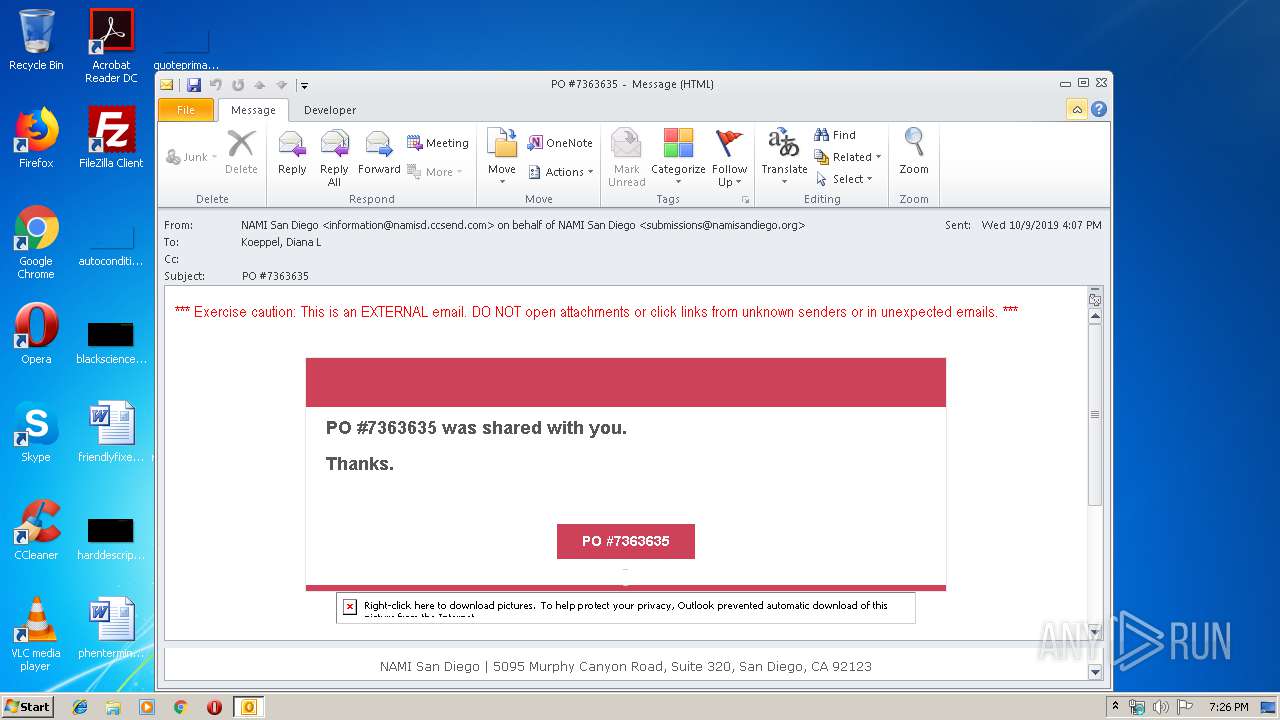
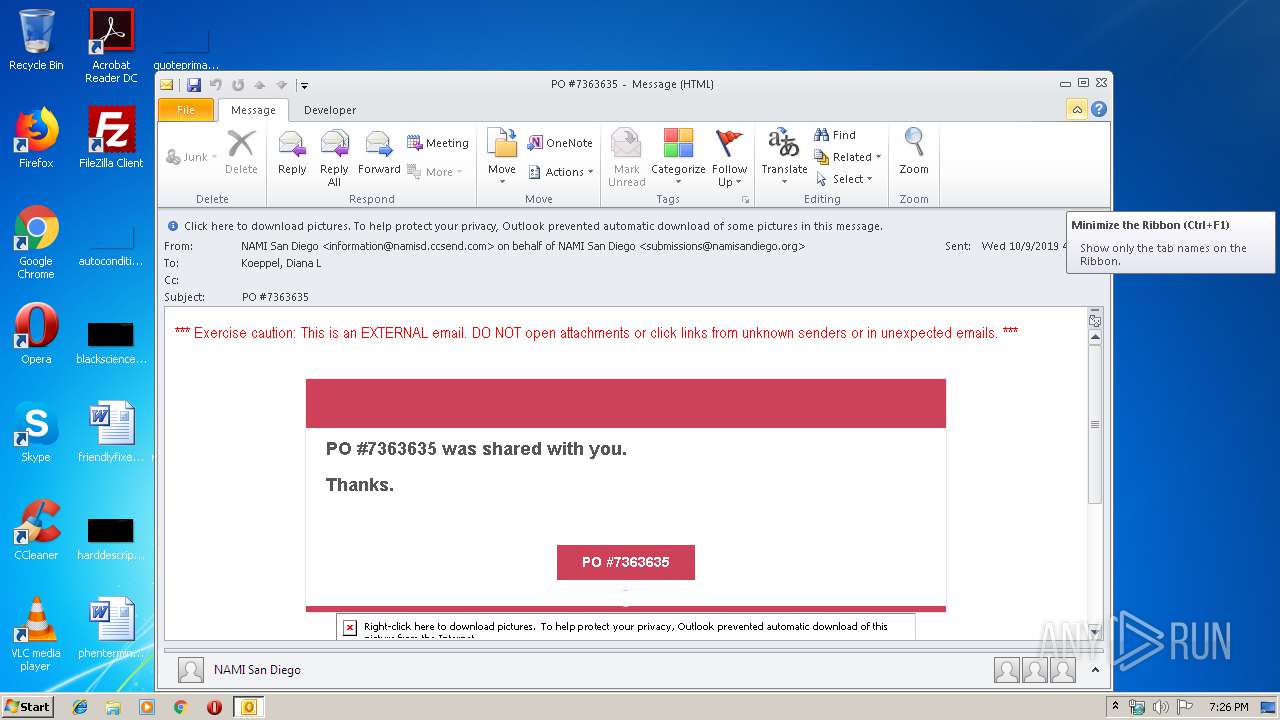
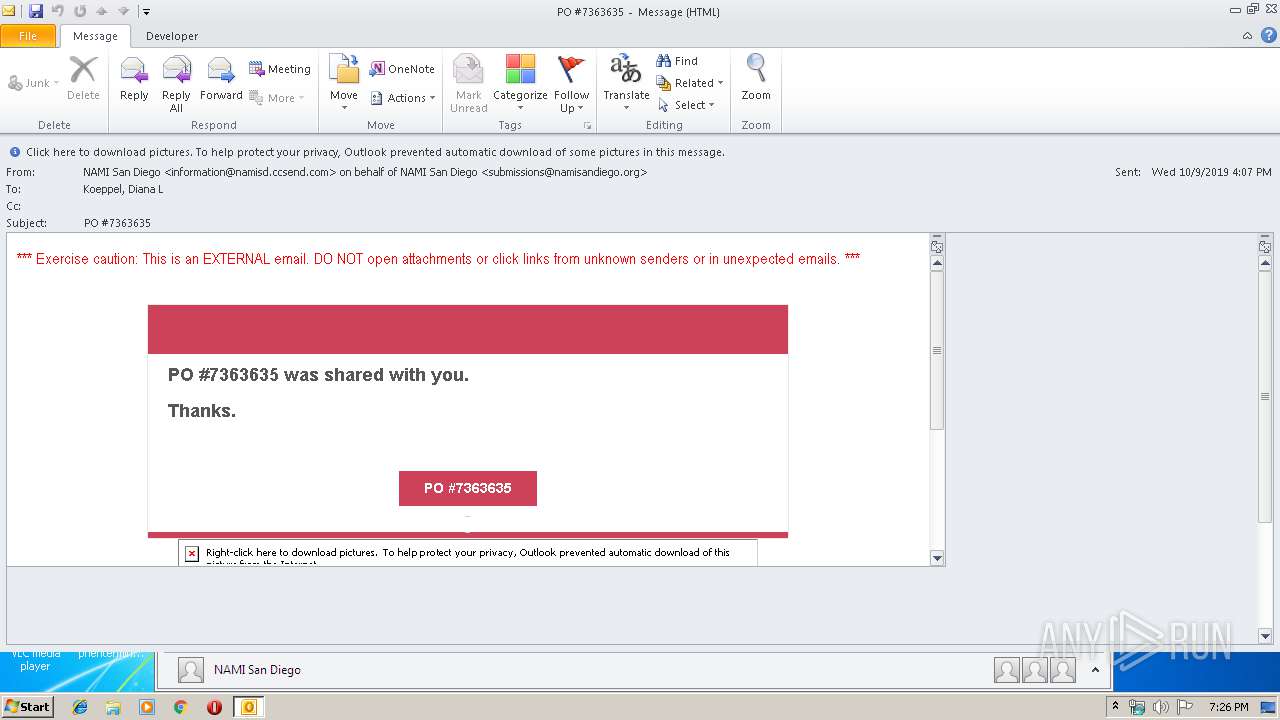
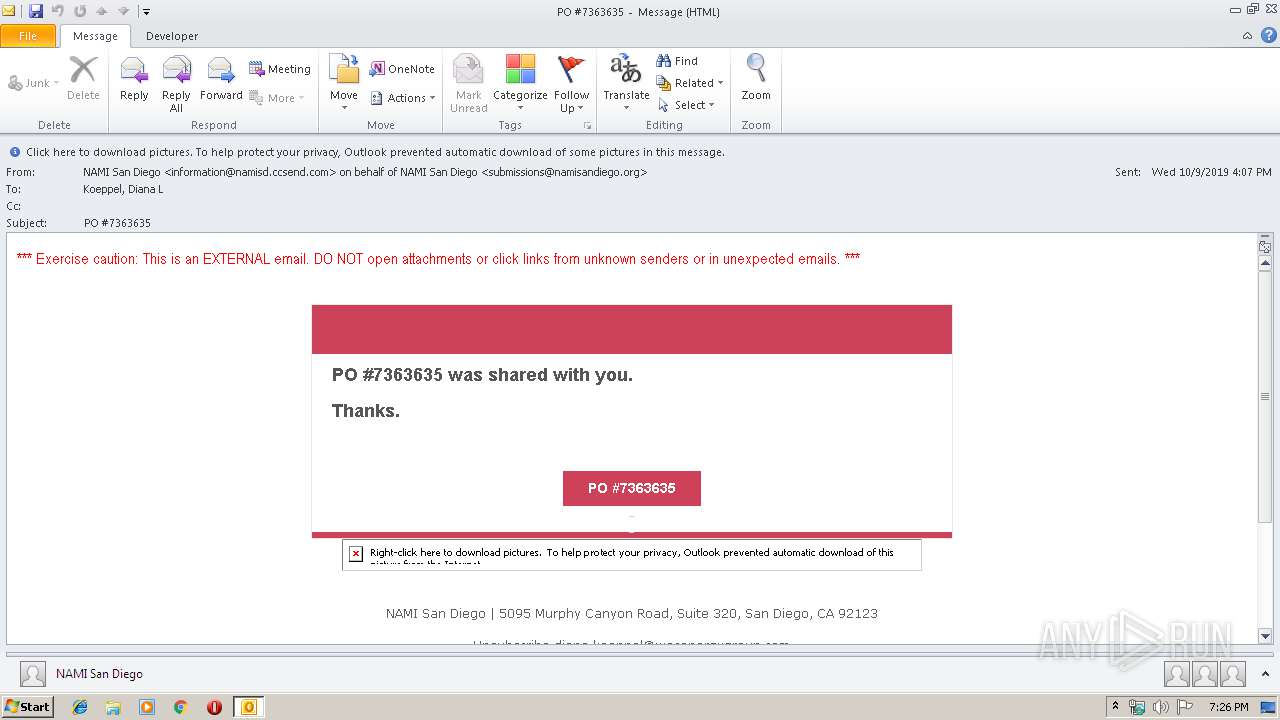
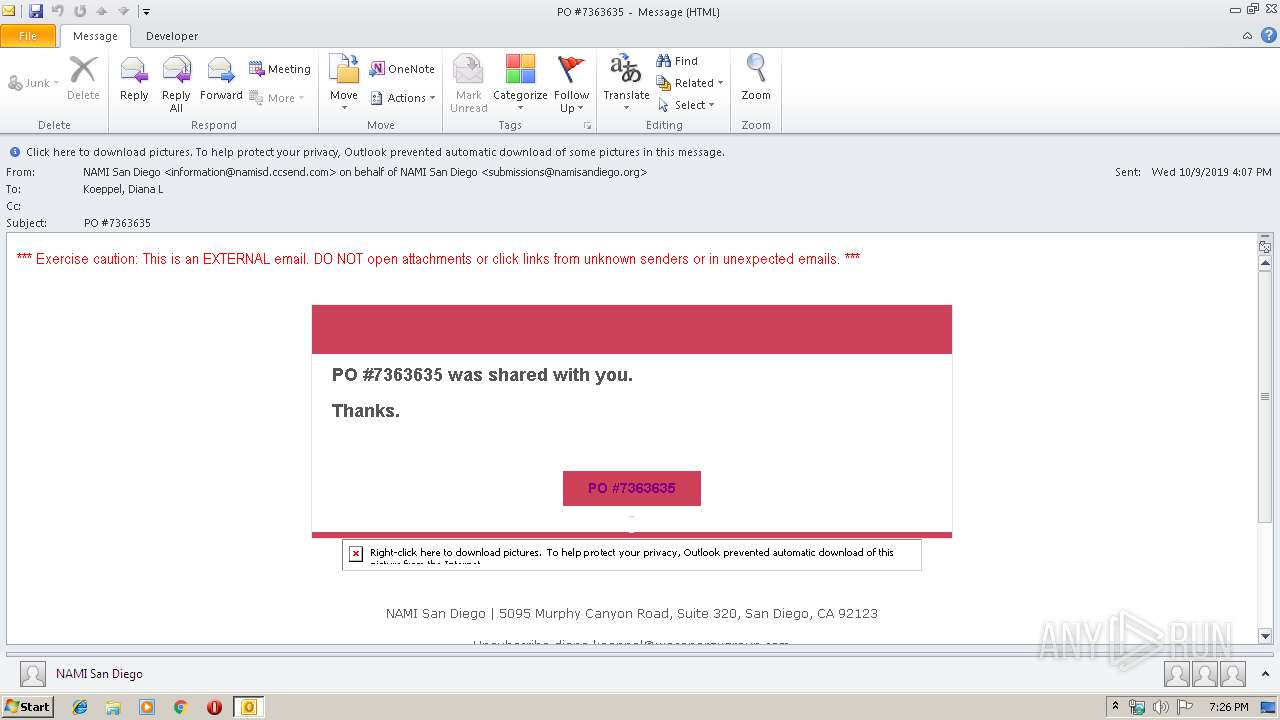
| File name: | PO.msg |
| Full analysis: | https://app.any.run/tasks/bb5be980-4443-4d92-aee3-5ad0b0b18fb8 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 18:26:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 12239F4AFAFEA1F60D8796ADE0F1347F |
| SHA1: | BD1309153E001D311EBB4C188FF07349DCA86C1B |
| SHA256: | 371B396133F4F1AB5C2E3693DF39F5C96CD2B1AC2B0B06F4D5EEB734F9AB8DE8 |
| SSDEEP: | 1536:MyJblNjG7G/LRBeMN+2i2We1RCyXB0Ce2CJPpnsMb6nSn:M0jJa2i2We1R5x072CJx |
MALICIOUS
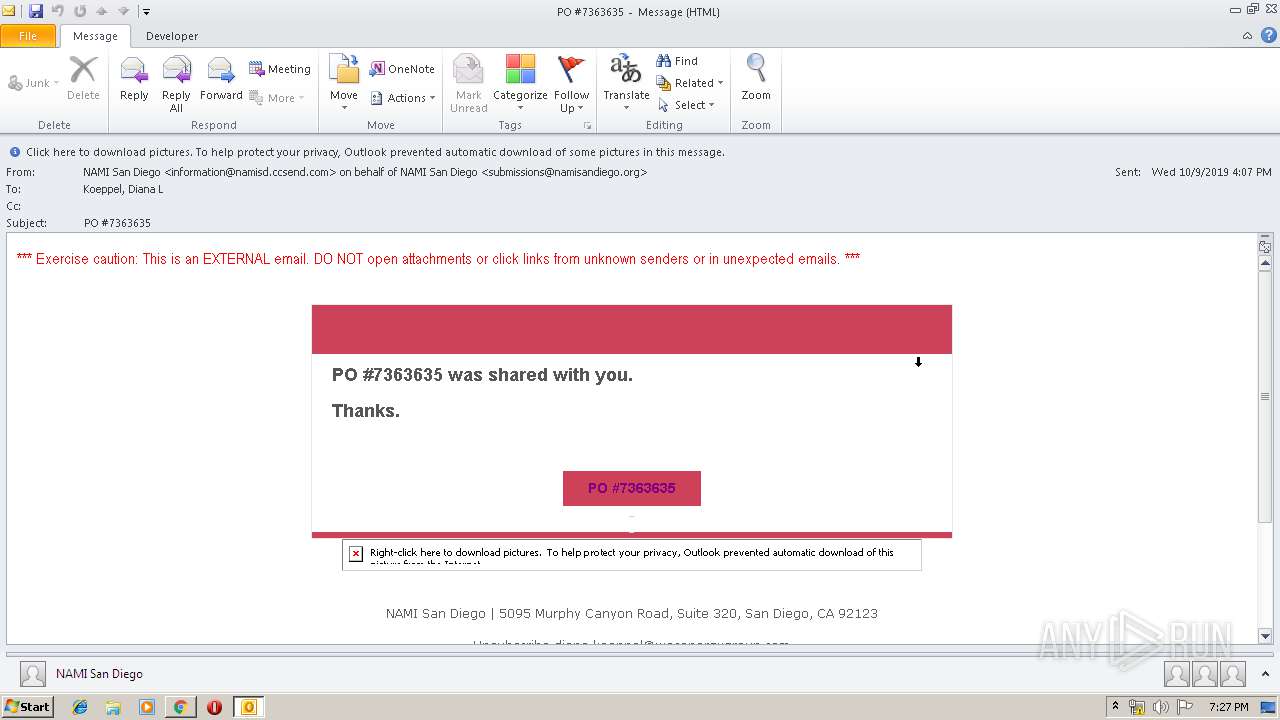
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2924)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2924)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2924)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2152)
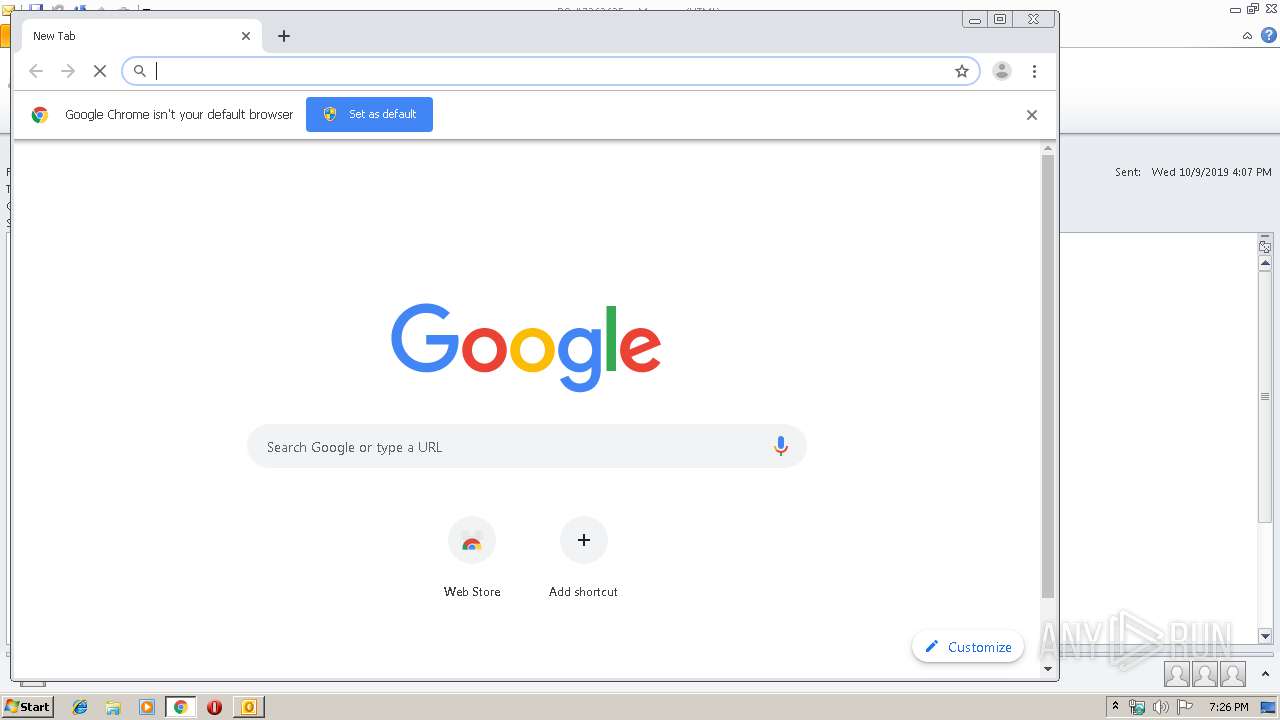
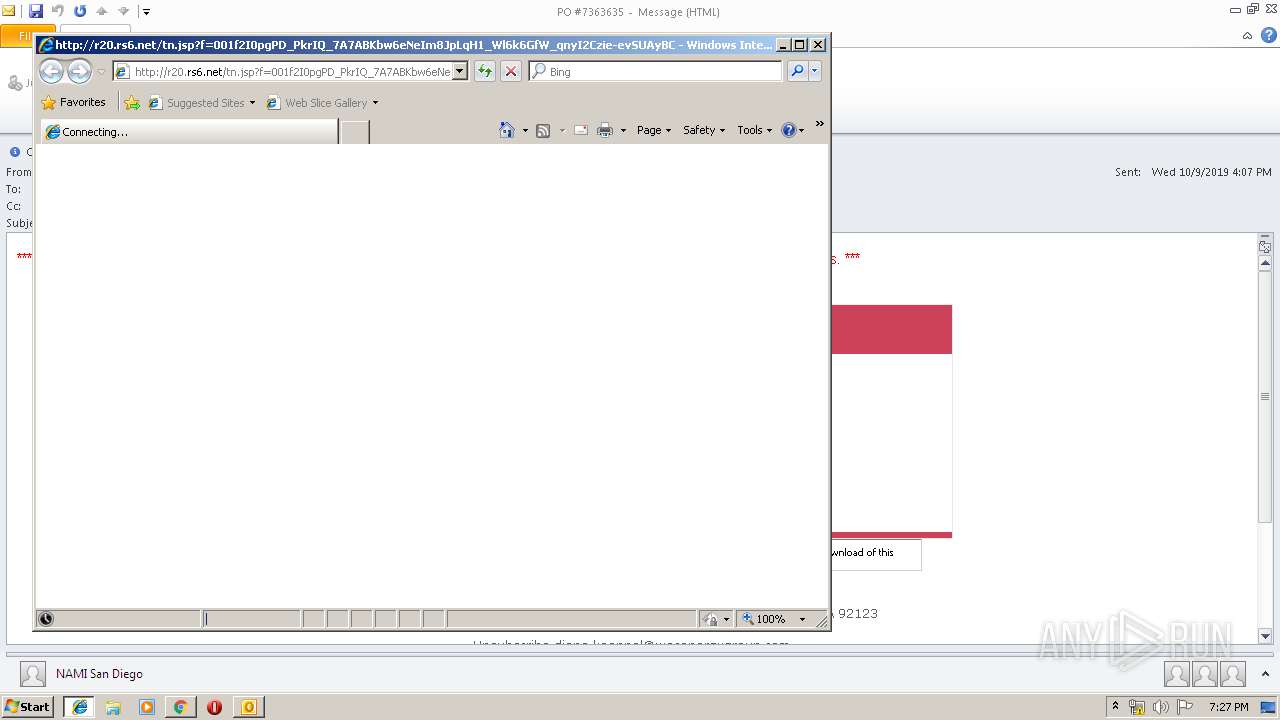
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2924)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2924)
Changes internet zones settings
- iexplore.exe (PID: 768)
- iexplore.exe (PID: 3224)
Reads internet explorer settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3552)
Application launched itself
- iexplore.exe (PID: 768)
- chrome.exe (PID: 2152)
Reads Internet Cache Settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 3552)
Creates files in the user directory
- iexplore.exe (PID: 768)
Reads settings of System Certificates
- iexplore.exe (PID: 768)
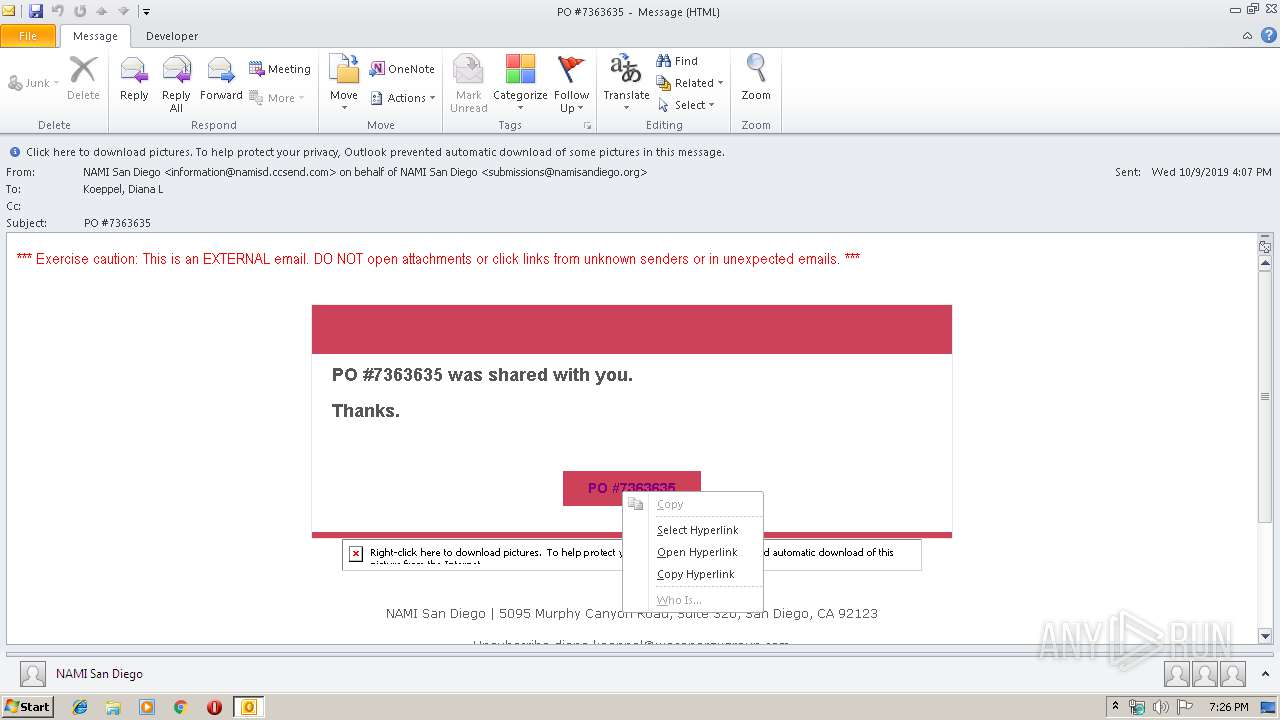
Manual execution by user
- chrome.exe (PID: 2152)
Reads the hosts file
- chrome.exe (PID: 2152)
- chrome.exe (PID: 544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
77
Monitored processes
40
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3675066545618780289 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7187763636172988438 --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
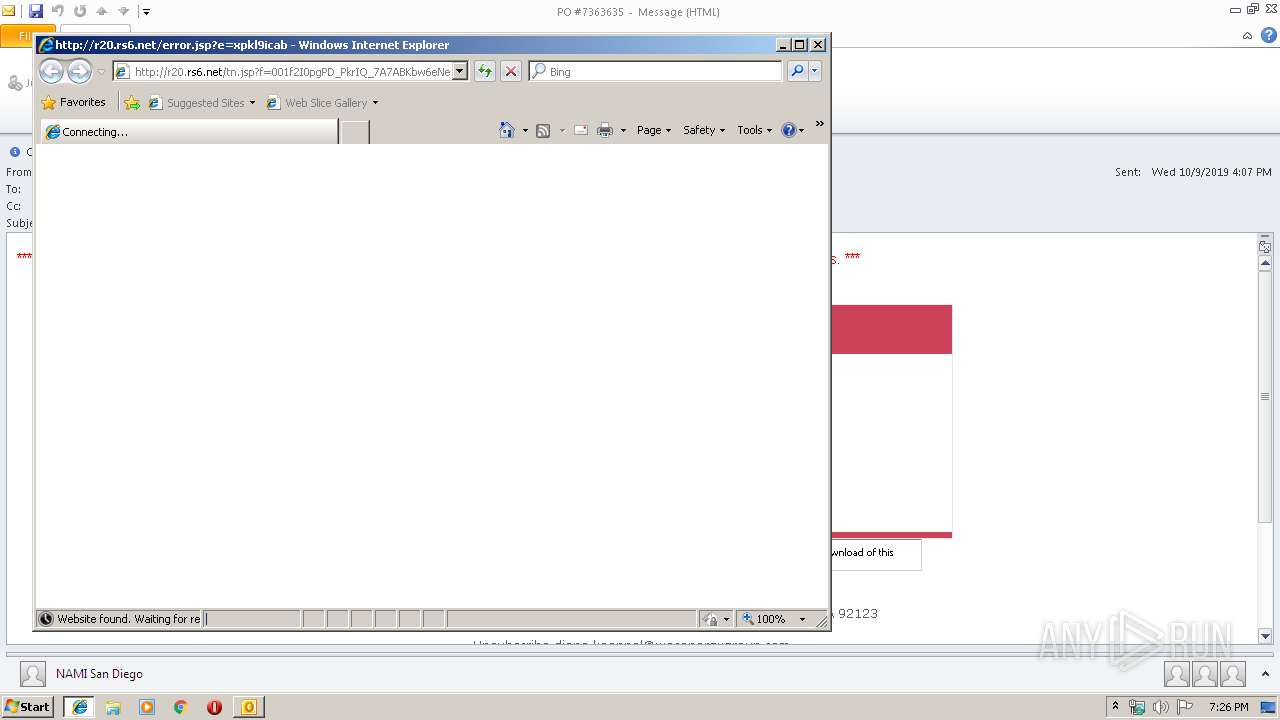
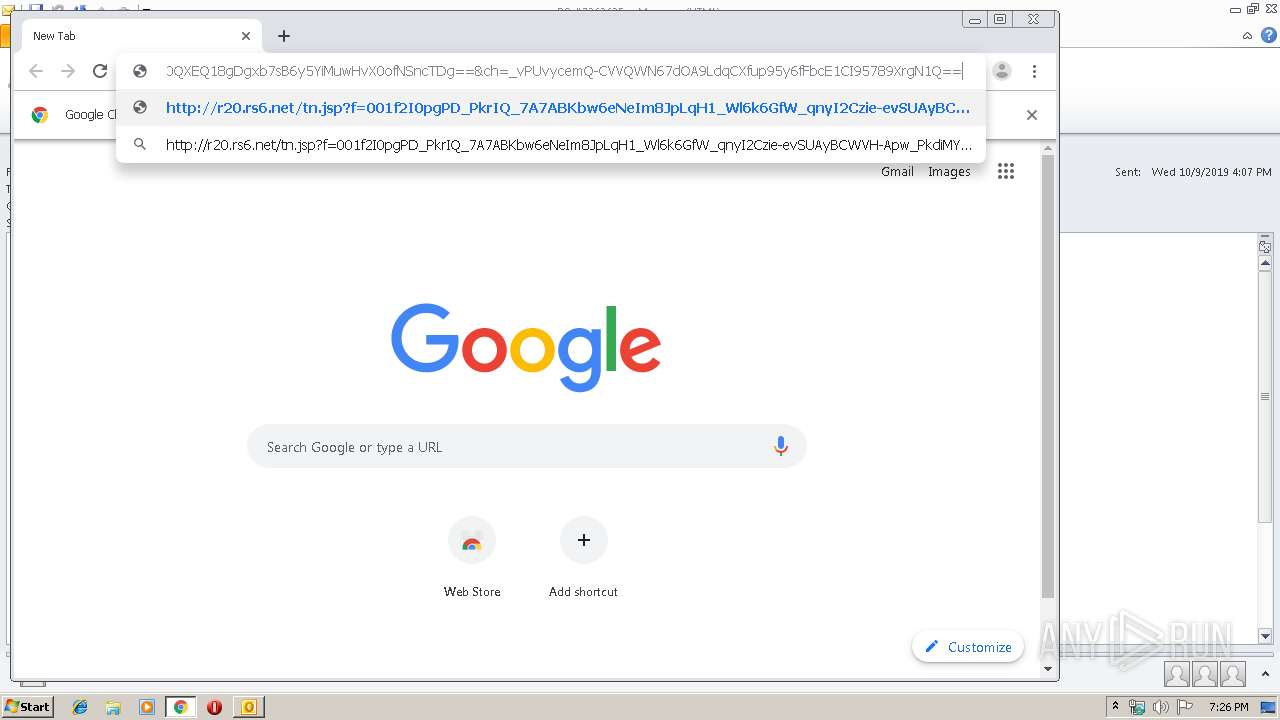
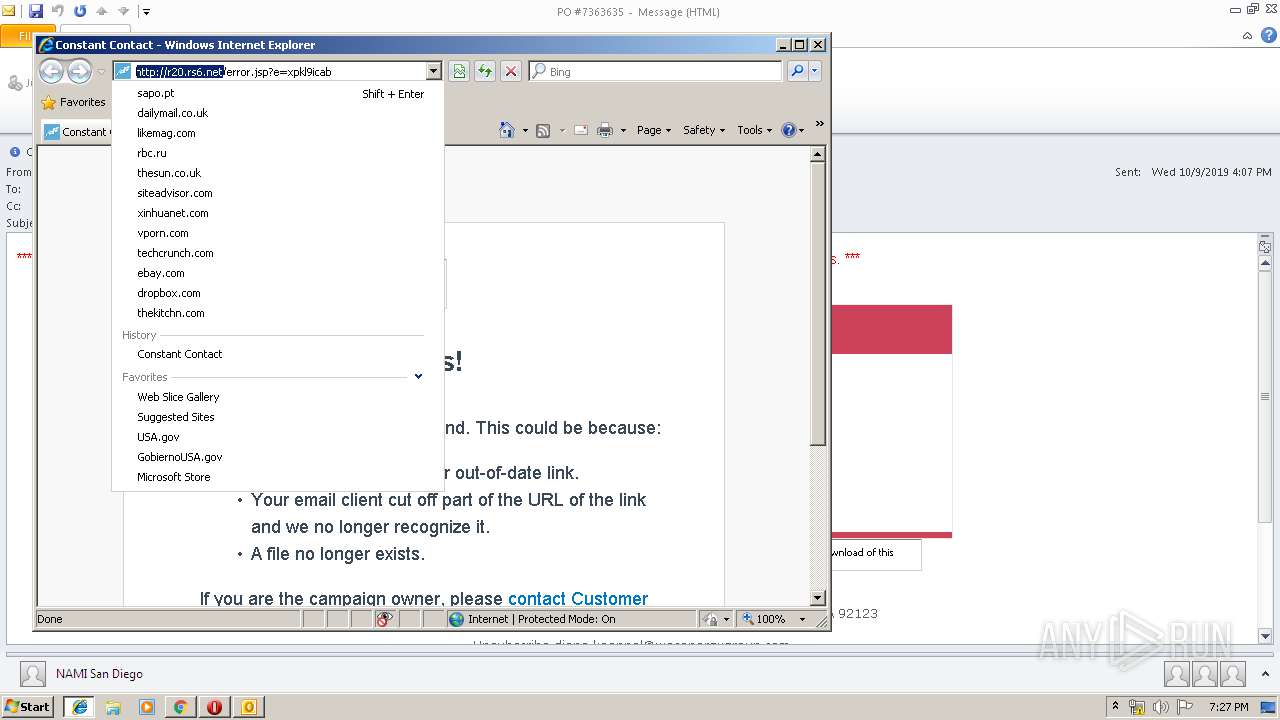
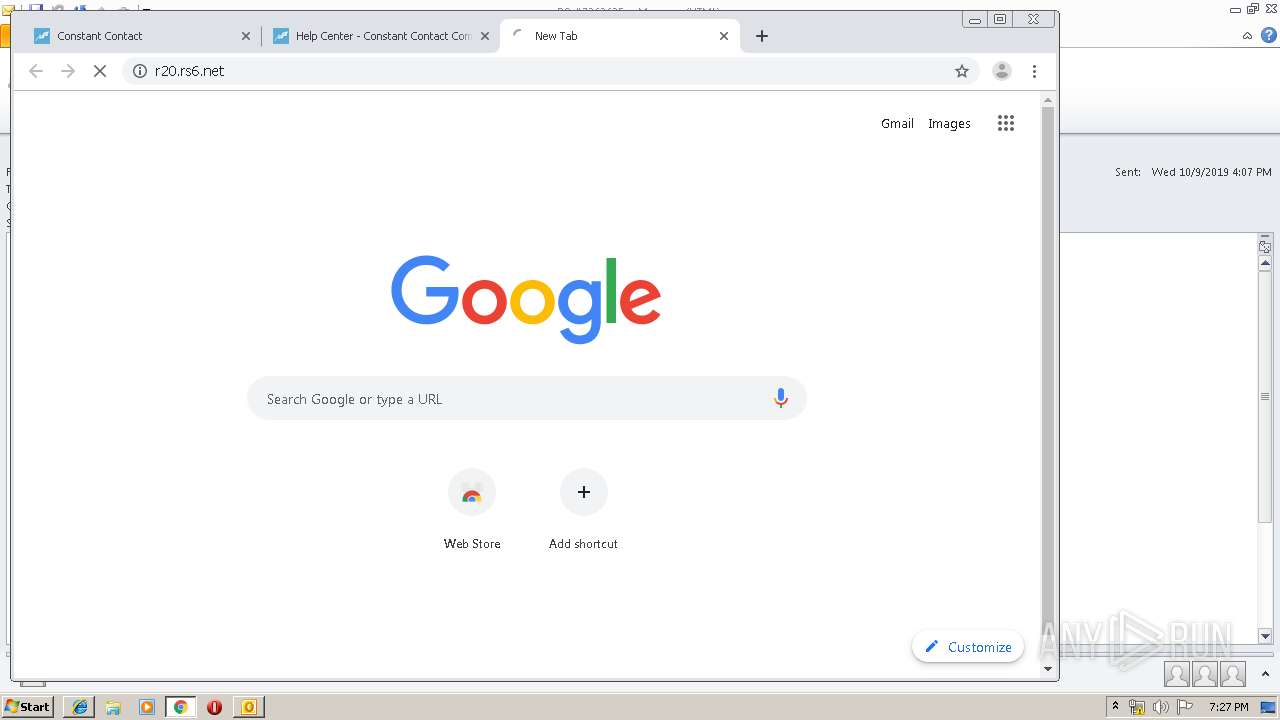
| 768 | "C:\Program Files\Internet Explorer\iexplore.exe" http://r20.rs6.net/tn.jsp?f=001f2I0pgPD_PkrIQ_7A7ABKbw6eNeIm8JpLqH1_Wl6k6GfW_qnyI2Czie-evSUAyBCWVH-Apw_PkdiMYWuyXp3mMNGJ5-1YjiUwqpTkI8dxvU-ziv6Bjbf9072uQNEcx4OWiub9UdaEfbjbkjdQ1ru_g==&c=xC3YBWF9bjQ6r79lUO0QXEQ18gDgxb7sB6y5YiMuwHvX0ofNSncTDg==&ch=_vPUvycemQ-CVVQWN67dOA9LdqCXfup95y6fFbcE1CI95789XrgN1Q== | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8138598520673865749 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14668237154018556329 --mojo-platform-channel-handle=1244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7279319556751324910 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1383818008287034481 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=456323139674664863 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3181195540988636184 --mojo-platform-channel-handle=4400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383844833193908716,11391119926325249526,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13611660227020990834 --mojo-platform-channel-handle=4256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 790
Read events
2 152
Write events
611
Delete events
27
Modification events
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | u;" |
Value: 753B22006C0B0000010000000000000000000000 | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 6C0B0000AEEA910FCF7ED50100000000 | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2924) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
0
Suspicious files
79
Text files
280
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR63C6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019092020190921\index.dat | — | |
MD5:— | SHA256:— | |||
| 2924 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\N8AWBVVQ\ctct_logo_full-color[1].svg | image | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF26943C4D8135B417.TMP | — | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF04012802F9515B68.TMP | — | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019100920191010\index.dat | dat | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF64CEE96F401849A6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
96
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
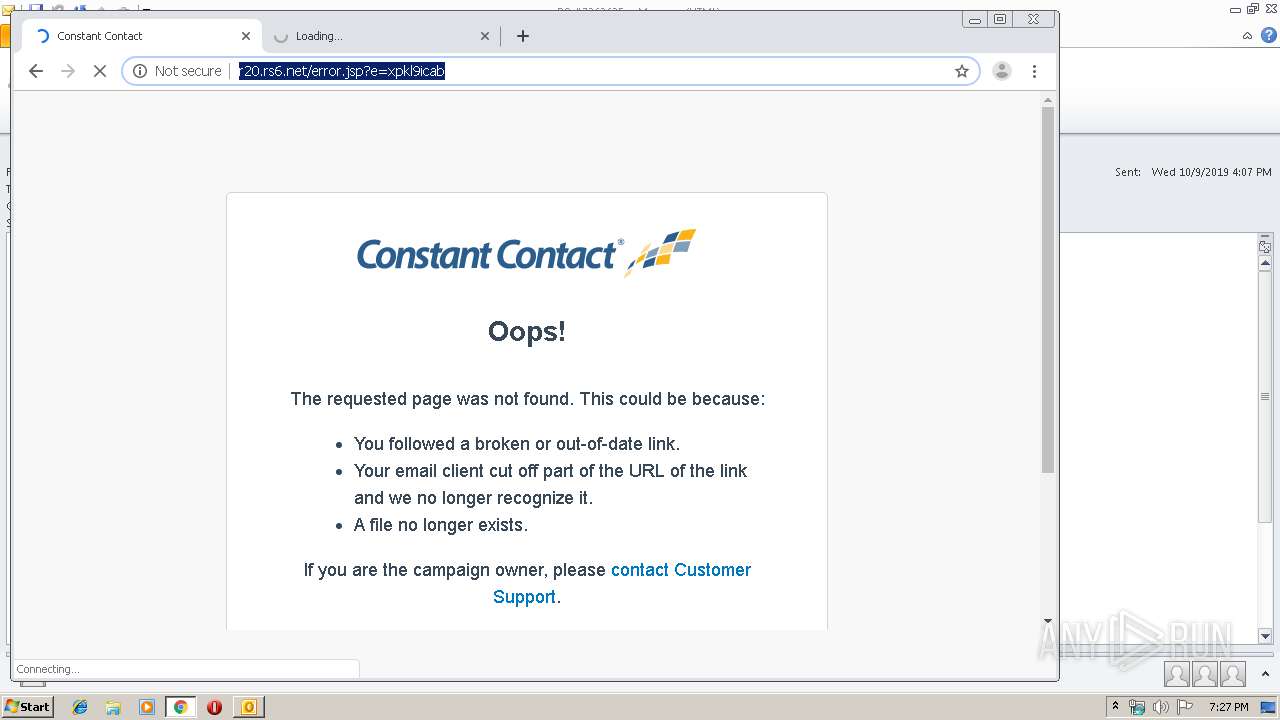
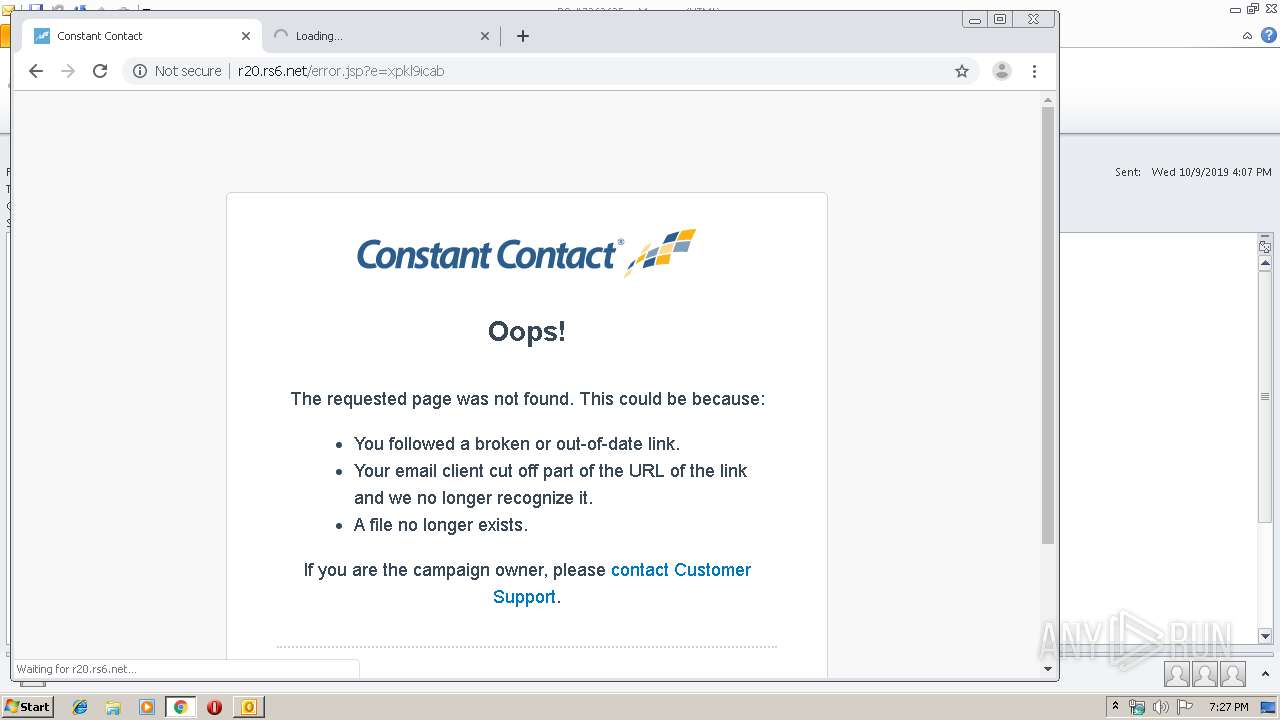
2876 | iexplore.exe | GET | 302 | 208.75.122.11:80 | http://r20.rs6.net/tn.jsp?f=001f2I0pgPD_PkrIQ_7A7ABKbw6eNeIm8JpLqH1_Wl6k6GfW_qnyI2Czie-evSUAyBCWVH-Apw_PkdiMYWuyXp3mMNGJ5-1YjiUwqpTkI8dxvU-ziv6Bjbf9072uQNEcx4OWiub9UdaEfbjbkjdQ1ru_g==&c=xC3YBWF9bjQ6r79lUO0QXEQ18gDgxb7sB6y5YiMuwHvX0ofNSncTDg==&ch=_vPUvycemQ-CVVQWN67dOA9LdqCXfup95y6fFbcE1CI95789XrgN1Q== | US | — | — | whitelisted |
2924 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
544 | chrome.exe | GET | 302 | 208.75.122.11:80 | http://r20.rs6.net/tn.jsp?f=001f2I0pgPD_PkrIQ_7A7ABKbw6eNeIm8JpLqH1_Wl6k6GfW_qnyI2Czie-evSUAyBCWVH-Apw_PkdiMYWuyXp3mMNGJ5-1YjiUwqpTkI8dxvU-ziv6Bjbf9072uQNEcx4OWiub9UdaEfbjbkjdQ1ru_g==&c=xC3YBWF9bjQ6r79lUO0QXEQ18gDgxb7sB6y5YiMuwHvX0ofNSncTDg==&ch=_vPUvycemQ-CVVQWN67dOA9LdqCXfup95y6fFbcE1CI95789XrgN1Q== | US | — | — | whitelisted |
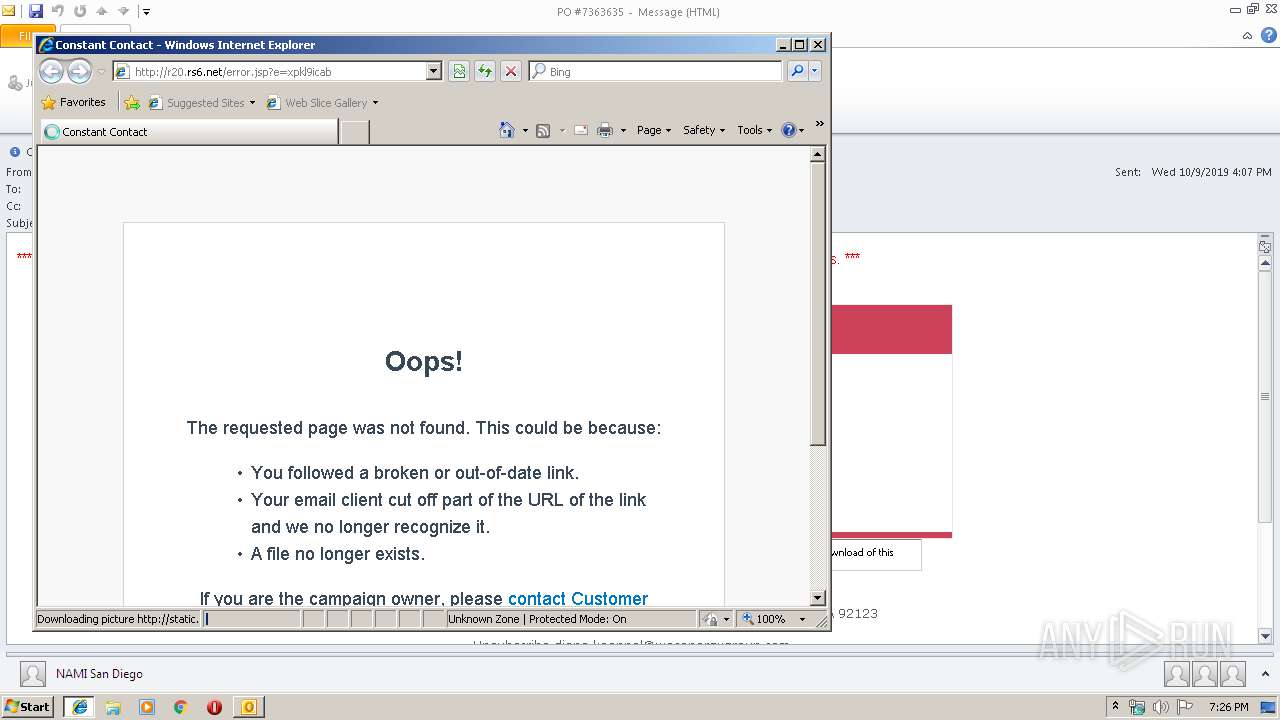
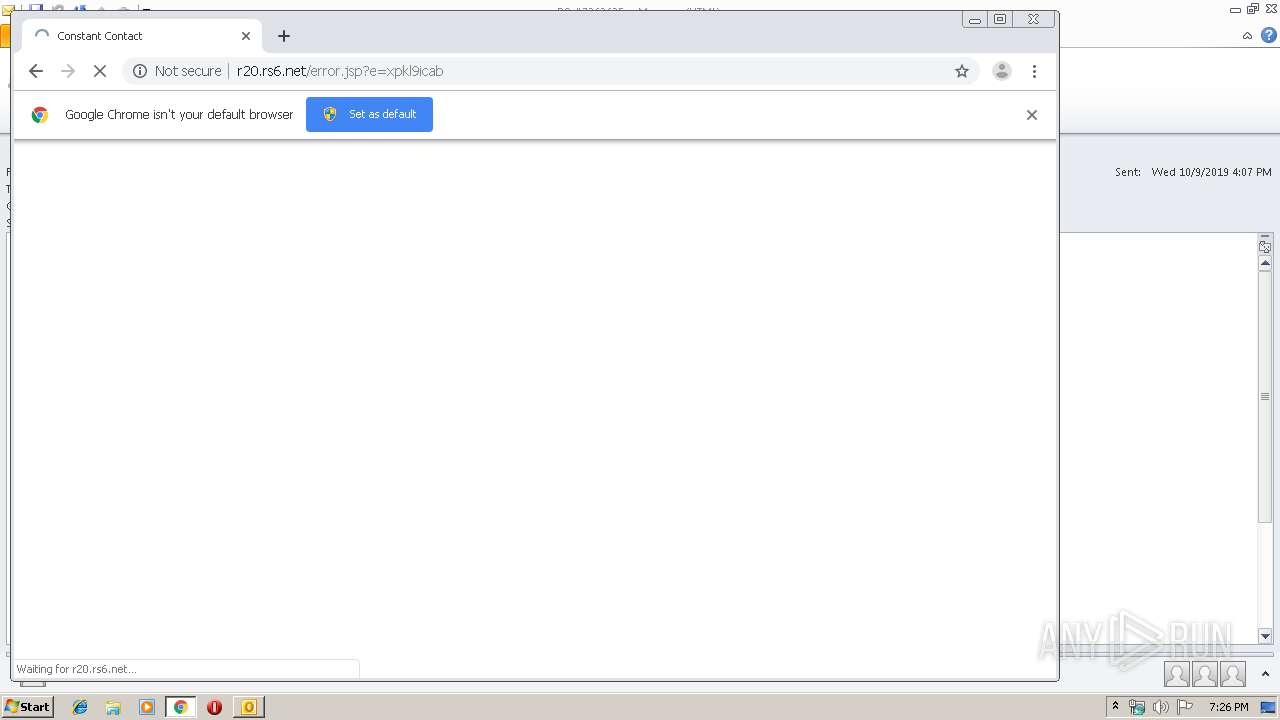
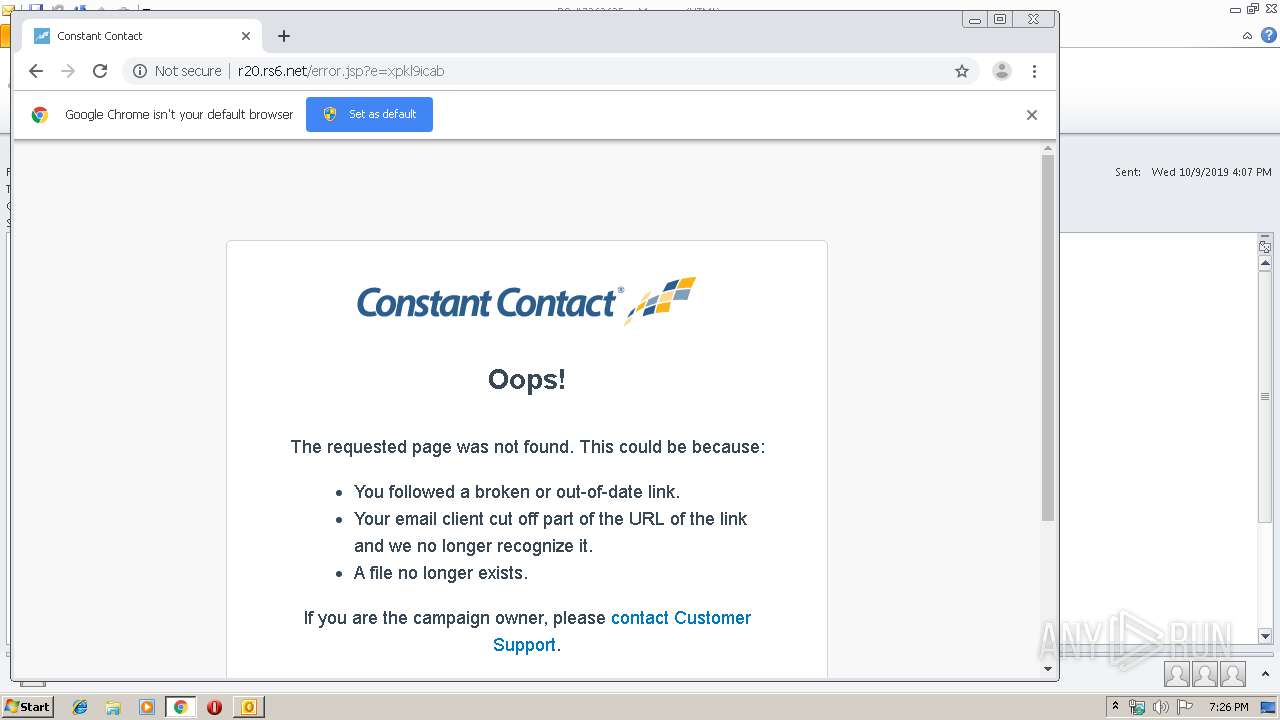
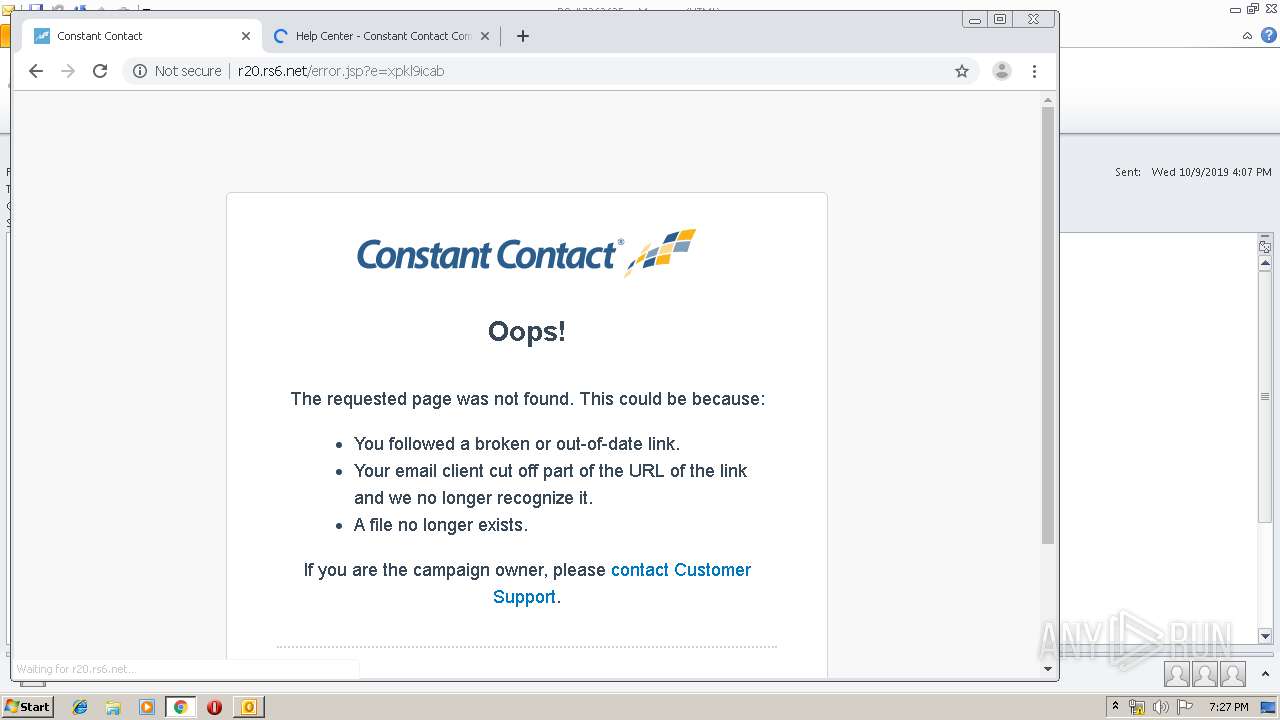
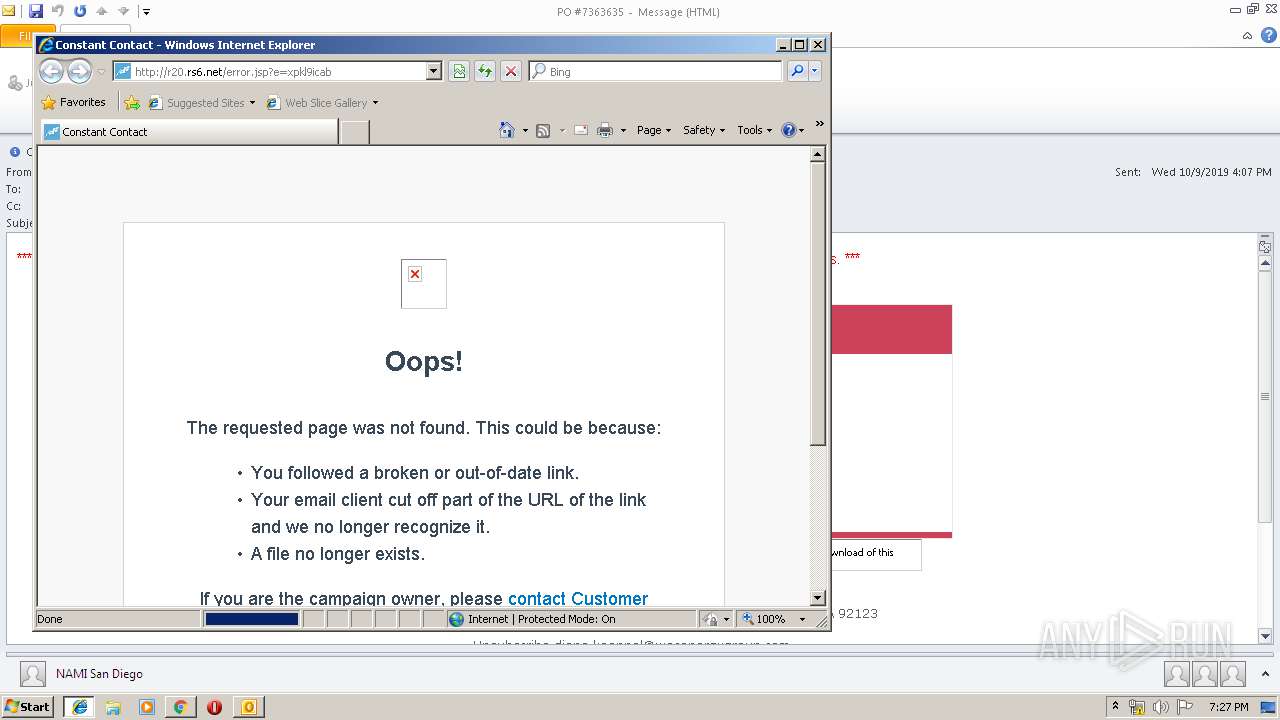
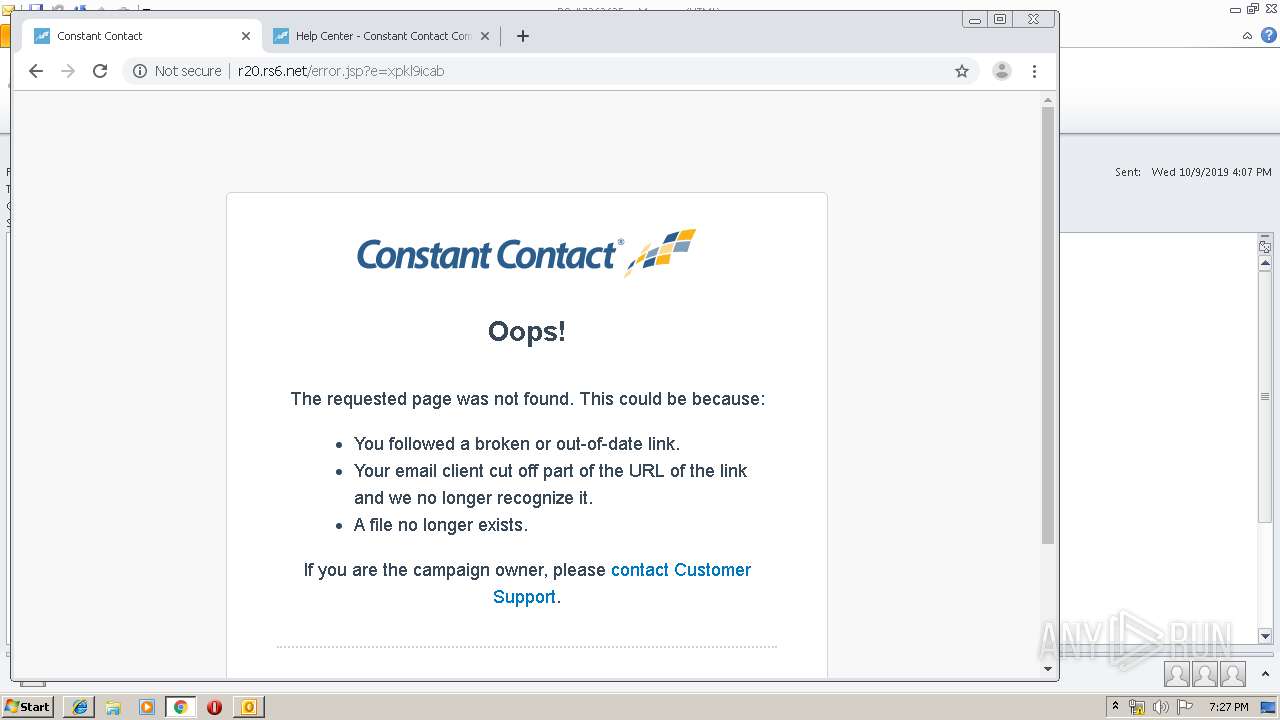
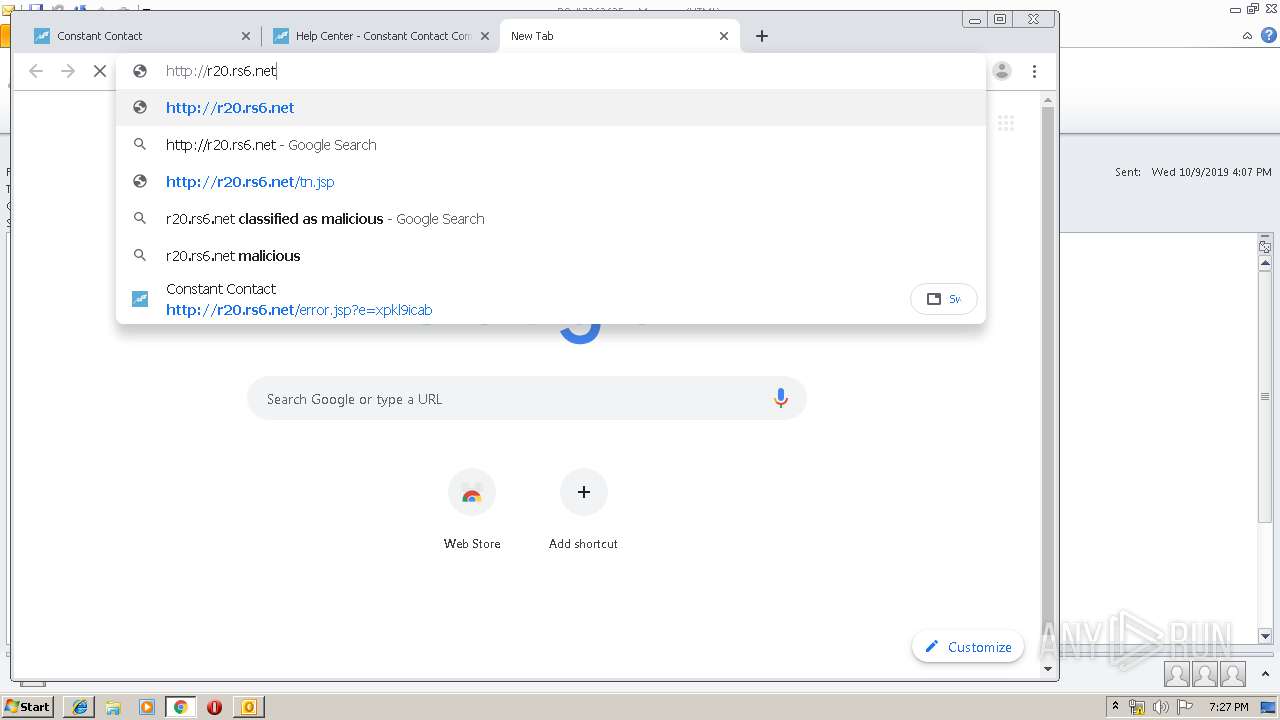
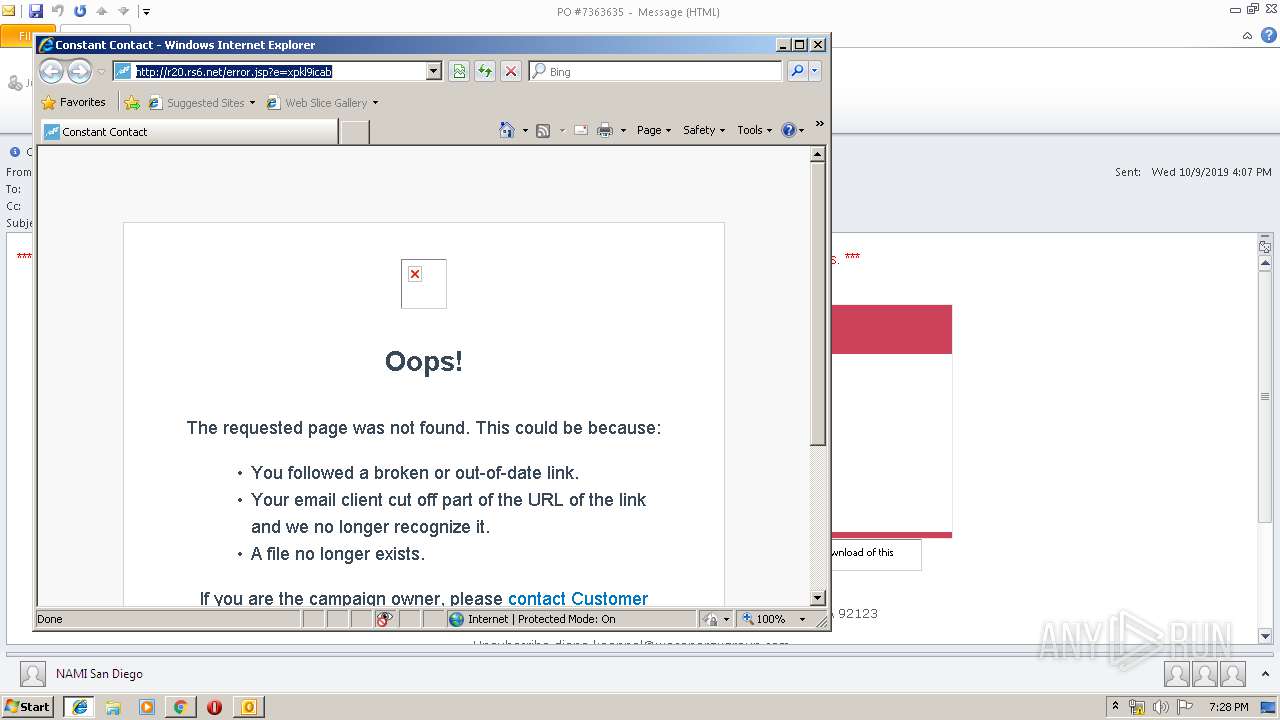
544 | chrome.exe | GET | — | 208.75.122.11:80 | http://r20.rs6.net/error.jsp?e=xpkl9icab | US | — | — | whitelisted |
544 | chrome.exe | GET | 301 | 104.17.55.175:80 | http://www.constantcontact.com/favicon.ico | US | — | — | whitelisted |
544 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 529 b | whitelisted |
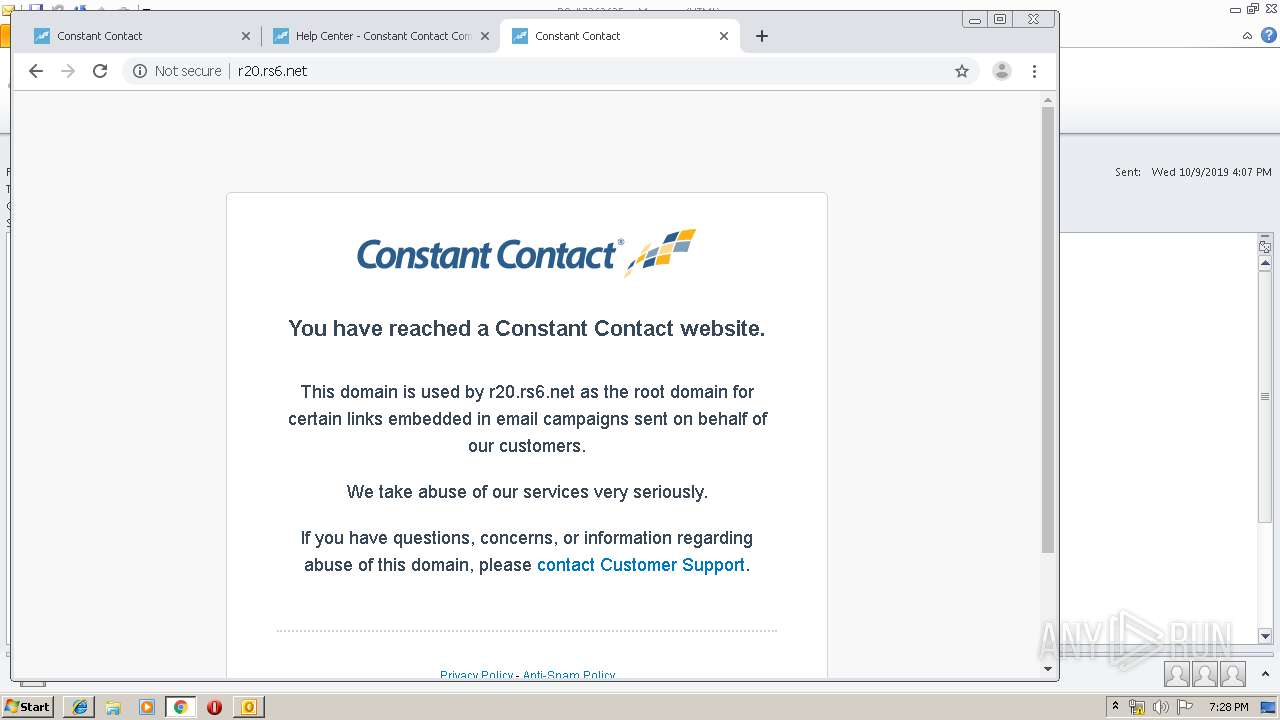
544 | chrome.exe | GET | 200 | 208.75.122.11:80 | http://r20.rs6.net/error.jsp?e=xpkl9icab | US | html | 6.71 Kb | whitelisted |
2876 | iexplore.exe | GET | 200 | 208.75.122.11:80 | http://r20.rs6.net/error.jsp?e=xpkl9icab | US | html | 6.71 Kb | whitelisted |
544 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 534 b | whitelisted |
544 | chrome.exe | GET | 200 | 104.109.88.197:80 | http://static.ctctcdn.com/lp/images/standard/logos/ctct_logo_full-color.svg | NL | image | 4.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2924 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
768 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2876 | iexplore.exe | 104.109.88.197:80 | static.ctctcdn.com | Akamai International B.V. | NL | whitelisted |
2876 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
544 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
544 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
544 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
r20.rs6.net |
| whitelisted |
www.bing.com |
| whitelisted |
static.ctctcdn.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
www.constantcontact.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |