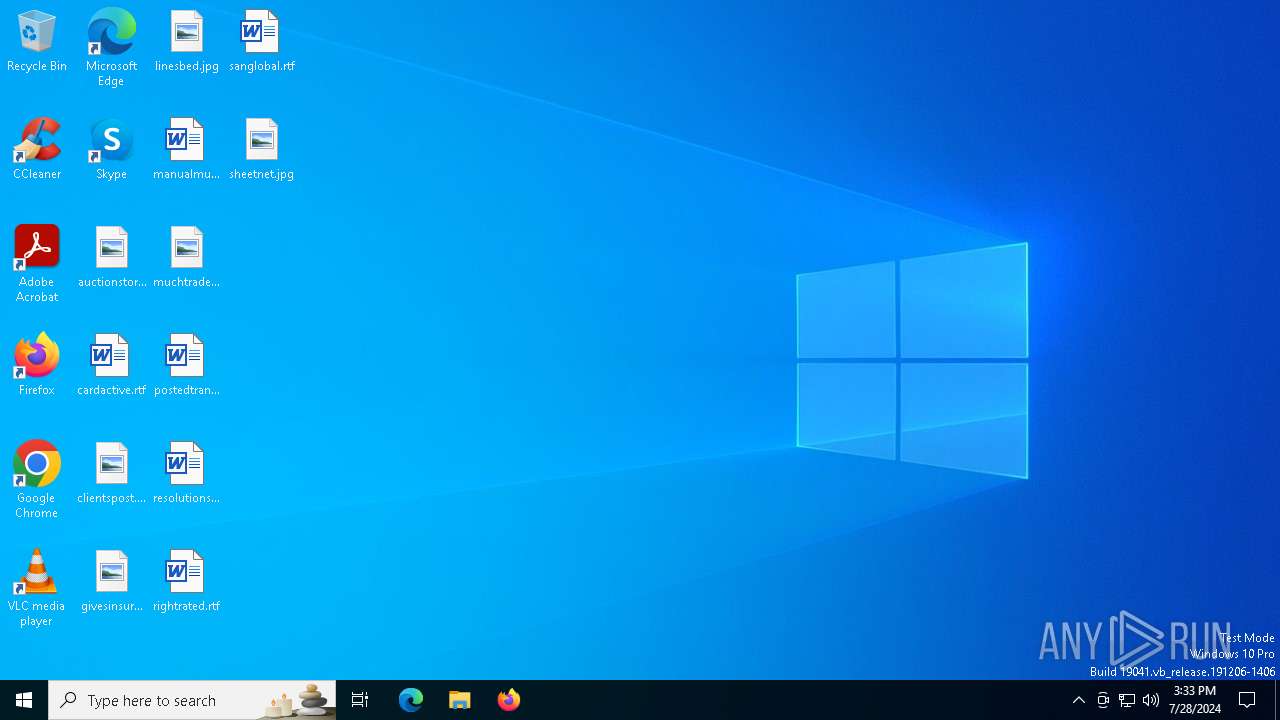
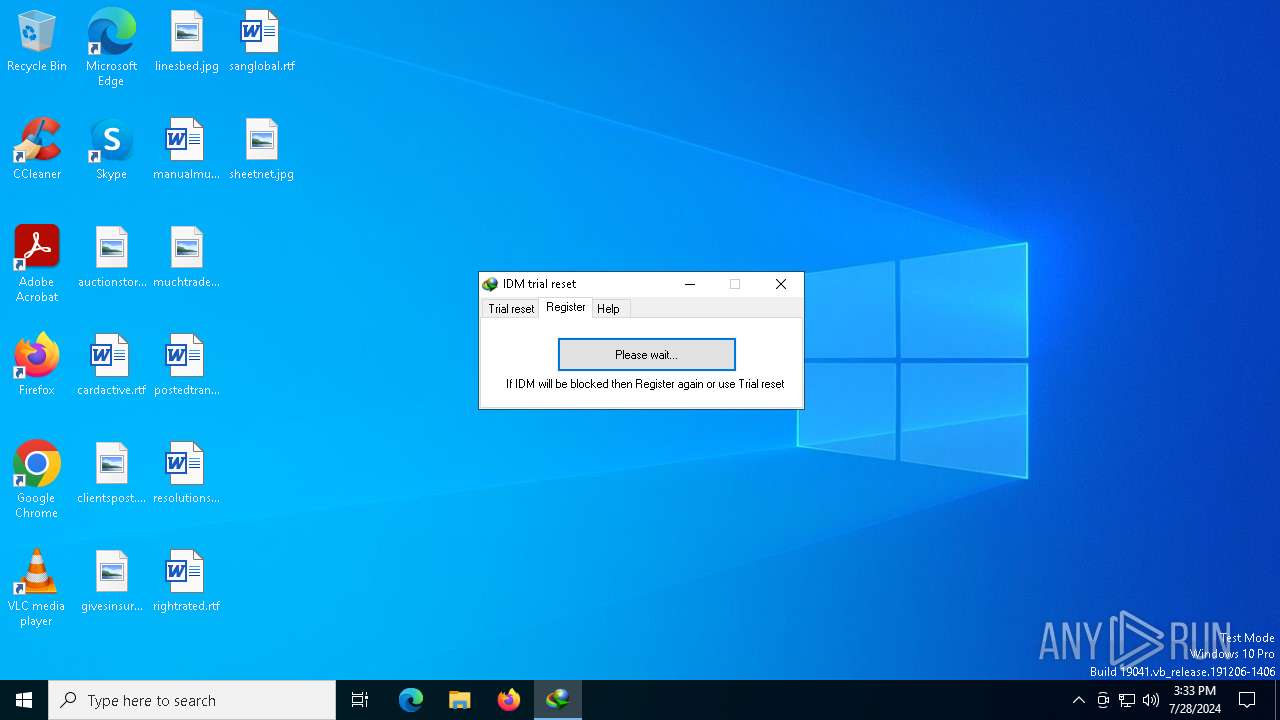
| File name: | IDM.Trial.Reset.v1.0.0.zip |
| Full analysis: | https://app.any.run/tasks/5bcb9c03-a715-471e-8bc7-8bf7e3d58ad9 |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2024, 15:33:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 016866100C1BEFF73C59F5E02323BE46 |
| SHA1: | 60AA90998FDE73E03FFBE42BF899793B32E2EE65 |
| SHA256: | 372DC10FBE87C1744D2852877E0D36D37E034B5507F868DE61C8BA6A46D0E012 |
| SSDEEP: | 12288:F3EHTdr/G+70+d5oVe+TghBAcRlbqm9Ks3wjNind3y4/VA/Sznml3gUdfFUWgsD5:BN+g6oVe+TgrVWAAjadF/XAVha2D7l |
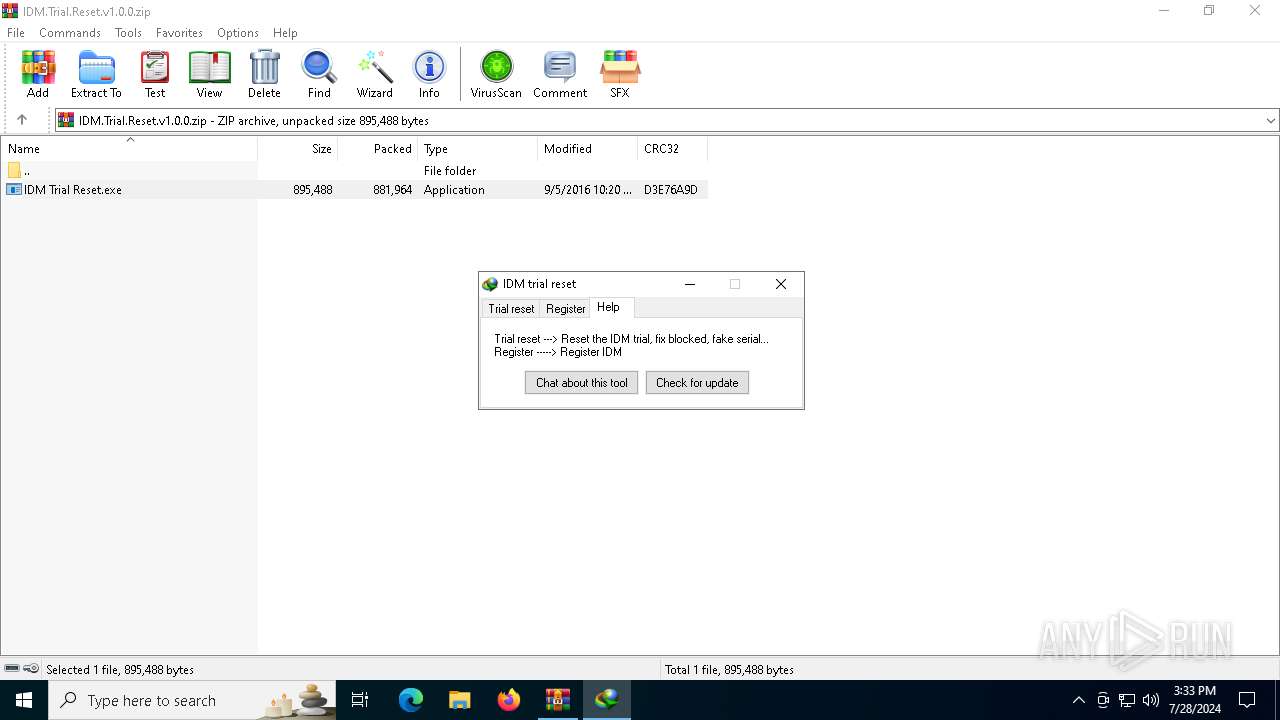
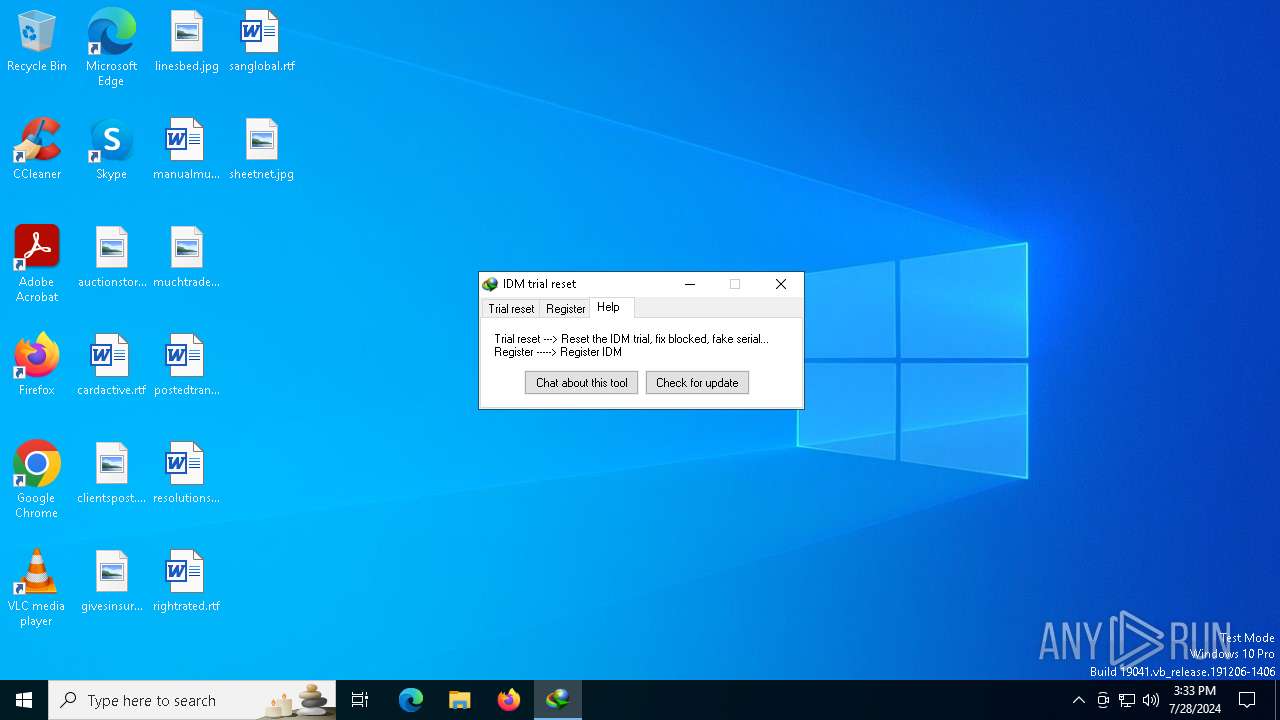
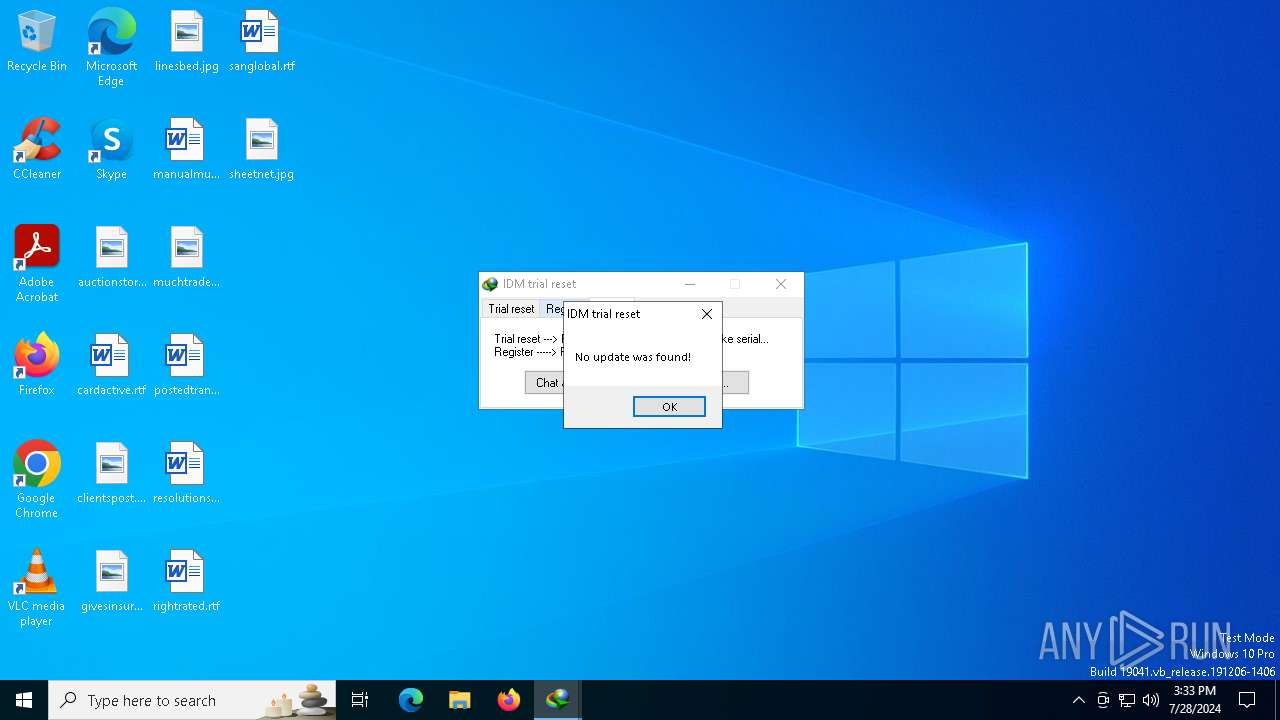
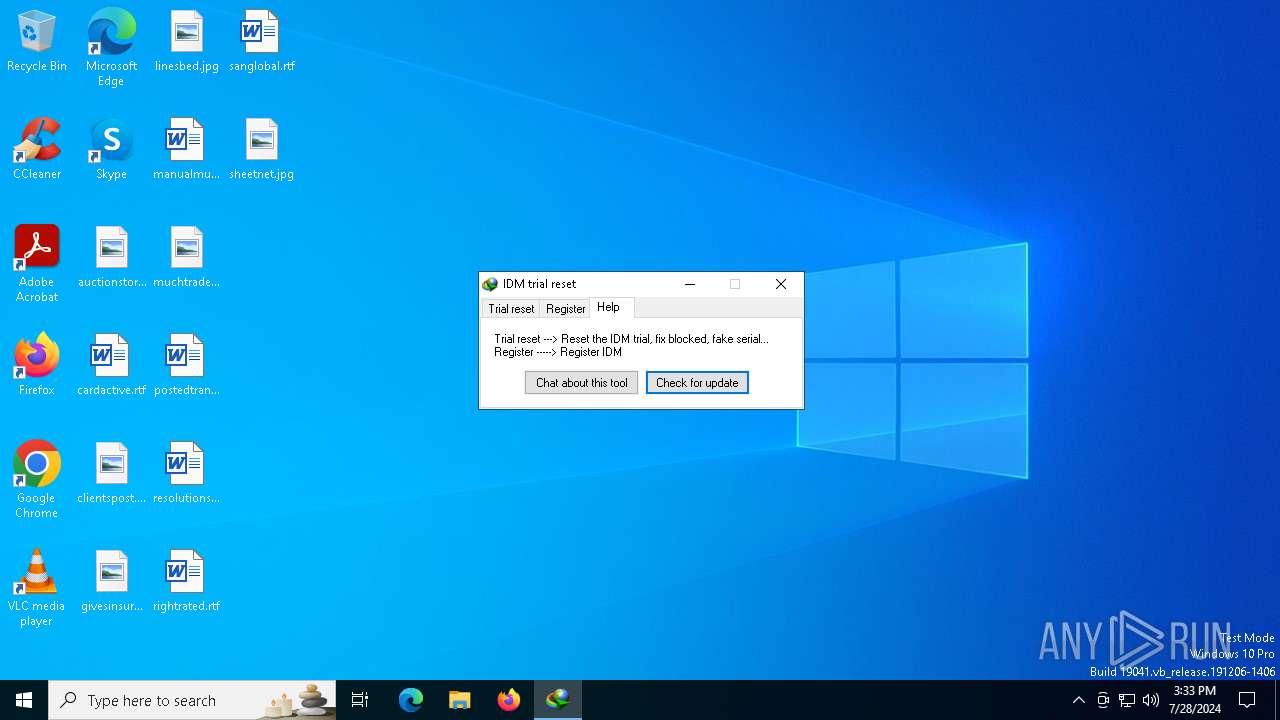
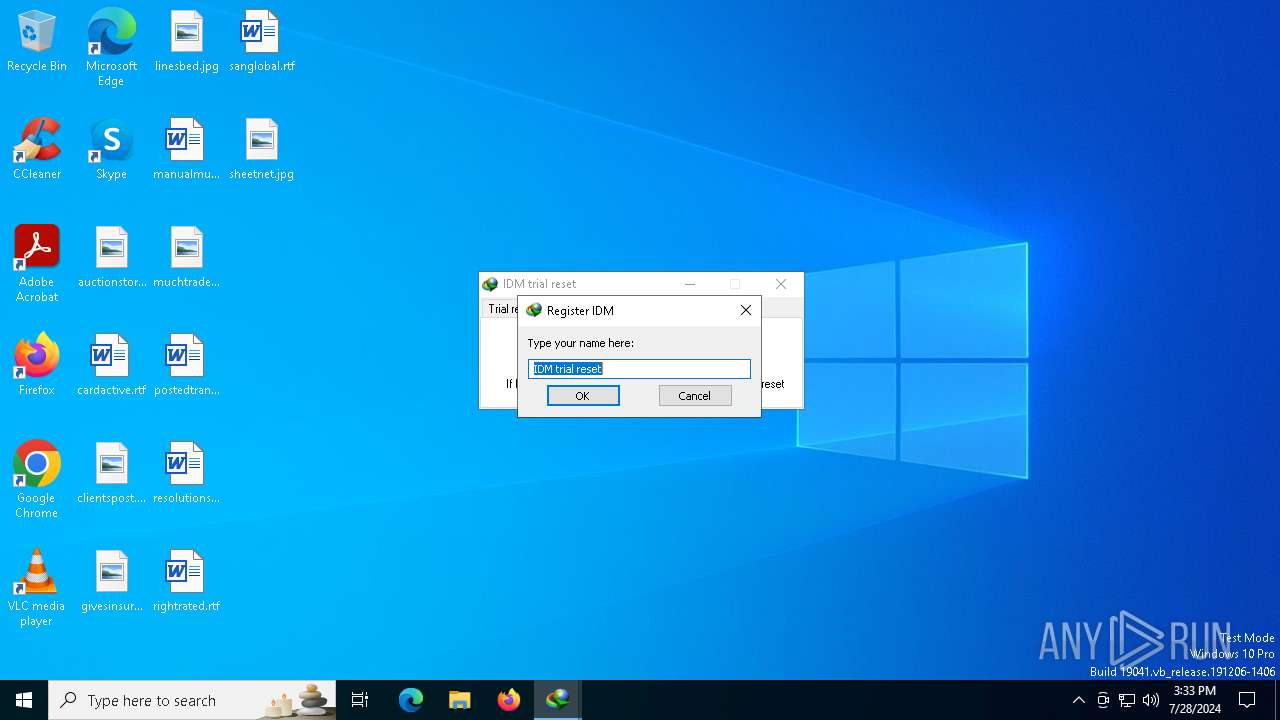
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- IDM Trial Reset.exe (PID: 2252)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4544)
- IDM Trial Reset.exe (PID: 2252)
SUSPICIOUS
Reads security settings of Internet Explorer
- IDM Trial Reset.exe (PID: 2252)
Executable content was dropped or overwritten
- IDM Trial Reset.exe (PID: 2252)
Potential Corporate Privacy Violation
- IDM Trial Reset.exe (PID: 2252)
Checks Windows Trust Settings
- IDM Trial Reset.exe (PID: 2252)
Starts CMD.EXE for commands execution
- IDM Trial Reset.exe (PID: 2252)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2824)
- IDM Trial Reset.exe (PID: 2252)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2132)
- cmd.exe (PID: 396)
INFO
Checks proxy server information
- IDM Trial Reset.exe (PID: 2252)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4544)
Creates files or folders in the user directory
- IDM Trial Reset.exe (PID: 2252)
Reads the machine GUID from the registry
- IDM Trial Reset.exe (PID: 2252)
Reads the software policy settings
- IDM Trial Reset.exe (PID: 2252)
UPX packer has been detected
- IDM Trial Reset.exe (PID: 2252)
Reads the computer name
- SetACLx64.exe (PID: 4476)
- SetACLx64.exe (PID: 752)
- SetACLx64.exe (PID: 2132)
- SetACLx64.exe (PID: 4340)
- SetACLx64.exe (PID: 6420)
- SetACLx64.exe (PID: 4772)
- SetACLx64.exe (PID: 2824)
- SetACLx64.exe (PID: 2136)
- SetACLx64.exe (PID: 1296)
- SetACLx64.exe (PID: 396)
- SetACLx64.exe (PID: 4376)
- SetACLx64.exe (PID: 4340)
- SetACLx64.exe (PID: 2824)
- SetACLx64.exe (PID: 5744)
- SetACLx64.exe (PID: 6316)
- SetACLx64.exe (PID: 2088)
- SetACLx64.exe (PID: 5832)
- SetACLx64.exe (PID: 812)
- SetACLx64.exe (PID: 736)
- SetACLx64.exe (PID: 1128)
- SetACLx64.exe (PID: 5812)
- SetACLx64.exe (PID: 2988)
- SetACLx64.exe (PID: 5592)
- SetACLx64.exe (PID: 4476)
- SetACLx64.exe (PID: 3980)
- SetACLx64.exe (PID: 4992)
- SetACLx64.exe (PID: 2192)
- SetACLx64.exe (PID: 2692)
- SetACLx64.exe (PID: 3980)
- SetACLx64.exe (PID: 6740)
- SetACLx64.exe (PID: 5700)
- SetACLx64.exe (PID: 7016)
- SetACLx64.exe (PID: 752)
- SetACLx64.exe (PID: 1992)
- SetACLx64.exe (PID: 2908)
- SetACLx64.exe (PID: 2936)
- SetACLx64.exe (PID: 3076)
- SetACLx64.exe (PID: 6716)
- SetACLx64.exe (PID: 1136)
- SetACLx64.exe (PID: 2956)
- SetACLx64.exe (PID: 5832)
- SetACLx64.exe (PID: 6876)
- SetACLx64.exe (PID: 6468)
- SetACLx64.exe (PID: 2132)
- SetACLx64.exe (PID: 4476)
- SetACLx64.exe (PID: 5832)
- SetACLx64.exe (PID: 7036)
- SetACLx64.exe (PID: 2932)
- SetACLx64.exe (PID: 6376)
- SetACLx64.exe (PID: 4788)
- SetACLx64.exe (PID: 1716)
- SetACLx64.exe (PID: 7052)
- SetACLx64.exe (PID: 6704)
- SetACLx64.exe (PID: 4340)
- SetACLx64.exe (PID: 1244)
- SetACLx64.exe (PID: 3392)
- SetACLx64.exe (PID: 2136)
- SetACLx64.exe (PID: 6220)
- SetACLx64.exe (PID: 1428)
- SetACLx64.exe (PID: 2132)
- SetACLx64.exe (PID: 6876)
- SetACLx64.exe (PID: 6292)
- SetACLx64.exe (PID: 2240)
- SetACLx64.exe (PID: 1128)
- SetACLx64.exe (PID: 2944)
- SetACLx64.exe (PID: 4044)
- SetACLx64.exe (PID: 1472)
- SetACLx64.exe (PID: 3124)
- SetACLx64.exe (PID: 2936)
- SetACLx64.exe (PID: 6716)
- SetACLx64.exe (PID: 4992)
- SetACLx64.exe (PID: 4356)
- SetACLx64.exe (PID: 788)
- SetACLx64.exe (PID: 4104)
- SetACLx64.exe (PID: 4196)
- SetACLx64.exe (PID: 5956)
- SetACLx64.exe (PID: 6484)
- SetACLx64.exe (PID: 736)
- SetACLx64.exe (PID: 6740)
- SetACLx64.exe (PID: 888)
Checks supported languages
- SetACLx64.exe (PID: 4476)
- SetACLx64.exe (PID: 2132)
- SetACLx64.exe (PID: 6420)
- SetACLx64.exe (PID: 4340)
- SetACLx64.exe (PID: 2824)
- SetACLx64.exe (PID: 4772)
- SetACLx64.exe (PID: 1296)
- SetACLx64.exe (PID: 752)
- SetACLx64.exe (PID: 396)
- SetACLx64.exe (PID: 4340)
- SetACLx64.exe (PID: 5744)
- SetACLx64.exe (PID: 4376)
- SetACLx64.exe (PID: 5832)
- SetACLx64.exe (PID: 6316)
- SetACLx64.exe (PID: 2824)
- SetACLx64.exe (PID: 2136)
- SetACLx64.exe (PID: 812)
- SetACLx64.exe (PID: 1128)
- SetACLx64.exe (PID: 3980)
- SetACLx64.exe (PID: 736)
- SetACLx64.exe (PID: 5812)
- SetACLx64.exe (PID: 2988)
- SetACLx64.exe (PID: 5700)
- SetACLx64.exe (PID: 5592)
- SetACLx64.exe (PID: 2088)
- SetACLx64.exe (PID: 4476)
- SetACLx64.exe (PID: 2192)
- SetACLx64.exe (PID: 2692)
- SetACLx64.exe (PID: 3980)
- SetACLx64.exe (PID: 1136)
- SetACLx64.exe (PID: 6740)
- SetACLx64.exe (PID: 7016)
- SetACLx64.exe (PID: 752)
- SetACLx64.exe (PID: 4992)
- SetACLx64.exe (PID: 2908)
- SetACLx64.exe (PID: 5832)
- SetACLx64.exe (PID: 3076)
- SetACLx64.exe (PID: 6716)
- SetACLx64.exe (PID: 2956)
- SetACLx64.exe (PID: 1992)
- SetACLx64.exe (PID: 2936)
- SetACLx64.exe (PID: 6876)
- SetACLx64.exe (PID: 2132)
- SetACLx64.exe (PID: 5832)
- SetACLx64.exe (PID: 7036)
- SetACLx64.exe (PID: 4476)
- SetACLx64.exe (PID: 6468)
- SetACLx64.exe (PID: 2932)
- SetACLx64.exe (PID: 6376)
- SetACLx64.exe (PID: 4788)
- SetACLx64.exe (PID: 1716)
- SetACLx64.exe (PID: 6292)
- SetACLx64.exe (PID: 6876)
- SetACLx64.exe (PID: 7052)
- SetACLx64.exe (PID: 6704)
- SetACLx64.exe (PID: 2132)
- SetACLx64.exe (PID: 2240)
- SetACLx64.exe (PID: 4340)
- SetACLx64.exe (PID: 2944)
- SetACLx64.exe (PID: 3392)
- SetACLx64.exe (PID: 4044)
- SetACLx64.exe (PID: 1244)
- SetACLx64.exe (PID: 1128)
- SetACLx64.exe (PID: 2136)
- SetACLx64.exe (PID: 788)
- SetACLx64.exe (PID: 3124)
- SetACLx64.exe (PID: 6716)
- SetACLx64.exe (PID: 4992)
- SetACLx64.exe (PID: 2936)
- SetACLx64.exe (PID: 6220)
- SetACLx64.exe (PID: 4356)
- SetACLx64.exe (PID: 1472)
- SetACLx64.exe (PID: 1428)
- SetACLx64.exe (PID: 5956)
- SetACLx64.exe (PID: 6484)
- SetACLx64.exe (PID: 4196)
- SetACLx64.exe (PID: 736)
- SetACLx64.exe (PID: 6740)
- SetACLx64.exe (PID: 4104)
- SetACLx64.exe (PID: 888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
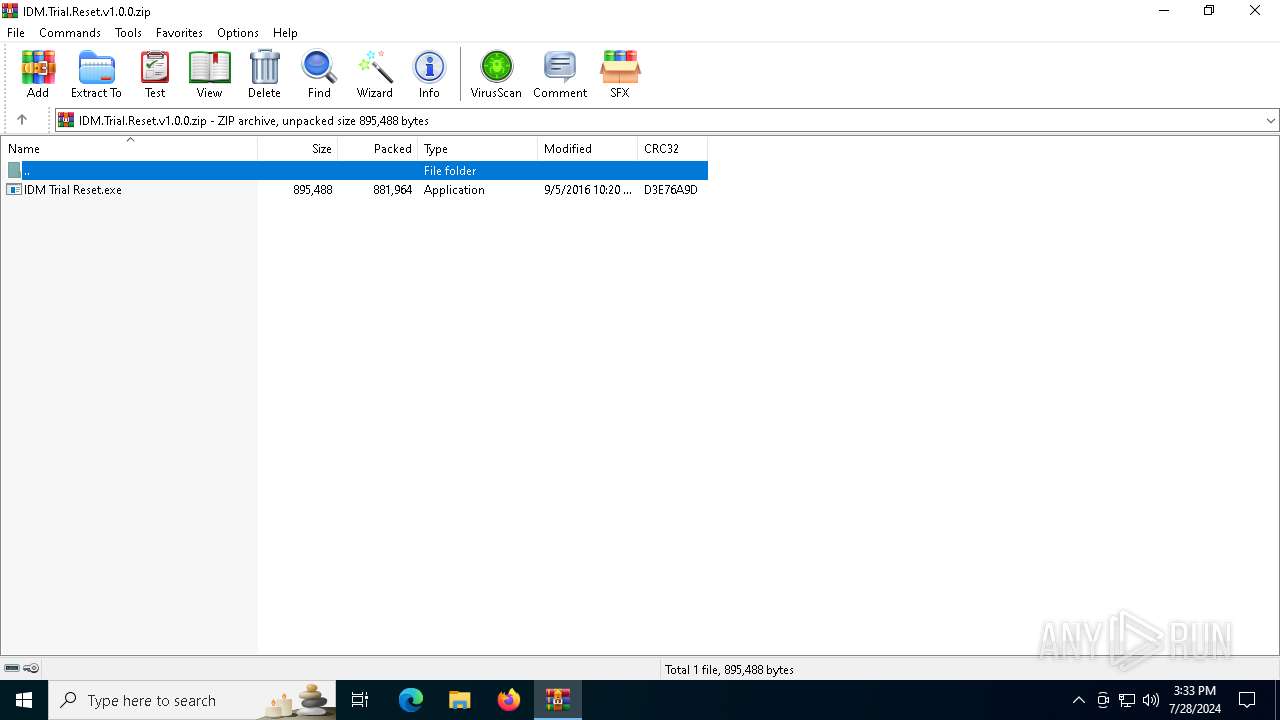
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:09:06 05:20:26 |
| ZipCRC: | 0xd3e76a9d |
| ZipCompressedSize: | 881964 |
| ZipUncompressedSize: | 895488 |
| ZipFileName: | IDM Trial Reset.exe |
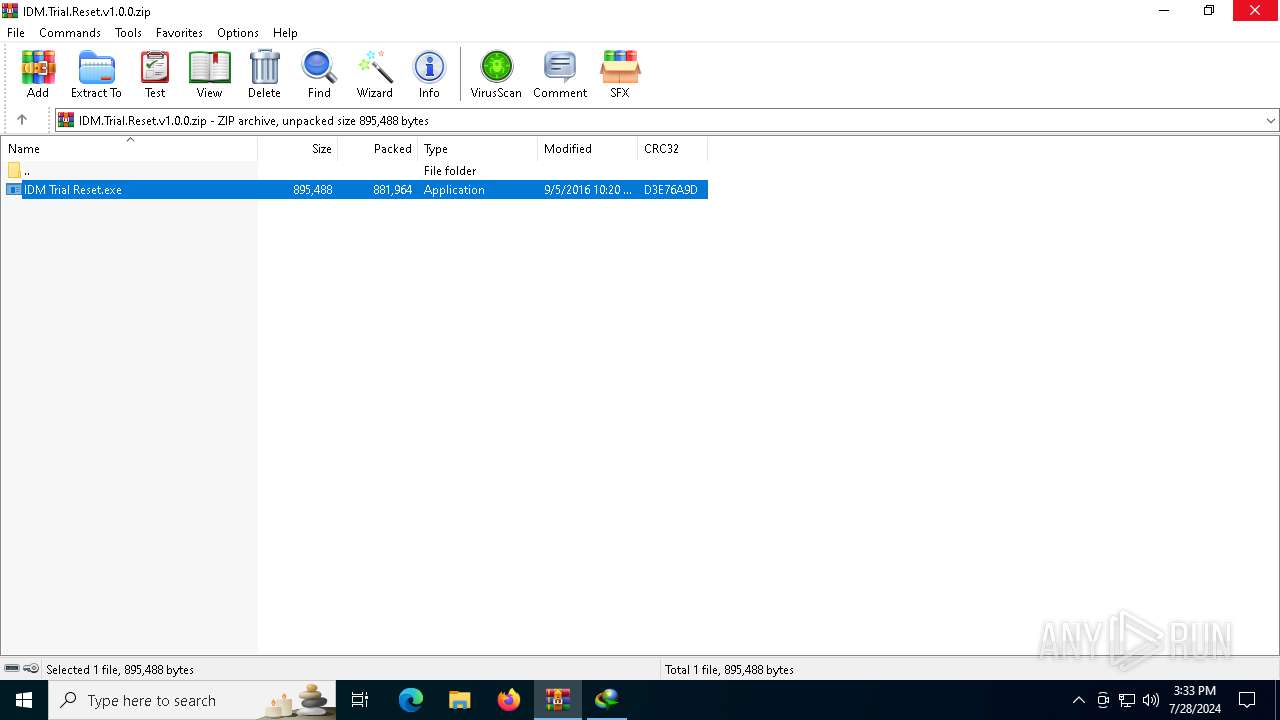
Total processes
324
Monitored processes
183
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\WINDOWS\system32\cmd.exe" /c findstr /N . C:\Users\admin\AppData\Local\Temp\reg_query.tmp | findstr /b -1: | C:\Windows\SysWOW64\cmd.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKLM\Software\Classes\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SetACLx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 484 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SetACLx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKCU\Software\Classes\CLSID\{6DDF00DB-1234-46EC-8356-27E7B2051192} -ot reg -actn ace -ace "n:everyone;p:full" -actn setprot -op "dacl:p_nc;sacl:p_nc" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 12 Version: 3.0.6.0 Modules
| |||||||||||||||
| 736 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKCU\Software\Classes\Wow6432Node\CLSID\{5ED60779-4DE2-4E07-B862-974CA4FF2E9C} -ot reg -actn setowner -ownr "n:S-1-0-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKCU\Software\Classes\Wow6432Node\CLSID\{6DDF00DB-1234-46EC-8356-27E7B2051192} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKLM\Software\Classes\Wow6432Node\CLSID\{7B8E9164-324D-4A2E-A46D-0165FB2000EC} -ot reg -actn ace -ace "n:everyone;p:full" -actn setprot -op "dacl:p_nc;sacl:p_nc" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 12 Version: 3.0.6.0 Modules
| |||||||||||||||
| 788 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKCU\Software\Classes\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn setowner -ownr "n:S-1-0-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
| 812 | "C:\Users\admin\AppData\Local\Temp\SetACLx64.exe" -on HKCU\Software\Classes\Wow6432Node\CLSID\{D5B91409-A8CA-4973-9A0B-59F713D25671} -ot reg -actn setowner -ownr "n:S-1-1-0" -silent | C:\Users\admin\AppData\Local\Temp\SetACLx64.exe | — | IDM Trial Reset.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: MEDIUM Description: SetACL 3 Exit code: 5 Version: 3.0.6.0 Modules
| |||||||||||||||
Total events
35 172
Read events
35 134
Write events
32
Delete events
6
Modification events
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | crc |
Value: 70 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F0000000000000000000000000000000000000000000DA030E0000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (4544) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000B2020F000000000000000000180000002A00000000000000000000000000000002000000 | |||
Executable files
3
Suspicious files
9
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\idm_trial.reg | text | |
MD5:237962E36948F3D0C9EC42EFA289AC52 | SHA256:40AD93CF424EEE41A0877B11ACB92F7F12D58AB3AA6FA6D64D92CFBBE11695A2 | |||
| 4544 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4544.11905\IDM Trial Reset.exe | executable | |
MD5:064F82094AE6A6E22C28A6F1EF868A26 | SHA256:A2D2B22CD0D5628976EB5996A8B20F3B5AC468907910DBC3F826F1069D435587 | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\idm_reset.reg | text | |
MD5:17EBF21FCCAC9756EAB46EB64BA6C029 | SHA256:290A3F67BBBDBD5C1101E90921475C2B95E97DC69A3141412FBAC79FCADD3EE8 | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\aut197F.tmp | binary | |
MD5:715EC543E4A386475E2105954DAD0929 | SHA256:C28E0CB287457A5B00BF34983D00256E263C00231B5CBB0F8BEF4233C47F7D55 | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\aut192F.tmp | binary | |
MD5:90585D687B4426794D2DED4DD0E5FBE2 | SHA256:84DE96E94FEAFB174FD2BF79007F27BC8B43C462FB7B4A1C5137D8BA0EEB8840 | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\aut193F.tmp | binary | |
MD5:2EBB8A2070729BC3CAE5B5E1CC27C963 | SHA256:B951A1F1EC92F71EEF08E59988267CC19BF35286B90A2CBE50C4B1062C2FD0AC | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\aut192E.tmp | binary | |
MD5:E68C65421712C99C0FA515EB087B412B | SHA256:2CE685037E366A0FD2FF1827C20F1866BCBE23D646DFCE30A459B8FF3C1B4F2E | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\SetACLx32.exe | executable | |
MD5:451AE03D3C92777F09840CA56F08AB62 | SHA256:D5E779D151772504662E8226EB4107330FFA7A51209EEE42B6D5883D99100BA9 | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\idm_reg.reg | text | |
MD5:3DEDFE7770A57CA2BCB76D01D1756EE6 | SHA256:832134EB65B2A91BE5B6584B48AB69B4B7CE9B6228EA4738F6D1B7A8A0E1915E | |||
| 2252 | IDM Trial Reset.exe | C:\Users\admin\AppData\Local\Temp\aut18FE.tmp | binary | |
MD5:D71743C02DF05822F49FF9E232DE76F0 | SHA256:62AAECFD2ECA11B635DDC0AC246F9EFC991A56CAE43E009EABA9367BB287AD89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
49
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2252 | IDM Trial Reset.exe | GET | 301 | 104.20.3.235:80 | http://pastebin.com/raw/uYr0cstV | unknown | — | — | shared |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2252 | IDM Trial Reset.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2252 | IDM Trial Reset.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6640 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
996 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6012 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4820 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4128 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5368 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
pastebin.com |
| shared |
c.pki.goog |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2252 | IDM Trial Reset.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
2284 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |