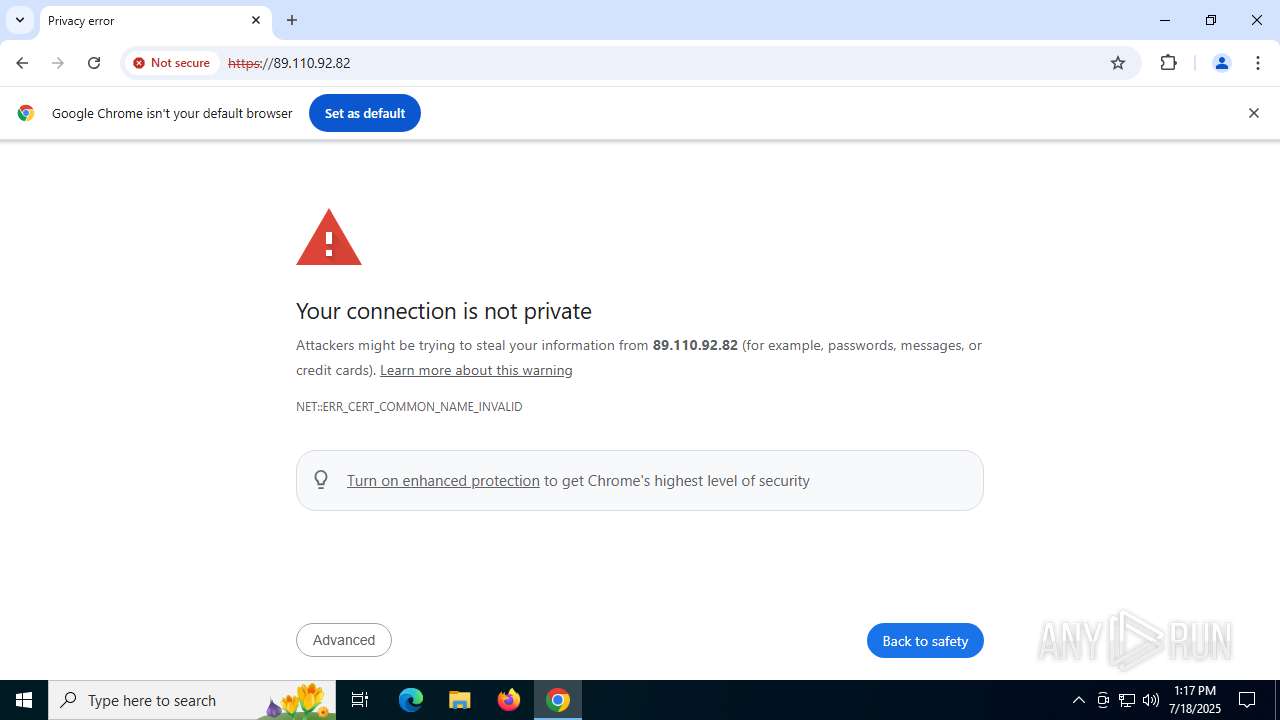
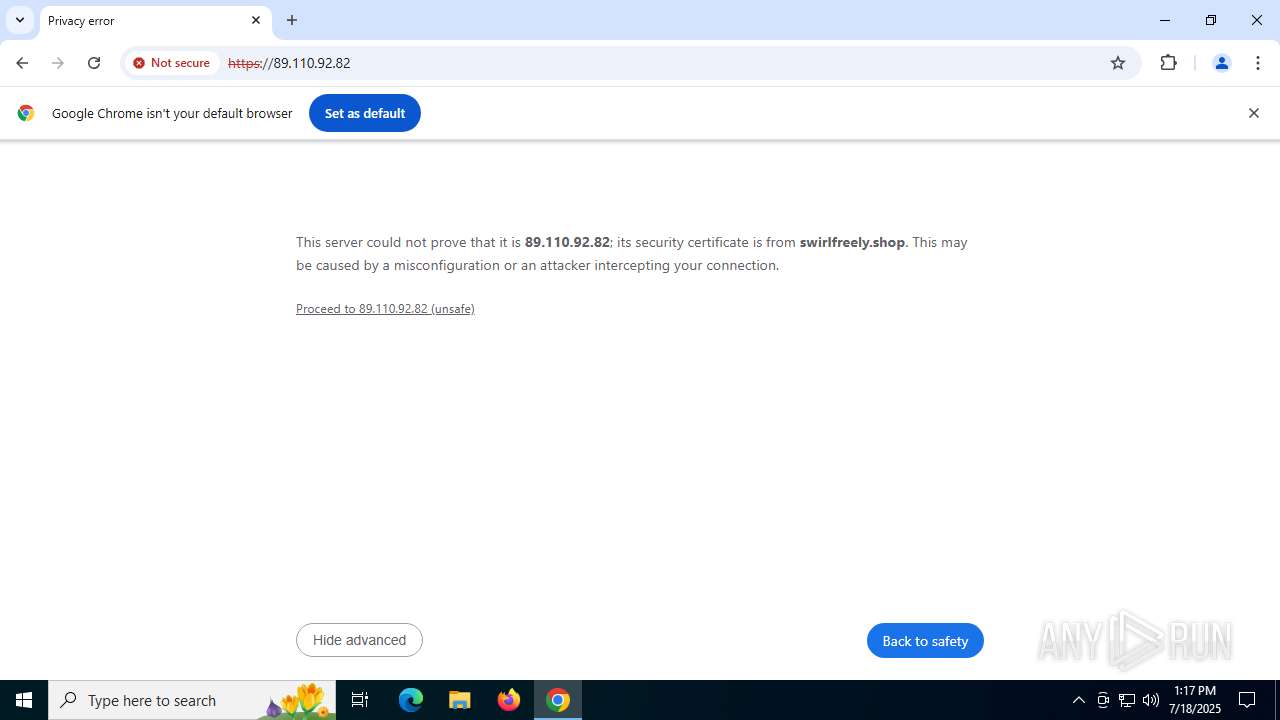
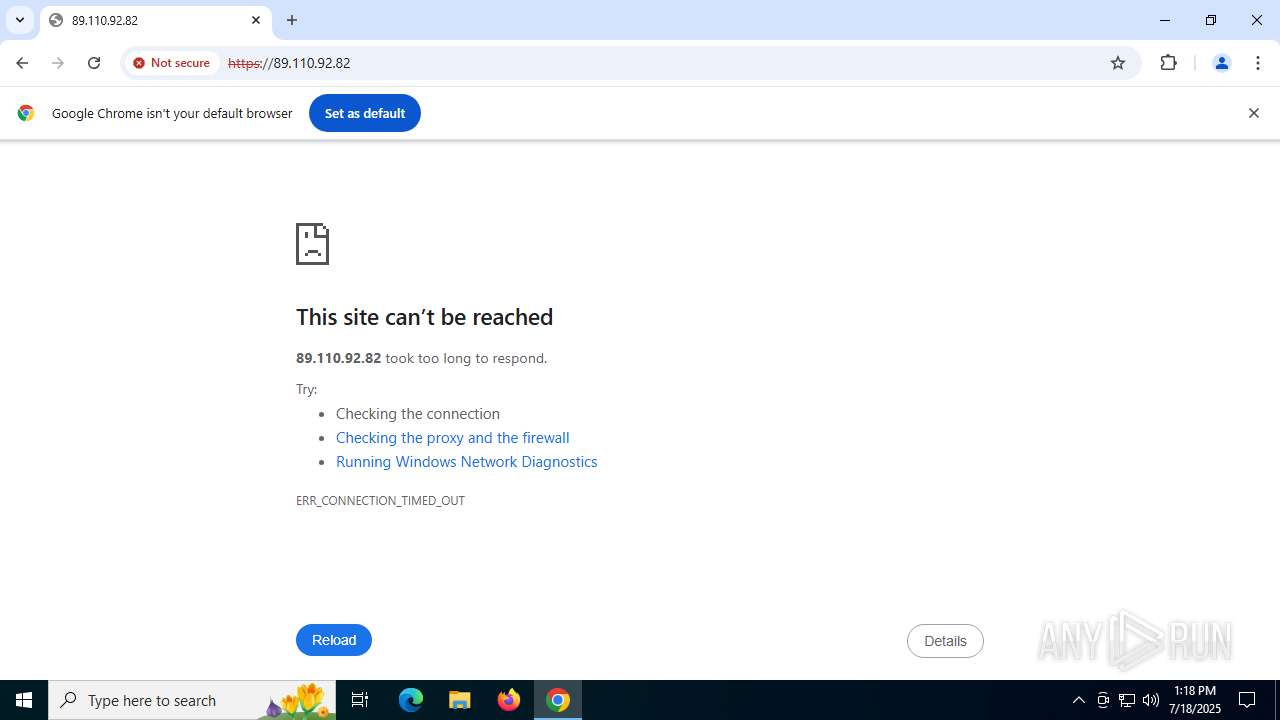
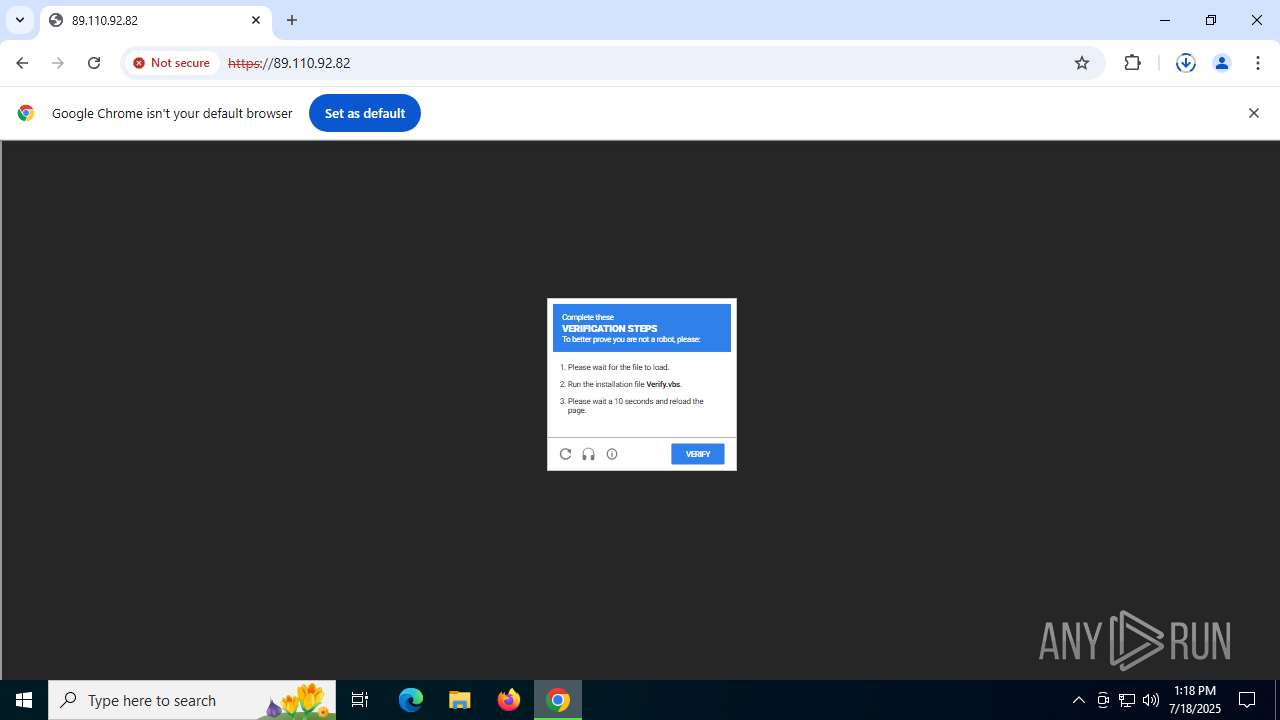
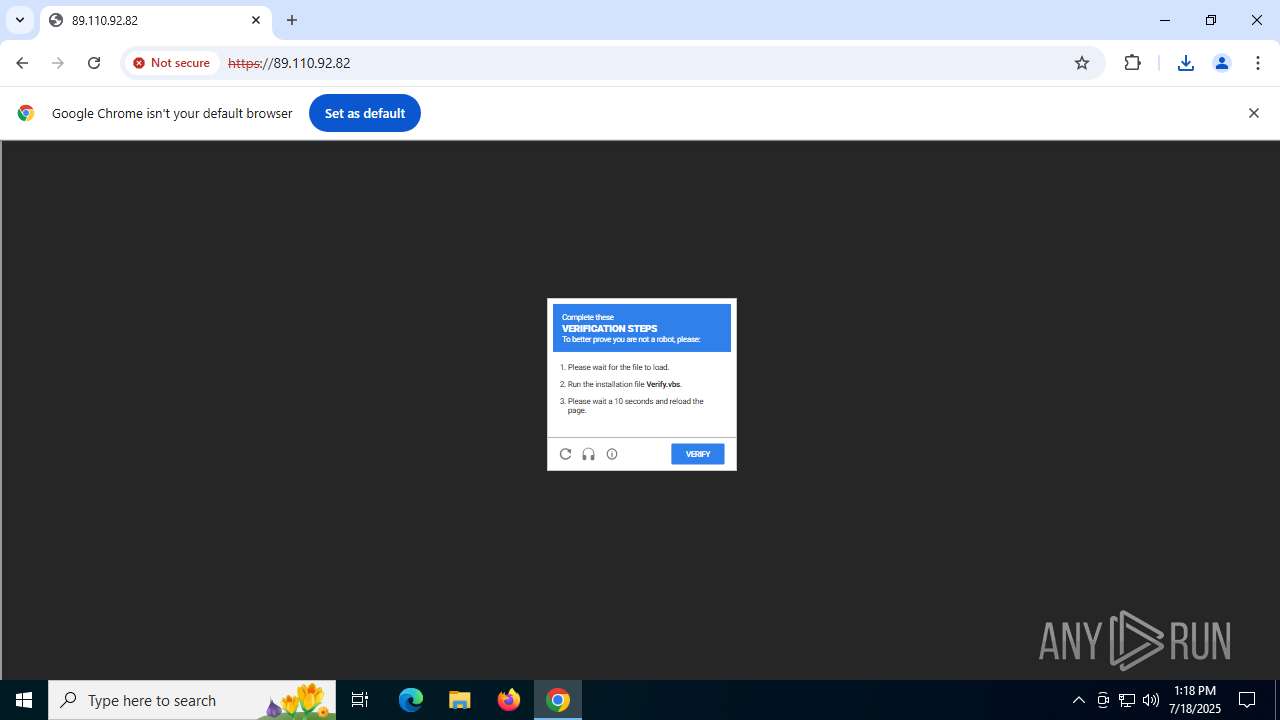
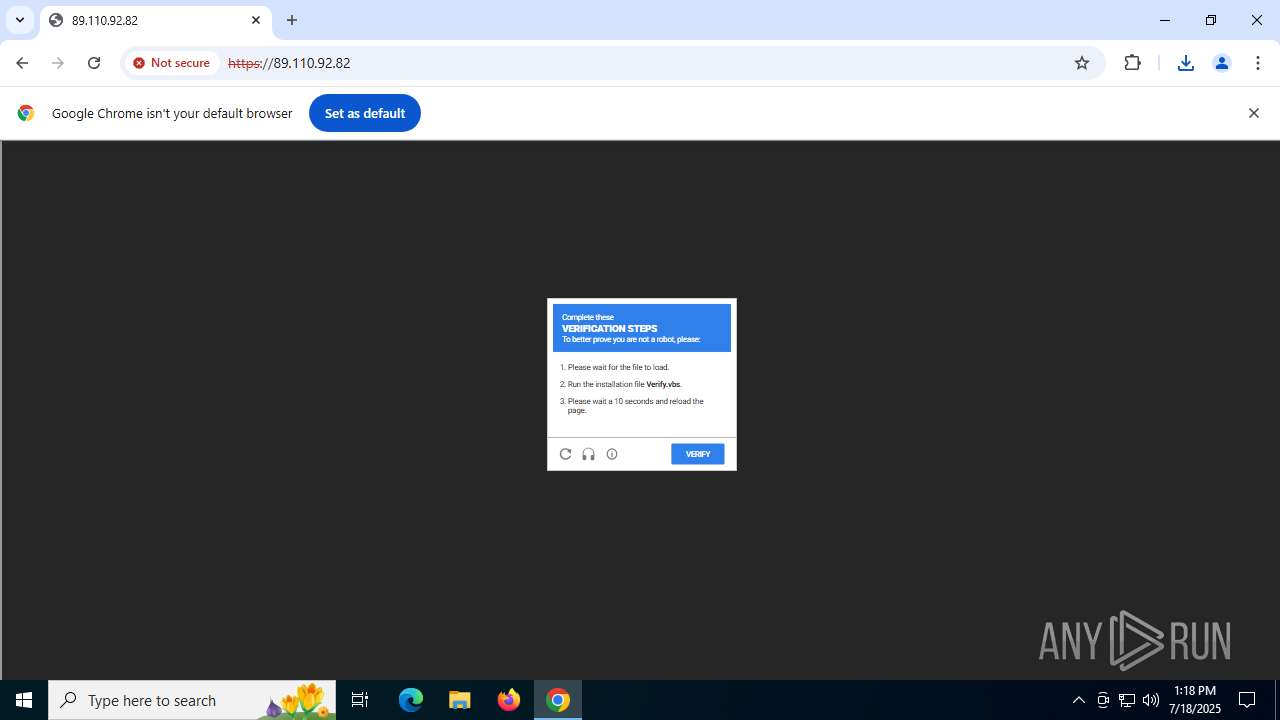
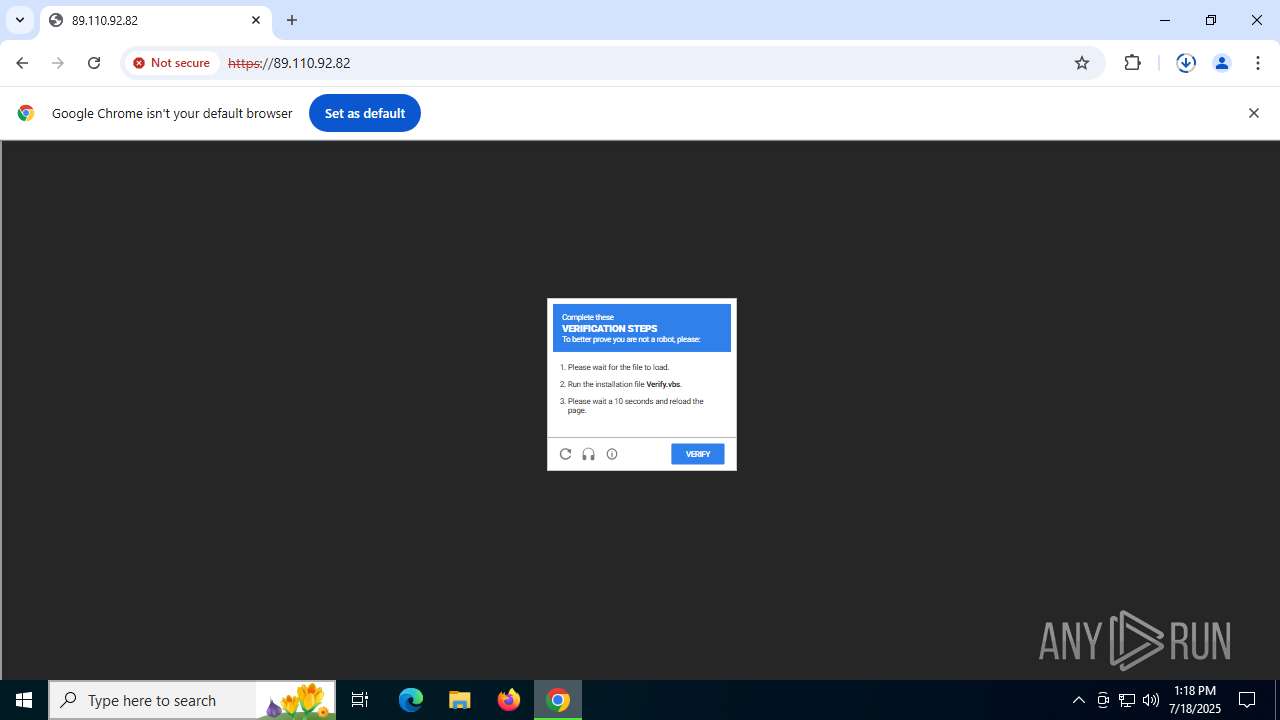
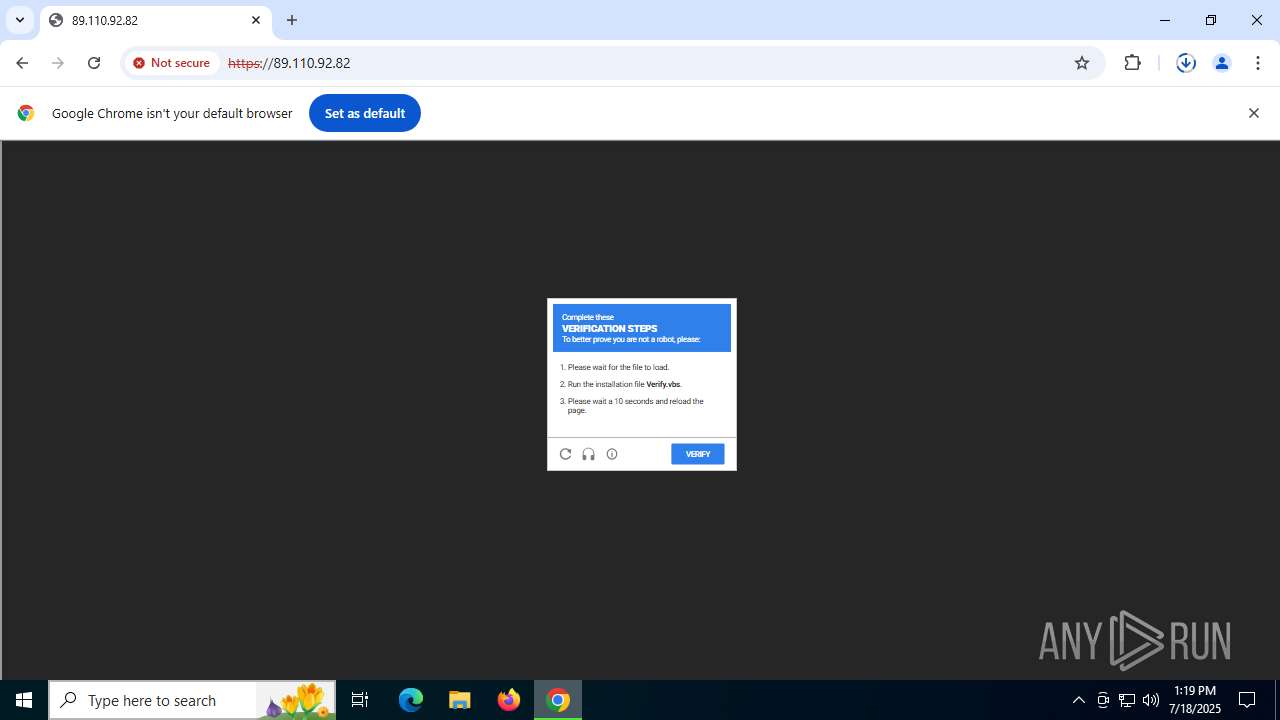
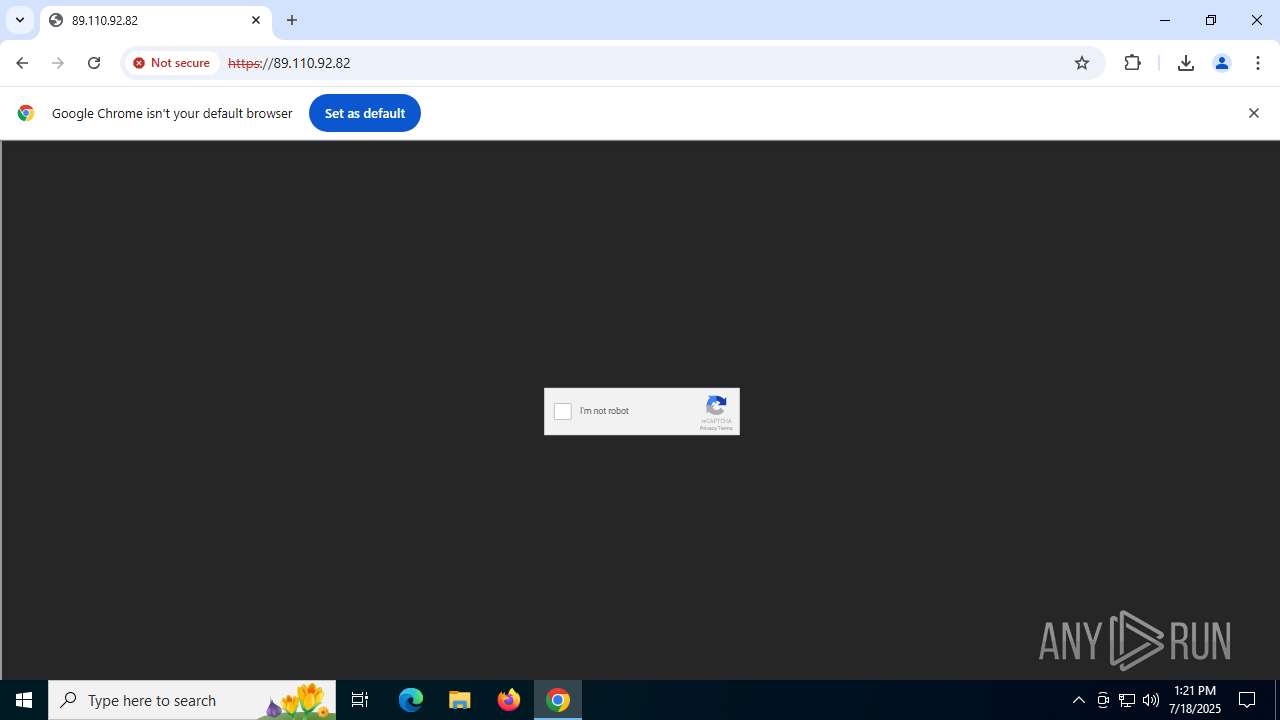
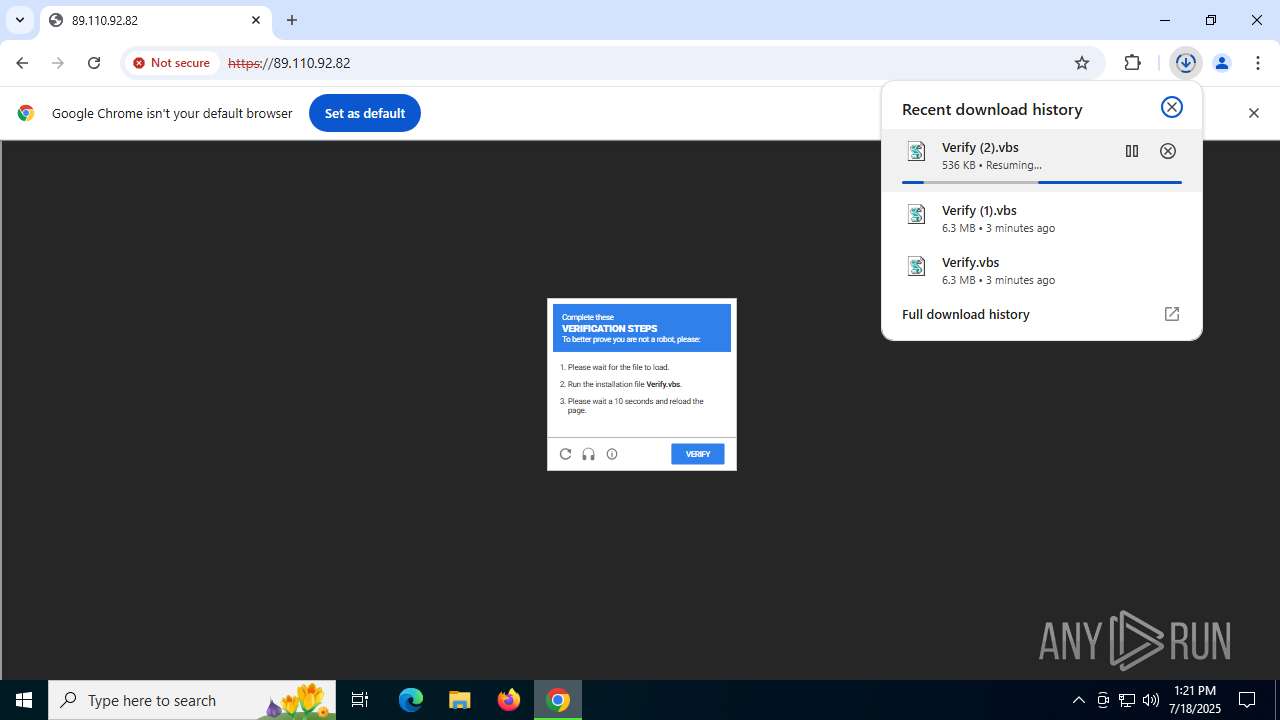
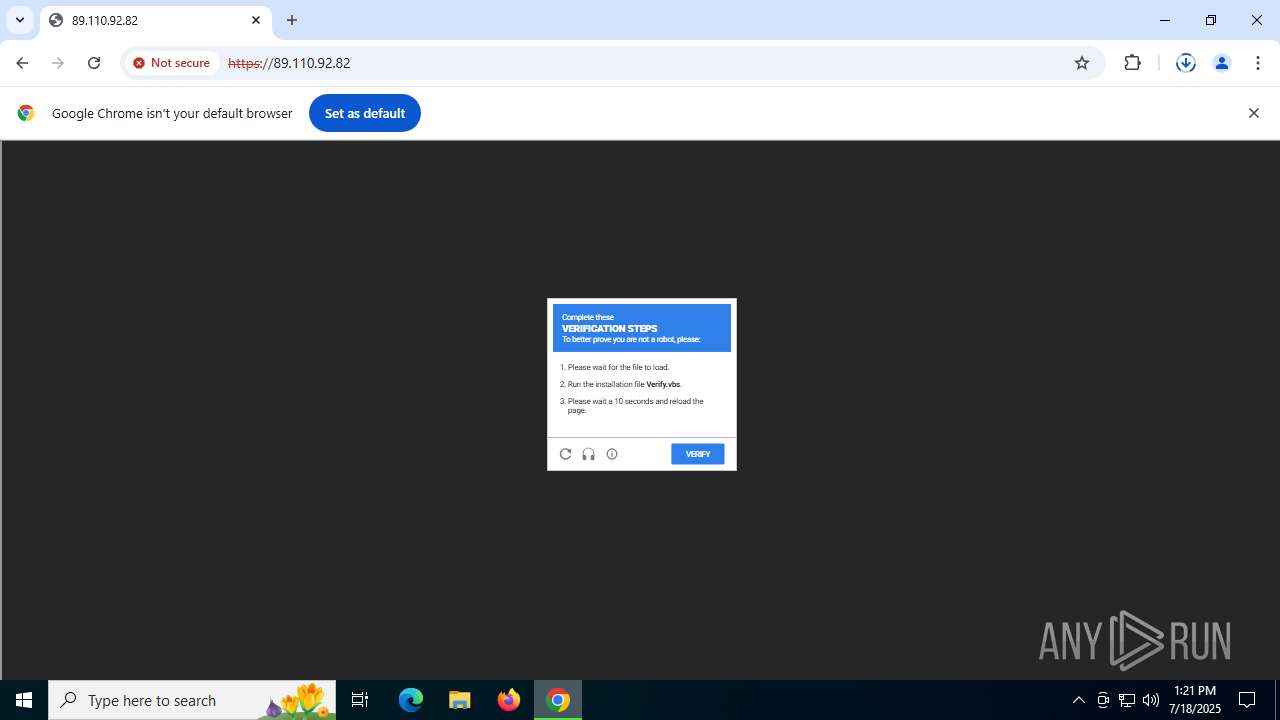
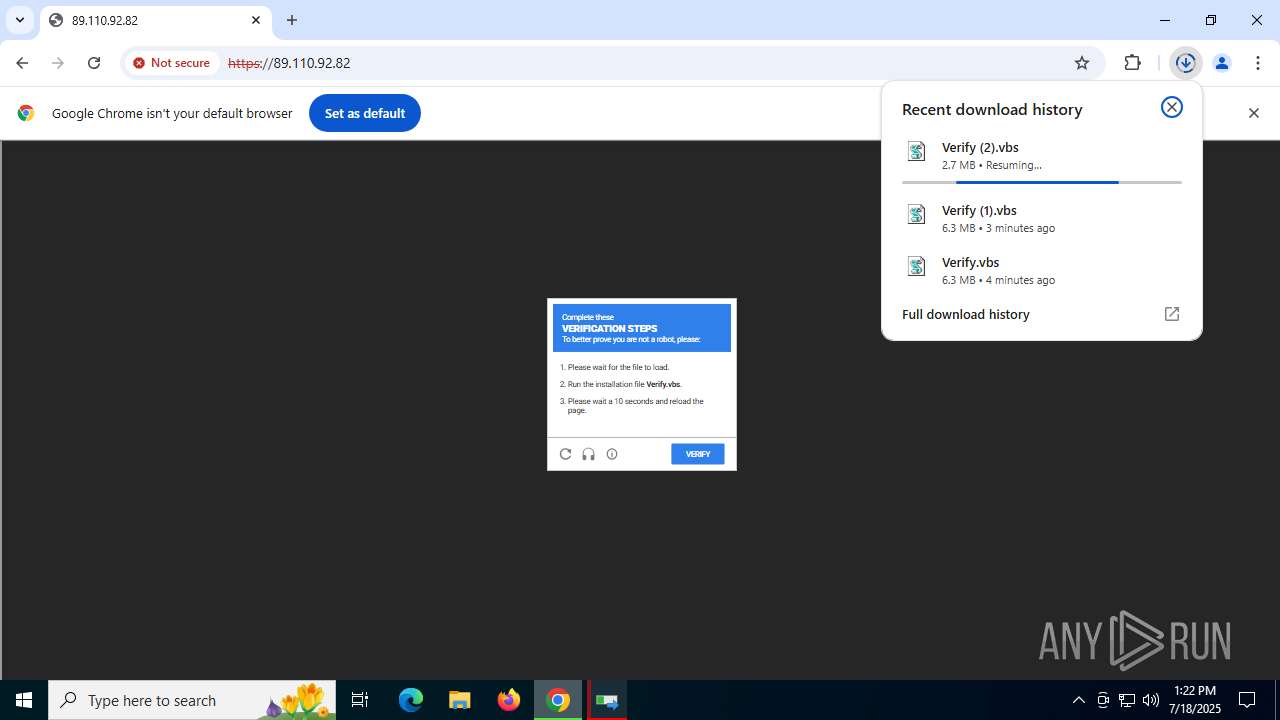
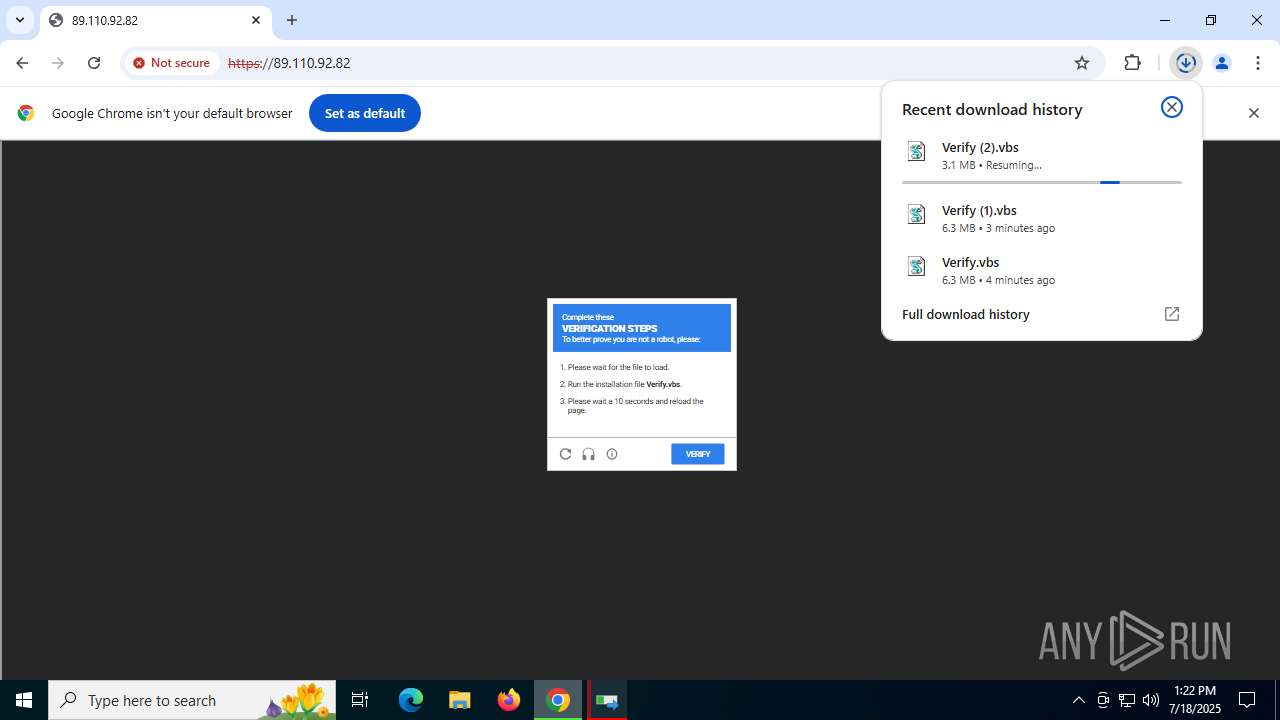
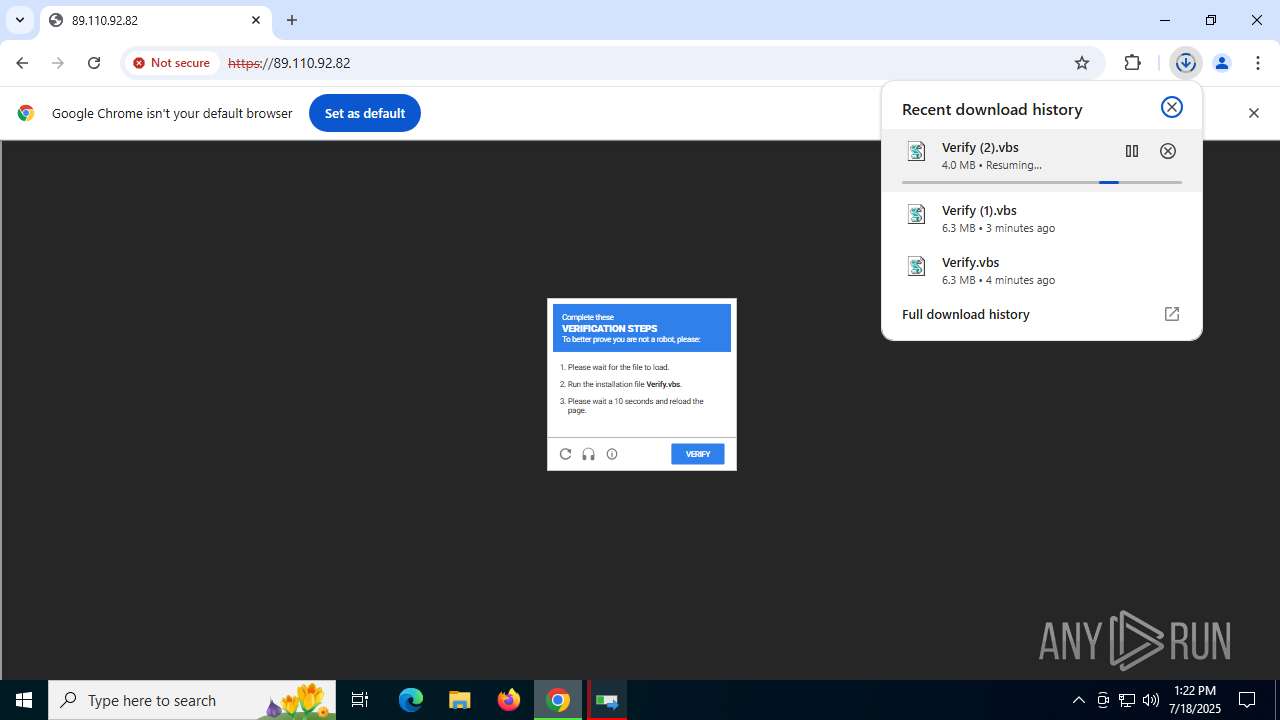
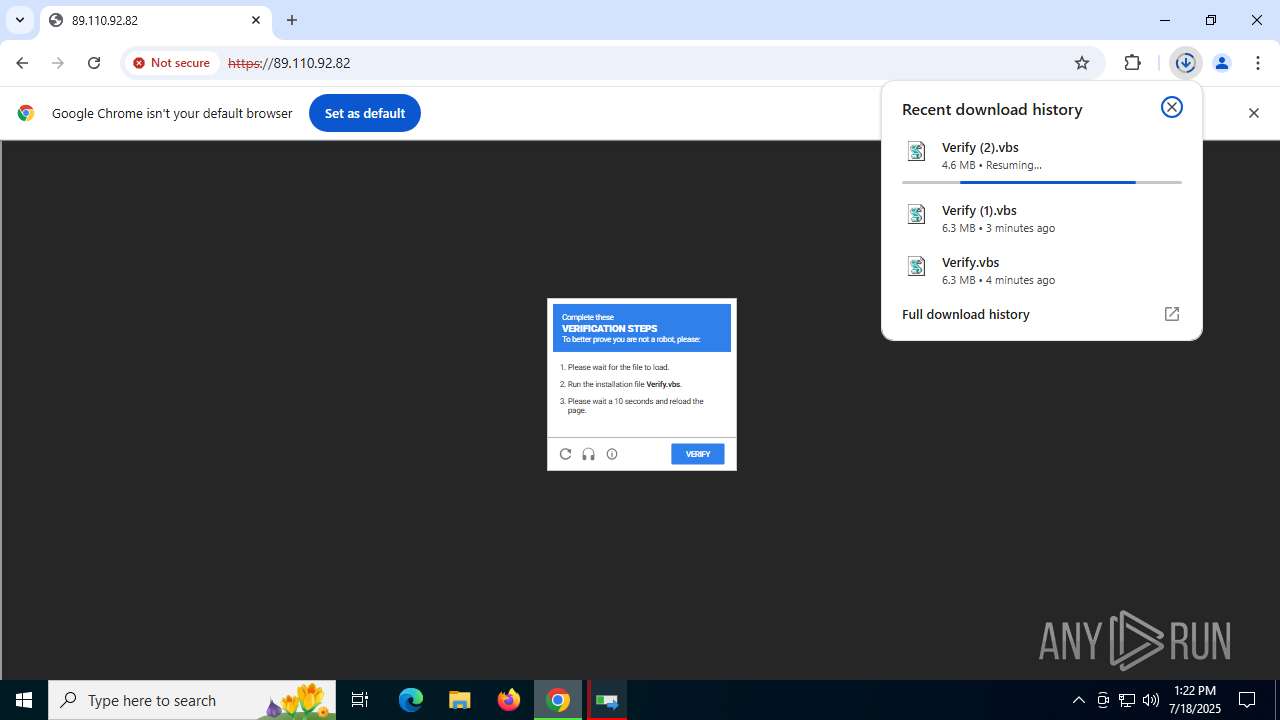
| URL: | 89.110.92.82 |
| Full analysis: | https://app.any.run/tasks/e36e8362-2998-4ebe-ab04-2b9a250cb658 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 13:17:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F5C2C322B2B0334AF2D4CF1F56E68D42 |
| SHA1: | C2FC5BBDE6ED1DBA468F0AAF95AA5F406CF5EB1C |
| SHA256: | 37146909E8EFDD0D9ECE1EEF126200CFC194DB6B81261FAA2891ADDB12F24E15 |
| SSDEEP: | 3:B5:f |
MALICIOUS
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Gets information about running processes via WMI (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
May hide the program window using WMI (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
SUSPICIOUS
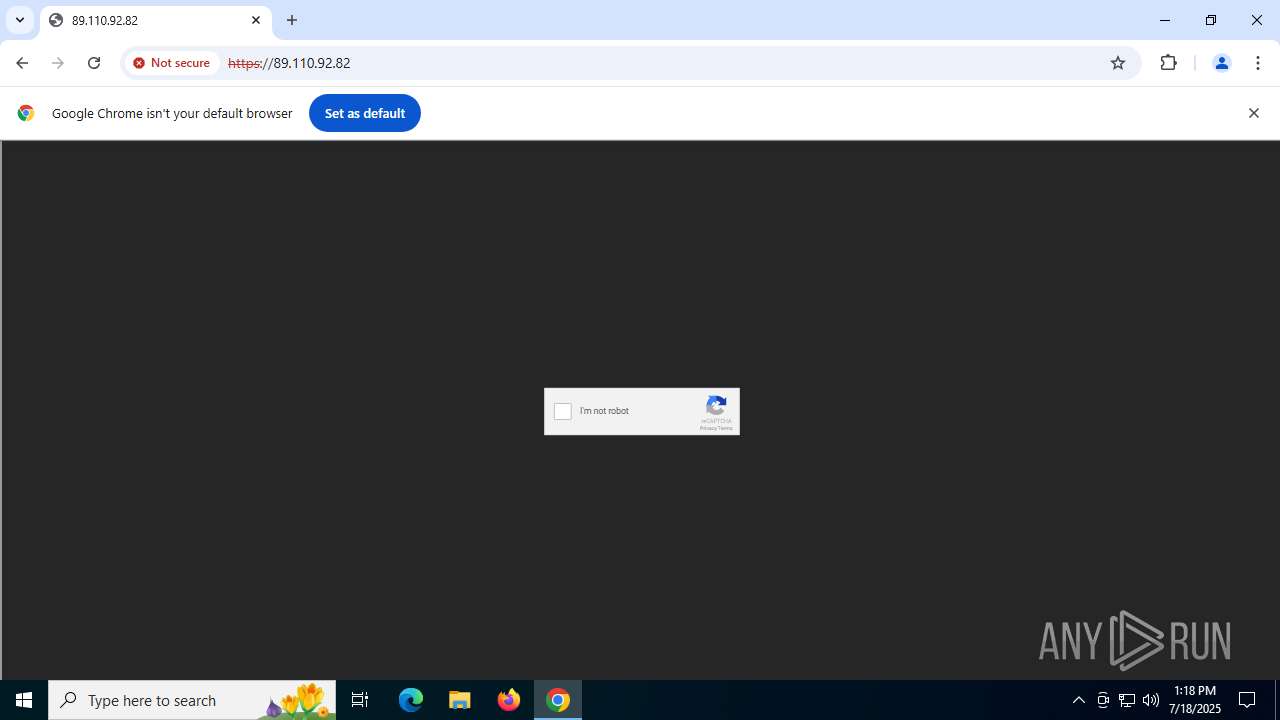
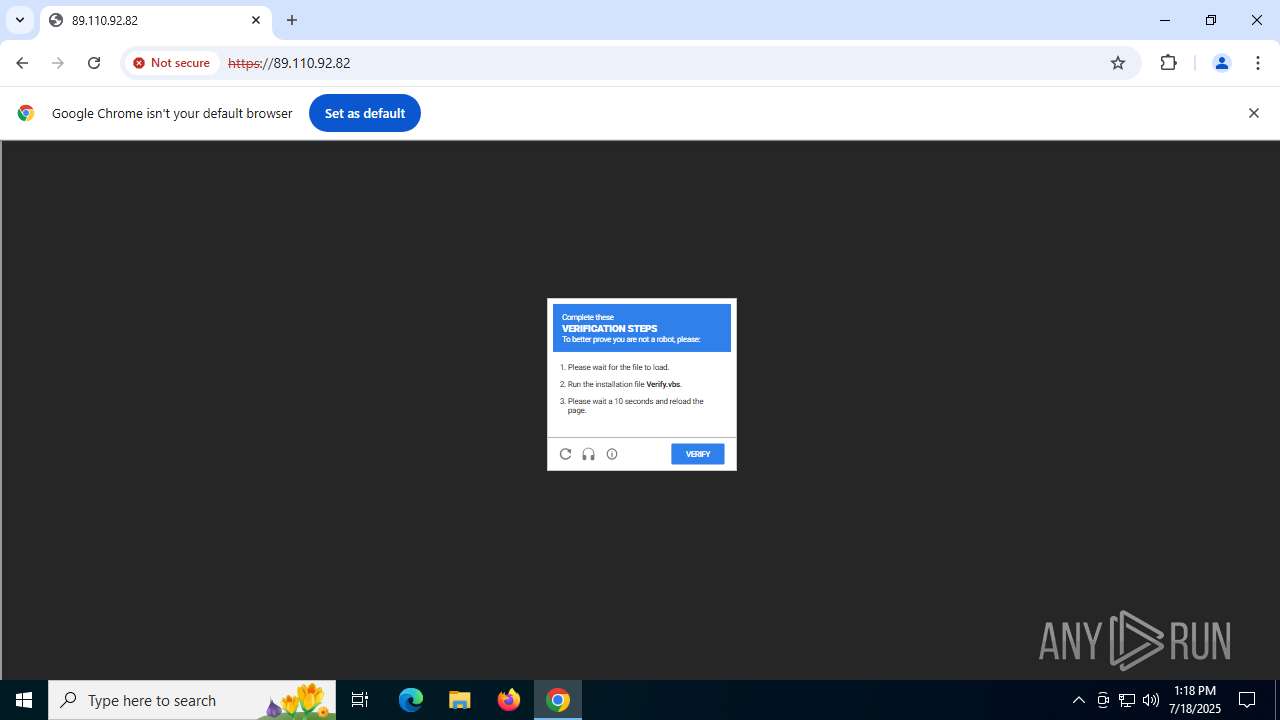
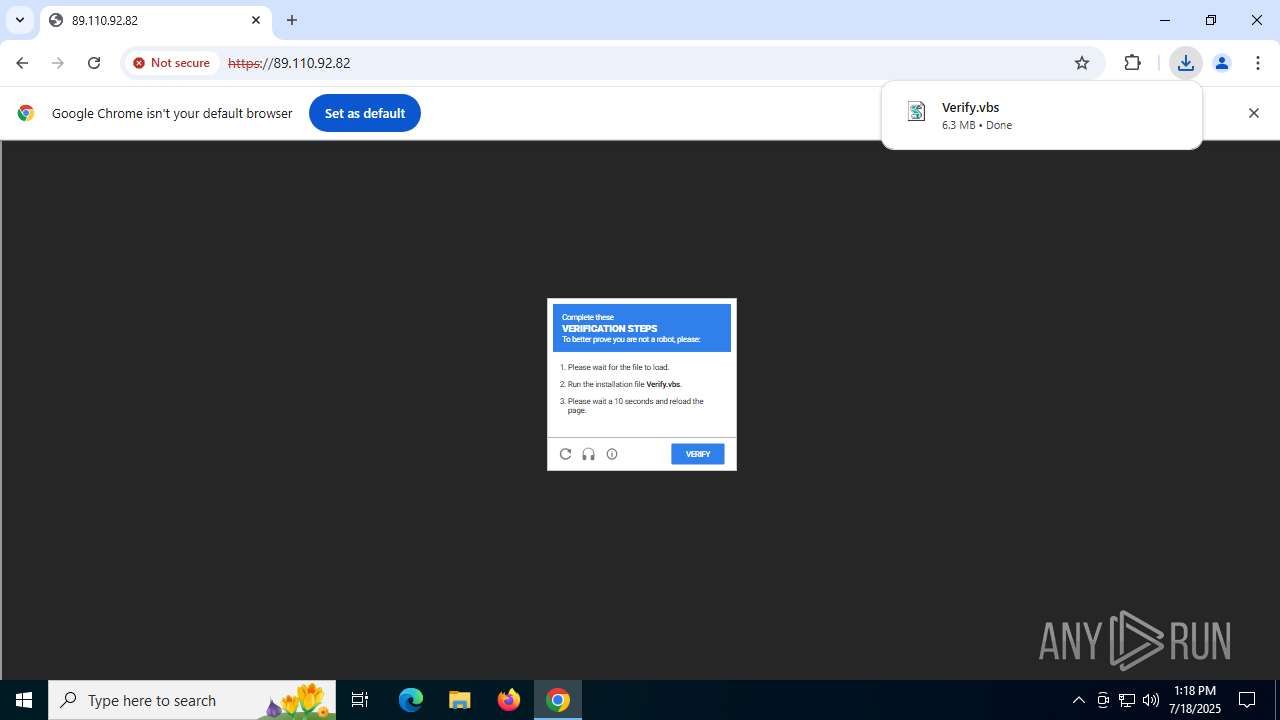
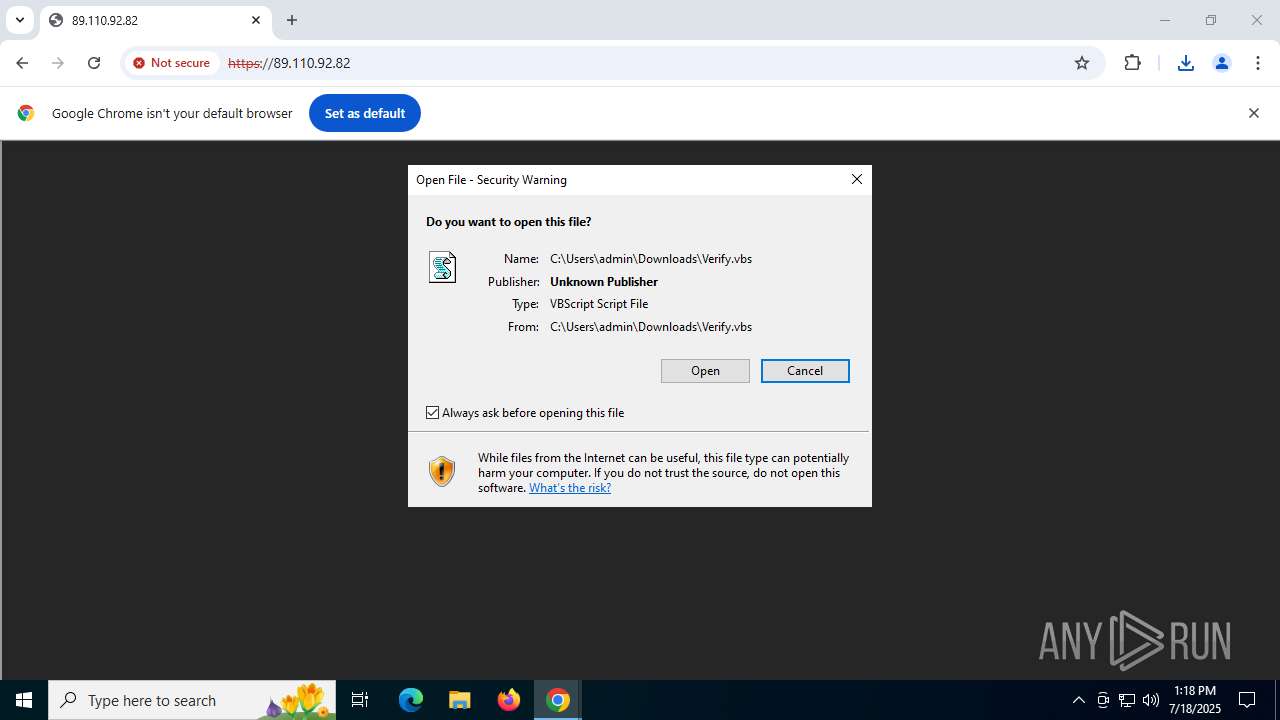
The process executes VB scripts
- chrome.exe (PID: 304)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Executed via WMI
- python.exe (PID: 3736)
- python.exe (PID: 8148)
Loads Python modules
- python.exe (PID: 3736)
- python.exe (PID: 8148)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
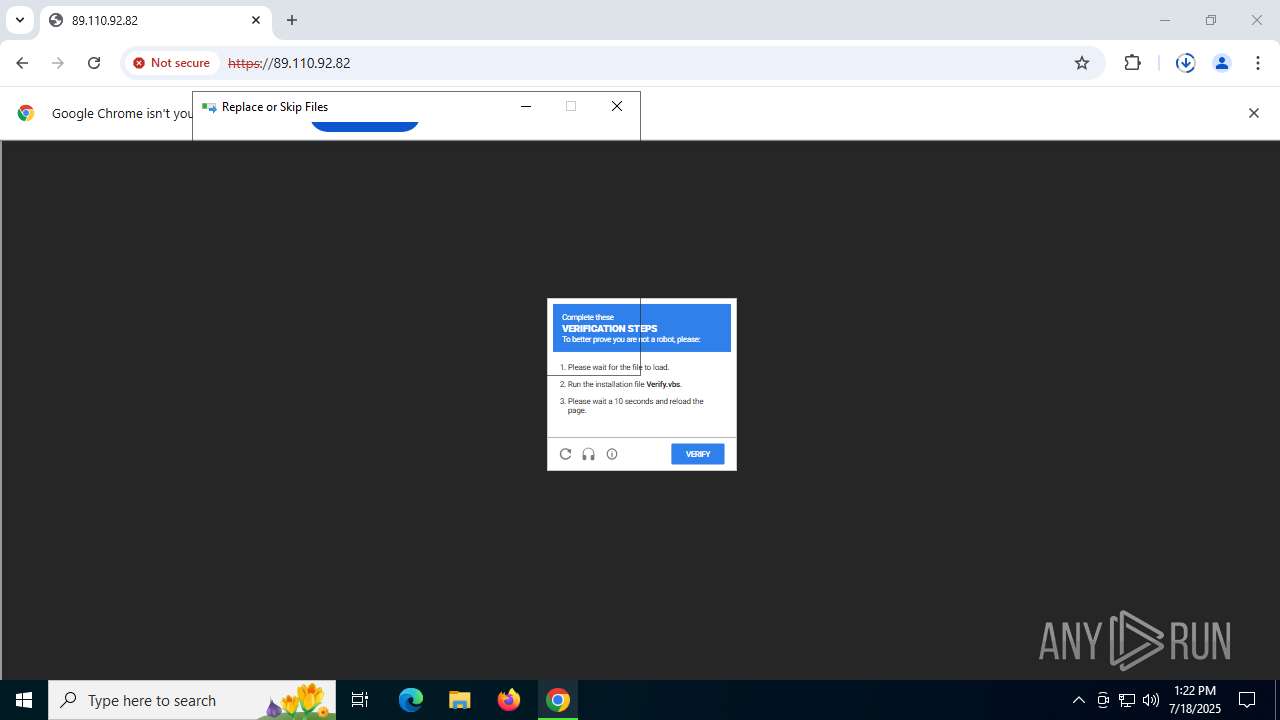
Process drops legitimate windows executable
- wscript.exe (PID: 4088)
- wscript.exe (PID: 684)
Process drops python dynamic module
- wscript.exe (PID: 4088)
- wscript.exe (PID: 684)
Creates a Folder object (SCRIPT)
- wscript.exe (PID: 4088)
- wscript.exe (PID: 684)
Executable content was dropped or overwritten
- wscript.exe (PID: 4088)
- wscript.exe (PID: 684)
The process drops C-runtime libraries
- wscript.exe (PID: 4088)
- wscript.exe (PID: 684)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 304)
Application launched itself
- chrome.exe (PID: 304)
The sample compiled with english language support
- wscript.exe (PID: 684)
- wscript.exe (PID: 4088)
Python executable
- python.exe (PID: 3736)
- python.exe (PID: 8148)
Reads the machine GUID from the registry
- python.exe (PID: 3736)
- python.exe (PID: 8148)
Reads the software policy settings
- slui.exe (PID: 7104)
Checks supported languages
- python.exe (PID: 3736)
- python.exe (PID: 8148)
Checks proxy server information
- slui.exe (PID: 7104)
Reads the computer name
- python.exe (PID: 8148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
182
Monitored processes
34
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "89.110.92.82" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
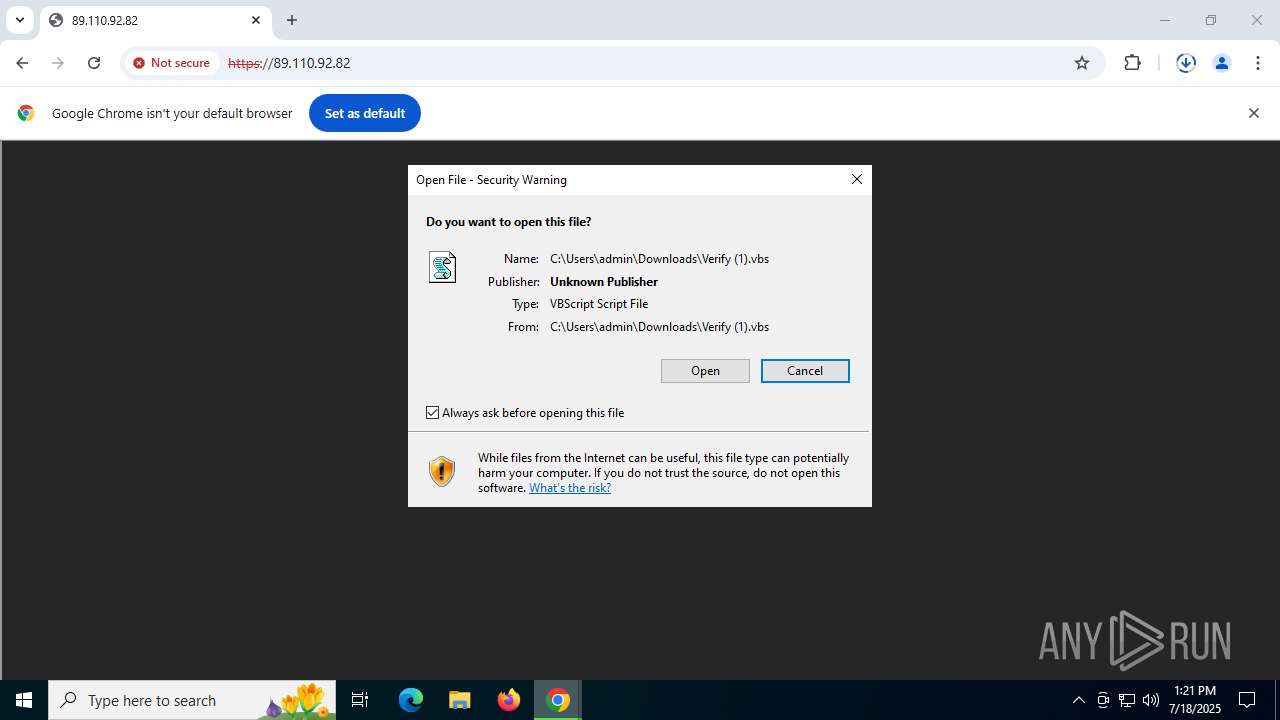
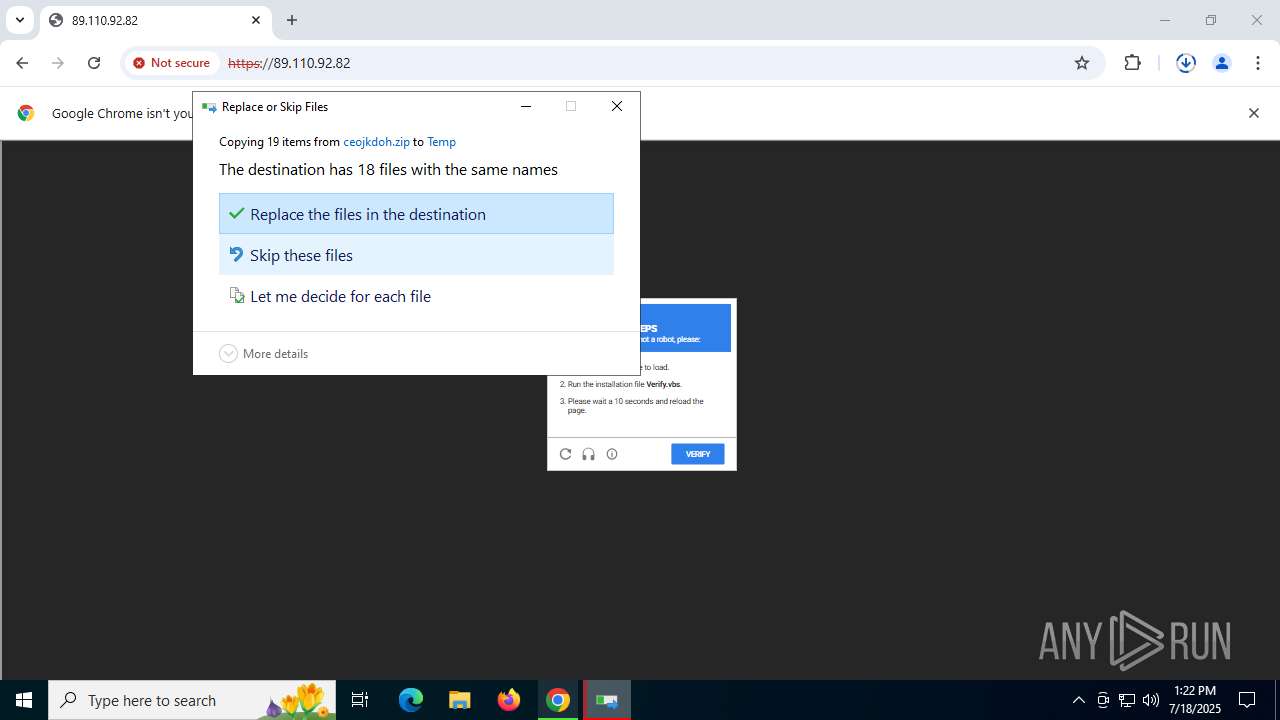
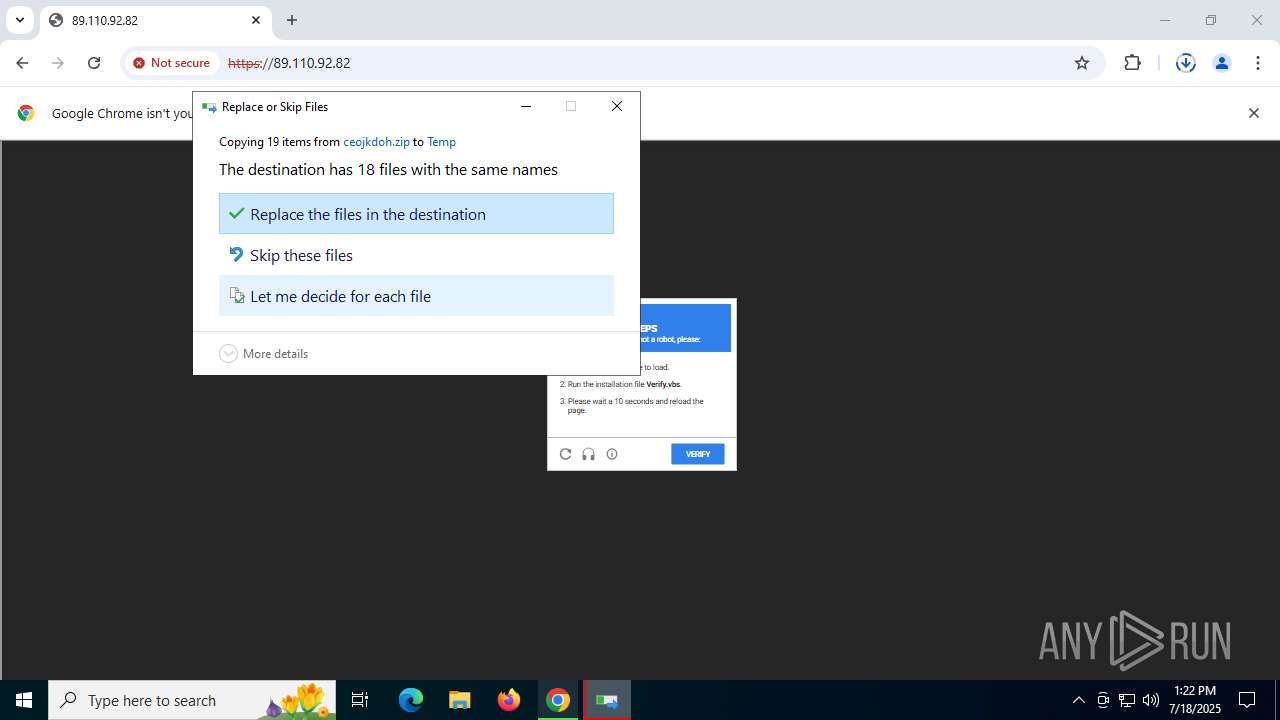
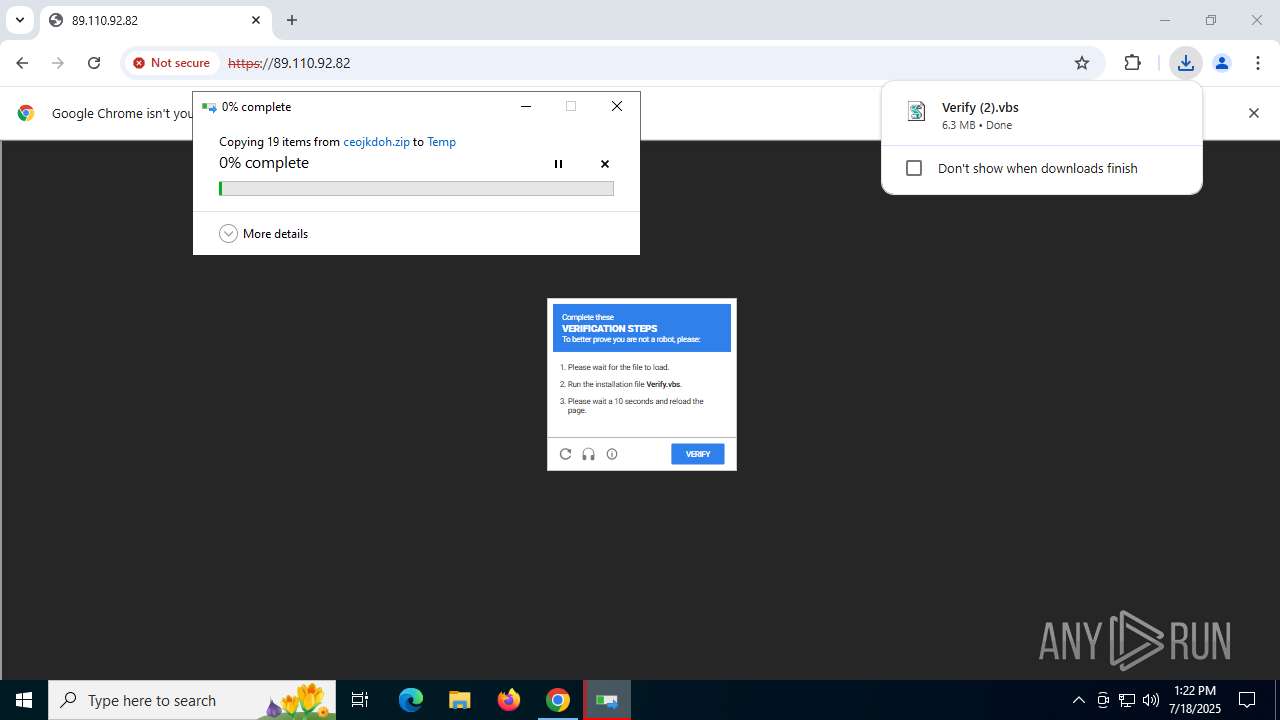
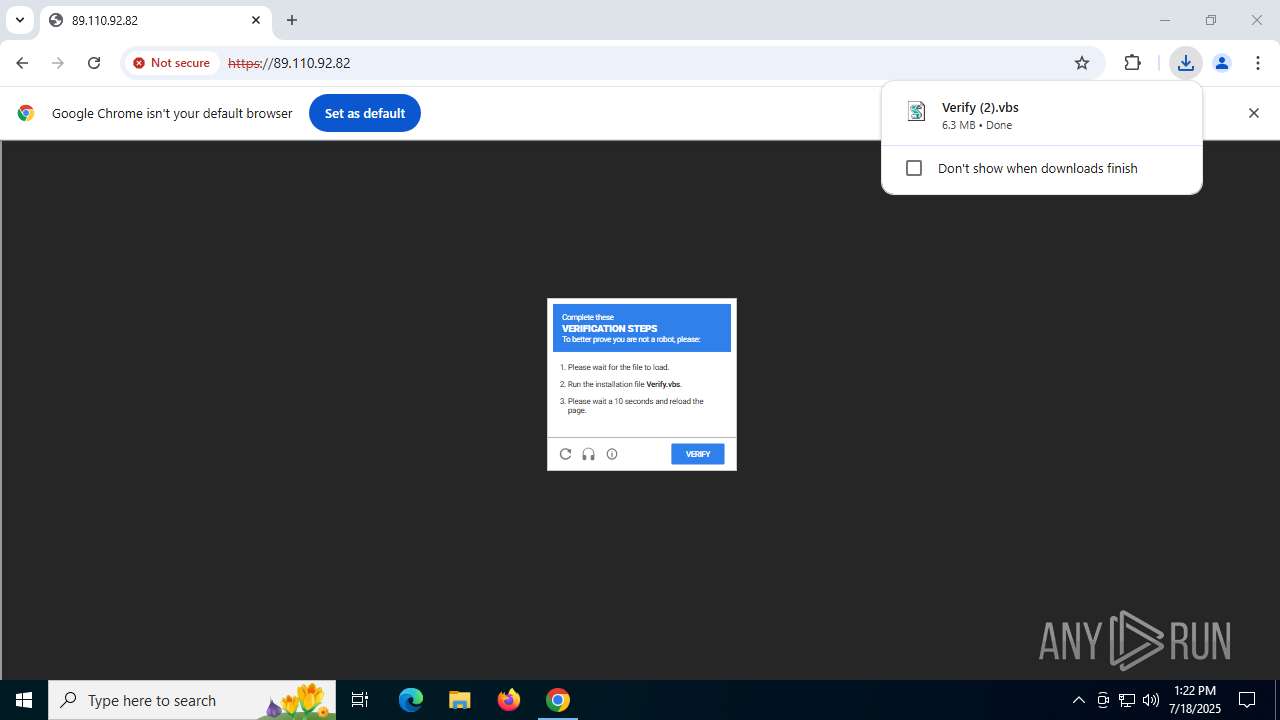
| 684 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Downloads\Verify.vbs" | C:\Windows\System32\wscript.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1904,i,11332851376689562306,9290997800797666405,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1976 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2036,i,11332851376689562306,9290997800797666405,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2028 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5424,i,11332851376689562306,9290997800797666405,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4452 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3736 | C:\Users\admin\AppData\Local\Temp\python_env\python.exe C:\Users\admin\AppData\Local\Temp\python_env\nykhhjgr.py | C:\Users\admin\AppData\Local\Temp\python_env\python.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.8.0 Modules
| |||||||||||||||
| 3888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5840,i,11332851376689562306,9290997800797666405,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 4088 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Downloads\Verify (1).vbs" | C:\Windows\System32\wscript.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=5172,i,11332851376689562306,9290997800797666405,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 4156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5416,i,11332851376689562306,9290997800797666405,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5280 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
12 430
Read events
12 403
Write events
21
Delete events
6
Modification events
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
Executable files
28
Suspicious files
92
Text files
49
Unknown types
228
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d5c9.TMP | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d5d9.TMP | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18d5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d5f8.TMP | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
112
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2028 | chrome.exe | GET | 200 | 89.110.92.82:80 | http://89.110.92.82/favicon.ico | RU | — | — | unknown |
2028 | chrome.exe | GET | 200 | 142.251.36.46:80 | http://clients2.google.com/time/1/current?cup2key=8:Hg0VNEo990rL9ZLRQy3yQR1a0xjetyIkPKDUjUsn-bA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
2028 | chrome.exe | GET | 204 | 142.251.39.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2028 | chrome.exe | GET | 200 | 89.110.92.82:80 | http://89.110.92.82/ | RU | html | 275 b | unknown |
1864 | svchost.exe | GET | 200 | 2.22.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | GB | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 96.16.53.165:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7916 | SIHClient.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 408 b | whitelisted |
1268 | svchost.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
7916 | SIHClient.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 420 b | whitelisted |
4788 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5fz6zxhu3e43vbz35hcqc5mrpq_2025.7.8.1/jflhchccmppkfebkiaminageehmchikm_2025.07.08.01_all_ad6hgk7uafcorir34g6ddjpg4nbq.crx3 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6312 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2028 | chrome.exe | 89.110.92.82:80 | — | RECONN LLC | RU | unknown |
2028 | chrome.exe | 89.110.92.82:443 | — | RECONN LLC | RU | unknown |
2028 | chrome.exe | 216.58.214.10:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
2028 | chrome.exe | 142.250.102.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2028 | chrome.exe | 142.251.36.46:80 | clients2.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |