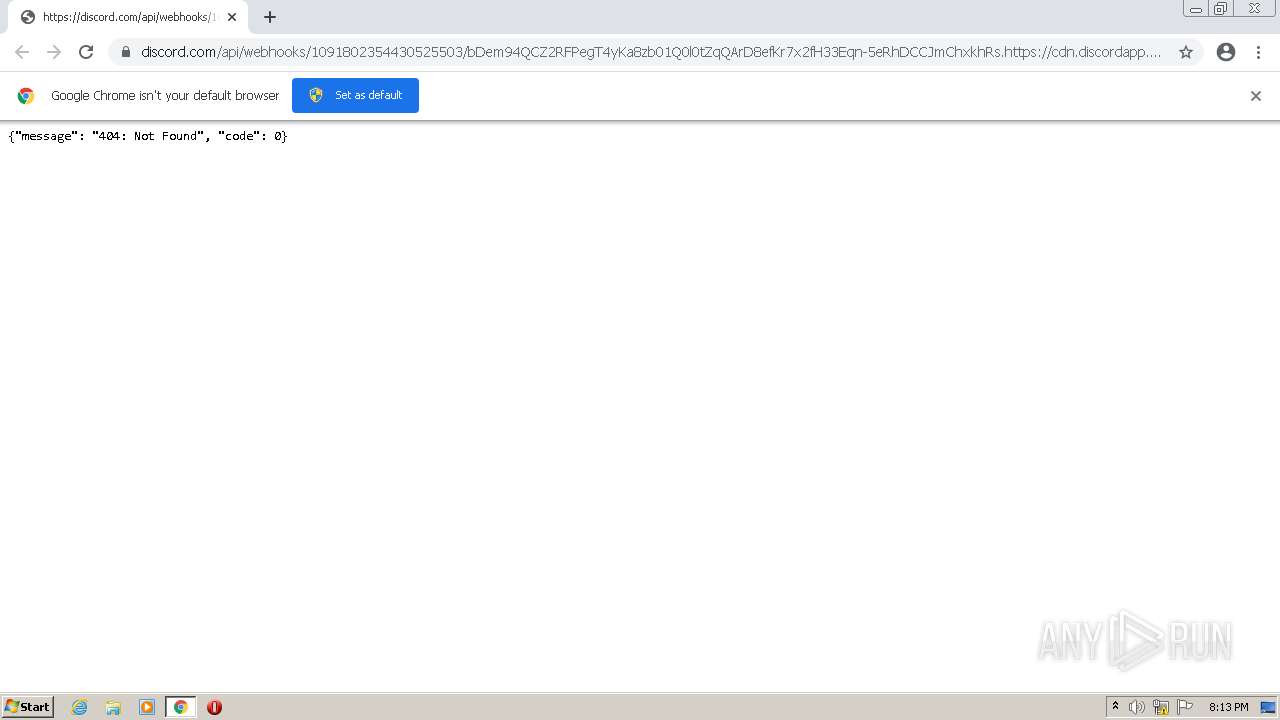
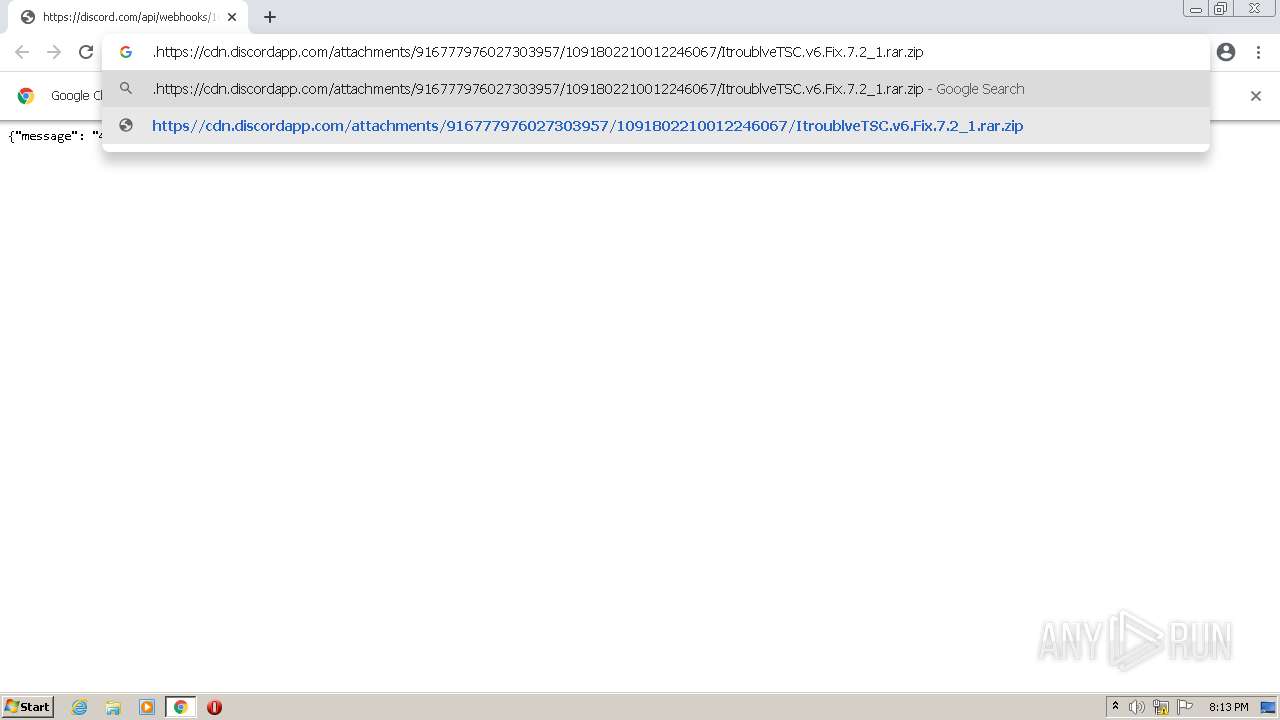
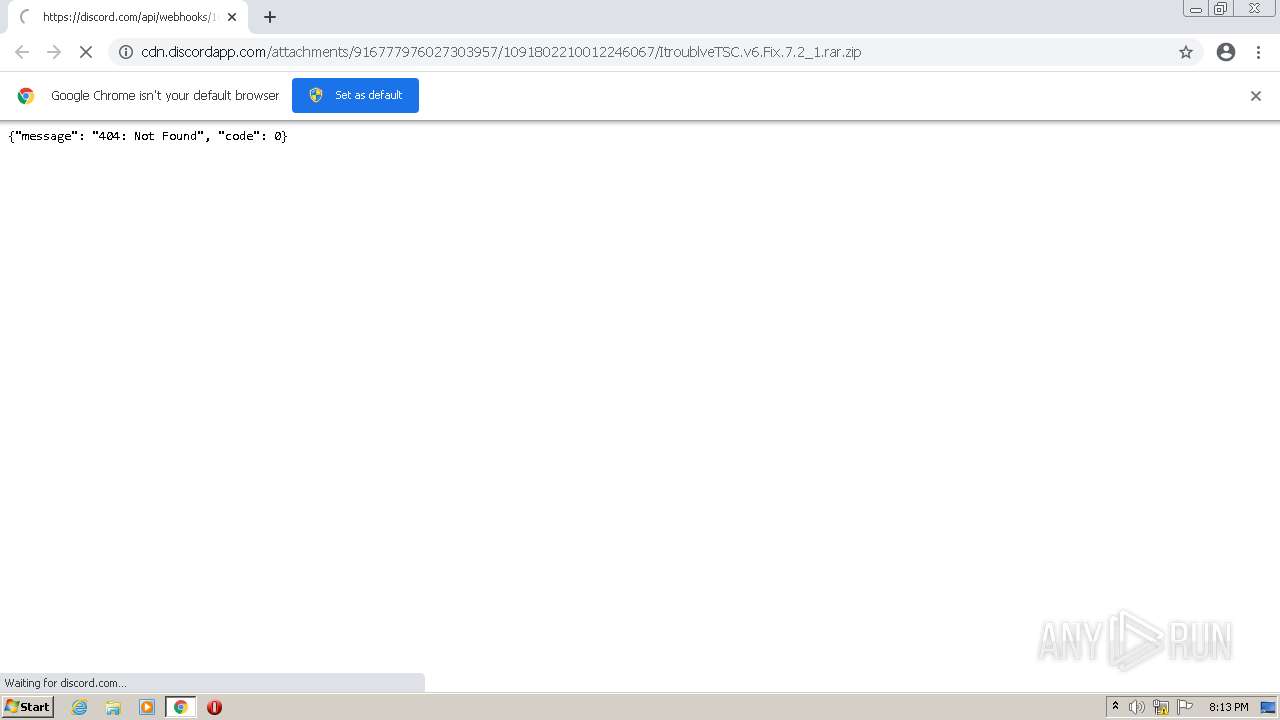
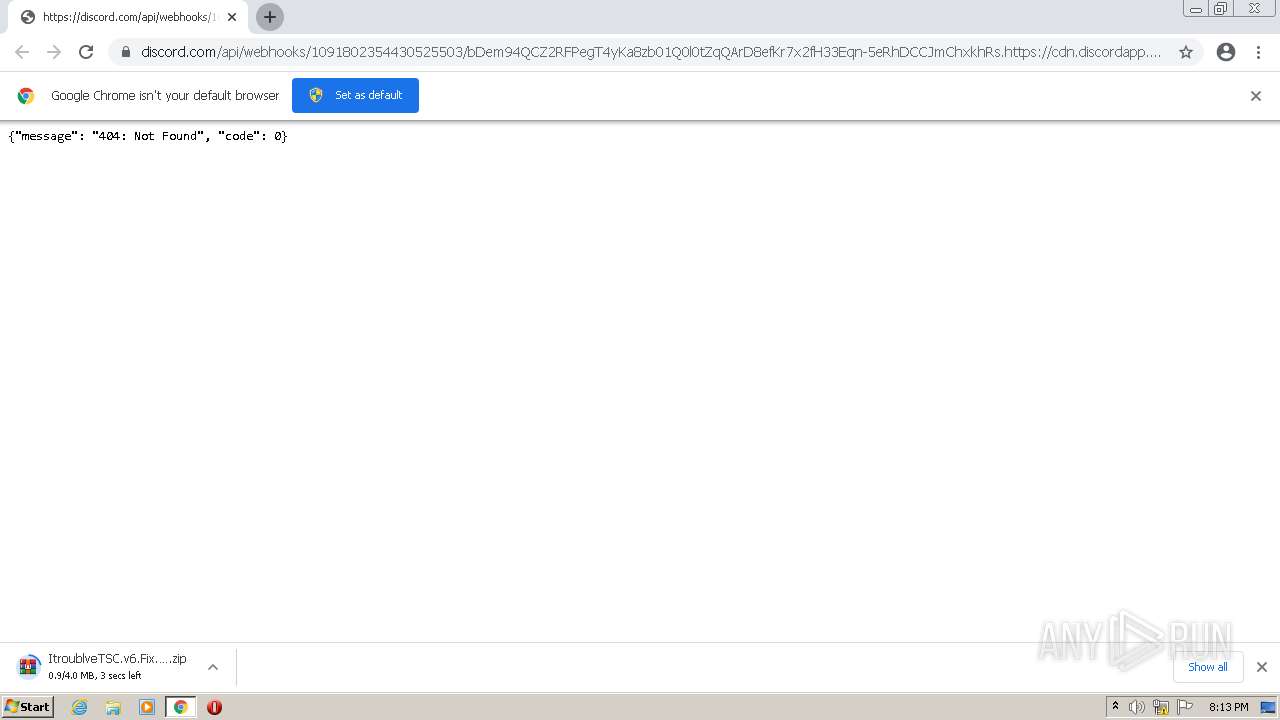
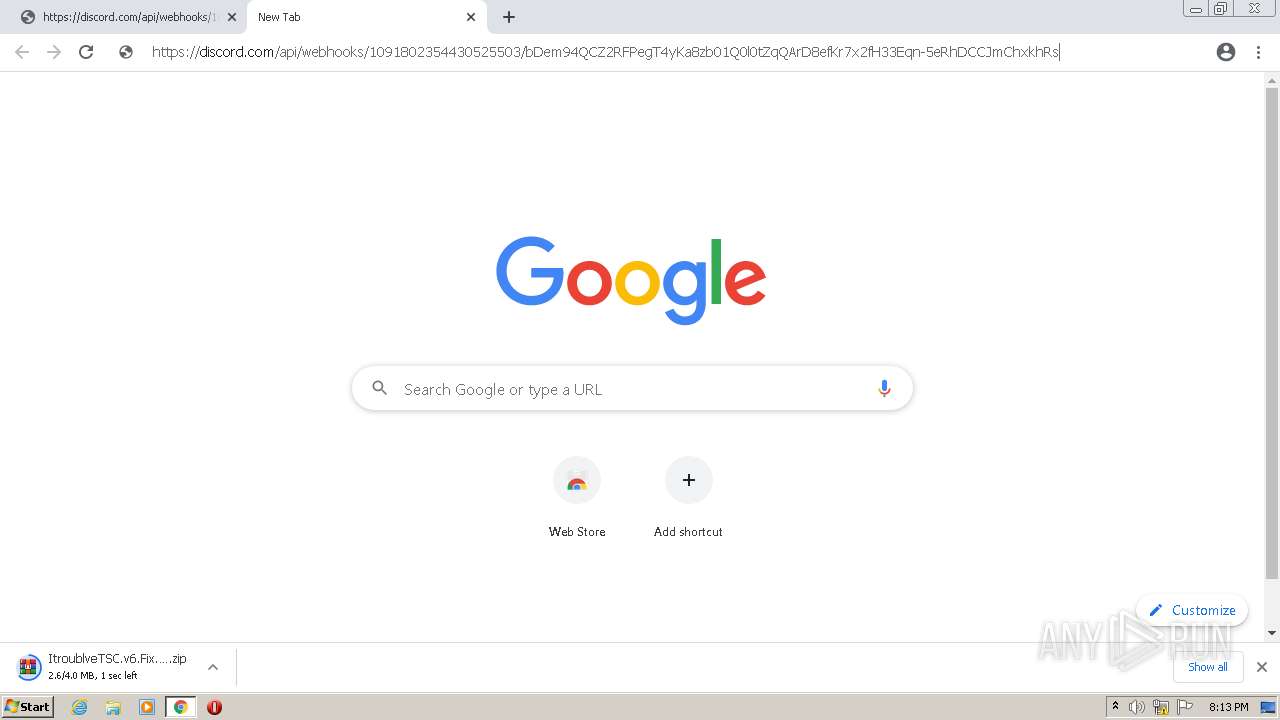
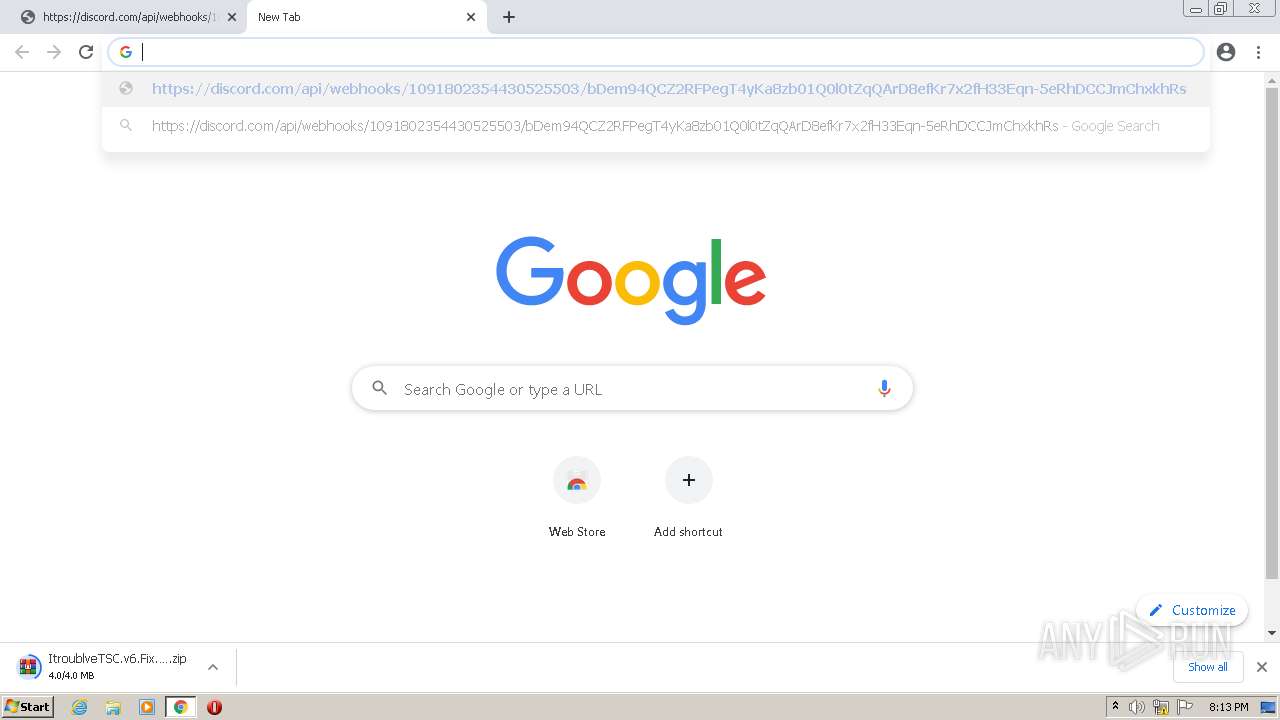
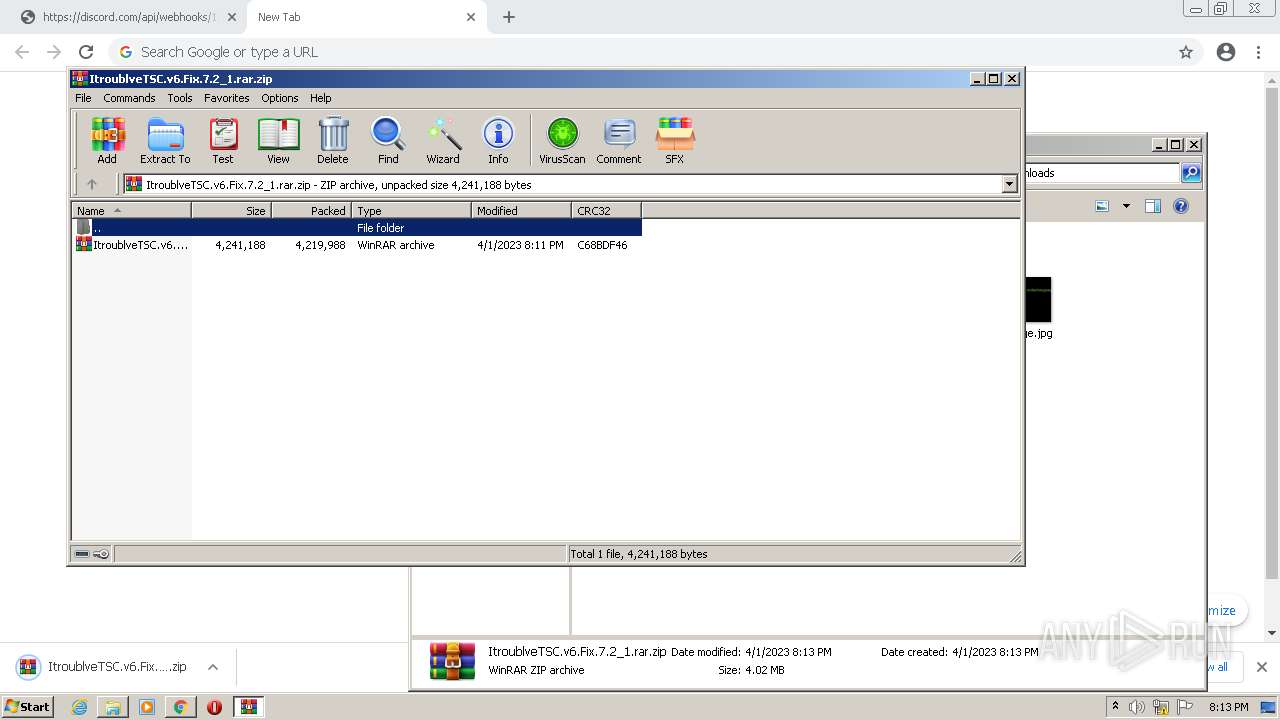
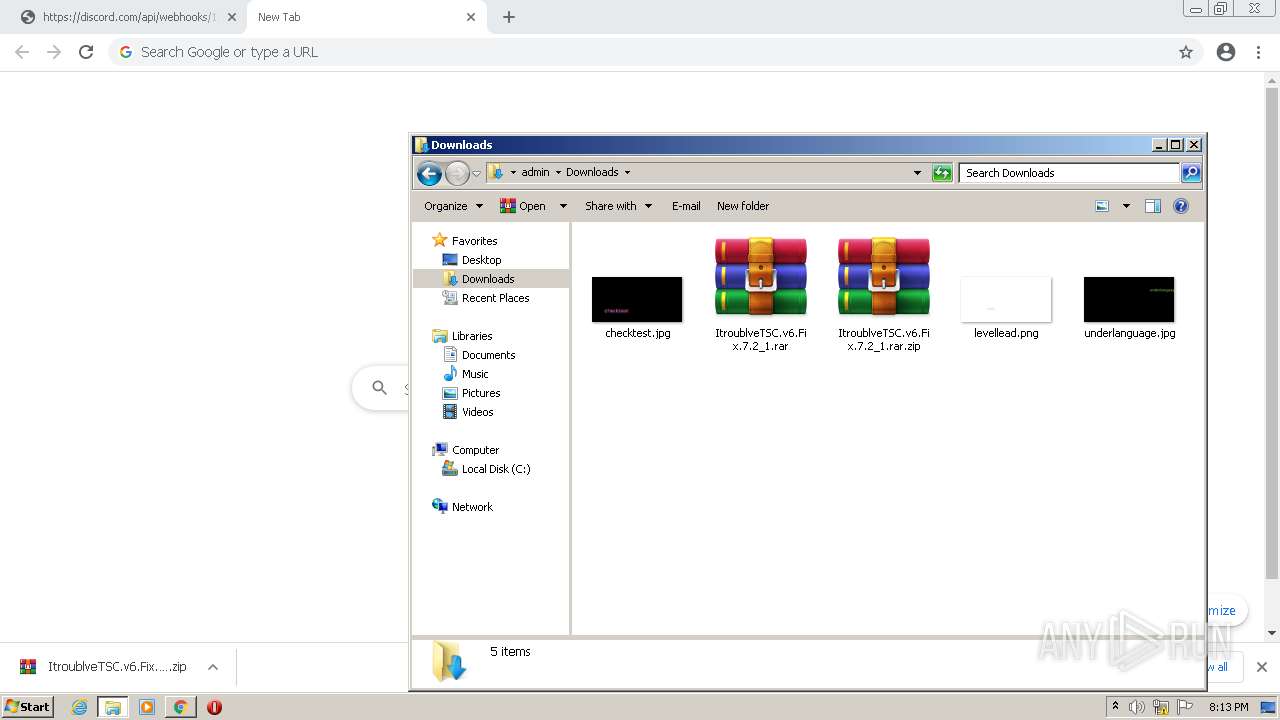
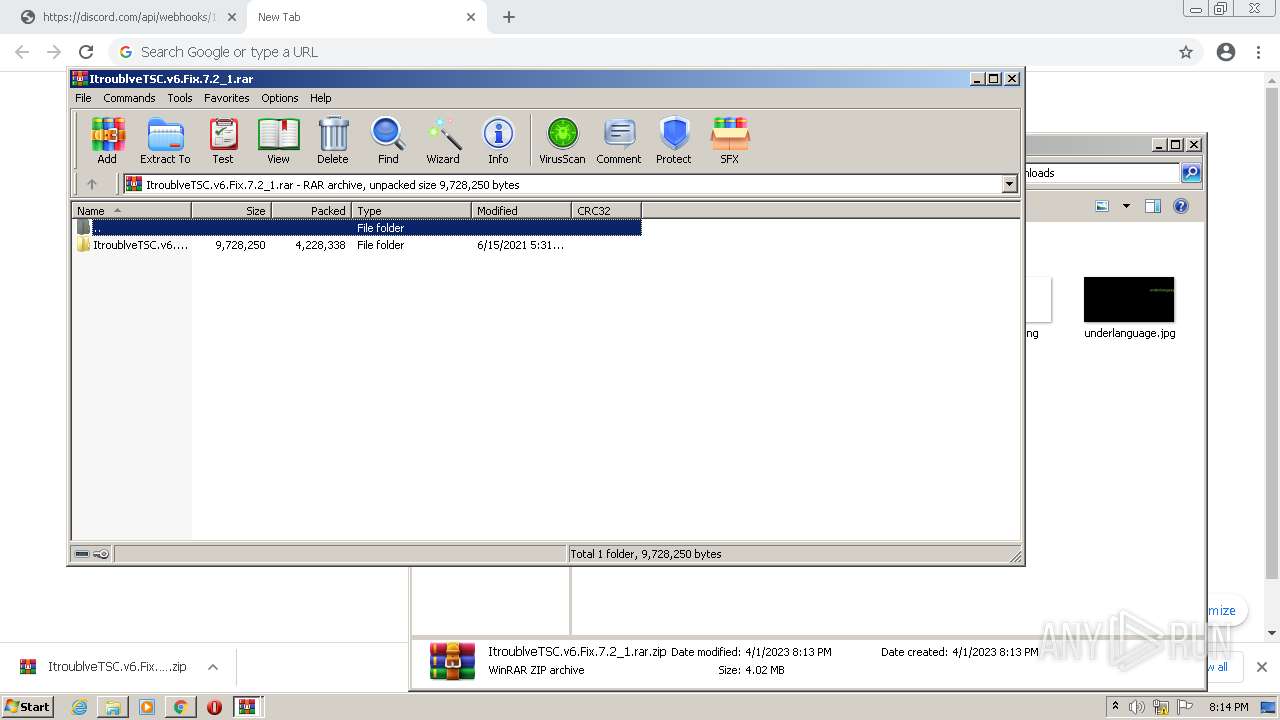
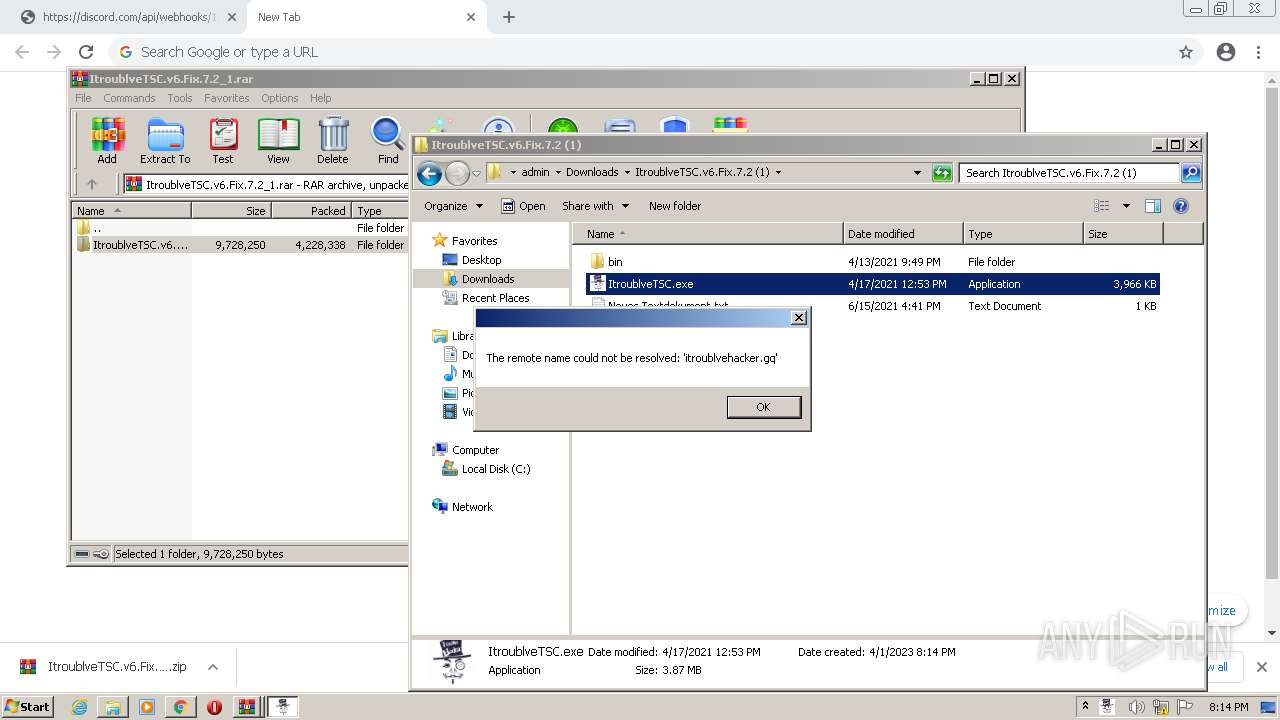
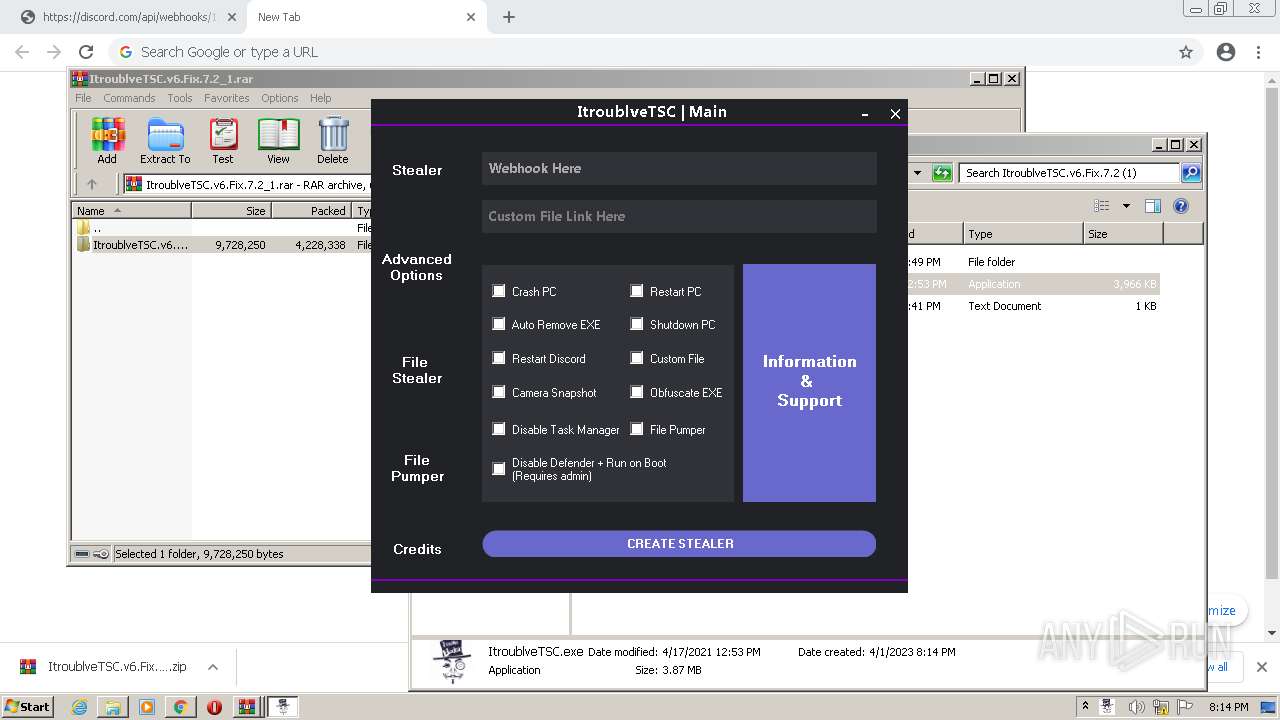
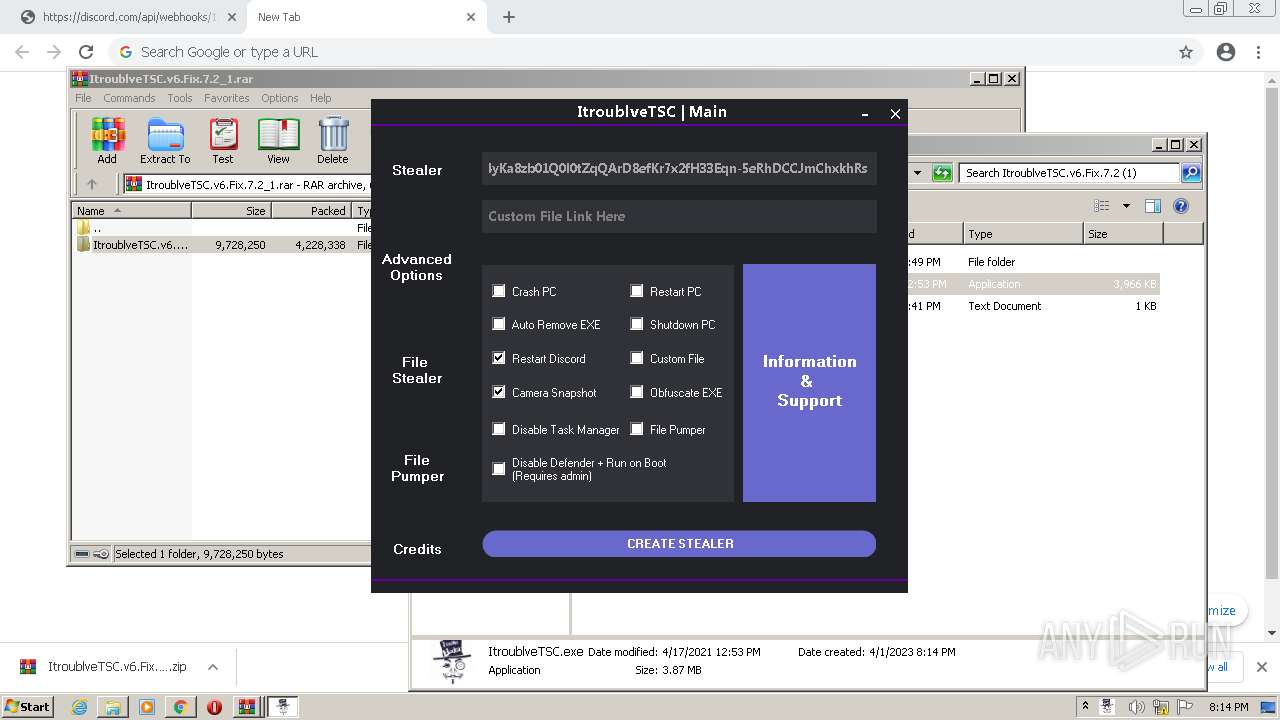
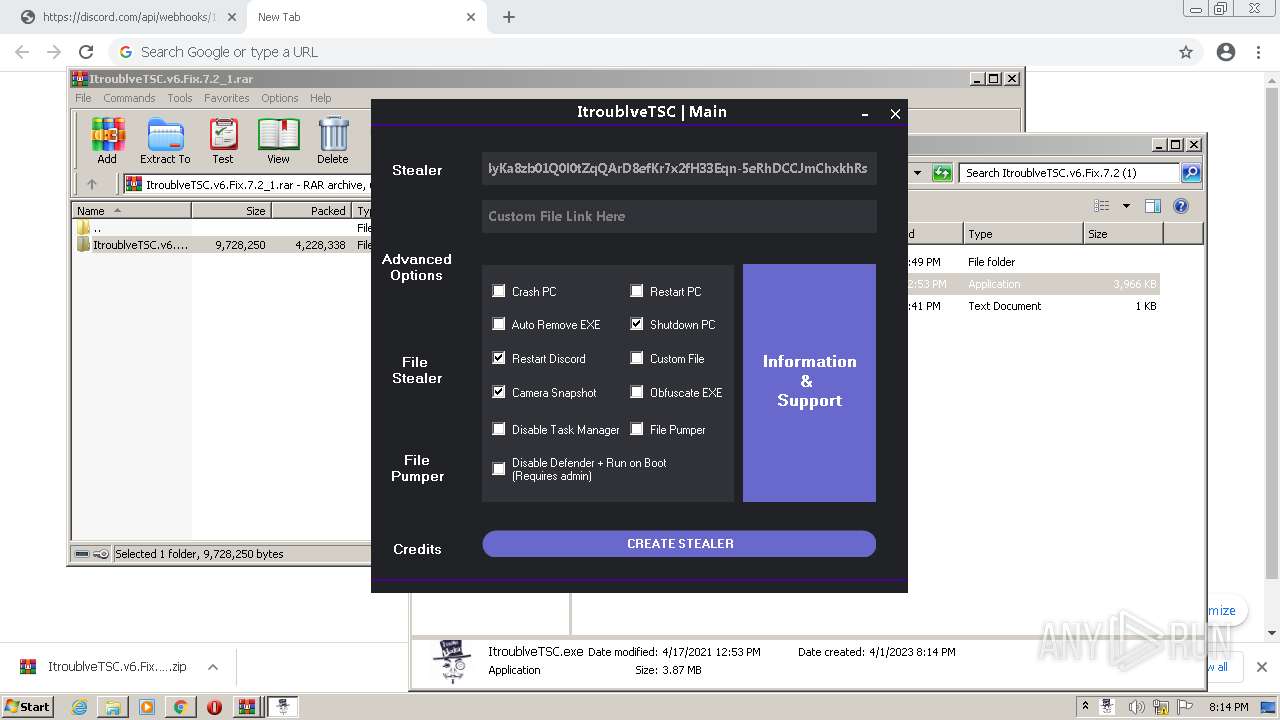
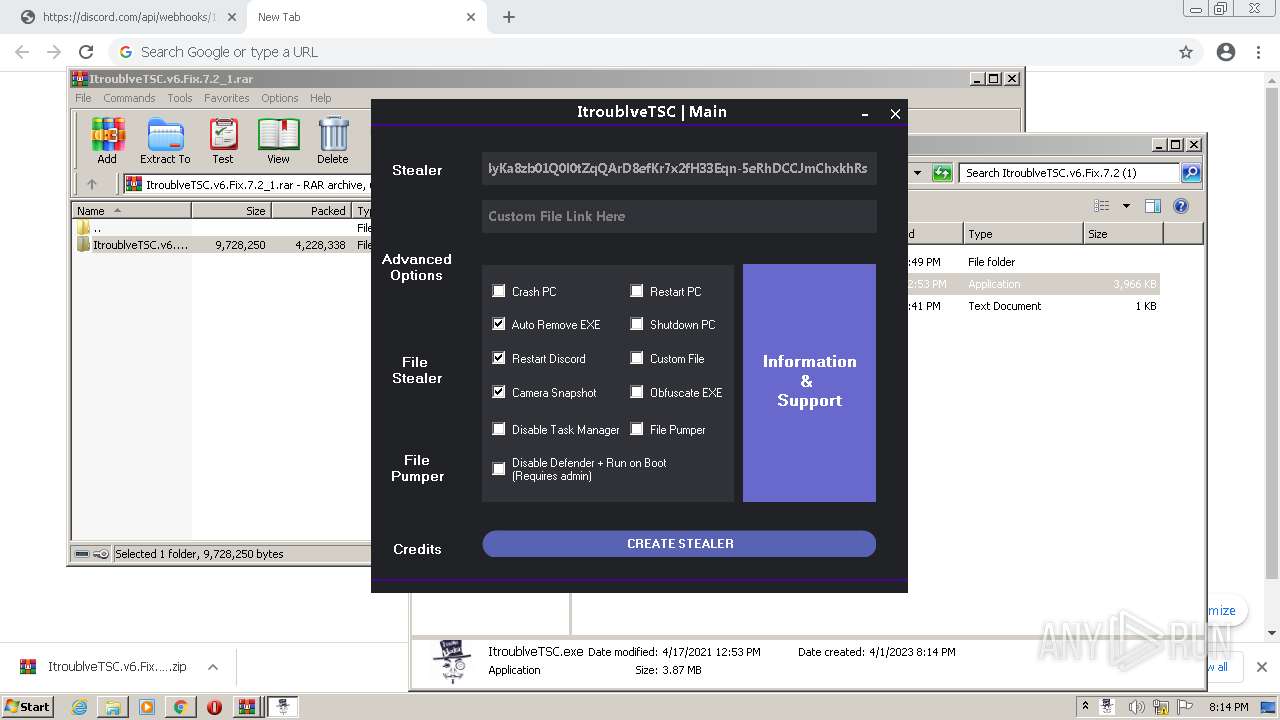
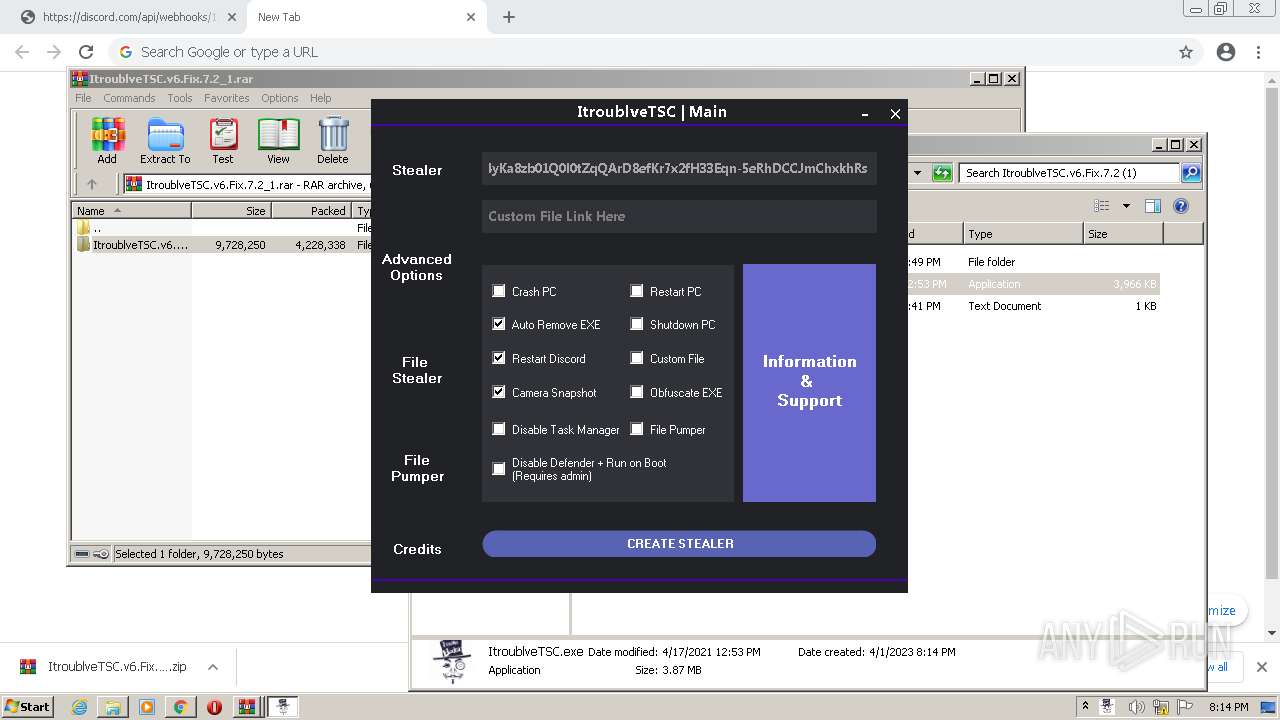
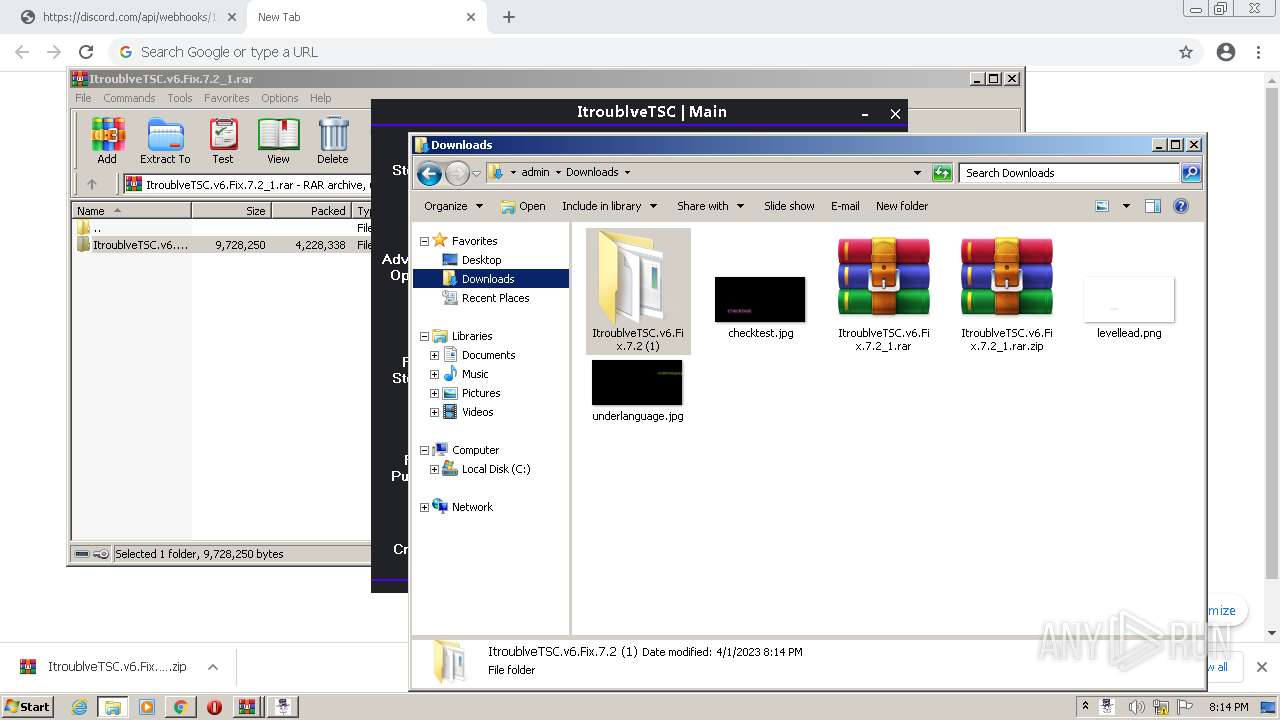
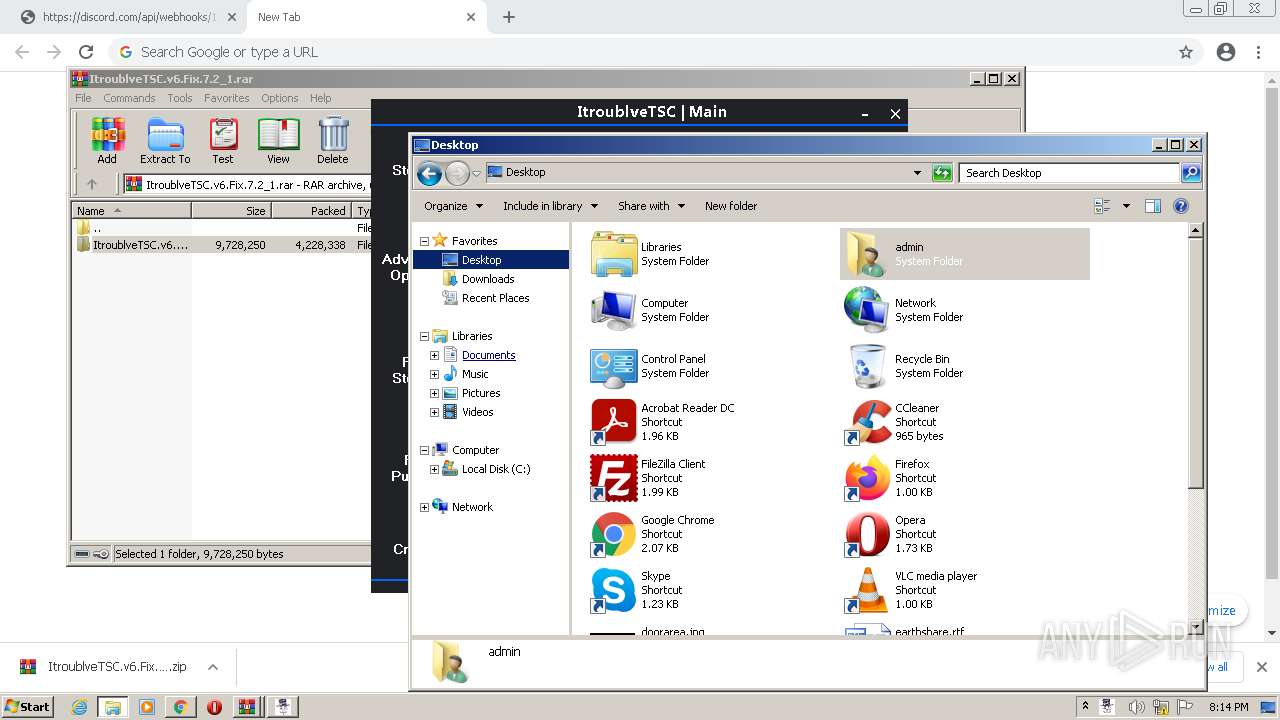
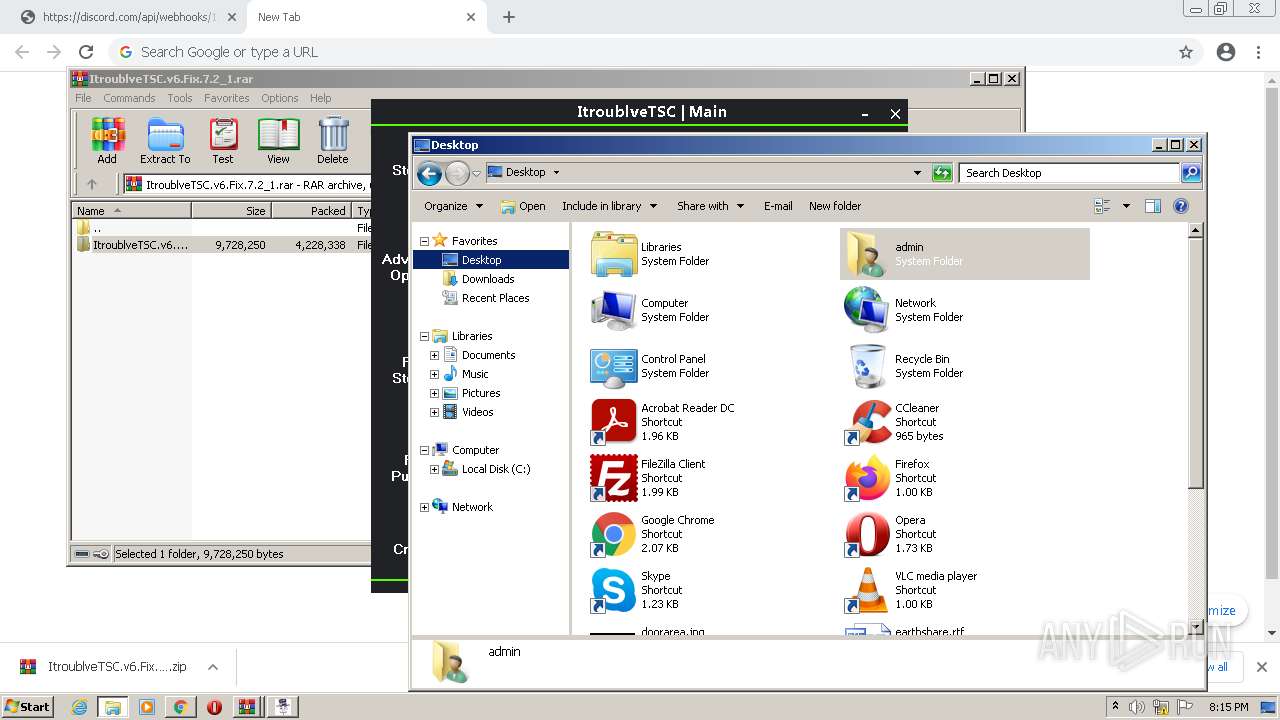
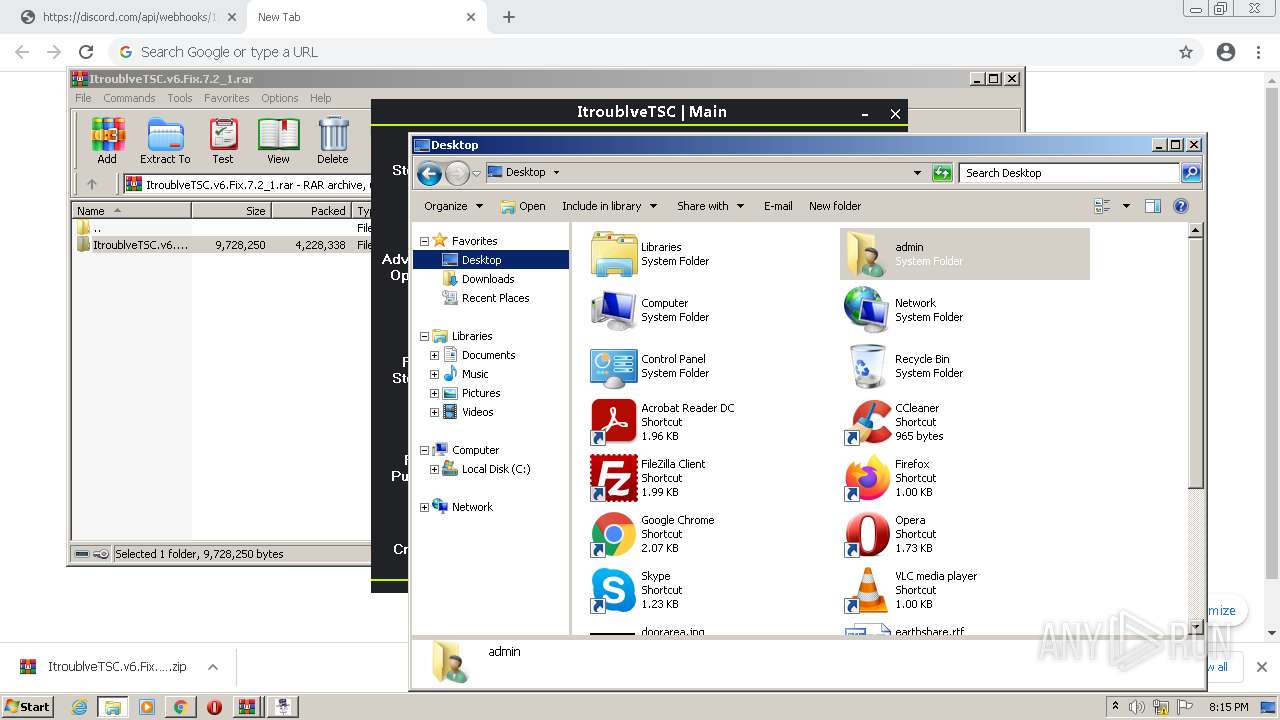
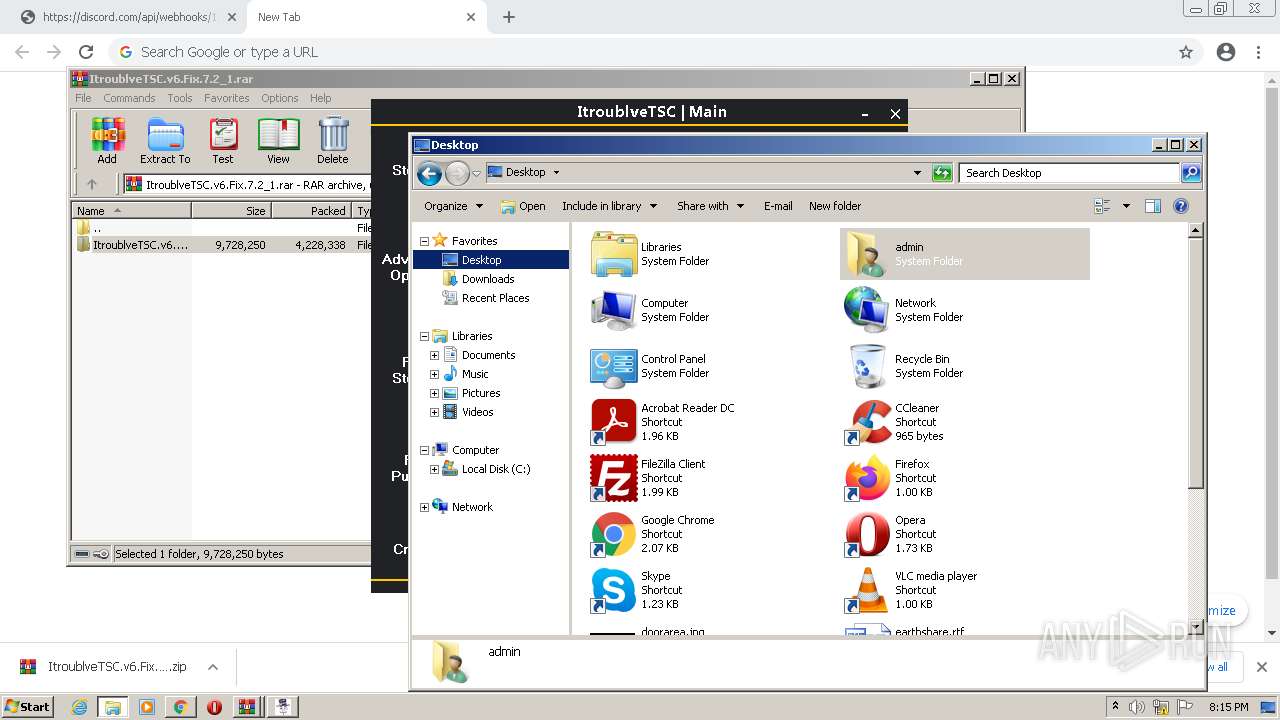
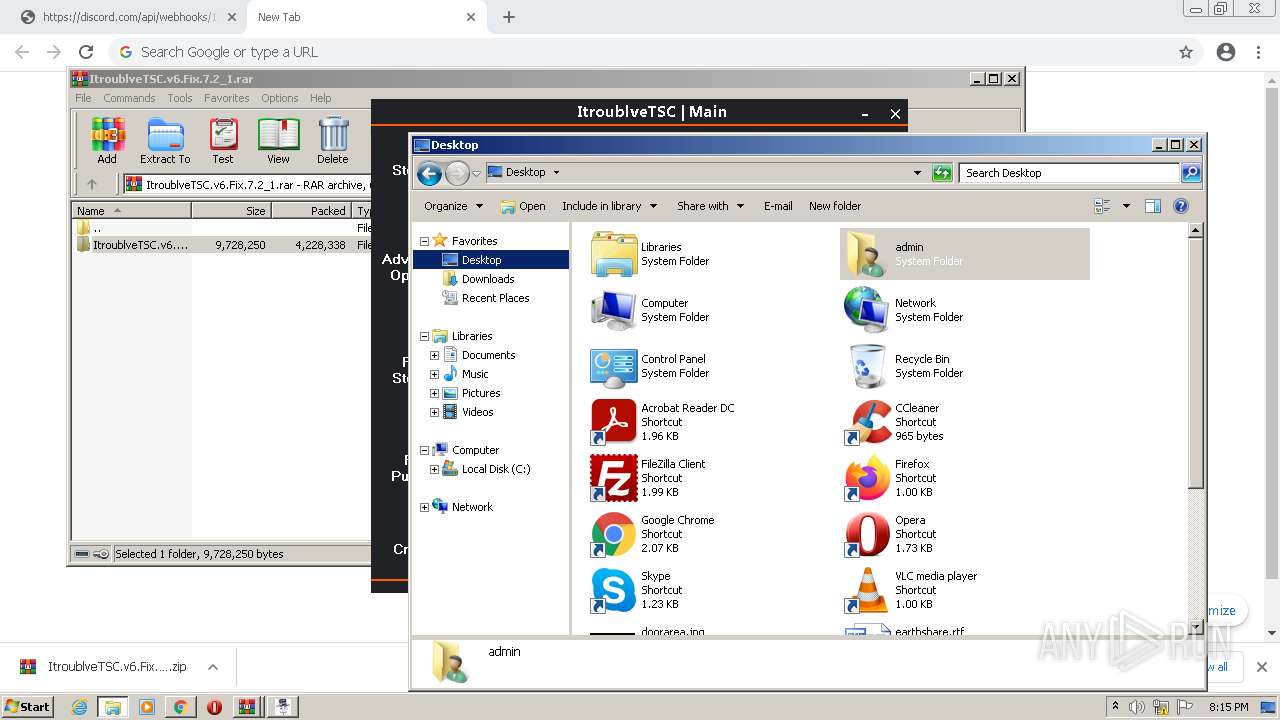
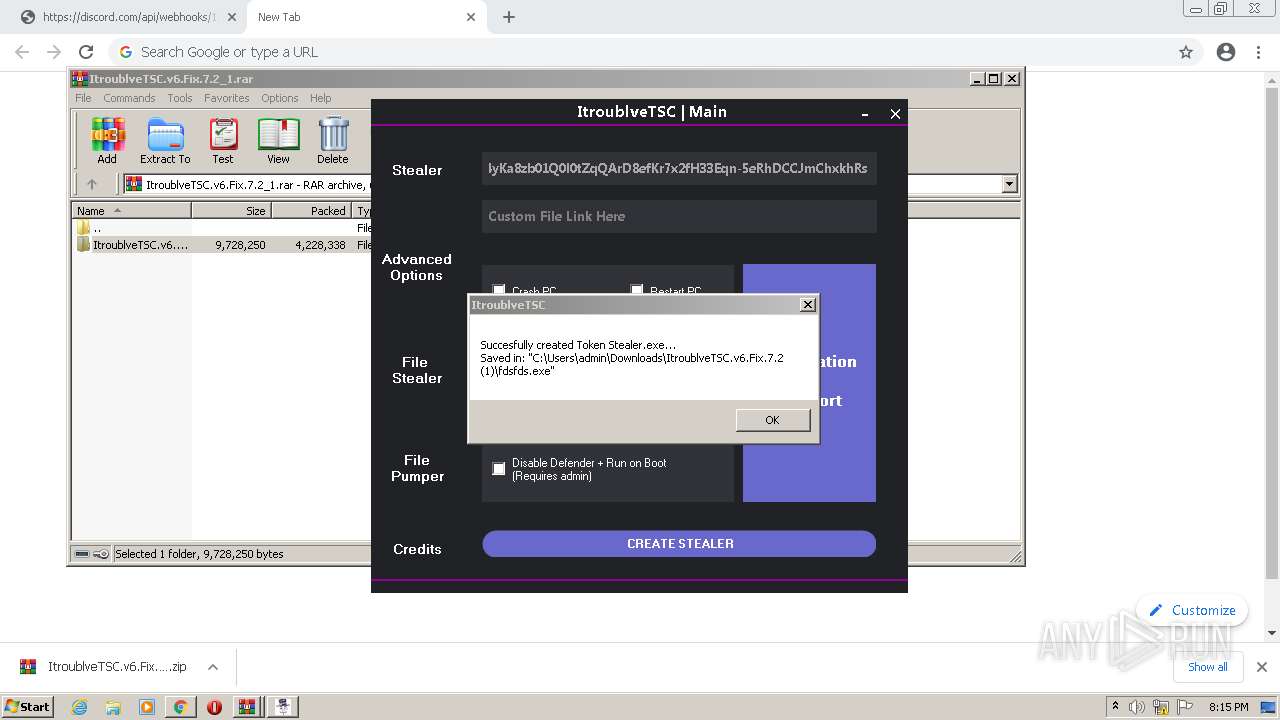
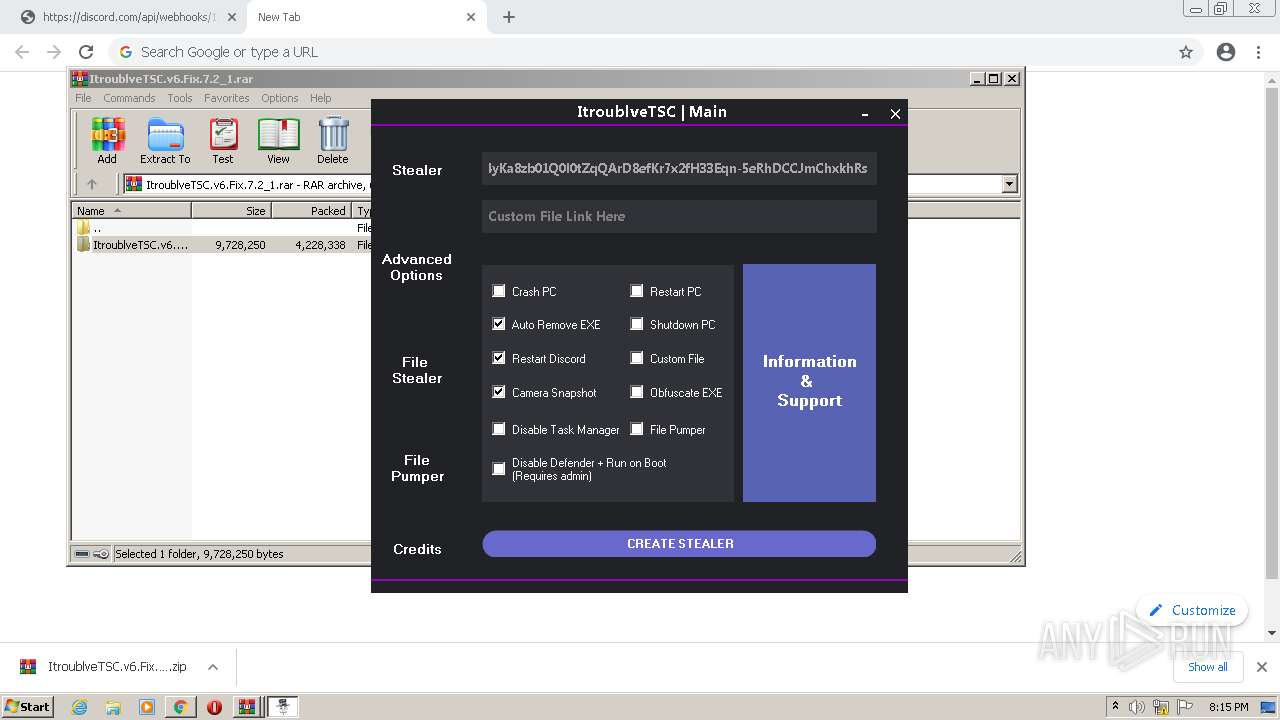
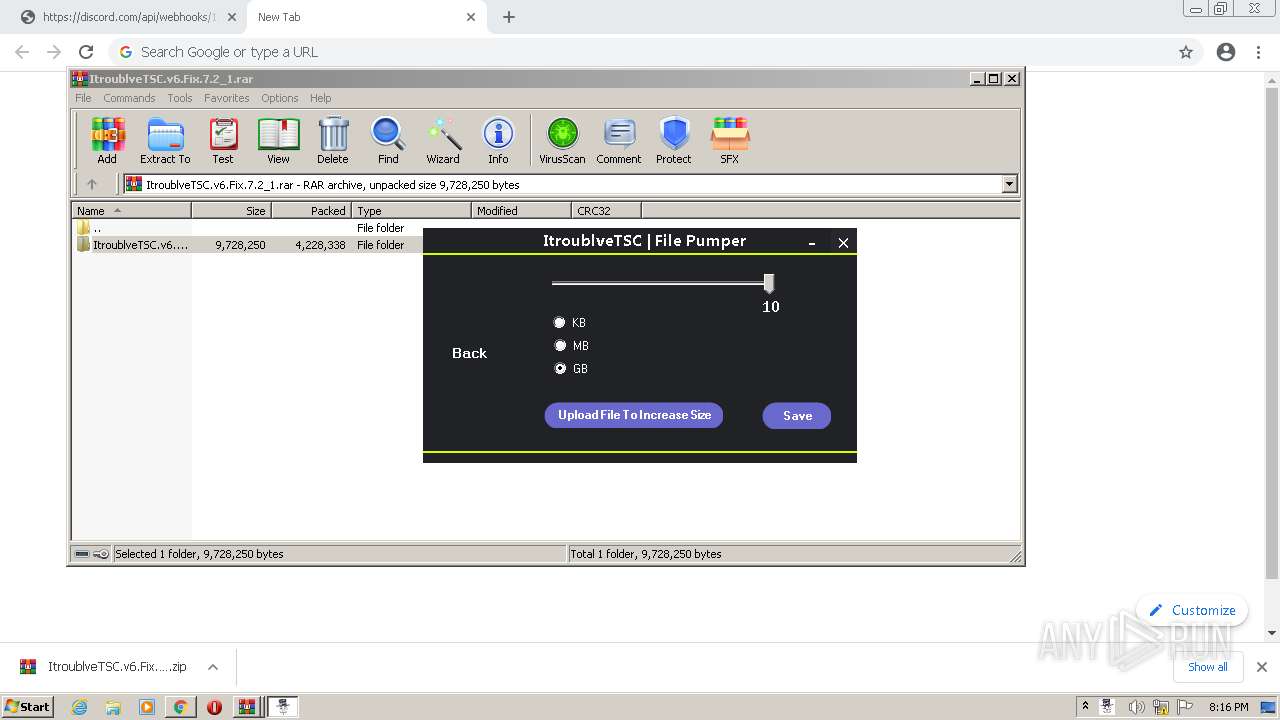
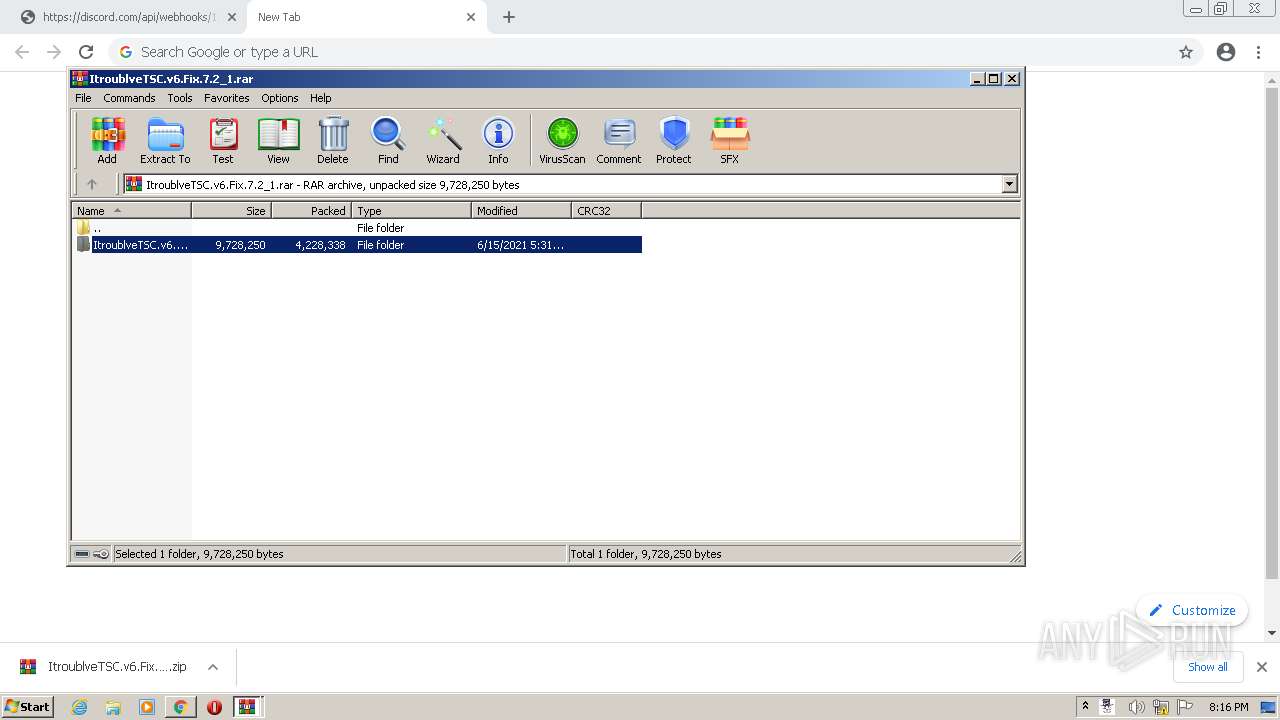
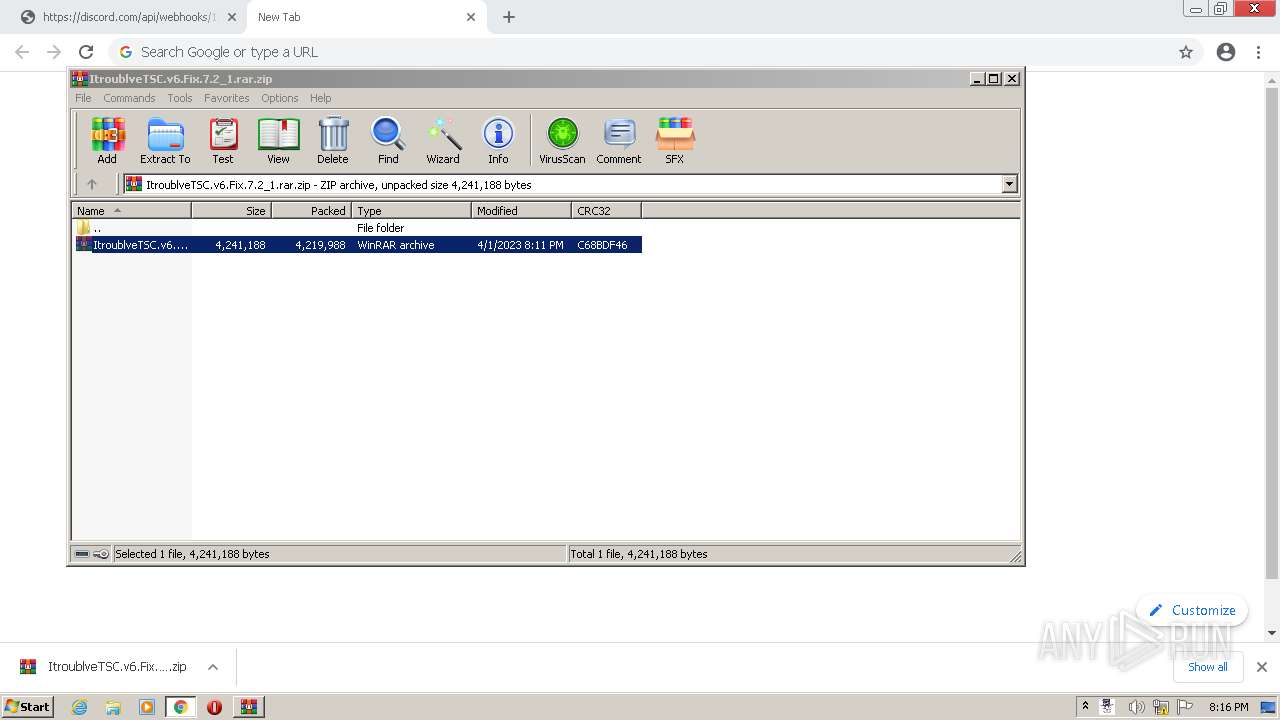
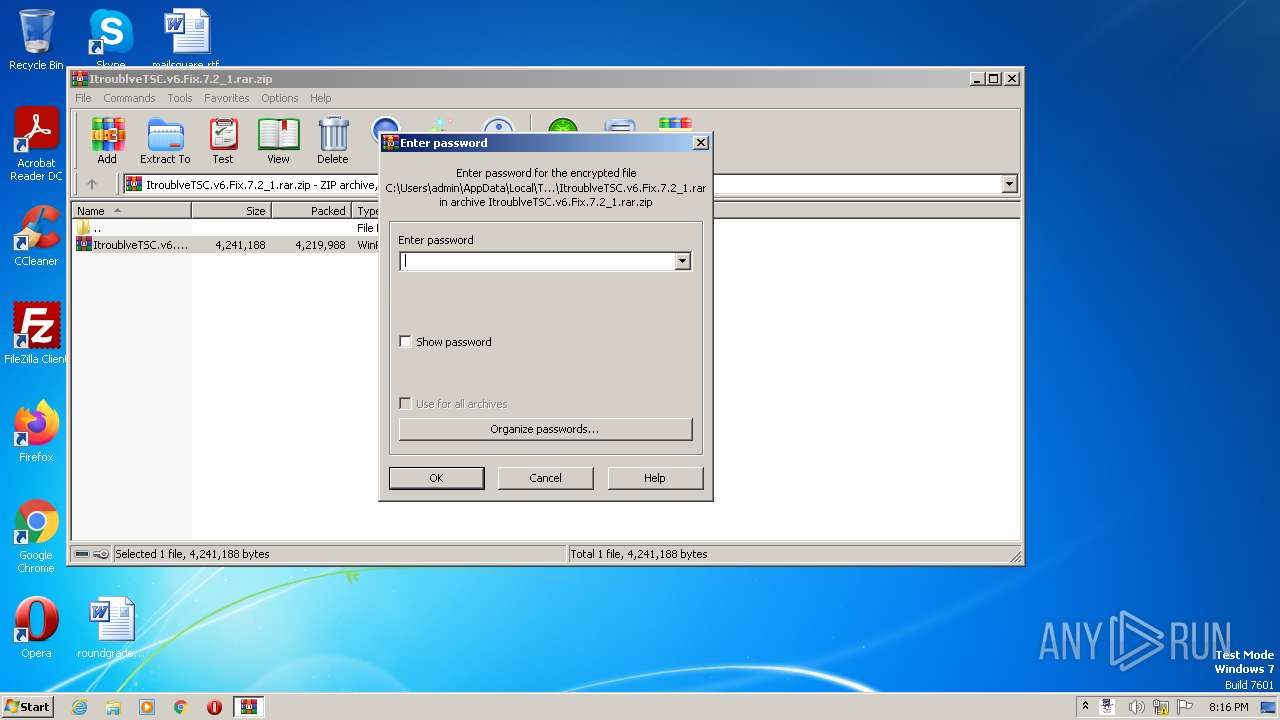
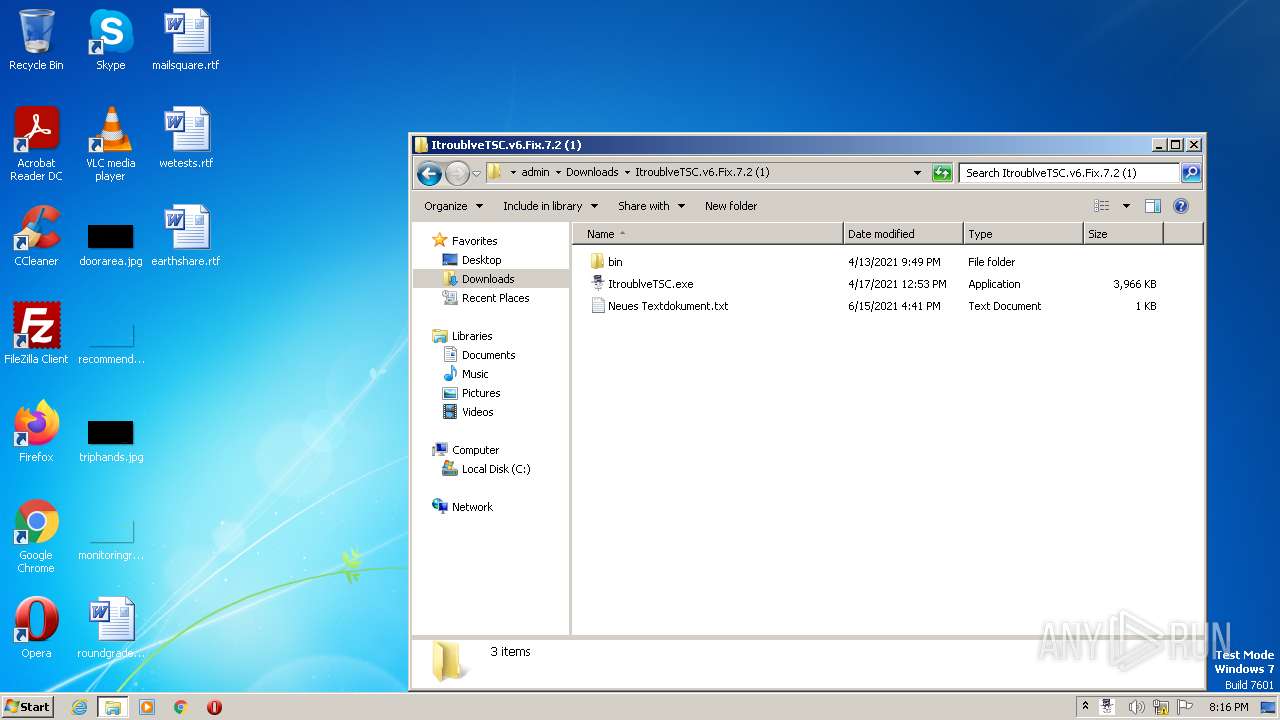
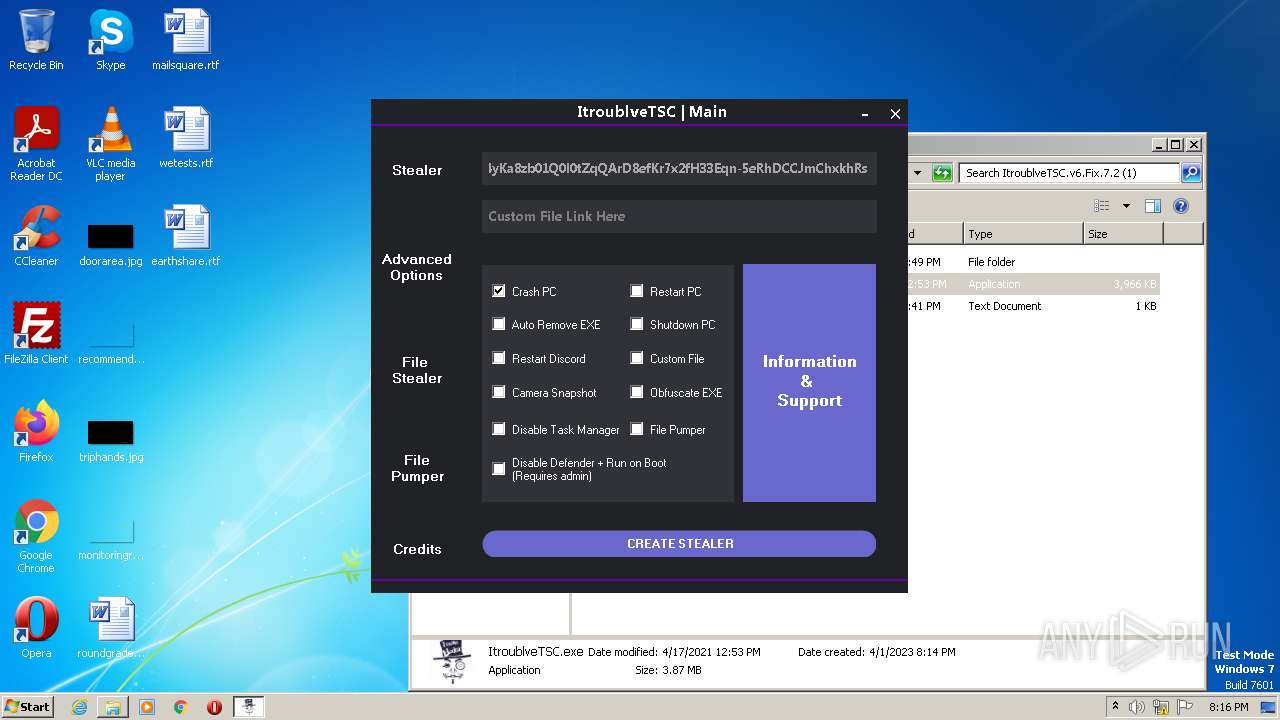
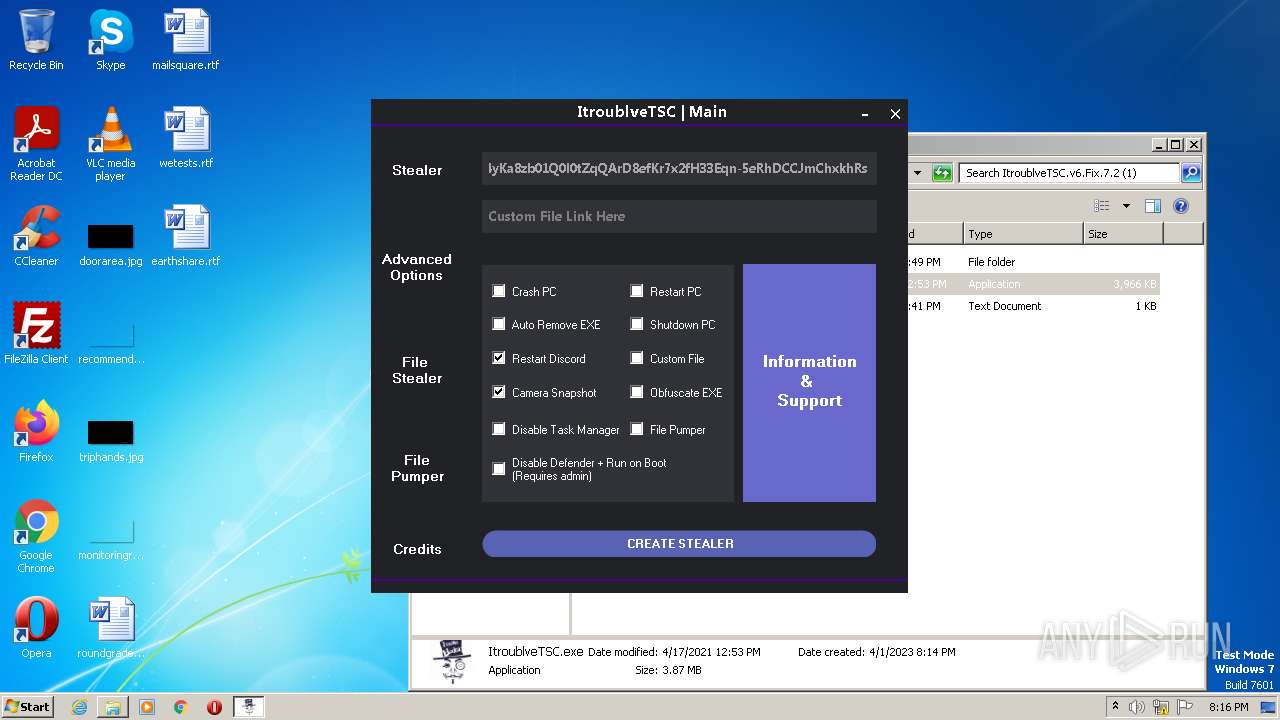
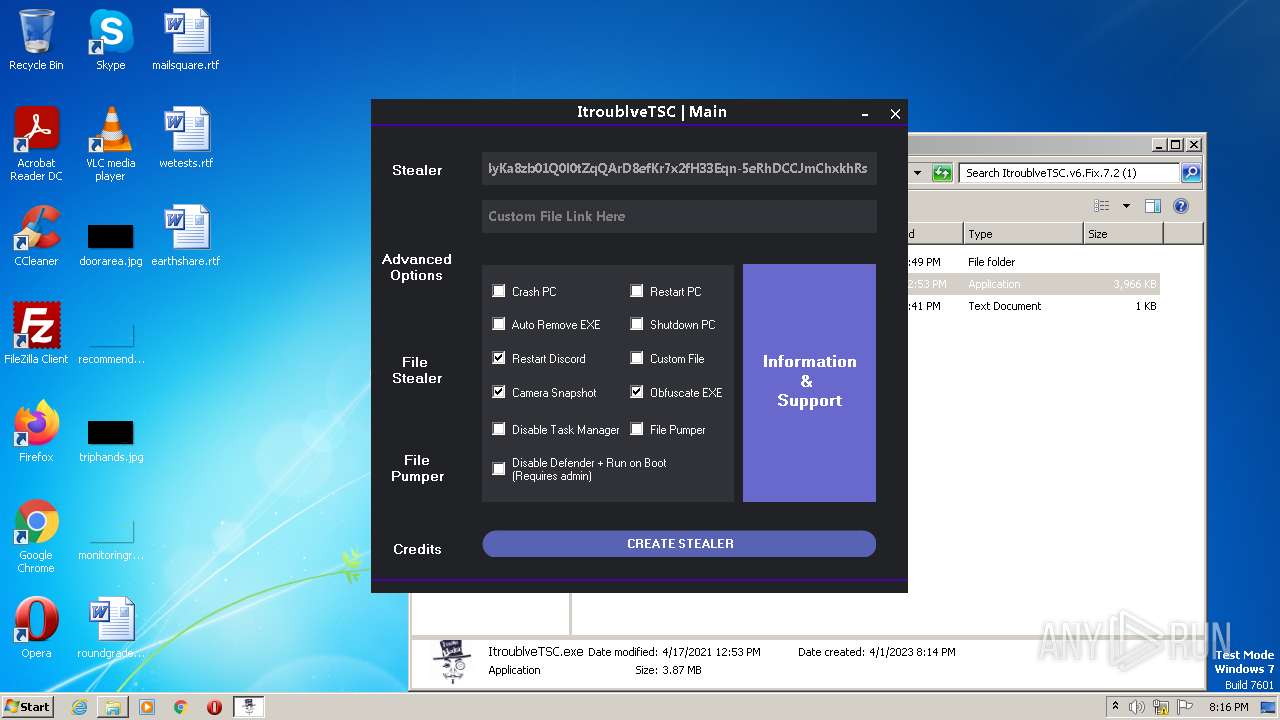
| URL: | https://discord.com/api/webhooks/1091802354430525503/bDem94QCZ2RFPegT4yKa8zb01Q0l0tZqQArD8efKr7x2fH33Eqn-5eRhDCCJmChxkhRs.https://cdn.discordapp.com/attachments/916777976027303957/1091802210012246067/ItroublveTSC.v6.Fix.7.2_1.rar.zip |
| Full analysis: | https://app.any.run/tasks/099f76ae-205f-4188-97e0-f475d2114d87 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 19:13:09 |
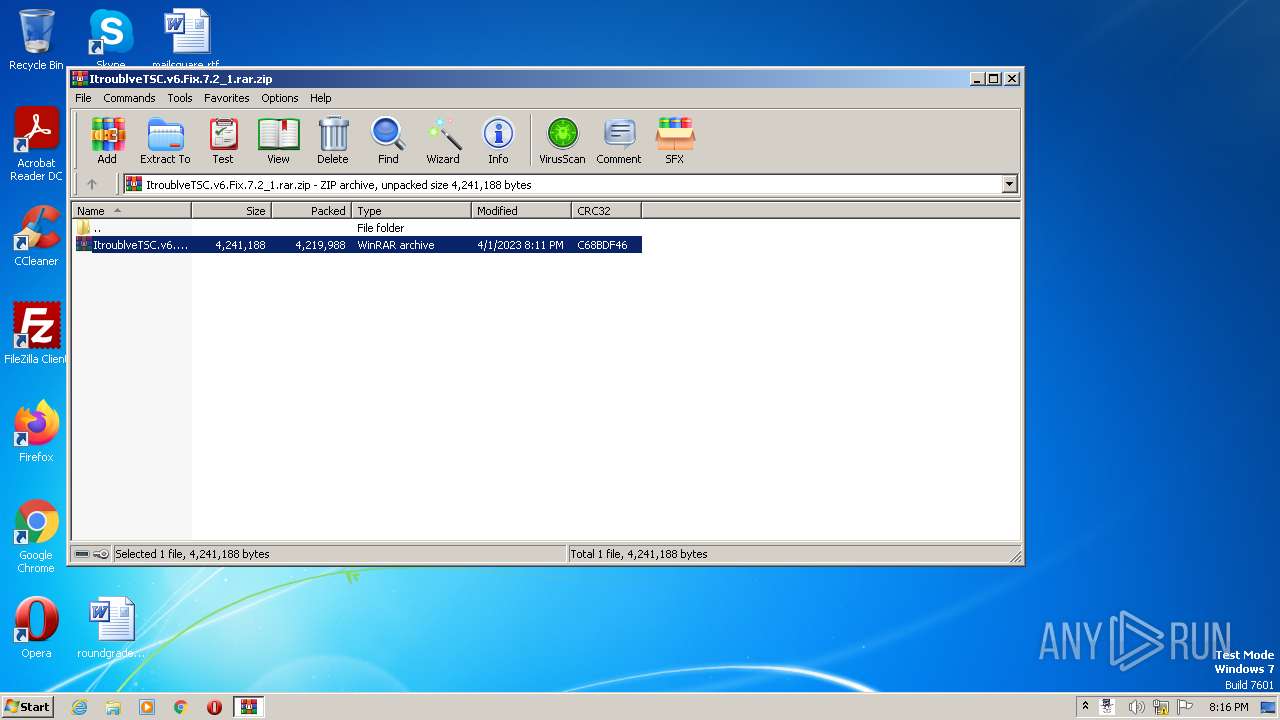
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A04D20E83AF1B7179AB735AA28D8951B |
| SHA1: | 93A9BCB0B676F33AD12504A6125ED8D6A81F538D |
| SHA256: | 3702A40C159FF3A1F309B730FED35D8159BF905C2F13A34C0B16AA8CAA0E957C |
| SSDEEP: | 6:2UzUzh1Xsh7UvCW3eHcry6XlehjtQzToAJvQLBPV:2UzKct8qHc6tQzToyeBPV |
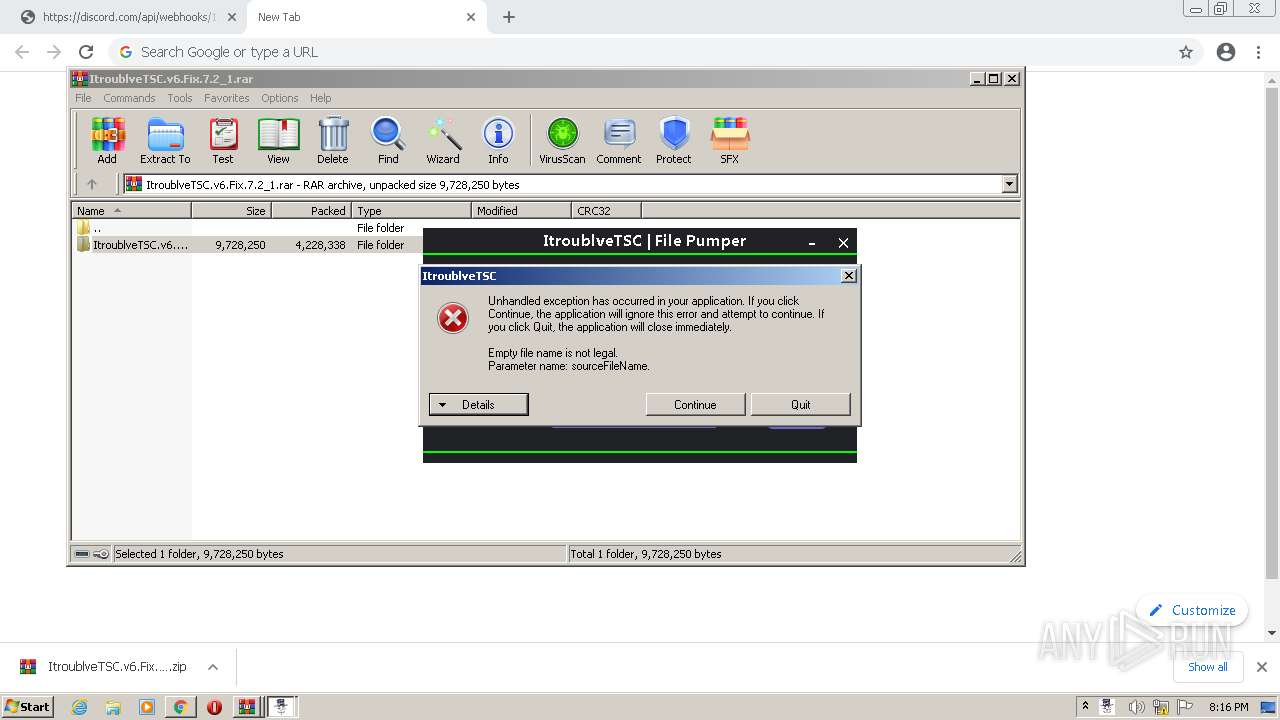
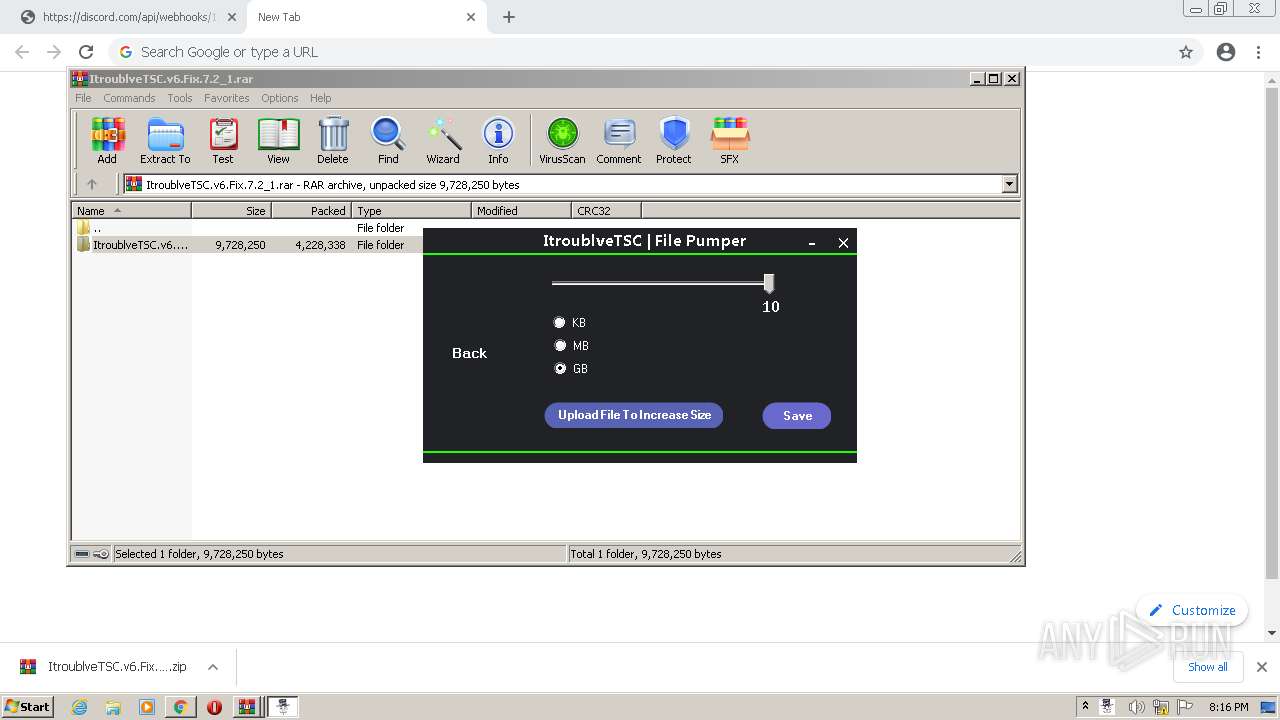
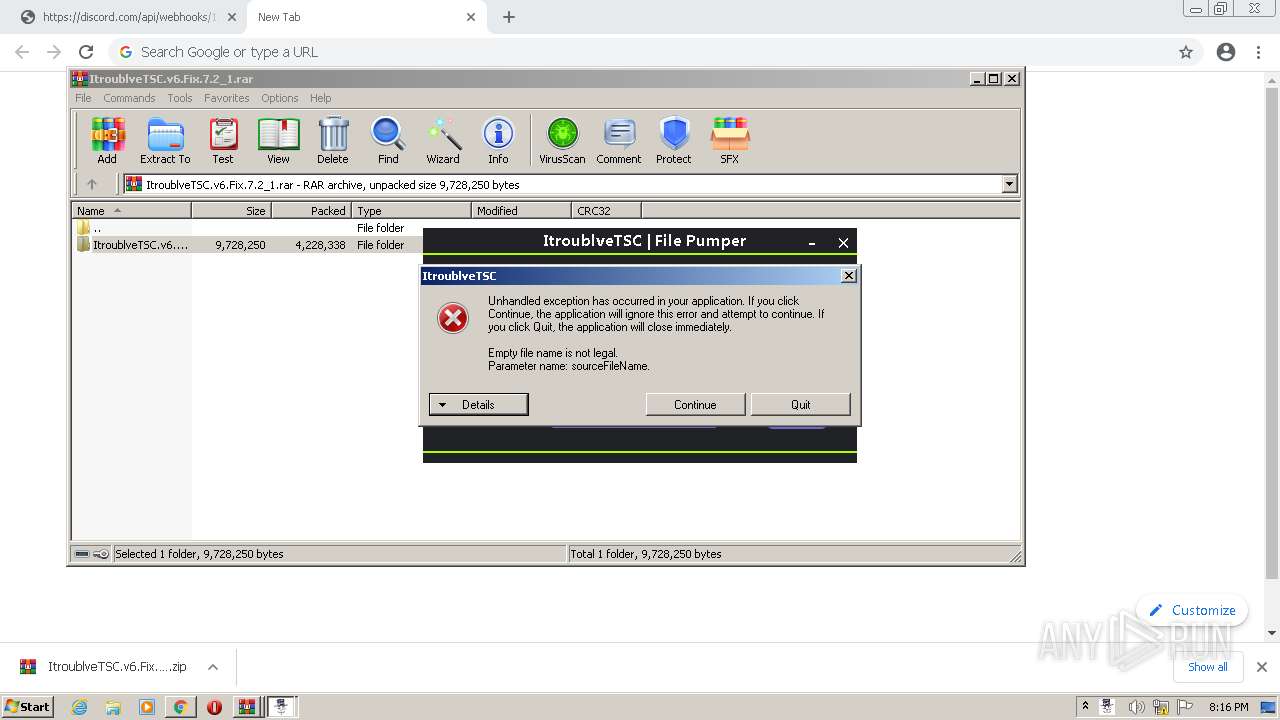
MALICIOUS
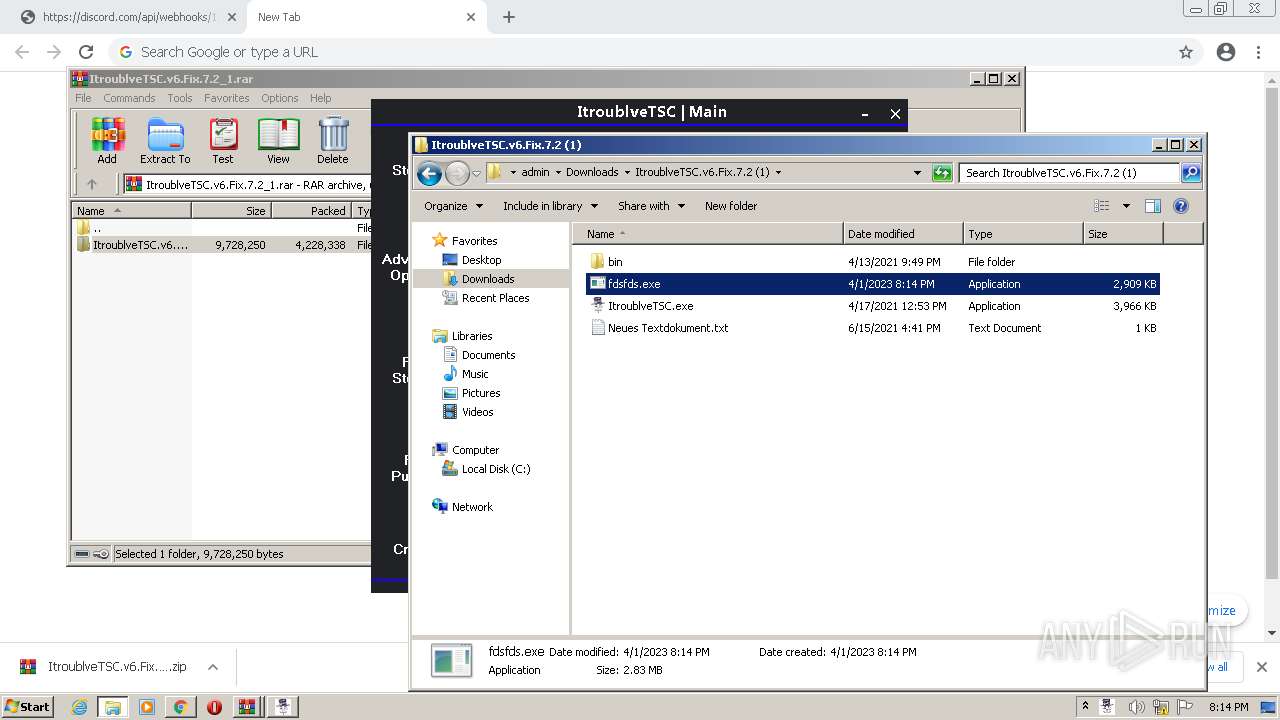
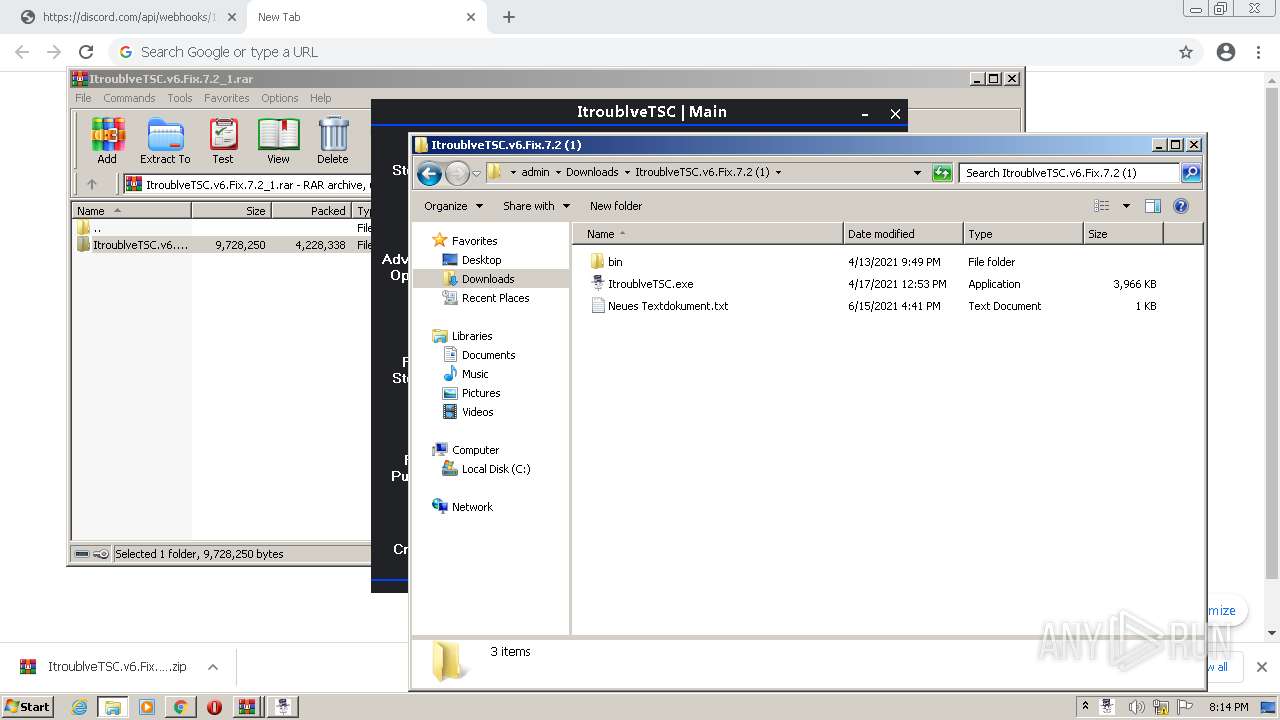
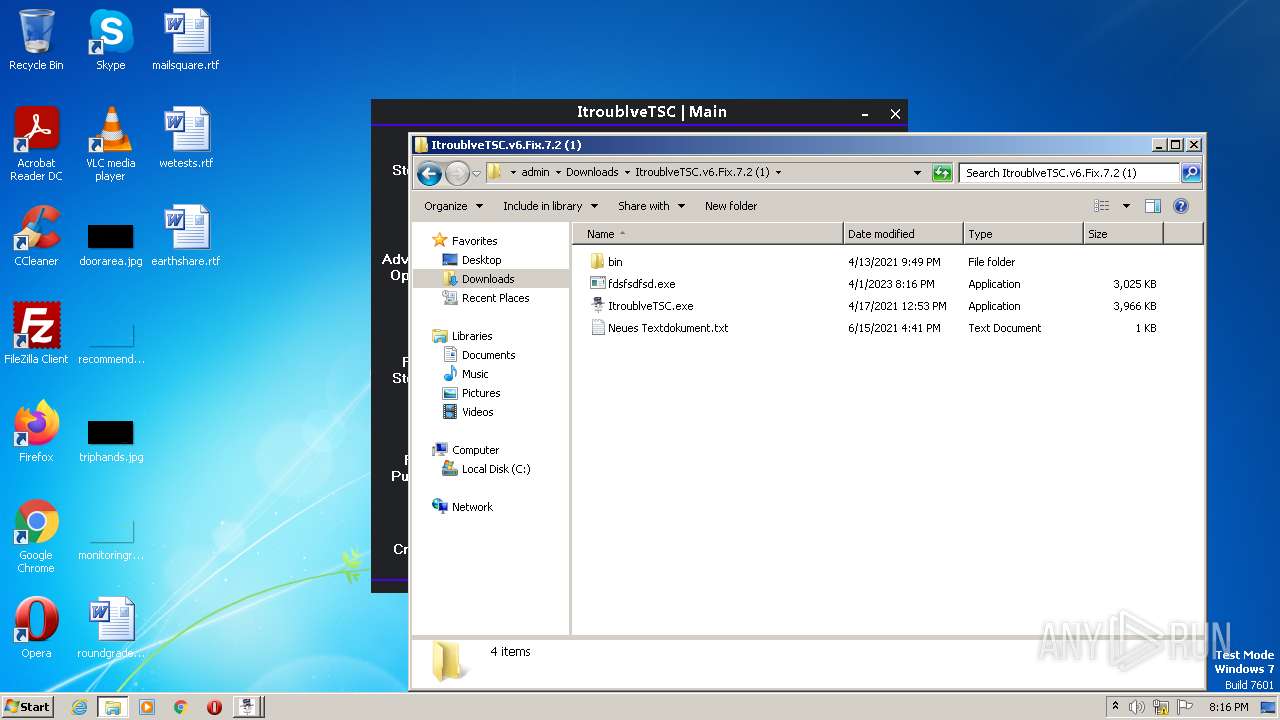
Application was dropped or rewritten from another process
- ItroublveTSC.exe (PID: 1748)
- fdsfds.exe (PID: 3488)
- RtkBtManServ.exe (PID: 1640)
- bfsvc.exe (PID: 1060)
- snuvcdsm.exe (PID: 600)
- winhlp32.exe (PID: 1940)
- splwow64.exe (PID: 3096)
- hh.exe (PID: 2096)
- xwizard.exe (PID: 3704)
- ItroublveTSC.exe (PID: 1436)
- CLI.exe (PID: 1392)
- fdsfsdfsd.exe (PID: 2428)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 2244)
- fdsfsdfsd.exe (PID: 1616)
- bfsvc.exe (PID: 3136)
- fdsfsdfsd.exe (PID: 3764)
- snuvcdsm.exe (PID: 2864)
- winhlp32.exe (PID: 1180)
- splwow64.exe (PID: 1412)
- hh.exe (PID: 3260)
- fdsfsdfsd.exe (PID: 2148)
- xwizard.exe (PID: 3768)
- RtkBtManServ.exe (PID: 3032)
- fdsfsdfsd.exe (PID: 116)
- bfsvc.exe (PID: 2188)
- snuvcdsm.exe (PID: 3768)
- winhlp32.exe (PID: 2384)
- hh.exe (PID: 3200)
- splwow64.exe (PID: 2772)
- xwizard.exe (PID: 2348)
Loads dropped or rewritten executable
- MSBuild.exe (PID: 2984)
- SearchProtocolHost.exe (PID: 2240)
- ItroublveTSC.exe (PID: 1748)
Starts Visual C# compiler
- MSBuild.exe (PID: 2984)
- MSBuild.exe (PID: 3672)
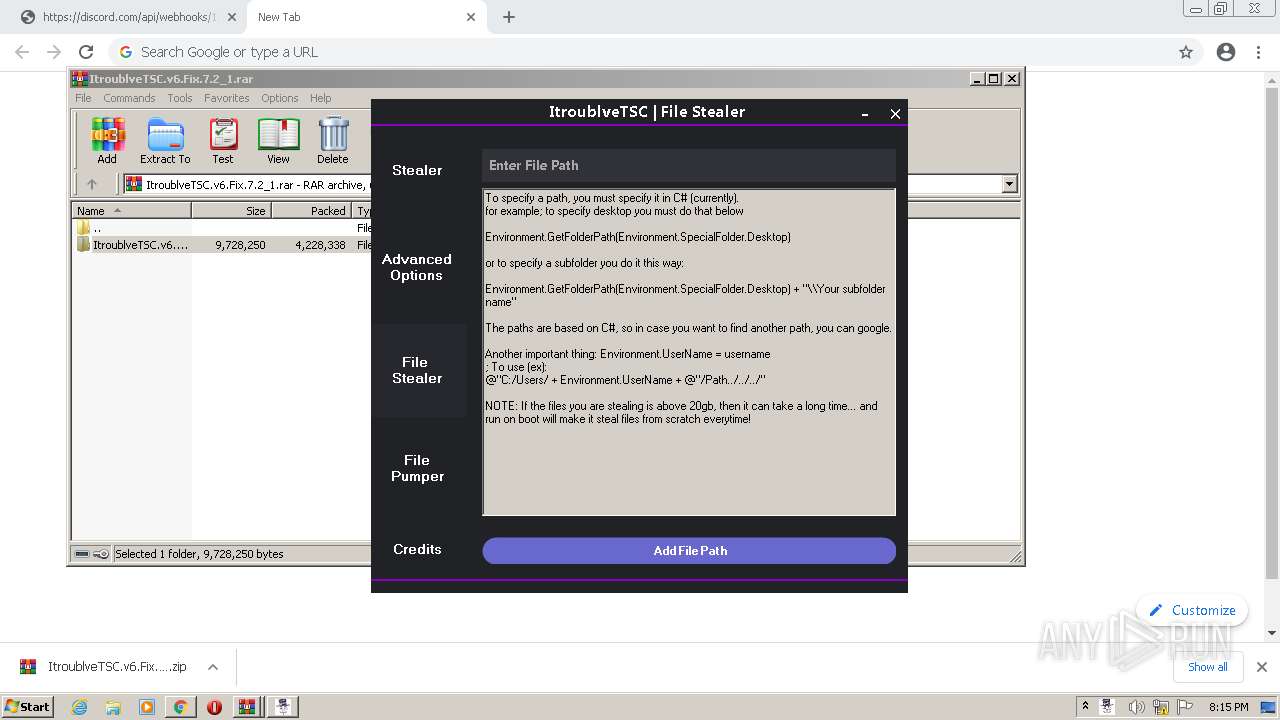
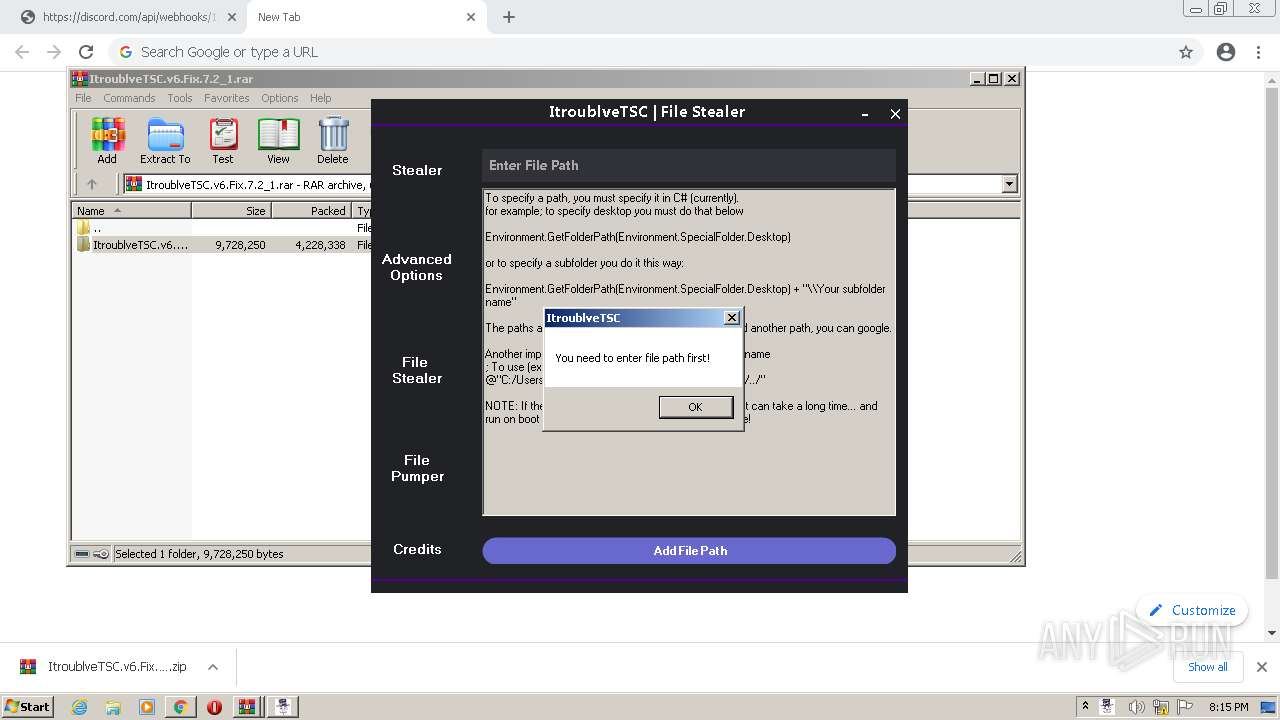
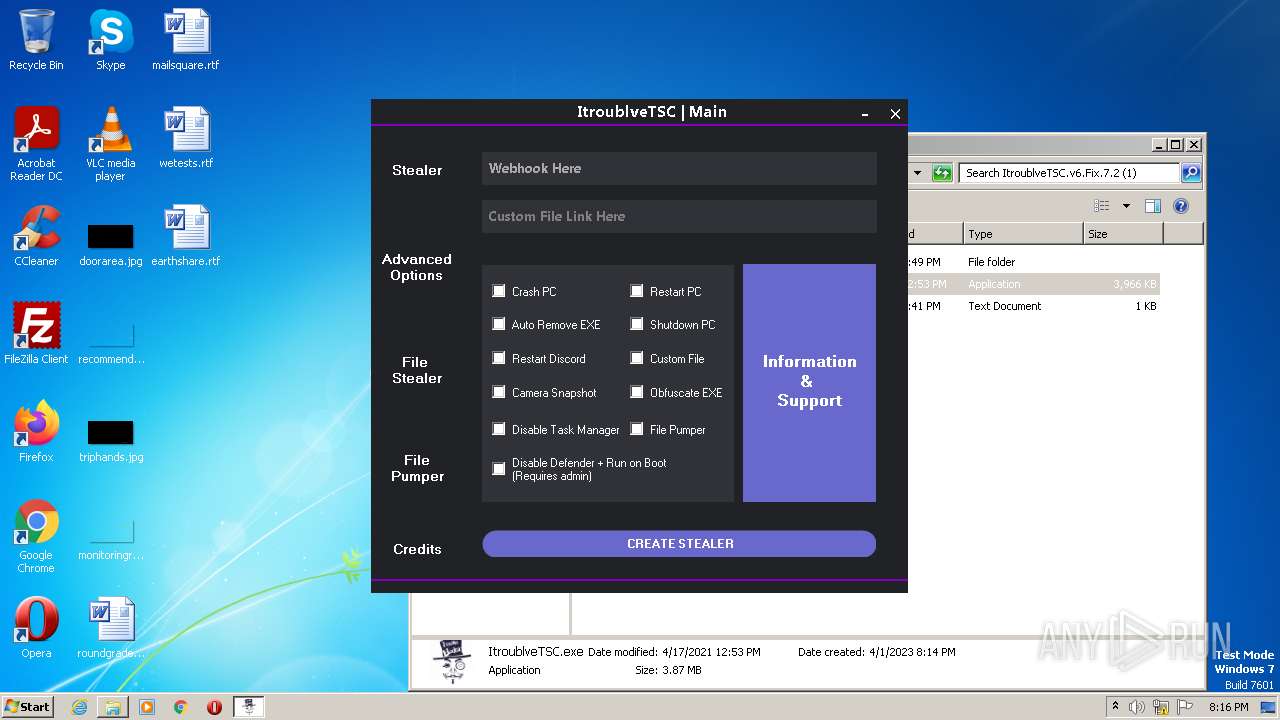
Actions looks like stealing of personal data
- RtkBtManServ.exe (PID: 1640)
- winhlp32.exe (PID: 1940)
- snuvcdsm.exe (PID: 600)
- splwow64.exe (PID: 3096)
- xwizard.exe (PID: 3704)
- RtkBtManServ.exe (PID: 1992)
- snuvcdsm.exe (PID: 2864)
- splwow64.exe (PID: 1412)
- winhlp32.exe (PID: 1180)
- xwizard.exe (PID: 3768)
- RtkBtManServ.exe (PID: 3032)
- snuvcdsm.exe (PID: 3768)
- winhlp32.exe (PID: 2384)
- splwow64.exe (PID: 2772)
- xwizard.exe (PID: 2348)
Steals credentials from Web Browsers
- snuvcdsm.exe (PID: 600)
- hh.exe (PID: 2096)
- xwizard.exe (PID: 3704)
- snuvcdsm.exe (PID: 2864)
- hh.exe (PID: 3260)
- xwizard.exe (PID: 3768)
- snuvcdsm.exe (PID: 3768)
- hh.exe (PID: 3200)
- xwizard.exe (PID: 2348)
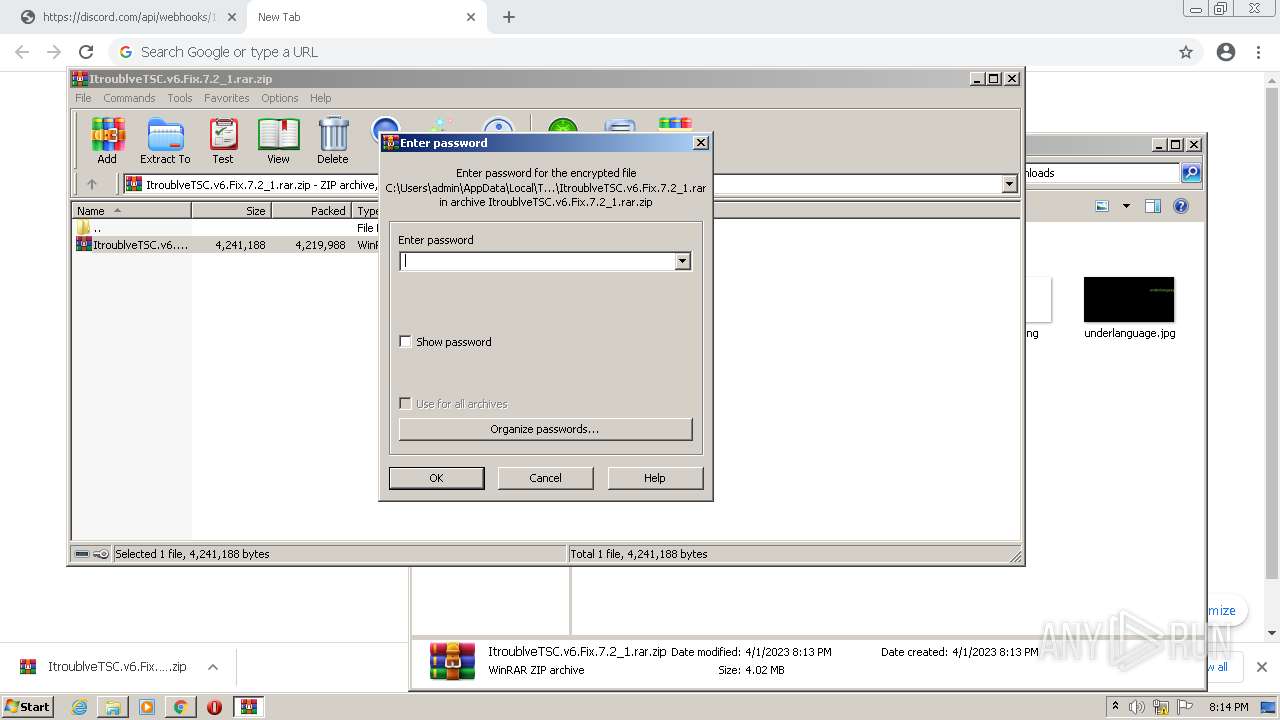
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 2808)
Reads the Internet Settings
- ItroublveTSC.exe (PID: 1748)
- wscript.exe (PID: 1472)
- fdsfds.exe (PID: 3488)
- RtkBtManServ.exe (PID: 1640)
- wscript.exe (PID: 2468)
- wscript.exe (PID: 3252)
- wscript.exe (PID: 2932)
- wscript.exe (PID: 2768)
- ItroublveTSC.exe (PID: 1436)
- wscript.exe (PID: 3320)
- fdsfsdfsd.exe (PID: 2428)
- CLI.exe (PID: 1392)
- RtkBtManServ.exe (PID: 1992)
- wscript.exe (PID: 1700)
- wscript.exe (PID: 2752)
- wscript.exe (PID: 1936)
- wscript.exe (PID: 1164)
- fdsfsdfsd.exe (PID: 116)
- fdsfsdfsd.exe (PID: 2148)
- wscript.exe (PID: 308)
- wscript.exe (PID: 296)
- RtkBtManServ.exe (PID: 3032)
- wscript.exe (PID: 852)
- wscript.exe (PID: 2576)
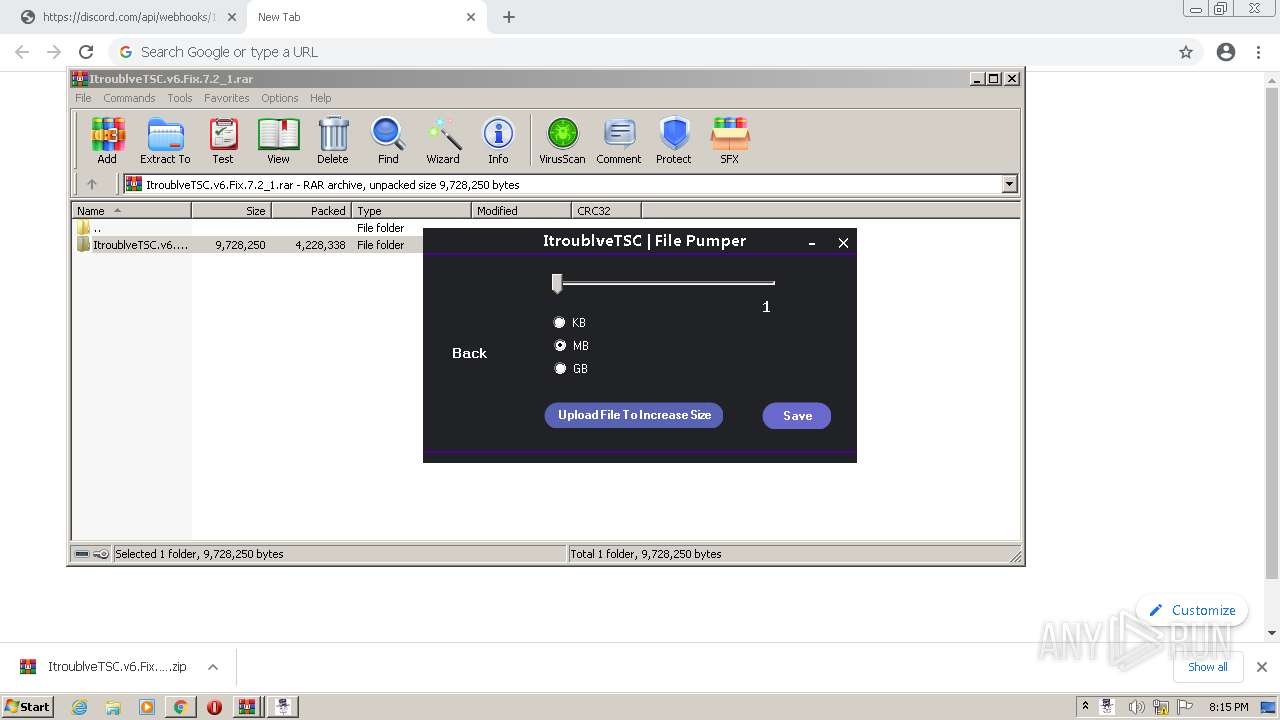
Executable content was dropped or overwritten
- ItroublveTSC.exe (PID: 1748)
- csc.exe (PID: 3920)
- MSBuild.exe (PID: 2984)
- cmd.exe (PID: 2956)
- RtkBtManServ.exe (PID: 1640)
- fdsfds.exe (PID: 3488)
- ItroublveTSC.exe (PID: 1436)
- csc.exe (PID: 3552)
- MSBuild.exe (PID: 3672)
- cmd.exe (PID: 1796)
- fdsfsdfsd.exe (PID: 2428)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 2148)
- RtkBtManServ.exe (PID: 3032)
The process executes VB scripts
- ItroublveTSC.exe (PID: 1748)
- ItroublveTSC.exe (PID: 1436)
- RtkBtManServ.exe (PID: 1640)
- RtkBtManServ.exe (PID: 1992)
- RtkBtManServ.exe (PID: 3032)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1472)
- fdsfds.exe (PID: 3488)
- wscript.exe (PID: 2468)
- wscript.exe (PID: 3252)
- wscript.exe (PID: 2932)
- wscript.exe (PID: 2768)
- RtkBtManServ.exe (PID: 1640)
- wscript.exe (PID: 3320)
- wscript.exe (PID: 1700)
- wscript.exe (PID: 2752)
- wscript.exe (PID: 1936)
- wscript.exe (PID: 1164)
- RtkBtManServ.exe (PID: 1992)
- wscript.exe (PID: 308)
- wscript.exe (PID: 296)
- wscript.exe (PID: 852)
- wscript.exe (PID: 2576)
- RtkBtManServ.exe (PID: 3032)
Executing commands from a ".bat" file
- wscript.exe (PID: 1472)
- wscript.exe (PID: 3252)
- wscript.exe (PID: 2932)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 3320)
- wscript.exe (PID: 2468)
- wscript.exe (PID: 1700)
- wscript.exe (PID: 2752)
- wscript.exe (PID: 1936)
- wscript.exe (PID: 1164)
- wscript.exe (PID: 308)
- wscript.exe (PID: 296)
- wscript.exe (PID: 852)
- wscript.exe (PID: 2576)
Reads browser cookies
- RtkBtManServ.exe (PID: 1640)
- RtkBtManServ.exe (PID: 1992)
- RtkBtManServ.exe (PID: 3032)
Reads settings of System Certificates
- RtkBtManServ.exe (PID: 1640)
- RtkBtManServ.exe (PID: 1992)
- RtkBtManServ.exe (PID: 3032)
Loads DLL from Mozilla Firefox
- splwow64.exe (PID: 3096)
- splwow64.exe (PID: 1412)
- splwow64.exe (PID: 2772)
INFO
Application launched itself
- chrome.exe (PID: 2400)
Create files in a temporary directory
- chrome.exe (PID: 3228)
- chrome.exe (PID: 2400)
- MSBuild.exe (PID: 2984)
- csc.exe (PID: 3920)
- ItroublveTSC.exe (PID: 1748)
- cvtres.exe (PID: 2064)
- RtkBtManServ.exe (PID: 1640)
- fdsfds.exe (PID: 3488)
- snuvcdsm.exe (PID: 600)
- winhlp32.exe (PID: 1940)
- hh.exe (PID: 2096)
- xwizard.exe (PID: 3704)
- splwow64.exe (PID: 3096)
- csc.exe (PID: 3552)
- ItroublveTSC.exe (PID: 1436)
- cvtres.exe (PID: 1964)
- MSBuild.exe (PID: 3672)
- fdsfsdfsd.exe (PID: 2428)
- CLI.exe (PID: 1392)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 2244)
- fdsfsdfsd.exe (PID: 3764)
- fdsfsdfsd.exe (PID: 1616)
- snuvcdsm.exe (PID: 2864)
- winhlp32.exe (PID: 1180)
- splwow64.exe (PID: 1412)
- hh.exe (PID: 3260)
- xwizard.exe (PID: 3768)
- fdsfsdfsd.exe (PID: 2148)
- fdsfsdfsd.exe (PID: 116)
- snuvcdsm.exe (PID: 3768)
- winhlp32.exe (PID: 2384)
- RtkBtManServ.exe (PID: 3032)
- hh.exe (PID: 3200)
- splwow64.exe (PID: 2772)
- xwizard.exe (PID: 2348)
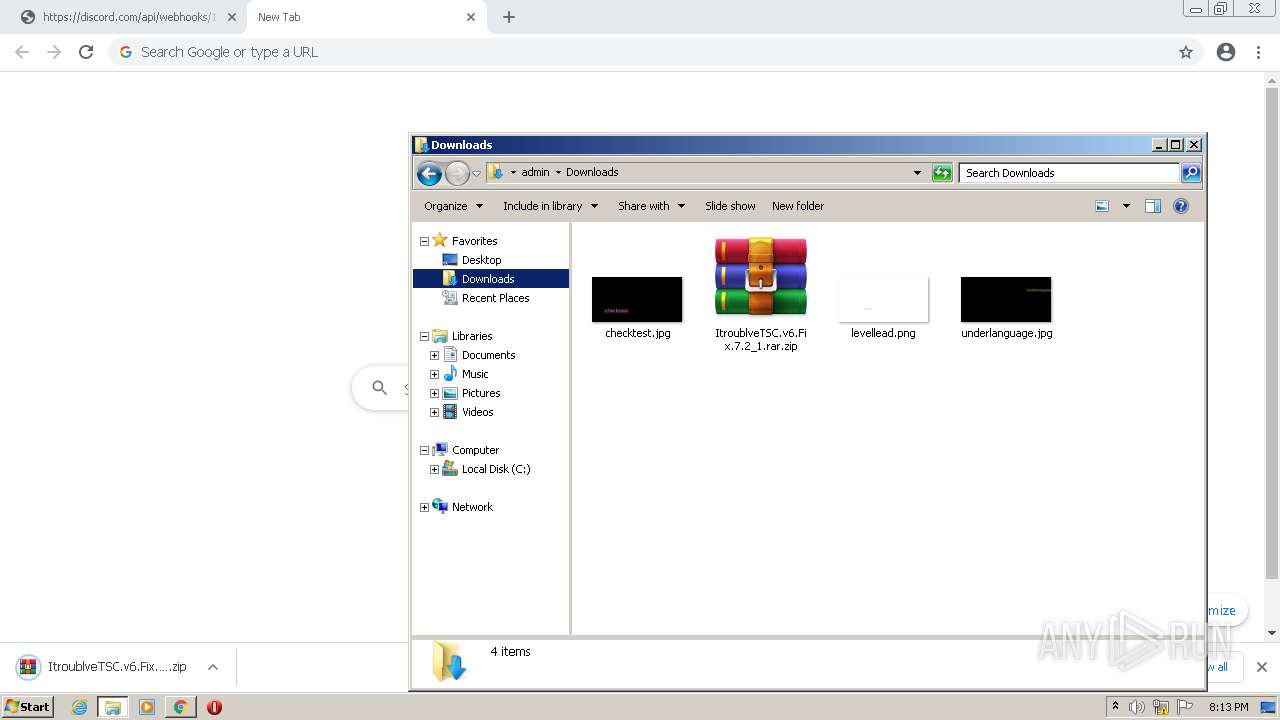
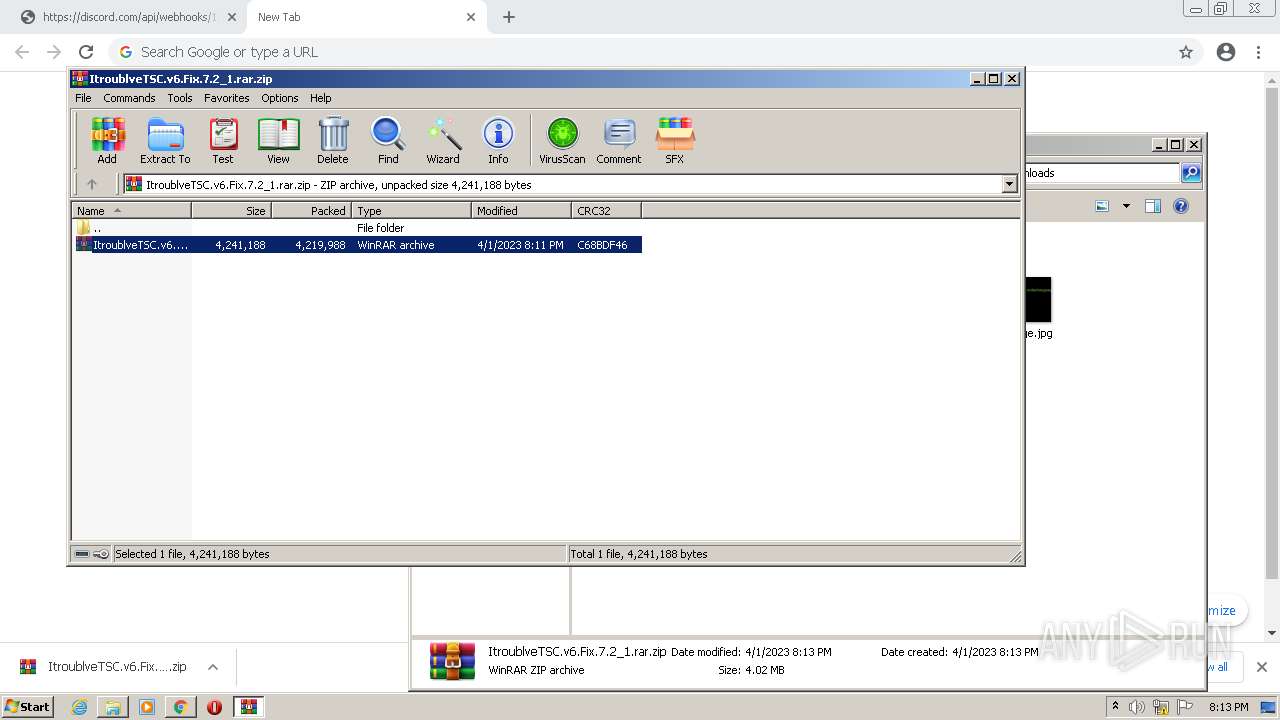
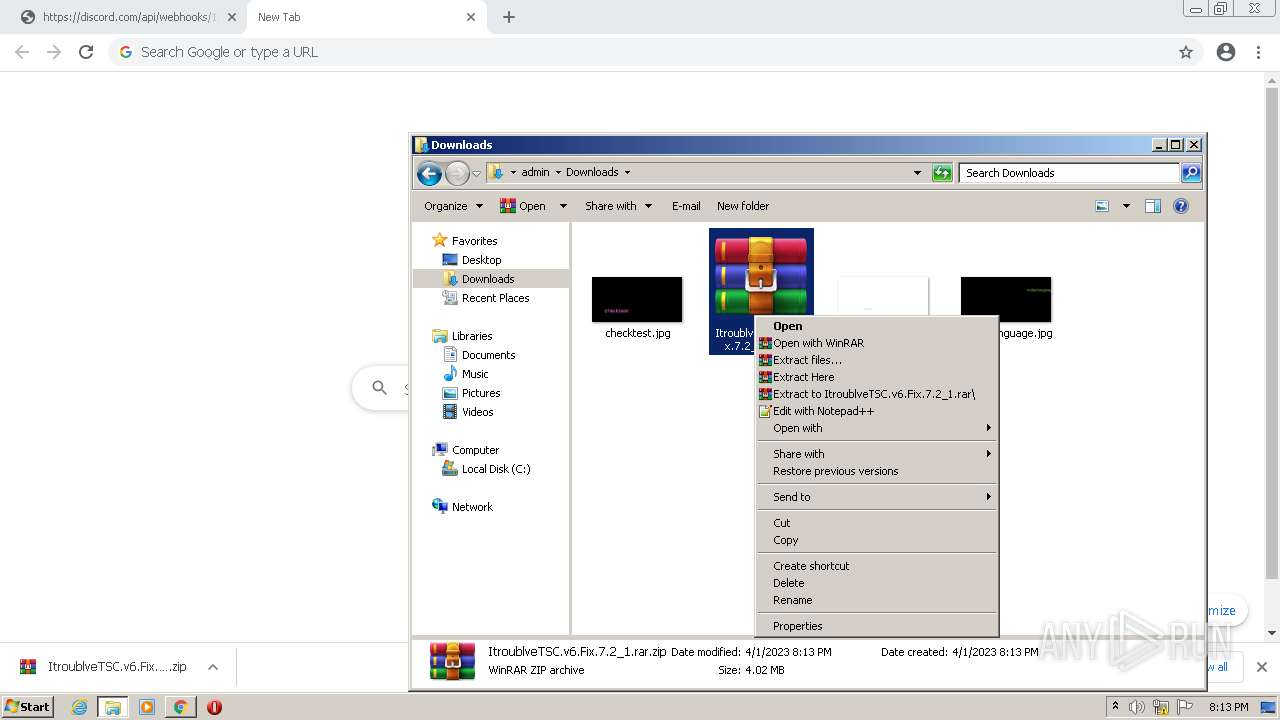
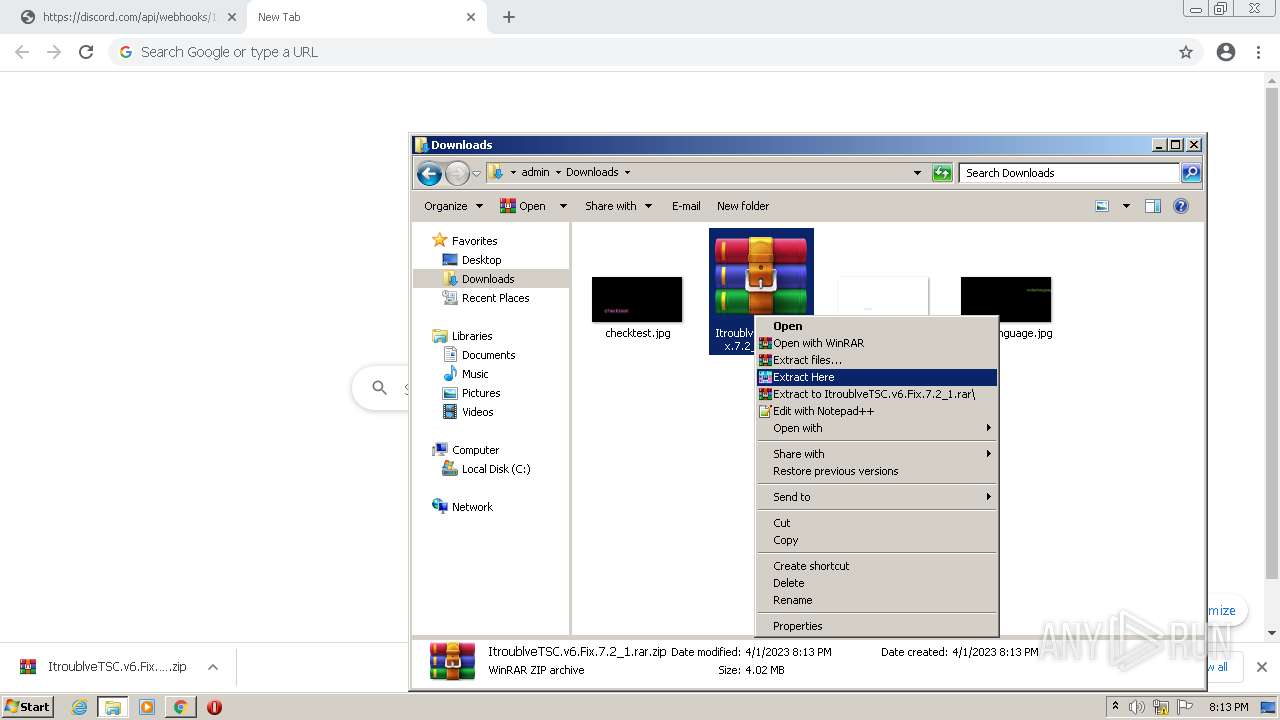
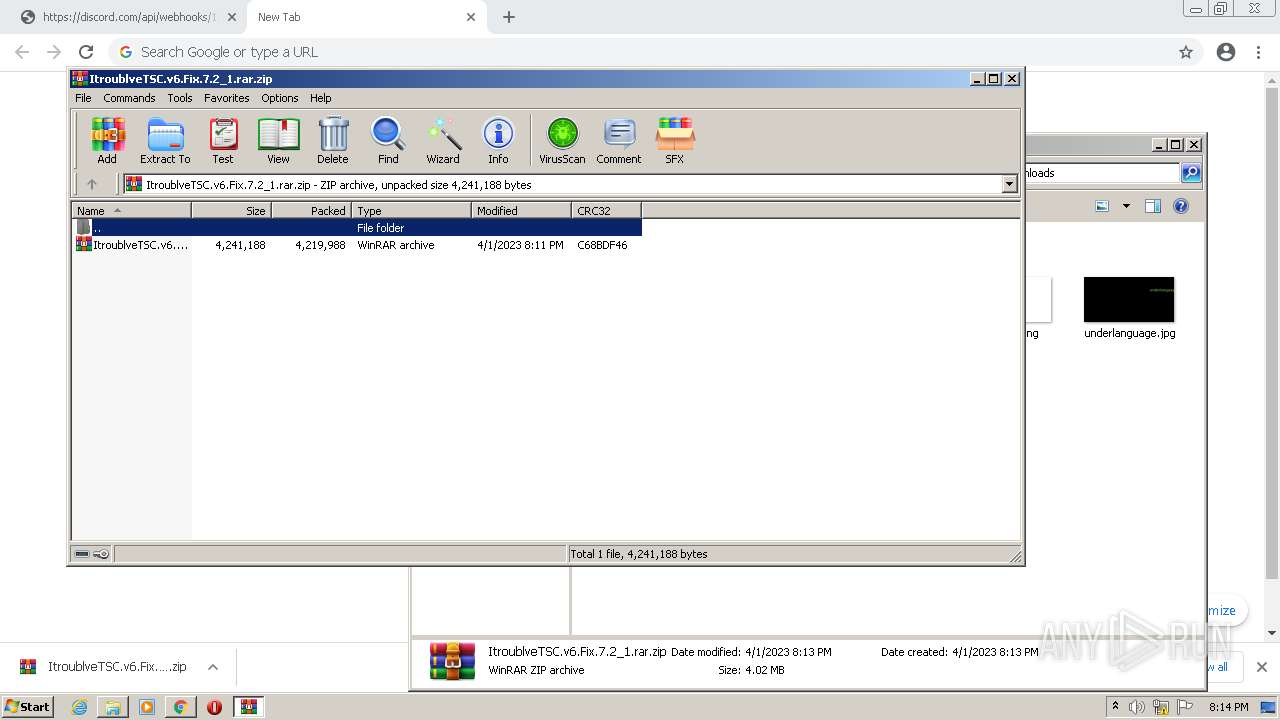
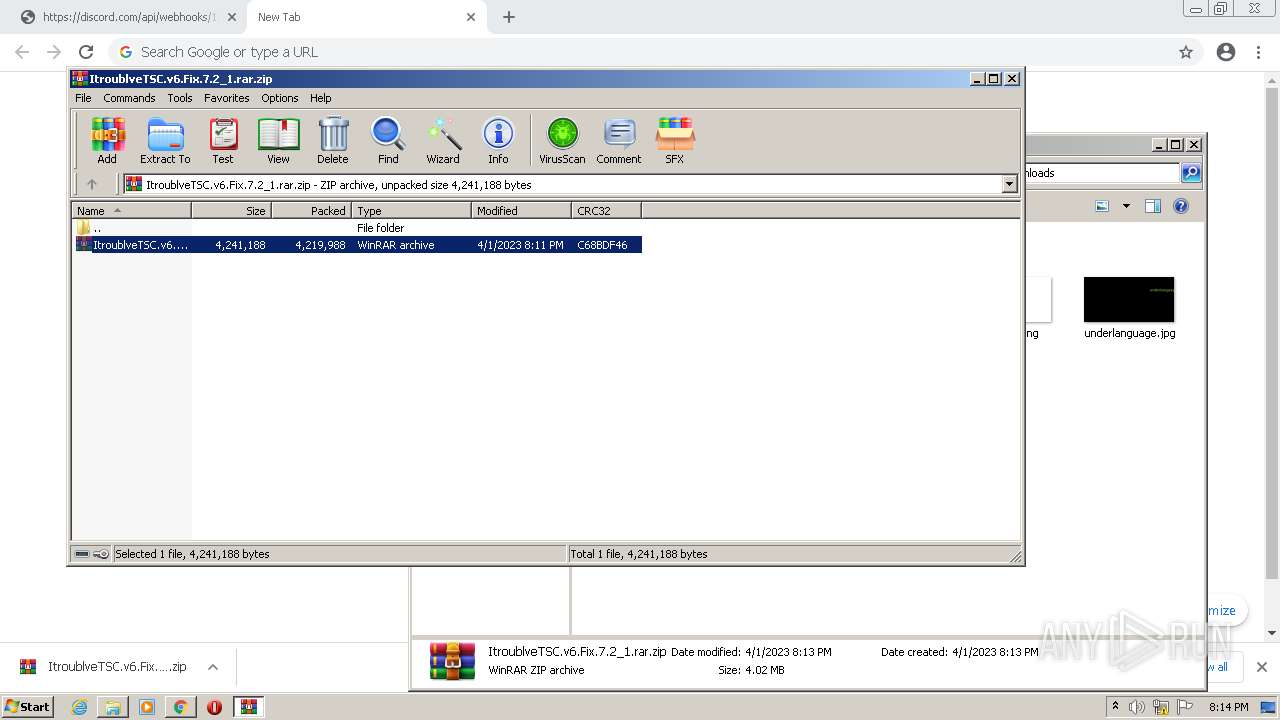
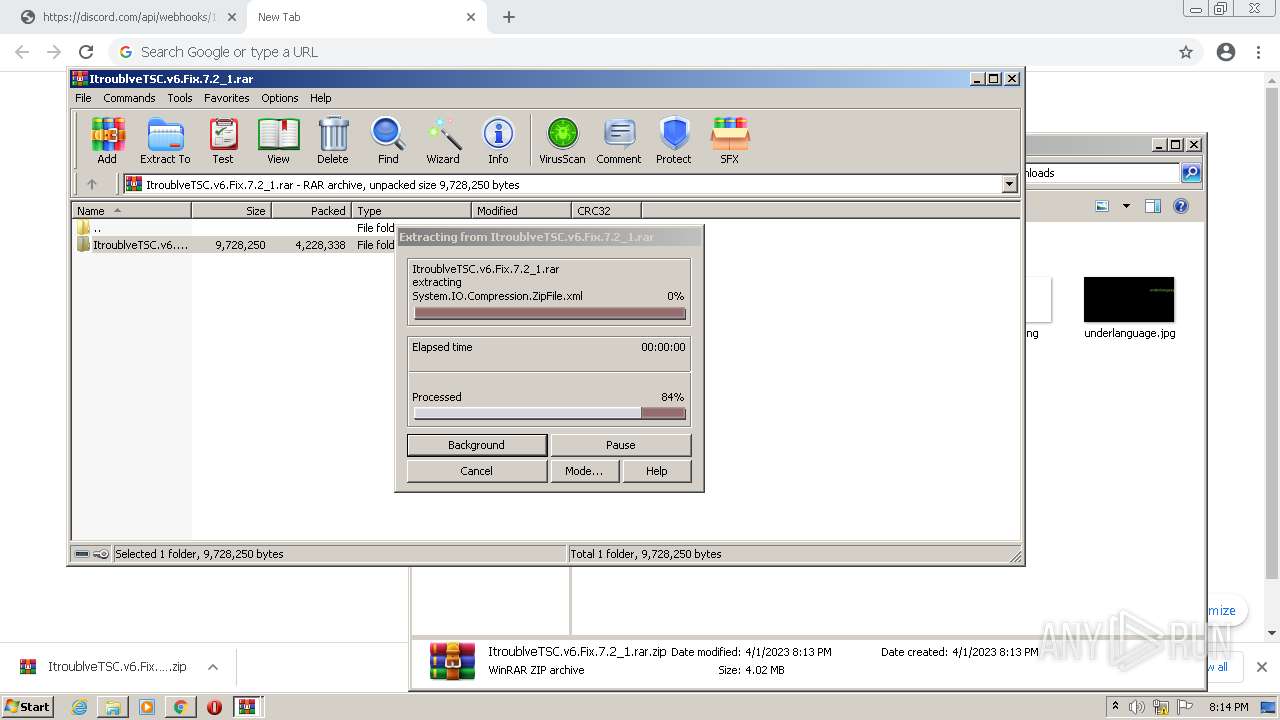
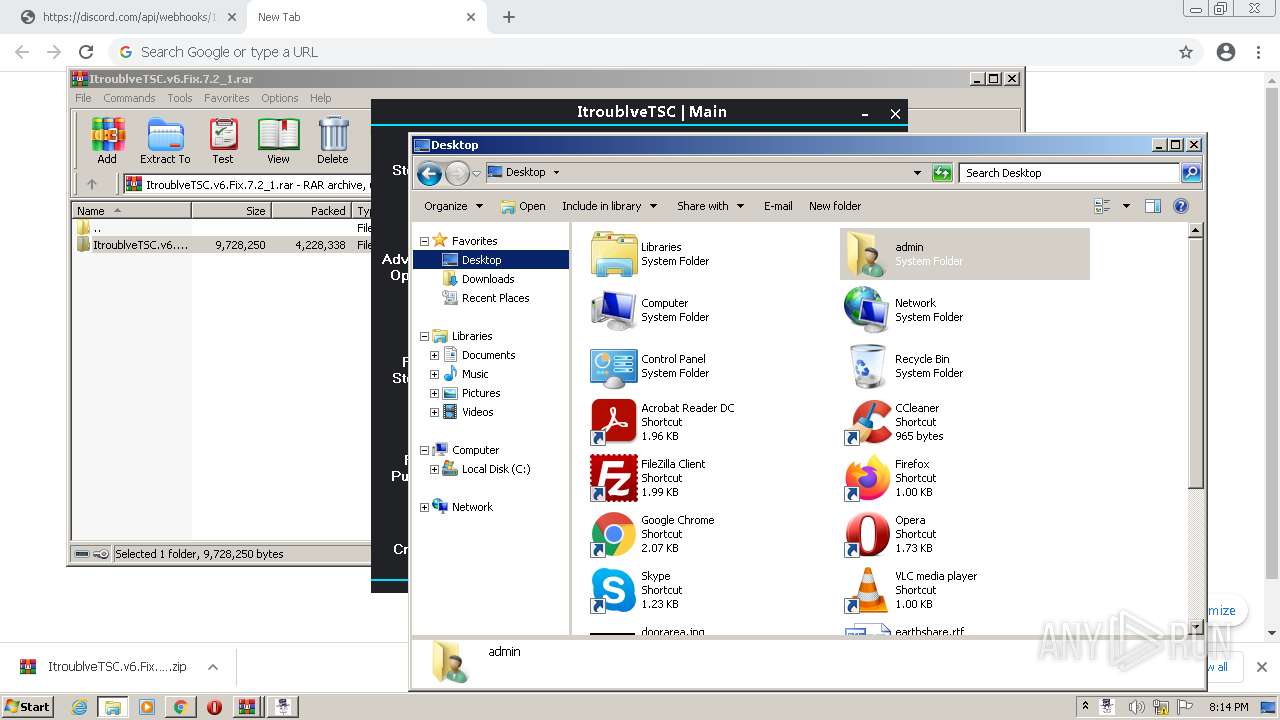
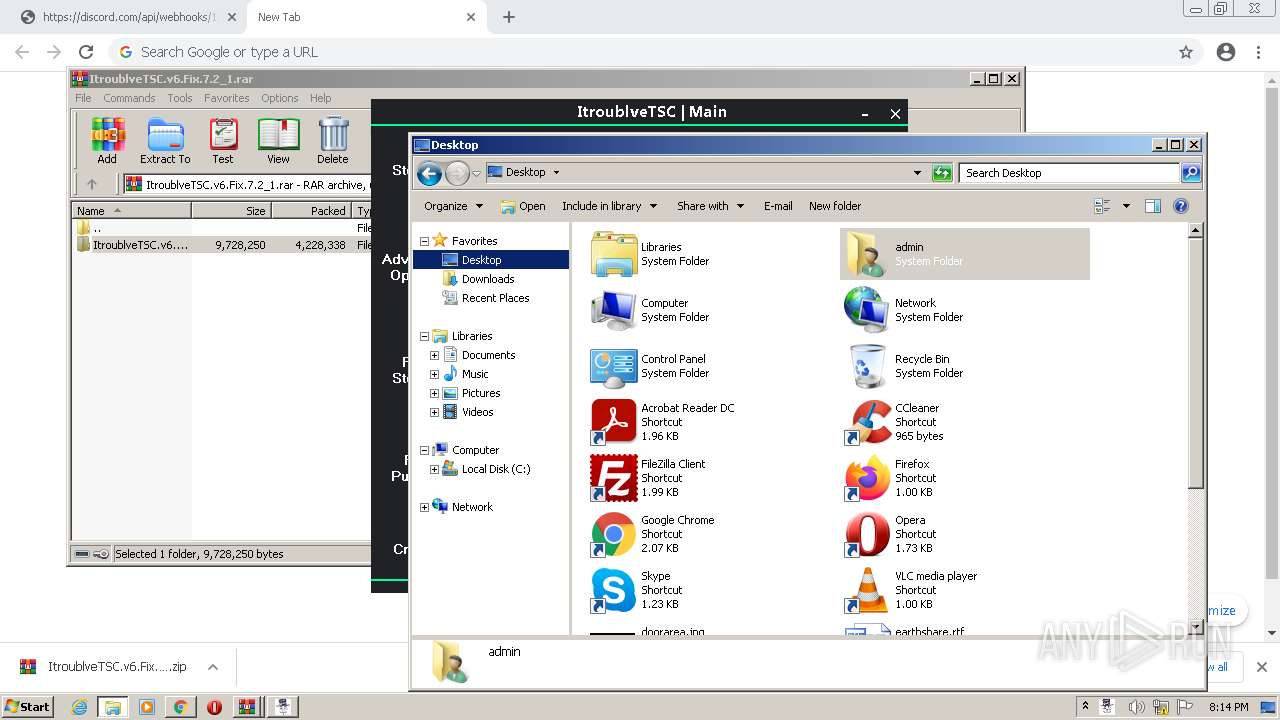
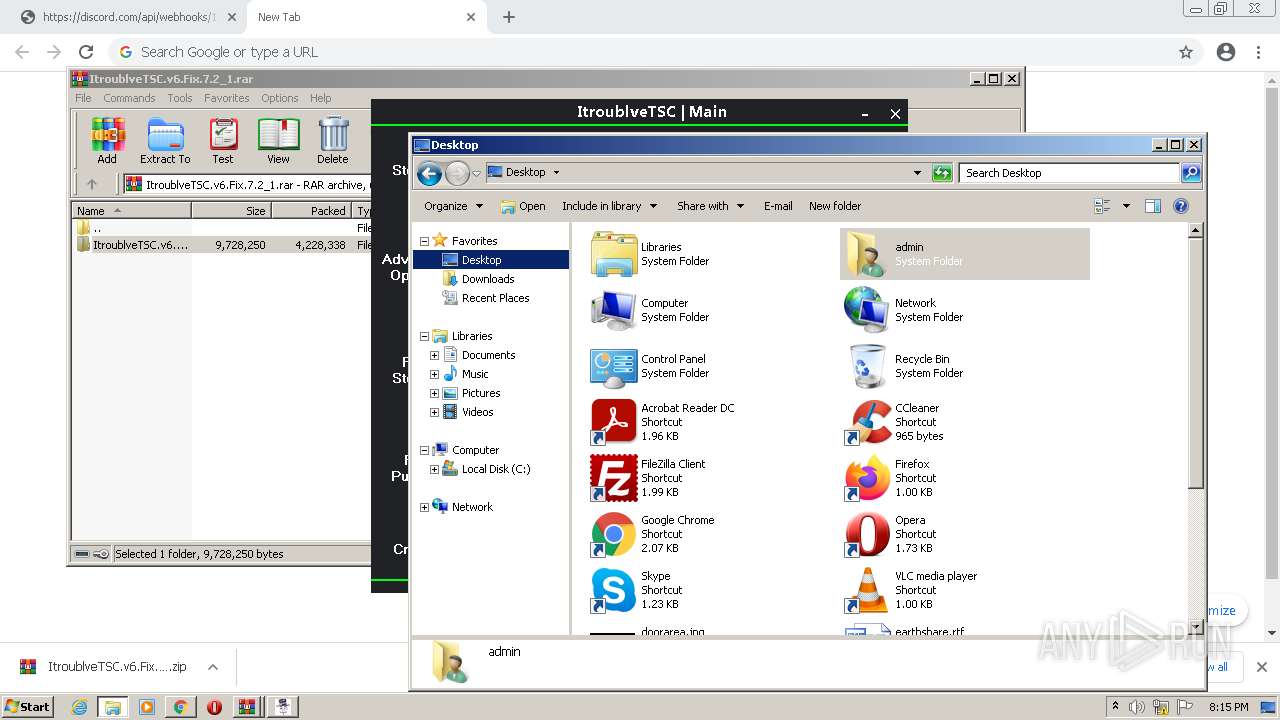
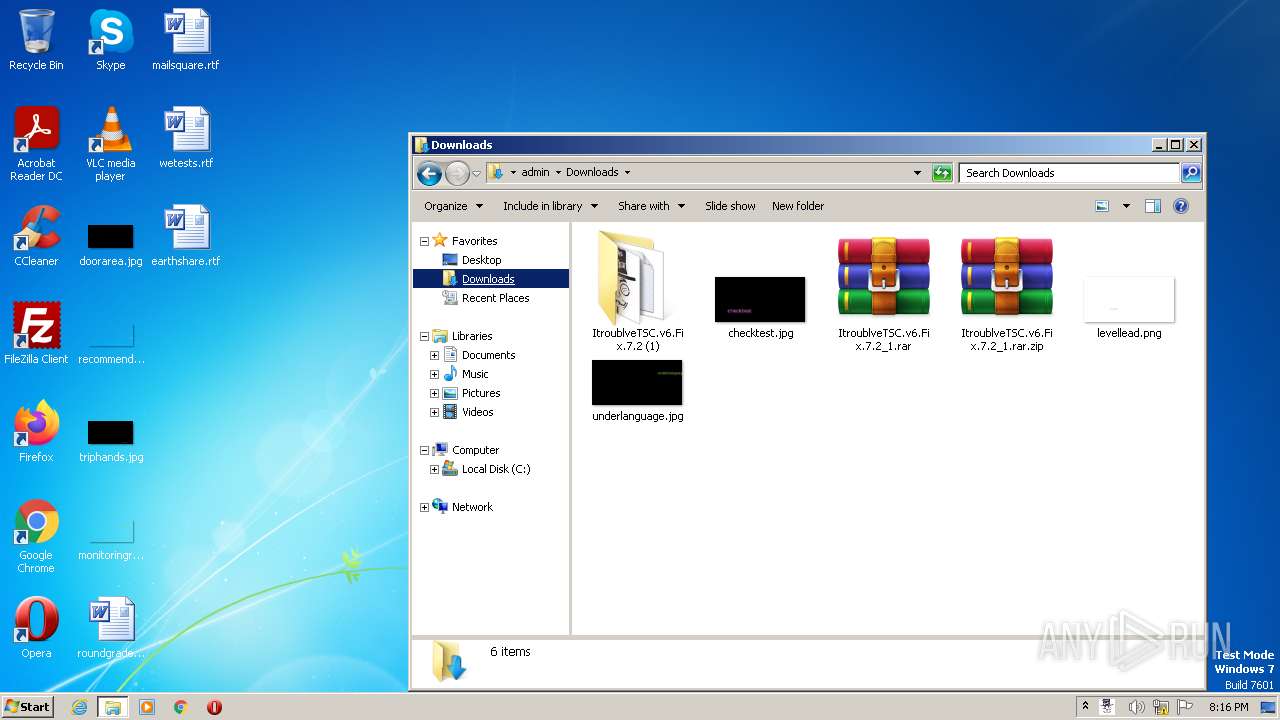
The process uses the downloaded file
- chrome.exe (PID: 1576)
- WinRAR.exe (PID: 3812)
- WinRAR.exe (PID: 3168)
- WinRAR.exe (PID: 2808)
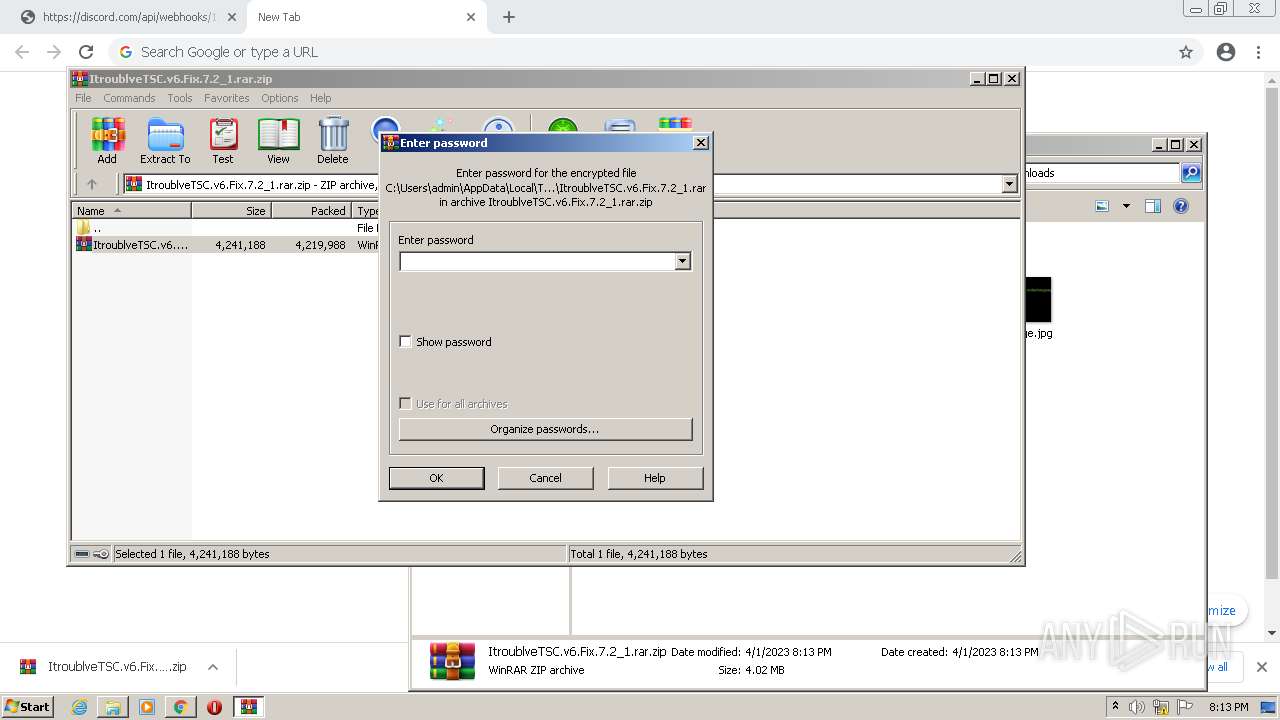
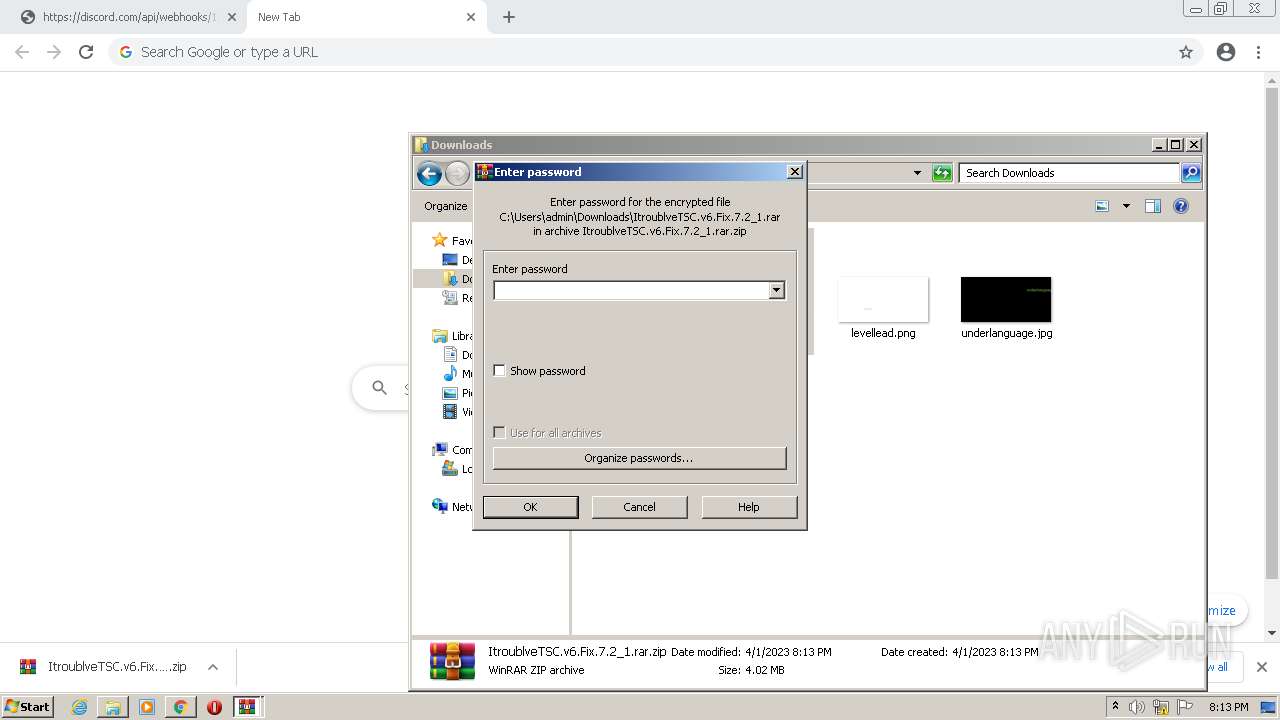
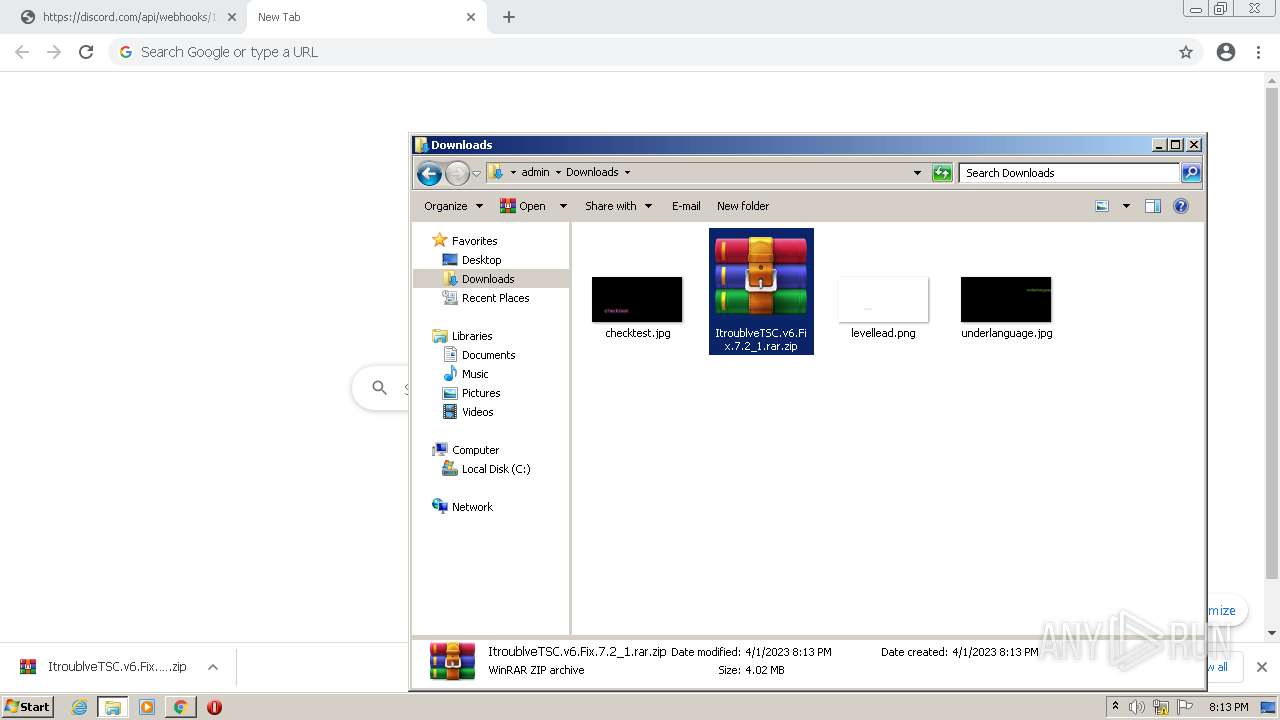
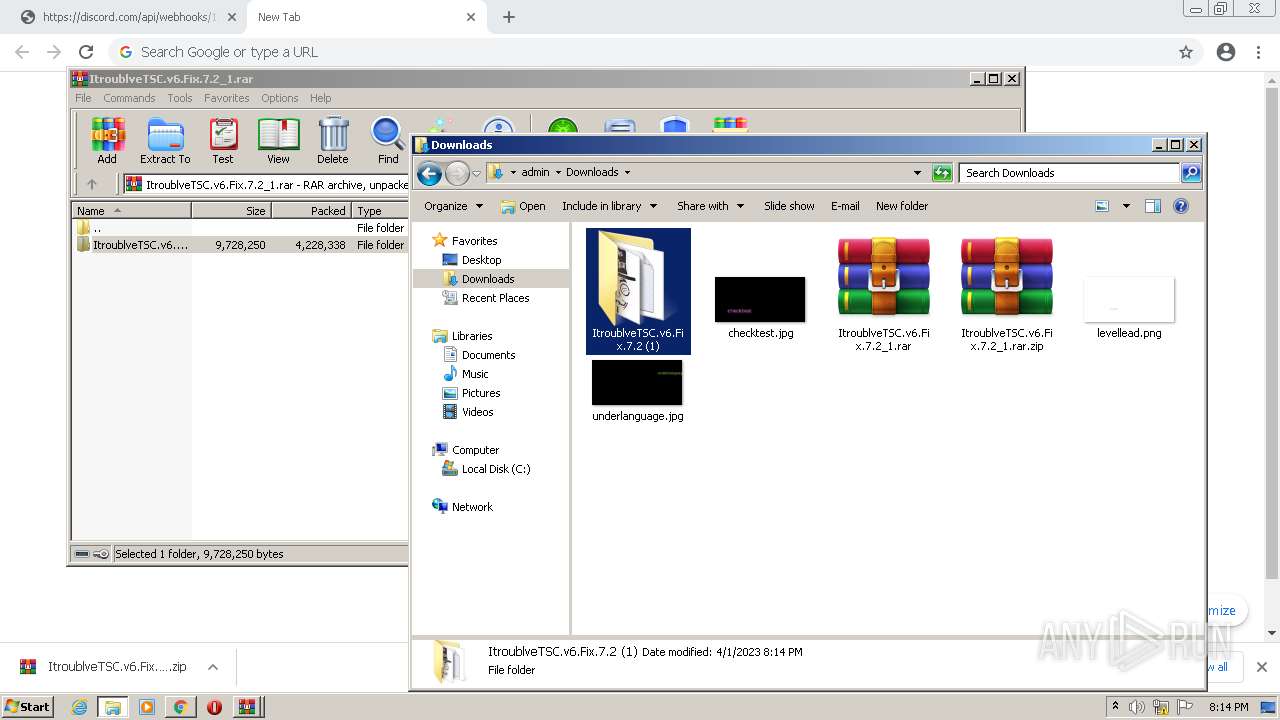
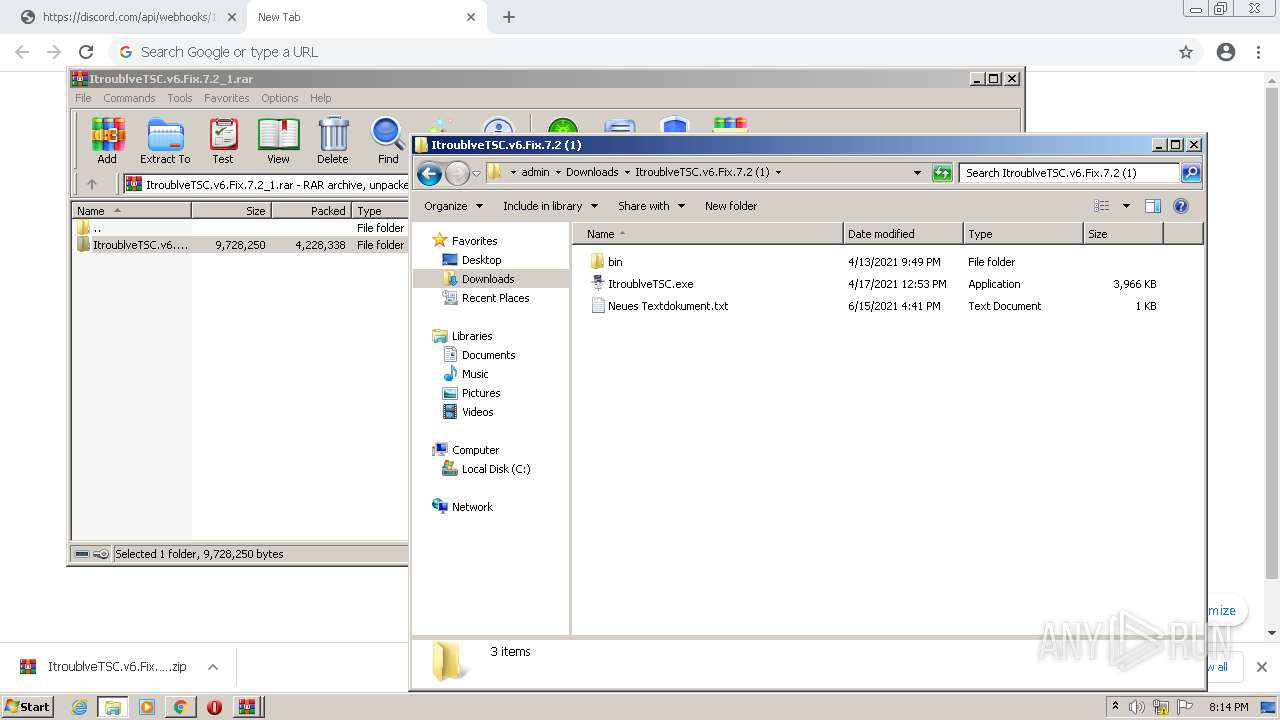
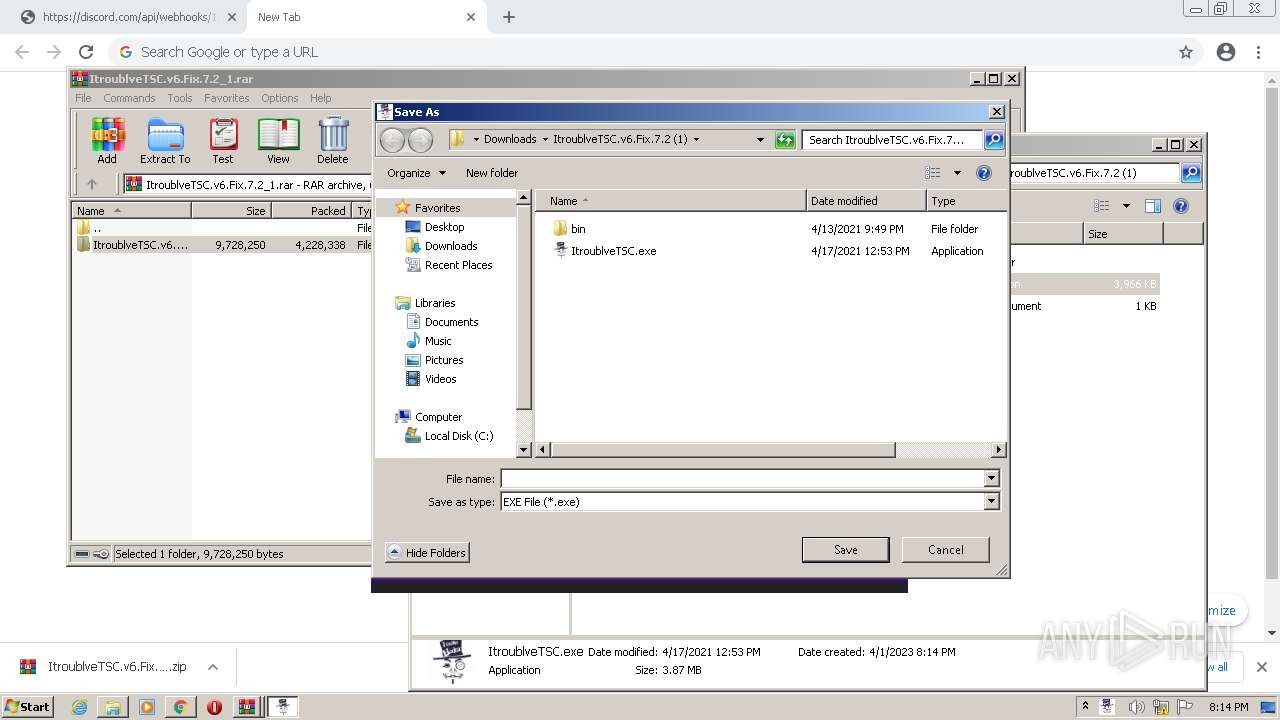
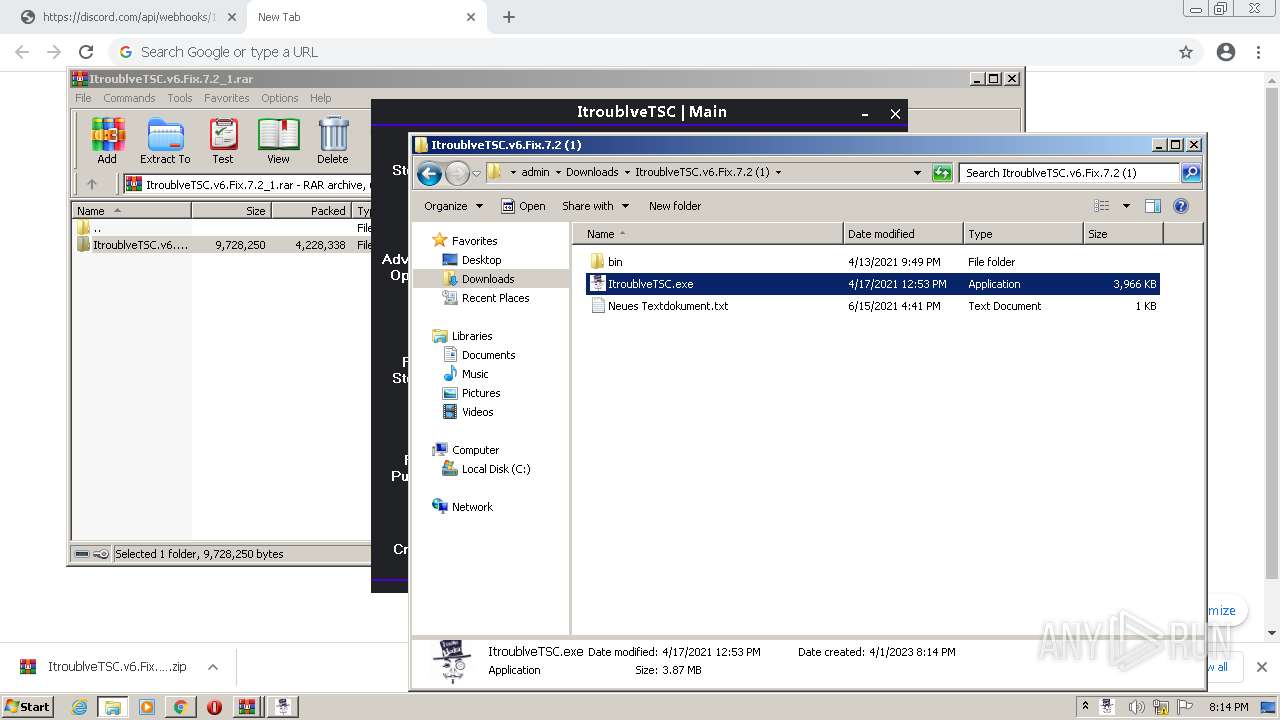
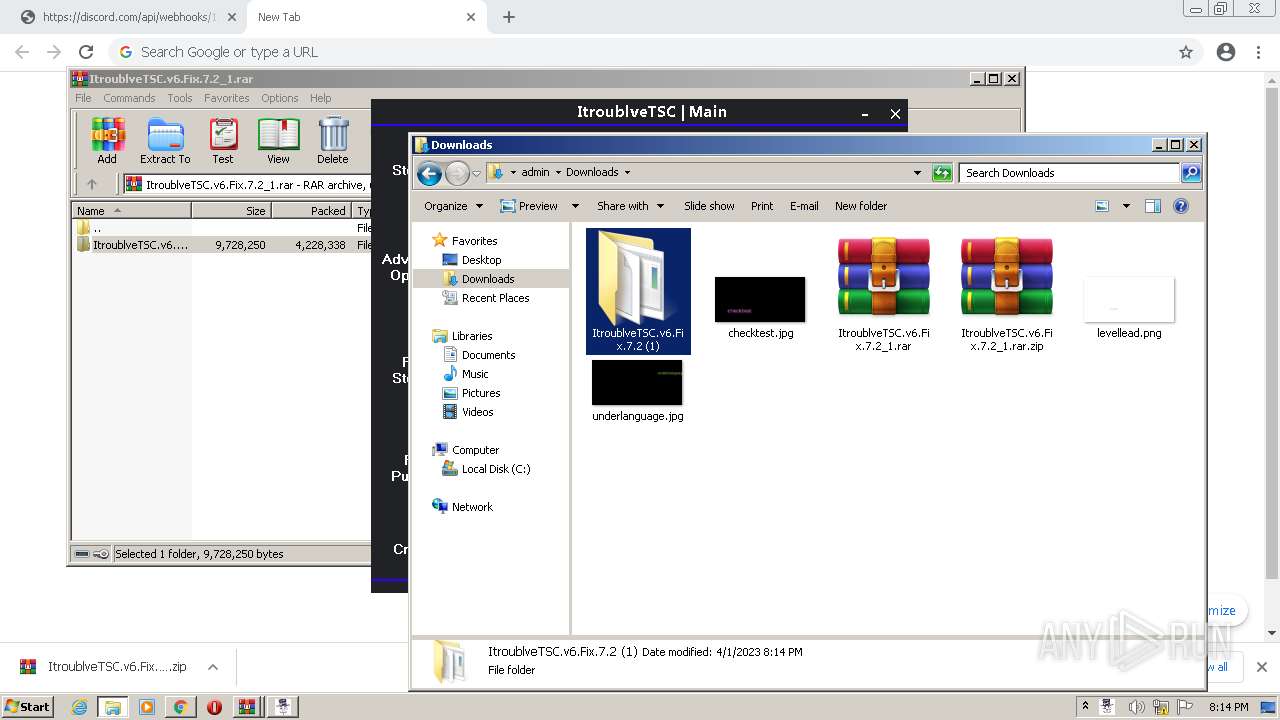
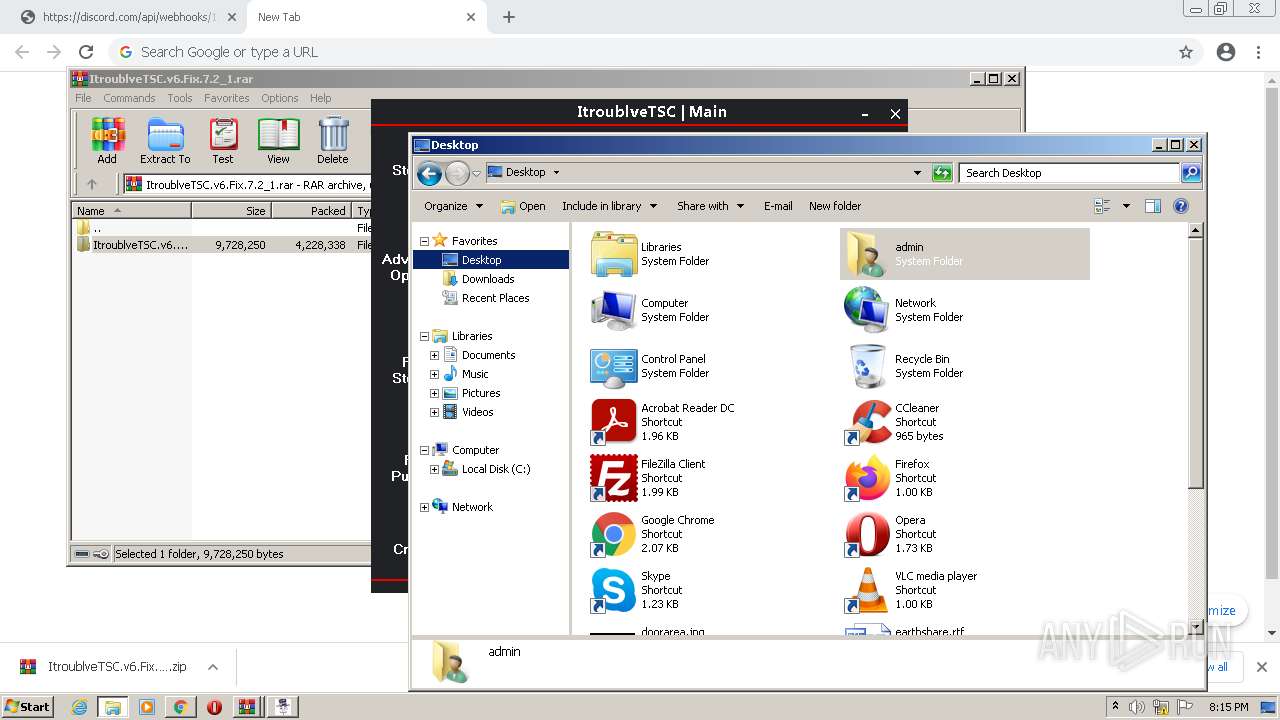
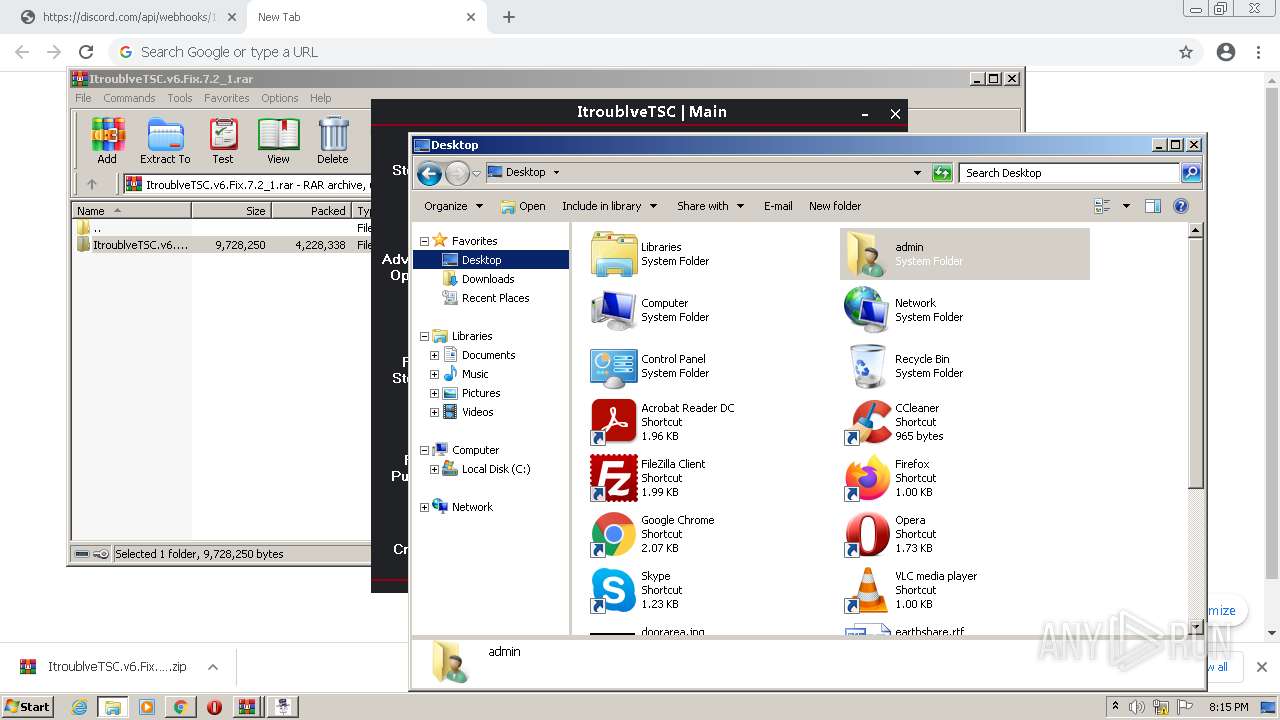
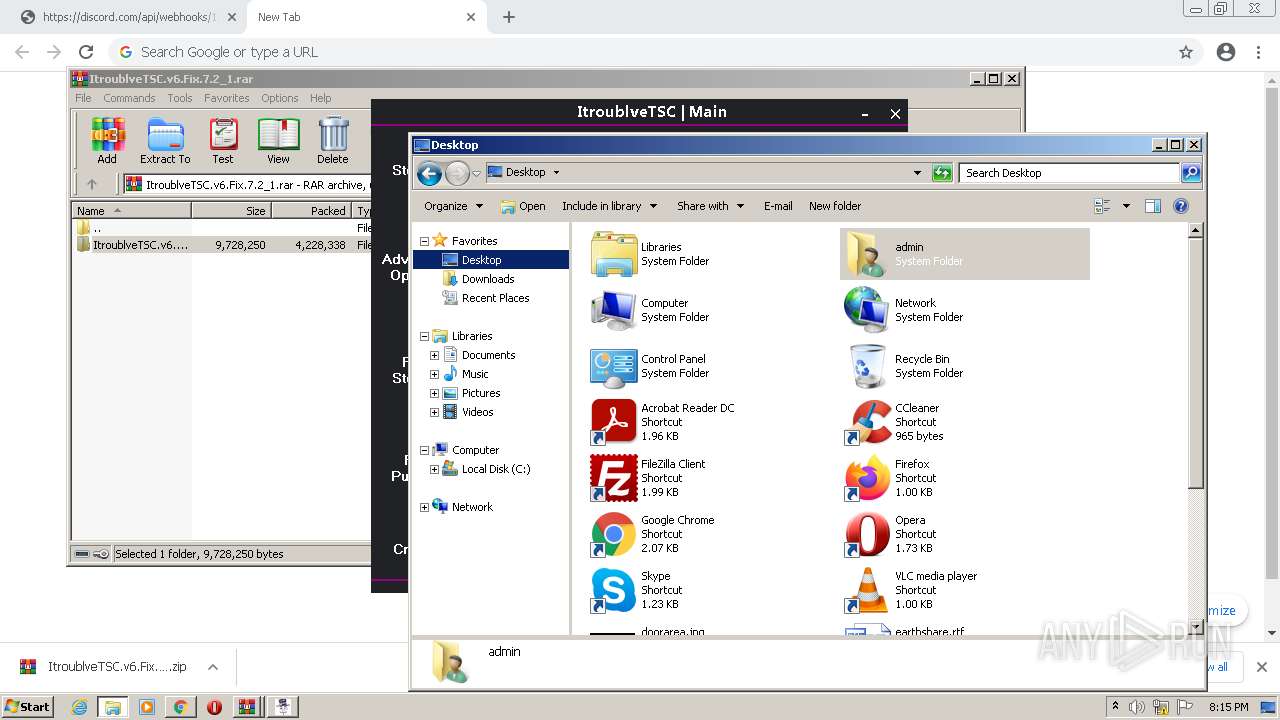
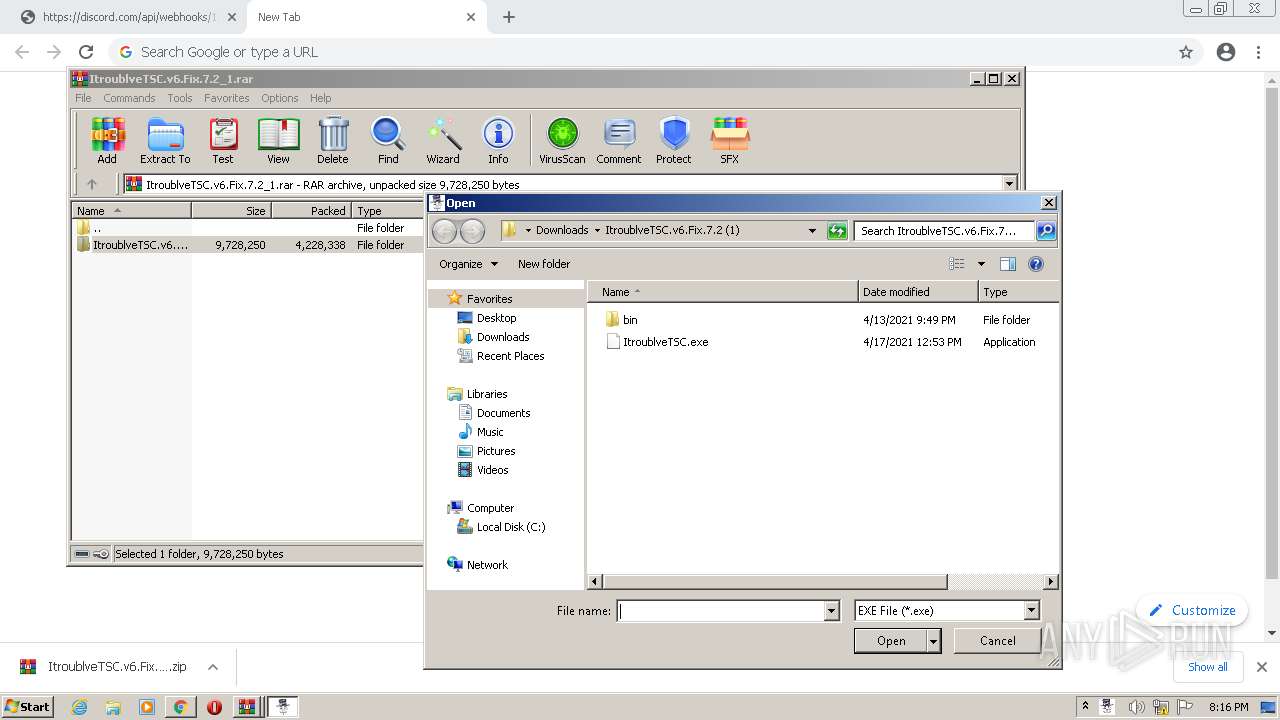
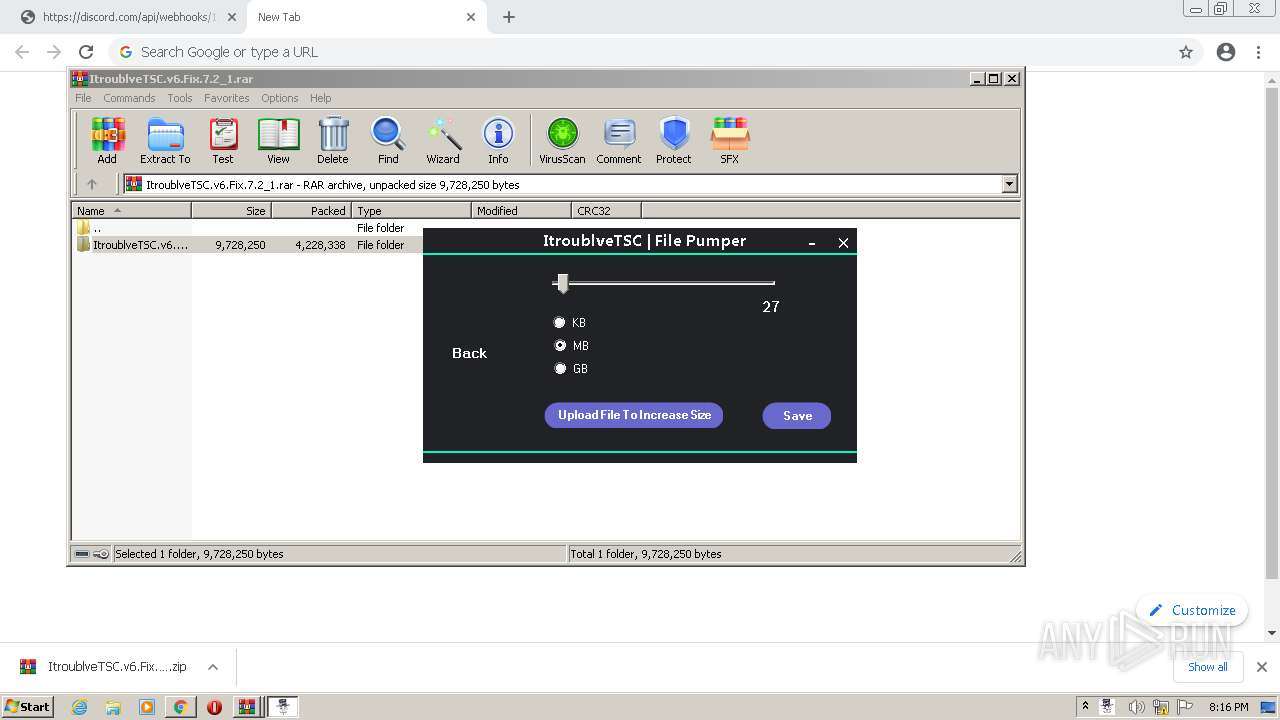
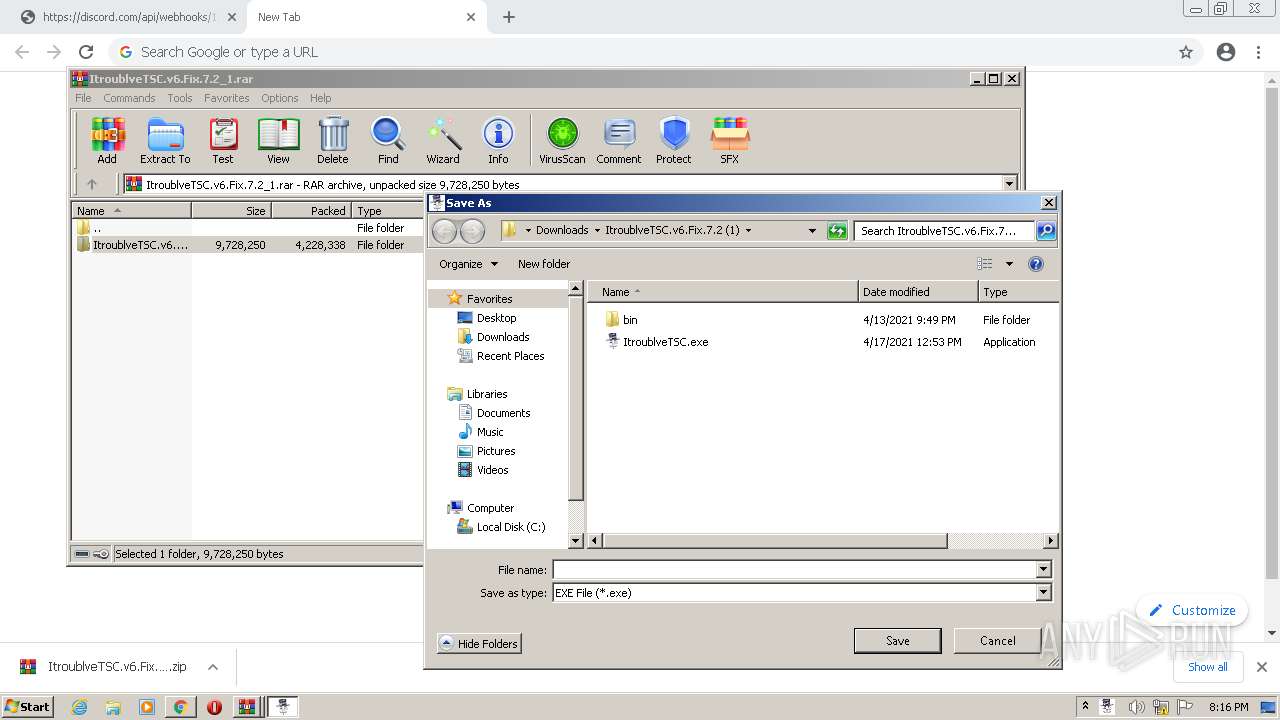
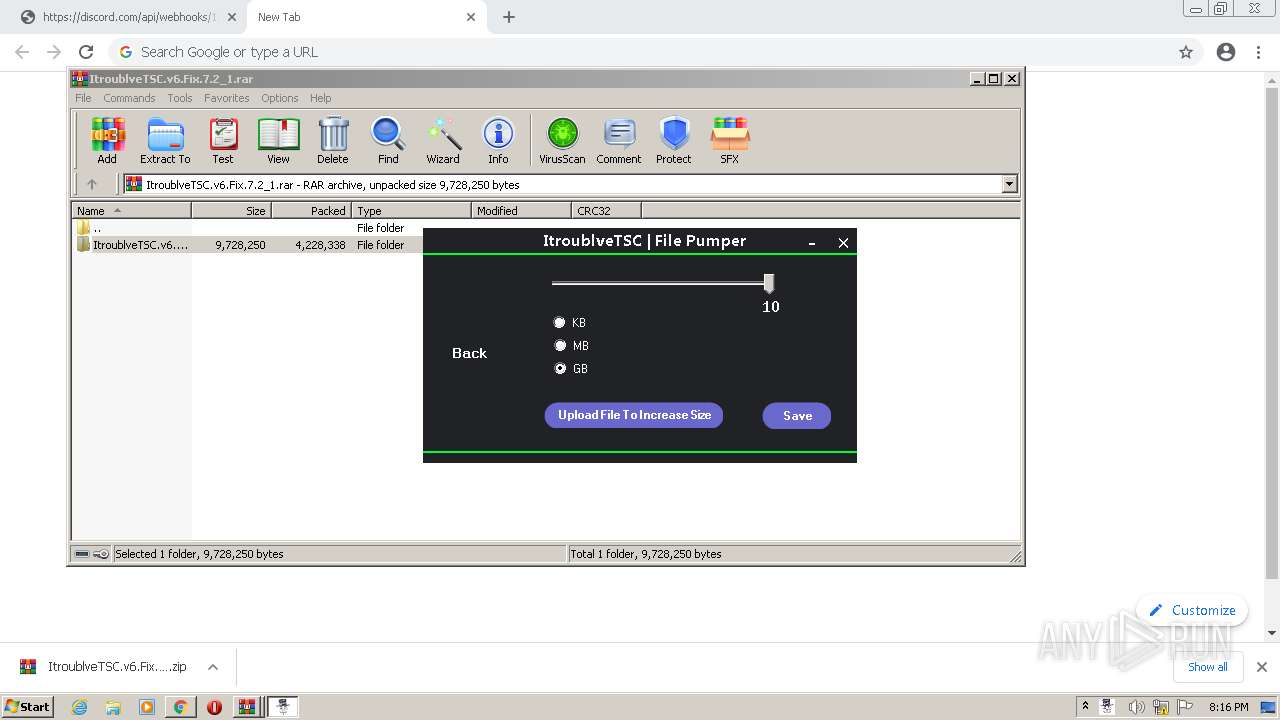
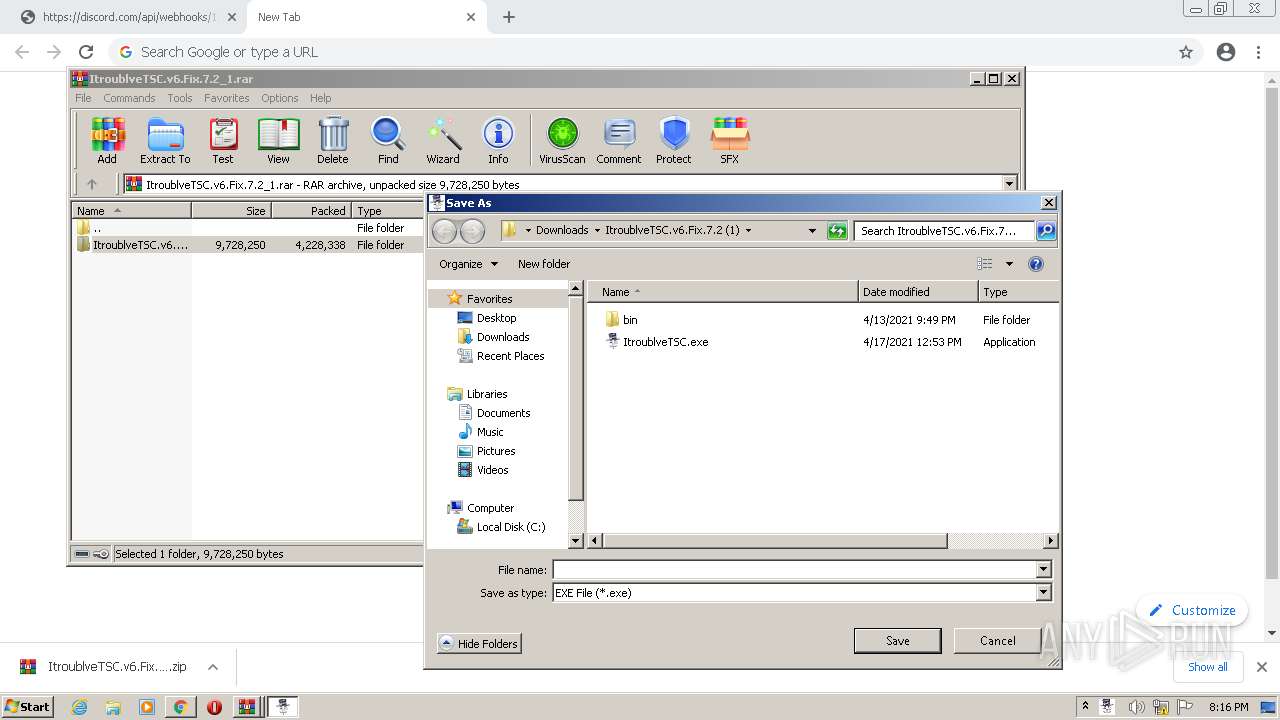
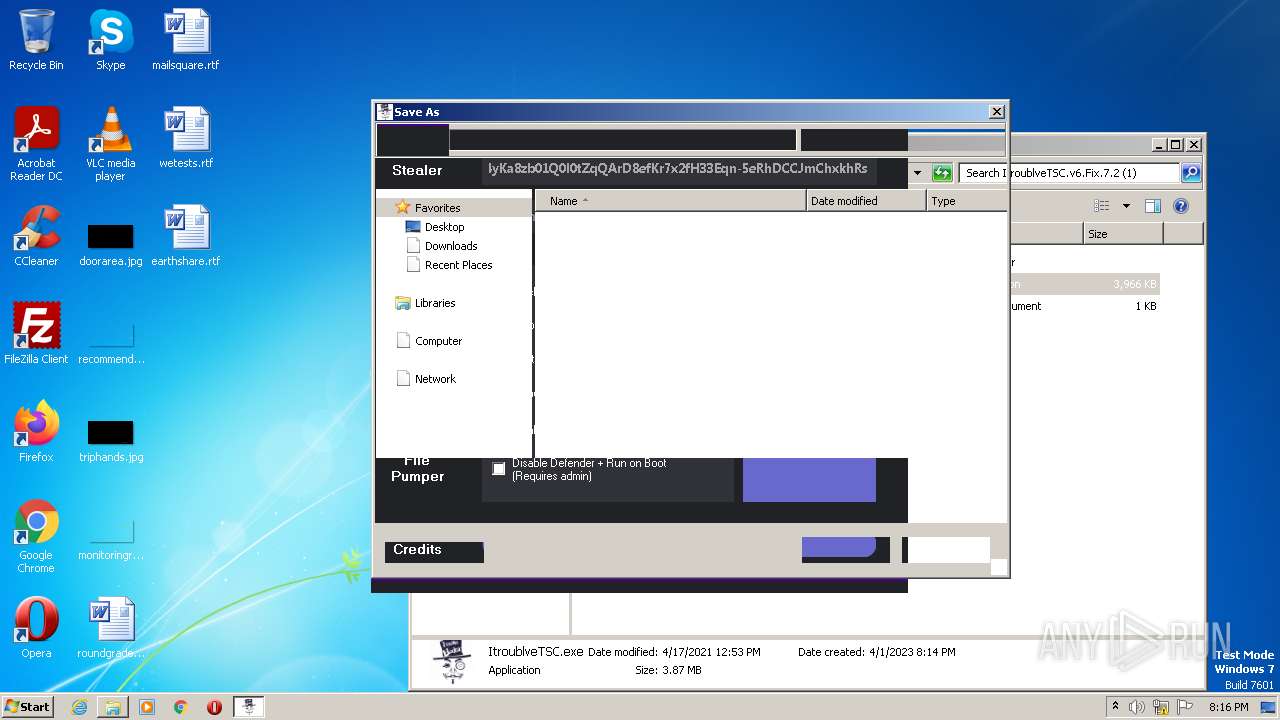
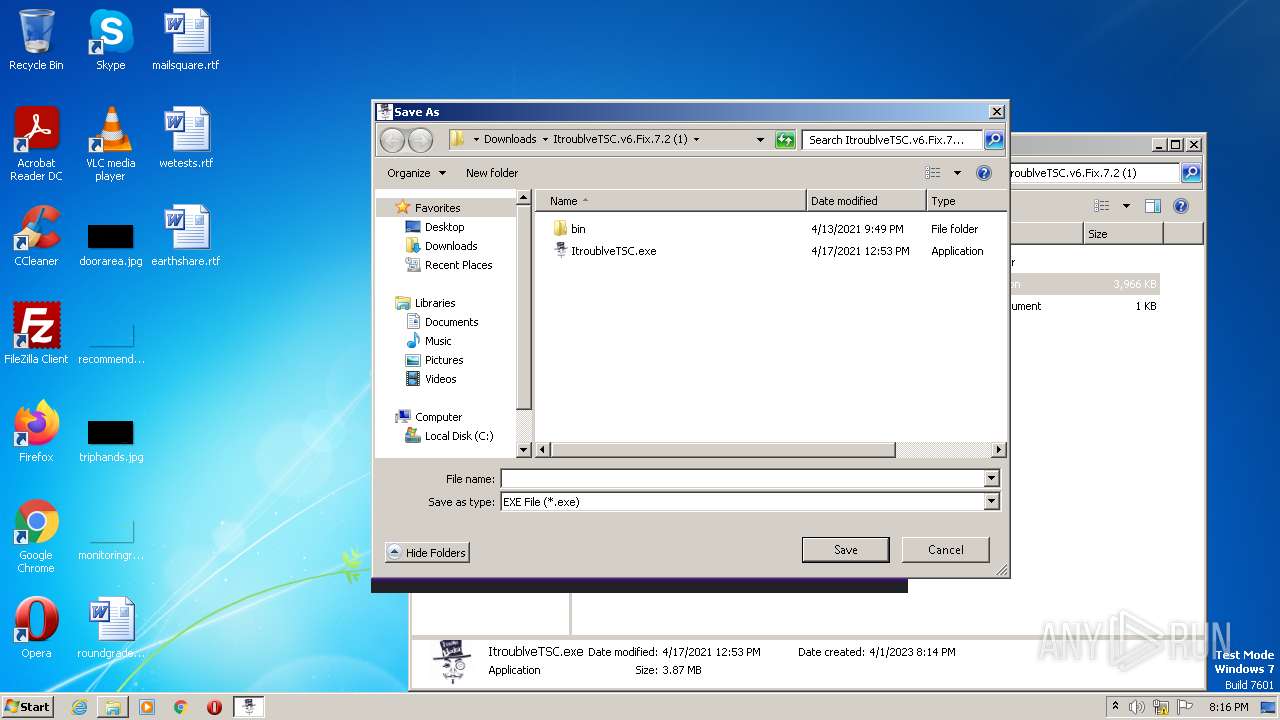
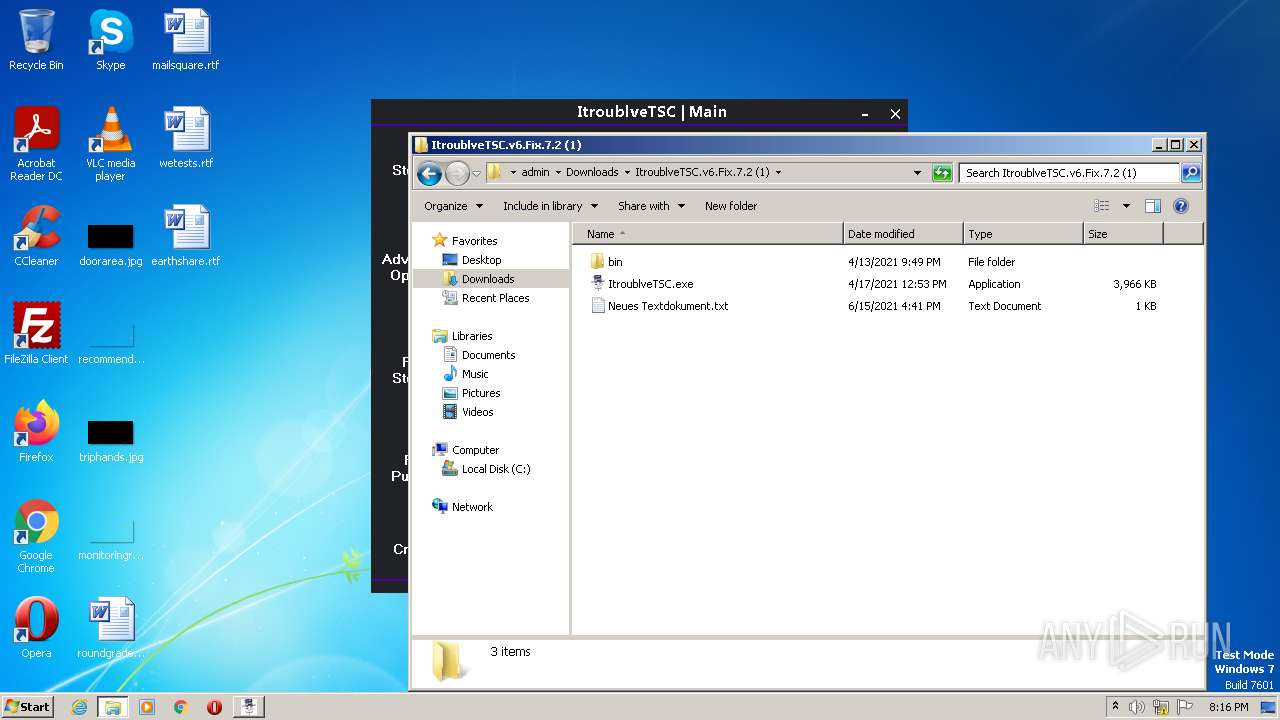
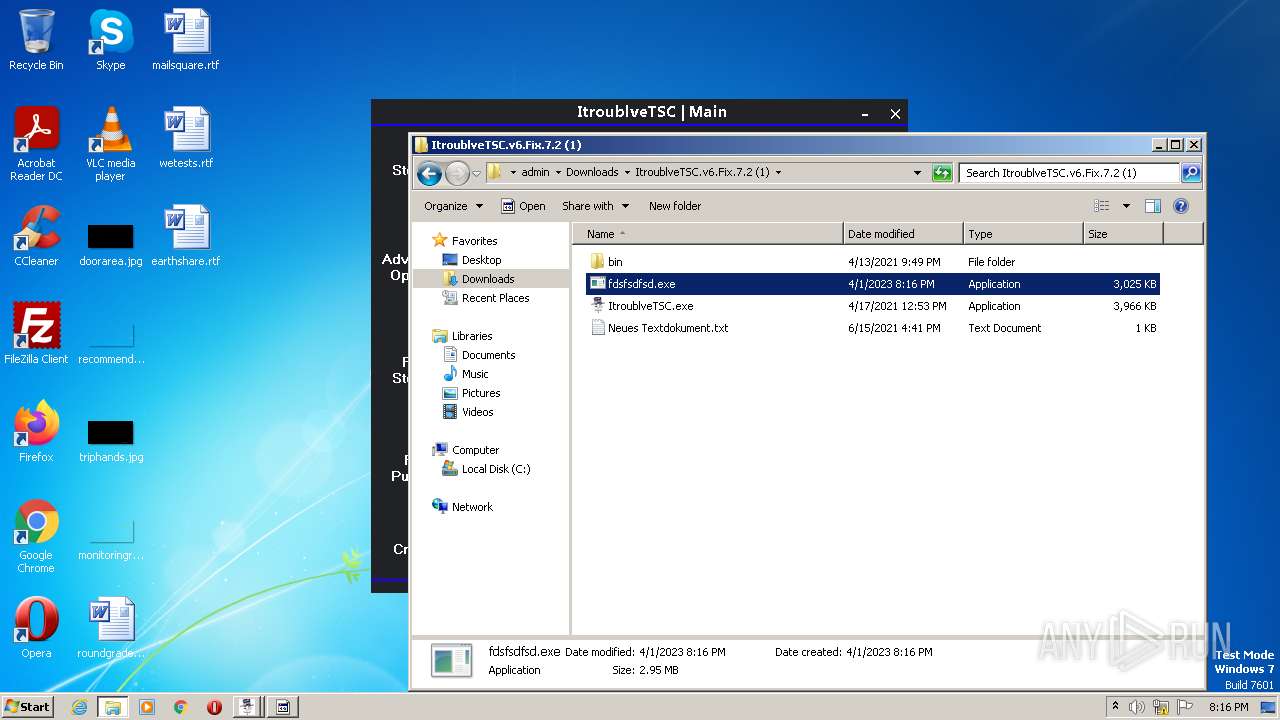
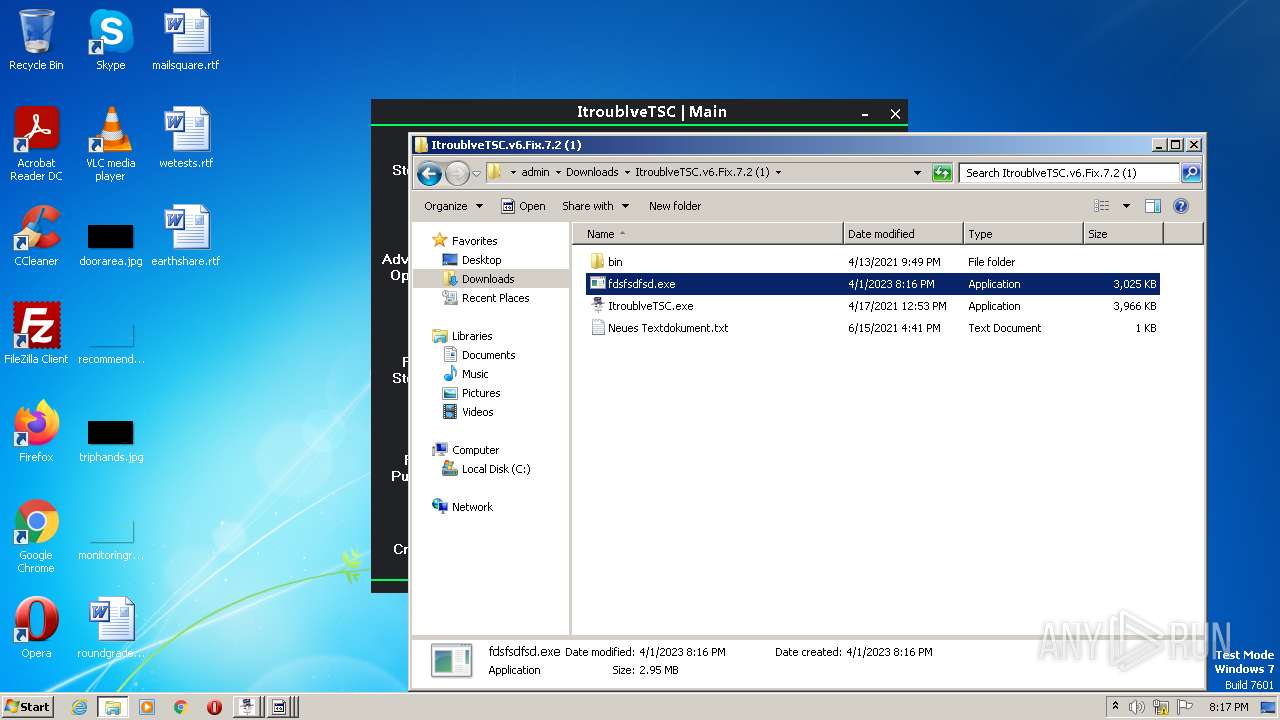
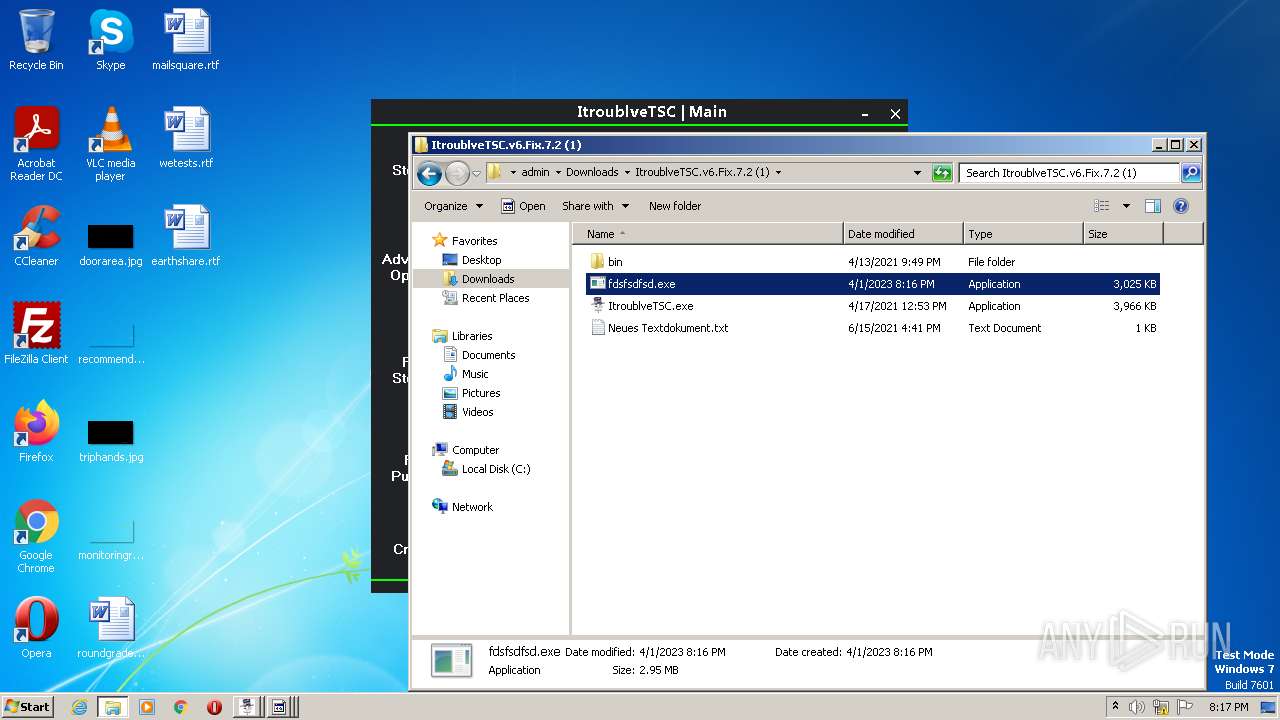
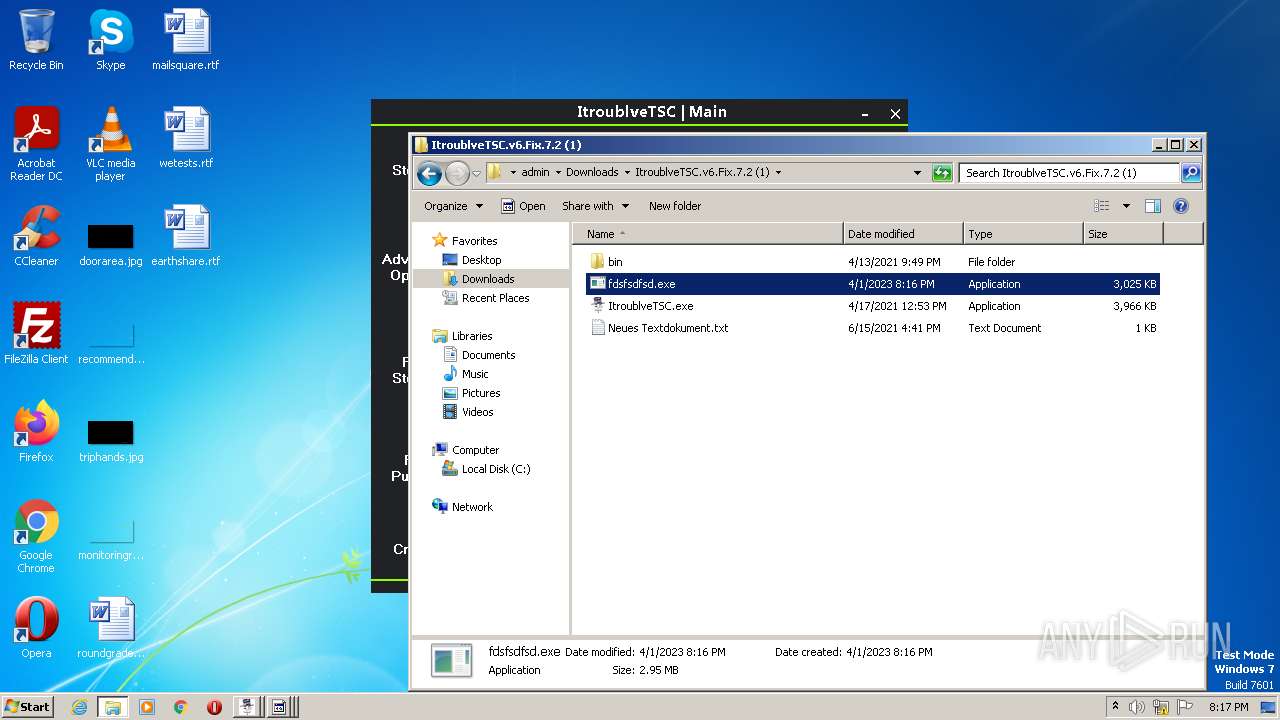
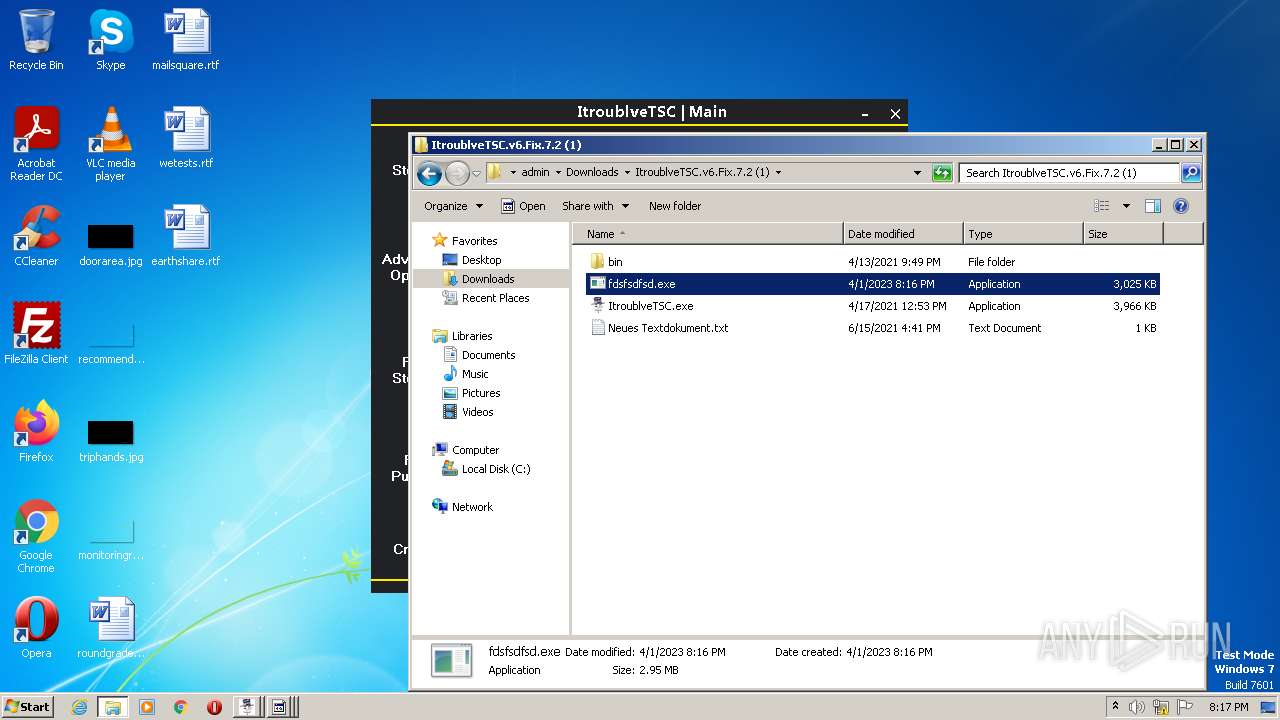
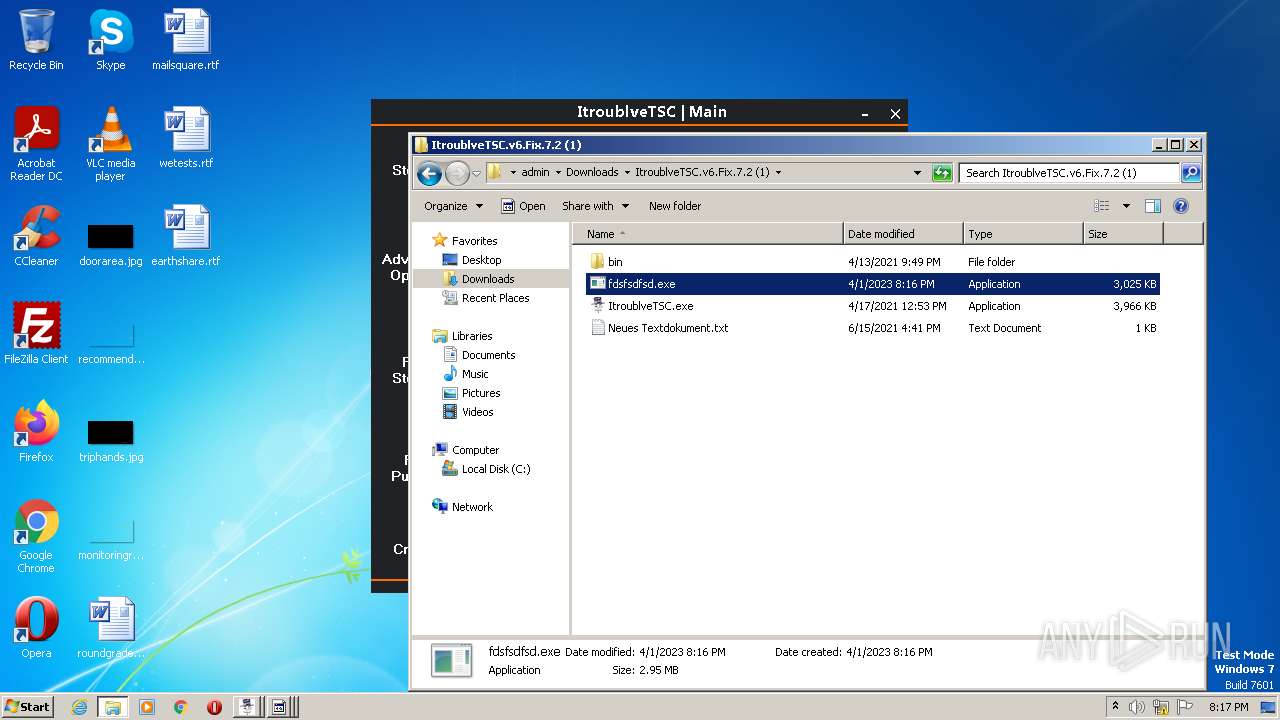
Manual execution by a user
- explorer.exe (PID: 3392)
- WinRAR.exe (PID: 2808)
- ItroublveTSC.exe (PID: 1748)
- WinRAR.exe (PID: 3812)
- WinRAR.exe (PID: 3168)
- fdsfds.exe (PID: 3488)
- explorer.exe (PID: 3456)
- ItroublveTSC.exe (PID: 1436)
- fdsfsdfsd.exe (PID: 2428)
- fdsfsdfsd.exe (PID: 2244)
- fdsfsdfsd.exe (PID: 1616)
- fdsfsdfsd.exe (PID: 3764)
- fdsfsdfsd.exe (PID: 2148)
- fdsfsdfsd.exe (PID: 116)
The process checks LSA protection
- explorer.exe (PID: 3392)
- ItroublveTSC.exe (PID: 1748)
- MSBuild.exe (PID: 2984)
- csc.exe (PID: 3920)
- cvtres.exe (PID: 2064)
- fdsfds.exe (PID: 3488)
- RtkBtManServ.exe (PID: 1640)
- snuvcdsm.exe (PID: 600)
- explorer.exe (PID: 3456)
- MSBuild.exe (PID: 3672)
- ItroublveTSC.exe (PID: 1436)
- csc.exe (PID: 3552)
- cvtres.exe (PID: 1964)
- CLI.exe (PID: 1392)
- fdsfsdfsd.exe (PID: 2428)
- fdsfsdfsd.exe (PID: 2244)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 3764)
- fdsfsdfsd.exe (PID: 1616)
- snuvcdsm.exe (PID: 2864)
- fdsfsdfsd.exe (PID: 2148)
- fdsfsdfsd.exe (PID: 116)
- RtkBtManServ.exe (PID: 3032)
- snuvcdsm.exe (PID: 3768)
Checks supported languages
- ItroublveTSC.exe (PID: 1748)
- MSBuild.exe (PID: 2984)
- csc.exe (PID: 3920)
- cvtres.exe (PID: 2064)
- fdsfds.exe (PID: 3488)
- RtkBtManServ.exe (PID: 1640)
- bfsvc.exe (PID: 1060)
- snuvcdsm.exe (PID: 600)
- winhlp32.exe (PID: 1940)
- splwow64.exe (PID: 3096)
- hh.exe (PID: 2096)
- xwizard.exe (PID: 3704)
- ItroublveTSC.exe (PID: 1436)
- MSBuild.exe (PID: 3672)
- csc.exe (PID: 3552)
- cvtres.exe (PID: 1964)
- fdsfsdfsd.exe (PID: 2428)
- CLI.exe (PID: 1392)
- fdsfsdfsd.exe (PID: 2244)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 3764)
- fdsfsdfsd.exe (PID: 1616)
- snuvcdsm.exe (PID: 2864)
- bfsvc.exe (PID: 3136)
- winhlp32.exe (PID: 1180)
- splwow64.exe (PID: 1412)
- hh.exe (PID: 3260)
- fdsfsdfsd.exe (PID: 2148)
- xwizard.exe (PID: 3768)
- fdsfsdfsd.exe (PID: 116)
- RtkBtManServ.exe (PID: 3032)
- bfsvc.exe (PID: 2188)
- snuvcdsm.exe (PID: 3768)
- winhlp32.exe (PID: 2384)
- splwow64.exe (PID: 2772)
- xwizard.exe (PID: 2348)
- hh.exe (PID: 3200)
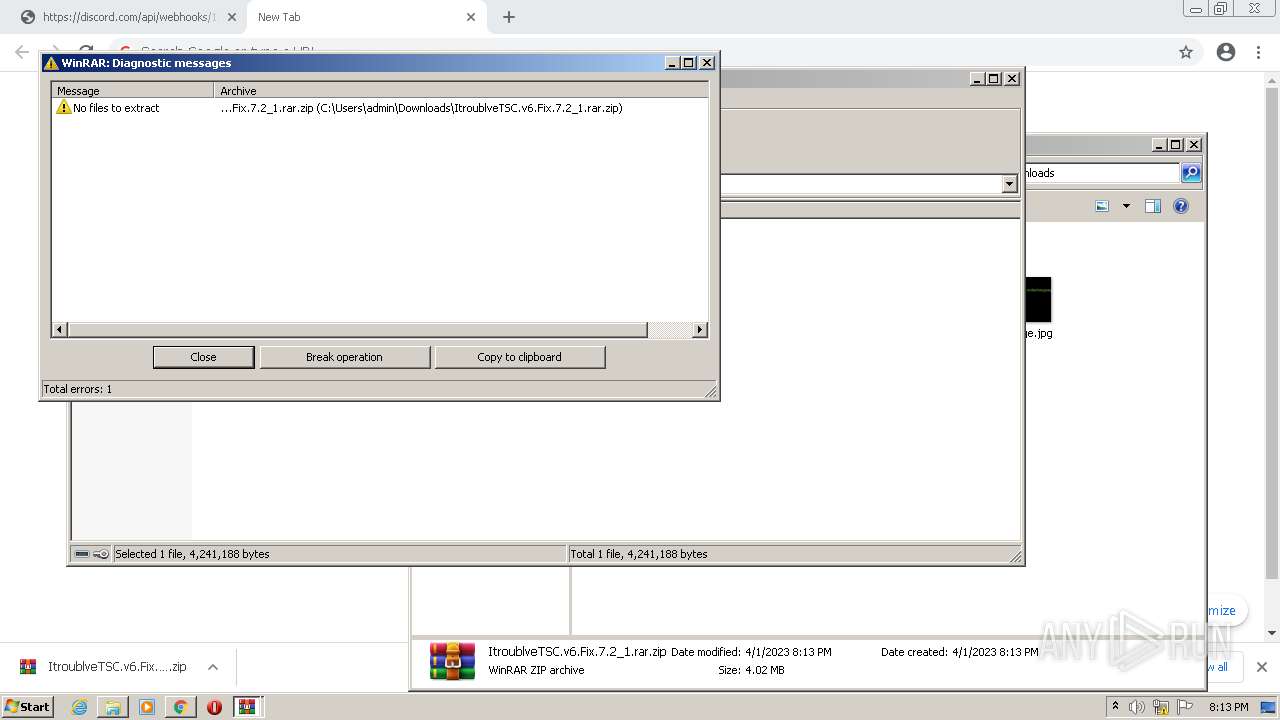
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3056)
Reads the computer name
- ItroublveTSC.exe (PID: 1748)
- MSBuild.exe (PID: 2984)
- fdsfds.exe (PID: 3488)
- RtkBtManServ.exe (PID: 1640)
- bfsvc.exe (PID: 1060)
- snuvcdsm.exe (PID: 600)
- winhlp32.exe (PID: 1940)
- ItroublveTSC.exe (PID: 1436)
- MSBuild.exe (PID: 3672)
- fdsfsdfsd.exe (PID: 2428)
- CLI.exe (PID: 1392)
- fdsfsdfsd.exe (PID: 2244)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 1616)
- fdsfsdfsd.exe (PID: 3764)
- snuvcdsm.exe (PID: 2864)
- bfsvc.exe (PID: 3136)
- winhlp32.exe (PID: 1180)
- fdsfsdfsd.exe (PID: 2148)
- RtkBtManServ.exe (PID: 3032)
- fdsfsdfsd.exe (PID: 116)
- bfsvc.exe (PID: 2188)
- snuvcdsm.exe (PID: 3768)
- winhlp32.exe (PID: 2384)
Reads Environment values
- ItroublveTSC.exe (PID: 1748)
- RtkBtManServ.exe (PID: 1640)
- ItroublveTSC.exe (PID: 1436)
- RtkBtManServ.exe (PID: 1992)
- RtkBtManServ.exe (PID: 3032)
Reads the machine GUID from the registry
- ItroublveTSC.exe (PID: 1748)
- MSBuild.exe (PID: 2984)
- csc.exe (PID: 3920)
- cvtres.exe (PID: 2064)
- fdsfds.exe (PID: 3488)
- RtkBtManServ.exe (PID: 1640)
- snuvcdsm.exe (PID: 600)
- ItroublveTSC.exe (PID: 1436)
- cvtres.exe (PID: 1964)
- MSBuild.exe (PID: 3672)
- csc.exe (PID: 3552)
- fdsfsdfsd.exe (PID: 2428)
- CLI.exe (PID: 1392)
- fdsfsdfsd.exe (PID: 2244)
- RtkBtManServ.exe (PID: 1992)
- fdsfsdfsd.exe (PID: 3764)
- snuvcdsm.exe (PID: 2864)
- fdsfsdfsd.exe (PID: 1616)
- fdsfsdfsd.exe (PID: 2148)
- fdsfsdfsd.exe (PID: 116)
- RtkBtManServ.exe (PID: 3032)
- snuvcdsm.exe (PID: 3768)
Creates files or folders in the user directory
- splwow64.exe (PID: 3096)
- xwizard.exe (PID: 3704)
- splwow64.exe (PID: 1412)
- xwizard.exe (PID: 3768)
- splwow64.exe (PID: 2772)
- xwizard.exe (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
171
Monitored processes
106
Malicious processes
52
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\Downloads\ItroublveTSC.v6.Fix.7.2 (1)\fdsfsdfsd.exe" | C:\Users\admin\Downloads\ItroublveTSC.v6.Fix.7.2 (1)\fdsfsdfsd.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 296 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\compile.vbs" | C:\Windows\System32\wscript.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 308 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\compile.vbs" | C:\Windows\System32\wscript.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 476 | "C:\Windows\System32\cmd.exe" /c compile.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe /stext "C:\Users\admin\AppData\Local\Temp\admin_Passwords.txt" | C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe | cmd.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Web Browser Password Viewer Exit code: 0 Version: 2.06 Modules
| |||||||||||||||
| 852 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\compile.vbs" | C:\Windows\System32\wscript.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1060 | C:\Users\admin\AppData\Local\Temp\bfsvc.exe /capture /Filename "C:\Users\admin\AppData\Local\Temp\capture.png" | C:\Users\admin\AppData\Local\Temp\bfsvc.exe | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: WebCamImageSave Exit code: 3221225547 Version: 1.11 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,2721312467202938198,16138510272847829393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Windows\System32\cmd.exe" /C choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\AppData\Local\Temp\RtkBtManServ.exe" | C:\Windows\System32\cmd.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1164 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\compile.vbs" | C:\Windows\System32\wscript.exe | — | RtkBtManServ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
97 494
Read events
96 374
Write events
1 064
Delete events
56
Modification events
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
152
Suspicious files
300
Text files
588
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6428824A-960.pma | — | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3cbdefbf-8a07-4a3e-8940-e5936ba67d2a.tmp | text | |
MD5:— | SHA256:— | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF24f7ce.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF24f7fd.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
35
DNS requests
15
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.95 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 13.8 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 11.5 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 21.8 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 5.54 Kb | whitelisted |
860 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.81 Kb | whitelisted |
860 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dl6iudcrkm7tlleep5b7sio2si_2937/jflookgnkcckhobaglndicnbbgbonegd_2937_all_n6dma56ie7wmbezc4aw6zyp2jq.crx3 | US | crx | 54.9 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | crx | 54.9 Kb | whitelisted |
860 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | crx | 10.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | chrome.exe | 142.250.184.237:443 | accounts.google.com | GOOGLE | US | suspicious |
3228 | chrome.exe | 162.159.137.232:443 | discord.com | CLOUDFLARENET | — | malicious |
3228 | chrome.exe | 142.250.186.110:443 | clients2.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | suspicious |
3228 | chrome.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3228 | chrome.exe | 142.250.185.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 162.159.130.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
3228 | chrome.exe | 142.250.186.78:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
discord.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
cdn.discordapp.com |
| shared |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
3228 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3228 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
3228 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3228 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
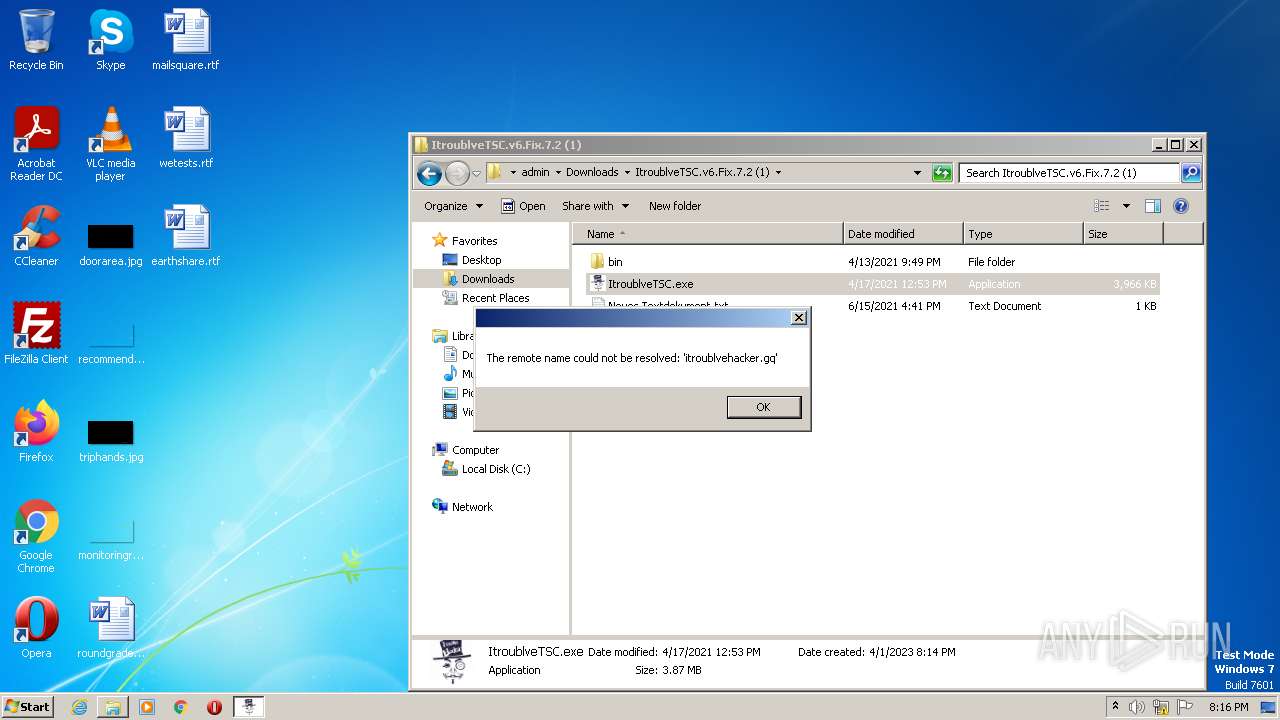
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1640 | RtkBtManServ.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1640 | RtkBtManServ.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |