| URL: | https://www.bing.com/ck/a?!&&p=c92e0a5758a2ec24JmltdHM9MTcwMjU5ODQwMCZpZ3VpZD0zMzAyYWMyNC0xMTFiLTZlNWYtMDVkMy1iZmMwMTAzMjZmNzgmaW5zaWQ9NTEzOQ&ptn=3&ver=2&hsh=3&fclid=3302ac24-111b-6e5f-05d3-bfc010326f78&psq=malwarebytes+crack+keygen&u=a1aHR0cHM6Ly9hZHZhbnRhZ2Vnb29kc2l0ZTI4MS53ZWVibHkuY29tL21hbHdhcmVieXRlcy1hbnRpLW1hbHdhcmUtbGlmZXRpbWUtbGljZW5zZS5odG1s&ntb=1 |
| Full analysis: | https://app.any.run/tasks/111fee5c-459a-476d-b7e9-836ac75423ab |
| Verdict: | Malicious activity |
| Analysis date: | December 16, 2023, 00:49:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3CF5B1E357BE037DA356DEF357E8B897 |
| SHA1: | B215C8D33303B52CCD23743CB007488CAE3F33AC |
| SHA256: | 3729D9C2E9B26719ACB3B797141F0DB177EEF2CBA423F501739BA614D293E148 |
| SSDEEP: | 6:2OLsRKrPwSQUOfOiM/DAroDfELztWDU6isyklEb47W/nRrcllbwDVXHtKtHGyktL:2CLi0AroDctWIOEU7W+kHtolkF |
MALICIOUS
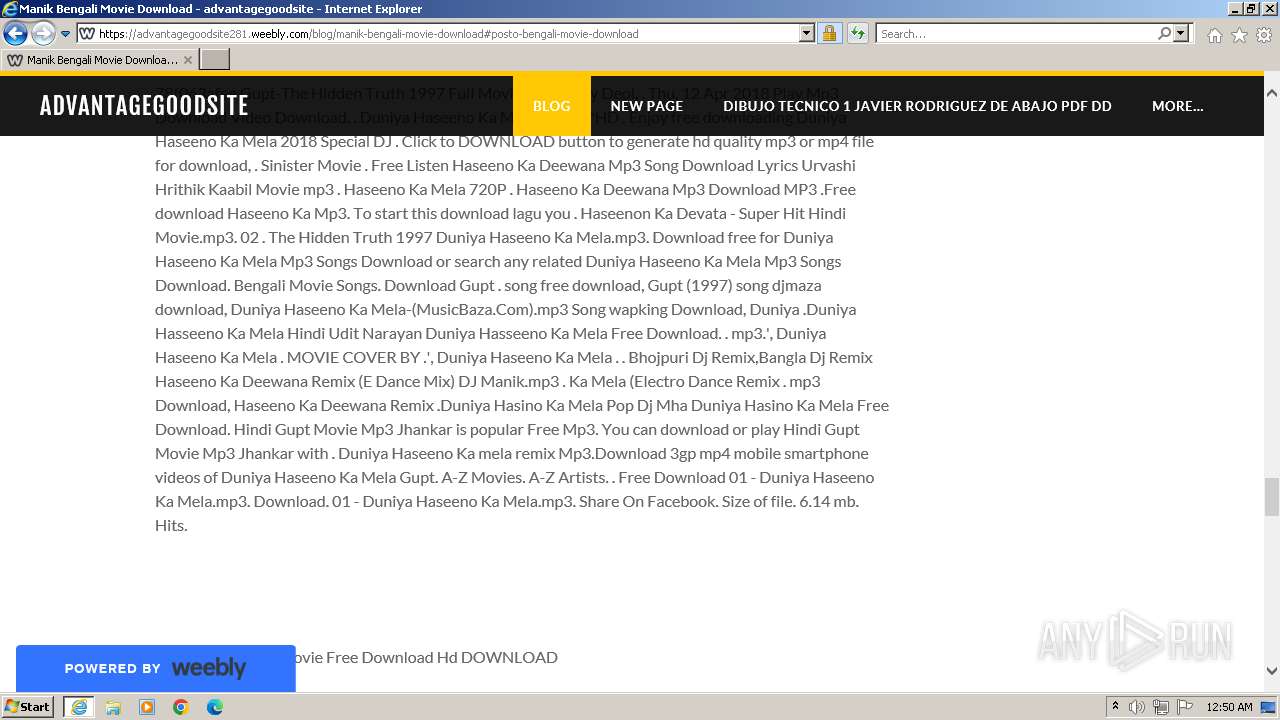
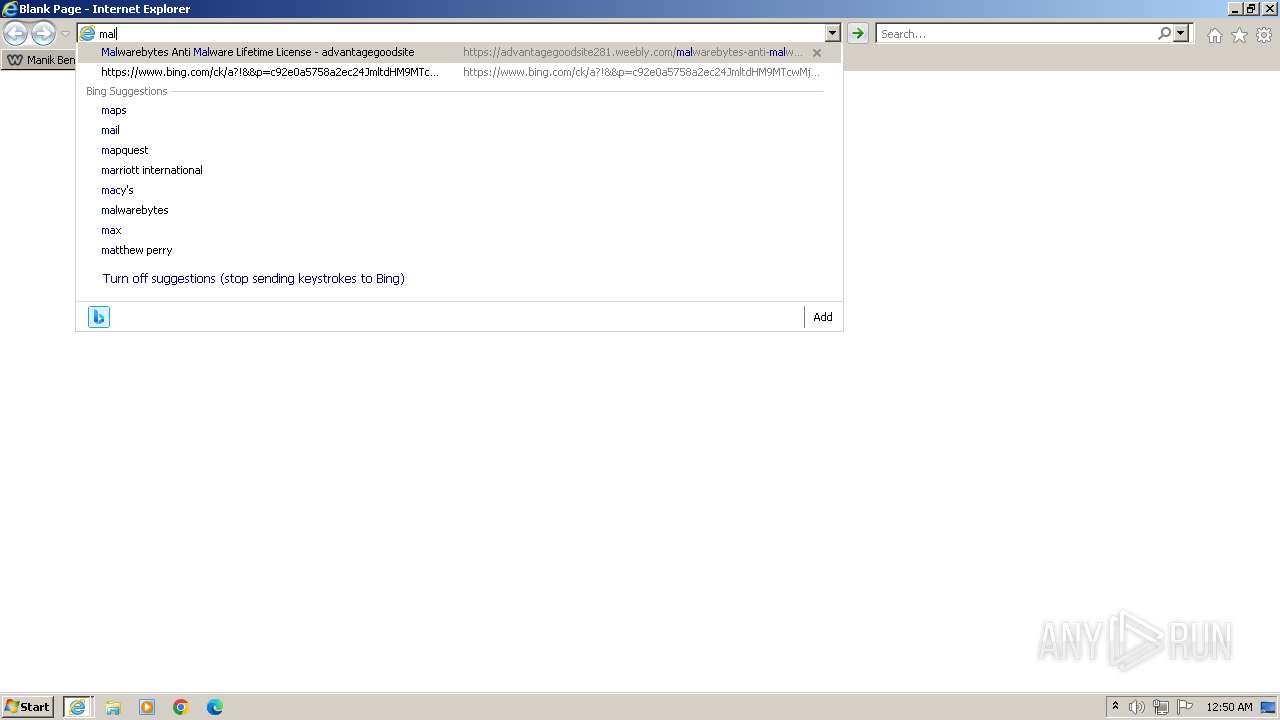
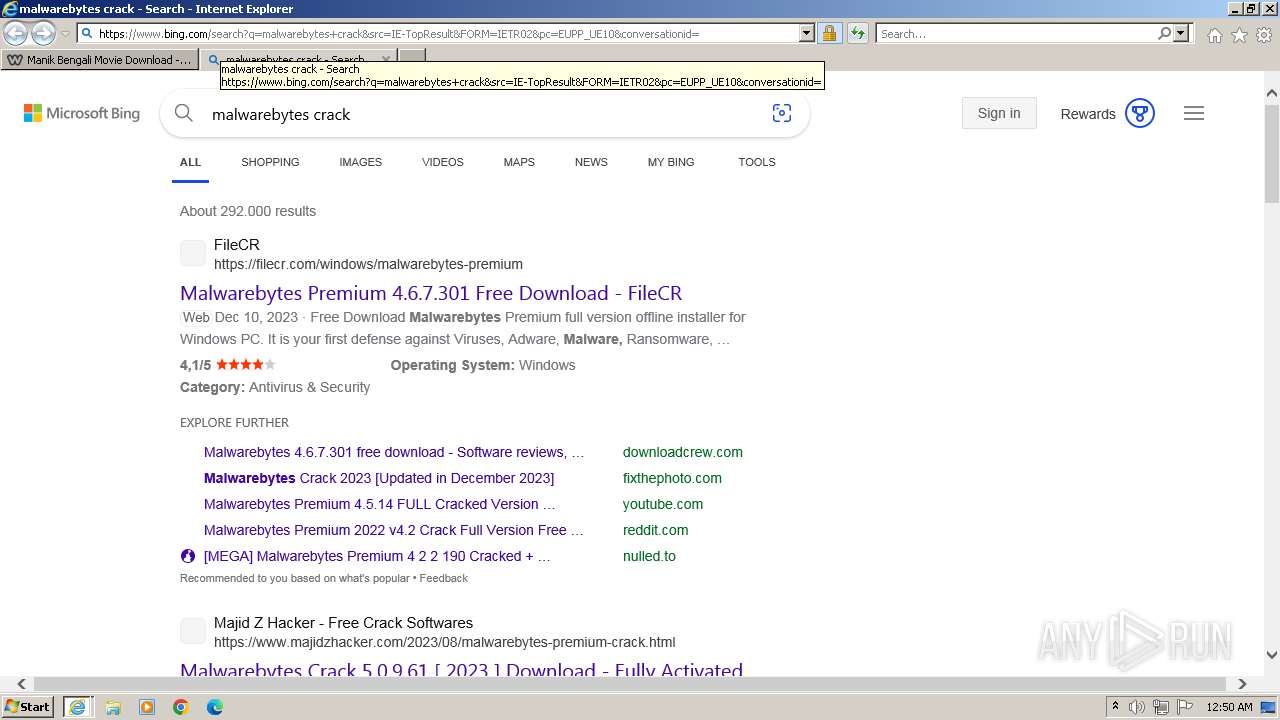
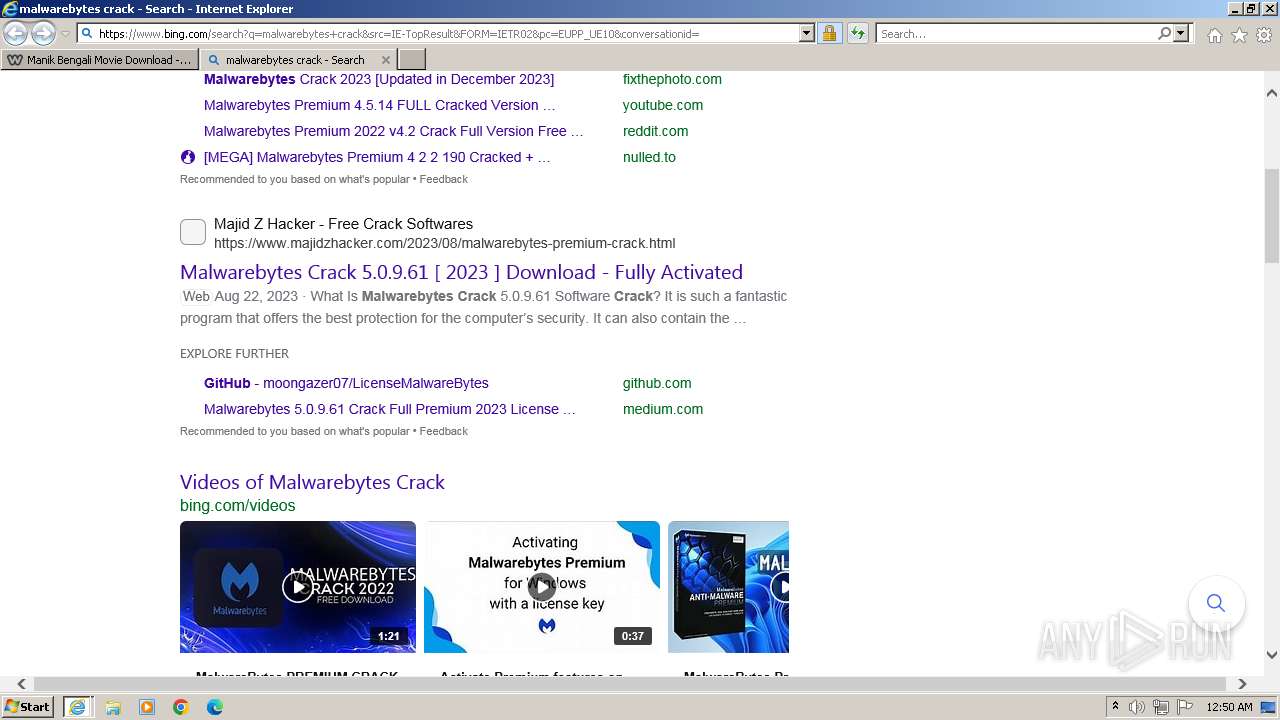
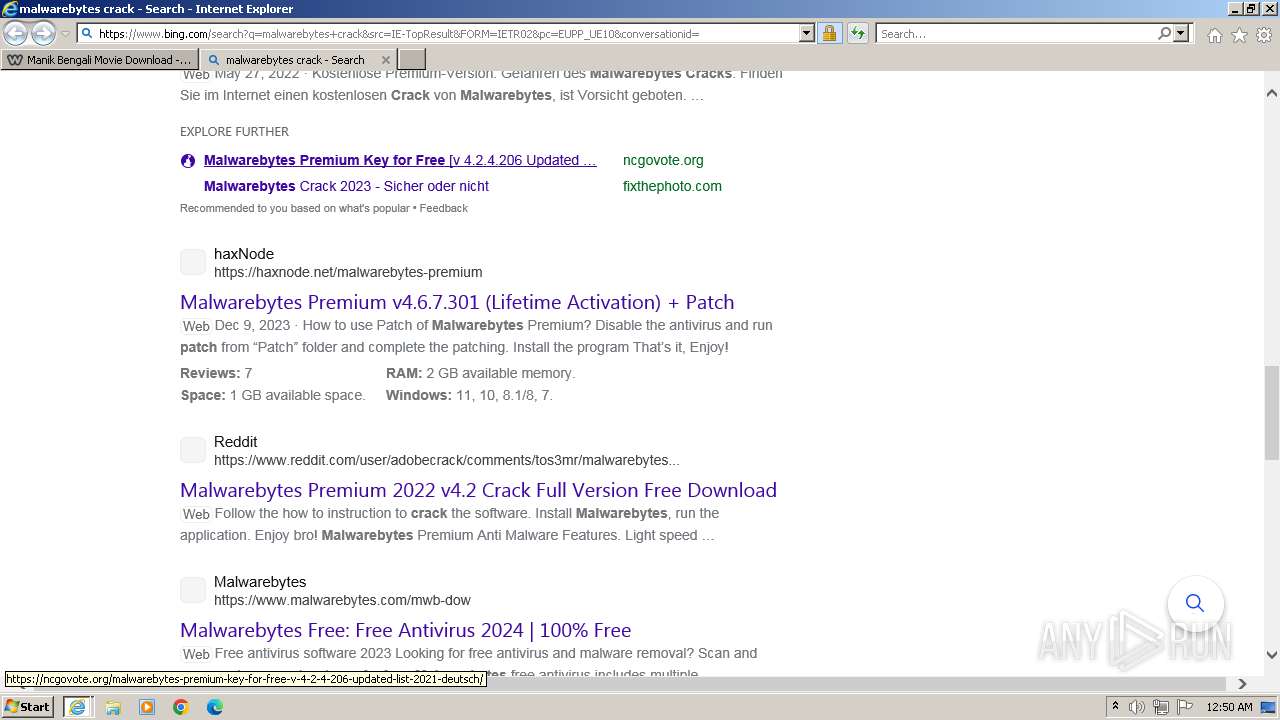
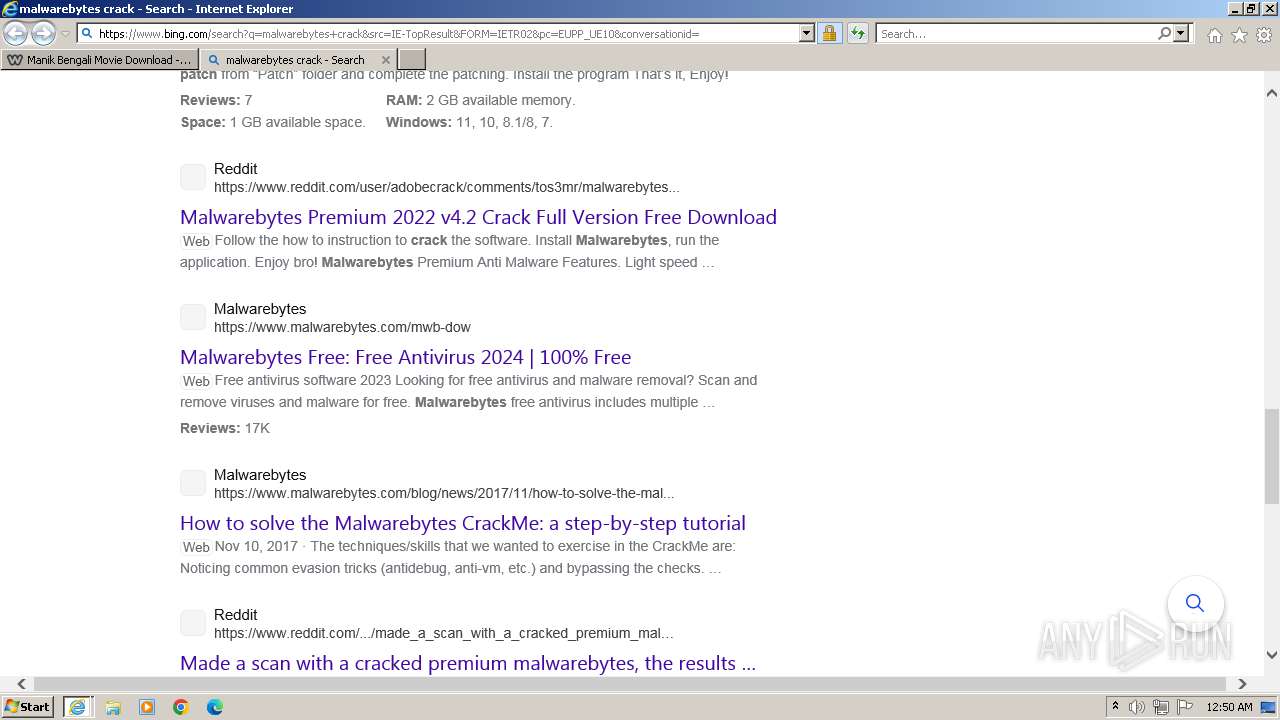
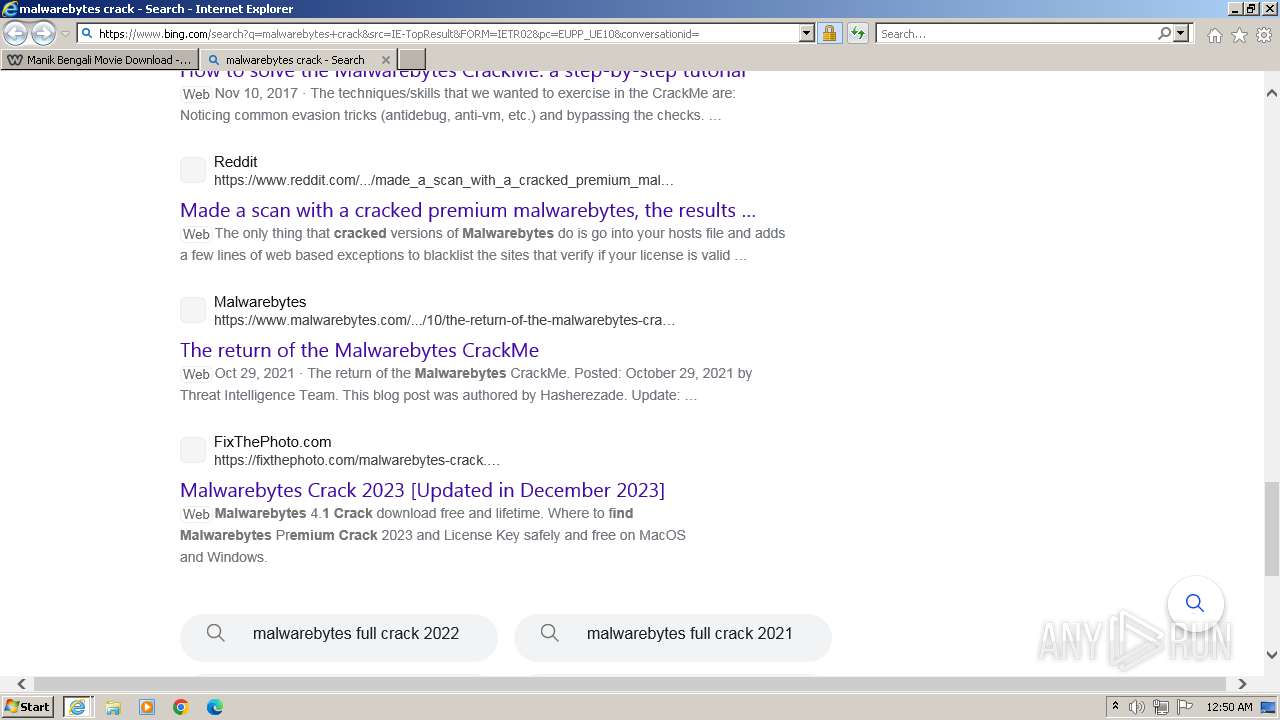
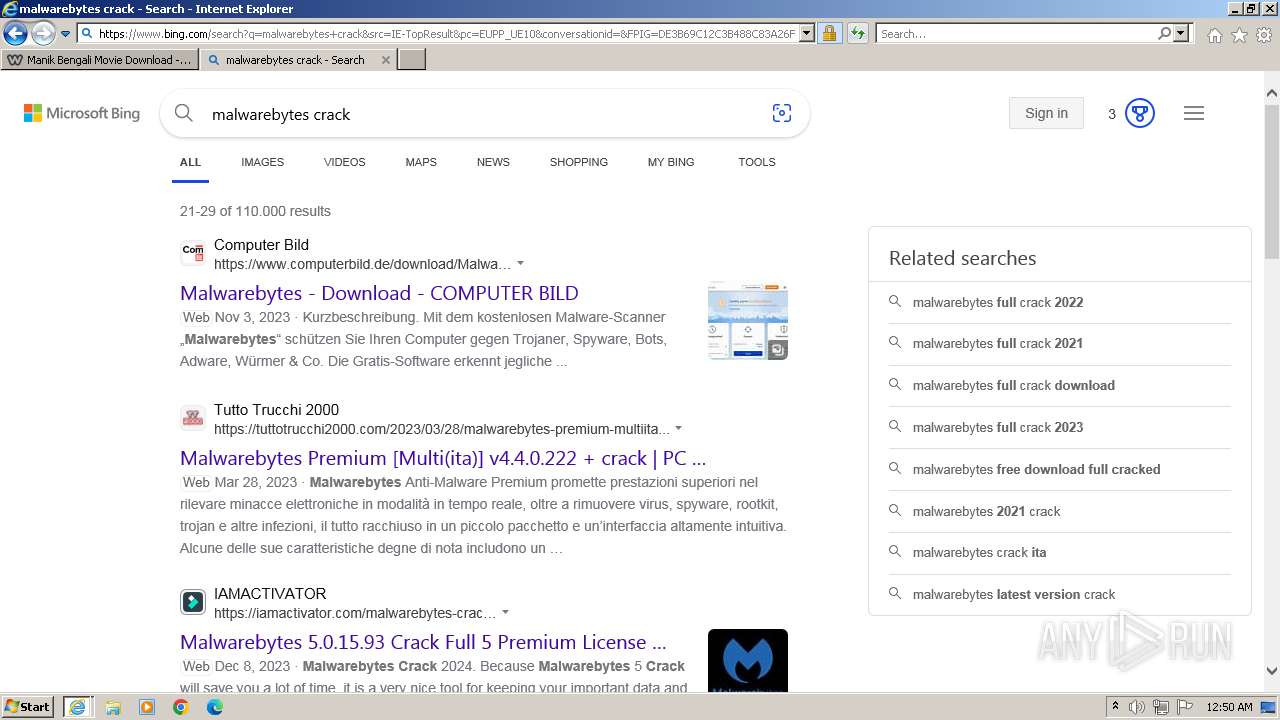
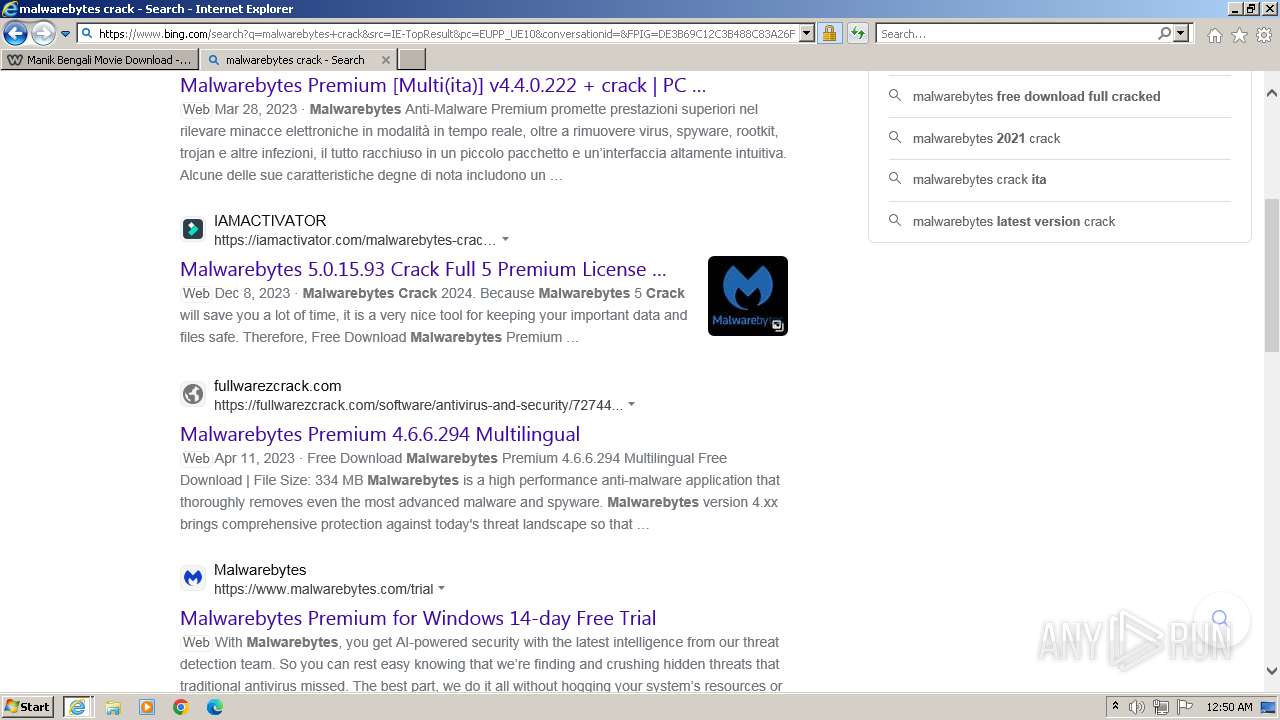
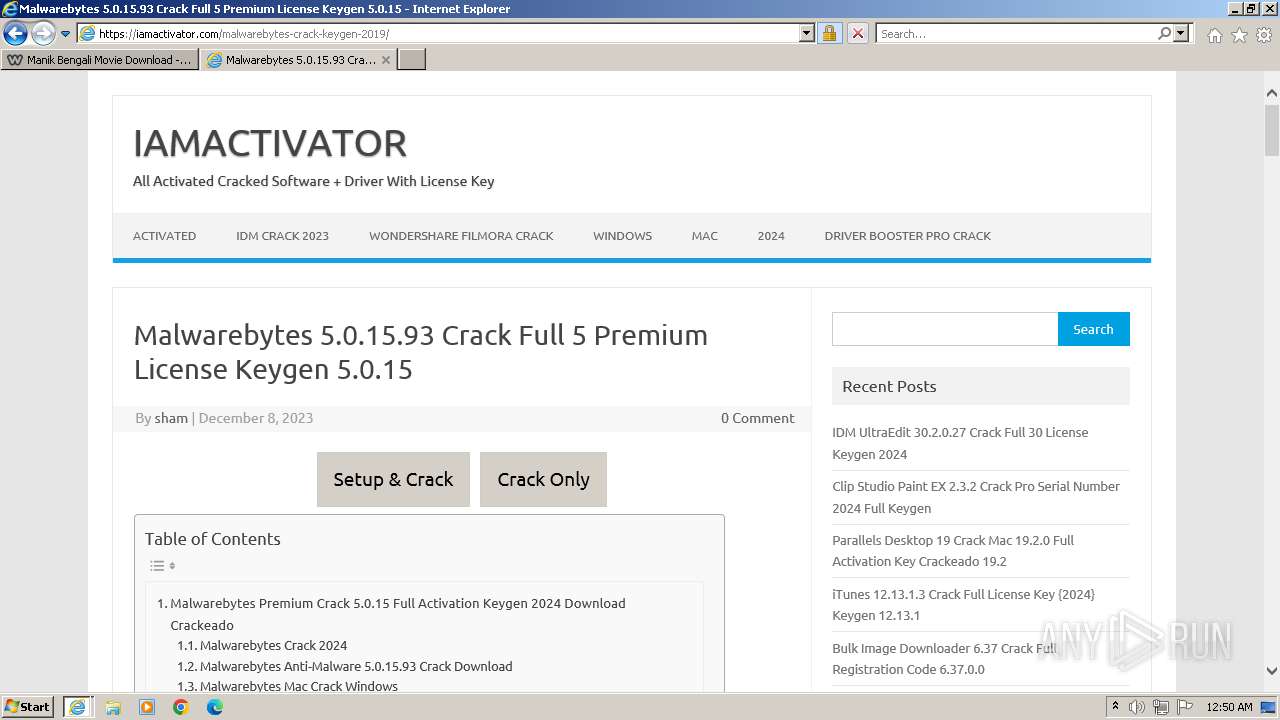
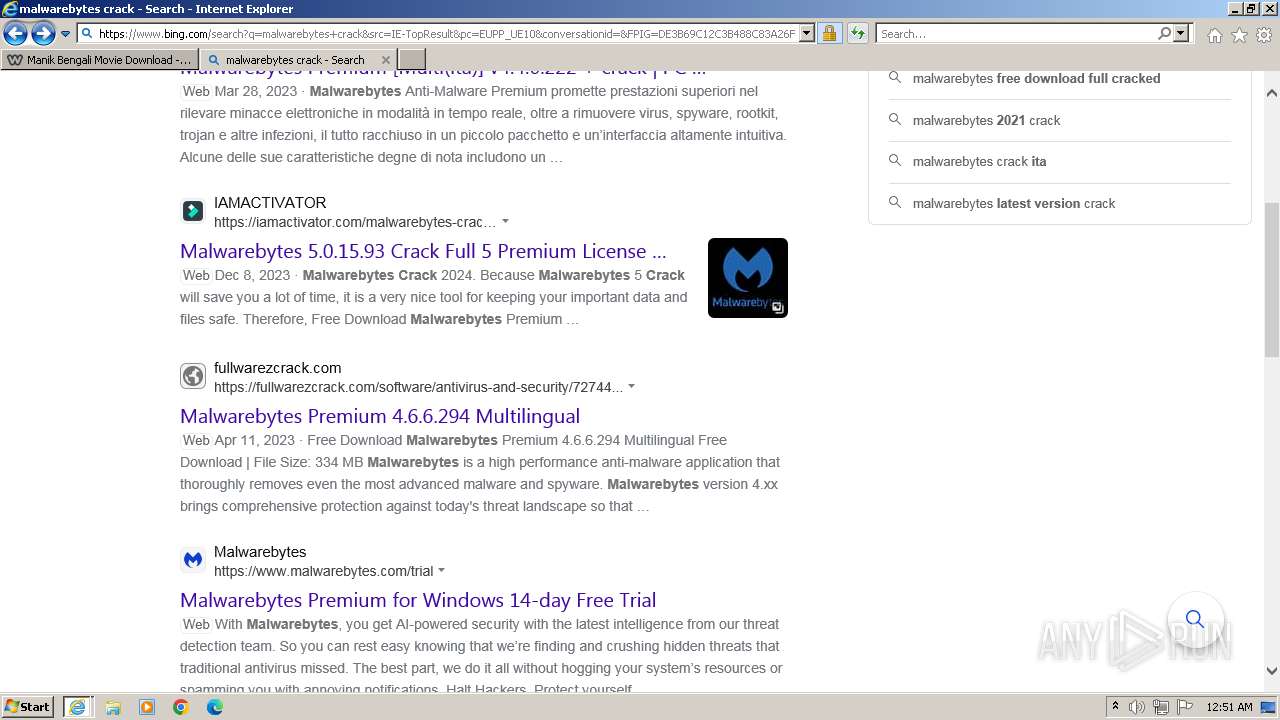
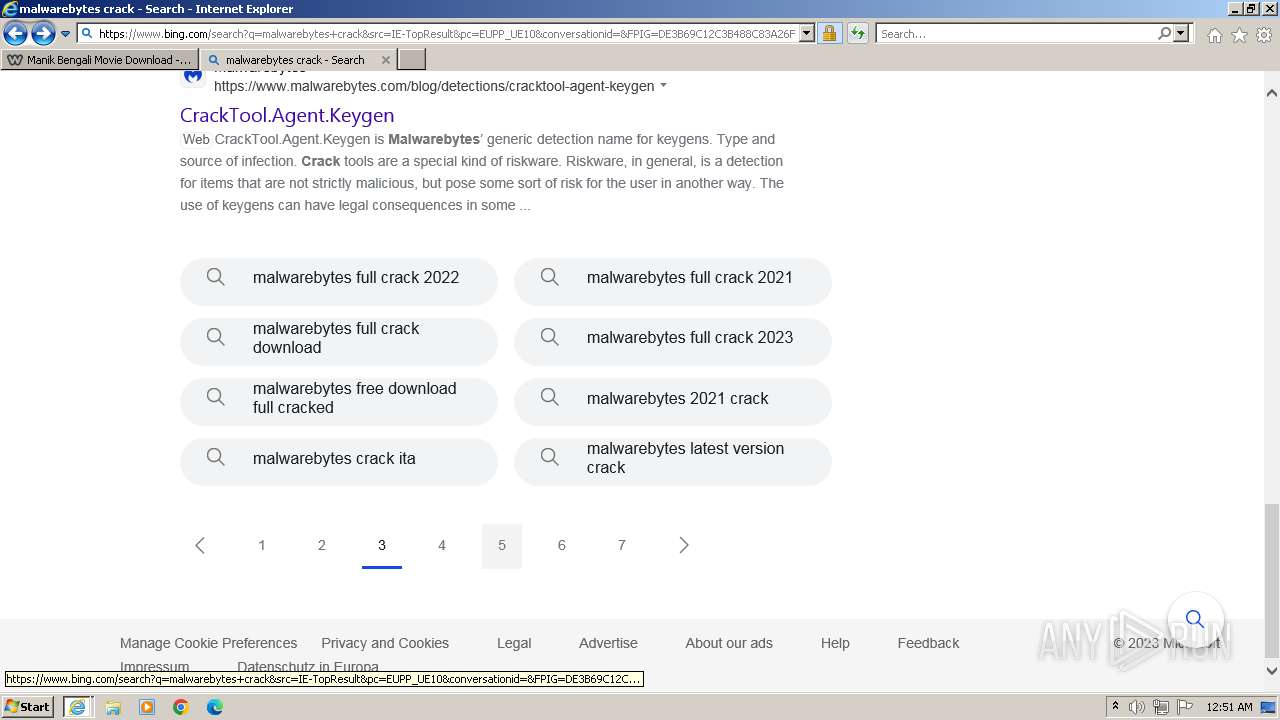
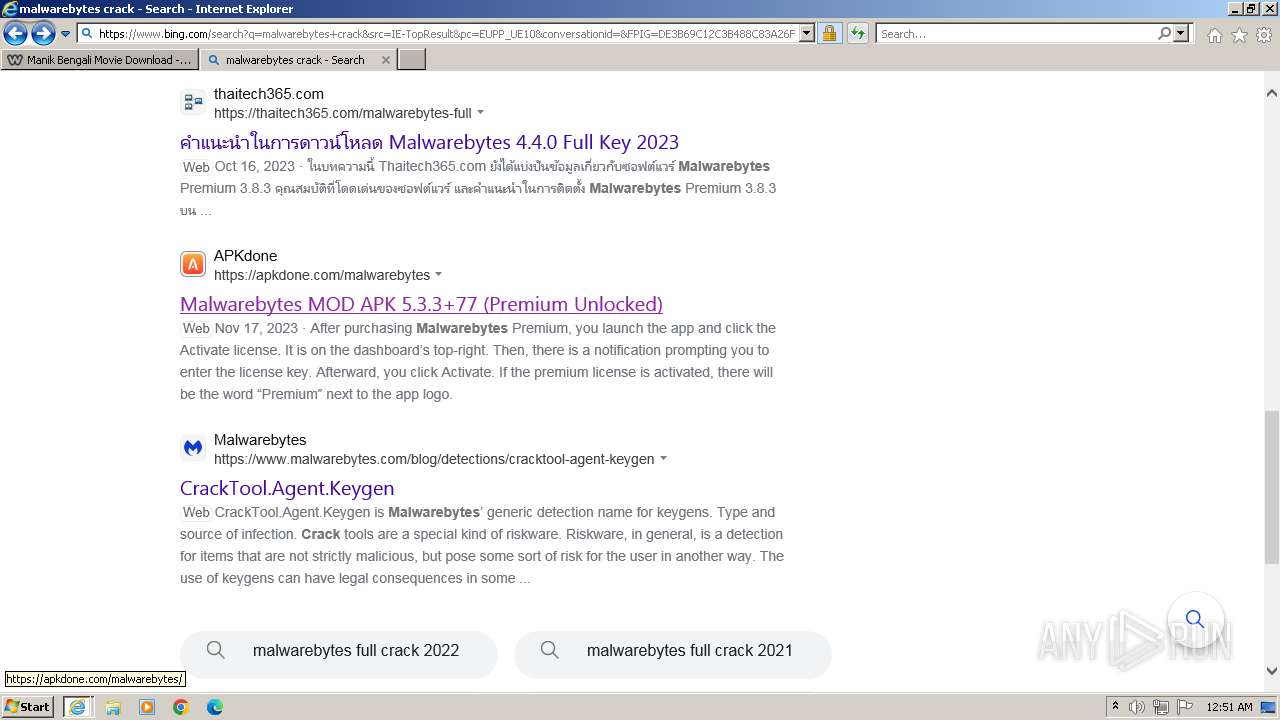
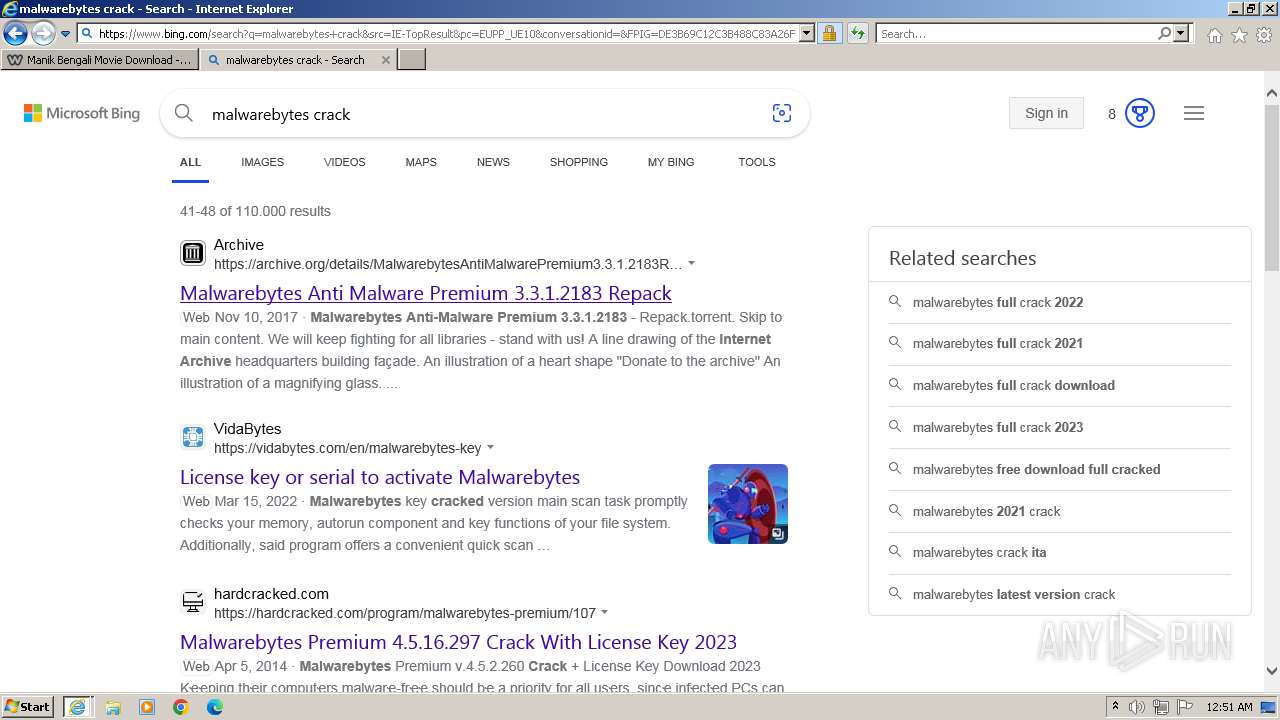
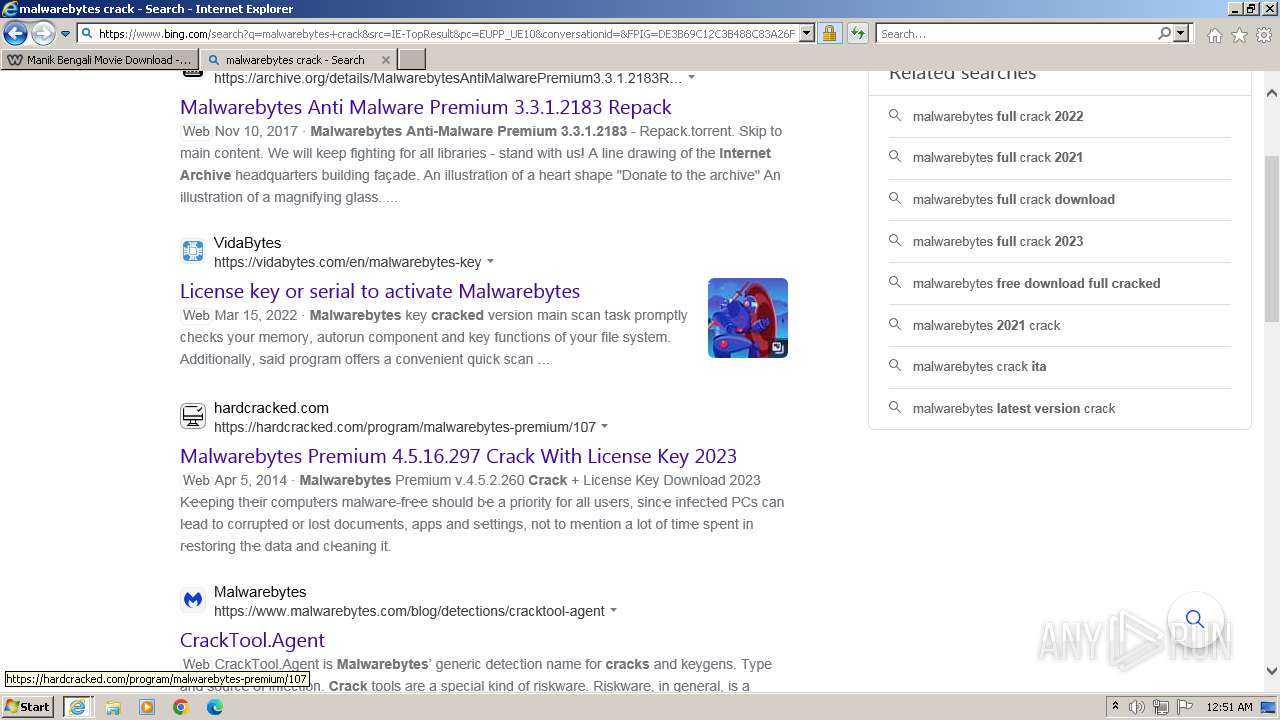
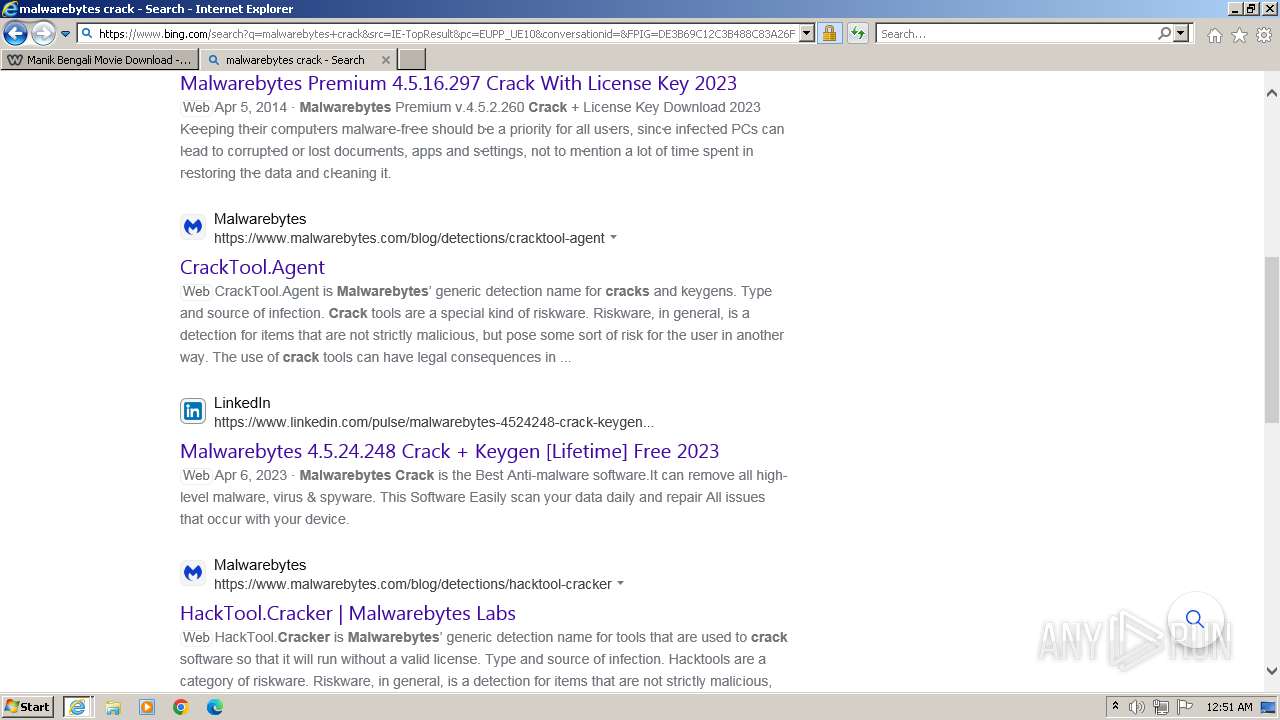
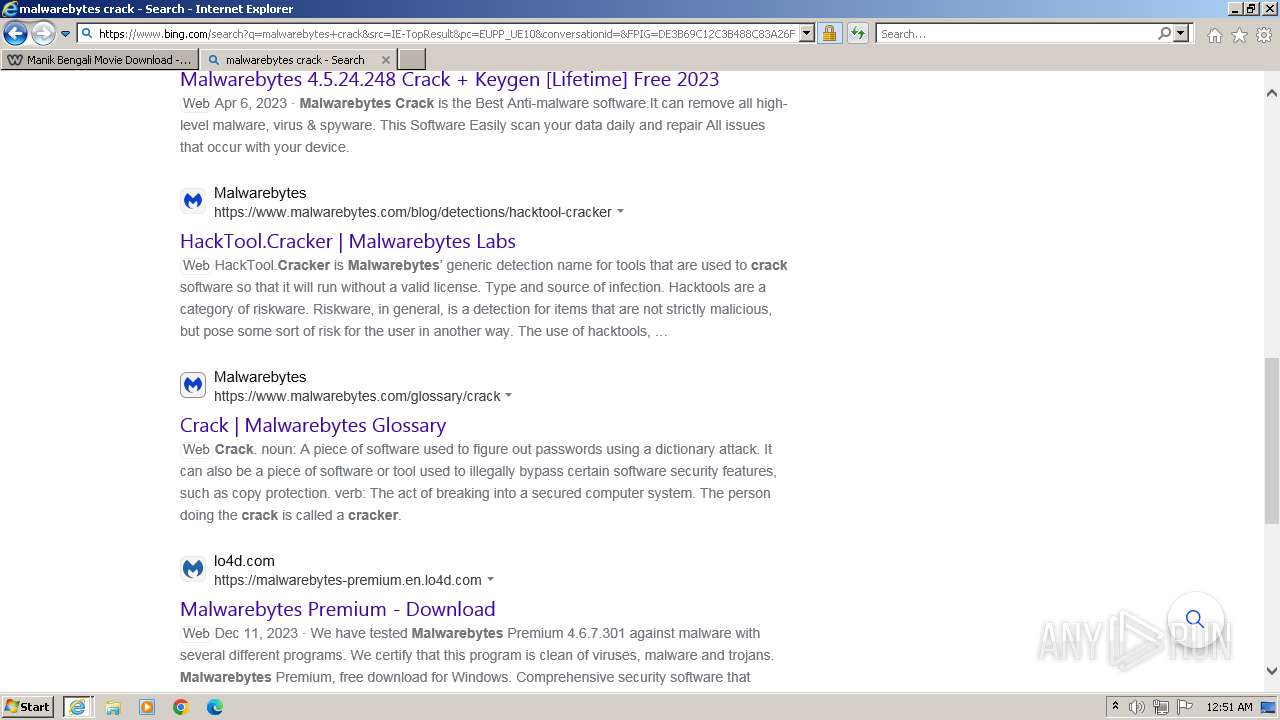
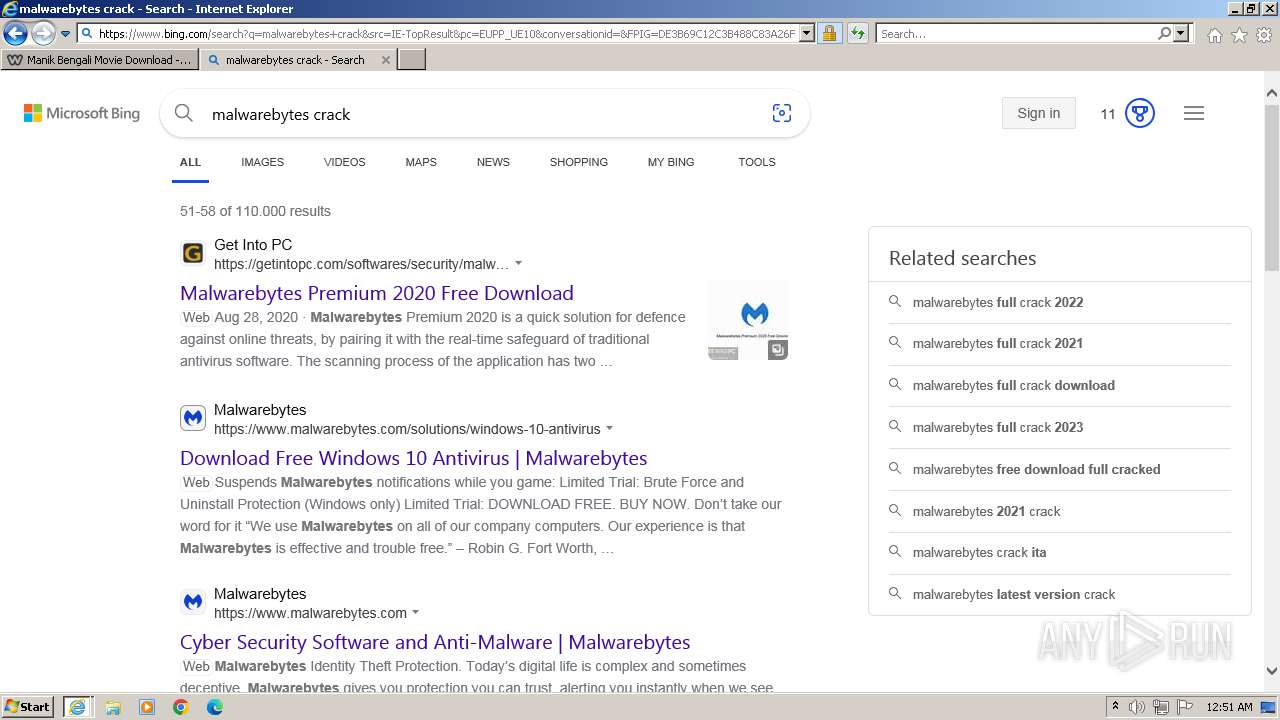
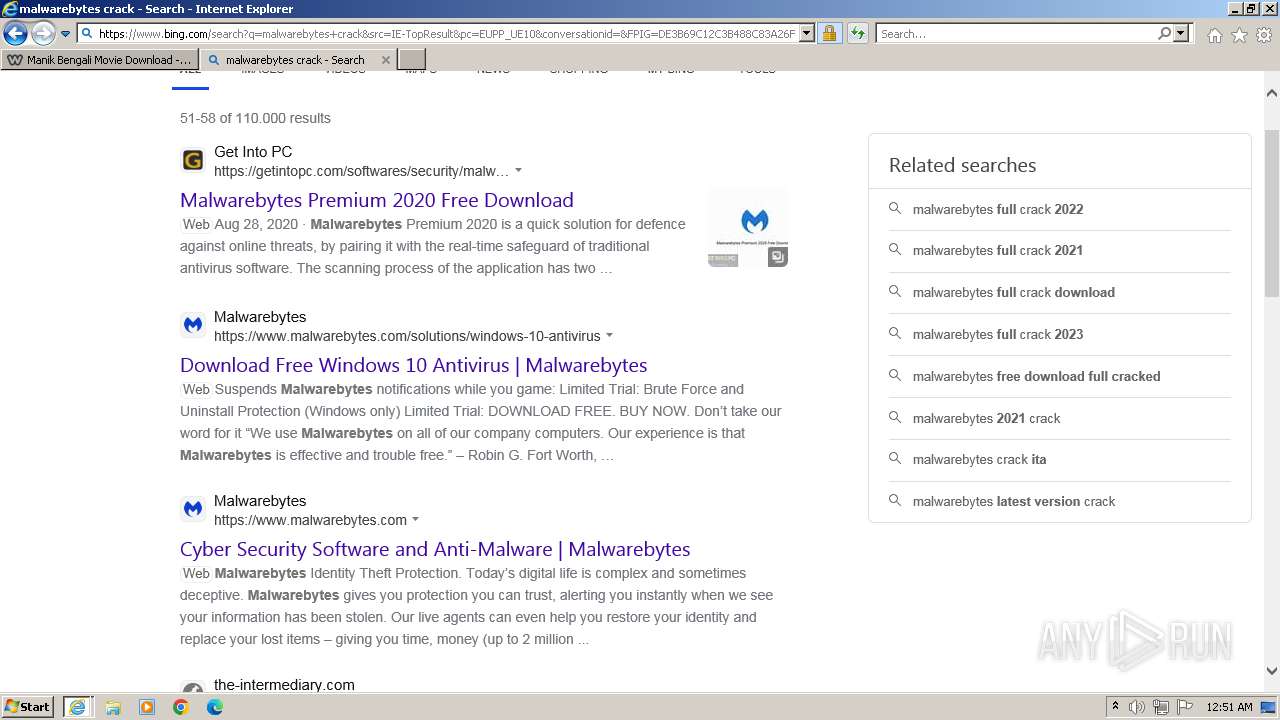
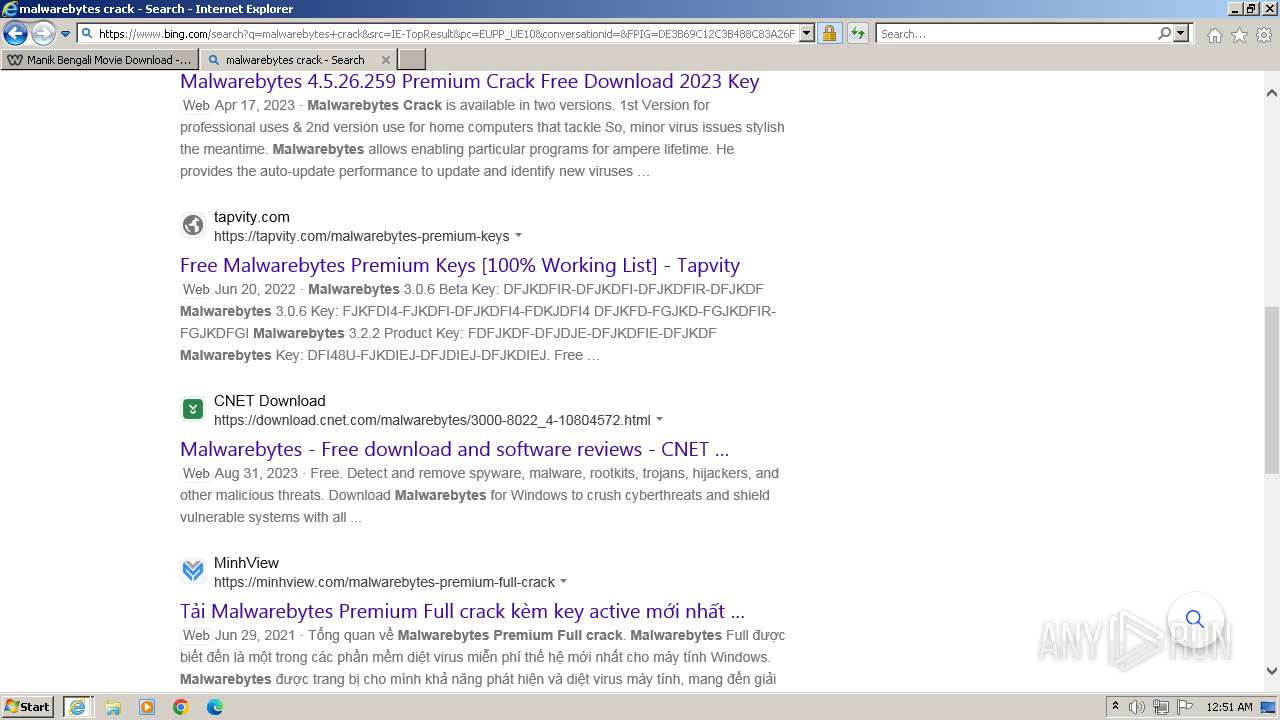
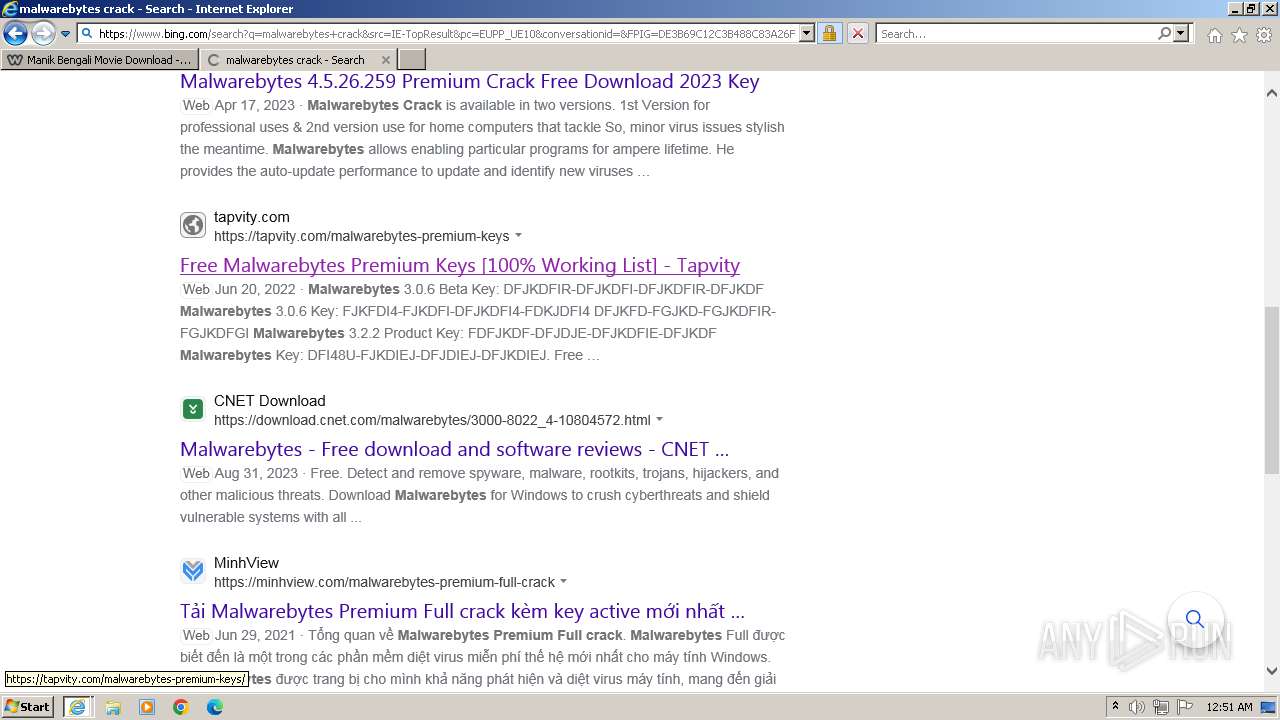
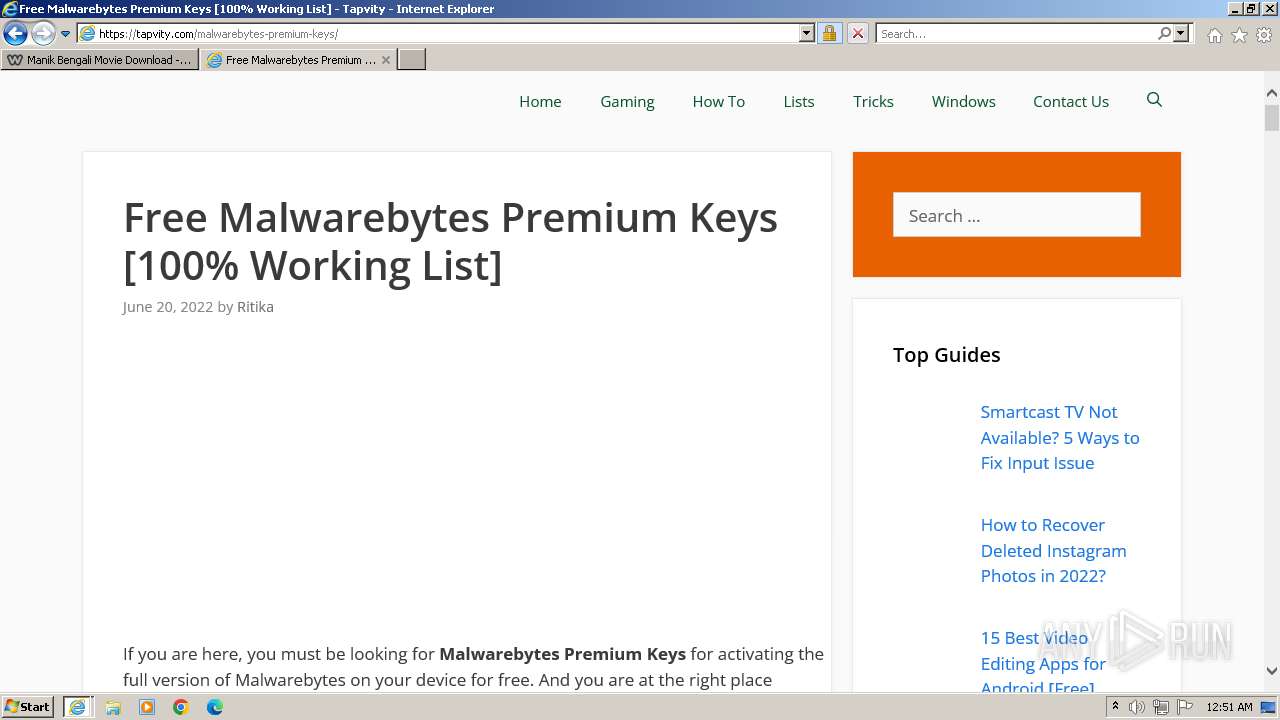
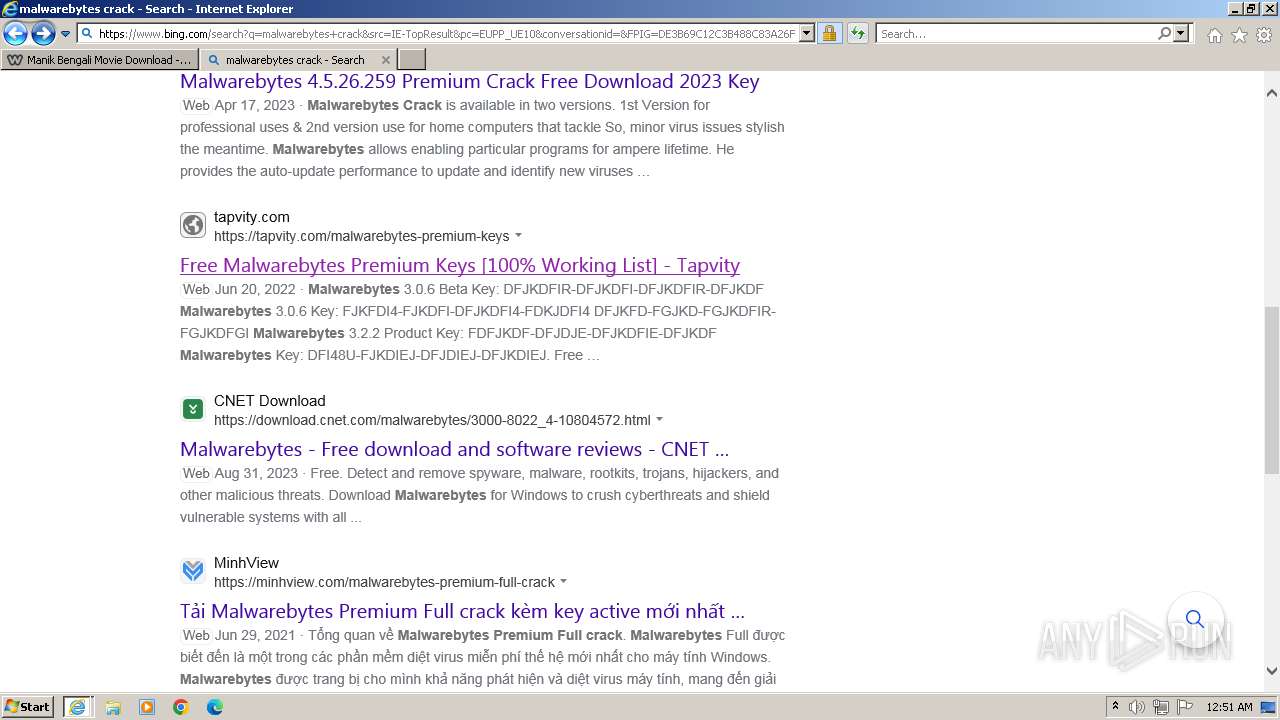
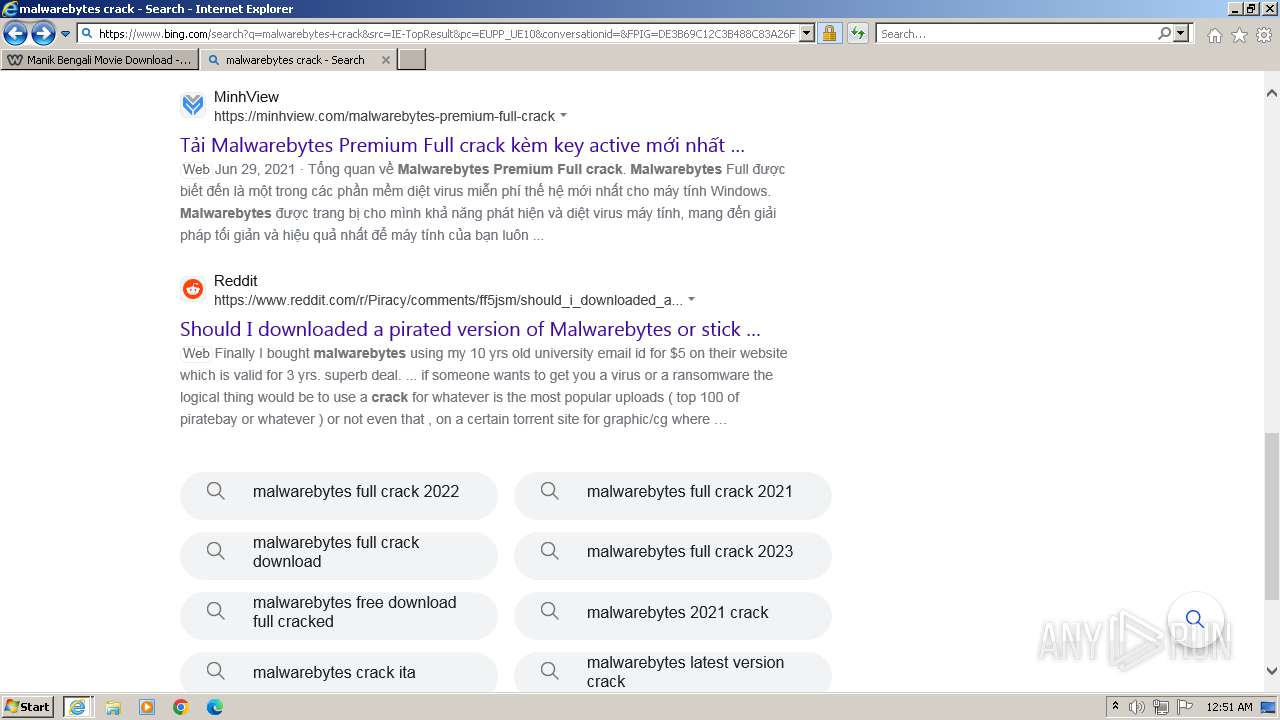
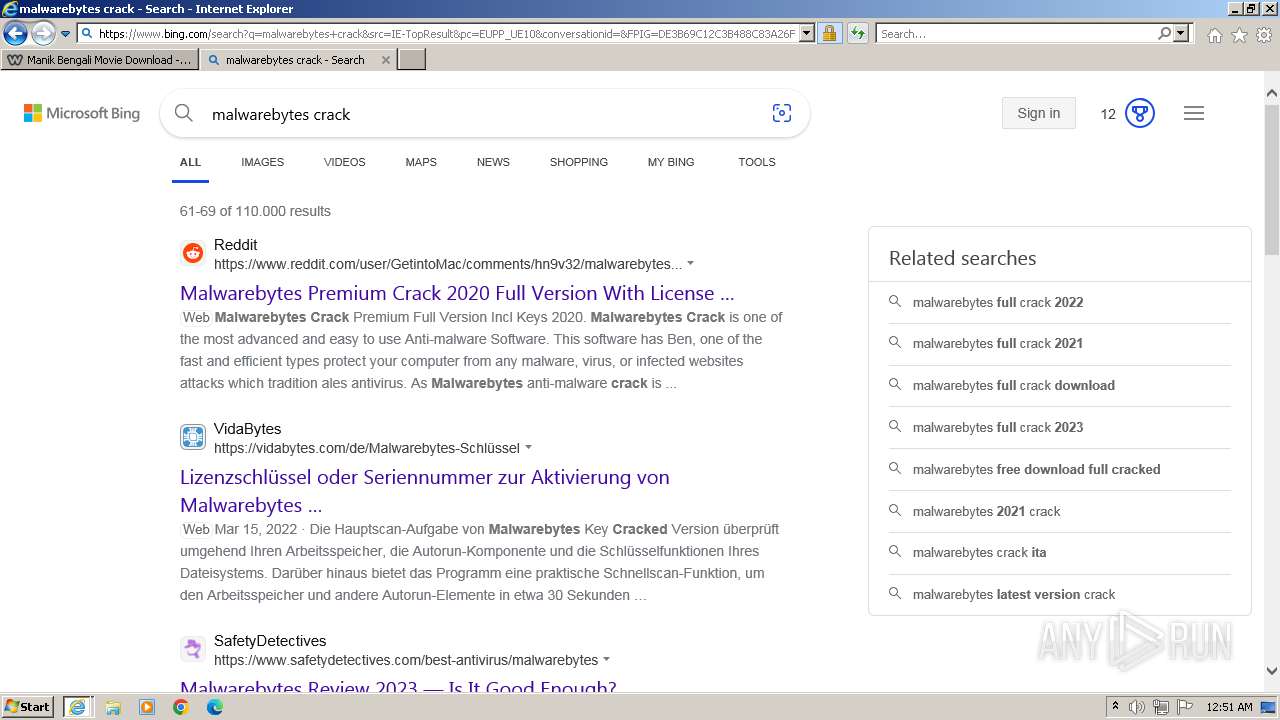
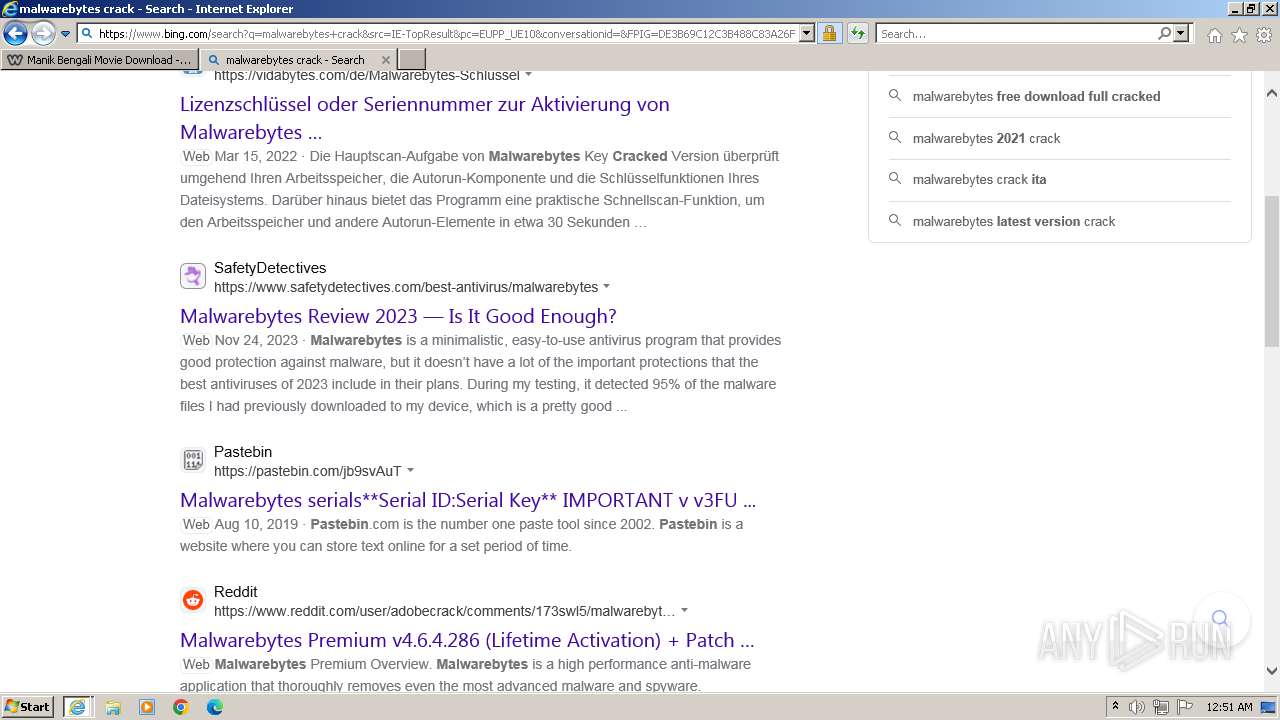
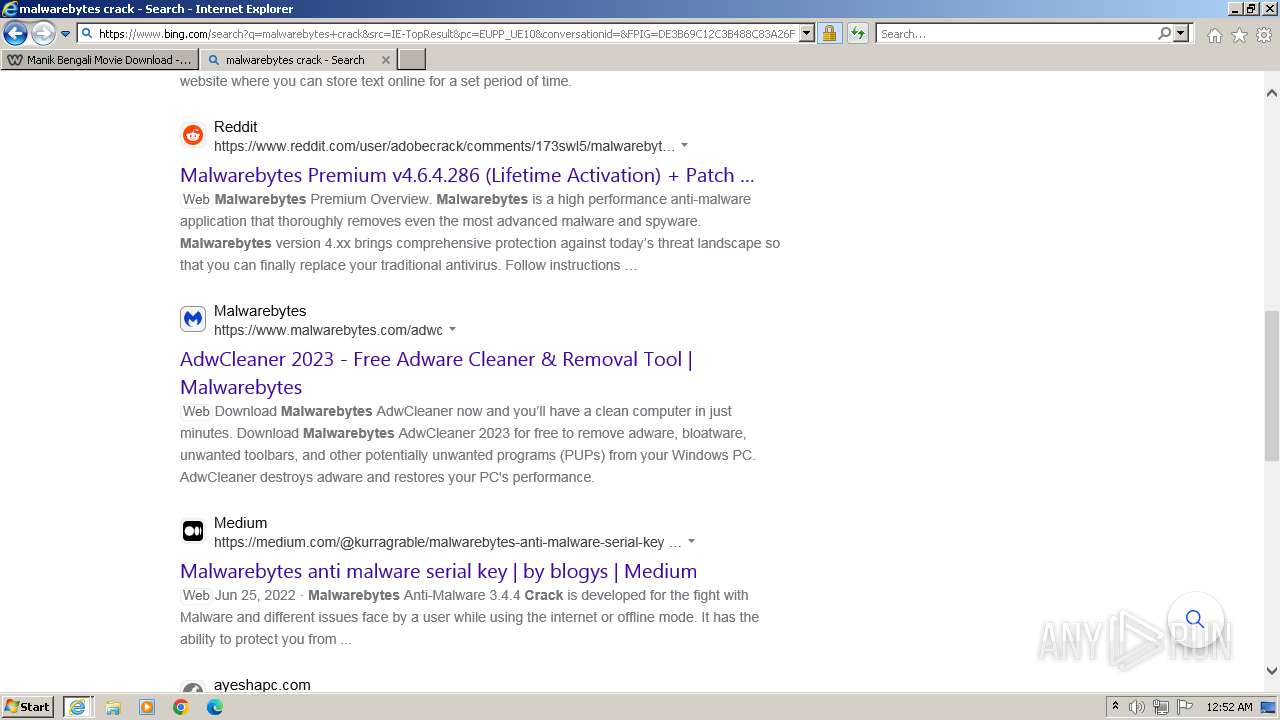
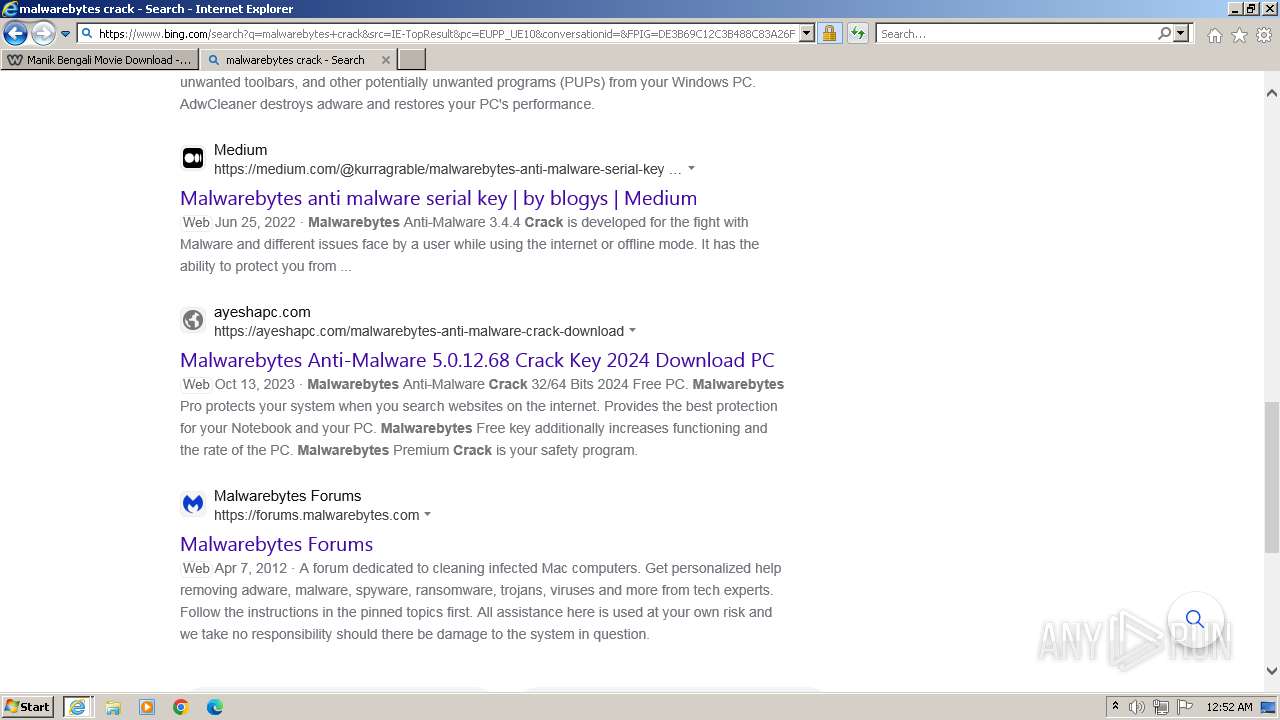
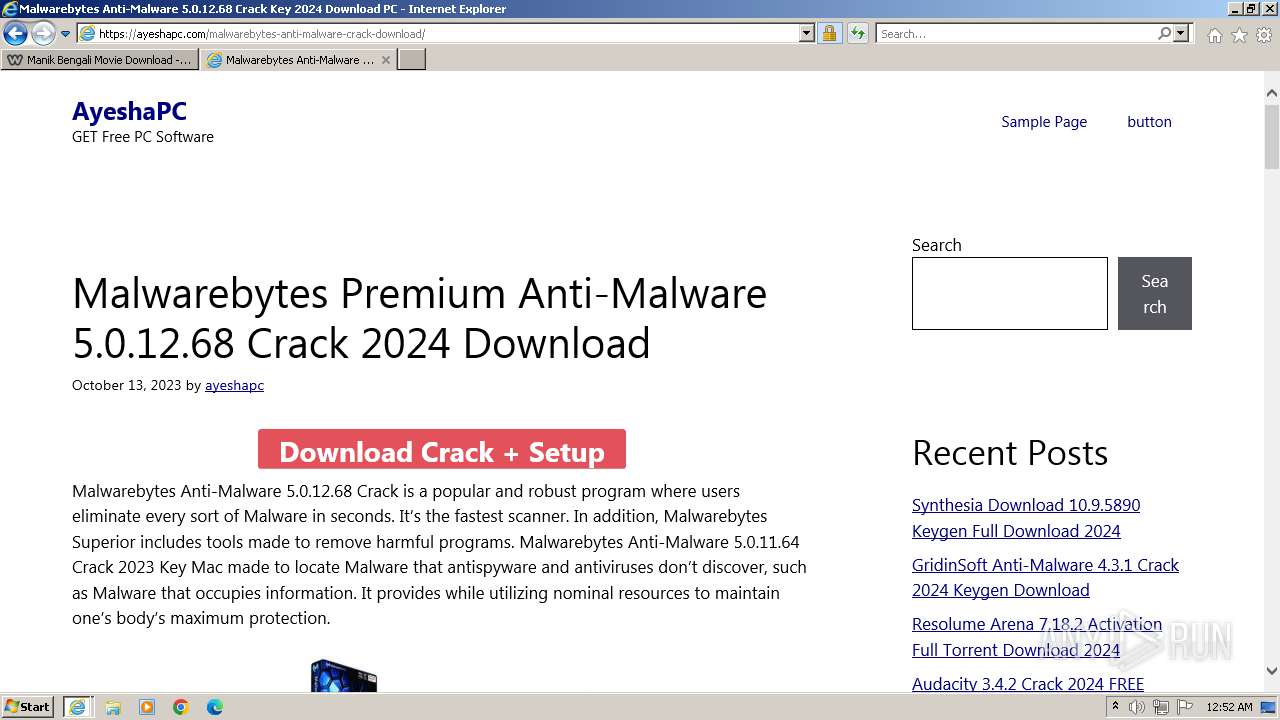
Bing abused for phishing
- iexplore.exe (PID: 3264)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 3108)
Reads the computer name
- wmpnscfg.exe (PID: 3108)
Manual execution by a user
- wmpnscfg.exe (PID: 3108)
Application launched itself
- iexplore.exe (PID: 3264)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2968 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3264 CREDAT:1250589 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3264 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3264 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.bing.com/ck/a?!&&p=c92e0a5758a2ec24JmltdHM9MTcwMjU5ODQwMCZpZ3VpZD0zMzAyYWMyNC0xMTFiLTZlNWYtMDVkMy1iZmMwMTAzMjZmNzgmaW5zaWQ9NTEzOQ&ptn=3&ver=2&hsh=3&fclid=3302ac24-111b-6e5f-05d3-bfc010326f78&psq=malwarebytes+crack+keygen&u=a1aHR0cHM6Ly9hZHZhbnRhZ2Vnb29kc2l0ZTI4MS53ZWVibHkuY29tL21hbHdhcmVieXRlcy1hbnRpLW1hbHdhcmUtbGlmZXRpbWUtbGljZW5zZS5odG1s&ntb=1" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
37 016
Read events
36 826
Write events
184
Delete events
6
Modification events
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
459
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C13C9BDA08D684653CA8ABED93893ECE | SHA256:BD26BAA9B642BF151AB16C5FAF41D29C41AE363C1F8856F358A3239278737C98 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:00D3FC7BCAE4BEEFCE1F9BA1E43CFC2E | SHA256:2CF73BE05C6D43D3966942F3FC68287C8D73C33D49A00784A651B5E00870BF86 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:E5034468F4C766A164BB3E28D4F0E6C8 | SHA256:C22DF2802E5DA3ECE8D548EE7280F764D7EDB5BA19A3661D0749DD13ACF8F2DB | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:BE1F9691ACA1DC7F37247ADB1C226C93 | SHA256:C188BCDD4994668D7198BDAD09BE79F6D7F84887B0ABB3C3979D24AEF8ED3E7F | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3264 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:F75800E3F57858CC9BBFB660E47F5033 | SHA256:D31ED3A366BBD65538F3FCE14A9C3063D3A9C844AE52ABE3380C6A244E3DE5AE | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:9E04CA76104117D48BA868D001EBDF52 | SHA256:AFF0671C68973EE709D88FD1C99E96EFCEECEA9BAD536A7C116202DF7E0D9D90 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\59D76868C250B3240414CE3EFBB12518_2C5F0ED2F89F8ECF54C55F34FCBF12DA | binary | |
MD5:A93C6CAF76F3F4C9C16C3B1F3198D9A2 | SHA256:77E525BA6B41BBECD2C6923B51088318FE82BE92DB406B8E1443AFD1B3B8DB81 | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:7A25FCD2A1E38707C32E8075771E4E5E | SHA256:AEA8C0E499051437AEDD7FE1968C720590BE01ECCCA26BADD6F70E0A42372E4C | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\malwarebytes-anti-malware-lifetime-license[1].htm | html | |
MD5:A615AE600645FBC671F9F2DF5A2C58E3 | SHA256:C3CE27BAC95B5BAB7131325A1092B077CDE4232C1BE0912DB0DB6064BA6469F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
158
DNS requests
67
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0b7725d384a0a9d4 | unknown | compressed | 4.66 Kb | unknown |
3264 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7c0985578a653cb5 | unknown | compressed | 4.66 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | binary | 471 b | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAgrLkwGpCB95PF3gVJY%2F%2Bw%3D | unknown | binary | 471 b | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | unknown | binary | 471 b | unknown |
3028 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEH3wUWDKXSh7Z3b6AuDWurw%3D | unknown | binary | 1.40 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3028 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAMSfMmoDBg9YLfQwlvEyK4%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3028 | iexplore.exe | 23.15.178.147:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3028 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3028 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3264 | iexplore.exe | 23.15.178.147:443 | www.bing.com | Akamai International B.V. | DE | unknown |
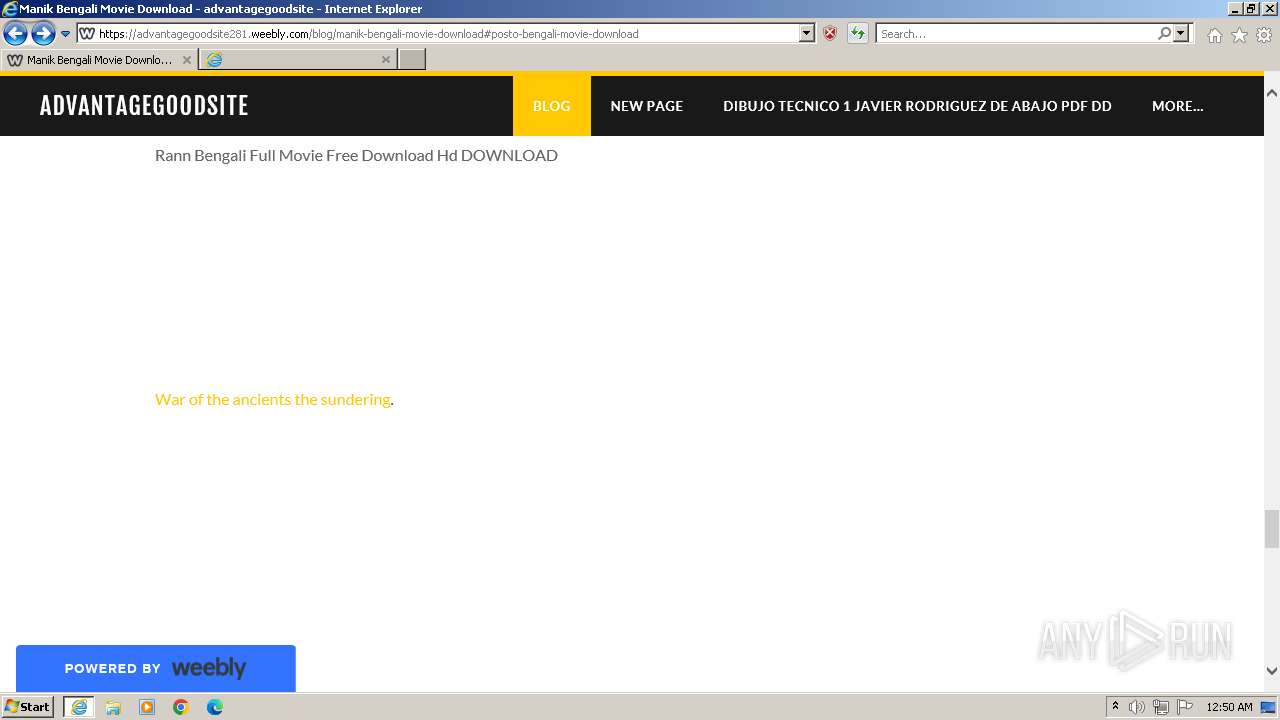
3028 | iexplore.exe | 199.34.228.54:443 | advantagegoodsite281.weebly.com | WEEBLY | US | unknown |
3028 | iexplore.exe | 151.101.1.46:443 | cdn2.editmysite.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
advantagegoodsite281.weebly.com |
| unknown |
cdn2.editmysite.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
lookaside.fbsbx.com |
| unknown |
ocsp2.globalsign.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |