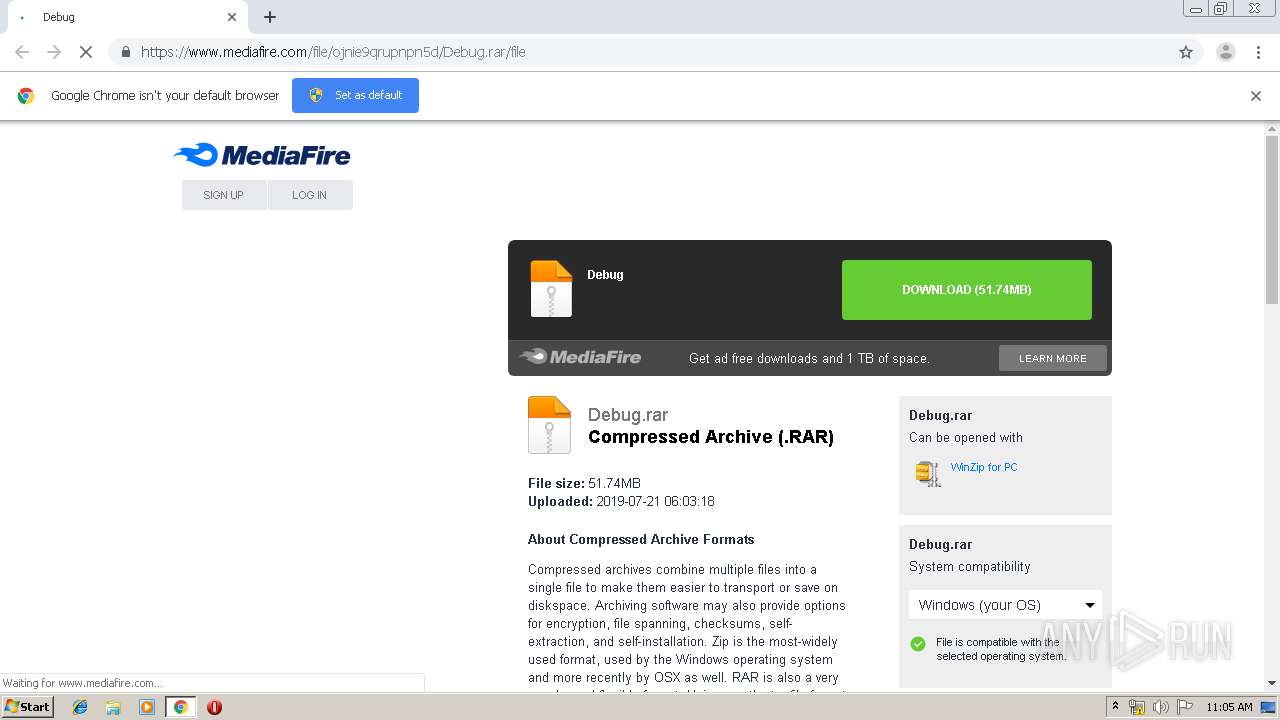
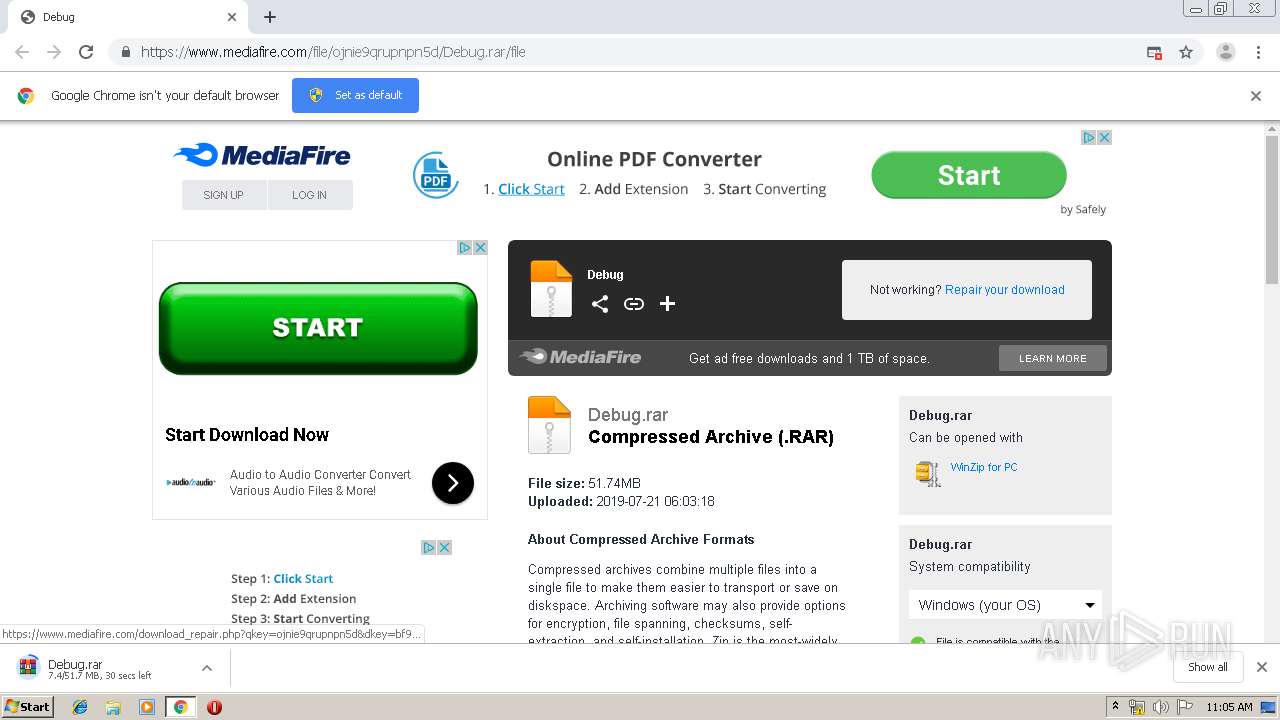
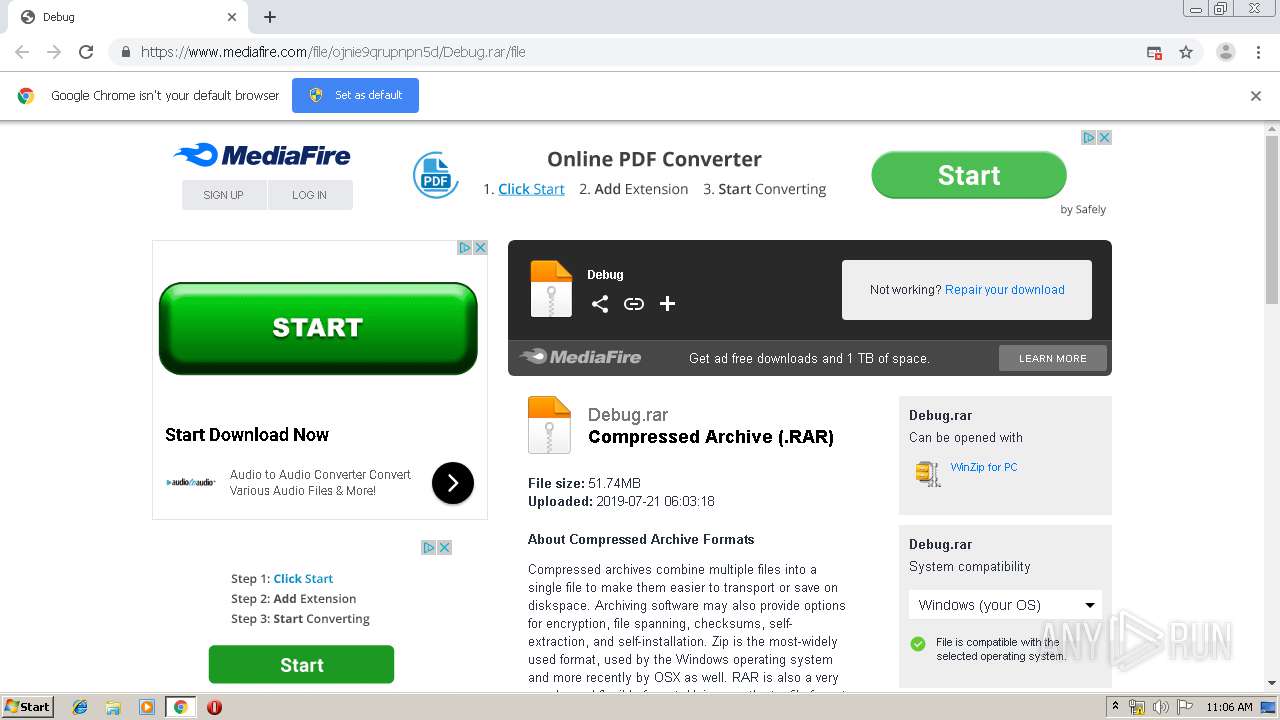
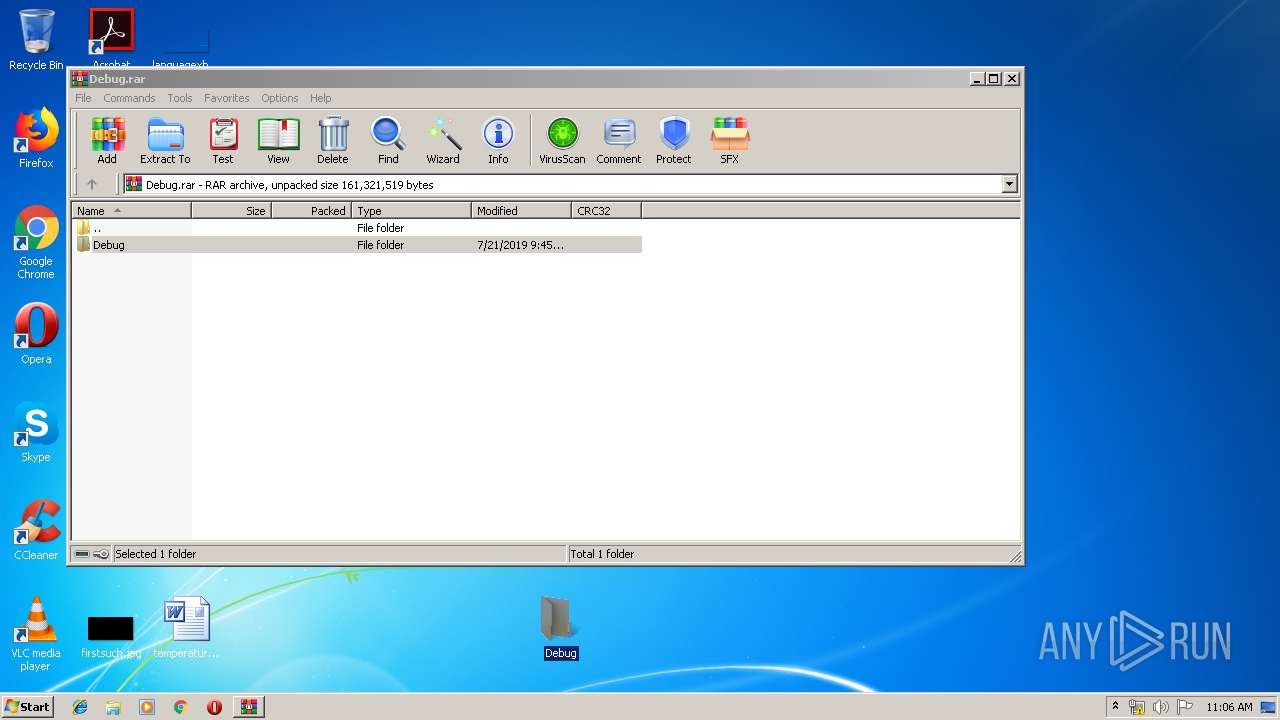
| URL: | https://www.mediafire.com/file/ojnie9qrupnpn5d/Debug.rar/file |
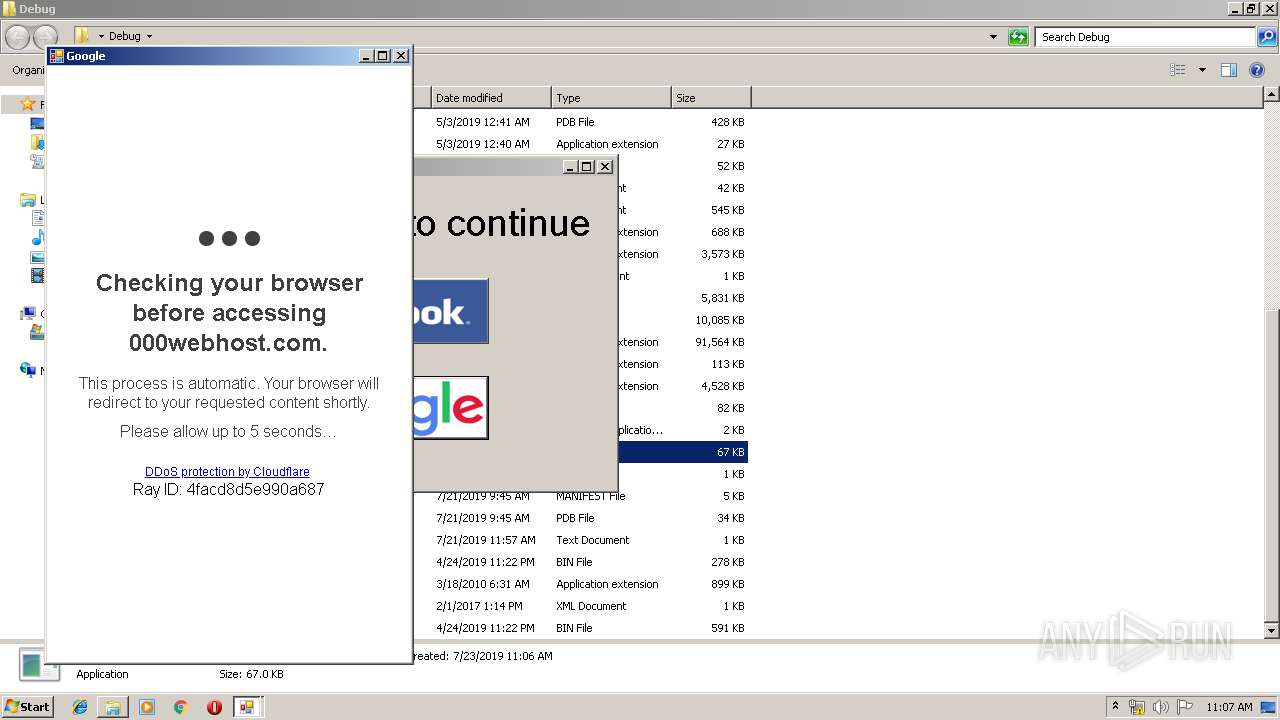
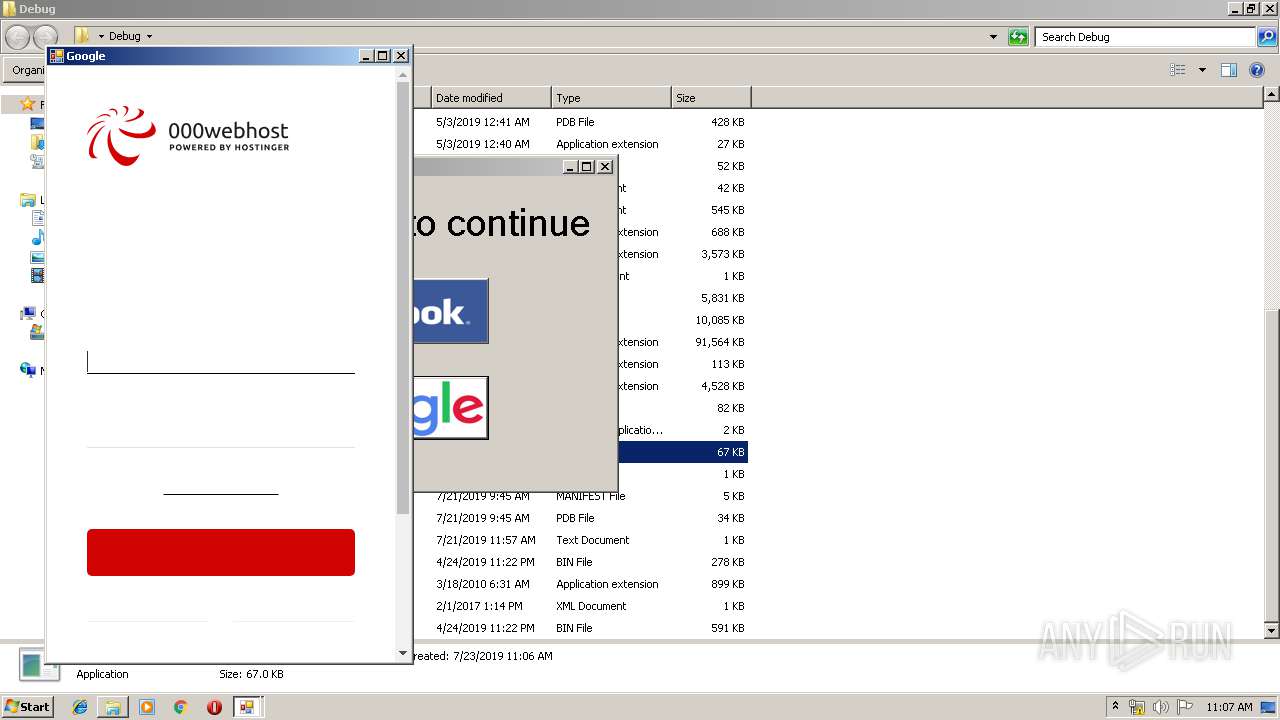
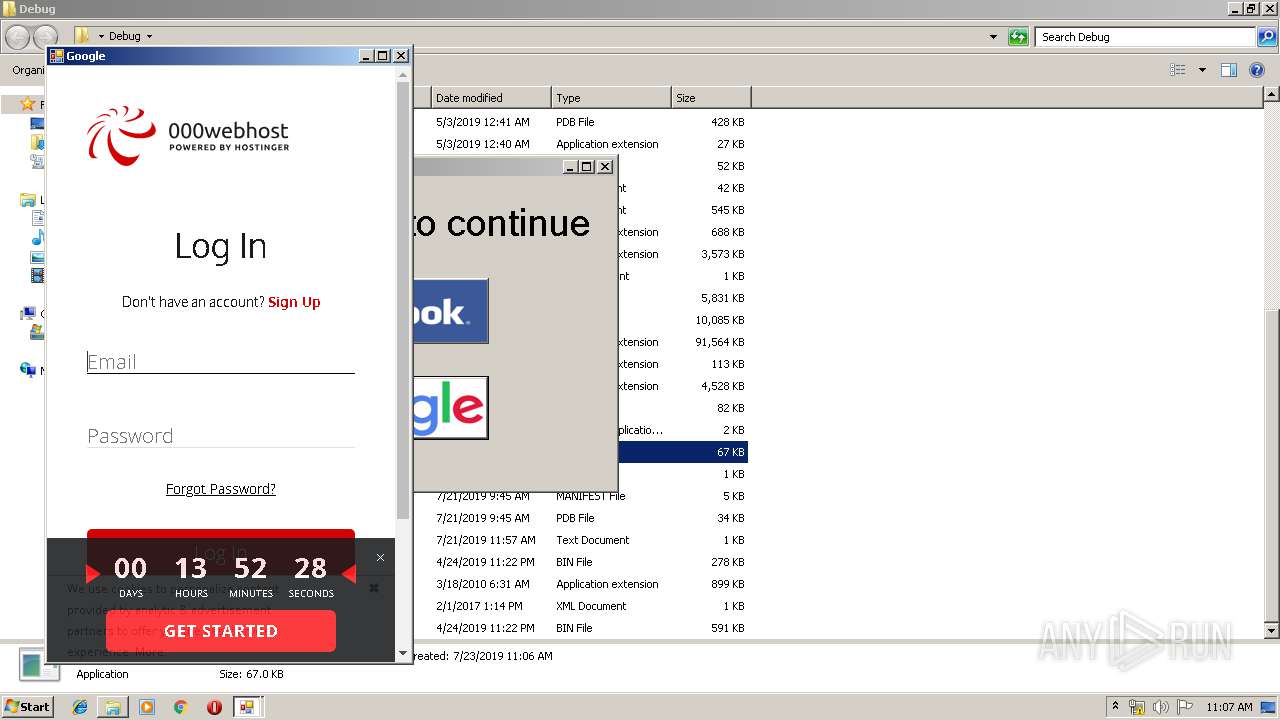
| Full analysis: | https://app.any.run/tasks/78117851-fb7f-4d6e-b716-7cdaab533391 |
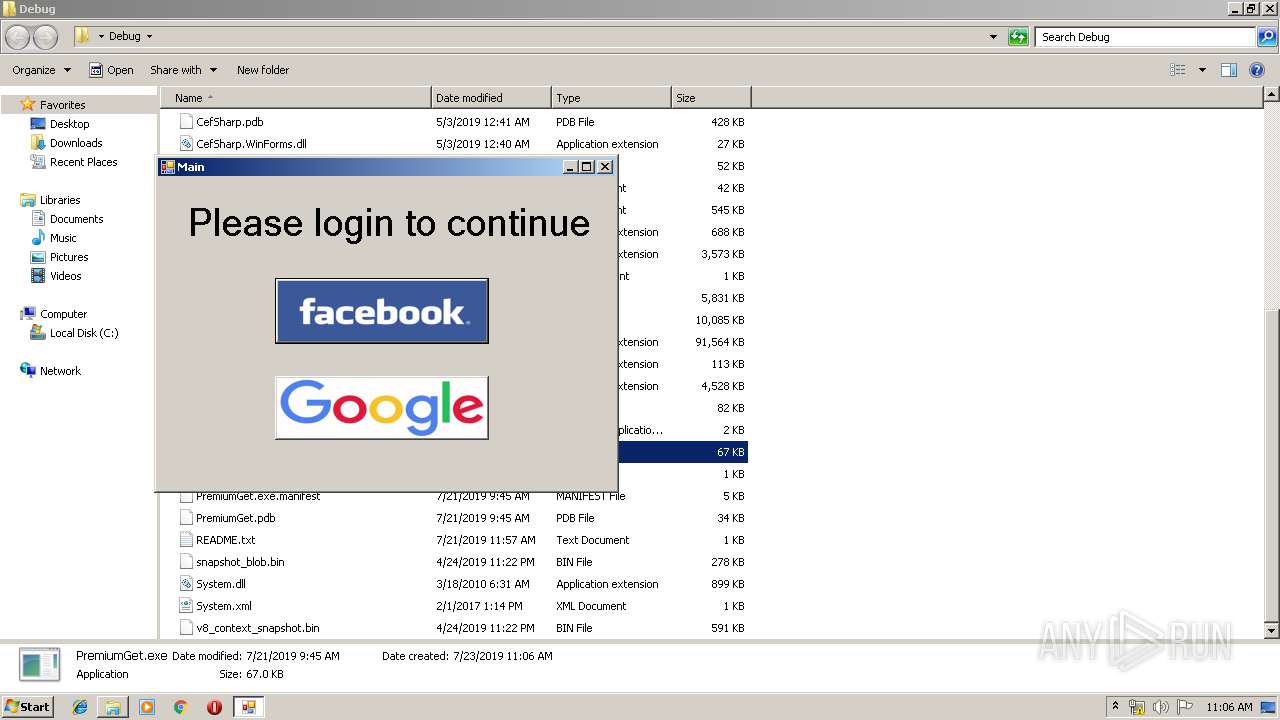
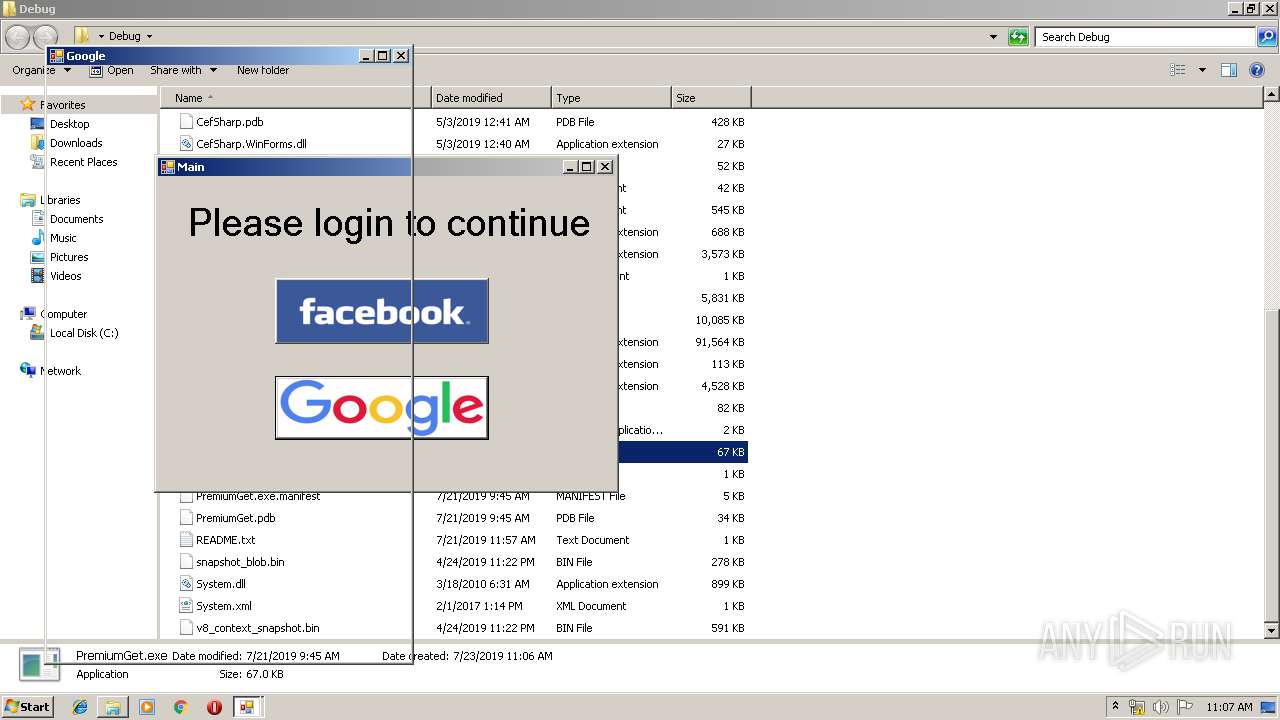
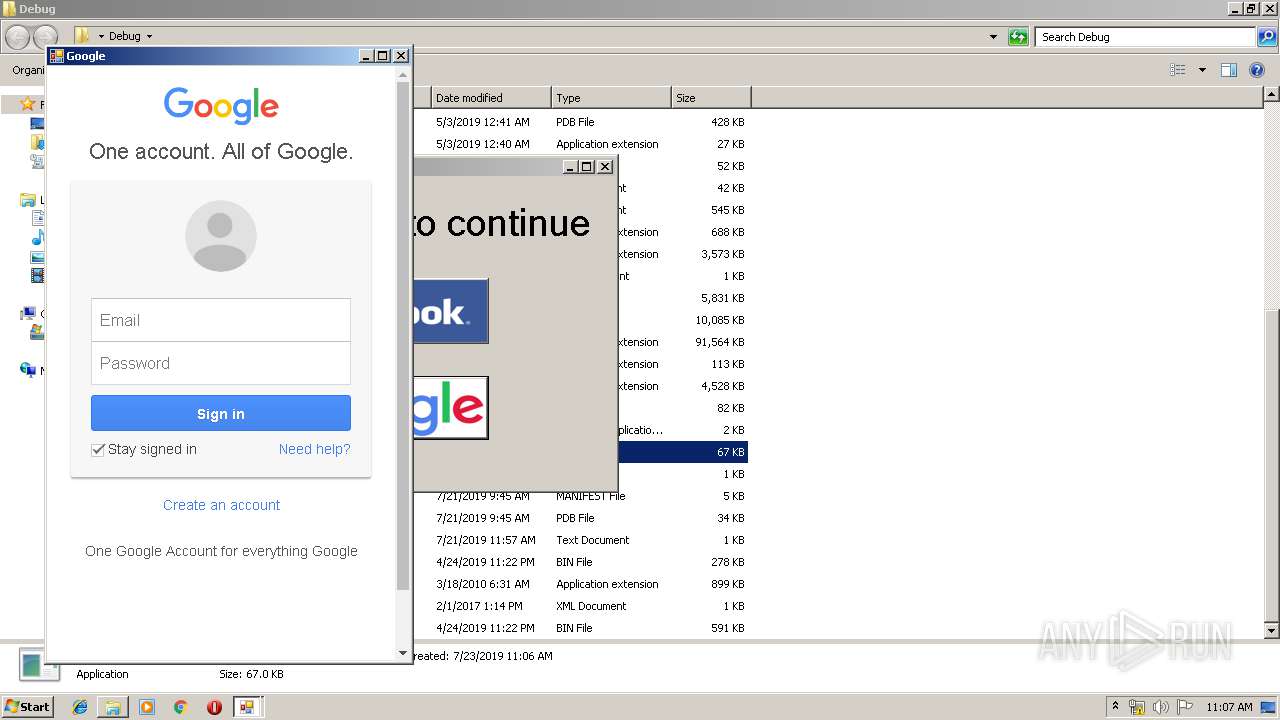
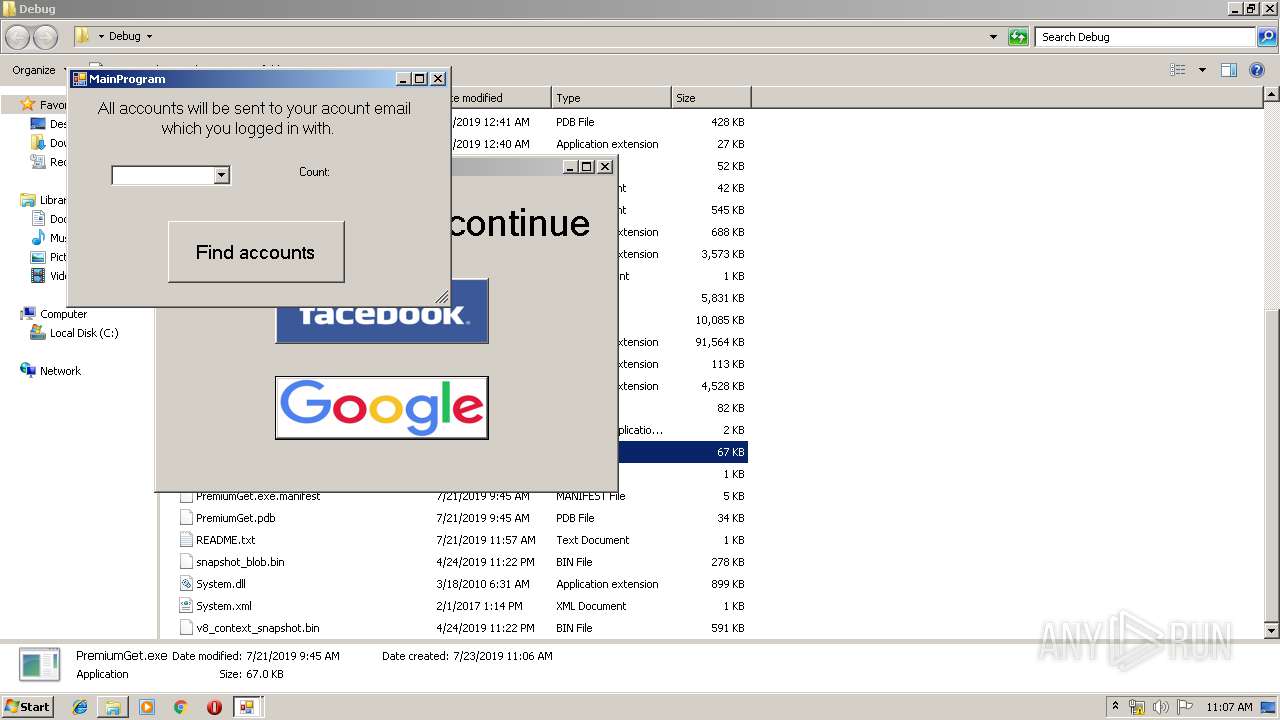
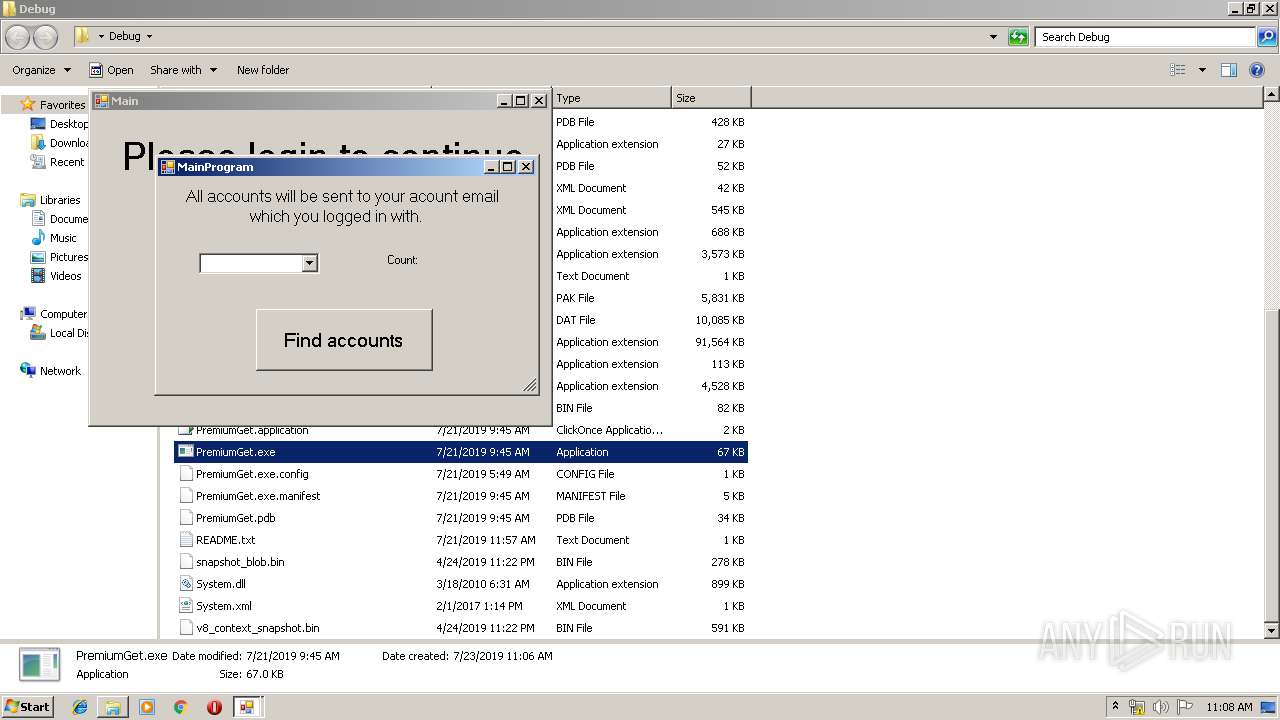
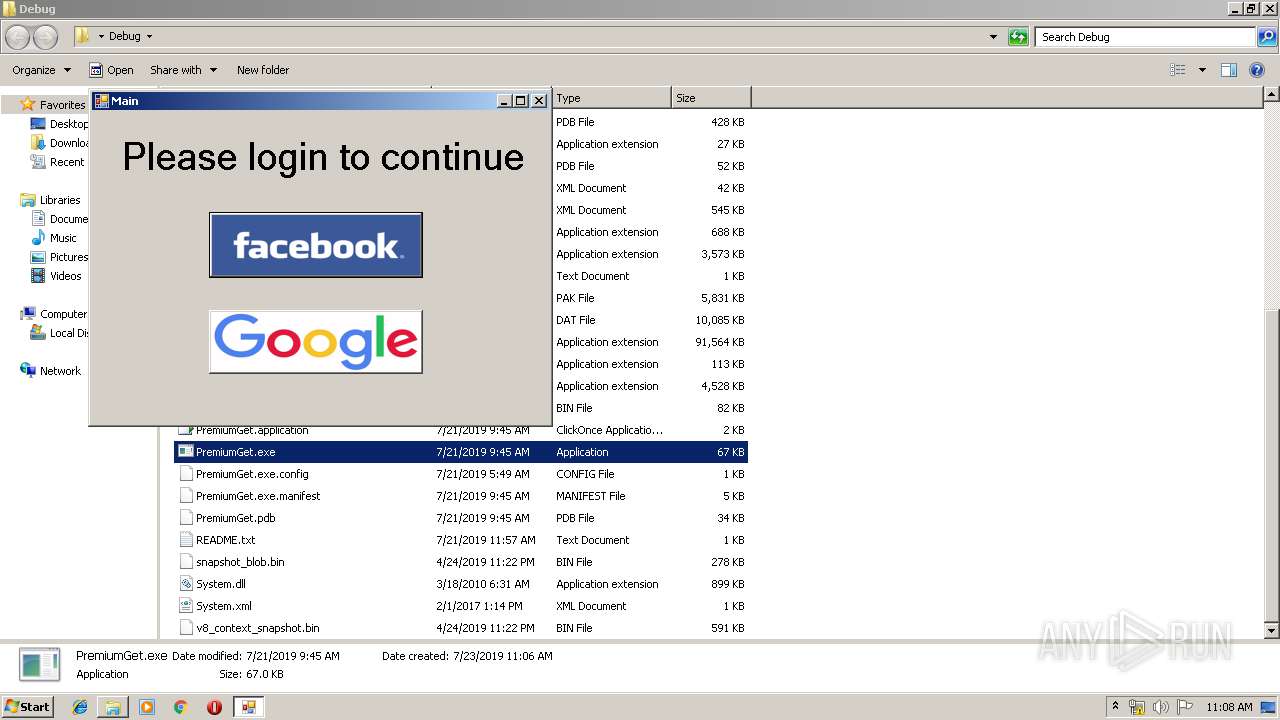
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2019, 10:05:02 |
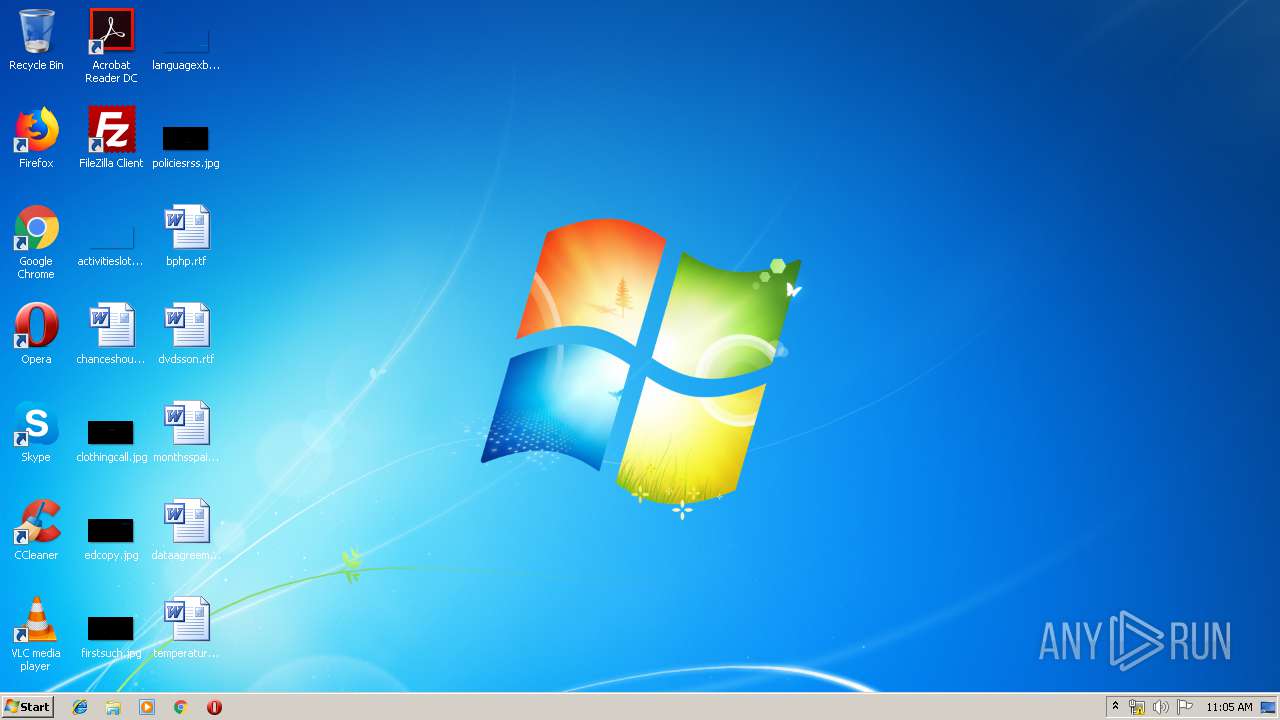
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 84643262F85ABBF76CDC716DA4098388 |
| SHA1: | D8BC192BD2AABFFAC8BBBF41BBC6DD4328678E1B |
| SHA256: | 36C49AC2A0524AD89579E780D3F1B68D860C40E9D026001CFED27C3F11311140 |
| SSDEEP: | 3:N8DSLw3eGUo/5dh3hzgIA:2OLw3eGD5dZ1HA |
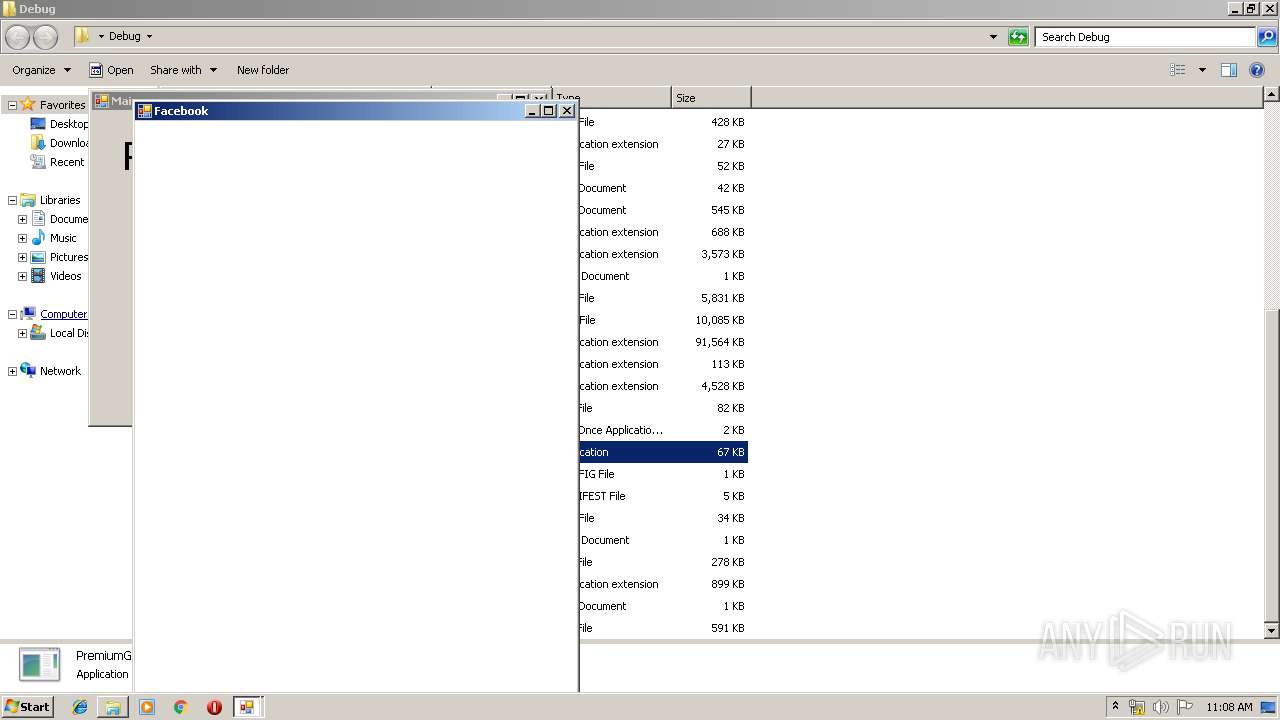
MALICIOUS
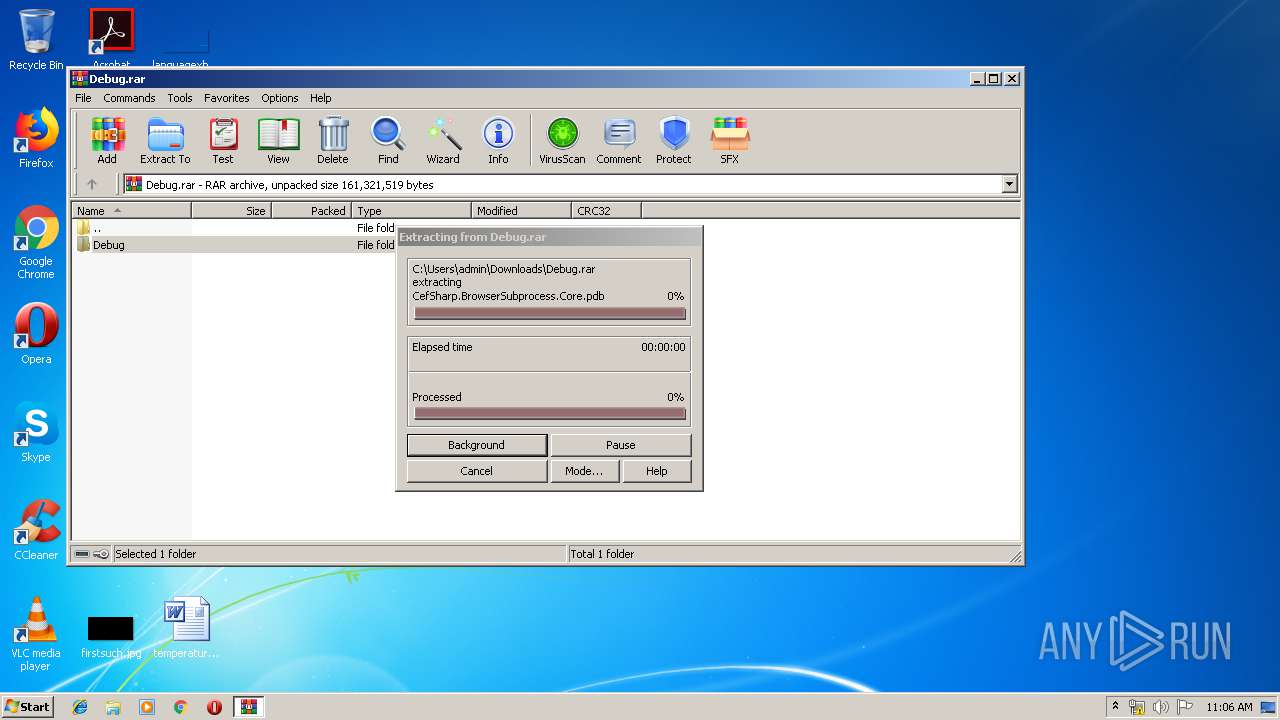
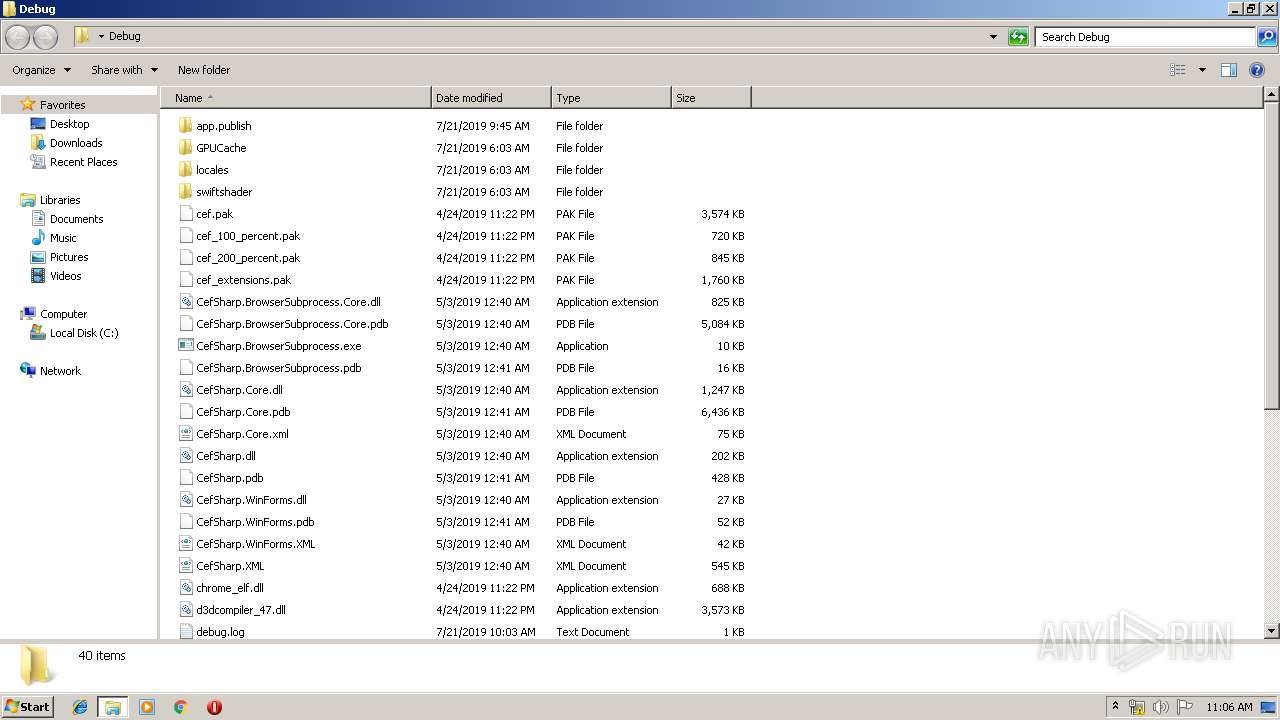
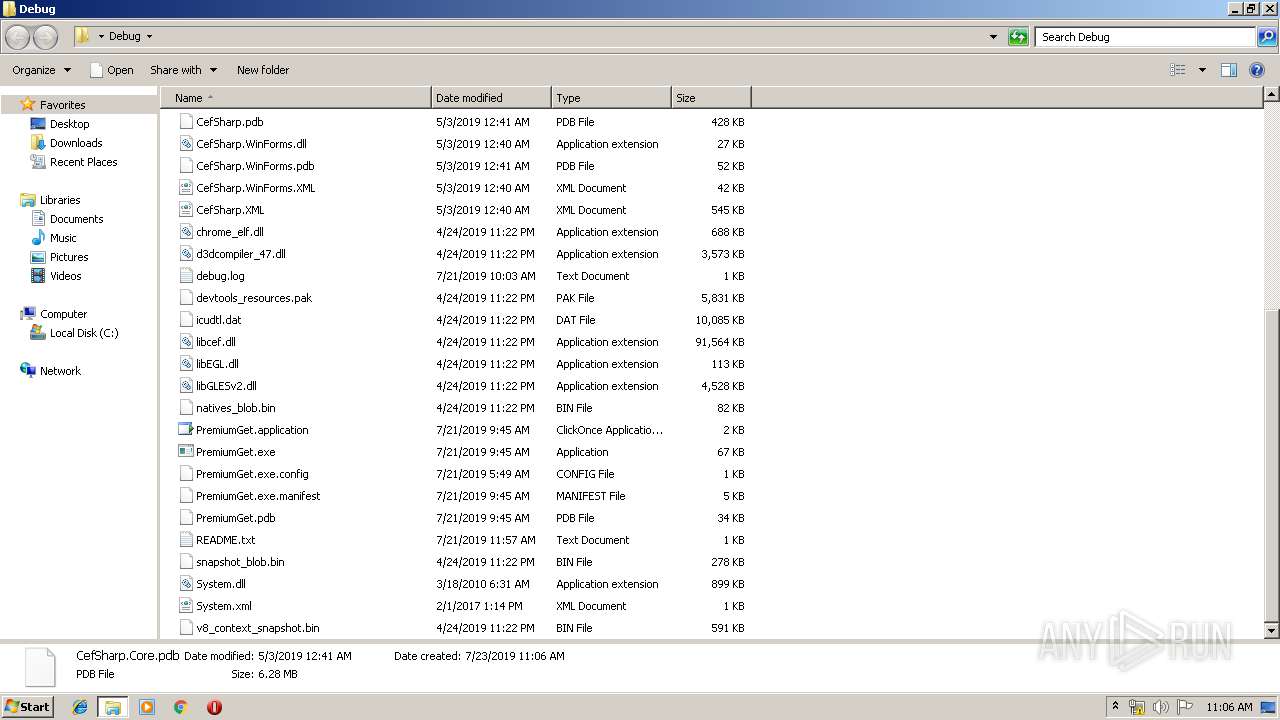
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3016)
- PremiumGet.exe (PID: 620)
- PremiumGet.exe (PID: 288)
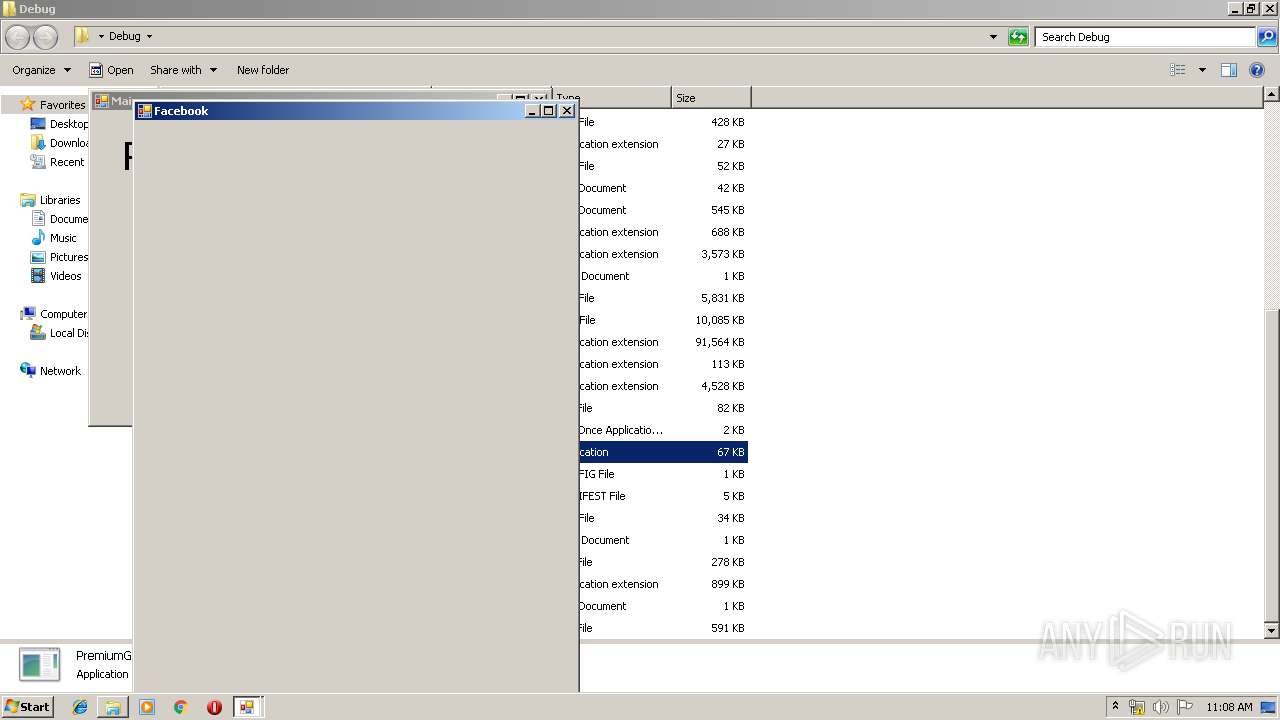
- CefSharp.BrowserSubprocess.exe (PID: 2812)
- CefSharp.BrowserSubprocess.exe (PID: 3964)
- CefSharp.BrowserSubprocess.exe (PID: 2800)
- WerFault.exe (PID: 2804)
- CefSharp.BrowserSubprocess.exe (PID: 1680)
- CefSharp.BrowserSubprocess.exe (PID: 3528)
- CefSharp.BrowserSubprocess.exe (PID: 3612)
Application was dropped or rewritten from another process
- CefSharp.BrowserSubprocess.exe (PID: 3964)
- CefSharp.BrowserSubprocess.exe (PID: 2812)
- CefSharp.BrowserSubprocess.exe (PID: 2800)
- CefSharp.BrowserSubprocess.exe (PID: 3528)
- CefSharp.BrowserSubprocess.exe (PID: 1680)
- CefSharp.BrowserSubprocess.exe (PID: 3612)
SUSPICIOUS
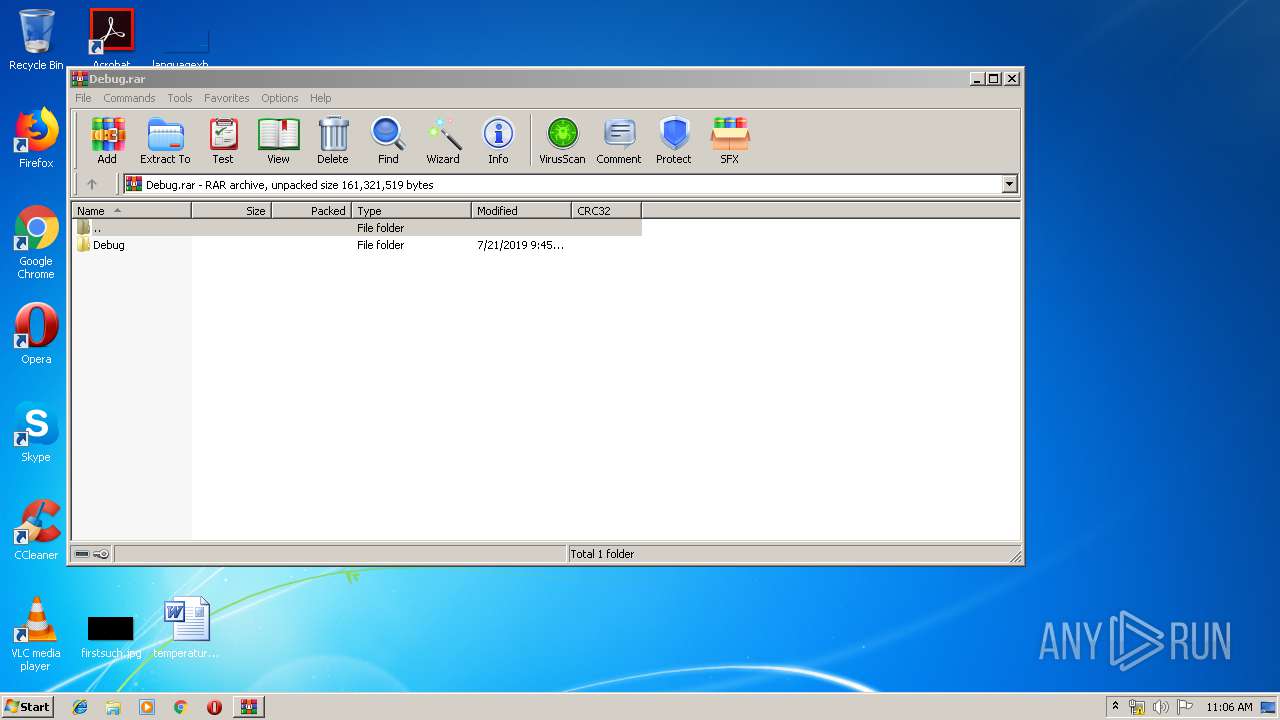
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3396)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3924)
INFO
Application launched itself
- chrome.exe (PID: 3924)
Reads settings of System Certificates
- chrome.exe (PID: 3800)
- PremiumGet.exe (PID: 620)
- PremiumGet.exe (PID: 288)
Reads Internet Cache Settings
- chrome.exe (PID: 3924)
Changes settings of System certificates
- chrome.exe (PID: 3800)
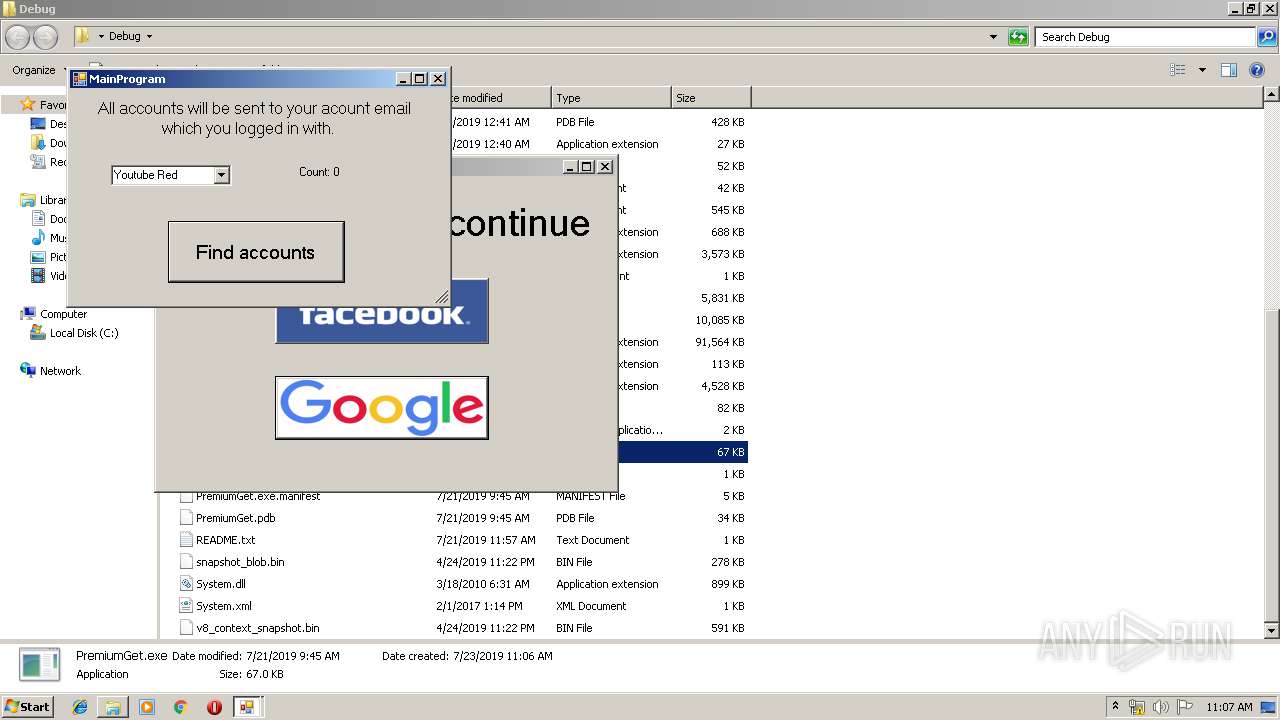
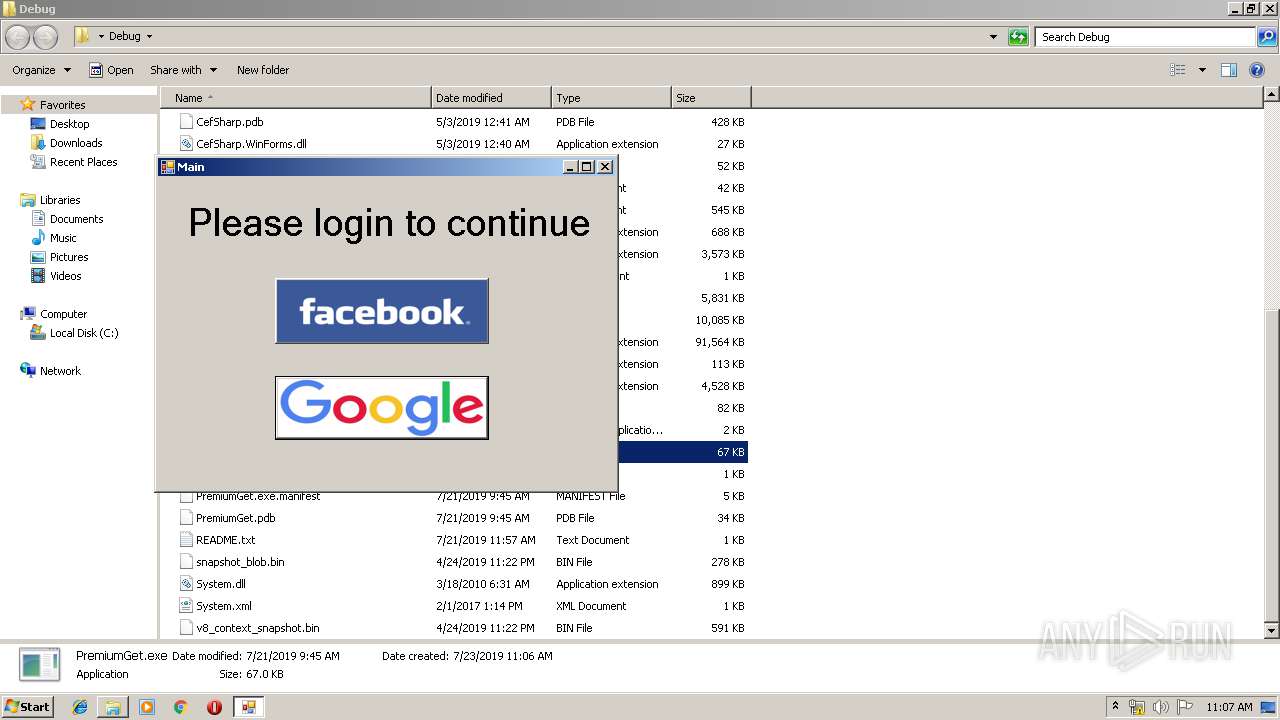
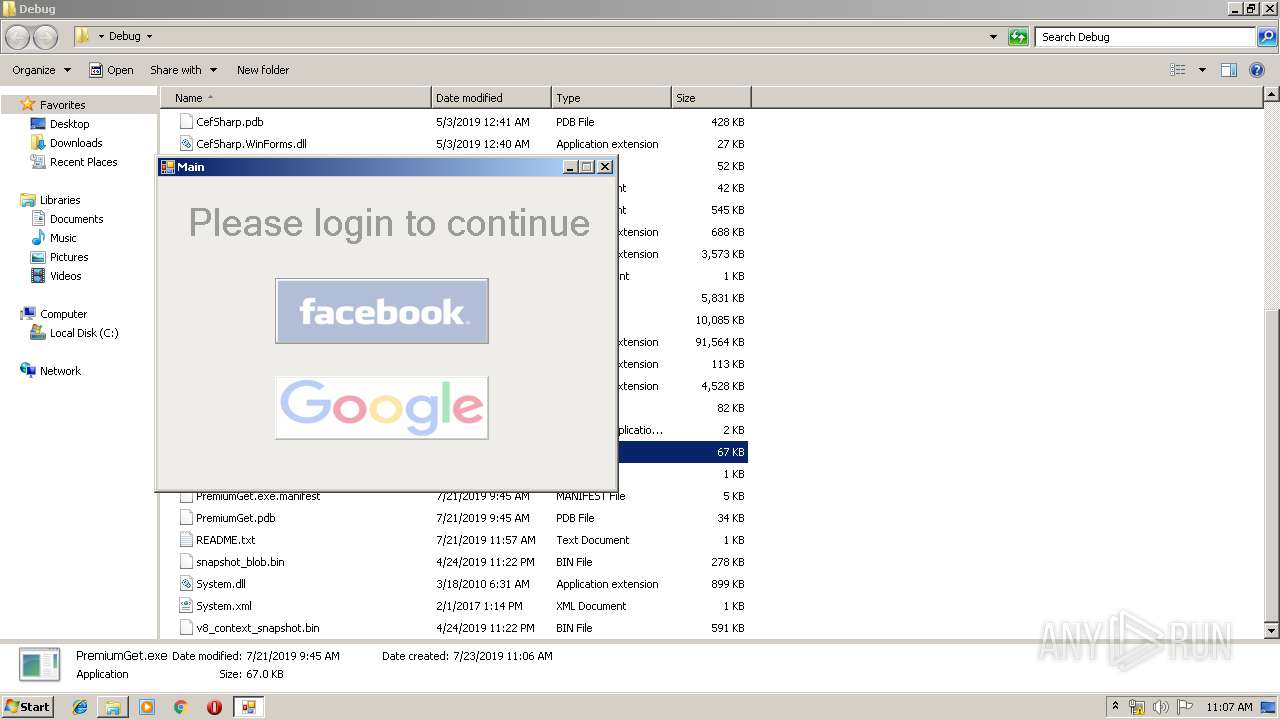
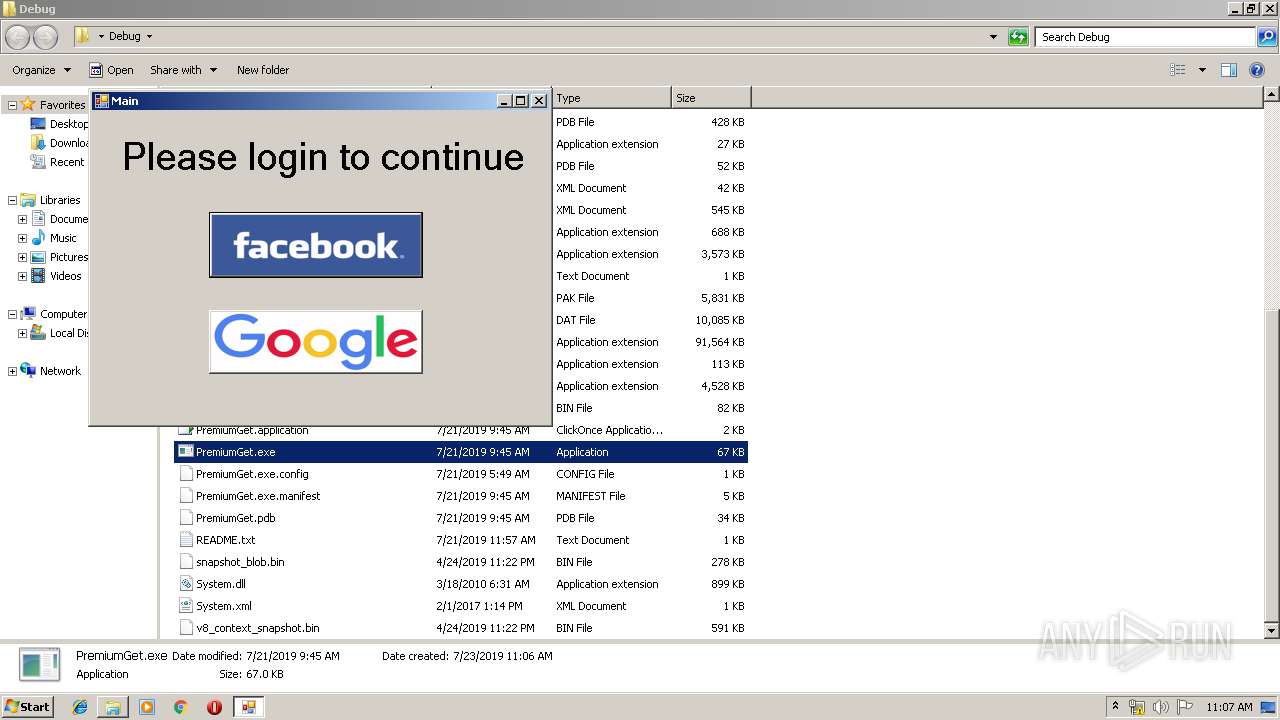
Manual execution by user
- PremiumGet.exe (PID: 288)
- PremiumGet.exe (PID: 620)
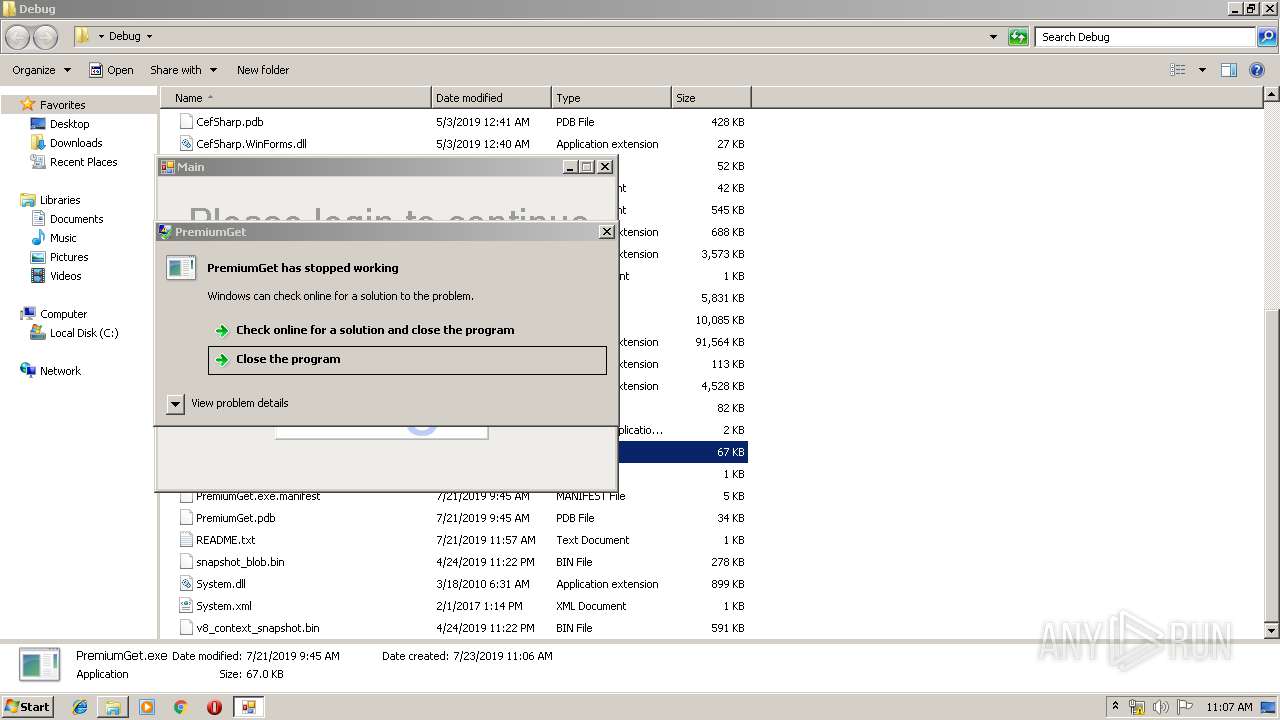
Application was crashed
- PremiumGet.exe (PID: 620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
38
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12763040644896390323,2109333734312739031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9640152476785809985 --mojo-platform-channel-handle=4276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
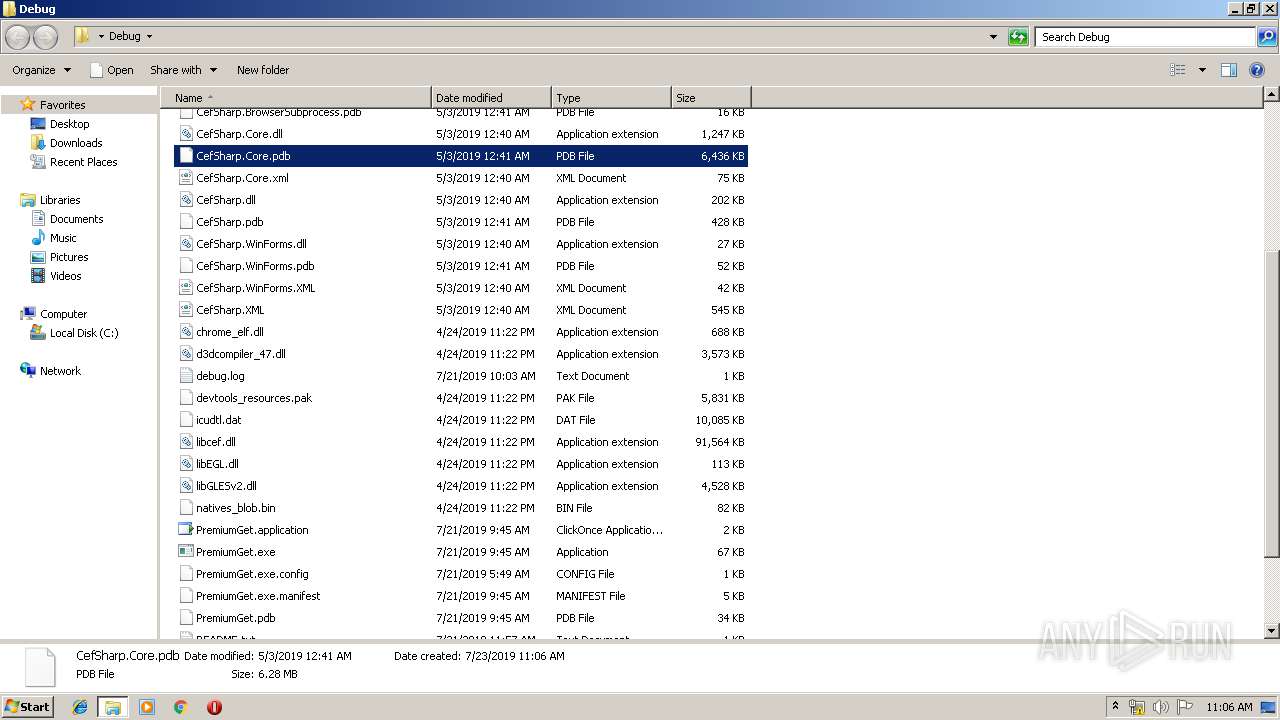
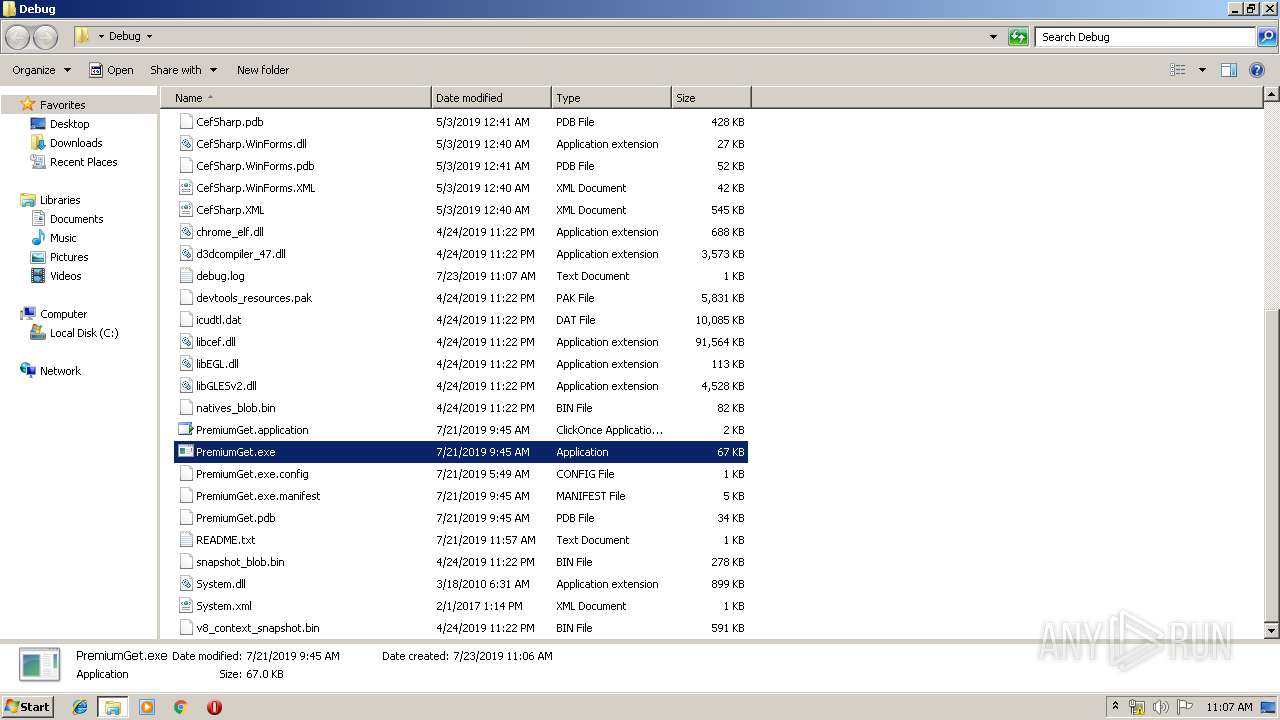
| 288 | "C:\Users\admin\Desktop\Debug\PremiumGet.exe" | C:\Users\admin\Desktop\Debug\PremiumGet.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PremiumGet Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 620 | "C:\Users\admin\Desktop\Debug\PremiumGet.exe" | C:\Users\admin\Desktop\Debug\PremiumGet.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PremiumGet Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12763040644896390323,2109333734312739031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13339825339463698908 --mojo-platform-channel-handle=4280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3928 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e55a9d0,0x6e55a9e0,0x6e55a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Users\admin\Desktop\Debug\CefSharp.BrowserSubprocess.exe" --type=gpu-process --field-trial-handle=1352,2456656332906244932,17133751383098970004,131072 --no-sandbox --log-file="C:\Users\admin\Desktop\Debug\debug.log" --lang=en-US --cefsharpexitsub --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --log-file="C:\Users\admin\Desktop\Debug\debug.log" --service-request-channel-token=1793807740861999575 --mojo-platform-channel-handle=1432 /prefetch:2 --host-process-id=288 | C:\Users\admin\Desktop\Debug\CefSharp.BrowserSubprocess.exe | — | PremiumGet.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: MEDIUM Description: CefSharp.BrowserSubprocess Exit code: 0 Version: 73.1.130.0 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12763040644896390323,2109333734312739031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6441246317960512421 --mojo-platform-channel-handle=3304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12763040644896390323,2109333734312739031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10680446728466176862 --mojo-platform-channel-handle=4280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12763040644896390323,2109333734312739031,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13449470682003872506 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 441
Read events
1 291
Write events
145
Delete events
5
Modification events
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3924-13208349942972500 |
Value: 259 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 572-13197843609579101 |
Value: 0 | |||
| (PID) Process: | (3924) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
11
Suspicious files
89
Text files
182
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3e6ea5f7-7951-4404-b30d-434eb914b7f4.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000022.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18b9f4.TMP | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF18ba91.TMP | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18bc27.TMP | — | |
MD5:— | SHA256:— | |||
| 3924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF18ba52.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
141
DNS requests
103
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3800 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEA8U5EqxnJKPhgtu86L%2BgMk%3D | US | der | 471 b | whitelisted |
3800 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
3800 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://download.televisionfanatic.com/index.jhtml?partner=XPxpw132&s1=101-c6a7de1e-6292-4fa9-a3d8-054352551a42&s2=eivDqnXRZFk | US | — | — | whitelisted |
3800 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3800 | chrome.exe | GET | 200 | 74.125.168.9:80 | http://r4---sn-q0cedn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.153.204.5&mm=28&mn=sn-q0cedn7s&ms=nvh&mt=1563875682&mv=u&mvi=3&pl=21&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3800 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
3800 | chrome.exe | GET | 200 | 52.222.245.68:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3800 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
3800 | chrome.exe | GET | 200 | 8.241.123.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3800 | chrome.exe | 104.19.195.29:443 | www.mediafire.com | Cloudflare Inc | US | shared |
3800 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 35.190.74.157:443 | desiredirt.com | Google Inc. | US | unknown |
3800 | chrome.exe | 172.217.22.74:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 172.217.18.98:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3800 | chrome.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
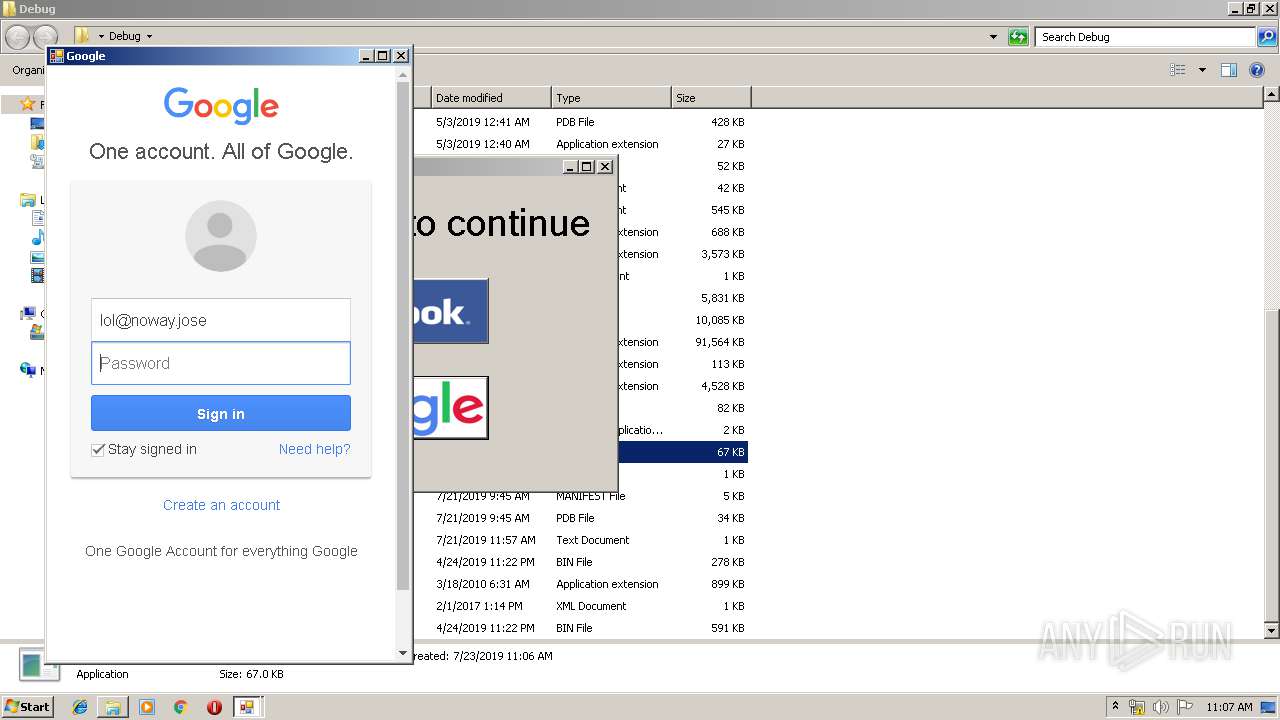
3800 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3800 | chrome.exe | 216.58.207.70:443 | ad.doubleclick.net | Google Inc. | US | whitelisted |
3800 | chrome.exe | 216.58.210.1:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
www.googletagservices.com |
| whitelisted |
desiredirt.com |
| unknown |
static.mediafire.com |
| shared |
adservice.google.ie |
| whitelisted |
adservice.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
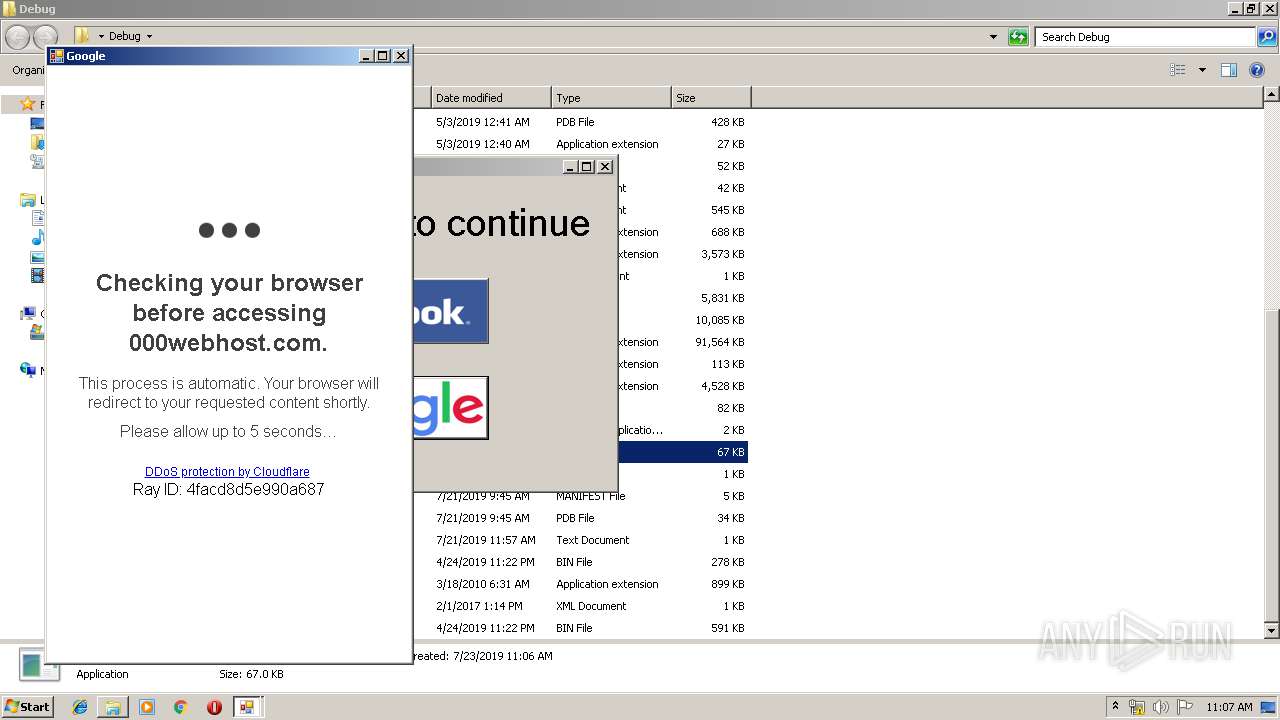
1044 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
Process | Message |
|---|---|
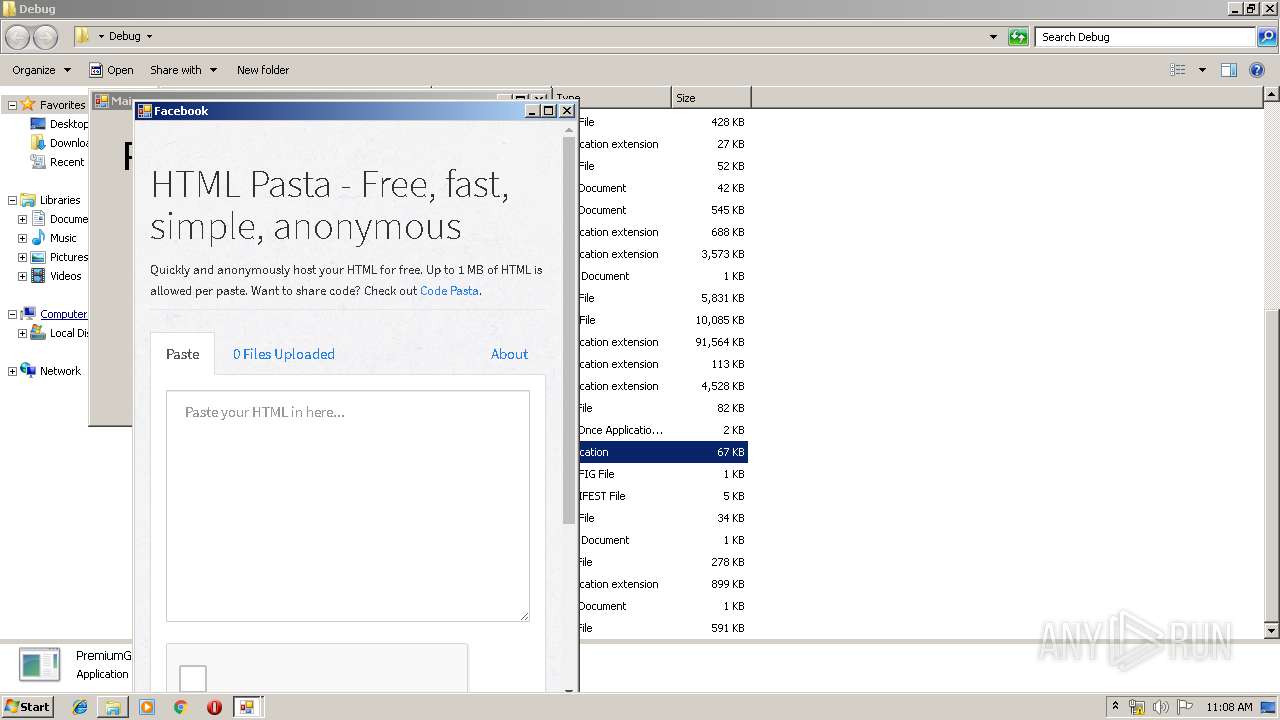
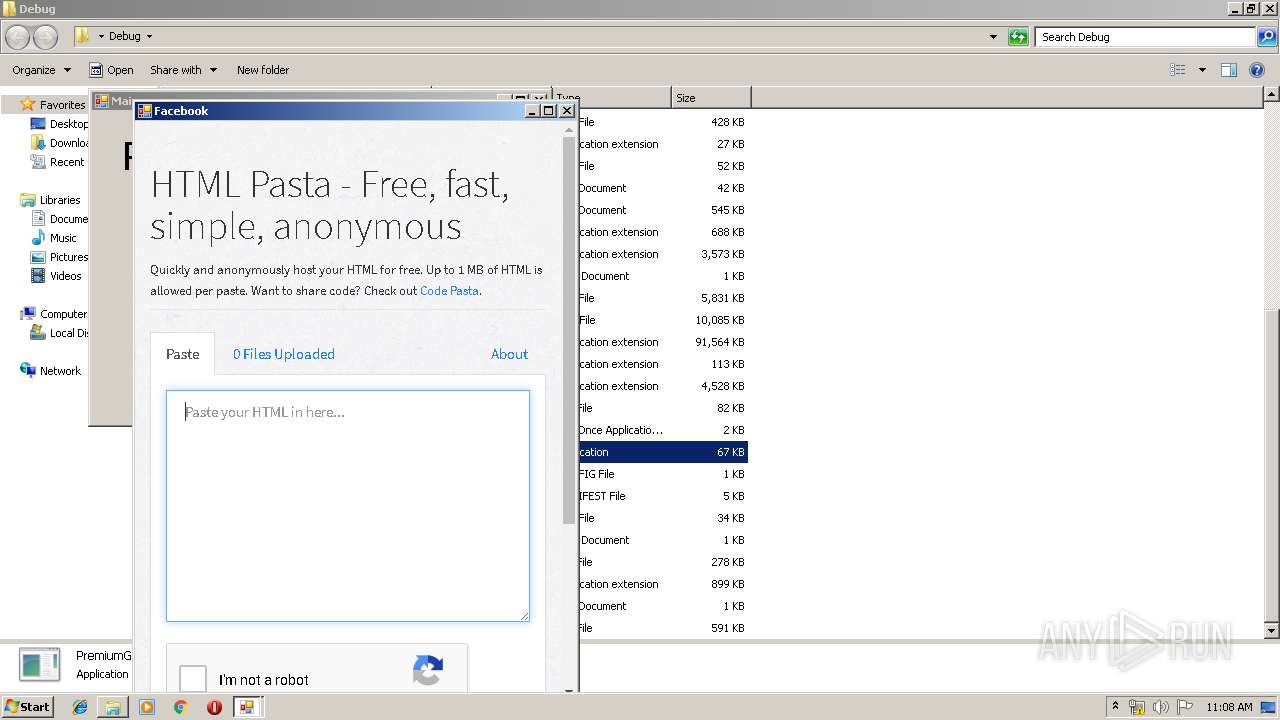
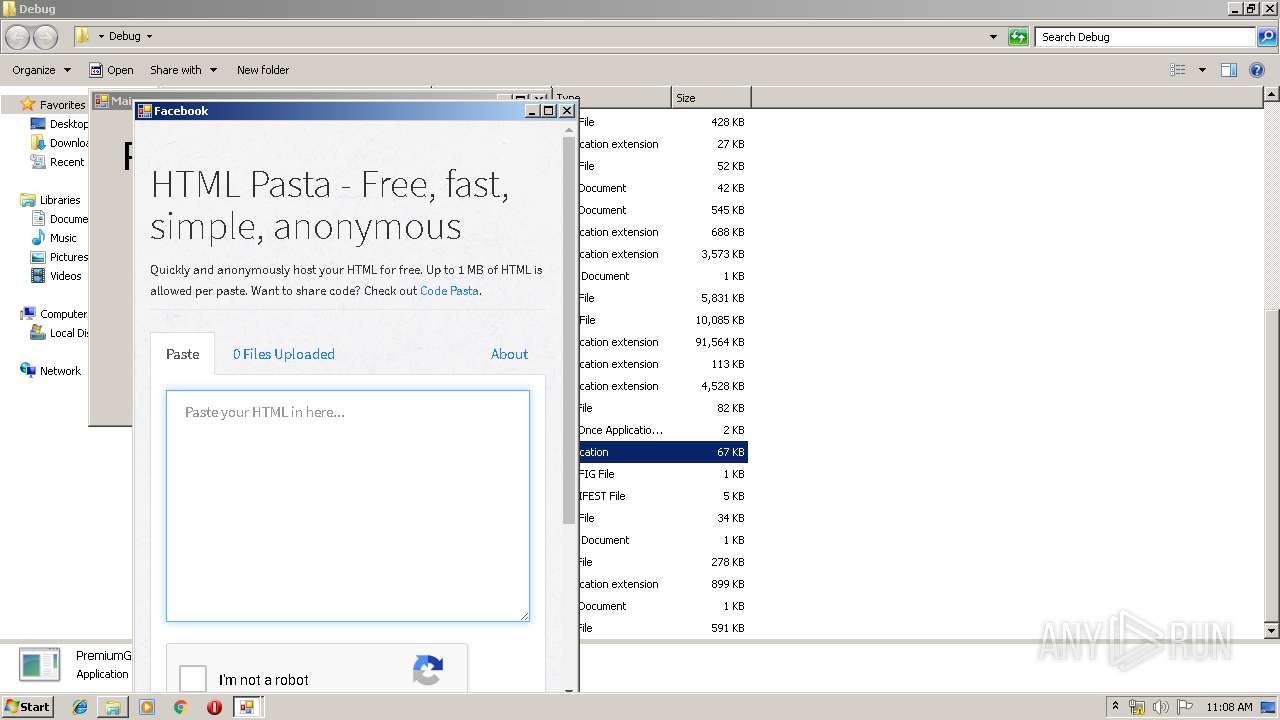
PremiumGet.exe | [0723/110717.035:INFO:CONSOLE(2)] "[OptinMonster]", source: https://a.optnmstr.com/app/js/api.min.js (2)
|
PremiumGet.exe | [0723/110804.676:INFO:CONSOLE(0)] "The connection used to load resources from https://ws-na.assoc-amazon.com used TLS 1.0 or TLS 1.1, which are deprecated and will be disabled in the future. Once disabled, users will be prevented from loading these resources. The server should enable TLS 1.2 or later. See https://www.chromestatus.com/feature/5654791610957824 for more information.", source: about:blank (0)
|
PremiumGet.exe | [0723/110804.676:INFO:CONSOLE(0)] "The connection used to load resources from https://ws-na.assoc-amazon.com used TLS 1.0 or TLS 1.1, which are deprecated and will be disabled in the future. Once disabled, users will be prevented from loading these resources. The server should enable TLS 1.2 or later. See https://www.chromestatus.com/feature/5654791610957824 for more information.", source: https://ws-na.assoc-amazon.com/widgets/cm?o=1&p=13&l=ez&f=ifr&linkID=1ee7ccc90e0b45c5ec25131a4504713f&t=pastalord-20&tracking_id=pastalord-20 (0)
|