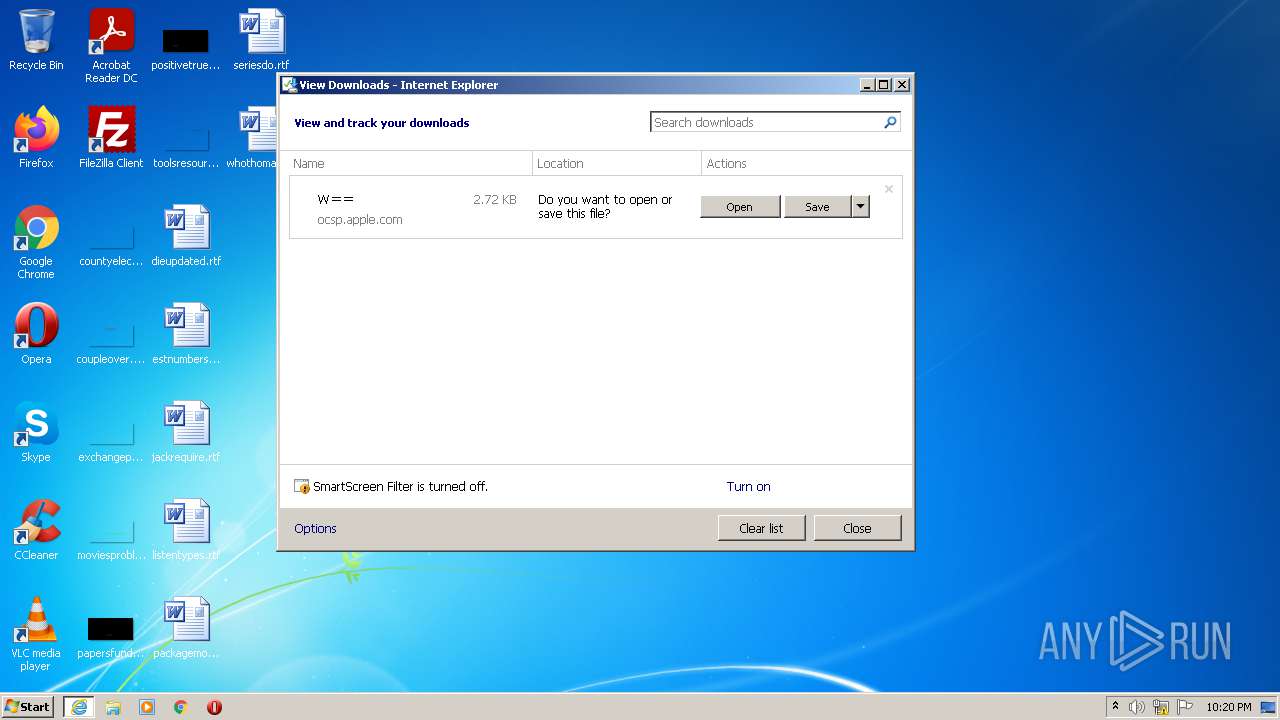
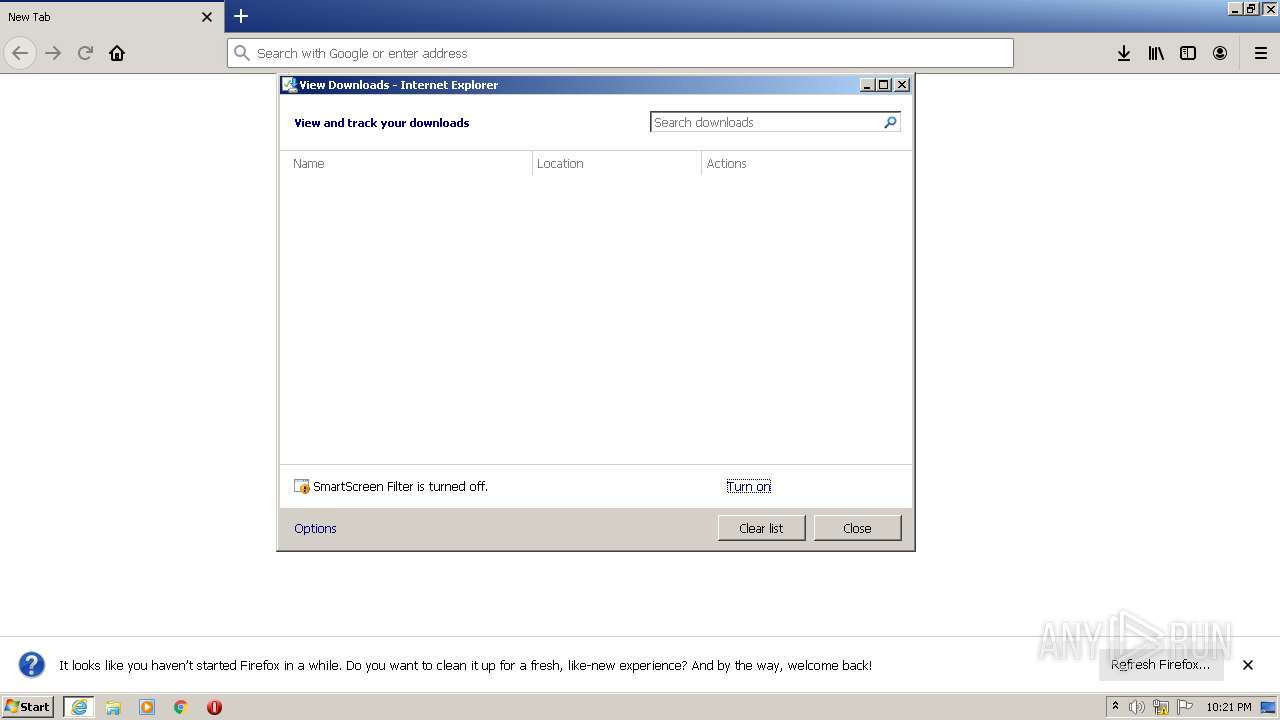
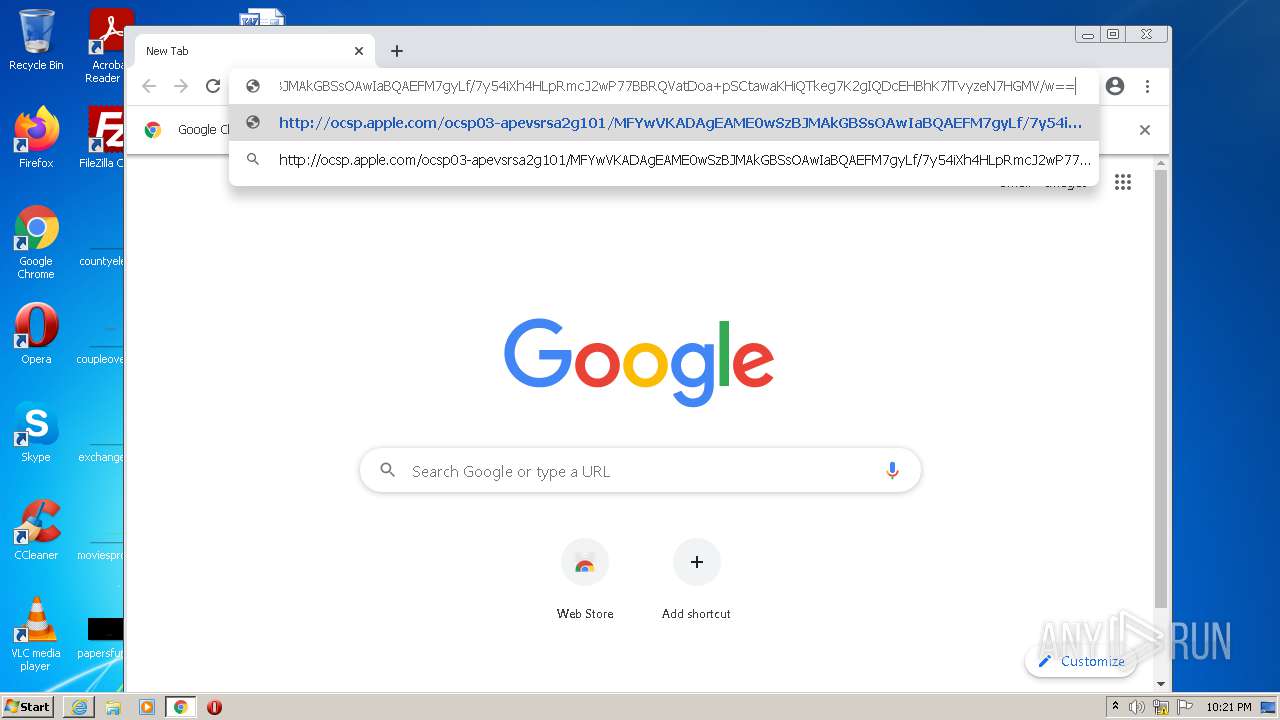
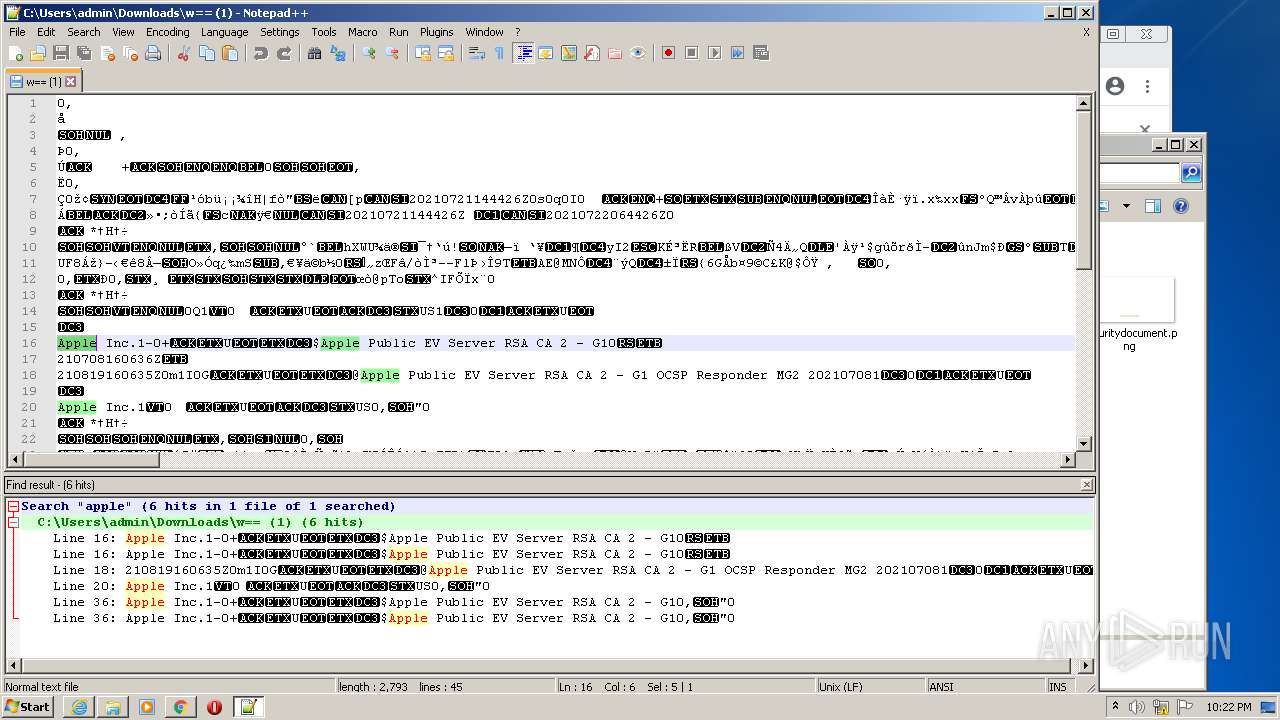
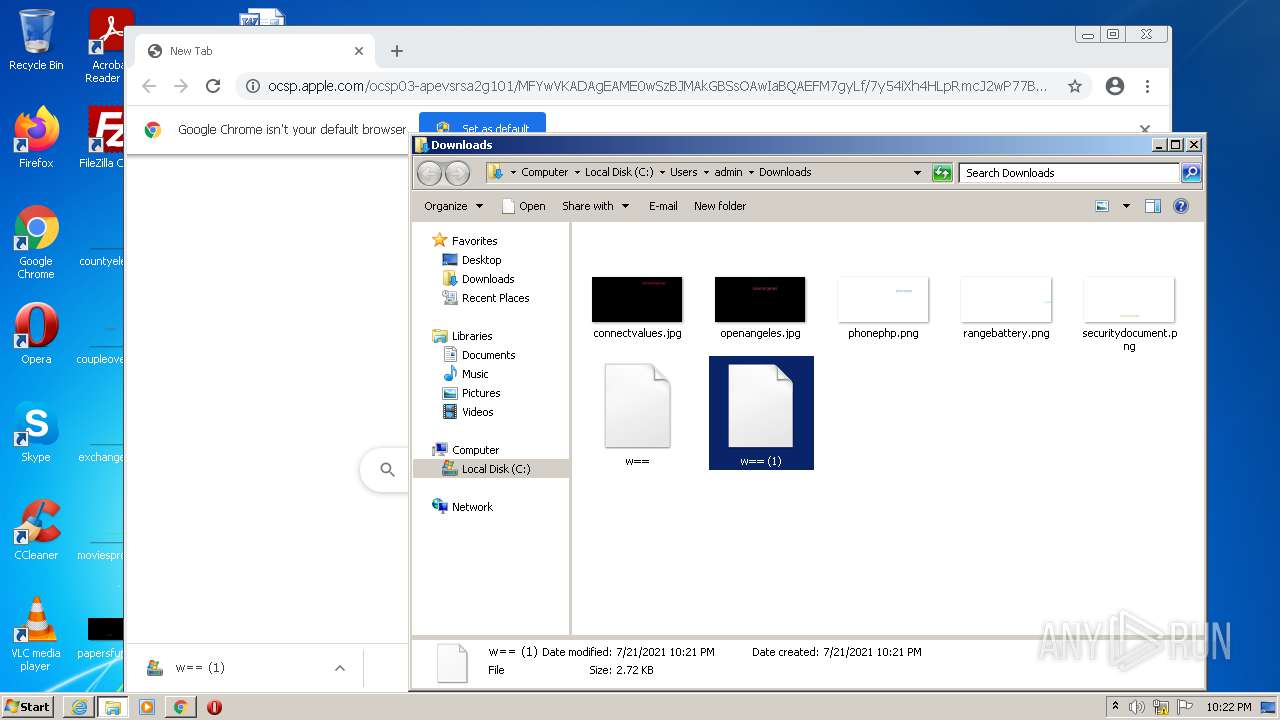
| URL: | http://ocsp.apple.com/ocsp03-apevsrsa2g101/MFYwVKADAgEAME0wSzBJMAkGBSsOAwIaBQAEFM7gyLf/7y54iXh4HLpRmcJ2wP77BBRQVatDoa+pSCtawaKHiQTkeg7K2gIQDcEHBhK7lTvyzeN7HGMV/w== |
| Full analysis: | https://app.any.run/tasks/089b8e6d-1cf1-44ad-a29b-ea0bd3af59a6 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2021, 21:20:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C19E65358EBBE0769FED21ABBE2BE688 |
| SHA1: | ED97BAE75C954E667877ECFFA6BF5C0D620D96D0 |
| SHA256: | 370E6D76ACB7A693D4BC619F60E8F6E51FE6BED9F9AA12B9CD298E9822178ADB |
| SSDEEP: | 3:N1KRGWVgVy6GWVZcmU+K+DCokYi4MdypW7PnVnLLxvRYCy6NFKOSz1:CgWVQy6jZLU+K+25N97nTqCrFqz1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2040)
Reads the date of Windows installation
- rundll32.exe (PID: 3896)
- rundll32.exe (PID: 3724)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3972)
Starts Internet Explorer
- rundll32.exe (PID: 3896)
Checks supported languages
- notepad++.exe (PID: 2708)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3324)
INFO
Checks supported languages
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 2040)
- rundll32.exe (PID: 3896)
- iexplore.exe (PID: 2336)
- rundll32.exe (PID: 3724)
- firefox.exe (PID: 2456)
- firefox.exe (PID: 3124)
- firefox.exe (PID: 1148)
- firefox.exe (PID: 612)
- firefox.exe (PID: 1868)
- firefox.exe (PID: 2560)
- firefox.exe (PID: 3892)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 1104)
- chrome.exe (PID: 3364)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 1440)
- chrome.exe (PID: 464)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 3544)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 1516)
Application launched itself
- iexplore.exe (PID: 3972)
- firefox.exe (PID: 2456)
- firefox.exe (PID: 3124)
- chrome.exe (PID: 3324)
Reads the computer name
- iexplore.exe (PID: 2040)
- iexplore.exe (PID: 3972)
- rundll32.exe (PID: 3896)
- rundll32.exe (PID: 3724)
- iexplore.exe (PID: 2336)
- firefox.exe (PID: 1868)
- firefox.exe (PID: 3124)
- firefox.exe (PID: 612)
- firefox.exe (PID: 1148)
- firefox.exe (PID: 2560)
- firefox.exe (PID: 3892)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 1516)
- chrome.exe (PID: 1440)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 3544)
Changes internet zones settings
- iexplore.exe (PID: 3972)
Checks Windows Trust Settings
- iexplore.exe (PID: 3972)
- rundll32.exe (PID: 3896)
- rundll32.exe (PID: 3724)
- firefox.exe (PID: 3124)
Reads the date of Windows installation
- iexplore.exe (PID: 3972)
- firefox.exe (PID: 3124)
- chrome.exe (PID: 2736)
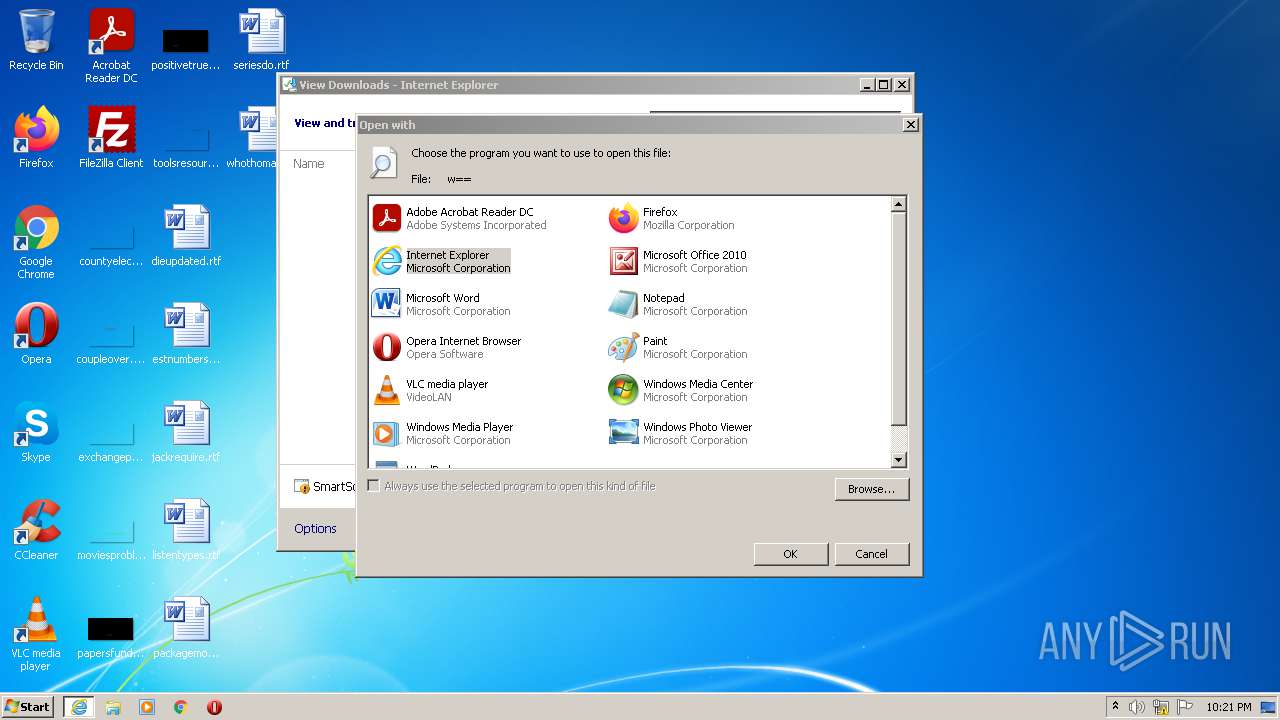
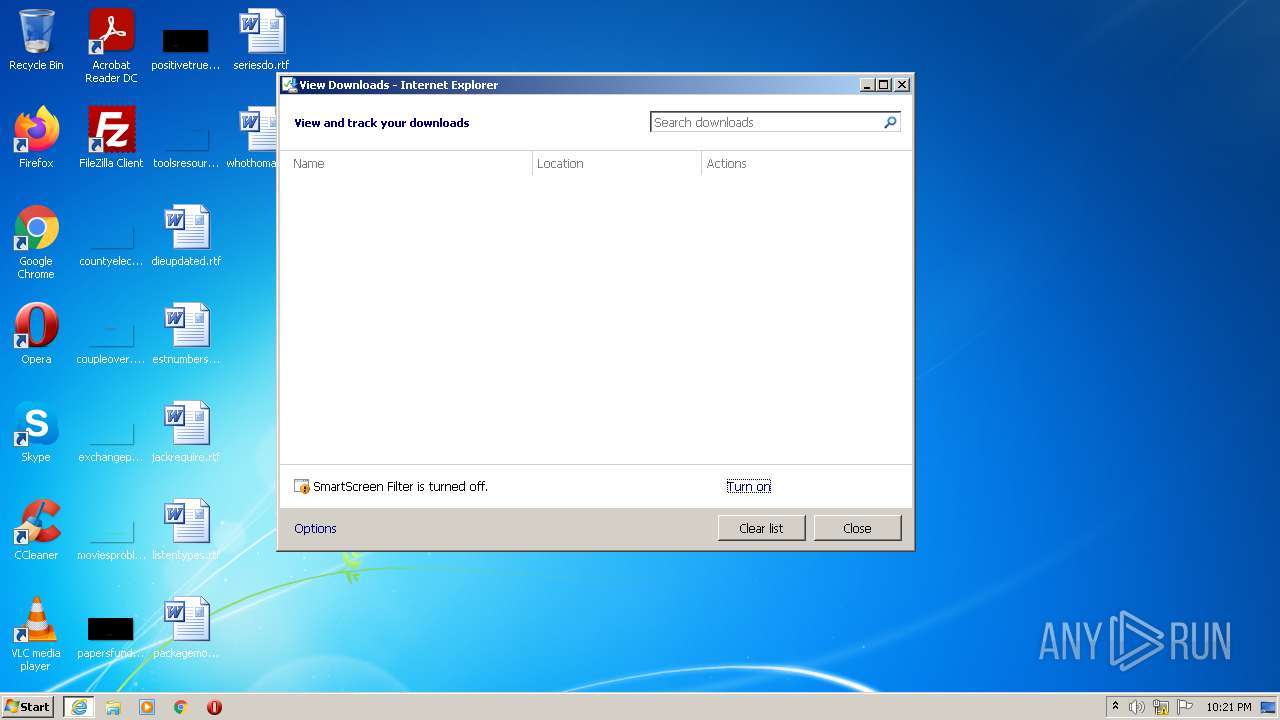
Modifies the phishing filter of IE
- iexplore.exe (PID: 3972)
Creates files in the user directory
- firefox.exe (PID: 3124)
- iexplore.exe (PID: 3972)
Creates files in the program directory
- firefox.exe (PID: 3124)
Reads settings of System Certificates
- iexplore.exe (PID: 3972)
- chrome.exe (PID: 3012)
Reads CPU info
- firefox.exe (PID: 3124)
Manual execution by user
- chrome.exe (PID: 3324)
- notepad++.exe (PID: 2708)
Reads the hosts file
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3012)
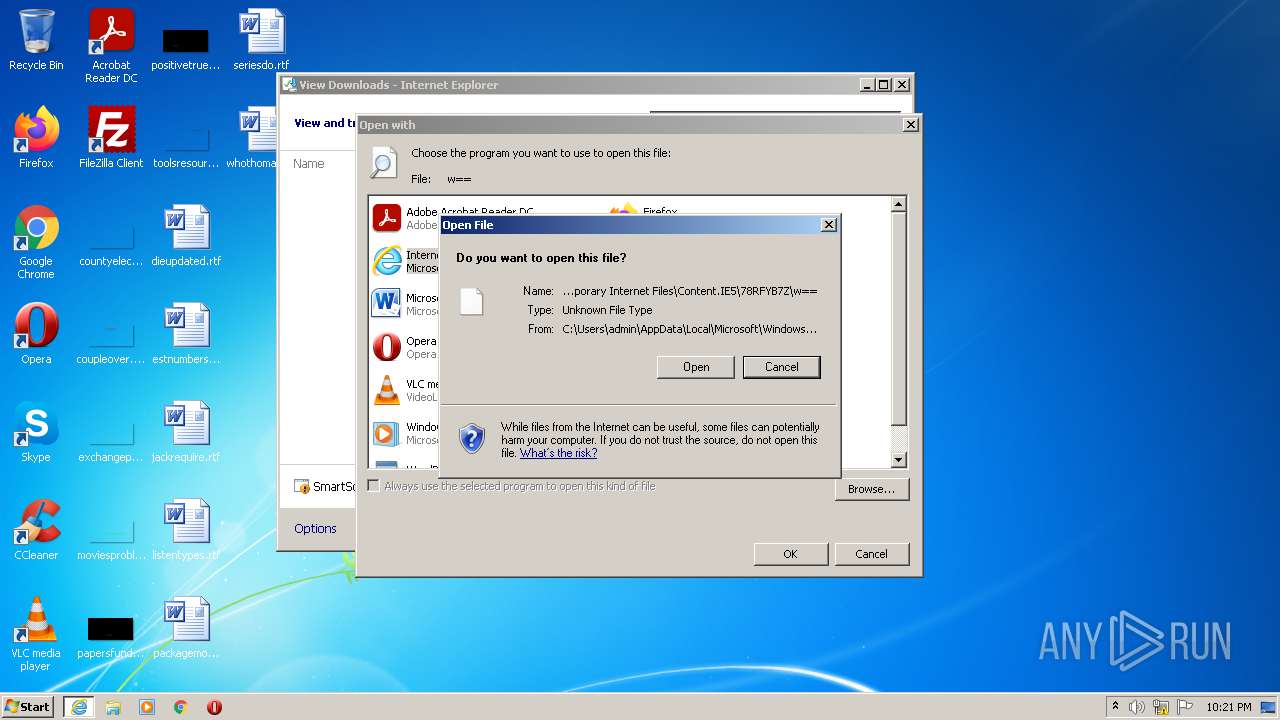
Changes settings of System certificates
- iexplore.exe (PID: 3972)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
38
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,1442342450344766783,3059605025347260897,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3124.0.1815251733\2089004772" -parentBuildID 20201112153044 -prefsHandle 1108 -prefMapHandle 1100 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3124 "\\.\pipe\gecko-crash-server-pipe.3124" 1180 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 83.0 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,1442342450344766783,3059605025347260897,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3124.6.1168263075\103149245" -childID 1 -isForBrowser -prefsHandle 3900 -prefMapHandle 3896 -prefsLen 181 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3124 "\\.\pipe\gecko-crash-server-pipe.3124" 3912 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,1442342450344766783,3059605025347260897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1056,1442342450344766783,3059605025347260897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,1442342450344766783,3059605025347260897,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1016 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,1442342450344766783,3059605025347260897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3124.13.565213915\1835842360" -childID 2 -isForBrowser -prefsHandle 2668 -prefMapHandle 2864 -prefsLen 7307 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3124 "\\.\pipe\gecko-crash-server-pipe.3124" 2736 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3972 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
35 324
Read events
34 887
Write events
427
Delete events
10
Modification events
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30899830 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30899830 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
83
Text files
280
Unknown types
36
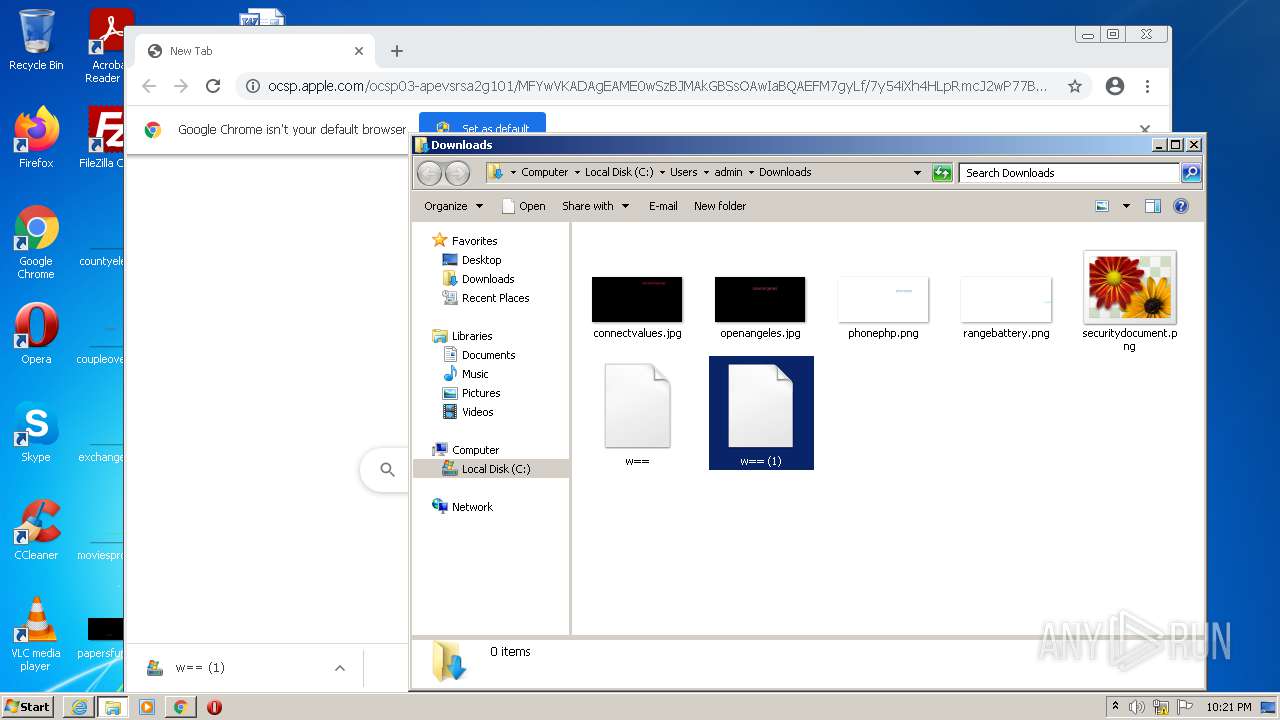
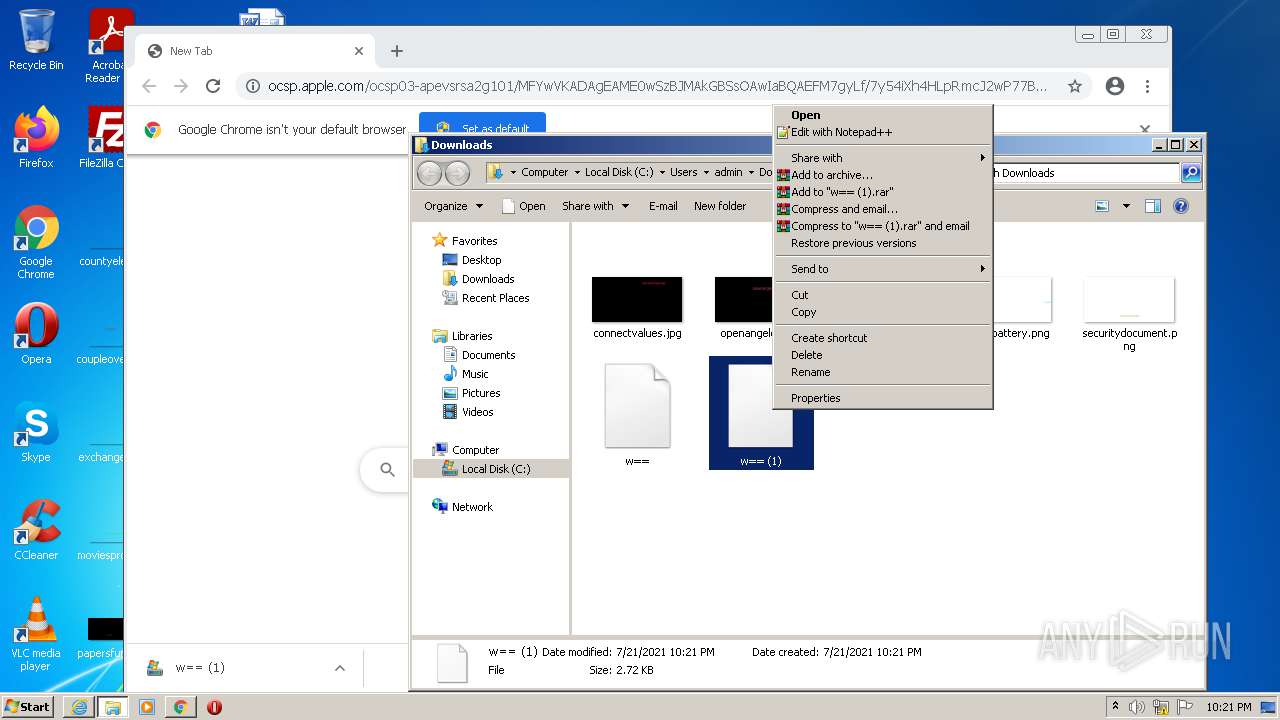
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3124 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
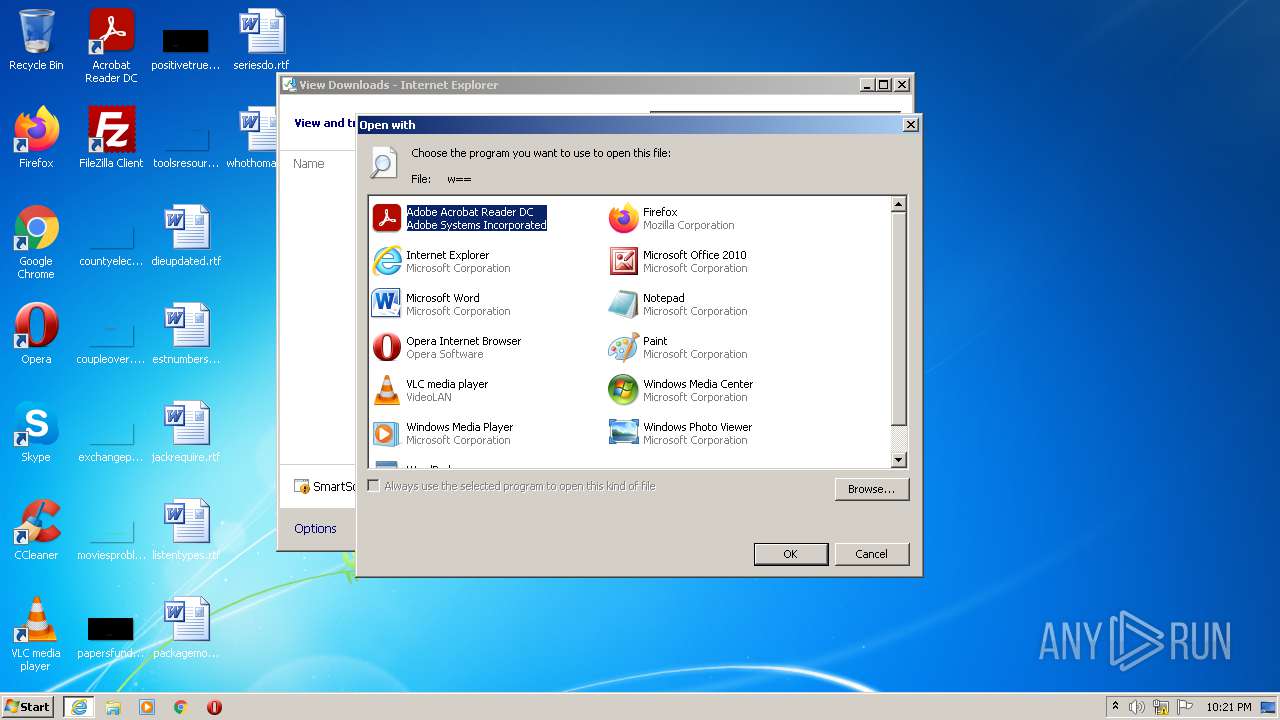
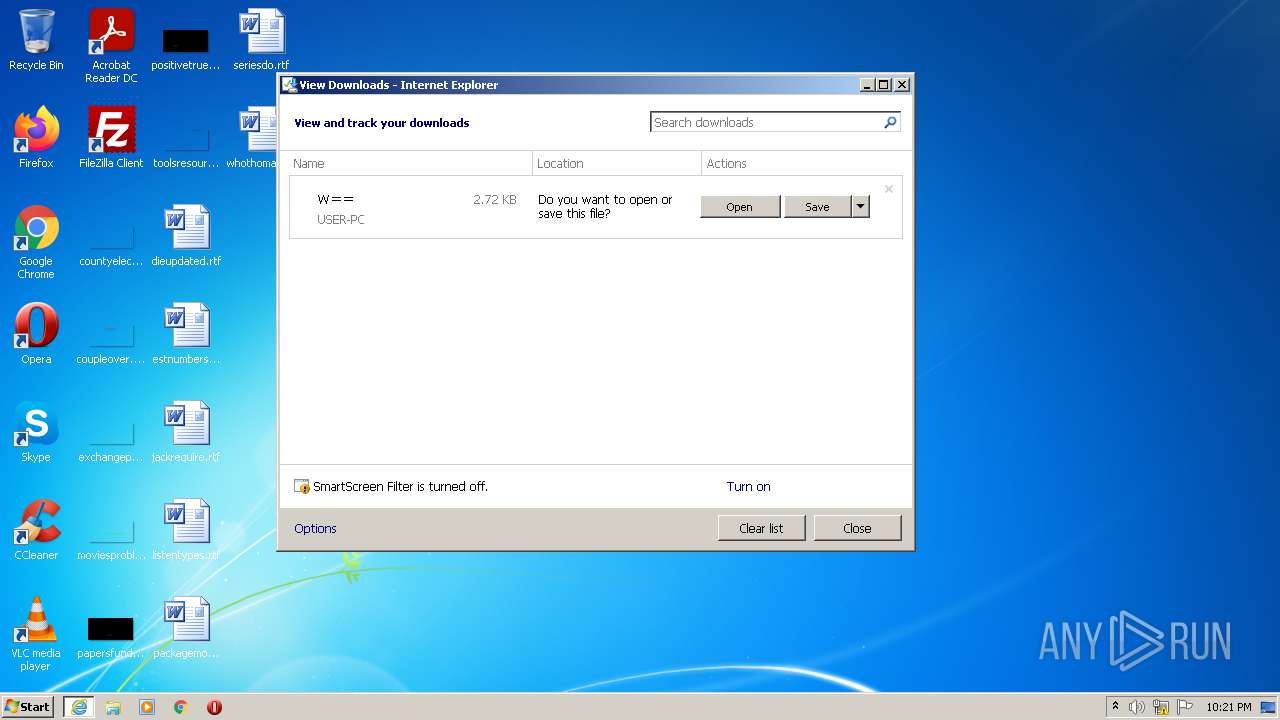
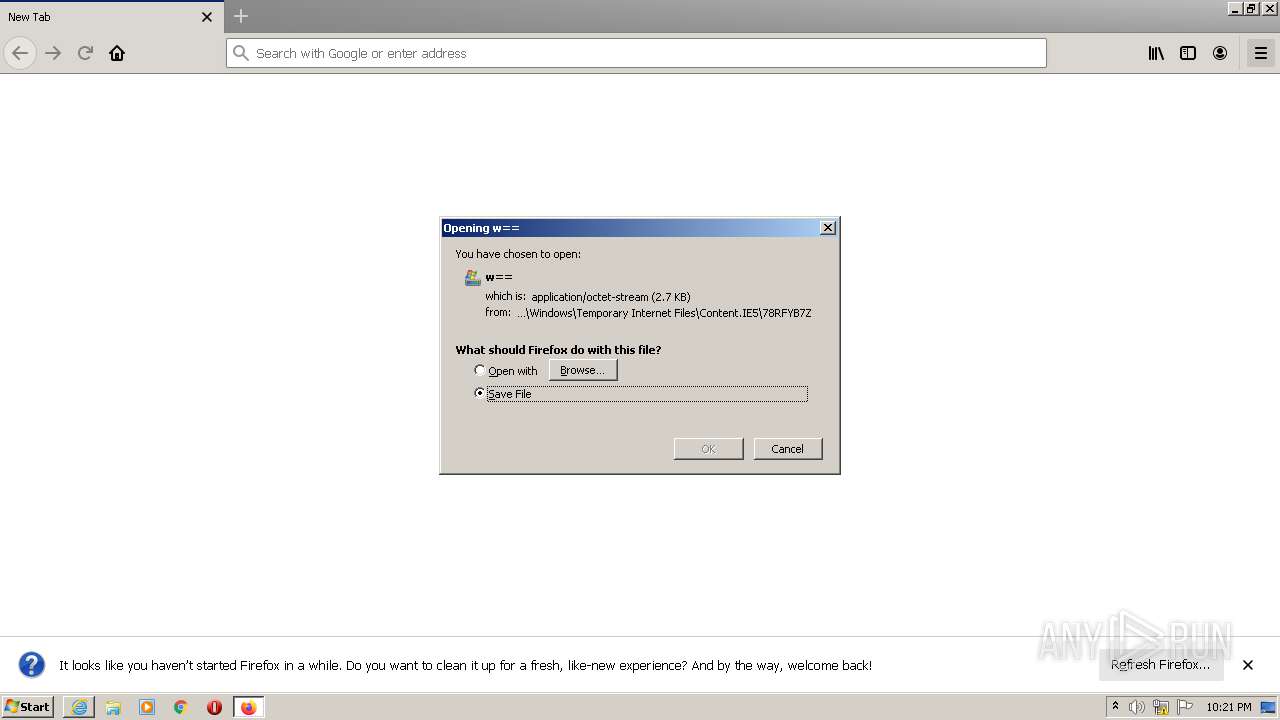
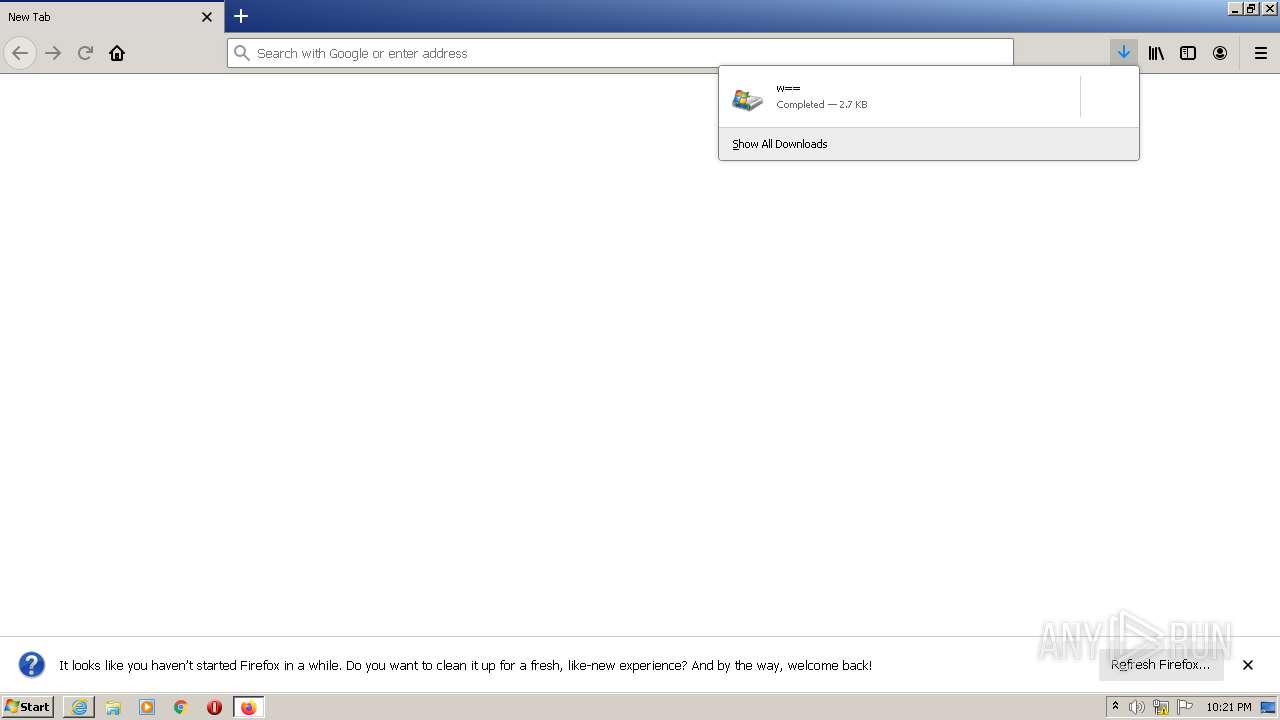
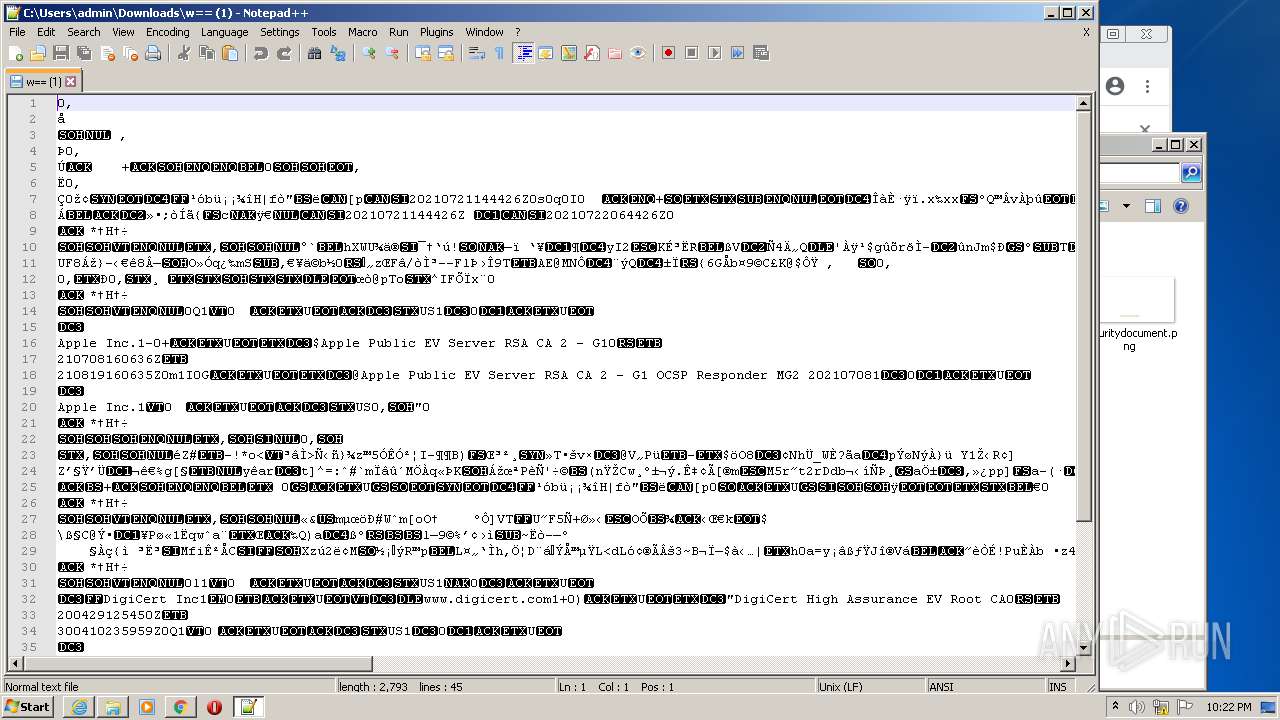
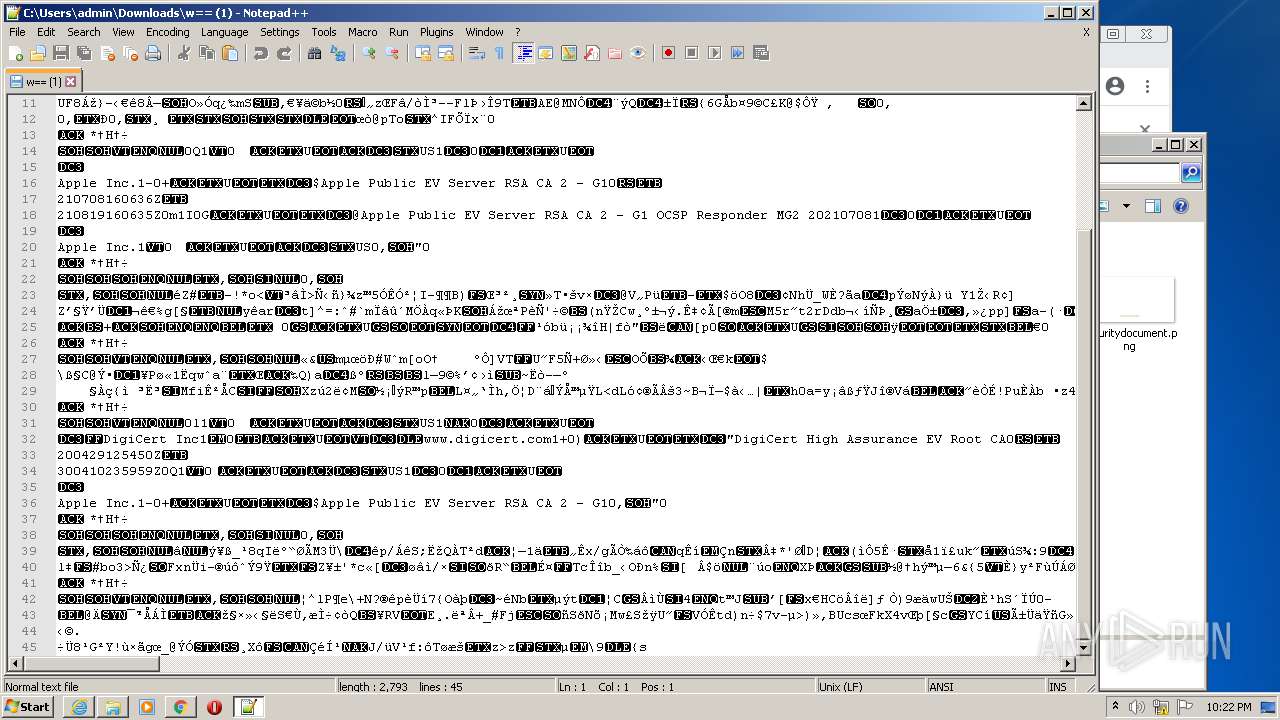
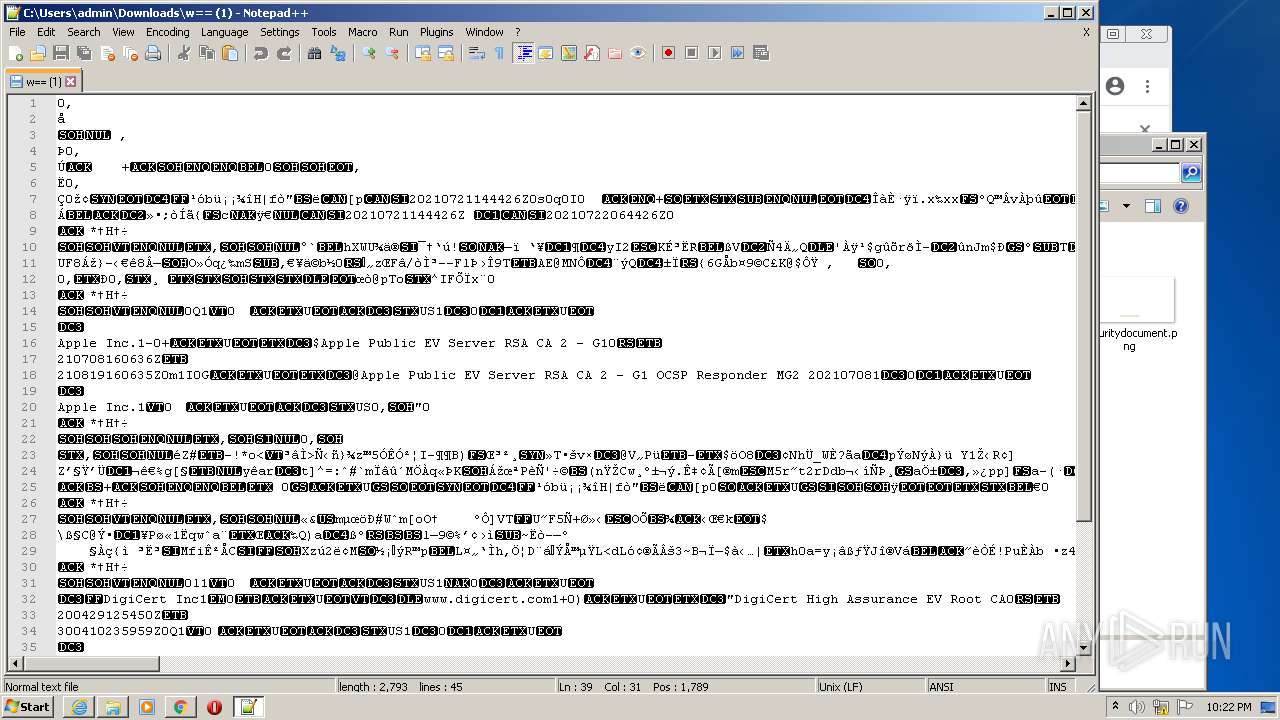
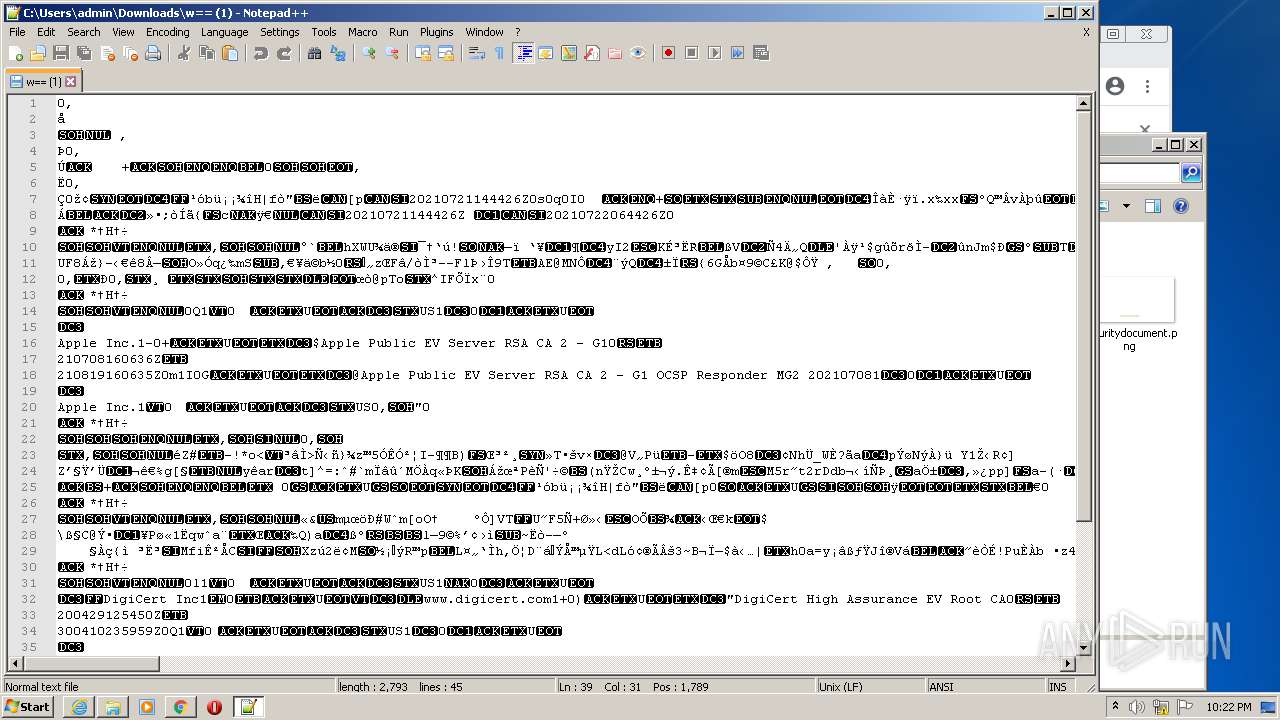
| 2040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\w==[1] | der | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF50121341DF7B4C5B.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6ABD440541AC586C.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3124 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
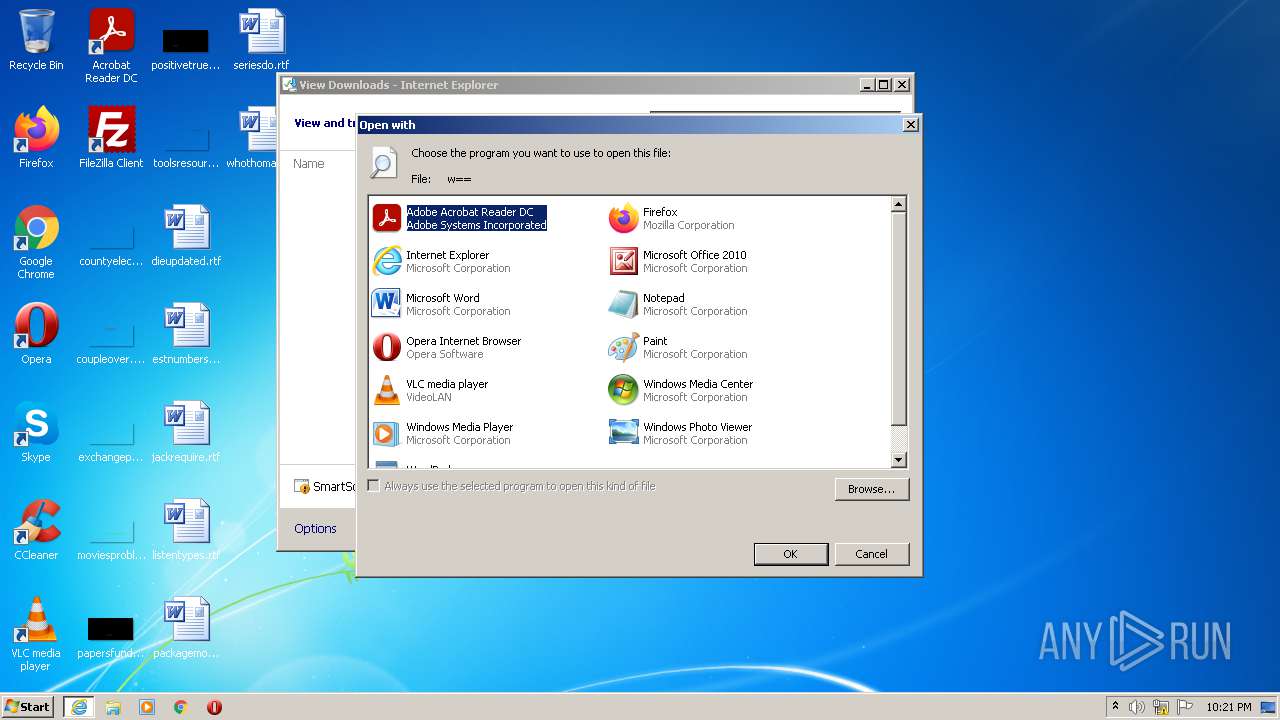
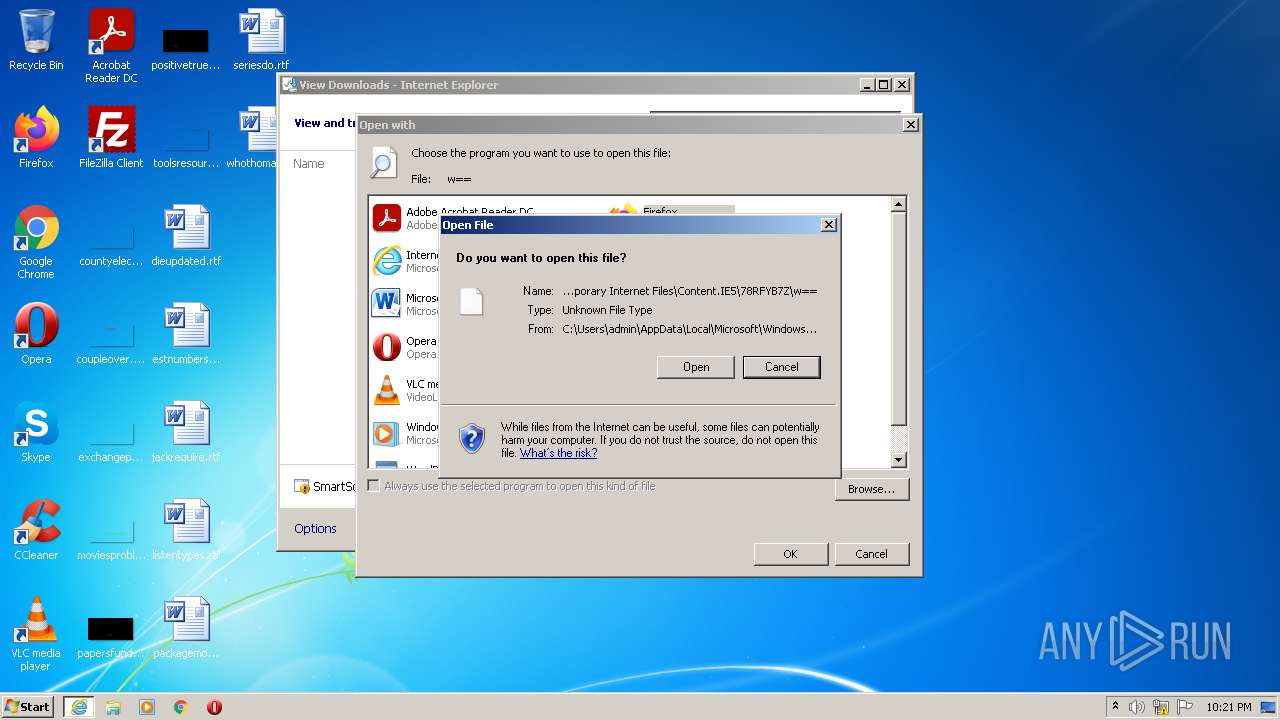
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\w== | der | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{93810706-EA69-11EB-B7EE-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\w==.sb3ioq4.partial | der | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{88D25DCA-EA69-11EB-B7EE-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3124 | firefox.exe | C:\Users\admin\AppData\Local\Temp\vN3dDBpK.part | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
61
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
888 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
2040 | iexplore.exe | GET | 200 | 17.253.57.203:80 | http://ocsp.apple.com/ocsp03-apevsrsa2g101/MFYwVKADAgEAME0wSzBJMAkGBSsOAwIaBQAEFM7gyLf/7y54iXh4HLpRmcJ2wP77BBRQVatDoa+pSCtawaKHiQTkeg7K2gIQDcEHBhK7lTvyzeN7HGMV/w== | US | der | 2.73 Kb | whitelisted |
3124 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3124 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
3972 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3972 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
888 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 5.76 Kb | whitelisted |
888 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 7.32 Kb | whitelisted |
888 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 10.2 Kb | whitelisted |
888 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 10.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3124 | firefox.exe | 13.224.193.80:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3972 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3012 | chrome.exe | 142.250.186.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2040 | iexplore.exe | 17.253.57.203:80 | ocsp.apple.com | Apple Inc. | US | suspicious |
3124 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3124 | firefox.exe | 13.224.193.70:443 | firefox.settings.services.mozilla.com | — | US | malicious |
3972 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3124 | firefox.exe | 13.225.74.110:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
3124 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3124 | firefox.exe | 34.215.35.6:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.apple.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
d2nxq2uap88usk.cloudfront.net |
| shared |