| File name: | file.ps1 |
| Full analysis: | https://app.any.run/tasks/919bf6b0-9476-45ee-ad88-dc6981c2b444 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 10:18:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 47ABE59F50C6D7657E14FBFBB5DB7804 |
| SHA1: | FEB5B306DCF7E16227705A65D3ED60111F59A98B |
| SHA256: | 36C5D4E97E6DC840EDD07B19E0BE0B3D845519667BBDF8E28D78322DF894C9E1 |
| SSDEEP: | 48:MoQMTz0jW+1F8J8fDyPkpHHdPQS1uBTwnYSzmqDQHKknsoBVw0Nj/xlnxfS:M3RU8fDJpFxETspDQ0o7wmg |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Run PowerShell with an invisible window
- powershell.exe (PID: 664)
SUSPICIOUS
Uses SYSTEMINFO.EXE to read the environment
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Changes AMSI initialization state that disables detection systems (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Process uses IPCONFIG to discover network configuration
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Uses NETSH.EXE to obtain data on the network
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Potential Corporate Privacy Violation
- powershell.exe (PID: 664)
- powershell.exe (PID: 7692)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7692)
Manual execution by a user
- powershell.exe (PID: 664)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Disables trace logs
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
Checks proxy server information
- powershell.exe (PID: 7692)
- powershell.exe (PID: 664)
- slui.exe (PID: 7464)
Reads the software policy settings
- slui.exe (PID: 7464)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
140
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | powershell -w hidden -ep bypass -f "C:\Users\admin\AppData\Roaming\WindowsUpdate.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\WINDOWS\system32\NETSTAT.EXE" -ano | C:\Windows\System32\NETSTAT.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\WINDOWS\system32\netsh.exe" wlan show profiles | C:\Windows\System32\netsh.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | "C:\WINDOWS\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | "C:\WINDOWS\system32\NETSTAT.EXE" -ano | C:\Windows\System32\NETSTAT.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7048 | "C:\WINDOWS\system32\netsh.exe" wlan show profiles | C:\Windows\System32\netsh.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7148 | "C:\WINDOWS\system32\systeminfo.exe" | C:\Windows\System32\systeminfo.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays system information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 283
Read events
32 277
Write events
6
Delete events
0
Modification events
| (PID) Process: | (7692) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SysUpdate |
Value: powershell -w hidden -ep bypass -f "C:\Users\admin\AppData\Roaming\WindowsUpdate.ps1" | |||
| (PID) Process: | (2108) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31176944 | |||
| (PID) Process: | (2108) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: 492025348 | |||
| (PID) Process: | (664) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SysUpdate |
Value: powershell -w hidden -ep bypass -f "C:\Users\admin\AppData\Roaming\WindowsUpdate.ps1" | |||
| (PID) Process: | (2108) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: 538243688 | |||
Executable files
0
Suspicious files
12
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iewrvveu.scv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10e38c.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EFYGCOQAYV8O4FXICFMW.temp | binary | |
MD5:22225C2072D41CF923BB5E38B0B8BF3B | SHA256:6B8A14BFCFCF9E425FCD0A7B0C46CB0333C42BA4B10A1A7DEA0C3EF6F2864E9C | |||
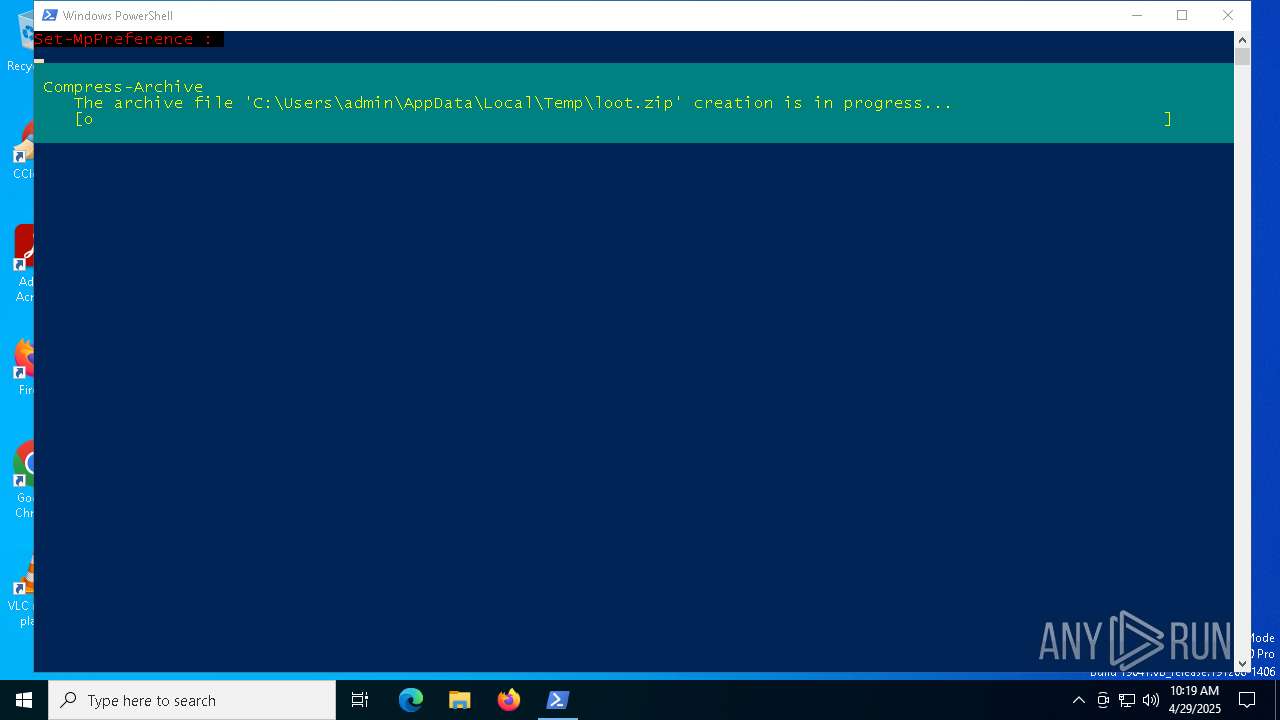
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\loot\system.txt | binary | |
MD5:766ADD5D9FF2C4B5B734E2E933F108F5 | SHA256:17C35F43035C9BF4E2DE324A906FF0B2B623DCE25BD4A621AB16AD2ADF008ED6 | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\loot.zip | compressed | |
MD5:76CDB2BAD9582D23C1F6F4D868218D6C | SHA256:8739C76E681F900923B900C9DF0EF75CF421D39CABB54650C4B9AD19B6A76D85 | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\loot\network.txt | binary | |
MD5:96898F77E551E4FC23E3FC3A124E915F | SHA256:F38C6222248C40A79CD634B5E19B70A1DB45B9FF8451B92E539785855BAA8E3F | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\loot\clipboard.txt | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2108 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:A1F2CC5ABC9D9C1E55BD0909F62AE240 | SHA256:2B4C8544EDD2FF765DE421AF7EC2DE263DCDCD776BBA7EE5639448B2F676A6D7 | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Temp\loot\bios.txt | binary | |
MD5:C9D9577AF27C18FDD33FF8016C0BA7E0 | SHA256:1CBB278B0322A86AFB94AF5C0355E168729DDC36D933C97D75BD2D81C78807E1 | |||
| 7692 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:C904B83F3EB6B36C24B175843EAE2F18 | SHA256:AE9C3B418FC314078AEA3B8FE77670BDBD72E127D1DAE886D031A73C2074B64F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
27
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7692 | powershell.exe | POST | 301 | 209.196.146.115:80 | http://attacker.com/upload.php | unknown | — | — | malicious |
664 | powershell.exe | POST | 301 | 209.196.146.115:80 | http://attacker.com/upload.php | unknown | — | — | malicious |
— | — | GET | 200 | 209.196.146.115:443 | https://attacker.com/upload.php | unknown | html | 12.3 Kb | malicious |
— | — | GET | 200 | 209.196.146.115:443 | https://attacker.com/upload.php | unknown | html | 12.3 Kb | malicious |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7692 | powershell.exe | 209.196.146.115:80 | attacker.com | COGECO-PEER1 | US | malicious |
7692 | powershell.exe | 209.196.146.115:443 | attacker.com | COGECO-PEER1 | US | malicious |
664 | powershell.exe | 209.196.146.115:80 | attacker.com | COGECO-PEER1 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
attacker.com |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7692 | powershell.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Sending Screenshot in Archive via POST Request |
664 | powershell.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Sending Screenshot in Archive via POST Request |
664 | powershell.exe | Misc activity | ET HUNTING ZIP file exfiltration over raw TCP |