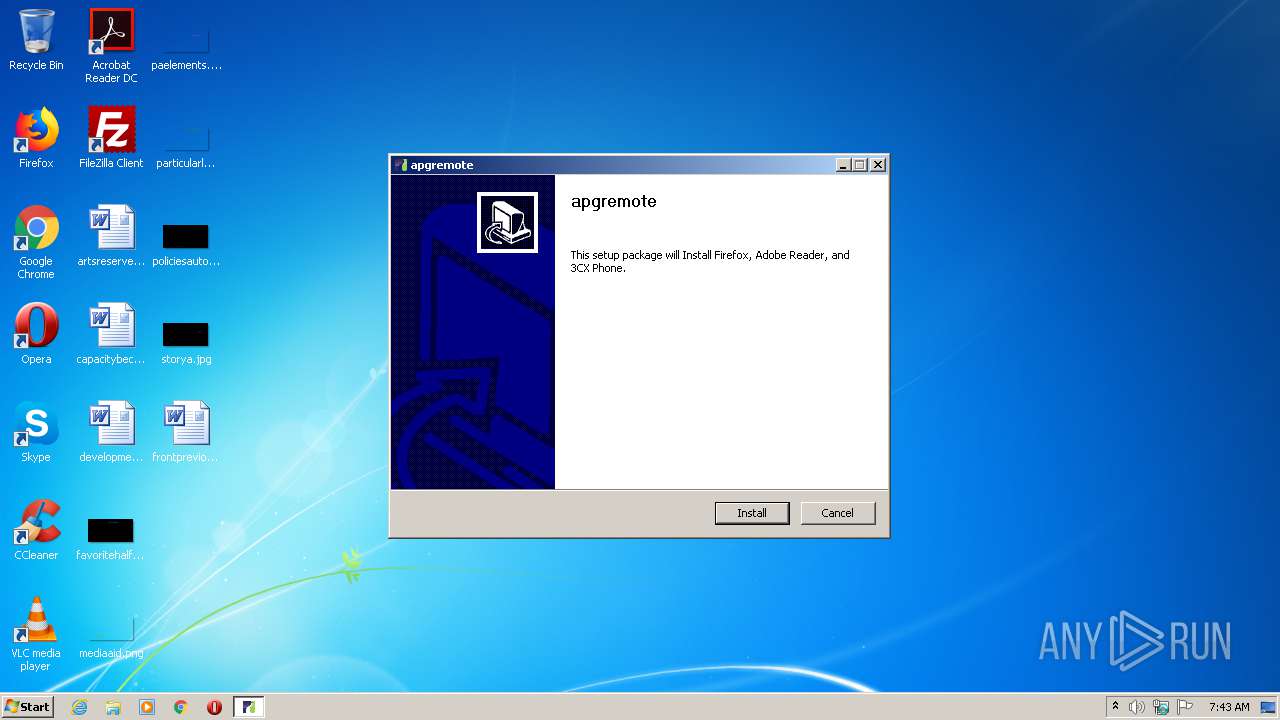
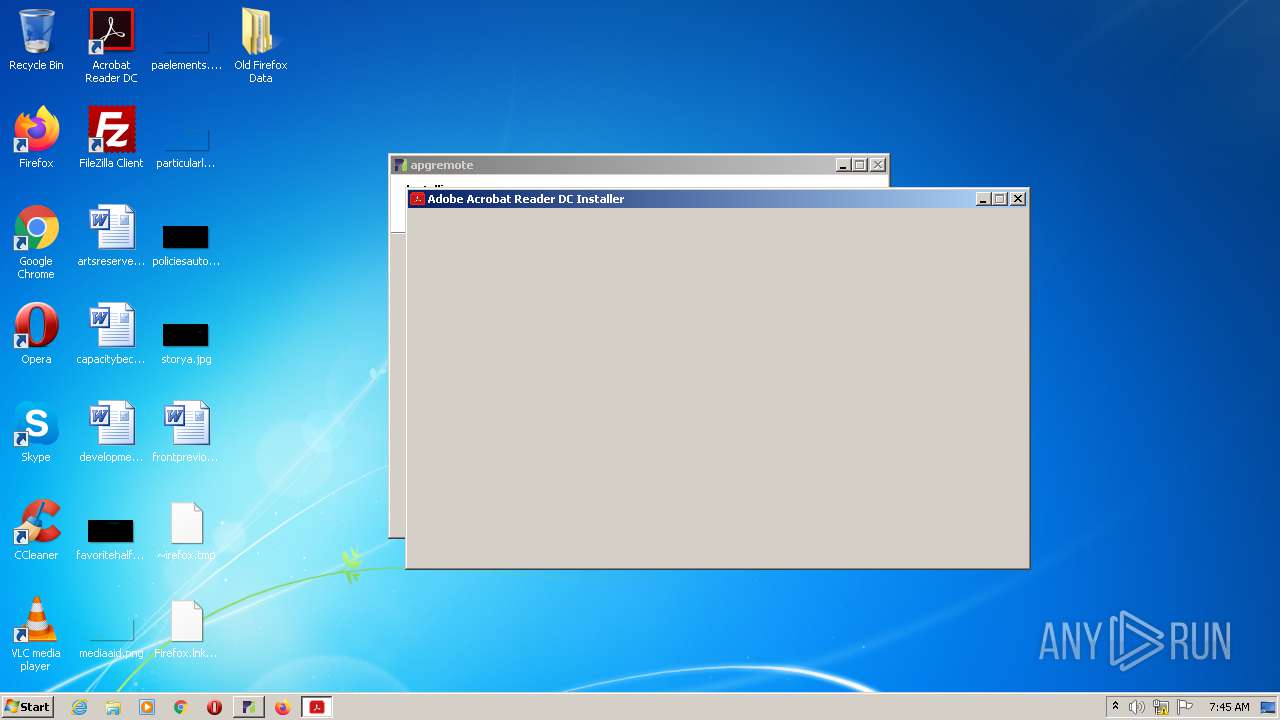
| File name: | open this file to install the software you need (1).exe |
| Full analysis: | https://app.any.run/tasks/a5774c22-c95c-4755-b89a-53afe31d7e60 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:43:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 22344C7598D883DEA1495984B1EA7FBE |
| SHA1: | 1AB66C88E0379A88E1698E2CF7C9135C4BBB7D44 |
| SHA256: | 37262AC81222CAC6A2348BB45EC87AE96EDB9E4F9EE317772A861F9ABAFBD6FD |
| SSDEEP: | 393216:hN7rbYLTPbvENud6K8kuK8nClIJEYdc22MMes0F76duS:vrsTOud6tc8nFJhOTanF7g |
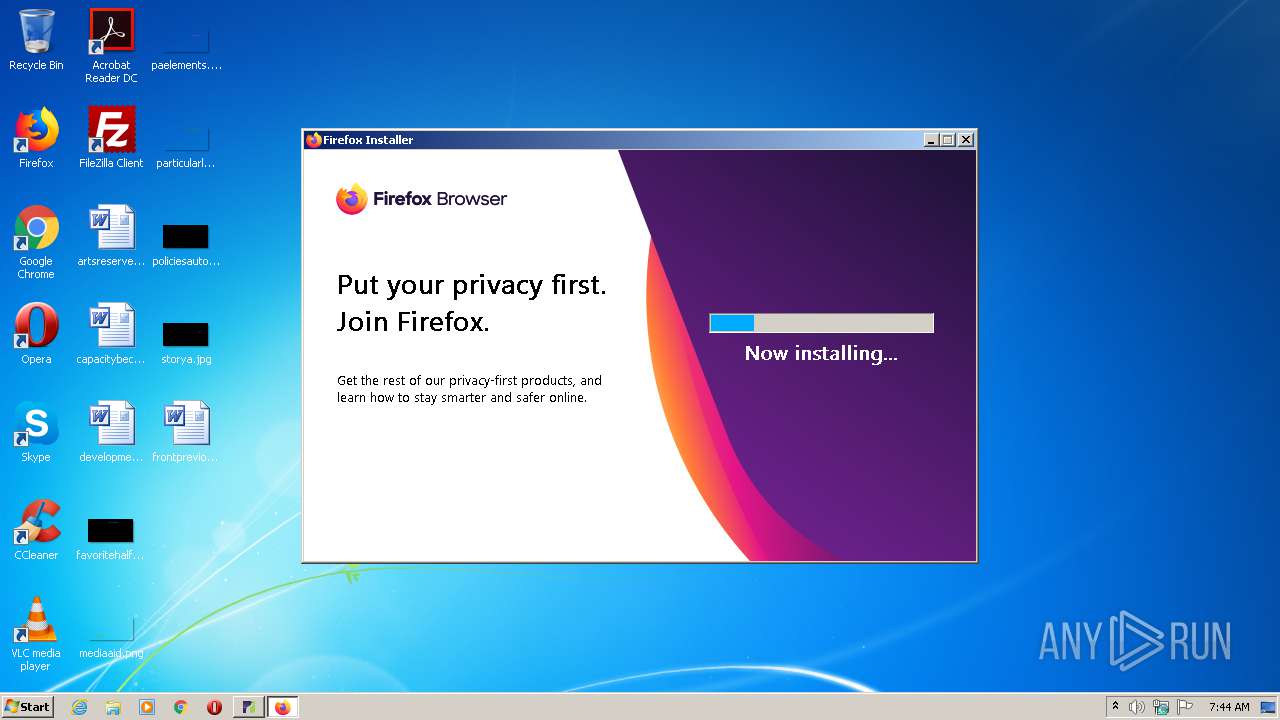
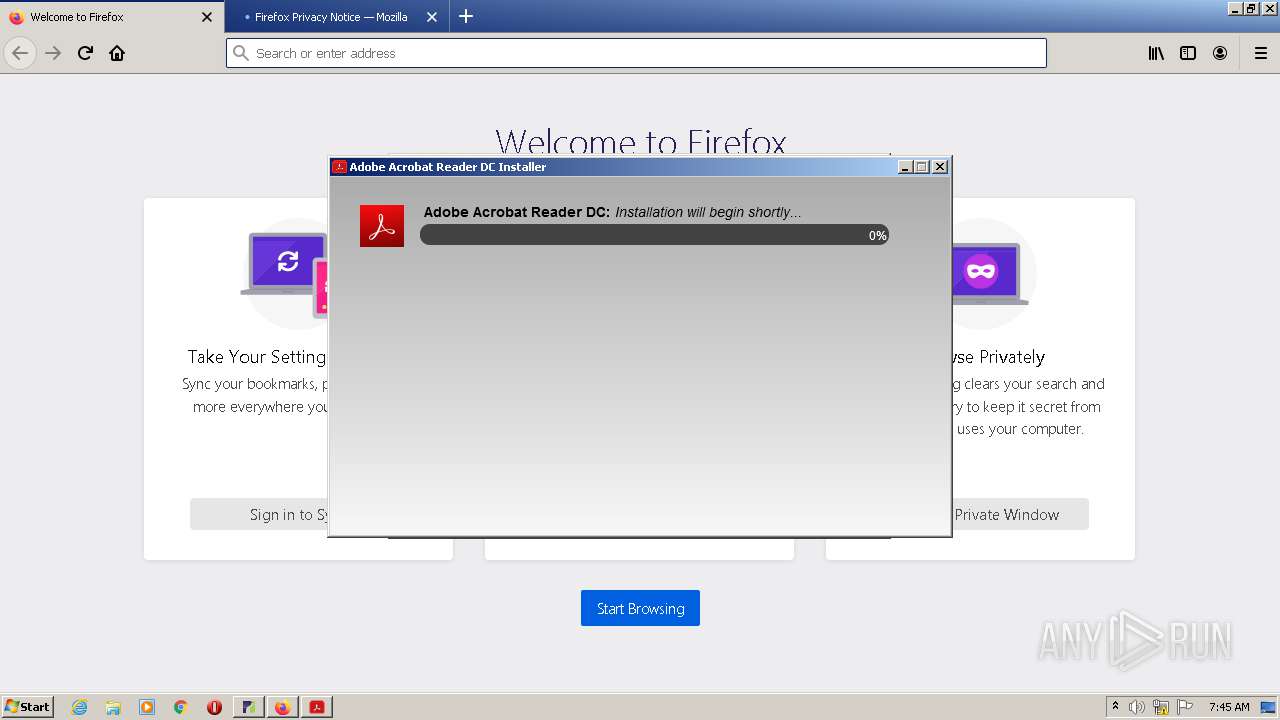
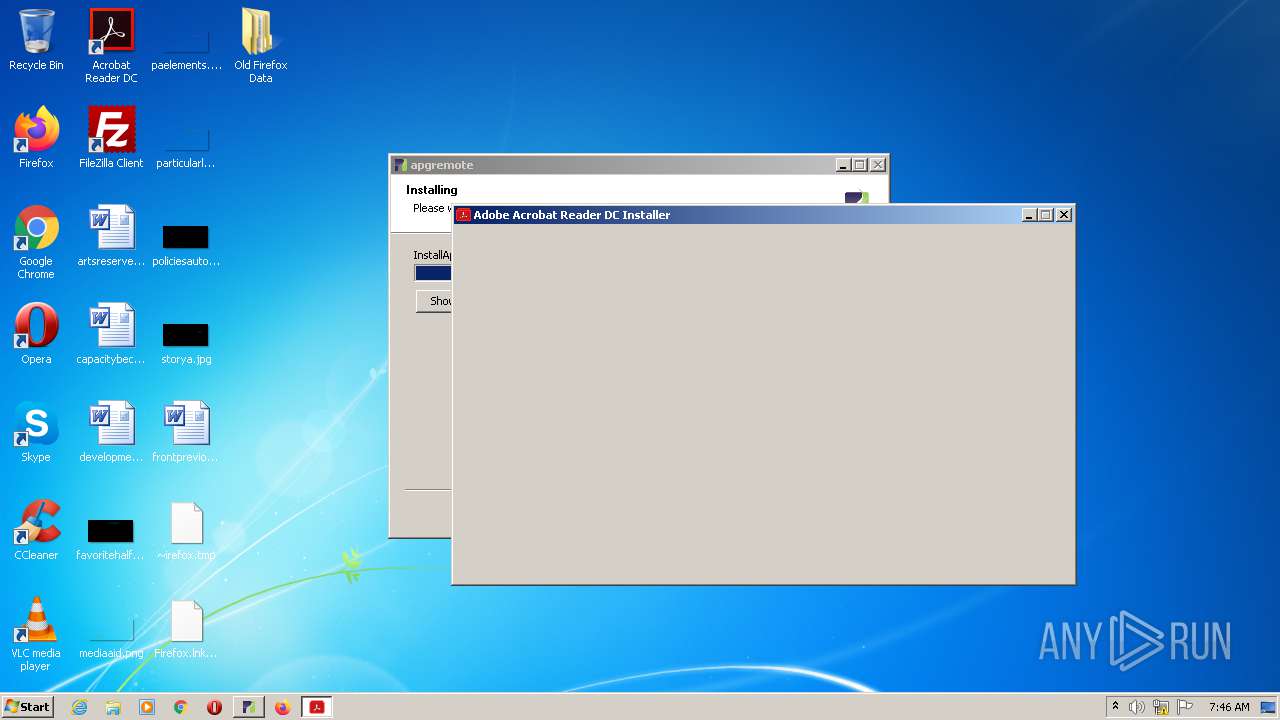
MALICIOUS
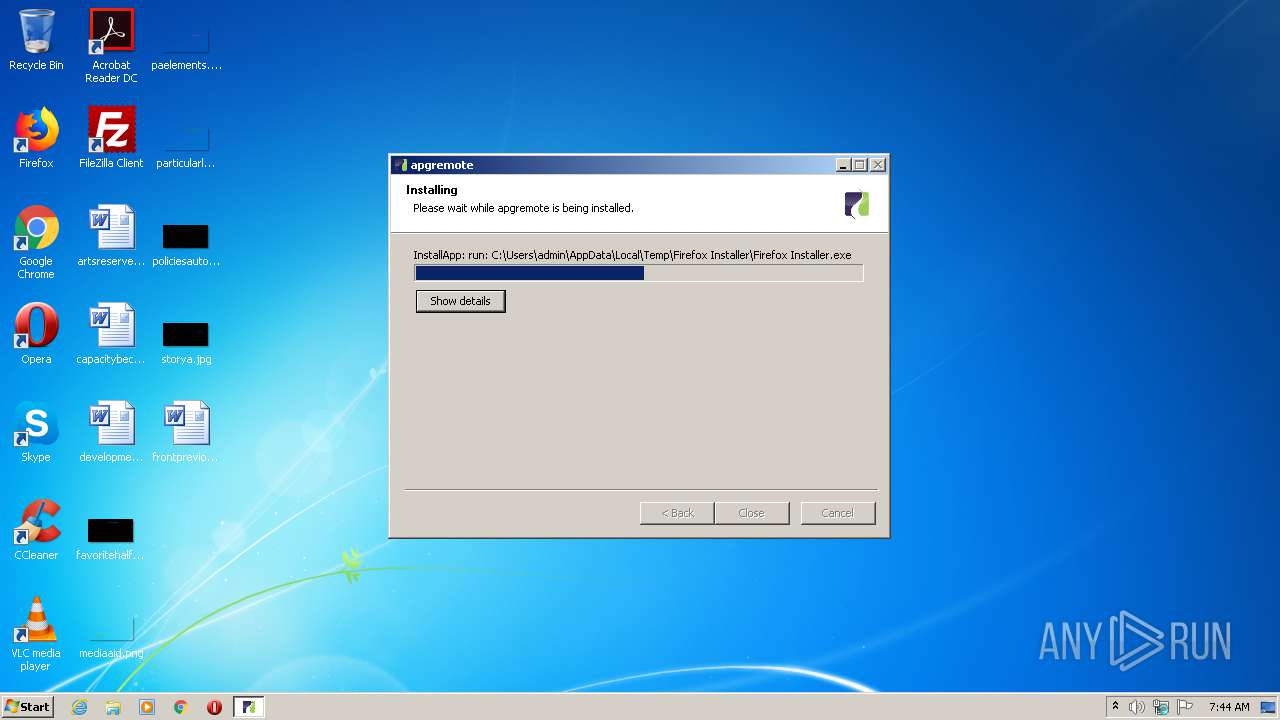
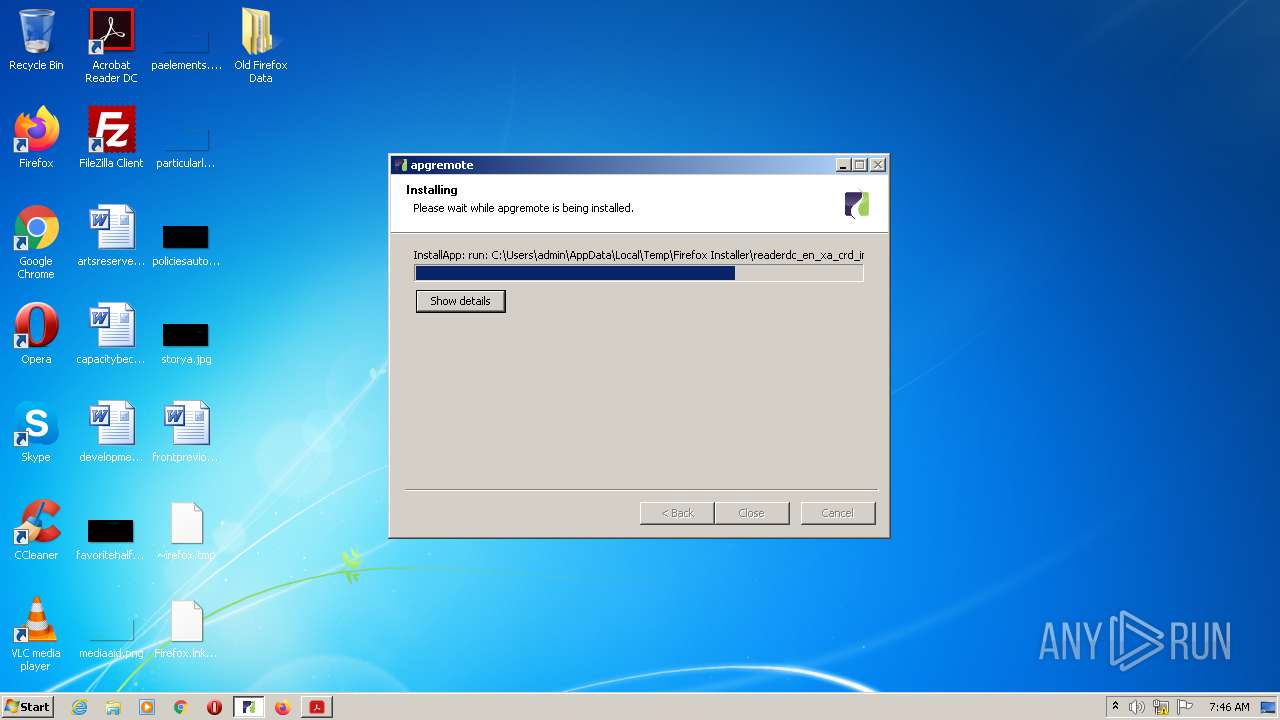
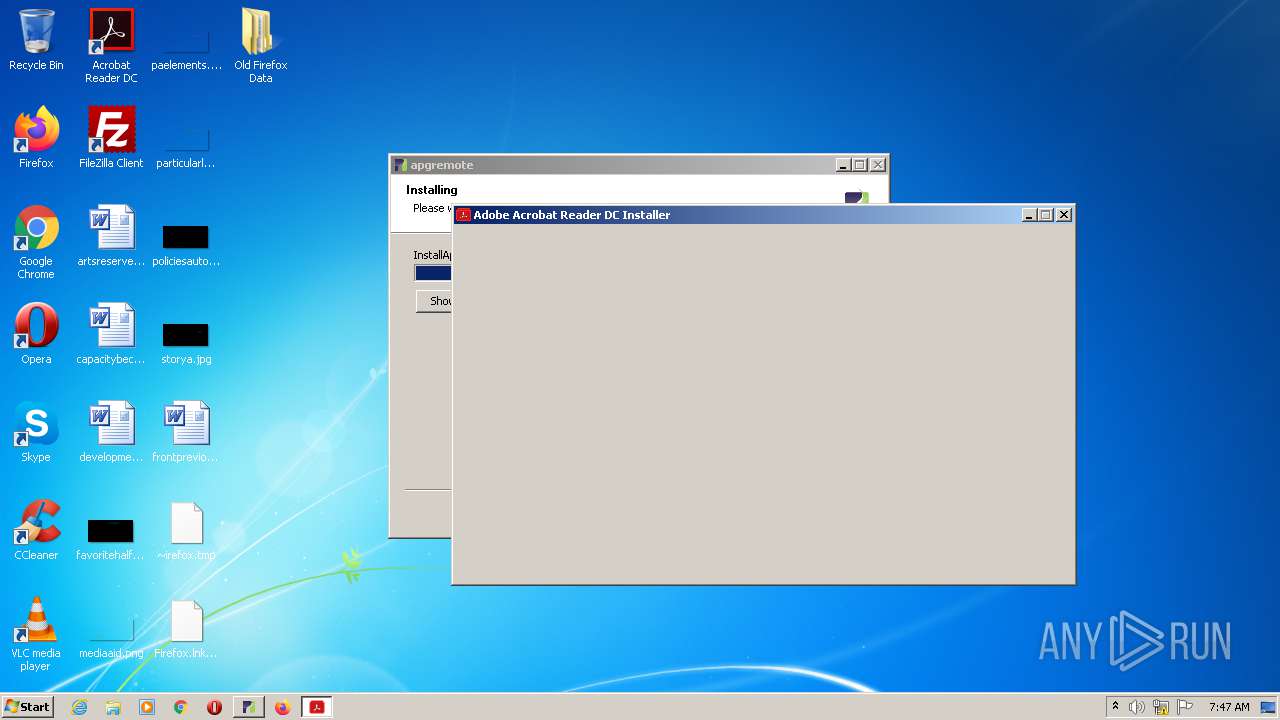
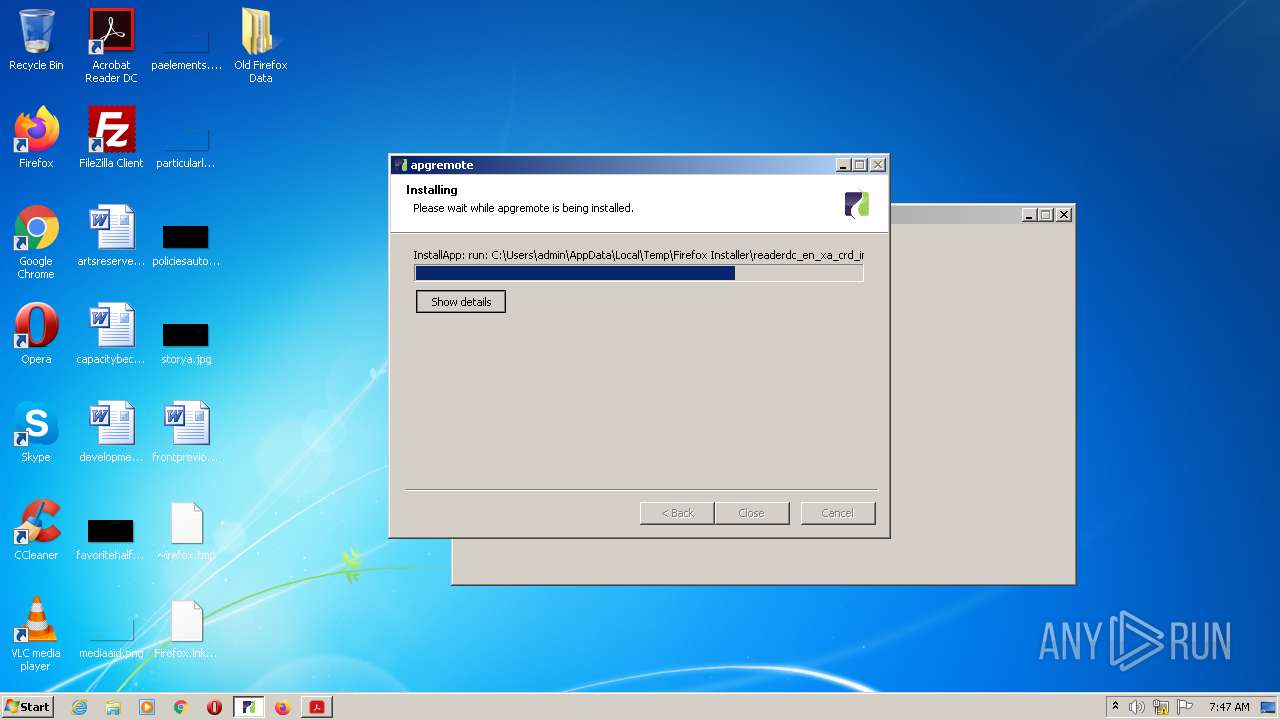
Loads dropped or rewritten executable
- open this file to install the software you need (1).exe (PID: 2128)
- open this file to install the software you need (1).exe (PID: 1360)
- setup-stub.exe (PID: 2308)
- setup.exe (PID: 2616)
- maintenanceservice_installer.exe (PID: 3716)
- default-browser-agent.exe (PID: 2976)
- csrss.exe (PID: 388)
- firefox.exe (PID: 916)
- firefox.exe (PID: 2824)
- csrss.exe (PID: 344)
- firefox.exe (PID: 4008)
- firefox.exe (PID: 2400)
- firefox.exe (PID: 4076)
- SearchProtocolHost.exe (PID: 676)
- firefox.exe (PID: 2352)
- firefox.exe (PID: 1456)
- firefox.exe (PID: 2344)
- pingsender.exe (PID: 124)
- firefox.exe (PID: 4028)
- pingsender.exe (PID: 2960)
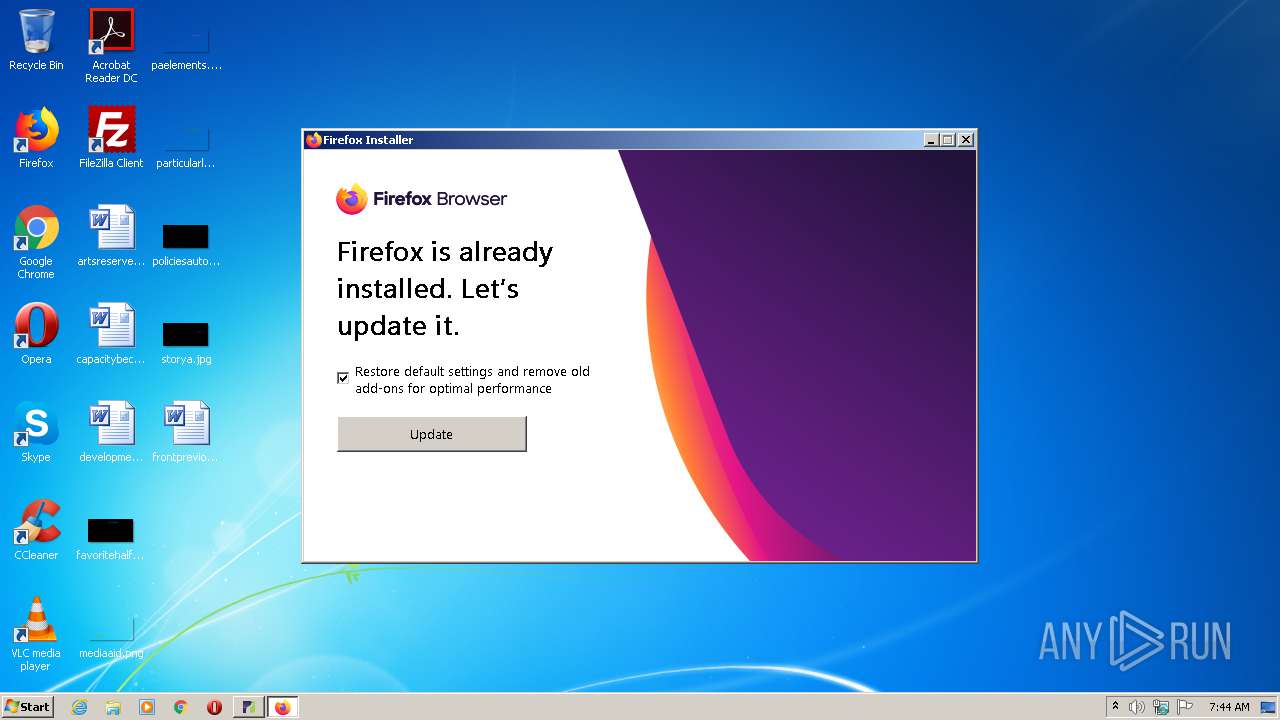
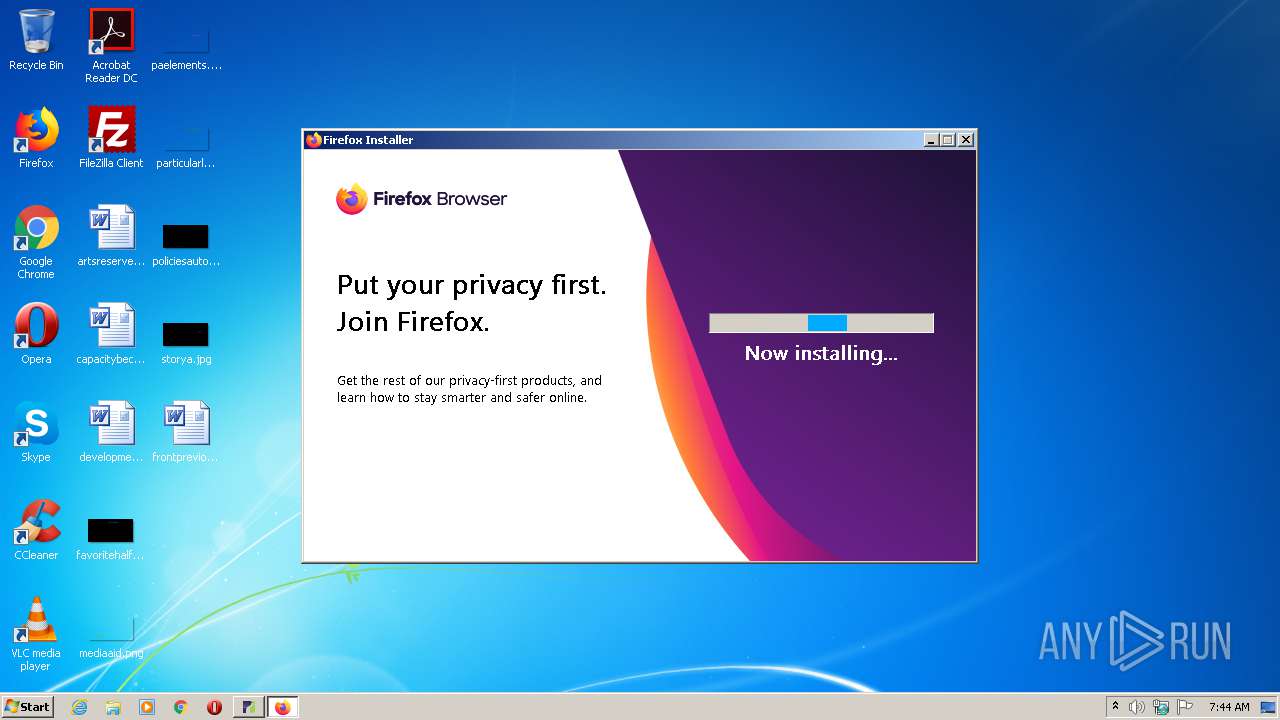
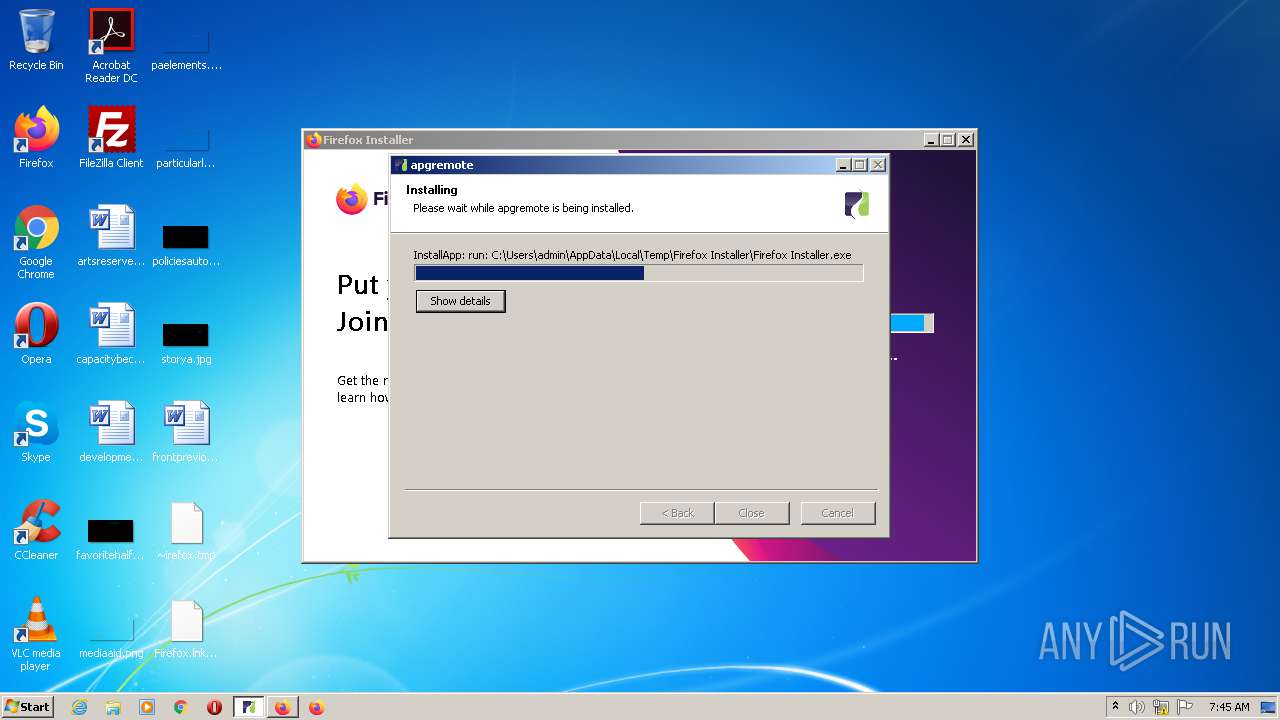
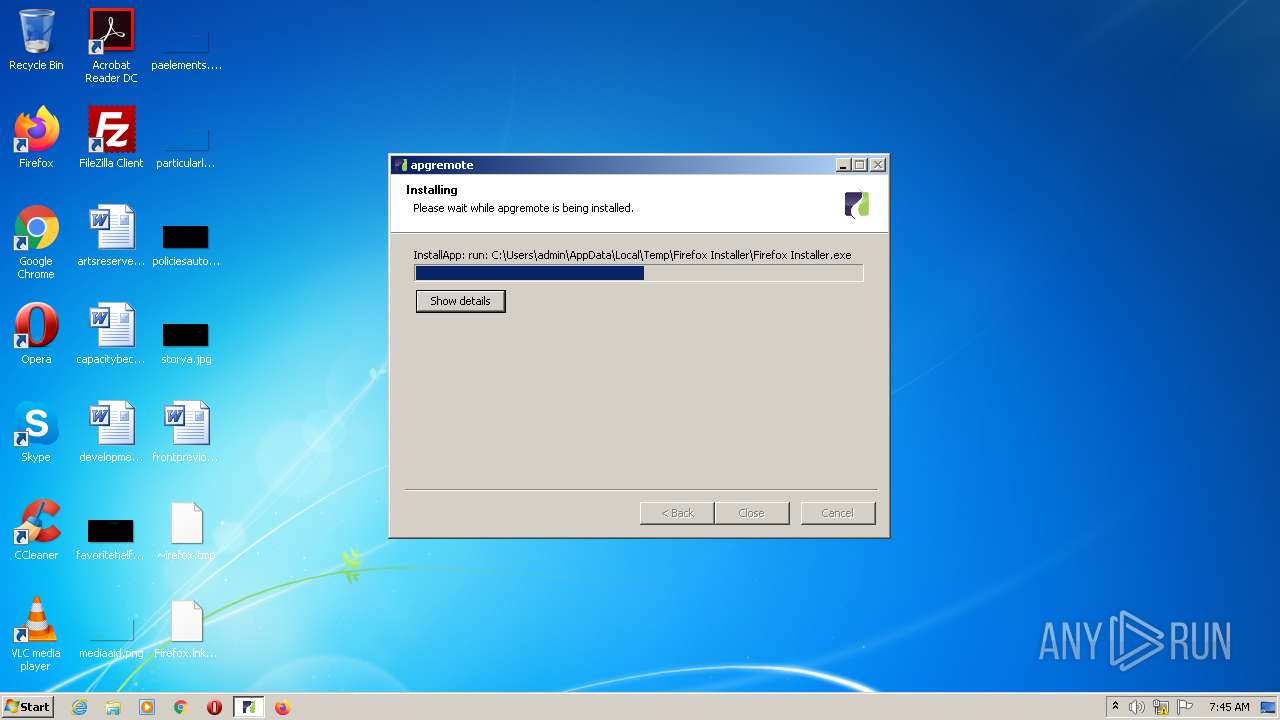
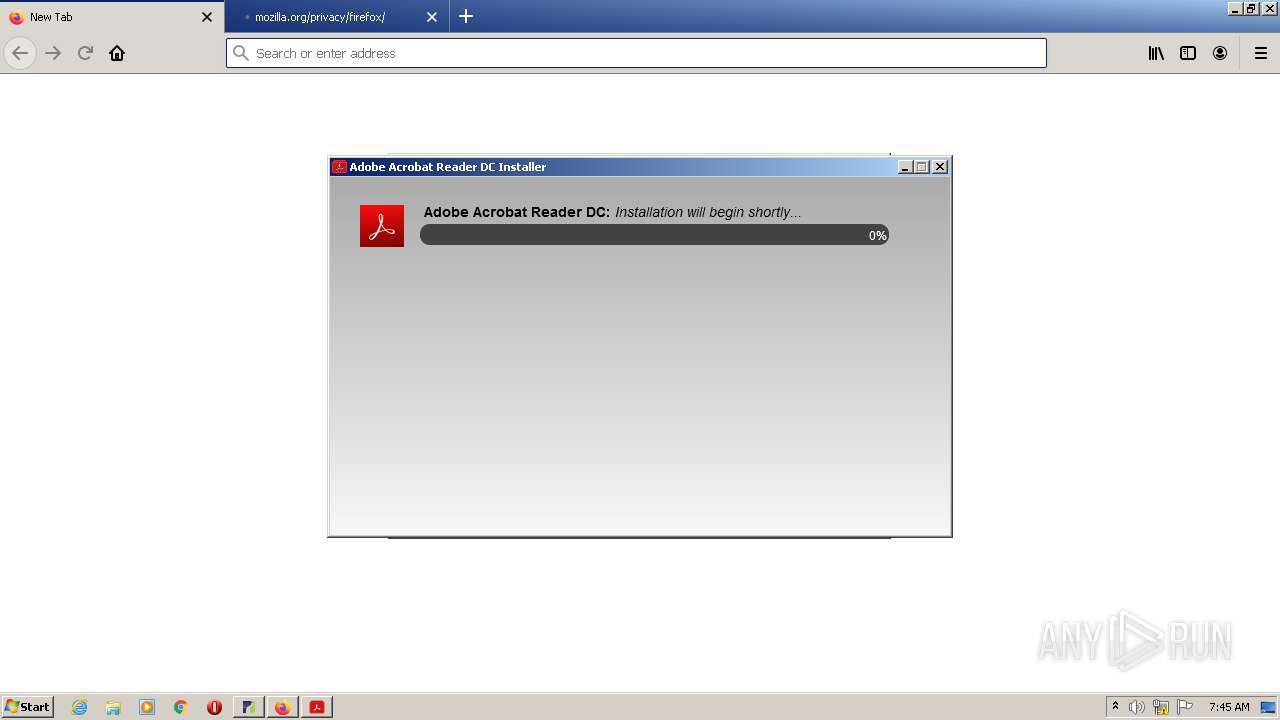
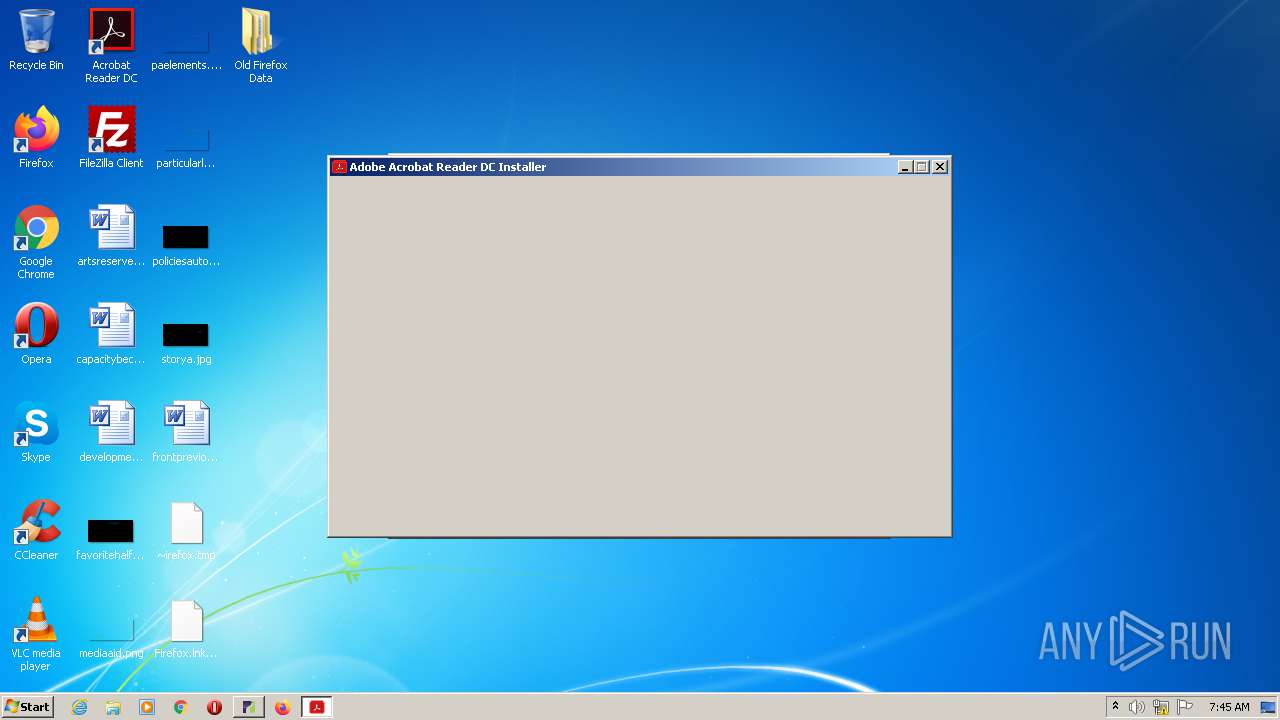
Application was dropped or rewritten from another process
- Firefox Installer.exe (PID: 4044)
- setup-stub.exe (PID: 2308)
- setup.exe (PID: 2616)
- maintenanceservice_installer.exe (PID: 3716)
- maintenanceservice.exe (PID: 2736)
- firefox.exe (PID: 916)
- firefox.exe (PID: 2824)
- firefox.exe (PID: 4028)
- ns9EC5.tmp (PID: 2224)
- firefox.exe (PID: 4008)
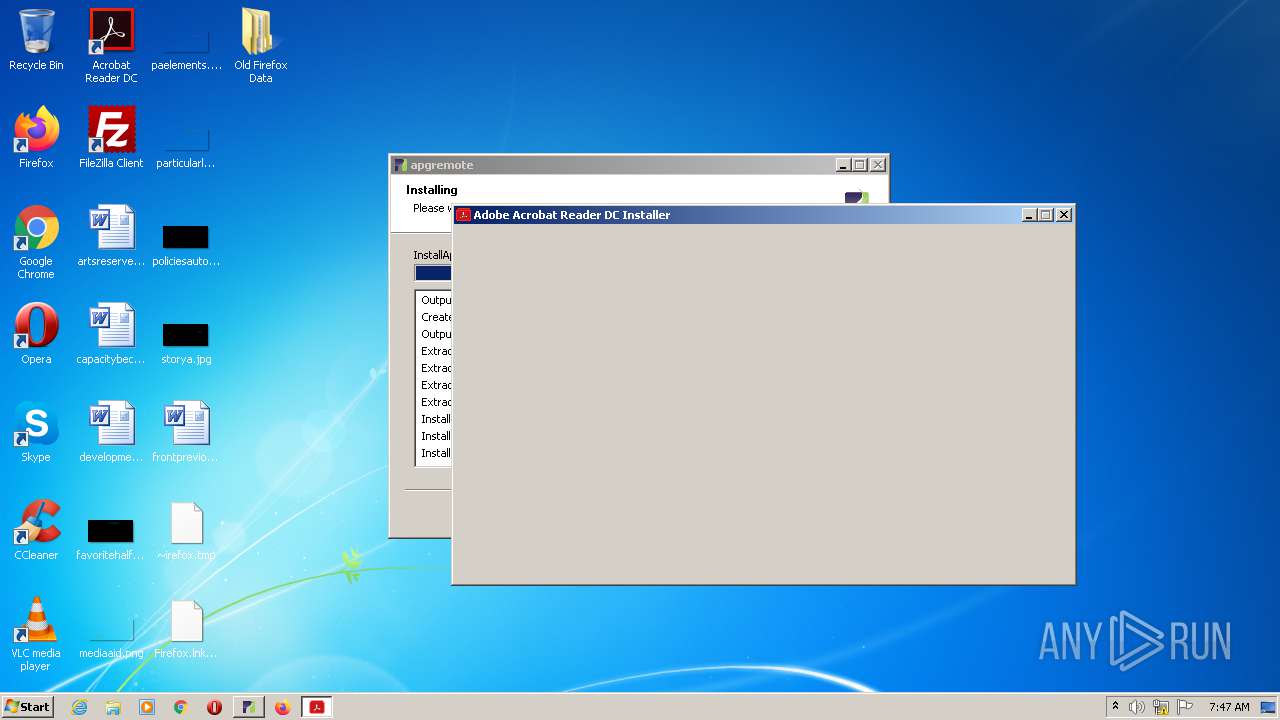
- readerdc_en_xa_crd_install.exe (PID: 2712)
- gtcheck.exe (PID: 2452)
- default-browser-agent.exe (PID: 2976)
- gccheck_small.exe (PID: 3720)
- gccheck_small.exe (PID: 2720)
- firefox.exe (PID: 2400)
- firefox.exe (PID: 2352)
- firefox.exe (PID: 4076)
- firefox.exe (PID: 1456)
- firefox.exe (PID: 2344)
- pingsender.exe (PID: 2960)
- pingsender.exe (PID: 124)
- setup.exe (PID: 272)
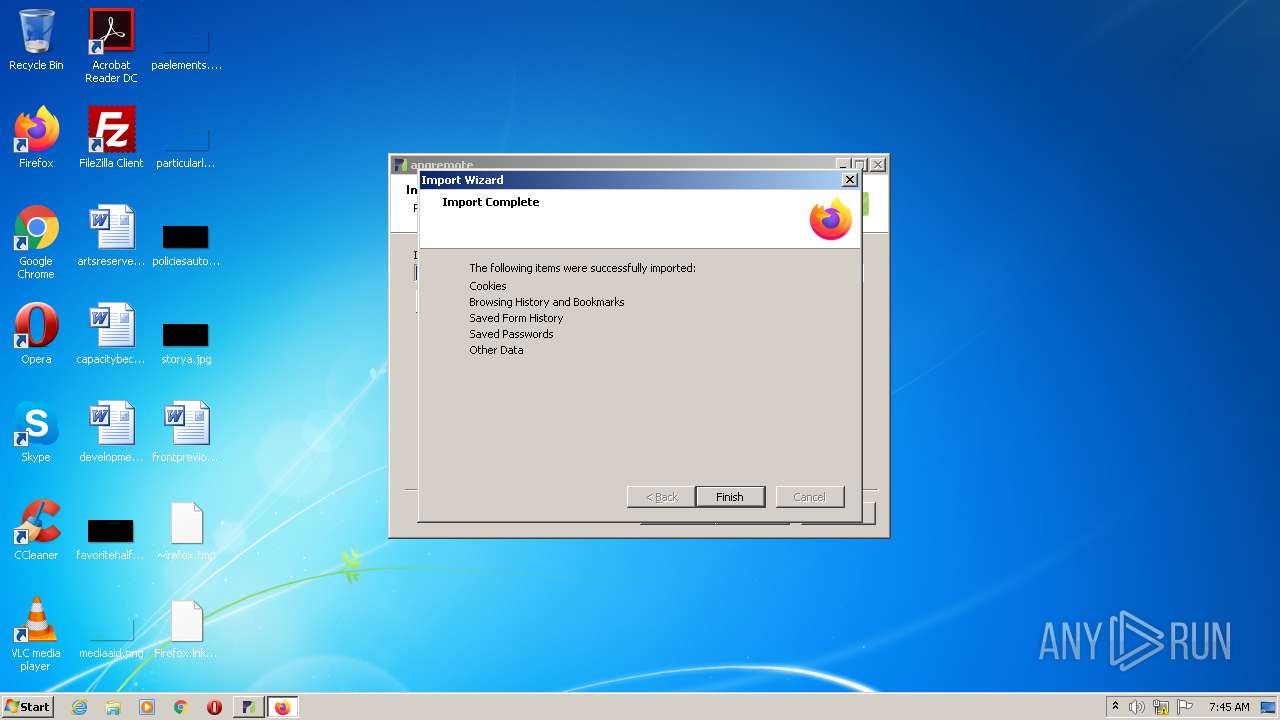
Actions looks like stealing of personal data
- setup-stub.exe (PID: 2308)
- download.exe (PID: 1712)
- 9B172B02-F924-493B-A8EA-85BF5BDCE688 (PID: 3956)
Loads the Task Scheduler COM API
- default-browser-agent.exe (PID: 2976)
Changes settings of System certificates
- readerdc_en_xa_crd_install.exe (PID: 2712)
- msiexec.exe (PID: 3832)
- setup-stub.exe (PID: 2308)
SUSPICIOUS
Executable content was dropped or overwritten
- open this file to install the software you need (1).exe (PID: 2128)
- open this file to install the software you need (1).exe (PID: 1360)
- Firefox Installer.exe (PID: 4044)
- setup-stub.exe (PID: 2308)
- download.exe (PID: 1712)
- setup.exe (PID: 2616)
- maintenanceservice_installer.exe (PID: 3716)
- readerdc_en_xa_crd_install.exe (PID: 2712)
- firefox.exe (PID: 4028)
- 9B172B02-F924-493B-A8EA-85BF5BDCE688 (PID: 3956)
- msiexec.exe (PID: 3832)
Application launched itself
- open this file to install the software you need (1).exe (PID: 2128)
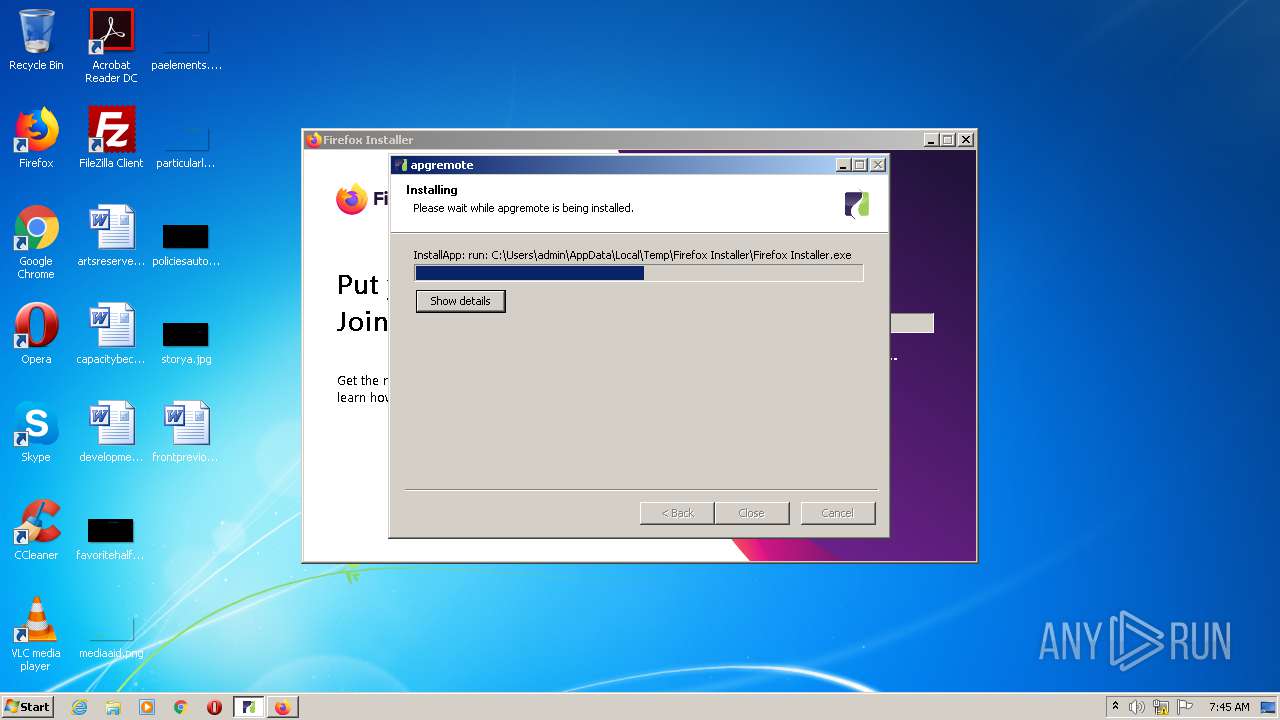
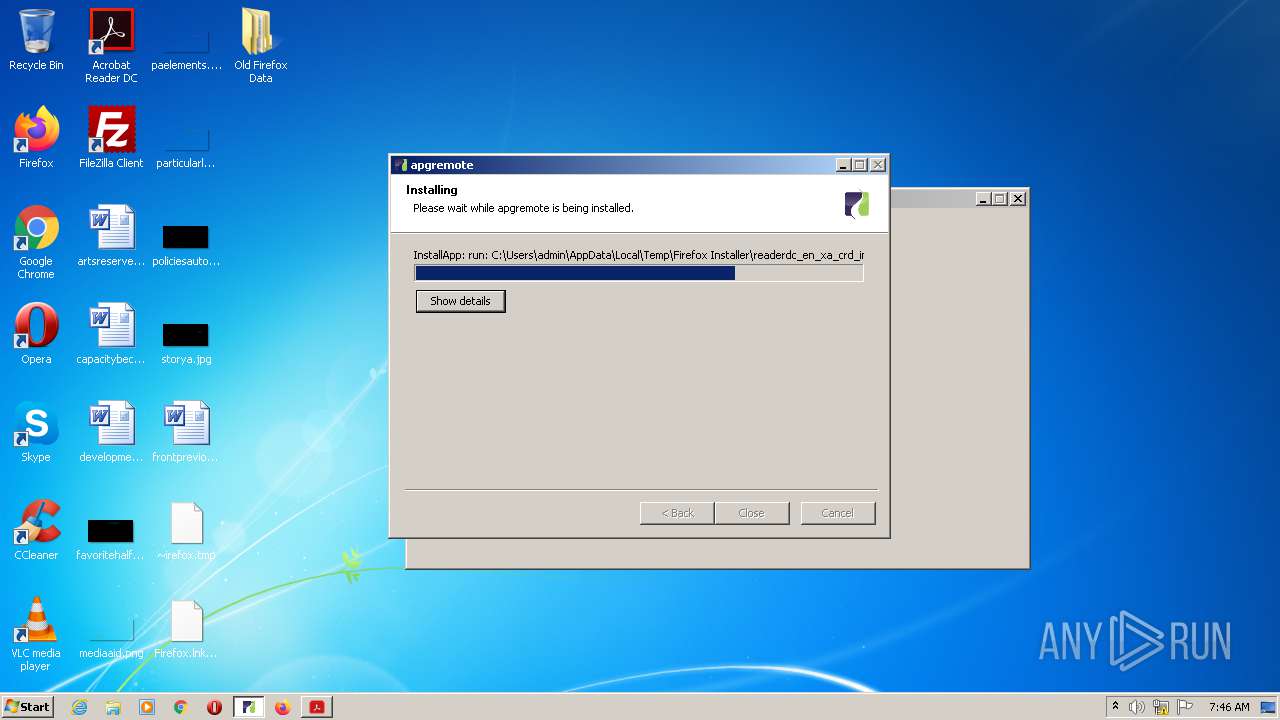
Creates a software uninstall entry
- open this file to install the software you need (1).exe (PID: 1360)
- setup.exe (PID: 2616)
- maintenanceservice_installer.exe (PID: 3716)
Reads Internet Cache Settings
- setup-stub.exe (PID: 2308)
- readerdc_en_xa_crd_install.exe (PID: 2712)
Creates files in the program directory
- setup-stub.exe (PID: 2308)
- setup.exe (PID: 2616)
- maintenanceservice.exe (PID: 2736)
- maintenanceservice_installer.exe (PID: 3716)
- firefox.exe (PID: 4028)
- 9B172B02-F924-493B-A8EA-85BF5BDCE688 (PID: 3956)
Loads DLL from Mozilla Firefox
- setup.exe (PID: 2616)
- default-browser-agent.exe (PID: 2976)
- csrss.exe (PID: 388)
- csrss.exe (PID: 344)
Creates COM task schedule object
- setup.exe (PID: 2616)
- msiexec.exe (PID: 3832)
Modifies the open verb of a shell class
- setup.exe (PID: 2616)
- msiexec.exe (PID: 3832)
Starts application with an unusual extension
- setup.exe (PID: 2616)
- readerdc_en_xa_crd_install.exe (PID: 2712)
Creates files in the user directory
- setup.exe (PID: 2616)
- readerdc_en_xa_crd_install.exe (PID: 2712)
Reads internet explorer settings
- readerdc_en_xa_crd_install.exe (PID: 2712)
Adds / modifies Windows certificates
- readerdc_en_xa_crd_install.exe (PID: 2712)
- msiexec.exe (PID: 3832)
- setup-stub.exe (PID: 2308)
Creates files in the Windows directory
- wusa.exe (PID: 308)
- MsiExec.exe (PID: 692)
- msiexec.exe (PID: 3832)
Disables SEHOP
- msiexec.exe (PID: 3832)
Removes files from Windows directory
- MsiExec.exe (PID: 692)
INFO
Reads settings of System Certificates
- setup-stub.exe (PID: 2308)
- readerdc_en_xa_crd_install.exe (PID: 2712)
- msiexec.exe (PID: 3832)
Dropped object may contain Bitcoin addresses
- download.exe (PID: 1712)
- setup.exe (PID: 2616)
- firefox.exe (PID: 4028)
- msiexec.exe (PID: 3832)
Manual execution by user
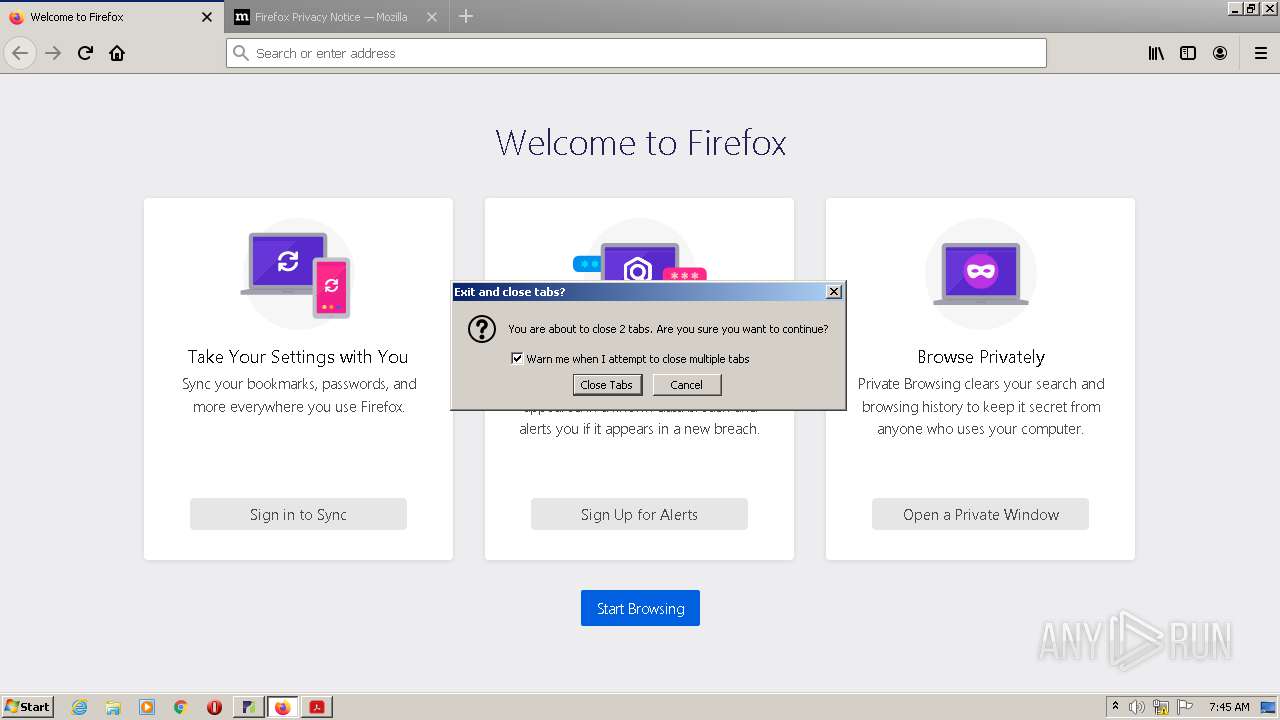
- firefox.exe (PID: 2824)
Application launched itself
- firefox.exe (PID: 4028)
- msiexec.exe (PID: 3832)
Reads Internet Cache Settings
- firefox.exe (PID: 4028)
- pingsender.exe (PID: 2960)
- pingsender.exe (PID: 124)
Creates files in the user directory
- firefox.exe (PID: 4028)
Dropped object may contain TOR URL's
- firefox.exe (PID: 4028)
Reads CPU info
- firefox.exe (PID: 4028)
Starts application with an unusual extension
- msiexec.exe (PID: 3832)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3832)
- MsiExec.exe (PID: 2196)
- MsiExec.exe (PID: 692)
Creates a software uninstall entry
- msiexec.exe (PID: 3832)
Creates files in the program directory
- msiexec.exe (PID: 3832)
Application was dropped or rewritten from another process
- MSIB342.tmp (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:20:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 489984 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | American Power and Gas |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:20:04 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | American Power and Gas |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:20:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000728C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49971 |
.rdata | 0x00009000 | 0x00002B6E | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49793 |
.data | 0x0000C000 | 0x00072B9C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.80494 |
.ndata | 0x0007F000 | 0x000E1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00160000 | 0x0000C778 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.08671 |
.reloc | 0x0016D000 | 0x00000FD6 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.33841 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2266 | 957 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.18266 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
81
Monitored processes
39
Malicious processes
24
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/9e3c7df0-ba17-4f43-a68d-d1316fe55905/event/Firefox/78.0.2/release/20200708170202?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\r472csc9.default-1594622716045\saved-telemetry-pings\9e3c7df0-ba17-4f43-a68d-d1316fe55905 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 78.0.2 Modules
| |||||||||||||||
| 272 | "C:\ProgramData\Adobe\Setup\{AC76BA86-7AD7-1033-7B44-AC0F074E4100}\setup.exe" /sAll /re /msi OWNERSHIP_STATE=1 UPDATE_MODE=3 EULA_ACCEPT=YES ENABLE_CHROMEEXT=0 DISABLE_CACHE=1 | C:\ProgramData\Adobe\Setup\{AC76BA86-7AD7-1033-7B44-AC0F074E4100}\setup.exe | — | 9B172B02-F924-493B-A8EA-85BF5BDCE688 | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Bootstrapper for Single Installation Exit code: 0 Version: 20.9.20063.381938 Modules
| |||||||||||||||
| 308 | wusa.exe "C:\Program Files\Adobe\Acrobat Reader DC\Redistributables\Windows6.1-KB2999226-x86.msu" /quiet /norestart | C:\Windows\system32\wusa.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update Standalone Installer Exit code: 2359302 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | C:\Windows\system32\MsiExec.exe -Embedding 52A48BDDAD1B49C9A37176891854DF4E | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Mozilla Firefox\firefox.exe" -reset-profile -migration -first-startup | C:\Program Files\Mozilla Firefox\firefox.exe | — | setup-stub.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: HIGH Description: Firefox Exit code: 0 Version: 78.0.2 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\Downloads\open this file to install the software you need (1).exe" /UAC:2012C /NCRC | C:\Users\admin\Downloads\open this file to install the software you need (1).exe | open this file to install the software you need (1).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4028.27.1758972714\694861113" -childID 4 -isForBrowser -prefsHandle 1368 -prefMapHandle 1364 -prefsLen 12306 -prefMapSize 219039 -parentBuildID 20200708170202 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4028 "\\.\pipe\gecko-crash-server-pipe.4028" 3964 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 78.0.2 Modules
| |||||||||||||||
Total events
15 772
Read events
8 277
Write events
4 665
Delete events
2 830
Modification events
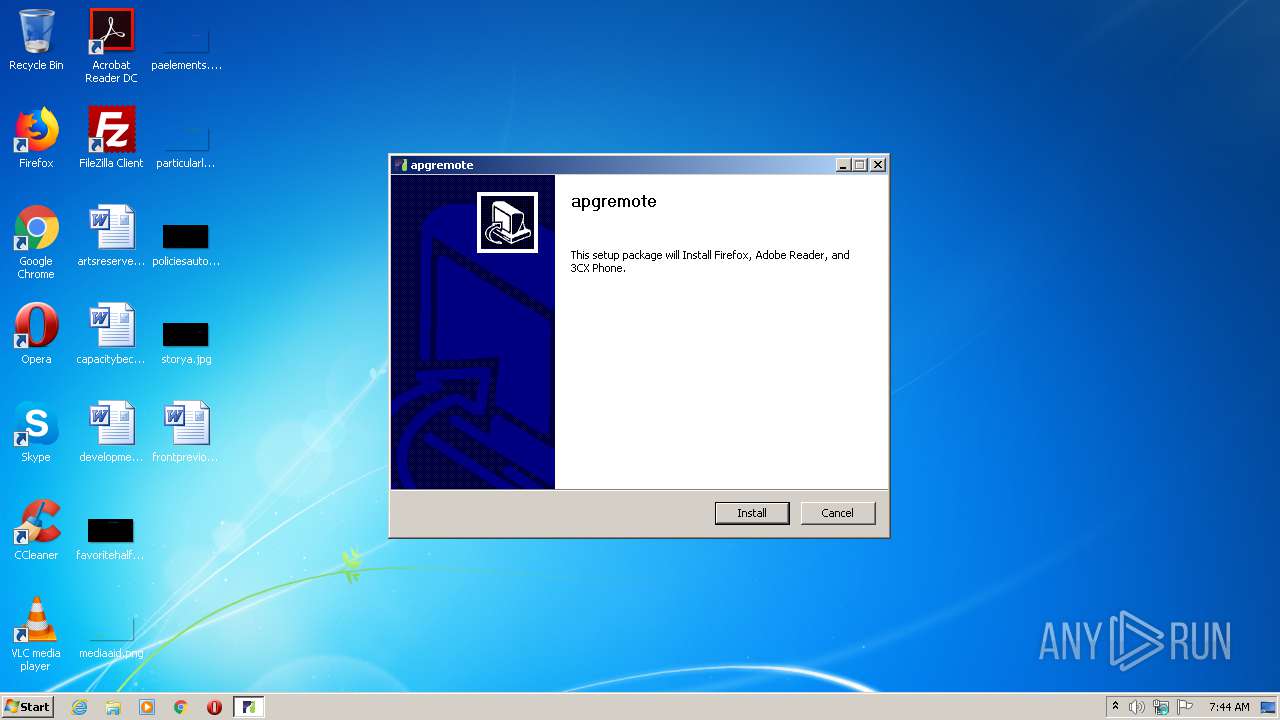
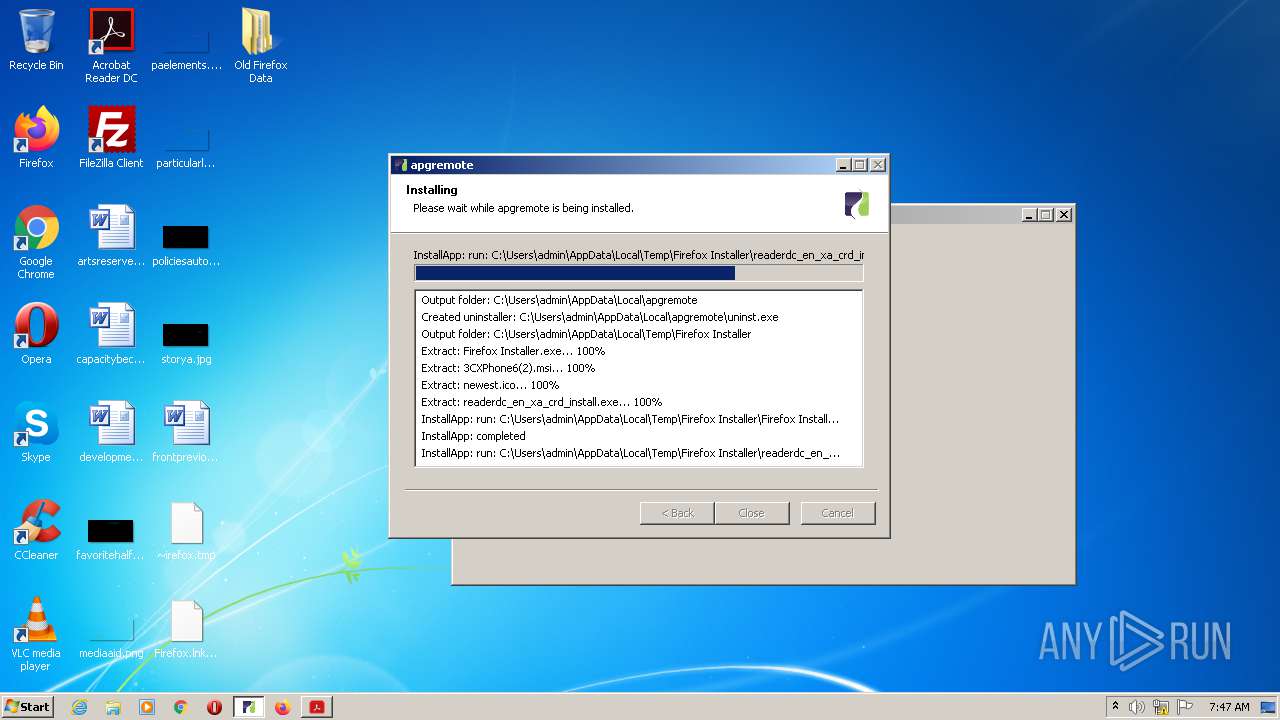
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | DisplayName |
Value: apgremote | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0 | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | Publisher |
Value: American Power and Gas | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | VersionMinor |
Value: 0 | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | ProductID |
Value: {BCB38FB9-360F-41AB-A696-5AB1DF2BEBE7} | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\apgremote\uninst.exe" | |||
| (PID) Process: | (1360) open this file to install the software you need (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\apgremote |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\apgremote\uninst.exe,0 | |||
Executable files
544
Suspicious files
139
Text files
478
Unknown types
257
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1360 | open this file to install the software you need (1).exe | C:\Users\admin\AppData\Local\Temp\Firefox Installer\3CXPhone6(2).msi | — | |
MD5:— | SHA256:— | |||
| 4044 | Firefox Installer.exe | C:\Users\admin\AppData\Local\Temp\7zSCCFFBADF\postSigningData | — | |
MD5:— | SHA256:— | |||
| 1360 | open this file to install the software you need (1).exe | C:\Users\admin\AppData\Local\Temp\Firefox Installer\newest.ico | image | |
MD5:— | SHA256:— | |||
| 4044 | Firefox Installer.exe | C:\Users\admin\AppData\Local\Temp\7zSCCFFBADF\setup-stub.exe | executable | |
MD5:— | SHA256:— | |||
| 1360 | open this file to install the software you need (1).exe | C:\Users\admin\AppData\Local\Temp\Firefox Installer\Firefox Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 1360 | open this file to install the software you need (1).exe | C:\Users\admin\AppData\Local\apgremote\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 1360 | open this file to install the software you need (1).exe | C:\Users\admin\AppData\Local\Temp\nsy81F9.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2308 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\CabB81.tmp | — | |
MD5:— | SHA256:— | |||
| 2308 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\TarB82.tmp | — | |
MD5:— | SHA256:— | |||
| 2308 | setup-stub.exe | C:\Users\admin\AppData\Local\Temp\nsgE249.tmp\download.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
47
DNS requests
88
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2712 | readerdc_en_xa_crd_install.exe | GET | 302 | 15.188.154.177:80 | http://stats.adobe.com/b/ss/adbacdcprod/1/H.25.4/s08367932714374?AQB=1&ndh=1&t=13%2F6%2F2020%207%3A45%3A20%201%20-60&ce=UTF-8&ns=adobecorp&pageName=acdc_rdr_adm_launched&g=res%3A%2F%2FC%3A%5CUsers%5Cadmin%5CAppData%5CLocal%5CTemp%5CFirefox%20Installer%5Creaderdc_en_xa_crd_install.exe%2F160&ch=acdc_reader&events=event96&products=%3Breader_adm&c1=adm&c2=acdc%20downloads&c3=get.adobe.com&c4=en_us&c5=en_us%3Aacdc_rdr_adm_launched&v18=new&v22=monday%20-%2012%3A30am&v73=acdc_reader&s=1280x720&c=32&j=1.5&v=Y&k=N&bw=620&bh=358&ct=lan&hp=N&AQE=1 | US | — | — | whitelisted |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2308 | setup-stub.exe | GET | 200 | 52.32.180.226:80 | http://download-stats.mozilla.org/stub/v8/release/release/en-US/0/0/6/1/7601/1/0/0/2/0/52816160/52816160/0/0/31/30/0/0/9/6/0/0/1/68.0.1/20190717172542/78.0.2/20200708170202/1/1/0/3/52.222.155.231/0/2/1 | US | — | — | whitelisted |
124 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAd1LOvlIi%2FPXH0gOJhMUZg%3D | US | der | 471 b | whitelisted |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2960 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAd1LOvlIi%2FPXH0gOJhMUZg%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | setup-stub.exe | 52.32.180.226:80 | download-stats.mozilla.org | Amazon.com, Inc. | US | unknown |
2712 | readerdc_en_xa_crd_install.exe | 23.210.248.251:443 | dlmping2.adobe.com | Akamai International B.V. | NL | whitelisted |
2308 | setup-stub.exe | 52.222.158.194:443 | product-details.mozilla.org | Amazon.com, Inc. | US | unknown |
2712 | readerdc_en_xa_crd_install.exe | 15.188.154.177:80 | stats.adobe.com | Hewlett-Packard Company | US | unknown |
4028 | firefox.exe | 52.222.158.168:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | whitelisted |
4028 | firefox.exe | 52.222.158.79:443 | content-signature-2.cdn.mozilla.net | Amazon.com, Inc. | US | malicious |
4028 | firefox.exe | 104.18.164.34:443 | www.mozilla.org | Cloudflare Inc | US | unknown |
4028 | firefox.exe | 34.98.75.36:443 | classify-client.services.mozilla.com | — | US | suspicious |
2308 | setup-stub.exe | 34.234.123.70:443 | download.mozilla.org | Amazon.com, Inc. | US | unknown |
4028 | firefox.exe | 52.222.158.66:443 | product-details.mozilla.org | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
product-details.mozilla.org |
| shared |
ocsp.digicert.com |
| whitelisted |
download.mozilla.org |
| whitelisted |
download-installer.cdn.mozilla.net |
| whitelisted |
download-stats.mozilla.org |
| whitelisted |
get.adobe.com |
| whitelisted |
dlmping2.adobe.com |
| whitelisted |
stats.adobe.com |
| whitelisted |
platformdl.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |