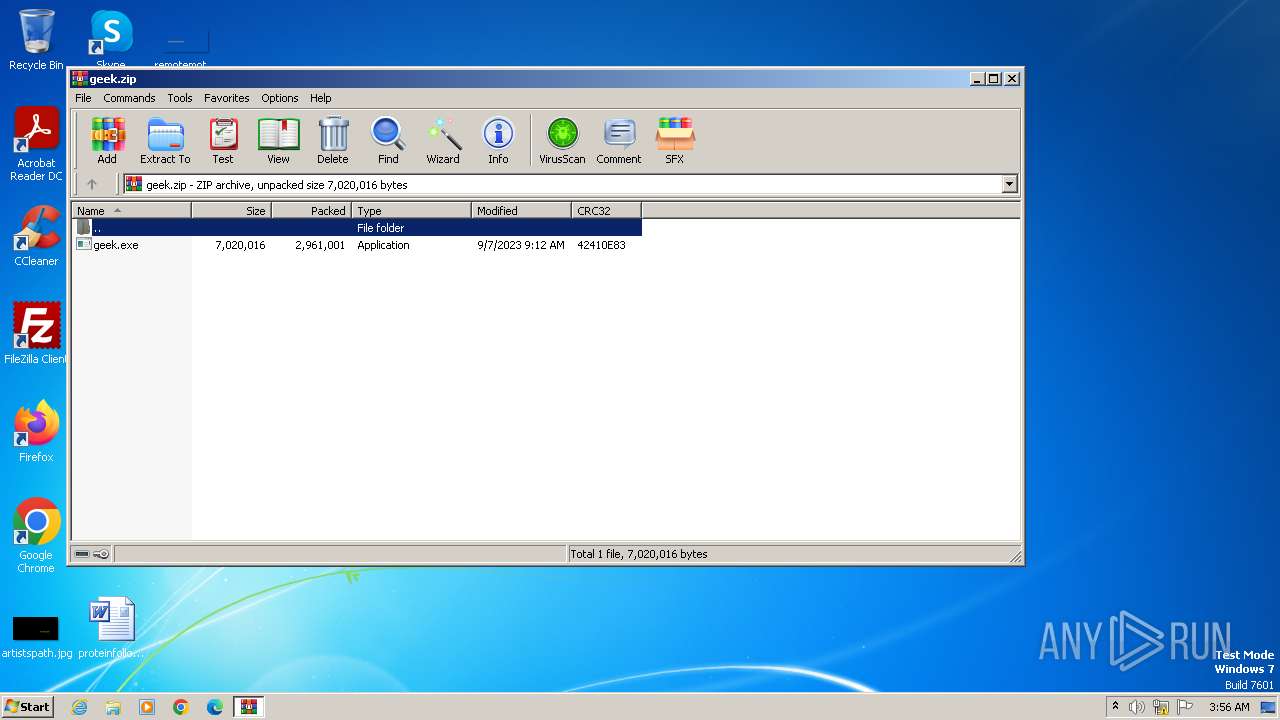
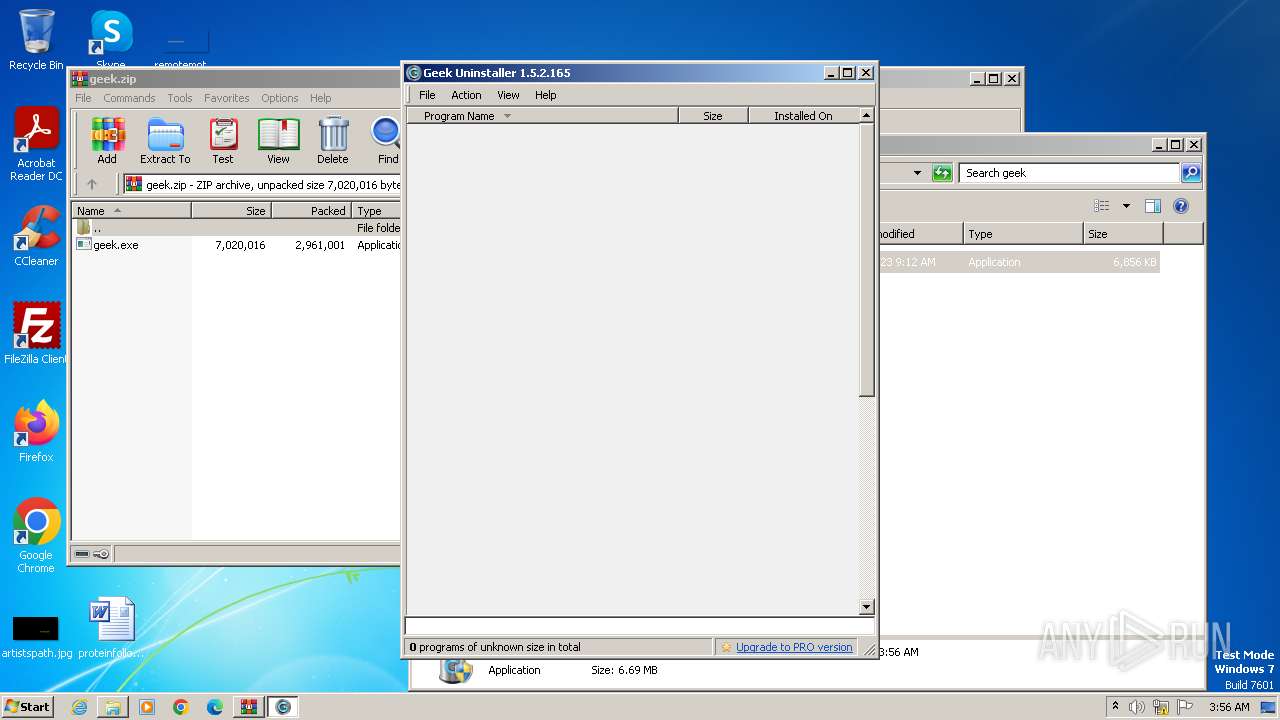
| File name: | geek.zip |
| Full analysis: | https://app.any.run/tasks/cbd8497b-4b42-4eed-9083-e2c6a875e65f |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 03:55:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BD73B1A5EA526E29680282637258DF25 |
| SHA1: | 477DF8D73299540FE8040B9B5102D8D56CCDDBD9 |
| SHA256: | 3706C440557692C612527C0EB437577EF2DAE8A1CA947DD2BC259B451E192F42 |
| SSDEEP: | 98304:2Es6l/S5Nmvp7lZoAzhgkJnntVJd6YOYFhWGHWqvP1WiWQVAKccCJ+SU62zGf5C5:2Un1lZ1 |
MALICIOUS
Actions looks like stealing of personal data
- geek.exe (PID: 1560)
SUSPICIOUS
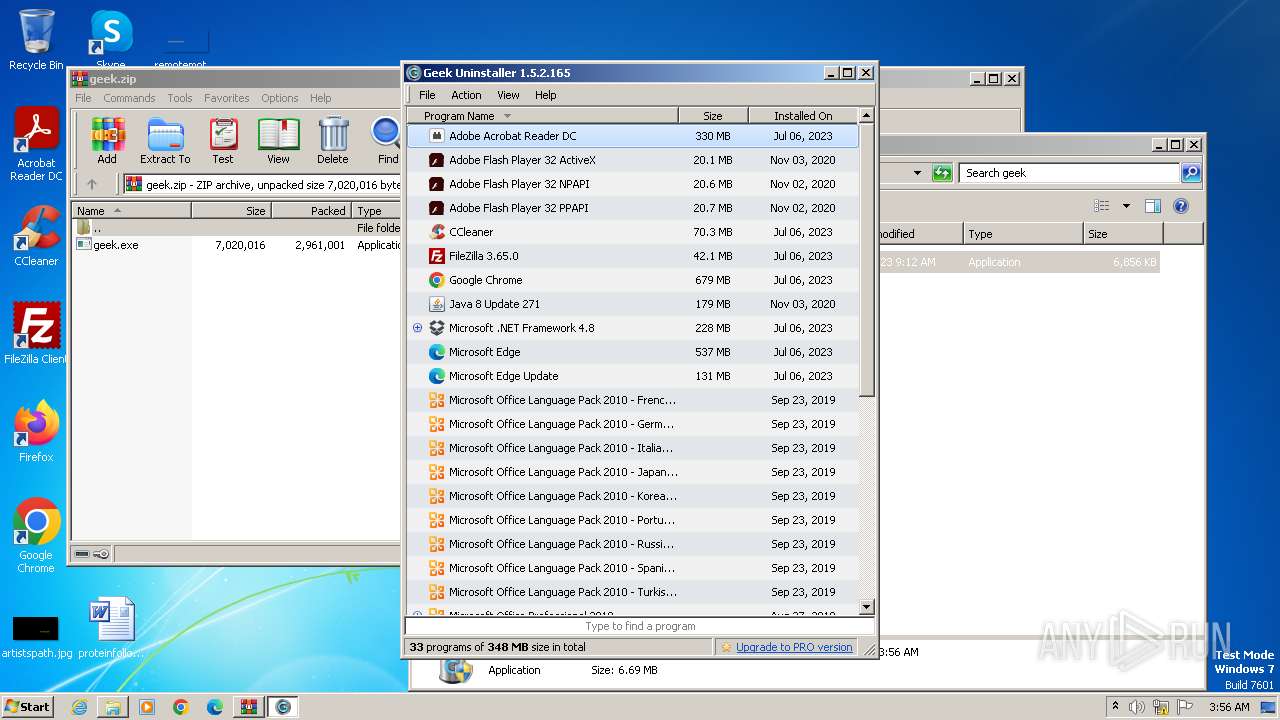
Searches for installed software
- geek.exe (PID: 1560)
Reads the Internet Settings
- geek.exe (PID: 1560)
Reads security settings of Internet Explorer
- geek.exe (PID: 1560)
Checks Windows Trust Settings
- geek.exe (PID: 1560)
Reads settings of System Certificates
- geek.exe (PID: 1560)
Adds/modifies Windows certificates
- geek.exe (PID: 1560)
INFO
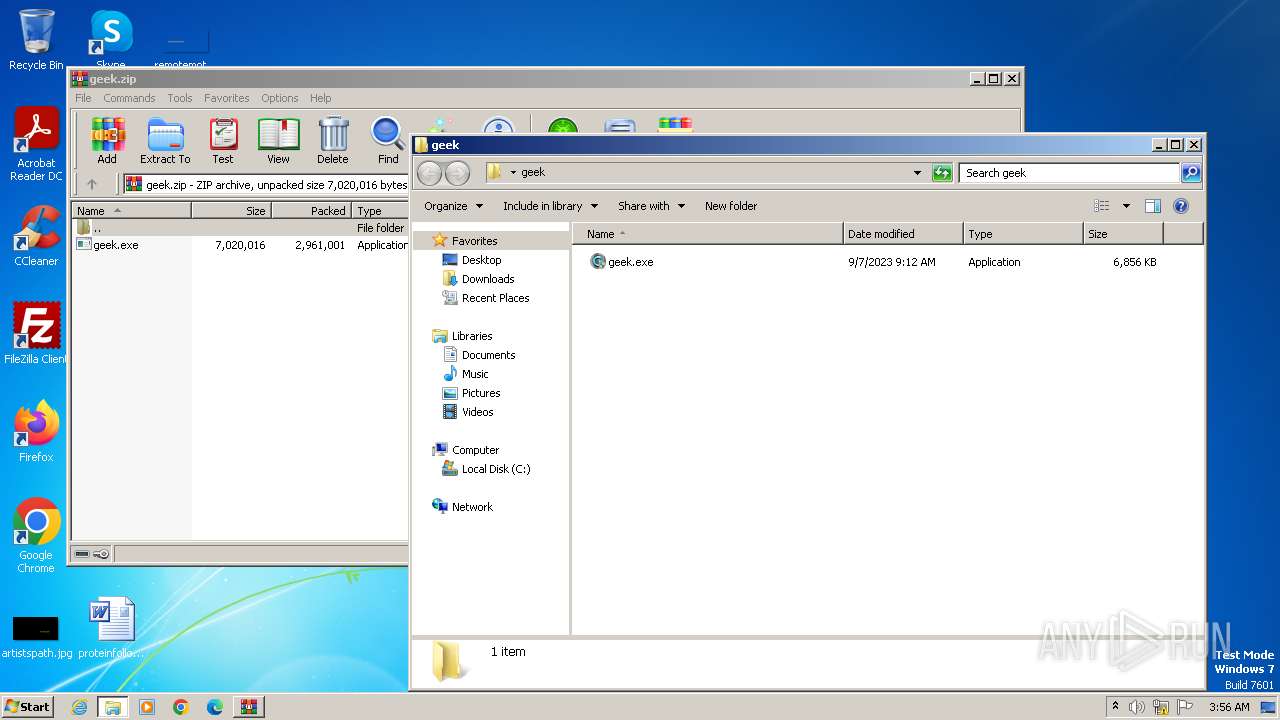
Manual execution by a user
- geek.exe (PID: 2464)
- geek.exe (PID: 1560)
- wmpnscfg.exe (PID: 3344)
Checks supported languages
- geek.exe (PID: 1560)
- wmpnscfg.exe (PID: 3344)
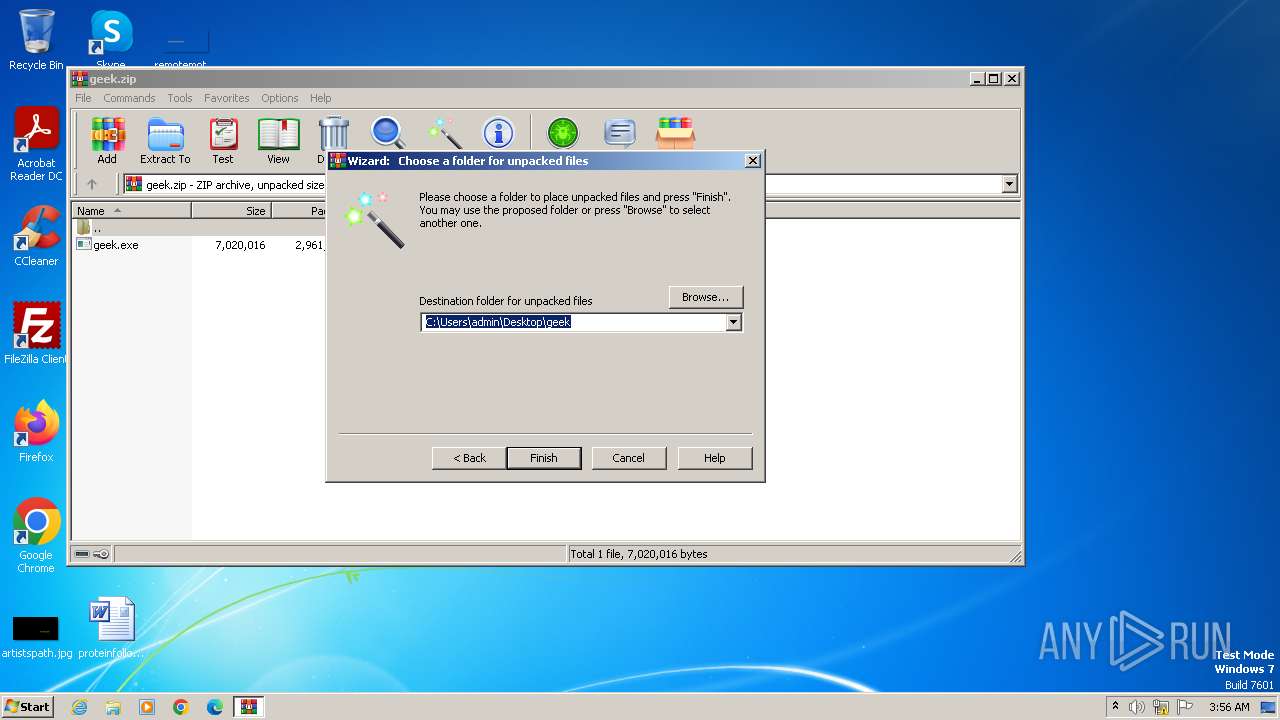
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2144)
Reads the computer name
- geek.exe (PID: 1560)
- wmpnscfg.exe (PID: 3344)
Checks proxy server information
- geek.exe (PID: 1560)
Reads the machine GUID from the registry
- geek.exe (PID: 1560)
Create files in a temporary directory
- geek.exe (PID: 1560)
Creates files or folders in the user directory
- geek.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:09:07 10:12:26 |
| ZipCRC: | 0x42410e83 |
| ZipCompressedSize: | 2961001 |
| ZipUncompressedSize: | 7020016 |
| ZipFileName: | geek.exe |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Users\admin\Desktop\geek\geek.exe" | C:\Users\admin\Desktop\geek\geek.exe | explorer.exe | ||||||||||||
User: admin Company: Geek Uninstaller Integrity Level: HIGH Description: Geek Uninstaller Exit code: 0 Version: 1.5.2.165 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\geek.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2464 | "C:\Users\admin\Desktop\geek\geek.exe" | C:\Users\admin\Desktop\geek\geek.exe | — | explorer.exe | |||||||||||
User: admin Company: Geek Uninstaller Integrity Level: MEDIUM Description: Geek Uninstaller Exit code: 3221226540 Version: 1.5.2.165 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 084
Read events
9 050
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1560) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1560) geek.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005A010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
11
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:81F4780C94574EFC0FCA8FC6C64C0D6C | SHA256:93A0B4226D6C13F51941BA256BDDA5309C2B824359F035AAD6187A5986AFF859 | |||
| 1560 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\66EEEA81AAF56AAC071822D4FD0246FE | binary | |
MD5:D1ED890C8E002E2220A17FC51C4DC155 | SHA256:B060E430EBE8F945221B26A0204279C31684A615305576DA2130A340A1EF73CE | |||
| 1560 | geek.exe | C:\Users\admin\AppData\Local\Temp\Cab8FF0.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1560 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1560 | geek.exe | C:\Users\admin\AppData\Local\Temp\Tar8FF1.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1560 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 1560 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3C5A598C651115574BD7D43516E98760 | SHA256:13A0DCDFD75F58C4818D5BF58F247BCA9548A63728B0E92FB7BEF3CF174917AE | |||
| 1560 | geek.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1560 | geek.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\update[1].txt | text | |
MD5:83838B4289E8C584CFD2A53EF414D33D | SHA256:72727B107B79962C08A14D80FFA925387E83CD9ACACFBAB7C7F5DA679B5BDD91 | |||
| 1560 | geek.exe | C:\Users\admin\AppData\Roaming\Geek Uninstaller\cache.dat | compressed | |
MD5:860D4993D43C7CC3C3F15925CEBFB7CA | SHA256:588882F6E5E4A37A57D2E023DA5A84E47A05C8D7D44DC87D054D8CEAD28D84C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1560 | geek.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7ed9eb38232c1501 | unknown | compressed | 4.66 Kb | unknown |
1560 | geek.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7900cbb26458d171 | unknown | compressed | 65.2 Kb | unknown |
1560 | geek.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1560 | geek.exe | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQloXxw7SRy%2BF2phayuh6Pleg%3D%3D | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1560 | geek.exe | 173.230.144.164:443 | geekuninstaller.com | Linode, LLC | US | unknown |
1560 | geek.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1560 | geek.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
1560 | geek.exe | 184.24.77.54:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geekuninstaller.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |