| File name: | SecuriteInfo.com.Variant.Tedy.627915.599.8749 |
| Full analysis: | https://app.any.run/tasks/b87f2f98-97b2-47c5-abd9-71b41ea063e4 |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2024, 21:44:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | A57DAD8C1DAE1FA551709713FA74BBEE |
| SHA1: | 42BC8573F4EB0A5E1EE83B7BCE5DCC952526CB88 |
| SHA256: | 3744AED5783F8FFD6DFF8D8BEB8BFCCF8ABD1320BC86F58D281F29BC58695EC0 |
| SSDEEP: | 49152:cVKRXmYnKXg6Vsn5WqBvM/IwLVcHA+Q4ooMHKjfrB5DJ5Kx1ZuYUo/qkZIHSjly3:YKRXXKXg6VsnYqBQIGZp4od4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe (PID: 6124)
- cmd.exe (PID: 6784)
Application launched itself
- cmd.exe (PID: 6784)
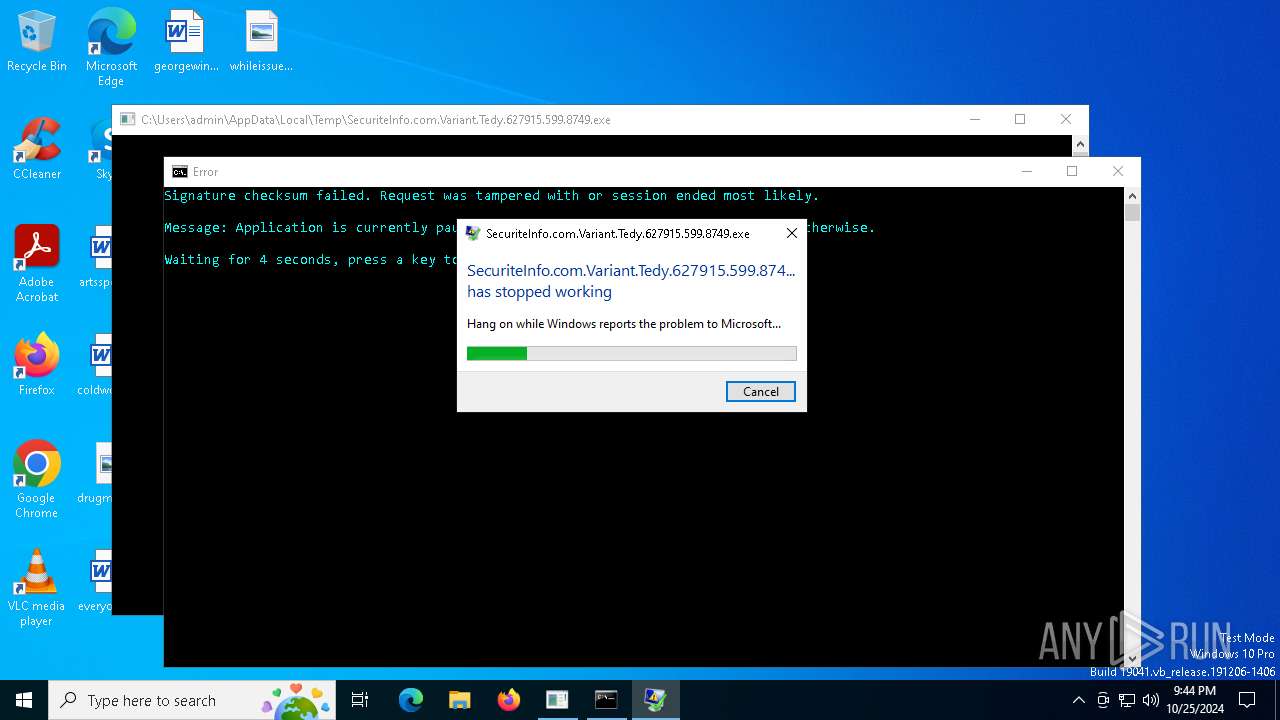
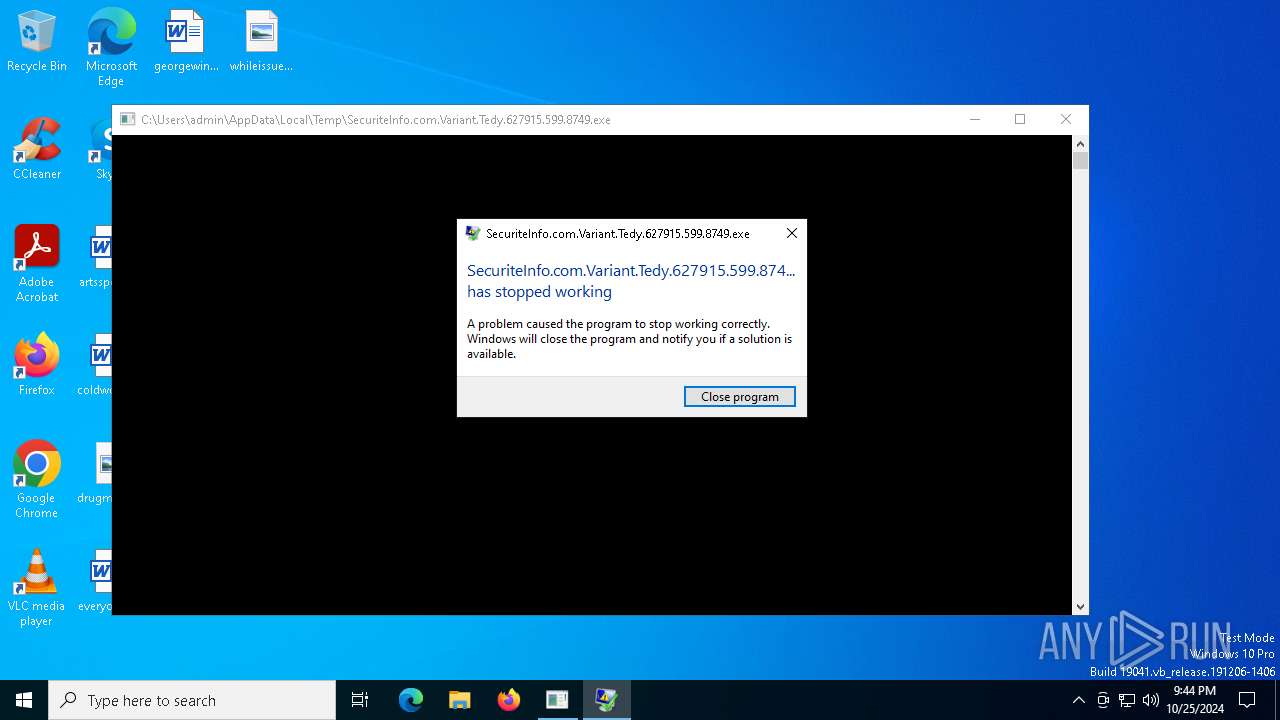
Executes application which crashes
- SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe (PID: 6124)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3848)
INFO
Checks supported languages
- SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe (PID: 6124)
Reads the computer name
- SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe (PID: 6124)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 6208)
Creates files in the program directory
- SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe (PID: 6124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:21 02:01:01+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 3041792 |
| InitializedDataSize: | 776704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e262c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
144
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | timeout /t 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
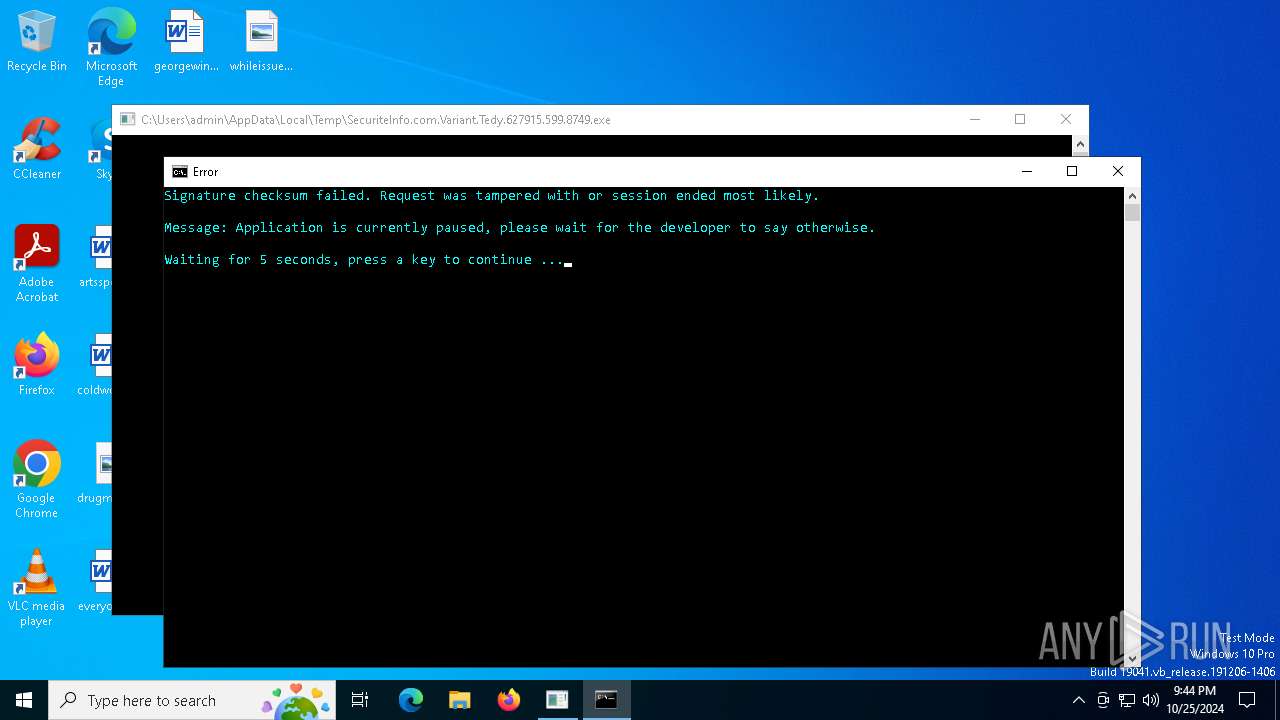
| 3848 | cmd /C "color b && title Error && echo Signature checksum failed. Request was tampered with or session ended most likely. & echo: & echo Message: Application is currently paused, please wait for the developer to say otherwise. && timeout /t 5" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6124 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 6184 | C:\WINDOWS\system32\WerFault.exe -u -p 6124 -s 688 | C:\Windows\System32\WerFault.exe | SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6208 | certutil -hashfile "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6332 | find /i /v "md5" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6784 | C:\WINDOWS\system32\cmd.exe /c start cmd /C "color b && title Error && echo Signature checksum failed. Request was tampered with or session ended most likely. & echo: & echo Message: Application is currently paused, please wait for the developer to say otherwise. && timeout /t 5" | C:\Windows\System32\cmd.exe | — | SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 235
Read events
4 235
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
6
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6184 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_SecuriteInfo.com_3614ad19c0cf73c93992fea3fa40529655361d0_1eb0641c_eb7d561f-163b-4831-96d3-c416955064d5\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6184 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC53F.tmp.xml | xml | |
MD5:8ADD4F3F5F94E331BDF8FB666CB393C0 | SHA256:5215562BDE2579FB7AE57386C12FFE4C22A89CF87F8BFF6ED491D8E3FC8ABE6C | |||
| 6184 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:55E2A4D62673D3F32DECFA500C236AB6 | SHA256:1CE28BE50120F20076C170B7F6A4237B6924C5095F1D1606BC20365BF3A3D104 | |||
| 6184 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC50F.tmp.WERInternalMetadata.xml | xml | |
MD5:7C9EFD384AF733868C92324ADB163A75 | SHA256:8DE5F2696D047B7AAE1F564ADEE53AA46F3BCB0BB1AB84512D6489F0D8E6A6AD | |||
| 6184 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:AF54D9C66B875869FD26A0187FA72206 | SHA256:F630A0E7D1D2C26675EF460F8FAA0901A4034EB13C557881D72407E31DCED011 | |||
| 6184 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:F0CF5B1794ECA7CD73F9C020DAAB8EF2 | SHA256:2AF00EDCE7EF3266897E52DC81E8DE3B7A079028C0F1F96EAFF9E38AD342F617 | |||
| 6184 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe.6124.dmp | binary | |
MD5:56F40ADD90E10652FAEC2CBF9FF122F8 | SHA256:4D9B01A15E55C807A25C64F383A20059614C085890DDD00B71A6376088D52552 | |||
| 6184 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:1B7FD5177461034E4086724C5845E927 | SHA256:065AF18C229898A1C2A8D989911ADCD9B1E2AB14B1953EBF8EAF34AE37EA1627 | |||
| 6124 | SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe | C:\ProgramData\KeyAuth\Debug\SecuriteInfo.com.Variant.Tedy.627915.599.8749\10-25-2024.txt | text | |
MD5:8289DC91C1AA1830140EBF3E196815D3 | SHA256:0D9EE35F63999D4E658ED7FD093B625EDF165164737EC97574802467724A3F77 | |||
| 6184 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC433.tmp.dmp | binary | |
MD5:66F968A8369A057868A4DE5102D713F3 | SHA256:D52AAD80066A38E26E9043AC9E75585FAF99319FE501A50EE9D6B115D05D994F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
62
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6184 | WerFault.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6184 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5564 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6024 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6024 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2936 | svchost.exe | GET | 304 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7060 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
keyauth.win |
| malicious |
watson.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
6124 | SecuriteInfo.com.Variant.Tedy.627915.599.8749.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |