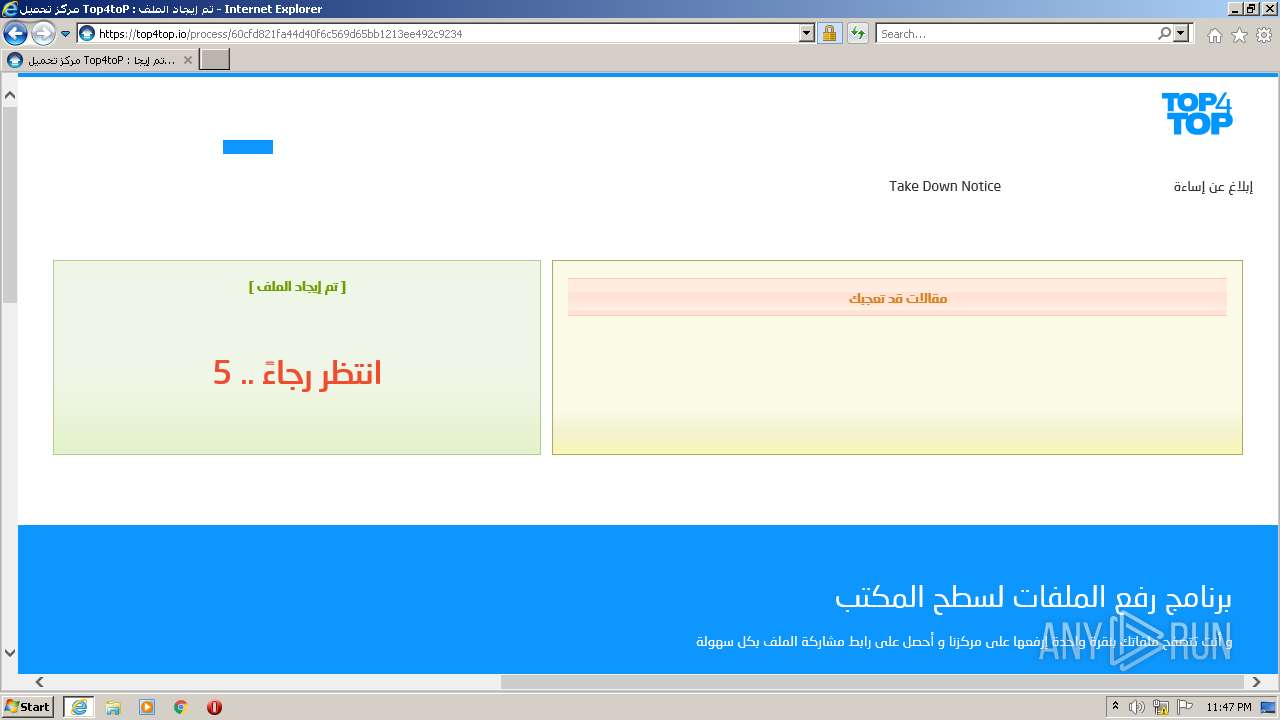
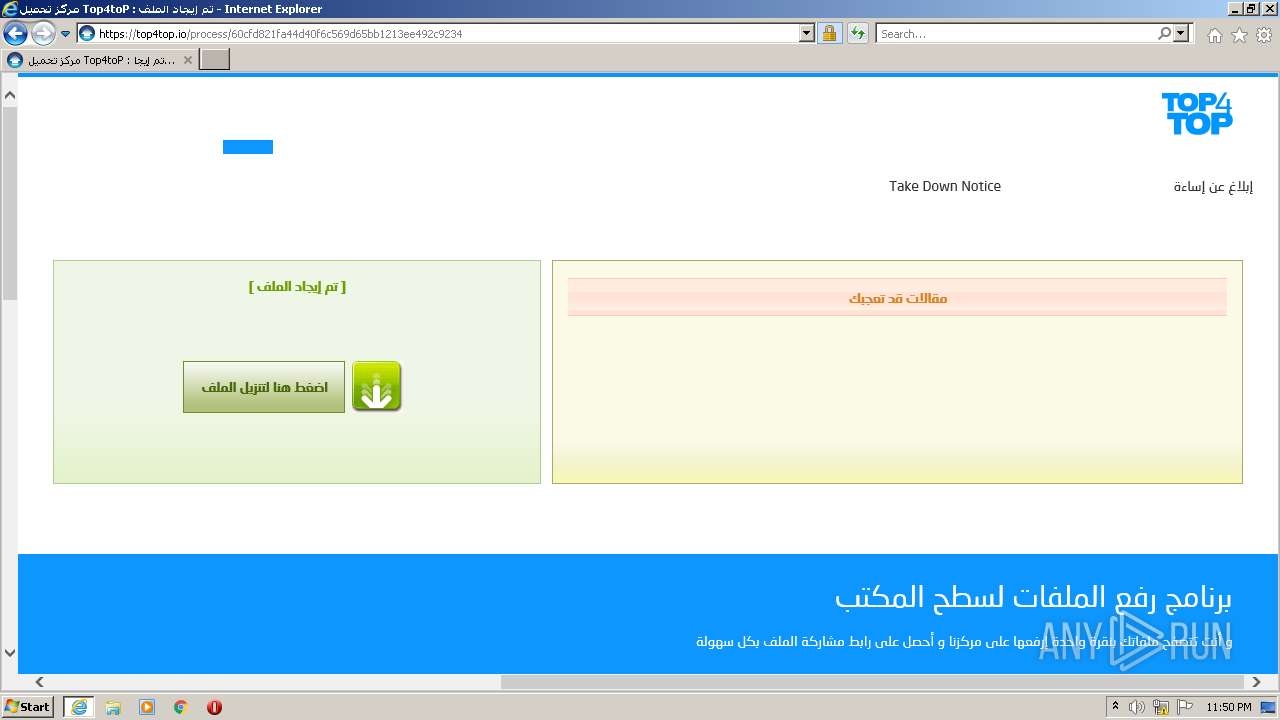
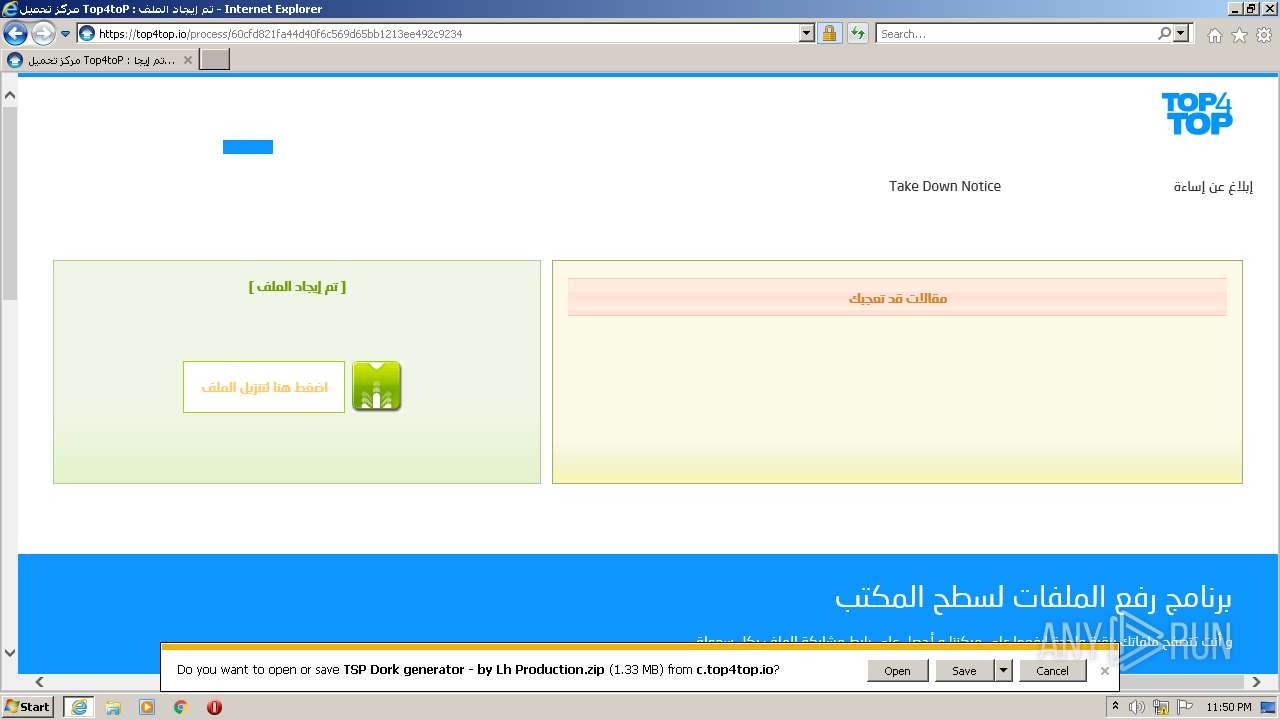
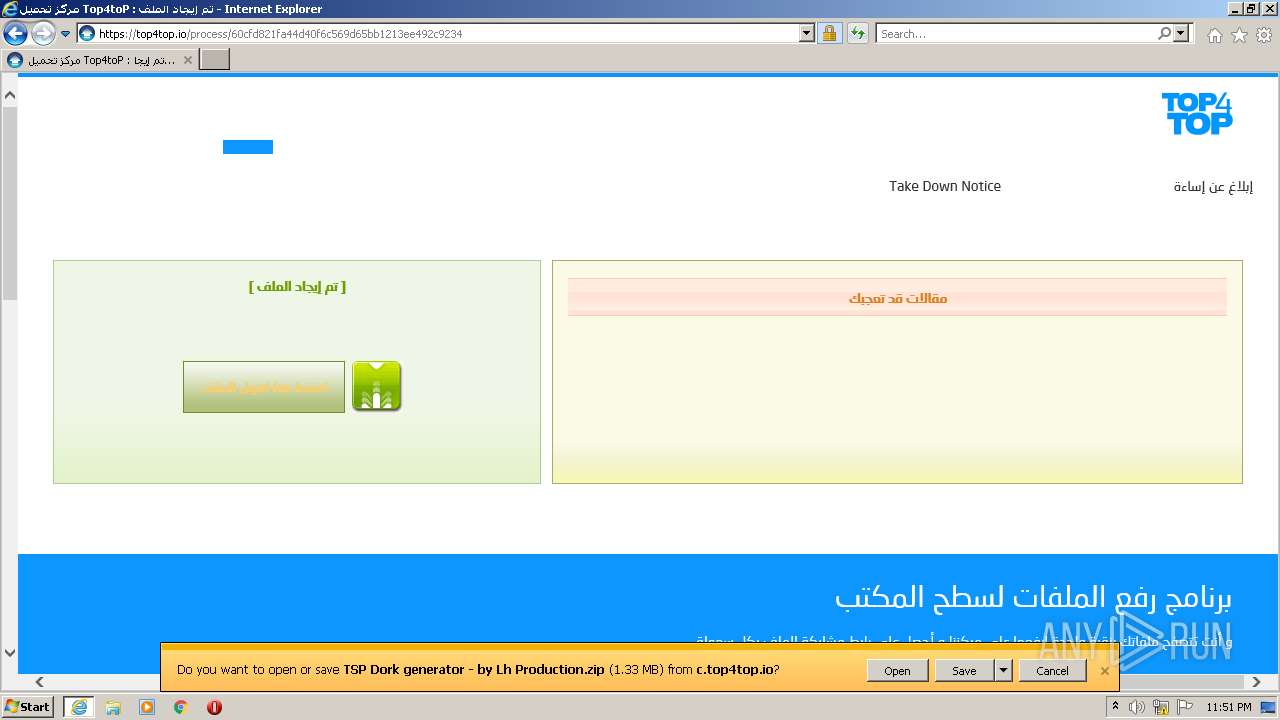
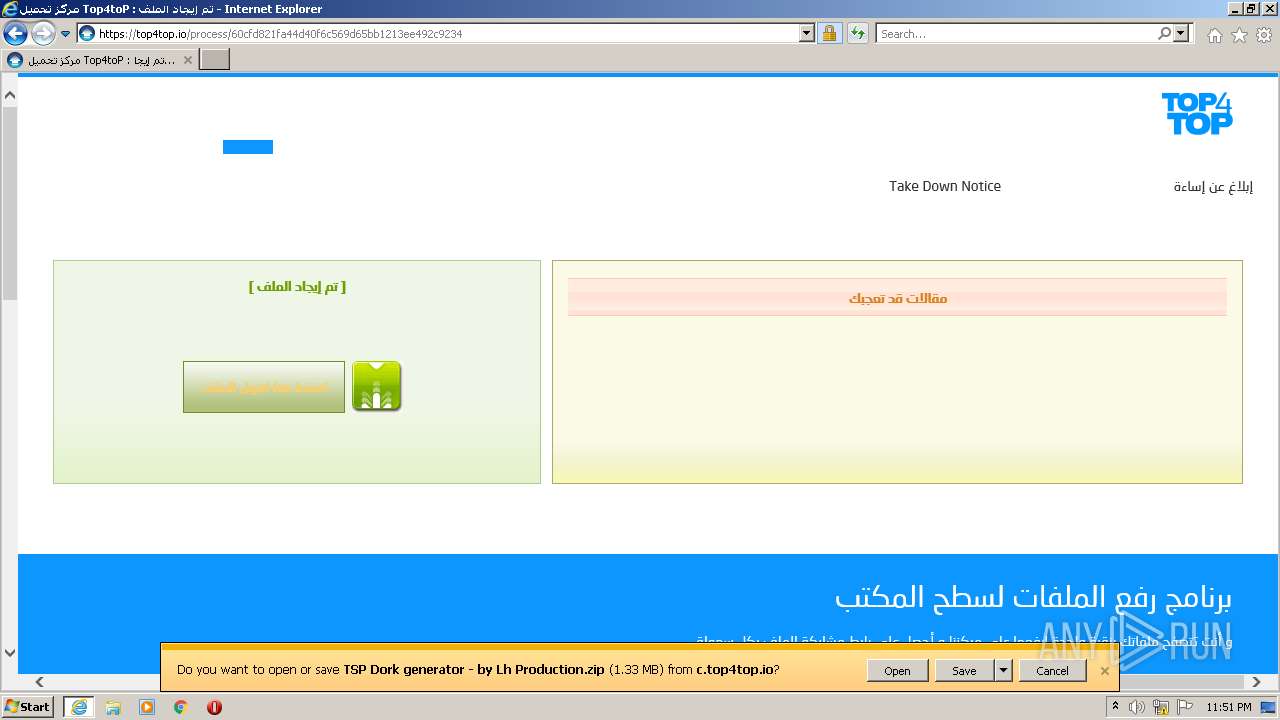
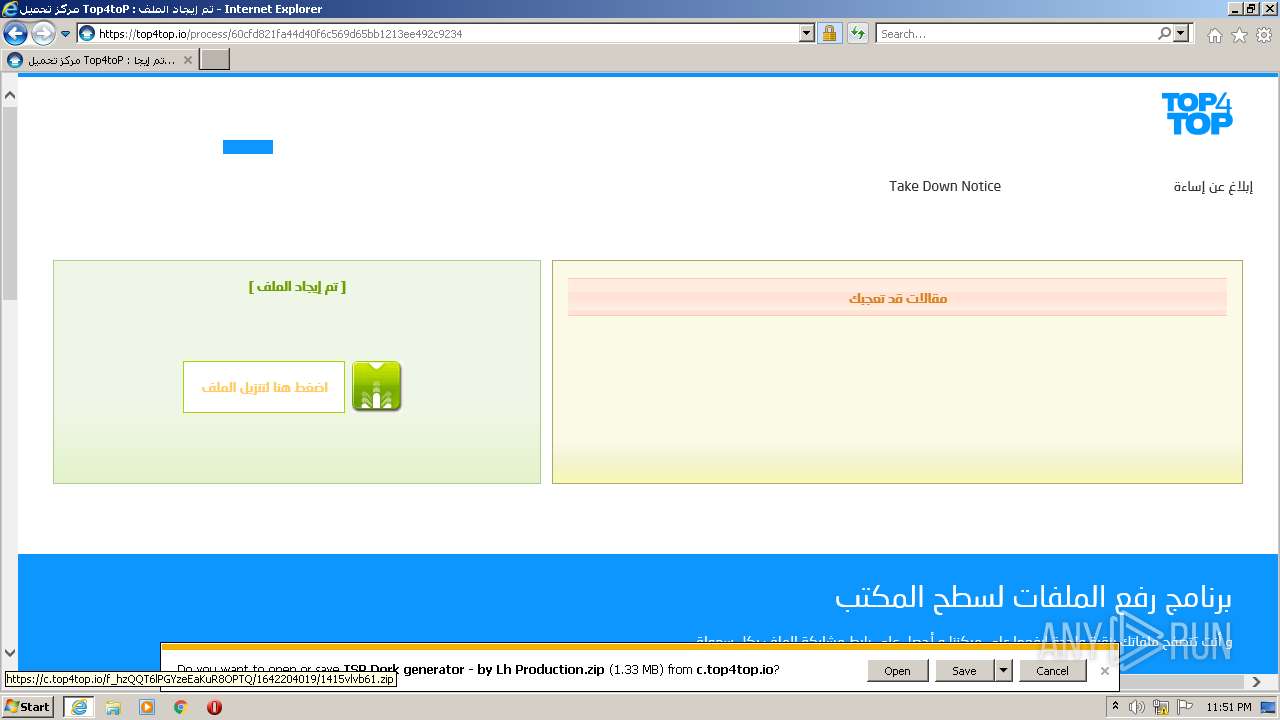
| URL: | https://c.top4top.io/f_S37CrS9mZlrJak392t4M1g/1642203966/1415vlvb61.zip |
| Full analysis: | https://app.any.run/tasks/2ac492e7-a929-44dc-89e6-15288ff24fa6 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2022, 23:46:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BCA40A1A483A88E3009F0CA1075F5702 |
| SHA1: | E183C618962FE356C51746F21578CA5F0FE3A220 |
| SHA256: | 372E8CD16E1721CD0E272D12127C51D3F2931EA4066ECD7565070AEB7103DE10 |
| SSDEEP: | 3:N8WOvm2Mm/vnzJC7RUGTSkVn:2WS2mn9YtTScn |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2328)
Application was dropped or rewritten from another process
- TSP Dork generator.exe (PID: 1260)
- TSP Dork generator.exe (PID: 2400)
- TSP Dork generator.exe (PID: 2544)
SUSPICIOUS
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3764)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3444)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3764)
- WinRAR.exe (PID: 2328)
- TSP Dork generator.exe (PID: 1260)
- TSP Dork generator.exe (PID: 2400)
- TSP Dork generator.exe (PID: 2544)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3764)
- WinRAR.exe (PID: 2328)
- TSP Dork generator.exe (PID: 1260)
- TSP Dork generator.exe (PID: 2400)
- TSP Dork generator.exe (PID: 2544)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3764)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2328)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2328)
Reads Environment values
- TSP Dork generator.exe (PID: 1260)
- TSP Dork generator.exe (PID: 2400)
- TSP Dork generator.exe (PID: 2544)
INFO
Reads the computer name
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3444)
Checks supported languages
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 3300)
- NOTEPAD.EXE (PID: 2864)
Checks Windows Trust Settings
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3444)
Reads internet explorer settings
- iexplore.exe (PID: 3444)
Reads CPU info
- iexplore.exe (PID: 3444)
Application launched itself
- iexplore.exe (PID: 3300)
Creates files in the user directory
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3444)
Reads settings of System Certificates
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 3444)
- TSP Dork generator.exe (PID: 1260)
- TSP Dork generator.exe (PID: 2400)
- TSP Dork generator.exe (PID: 2544)
Changes settings of System certificates
- iexplore.exe (PID: 3300)
Changes internet zones settings
- iexplore.exe (PID: 3300)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3300)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3300)
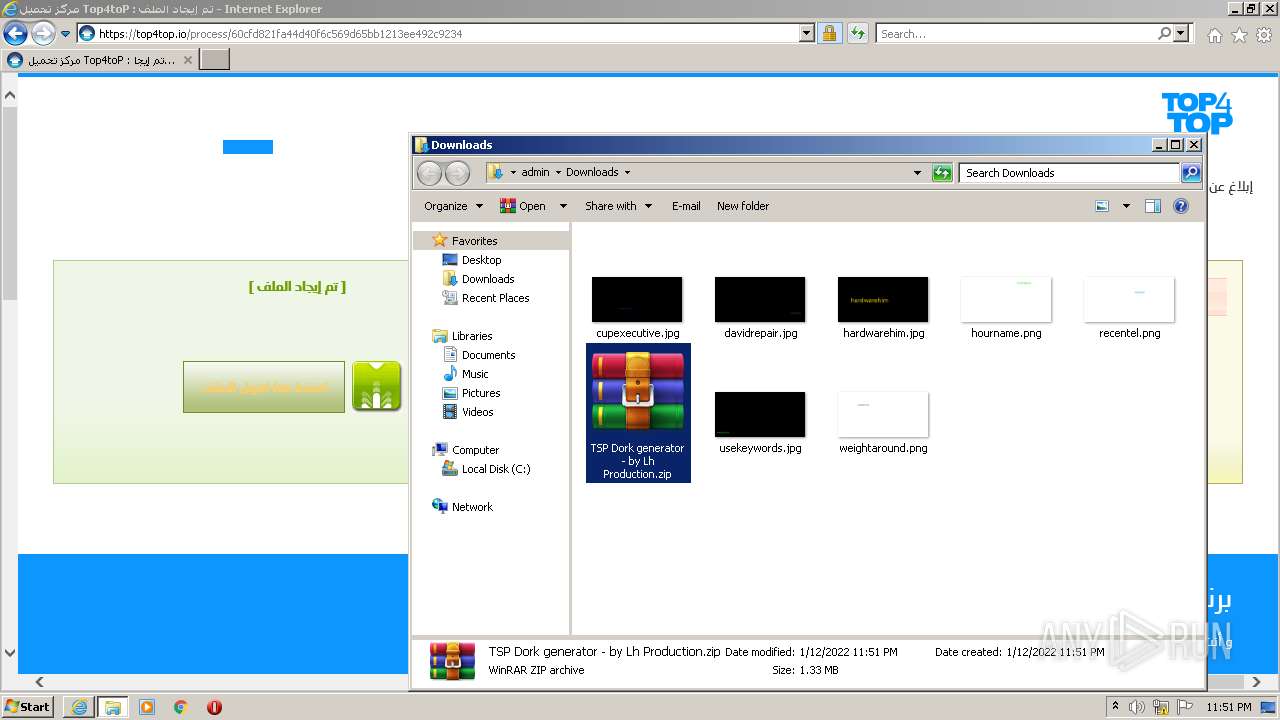
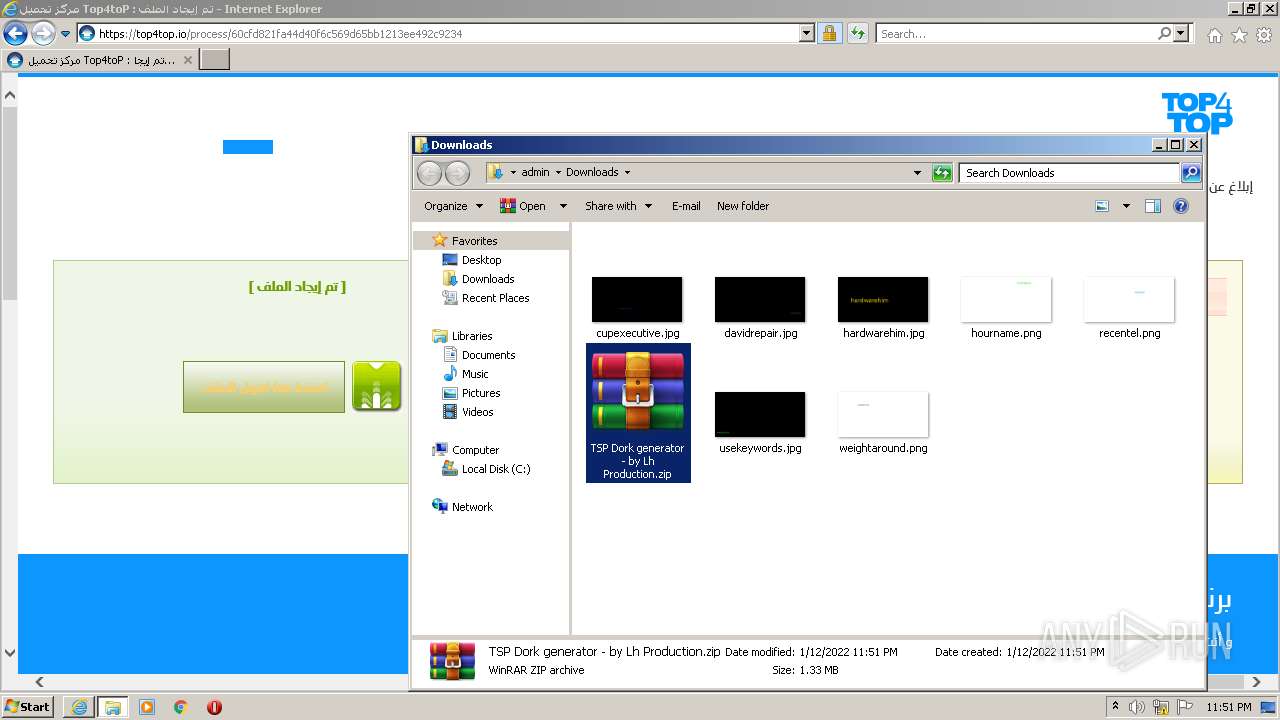
Manual execution by user
- WinRAR.exe (PID: 2328)
- NOTEPAD.EXE (PID: 2864)
- TSP Dork generator.exe (PID: 1260)
- TSP Dork generator.exe (PID: 2400)
- TSP Dork generator.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
8
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
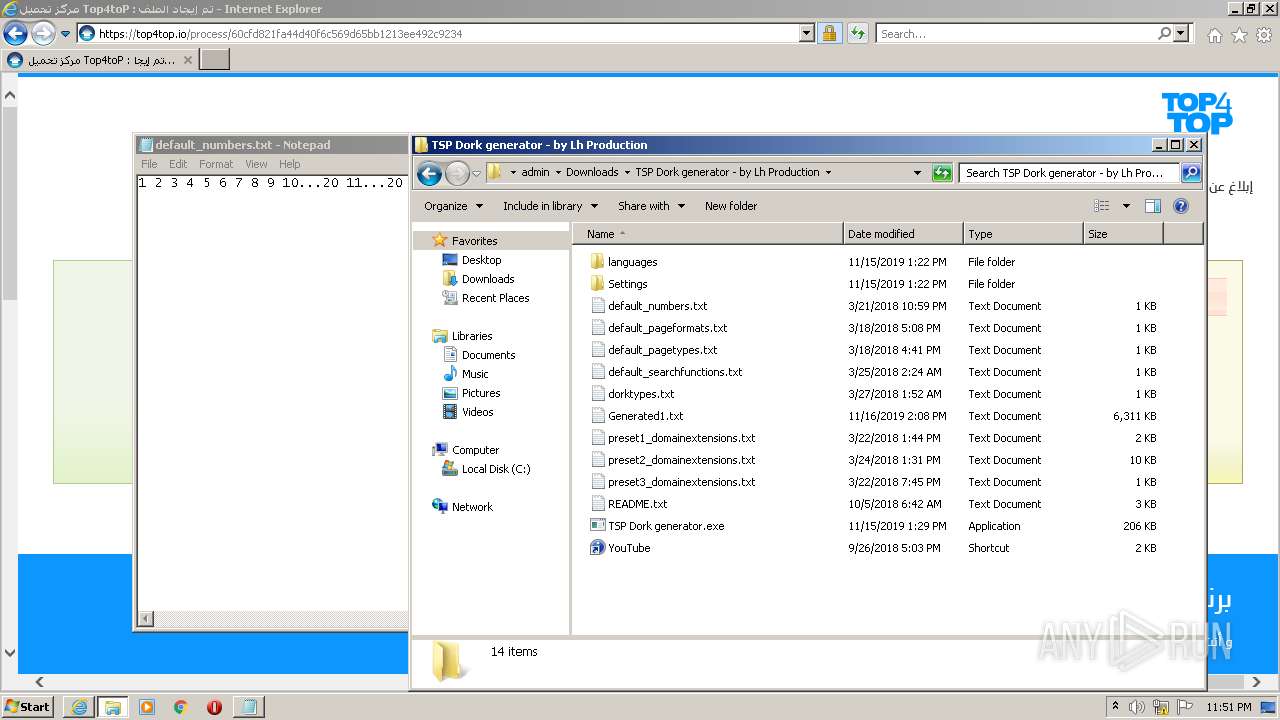
| 1260 | "C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\TSP Dork generator.exe" | C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\TSP Dork generator.exe | Explorer.EXE | ||||||||||||
User: admin Company: thiplol Integrity Level: MEDIUM Description: Gorker Private TSP Edition Exit code: 0 Version: 7.0 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\TSP Dork generator - by Lh Production.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\TSP Dork generator.exe" | C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\TSP Dork generator.exe | Explorer.EXE | ||||||||||||
User: admin Company: thiplol Integrity Level: MEDIUM Description: Gorker Private TSP Edition Exit code: 0 Version: 7.0 Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\TSP Dork generator.exe" | C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\TSP Dork generator.exe | Explorer.EXE | ||||||||||||
User: admin Company: thiplol Integrity Level: MEDIUM Description: Gorker Private TSP Edition Exit code: 0 Version: 7.0 Modules
| |||||||||||||||
| 2864 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\TSP Dork generator - by Lh Production\default_numbers.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://c.top4top.io/f_S37CrS9mZlrJak392t4M1g/1642203966/1415vlvb61.zip" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3300 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3764 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
26 417
Read events
26 217
Write events
198
Delete events
2
Modification events
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935054 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935054 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3300) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
29
Text files
318
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6AF72DC1CC855597ABE1BA0FB9A4D289 | binary | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\f-1415vlvb61-zip[1].htm | html | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\E3KOPZCW.txt | text | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\83CF8B5BB5343F329FF080F6450A55CE | der | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YPSYF8JQ.txt | text | |
MD5:— | SHA256:— | |||
| 3300 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3444 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\83CF8B5BB5343F329FF080F6450A55CE | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
80
DNS requests
32
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3444 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCAnDacZA1UWwoAAAABJ9nq | US | der | 472 b | whitelisted |
3444 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3444 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDSgULZ%2BKzOuMFl8EbDyVt8 | US | der | 472 b | whitelisted |
3444 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3300 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3444 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3444 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAl44zHc7MVuvKz1sDC1SIU%3D | US | der | 471 b | whitelisted |
3300 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
3444 | iexplore.exe | GET | 200 | 92.123.224.113:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRcVmosUVEvhQfi9UhaZ80K3w%3D%3D | unknown | der | 503 b | shared |
3444 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3444 | iexplore.exe | 157.240.236.1:443 | connect.facebook.net | — | US | unknown |
3444 | iexplore.exe | 142.250.186.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3444 | iexplore.exe | 195.154.113.3:443 | c.top4top.io | Online S.a.s. | FR | unknown |
3444 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
3444 | iexplore.exe | 188.165.137.170:443 | top4top.io | OVH SAS | FI | unknown |
3444 | iexplore.exe | 142.250.186.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3444 | iexplore.exe | 23.111.8.154:443 | oss.maxcdn.com | netDNA | US | unknown |
3444 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3444 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3444 | iexplore.exe | 104.16.86.20:443 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
c.top4top.io |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
top4top.io |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
s.top4top.io |
| malicious |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | AV INFO Observed DNS Request to Filesharing Service (top5top. io) |
— | — | Misc activity | AV INFO Observed DNS Request to Filesharing Service (top5top. io) |
— | — | Misc activity | AV INFO Observed DNS Request to Filesharing Service (top5top. io) |