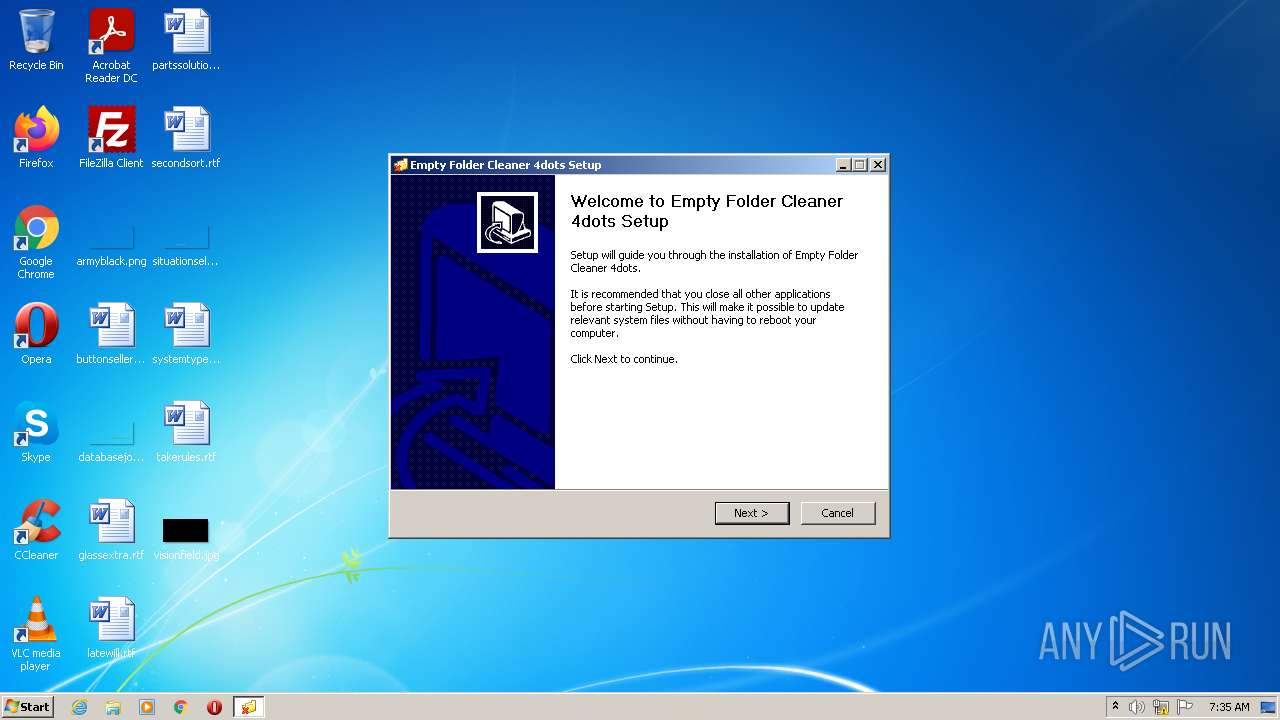
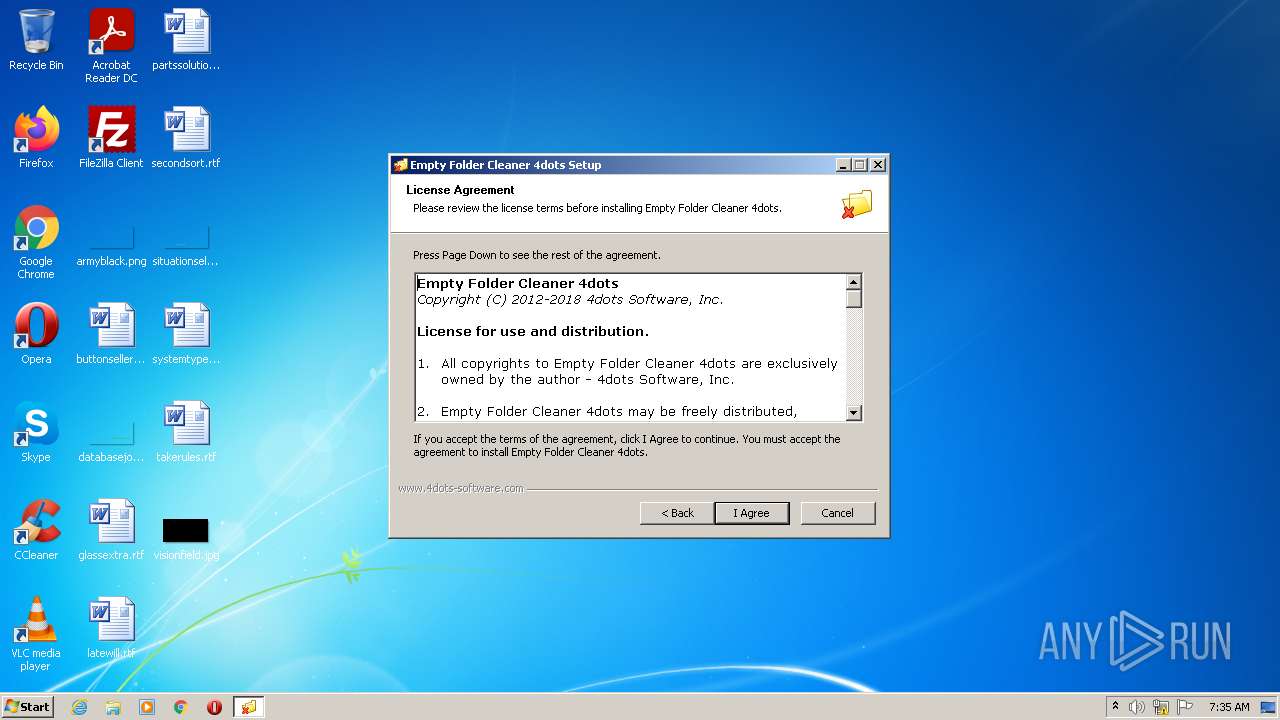
| File name: | EmptyFolderCleanerSetup.exe |
| Full analysis: | https://app.any.run/tasks/aef6f826-2fc6-4a2e-8be6-f58206232ea9 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2022, 07:35:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D31C82F6B1F8C6B013F3778396900B65 |
| SHA1: | 55B18D97A16F5F153B0C36EB335FF564B64C6BCD |
| SHA256: | 3749A209D3CA68CAFD5B0A18BA8314733A66DE610188D07848B4C49DE72651AE |
| SSDEEP: | 393216:DGW8qoApJLg+//HPRcTfGJdLzduvZeDf2hRT:YqoApJLgyM+LDKfT |
MALICIOUS
Drops executable file immediately after starts
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 3928)
Application was dropped or rewritten from another process
- vcredist_x86.exe (PID: 3928)
- vcredist_x86.exe (PID: 2888)
Loads dropped or rewritten executable
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 3928)
- regsvr32.exe (PID: 2852)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 2888)
Registers / Runs the DLL via REGSVR32.EXE
- EmptyFolderCleanerSetup.exe (PID: 2892)
SUSPICIOUS
Checks supported languages
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 2888)
- vcredist_x86.exe (PID: 3928)
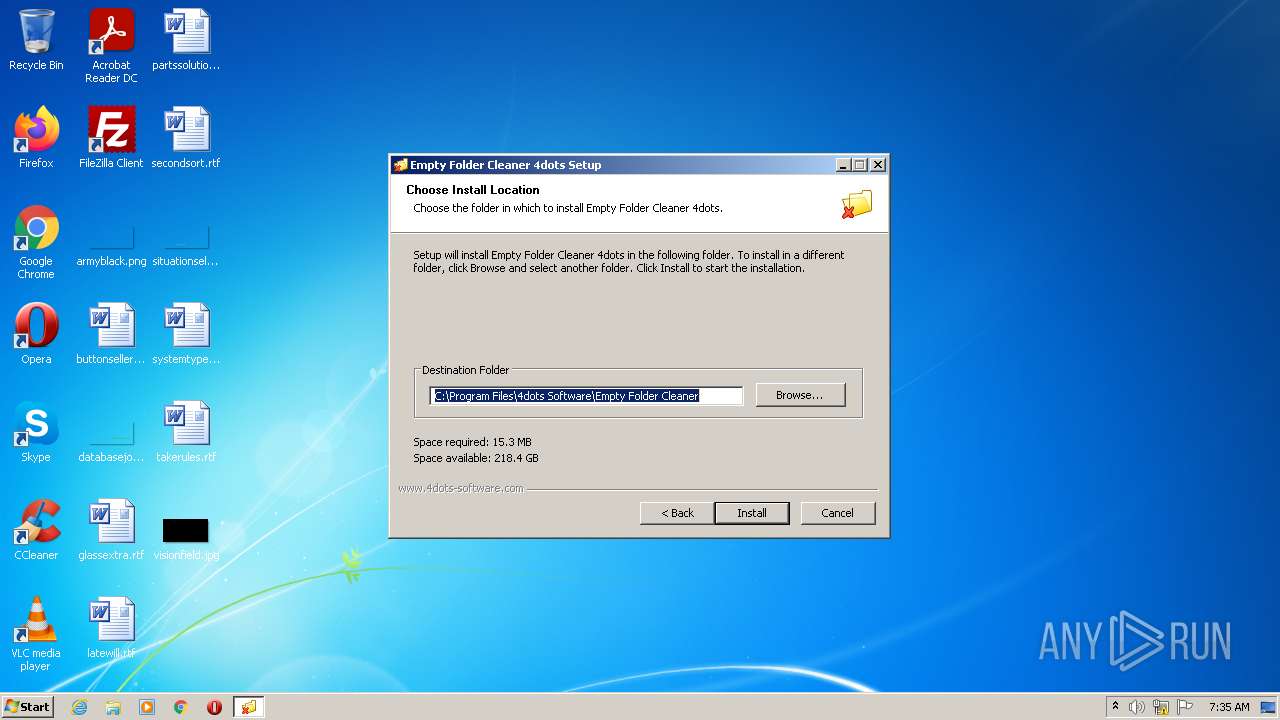
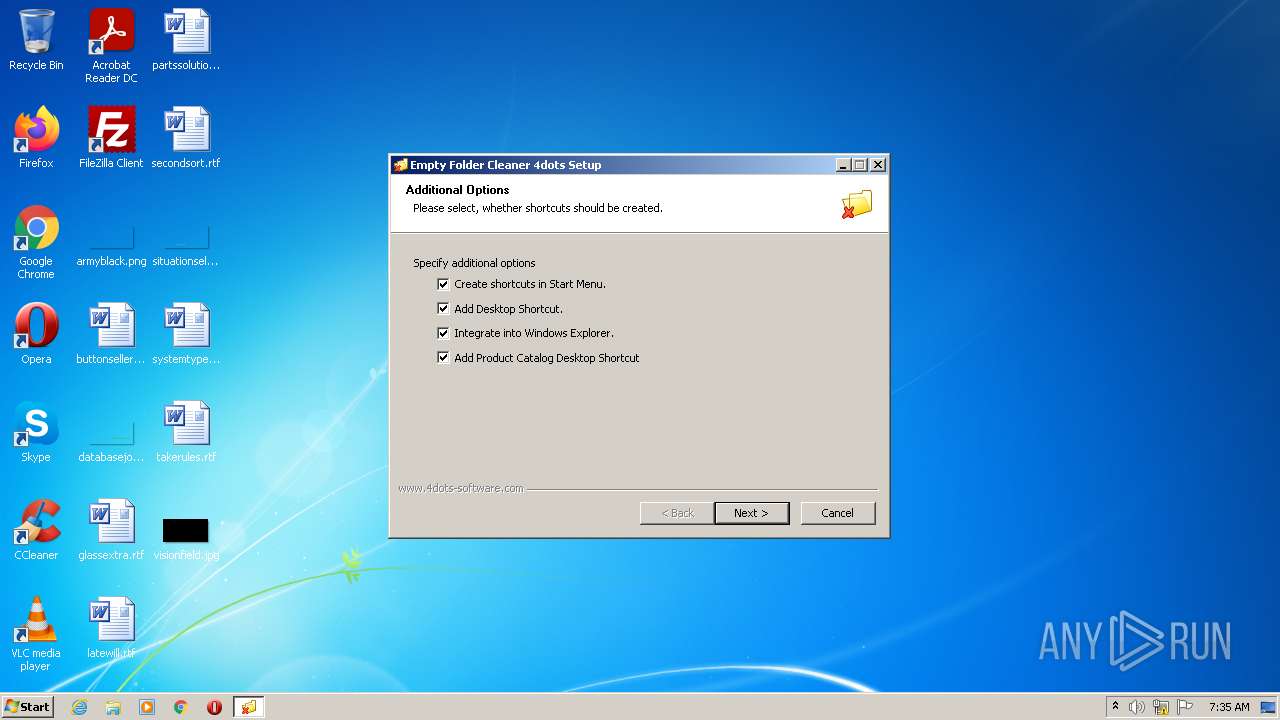
Creates a directory in Program Files
- EmptyFolderCleanerSetup.exe (PID: 2892)
Creates files in the program directory
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 2888)
Drops a file that was compiled in debug mode
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 3928)
- vcredist_x86.exe (PID: 2888)
- msiexec.exe (PID: 3700)
Reads the computer name
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 3928)
- vcredist_x86.exe (PID: 2888)
Executable content was dropped or overwritten
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 3928)
- vcredist_x86.exe (PID: 2888)
- msiexec.exe (PID: 3700)
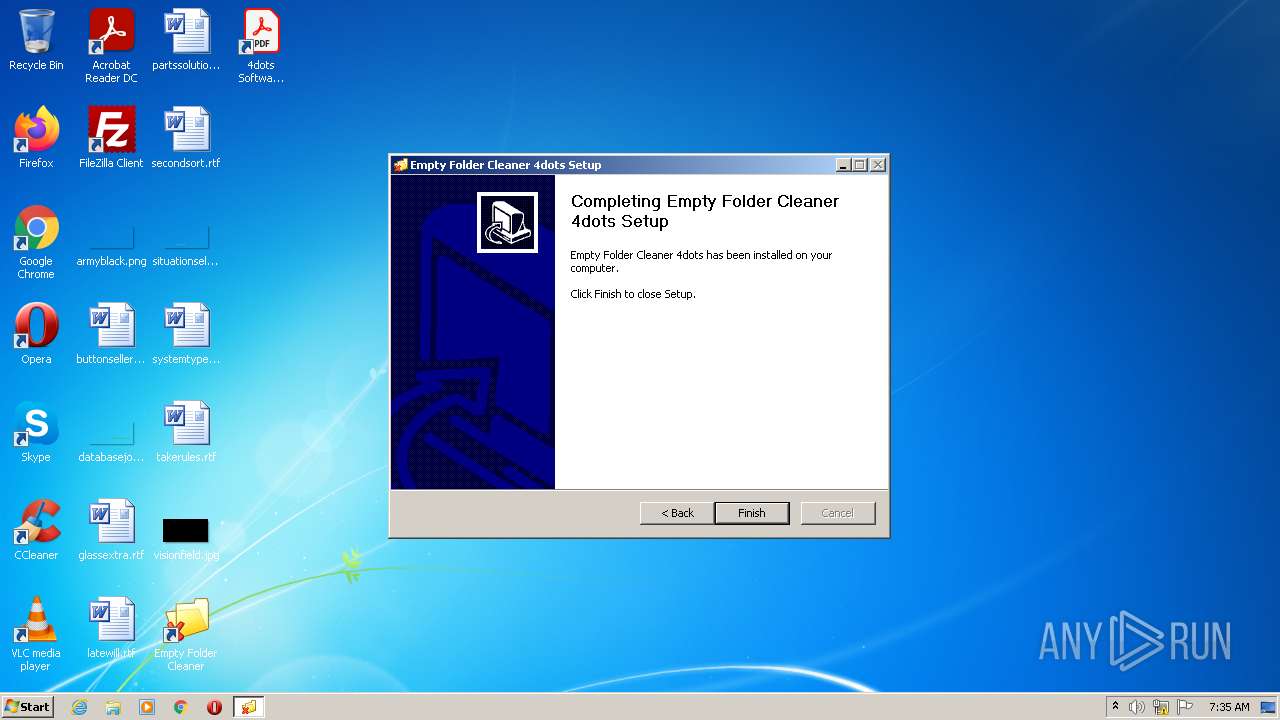
Creates a software uninstall entry
- EmptyFolderCleanerSetup.exe (PID: 2892)
- vcredist_x86.exe (PID: 2888)
- msiexec.exe (PID: 3700)
Application launched itself
- vcredist_x86.exe (PID: 2888)
Searches for installed software
- vcredist_x86.exe (PID: 3928)
- vcredist_x86.exe (PID: 2888)
Executed as Windows Service
- vssvc.exe (PID: 3140)
- msiexec.exe (PID: 3700)
Reads Environment values
- vssvc.exe (PID: 3140)
Reads the Windows organization settings
- msiexec.exe (PID: 3700)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3700)
Creates files in the Windows directory
- msiexec.exe (PID: 3700)
- EmptyFolderCleanerSetup.exe (PID: 2892)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2852)
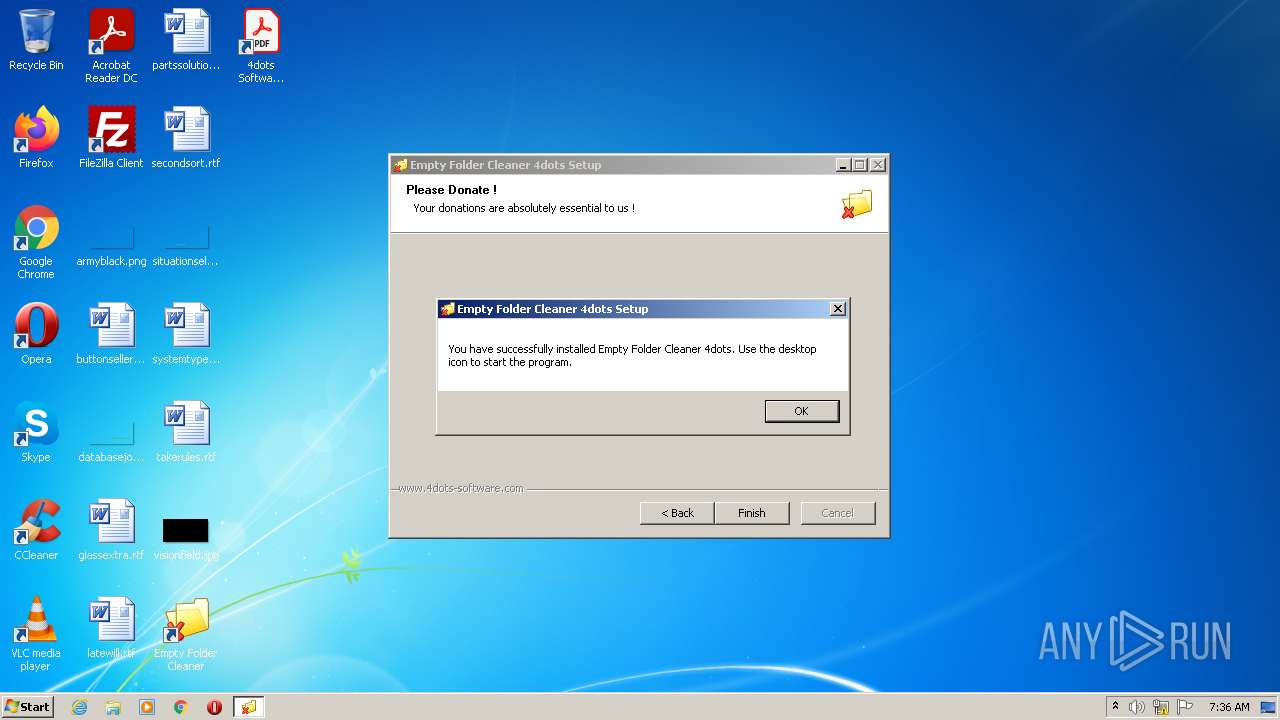
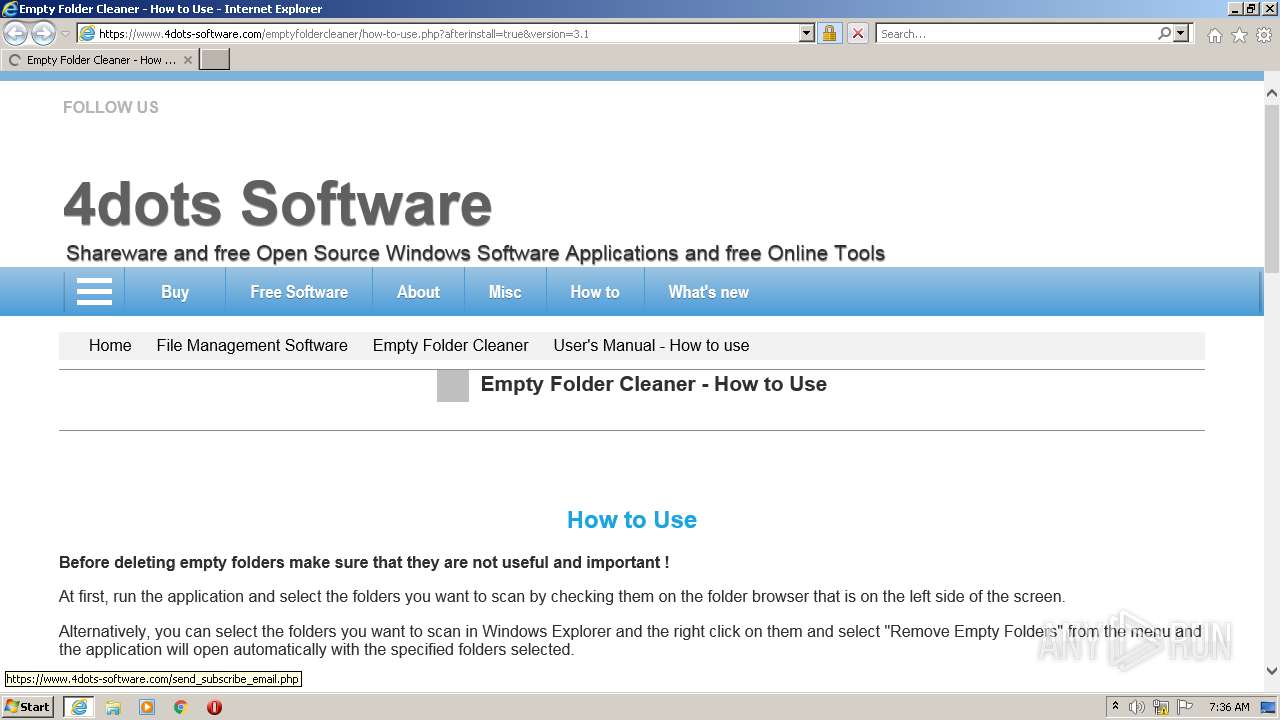
Starts Internet Explorer
- EmptyFolderCleanerSetup.exe (PID: 2892)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2620)
INFO
Checks supported languages
- vssvc.exe (PID: 3140)
- msiexec.exe (PID: 3700)
- regsvr32.exe (PID: 2852)
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 2620)
Reads the computer name
- vssvc.exe (PID: 3140)
- msiexec.exe (PID: 3700)
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 2620)
Checks Windows Trust Settings
- vcredist_x86.exe (PID: 2888)
- msiexec.exe (PID: 3700)
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 2620)
Reads settings of System Certificates
- vcredist_x86.exe (PID: 2888)
- msiexec.exe (PID: 3700)
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 3152)
Dropped object may contain Bitcoin addresses
- vcredist_x86.exe (PID: 2888)
- msiexec.exe (PID: 3700)
Application launched itself
- iexplore.exe (PID: 3152)
Changes internet zones settings
- iexplore.exe (PID: 3152)
Reads internet explorer settings
- iexplore.exe (PID: 2620)
Creates files in the user directory
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 3152)
Changes settings of System certificates
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 3152)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x320c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 162816 |
| CodeSize: | 25600 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2018:01:30 04:57:45+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4422 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x00015000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x00007640 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.81581 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.34226 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.55272 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.31274 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 5.94667 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.80903 | 1736 | UNKNOWN | English - United States | RT_ICON |
7 | 4.15945 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 4.15881 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.85812 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
53
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3152 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2852 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\EmptyFolderCleanerExt.dll" | C:\Windows\system32\regsvr32.exe | — | EmptyFolderCleanerSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | "C:\Program Files\4dots Software\Empty Folder Cleaner\vcredist_x86.exe" /q | C:\Program Files\4dots Software\Empty Folder Cleaner\vcredist_x86.exe | EmptyFolderCleanerSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\AppData\Local\Temp\EmptyFolderCleanerSetup.exe" | C:\Users\admin\AppData\Local\Temp\EmptyFolderCleanerSetup.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3140 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.4dots-software.com/emptyfoldercleaner/how-to-use.php?afterinstall=true&version=3.1 | C:\Program Files\Internet Explorer\iexplore.exe | EmptyFolderCleanerSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3240 | "C:\Users\admin\AppData\Local\Temp\EmptyFolderCleanerSetup.exe" | C:\Users\admin\AppData\Local\Temp\EmptyFolderCleanerSetup.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3700 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3928 | "C:\Program Files\4dots Software\Empty Folder Cleaner\vcredist_x86.exe" /q -burn.unelevated BurnPipe.{F58586C0-40A3-47C6-B3F8-38B7DDCB6F47} {0C1D18D5-FCE6-45F9-84C4-4D2B191FB43E} 2888 | C:\Program Files\4dots Software\Empty Folder Cleaner\vcredist_x86.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
Total events
40 211
Read events
39 425
Write events
760
Delete events
26
Modification events
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Empty Folder Cleaner |
| Operation: | write | Name: | DisplayName |
Value: Empty Folder Cleaner (remove only) | |||
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Empty Folder Cleaner |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\4dots Software\Empty Folder Cleaner\EmptyFolderCleaner.exe | |||
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Empty Folder Cleaner |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\4dots Software\Empty Folder Cleaner\Uninstall.exe | |||
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Empty Folder Cleaner |
| Operation: | write | Name: | Publisher |
Value: 4dots Software | |||
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\4dots Software\EmptyFolderCleaner |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\4dots Software\Empty Folder Cleaner | |||
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\4dots Software\EmptyFolderCleaner |
| Operation: | write | Name: | InstallationDirectory |
Value: C:\Program Files\4dots Software\Empty Folder Cleaner | |||
| (PID) Process: | (2892) EmptyFolderCleanerSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\4dots Software\EmptyFolderCleaner |
| Operation: | write | Name: | Menu Item Caption |
Value: Remove Empty Folders | |||
| (PID) Process: | (2888) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000091EA8F71BF3DD801480B0000680B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2888) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000EB4C9271BF3DD801480B0000680B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2888) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
Executable files
42
Suspicious files
55
Text files
150
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\license_agreement.rtf | text | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Users\admin\AppData\Local\Temp\nsw230B.tmp\NSISAdditionalActionsPage.ini | ini | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\settings.xml | text | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\EmptyFolderCleaner.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\Empty Folder Cleaner - User's Manual.url | url | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\CheckedExpTreeLib.dll | executable | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\4dotsLanguageDownloader.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\Program Files\4dots Software\Empty Folder Cleaner\4dots-Software-PRODUCT-CATALOG-2015.pdf | ||
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Empty Folder Cleaner\Empty Folder Cleaner.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2892 | EmptyFolderCleanerSetup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Empty Folder Cleaner\4dots Software PRODUCT CATALOG 2015.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
136
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | iexplore.exe | GET | 301 | 104.26.0.24:80 | http://www.4dots-software.com/emptyfoldercleaner/how-to-use.php?afterinstall=true&version=3.1 | US | — | — | suspicious |
2620 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDGnabG9NzXBQoAAAABOO6k | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAxZRRY2h9z3aY%2FGbZ9jzjw%3D | US | der | 471 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAmeJCQPtndvAPICal56Uvg%3D | US | der | 471 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEE5h466ffVcGCgAAAAE4730%3D | US | der | 471 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDGntkWsVwfkgoAAAABOO%2F8 | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCJUOvZw%2FGQVBIAAAAABE8U | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDyCy7NRKrIBBIAAAAABE8V | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2620 | iexplore.exe | 104.26.0.24:80 | www.4dots-software.com | Cloudflare Inc | US | suspicious |
2620 | iexplore.exe | 142.250.74.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2620 | iexplore.exe | 104.26.0.24:443 | www.4dots-software.com | Cloudflare Inc | US | suspicious |
2620 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2620 | iexplore.exe | 142.250.186.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2620 | iexplore.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2620 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2620 | iexplore.exe | 216.58.201.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2620 | iexplore.exe | 142.250.185.130:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
2620 | iexplore.exe | 142.250.186.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.4dots-software.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |