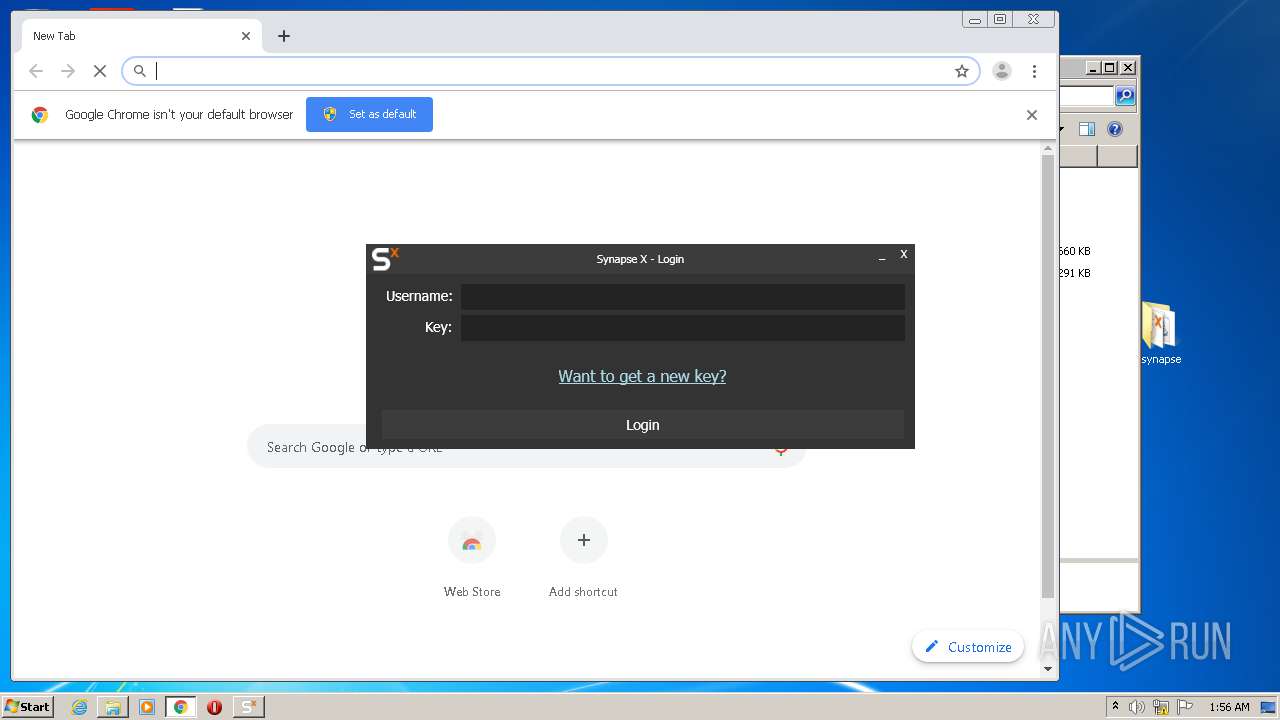
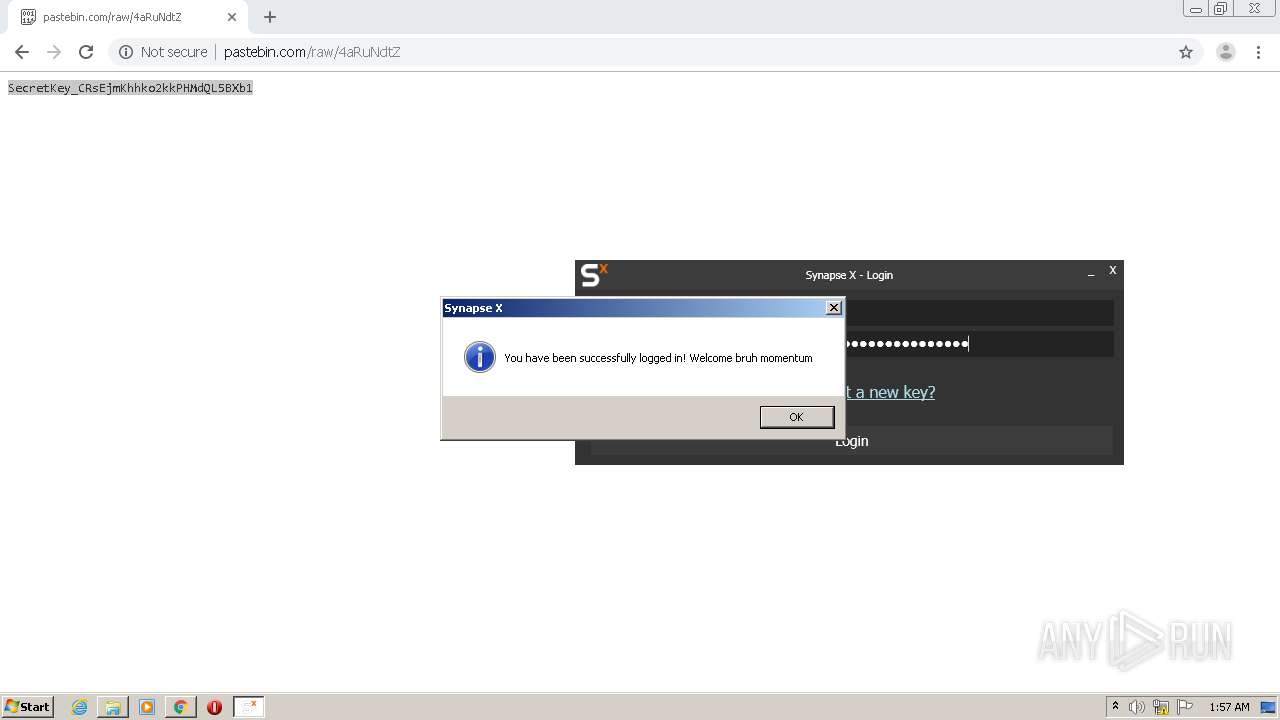
Starts Internet Explorer
- Synapse X.exe (PID: 2724)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 984)
- Synapse X.exe (PID: 2724)
- Updater.exe (PID: 2452)
Reads Environment values
- Synapse X.exe (PID: 2724)
- Synapse X.exe (PID: 2288)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2332)
Changes IE settings (feature browser emulation)
- Synapse X.exe (PID: 2288)
Reads Internet Cache Settings
- Synapse X.exe (PID: 2288)
Reads internet explorer settings
- Synapse X.exe (PID: 2288)
INFO
Manual execution by user
- Synapse X.exe (PID: 2724)
- chrome.exe (PID: 2332)
- notepad.exe (PID: 2716)
Creates files in the user directory
- iexplore.exe (PID: 1440)
Reads internet explorer settings
- iexplore.exe (PID: 1440)
Reads Internet Cache Settings
- iexplore.exe (PID: 464)
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 1440)
Application launched itself
- iexplore.exe (PID: 464)
- chrome.exe (PID: 2332)
Changes internet zones settings
- iexplore.exe (PID: 464)
Reads settings of System Certificates
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 1440)
- chrome.exe (PID: 944)
- iexplore.exe (PID: 464)
Reads the hosts file
- chrome.exe (PID: 2332)
- chrome.exe (PID: 944)
Changes settings of System certificates
- iexplore.exe (PID: 464)
Adds / modifies Windows certificates
- iexplore.exe (PID: 464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
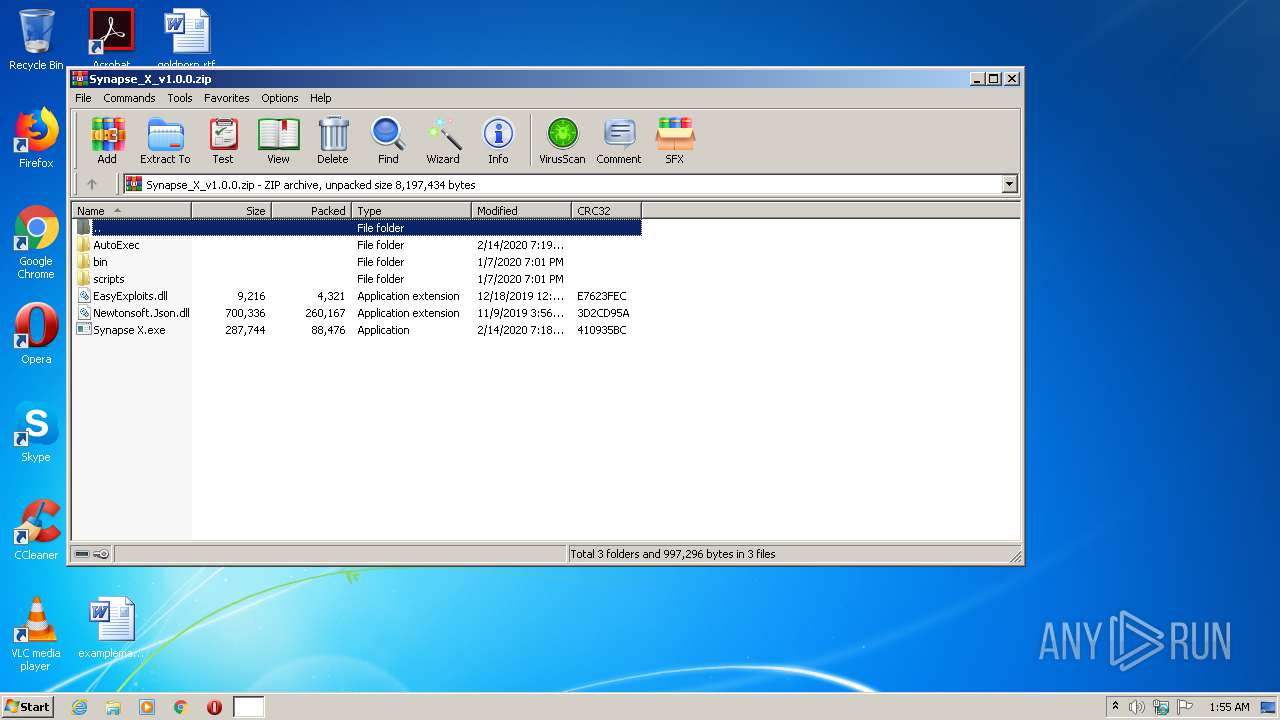
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:02:14 16:18:17 |
| ZipCRC: | 0x410935bc |
| ZipCompressedSize: | 88476 |
| ZipUncompressedSize: | 287744 |
| ZipFileName: | Synapse X.exe |
Total processes
82
Monitored processes
41
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9713750318364454944,12687892654816160482,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3900678815866496915 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,9713750318364454944,12687892654816160482,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2260255017996183929 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 464 | "C:\Program Files\Internet Explorer\iexplore.exe" https://youtube.com/eraniuns | C:\Program Files\Internet Explorer\iexplore.exe | Synapse X.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9713750318364454944,12687892654816160482,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9028269646964300614 --mojo-platform-channel-handle=1644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Synapse_X_v1.0.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9713750318364454944,12687892654816160482,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13359679394589700250 --mojo-platform-channel-handle=3728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:464 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,9713750318364454944,12687892654816160482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13371058911935612086 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2340 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,9713750318364454944,12687892654816160482,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2154703563204872075 --mojo-platform-channel-handle=2084 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 415
Read events
2 995
Write events
3 693
Delete events
1 727
Modification events
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Synapse_X_v1.0.0.zip | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3536) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
5
Suspicious files
59
Text files
277
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\Auth.ini | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\Monaco.html | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\base\worker\workerMain.js | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\basic-languages\lua\lua.js | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\editor\contrib\suggest\media\String_16x.svg | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\editor\contrib\suggest\media\String_inverse_16x.svg | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\editor\editor.main.css | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\editor\editor.main.js | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\editor\editor.main.nls.de.js | — | |
MD5:— | SHA256:— | |||
| 984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa984.18672\bin\vs\editor\editor.main.nls.es.js | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
75
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
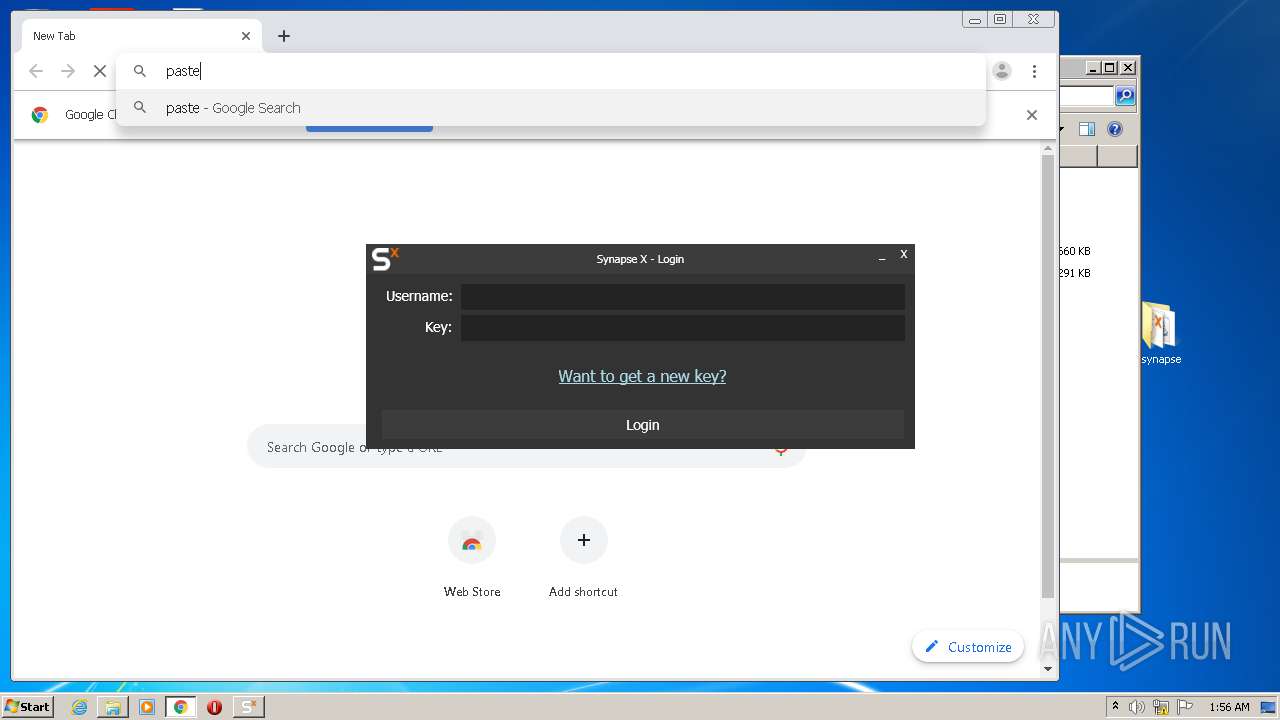
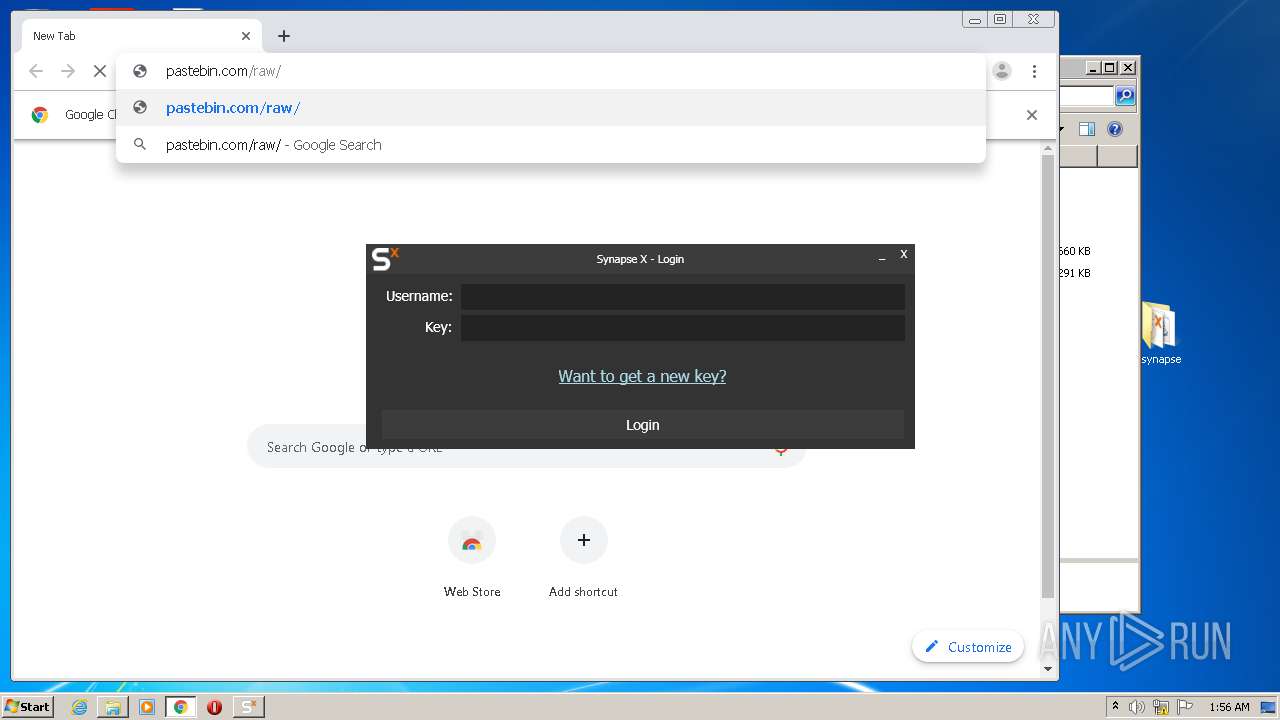
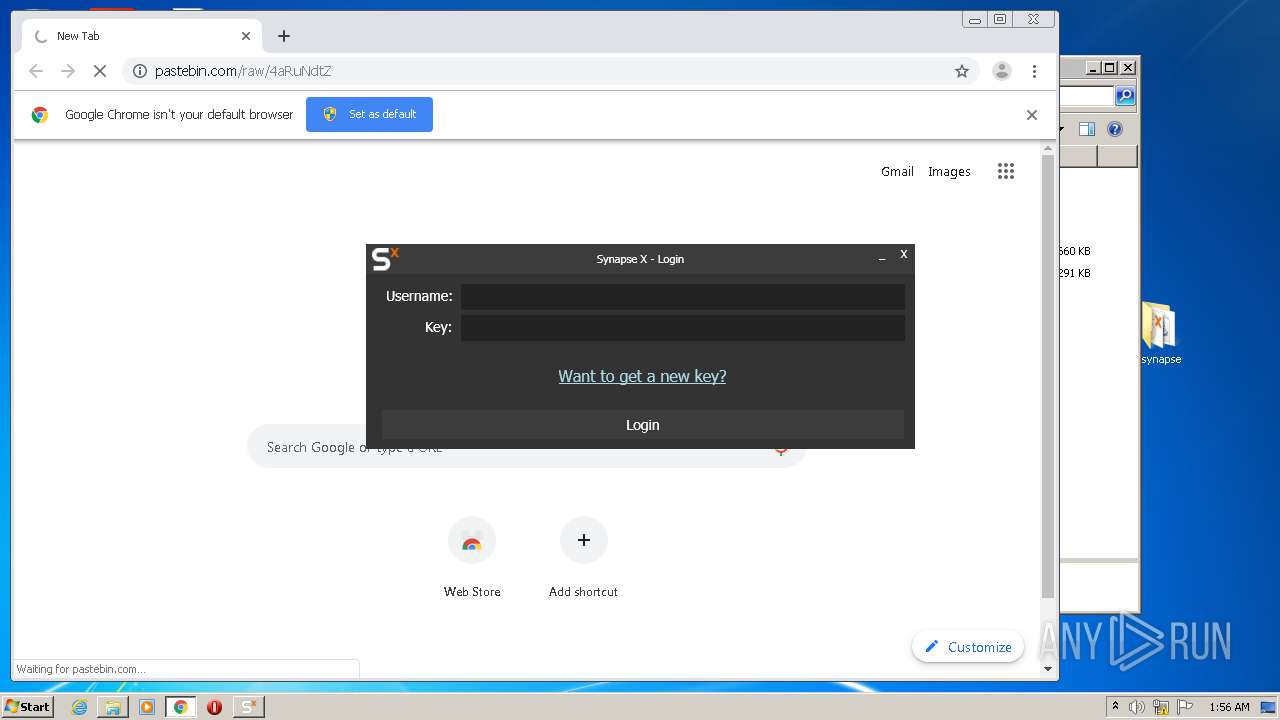
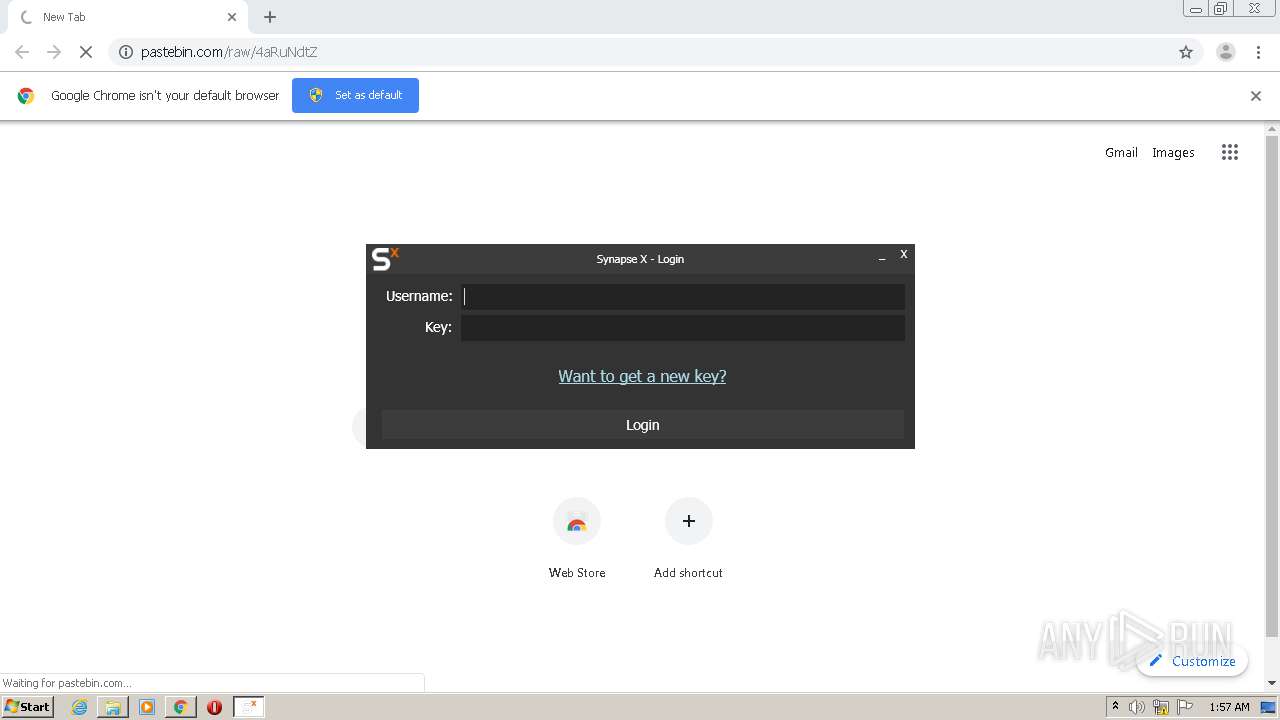
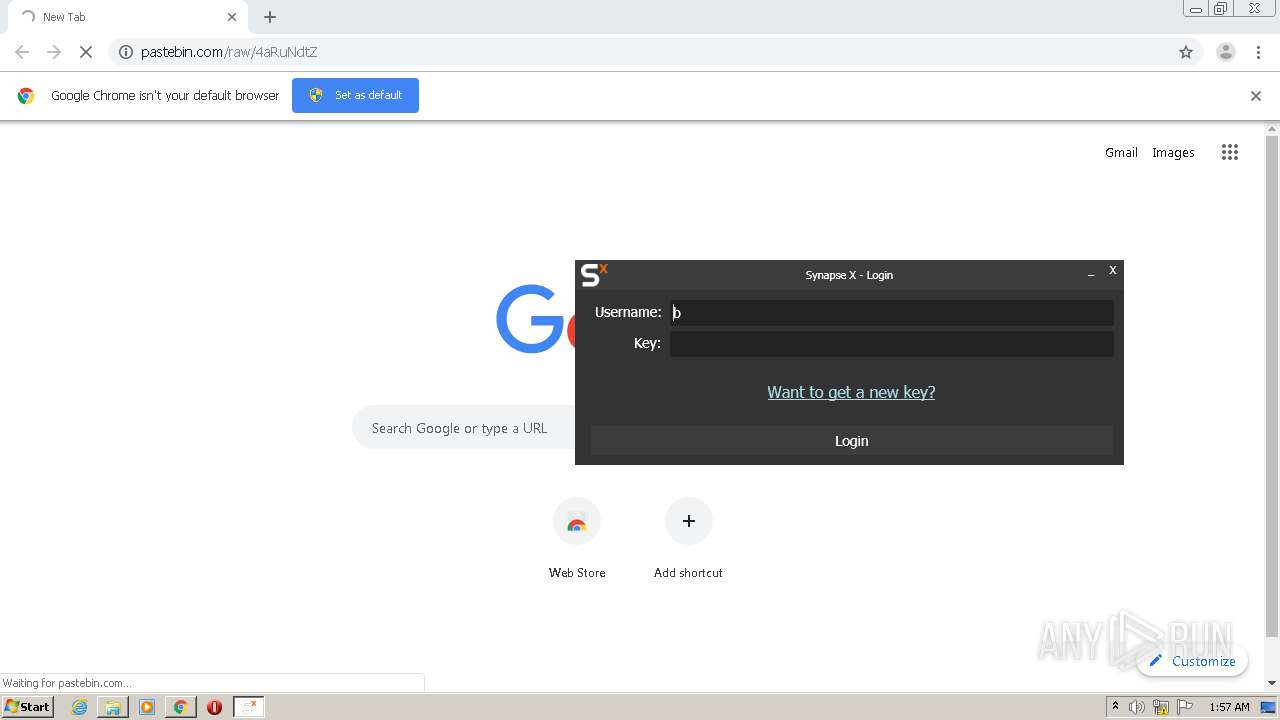
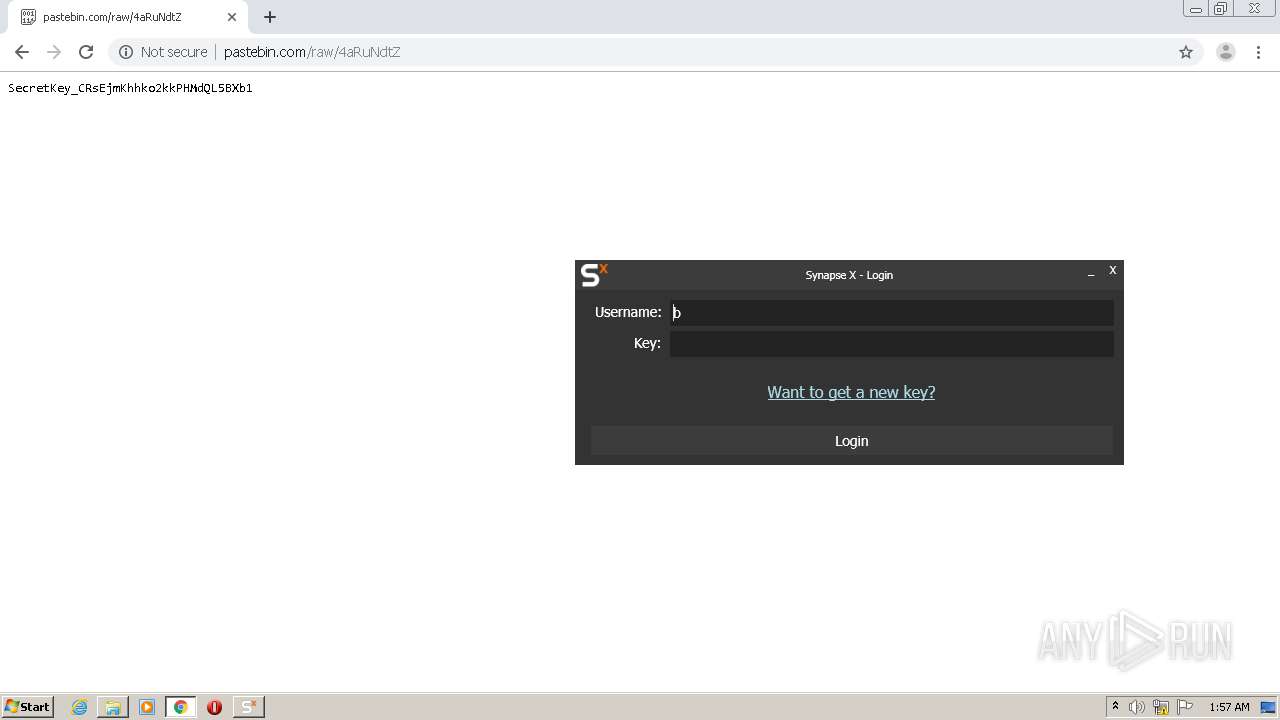
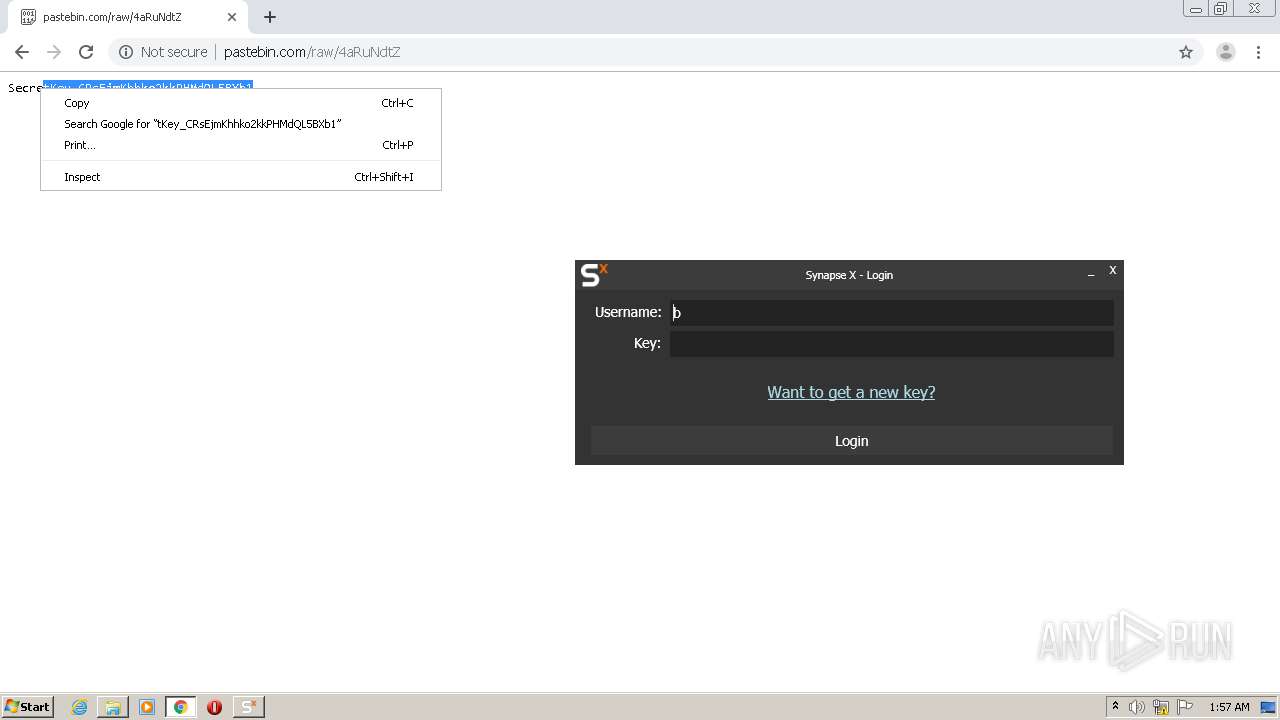
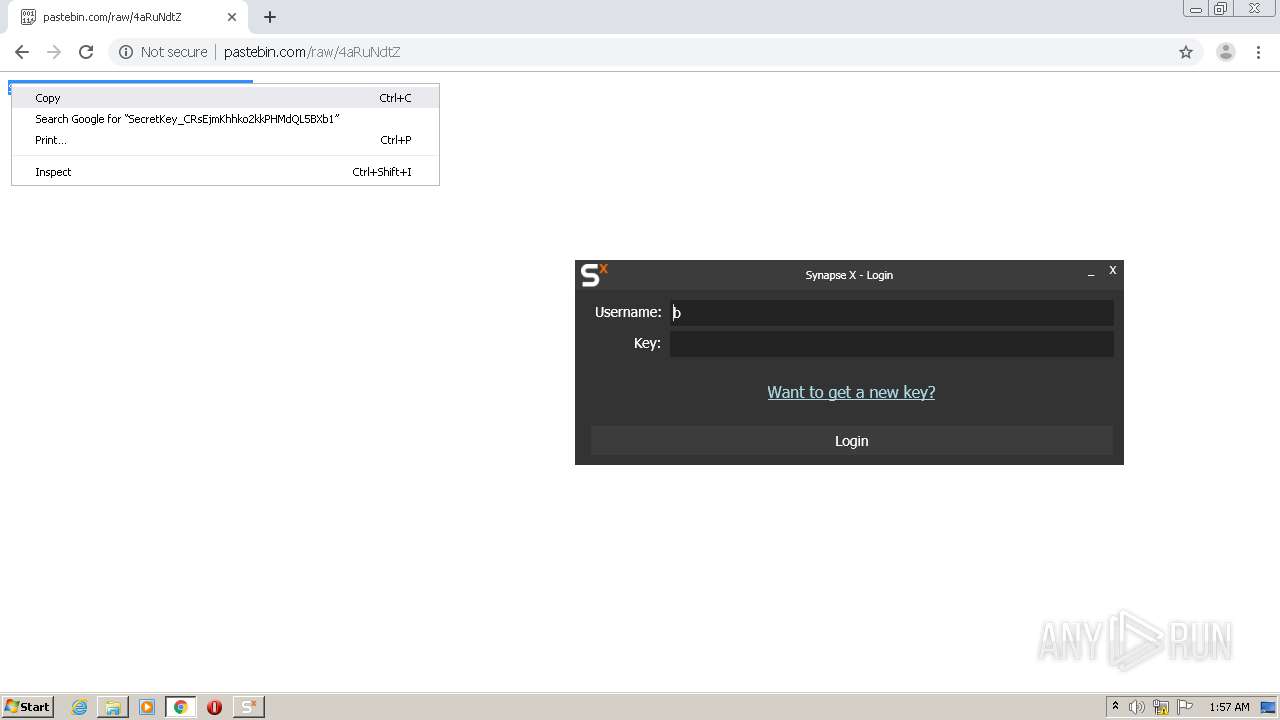
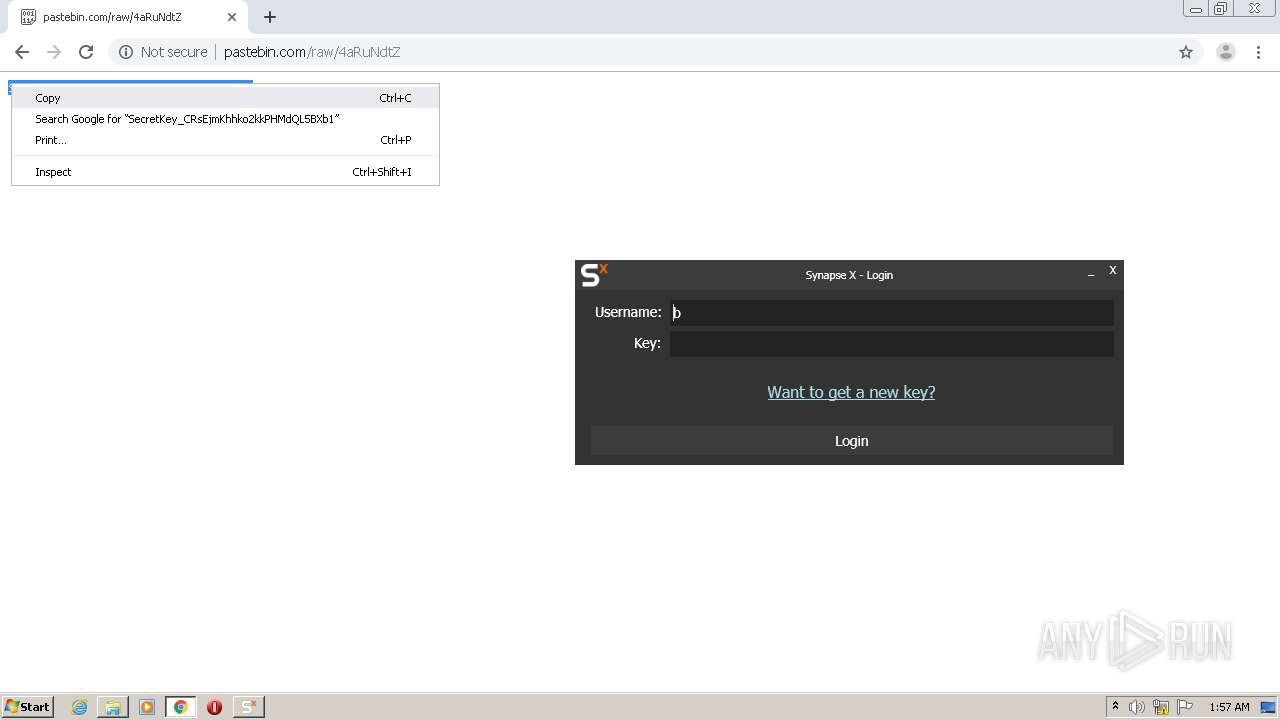
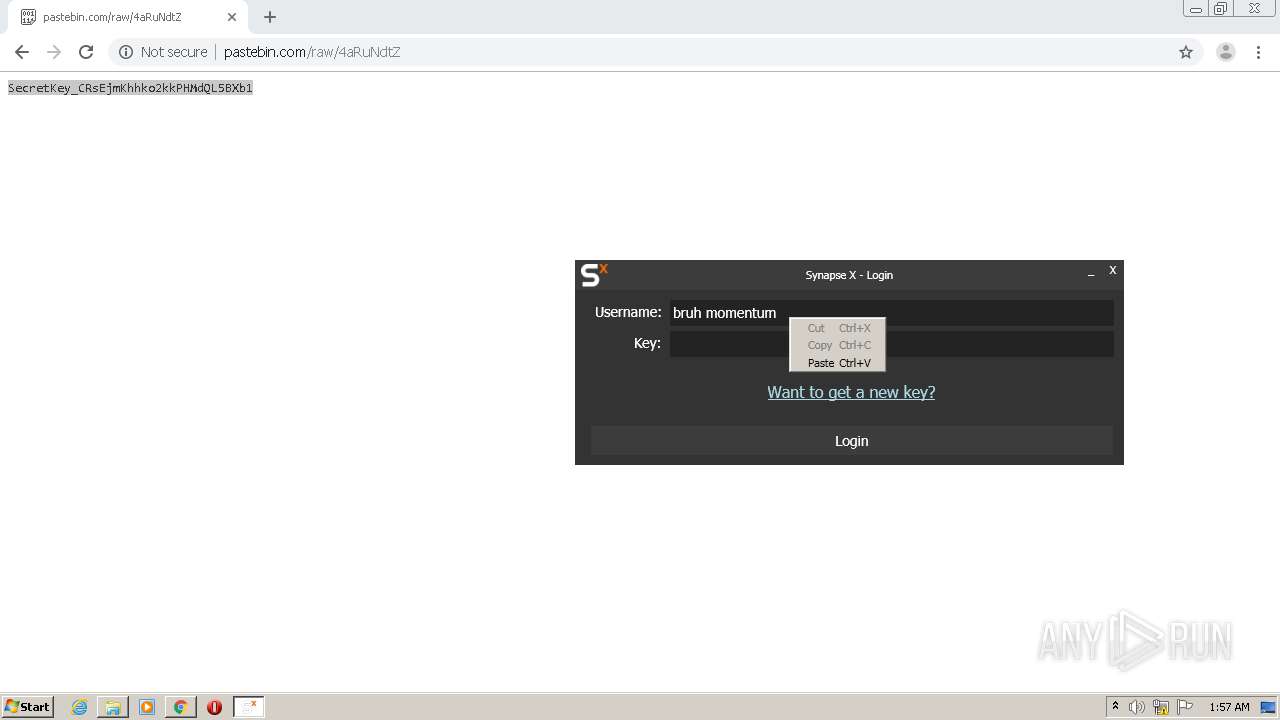
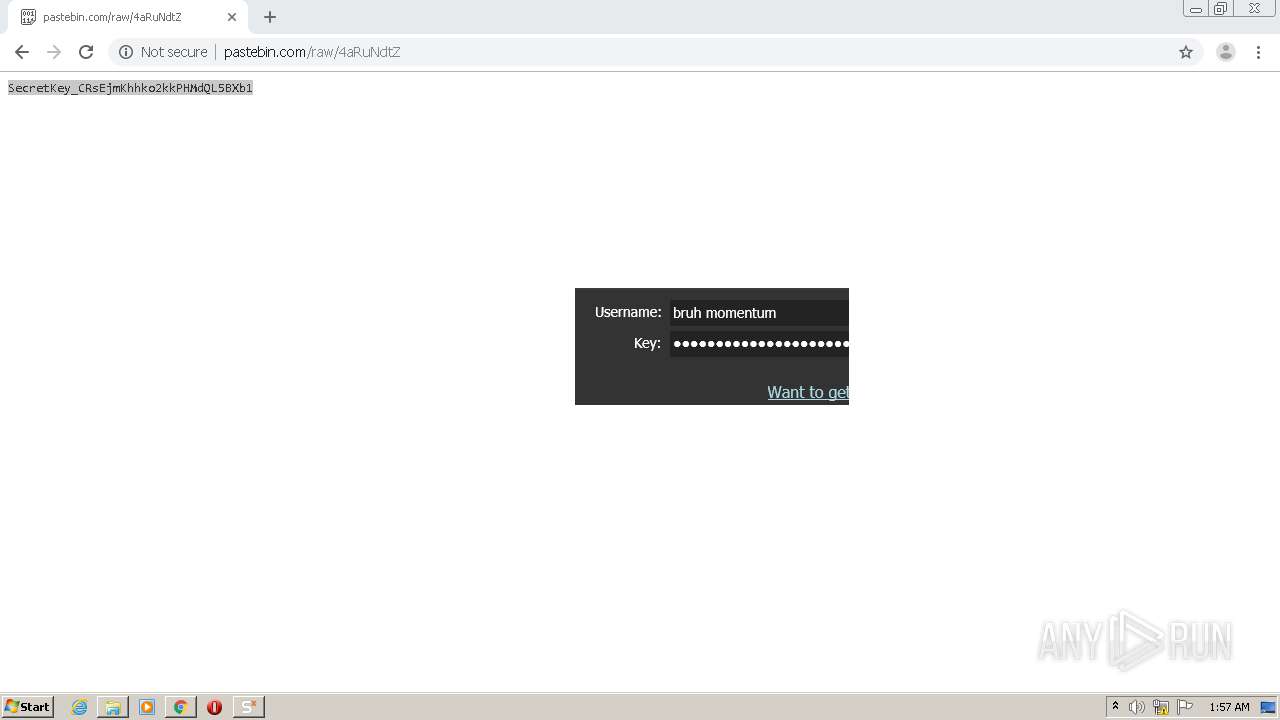
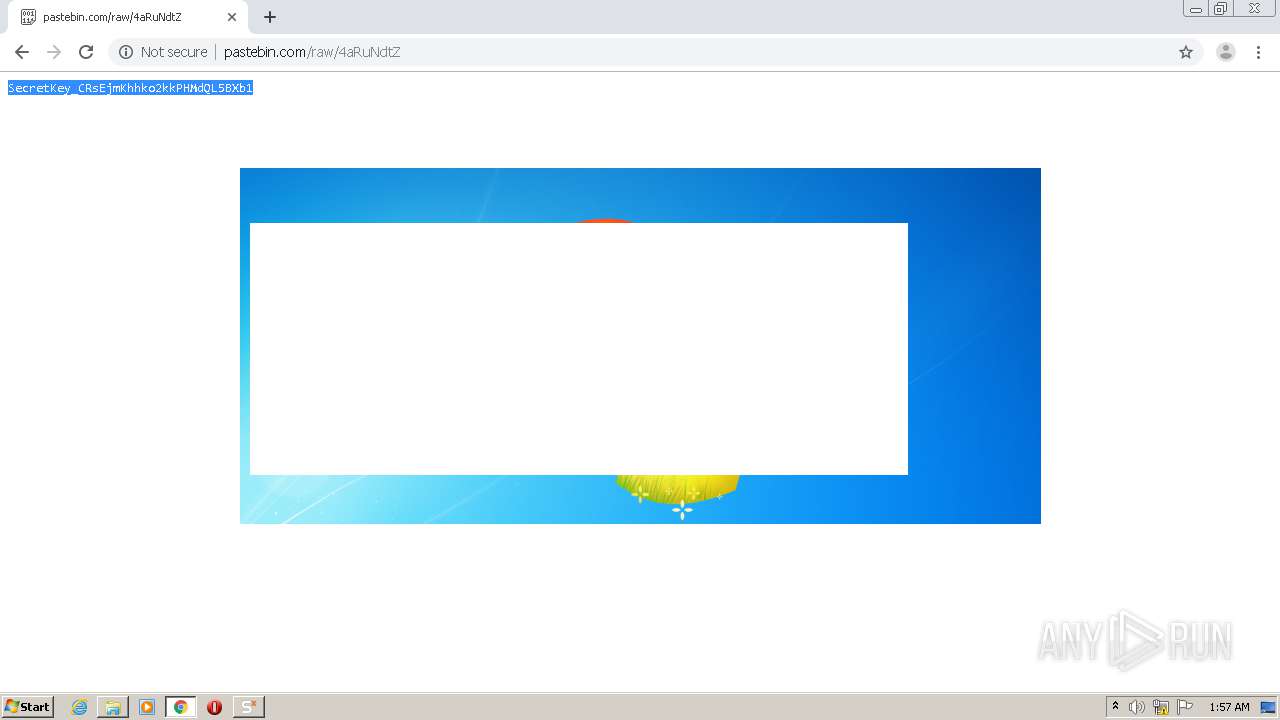
944 | chrome.exe | GET | — | 104.23.98.190:80 | http://pastebin.com/raw/4aRuNdtZ | US | — | — | malicious |
1440 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCNgpgQKfOGwAgAAAAAQ1Td | US | der | 472 b | whitelisted |
1440 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCNgpgQKfOGwAgAAAAAQ1Td | US | der | 472 b | whitelisted |
1440 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCNgpgQKfOGwAgAAAAAQ1Td | US | der | 472 b | whitelisted |
1440 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFb63M0OvvAcCAAAAABDVec%3D | US | der | 471 b | whitelisted |
464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1440 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDYtsl5jxUVpgIAAAAAayEm | US | der | 472 b | whitelisted |
944 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
944 | chrome.exe | GET | 200 | 209.85.226.73:80 | http://r4---sn-5hnekn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.128.27.133&mm=28&mn=sn-5hnekn7k&ms=nvh&mt=1592355313&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1440 | iexplore.exe | 172.217.18.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
1440 | iexplore.exe | 172.217.16.129:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
2724 | Synapse X.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
2724 | Synapse X.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2452 | Updater.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
1440 | iexplore.exe | 216.58.207.65:443 | s2.googleusercontent.com | Google Inc. | US | whitelisted |
1440 | iexplore.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1440 | iexplore.exe | 216.58.205.238:443 | s.ytimg.com | Google Inc. | US | whitelisted |
464 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1440 | iexplore.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
cdn.discordapp.com |
| shared |
youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.youtube.com |
| whitelisted |
yt3.ggpht.com |
| whitelisted |
s2.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
api.bing.com |
| whitelisted |