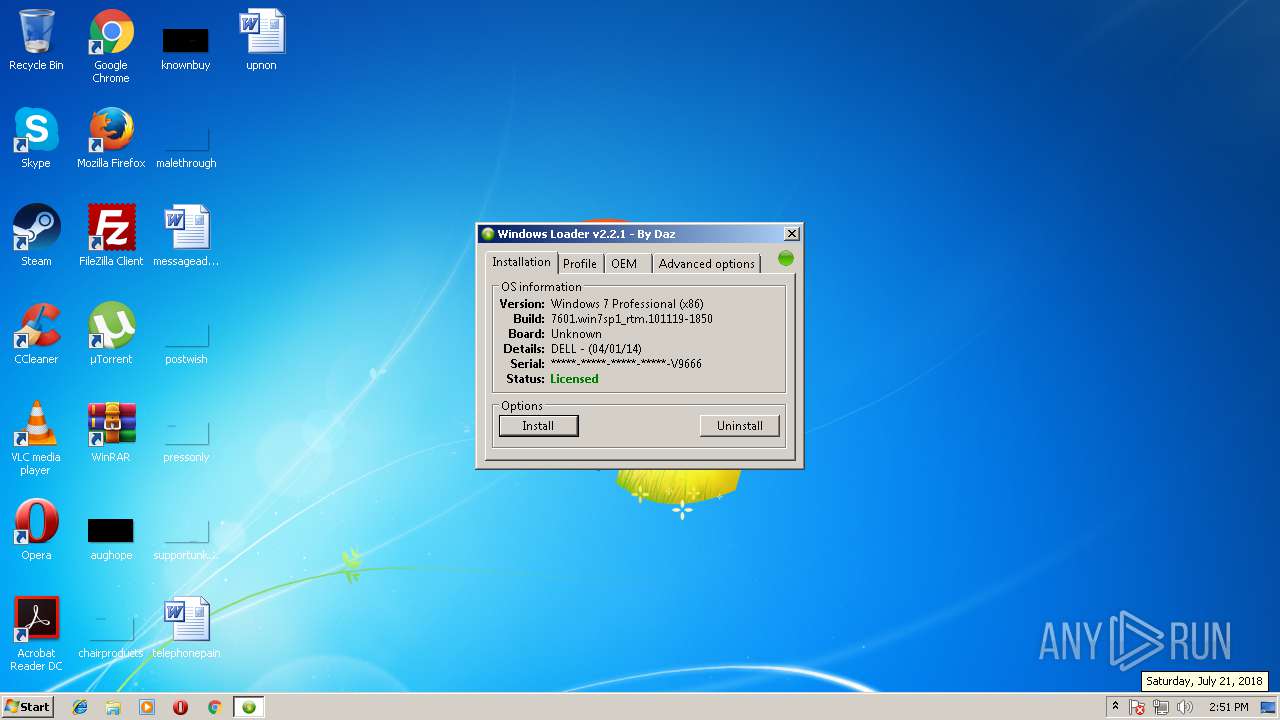
| File name: | Windows 7 Loader.exe |
| Full analysis: | https://app.any.run/tasks/0da93080-93fb-4013-adf9-49b3f924c1b9 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2018, 13:51:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 619B333FC8BE018BA8697477E29D6DBD |
| SHA1: | A92279C649E51617F6300EC52C9D7E91D79FFF6E |
| SHA256: | 36A234B133C5B7FC6A20834C795C6FD60811A54D656A538C9D6BA423383270BC |
| SSDEEP: | 49152:V2CasancJcrVamZVJUAvUF8R3/qKNN+IZWURUkS6YdQtB76N+NhdoJg/GCDMRrS5:wCasanUs |
MALICIOUS
Application was dropped or rewritten from another process
- Windows Activator.exe (PID: 4008)
- Windows Activator.exe (PID: 2316)
- Wintup.exe (PID: 2988)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2260)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2328)
SUSPICIOUS
Creates files in the user directory
- Windows 7 Loader.exe (PID: 2660)
Starts CMD.EXE for commands execution
- Windows Activator.exe (PID: 2316)
- Wintup.exe (PID: 2988)
- cmd.exe (PID: 2080)
- cmd.exe (PID: 2284)
Executable content was dropped or overwritten
- Windows 7 Loader.exe (PID: 2660)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2504)
- cmd.exe (PID: 1540)
Executes scripts
- cmd.exe (PID: 476)
- cmd.exe (PID: 3740)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:07 21:52:11+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 265216 |
| InitializedDataSize: | 7476736 |
| UninitializedDataSize: | 19968 |
| EntryPoint: | 0x1240 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.1.1 |
| ProductVersionNumber: | 3.1.1.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileVersion: | - |
| FileDescription: | Windows 7 Activator Installation |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Mar-2018 20:52:11 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileVersion: | - |
| FileDescription: | Windows 7 Activator Installation |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 07-Mar-2018 20:52:11 |
| Pointer to Symbol Table: | 0x00721A00 |
| Number of symbols: | 5611 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00040A50 | 0x00040C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09854 |
.data | 0x00042000 | 0x00000230 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.742514 |
.rdata | 0x00043000 | 0x006C3740 | 0x006C3800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.5089 |
.bss | 0x00707000 | 0x00004C80 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0070C000 | 0x00000884 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.26 |
.rsrc | 0x0070D000 | 0x0001C3B8 | 0x0001C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.40754 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.11075 | 640 | UNKNOWN | English - United States | RT_VERSION |
2 | 5.99496 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 6.1982 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 6.31303 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 6.22218 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 6.27666 | 1128 | UNKNOWN | English - United States | RT_ICON |
A | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
69
Monitored processes
24
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | cmd.exe /A /C "C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ilc "C:\Dell.XRM-MS"" | C:\Windows\system32\cmd.exe | — | Windows Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1540 | cmd.exe /A /C "icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F)" | C:\Windows\system32\cmd.exe | — | Windows Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1644 | cmd.exe /A /C "compact /u \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\CZYKN" | C:\Windows\system32\cmd.exe | — | Windows Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 2080 | cmd.exe /A /C "cmd.exe /c takeown /f C:\ldrscan\bootwin" | C:\Windows\system32\cmd.exe | — | Windows Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2188 | cmd.exe /c takeown /f C:\ldrscan\bootwin | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2260 | schtasks /create /sc onlogon /f /tn "UpdateChecker" /tr "C:\Users\admin\AppData\Roaming\Wintup.exe" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | cmd.exe /A /C "cmd.exe /c takeown /f C:\ldrscan\bootwin" | C:\Windows\system32\cmd.exe | — | Windows Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Roaming\Windows_Activator\Windows Activator.exe" | C:\Users\admin\AppData\Roaming\Windows_Activator\Windows Activator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2328 | "C:\Windows\System32\cmd.exe" /c schtasks /create /sc onlogon /f /tn "UpdateChecker" /tr "C:\Users\admin\AppData\Roaming\Wintup.exe" | C:\Windows\System32\cmd.exe | — | Wintup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2368 | takeown /f C:\ldrscan\bootwin | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
659
Read events
645
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2660) Windows 7 Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2660) Windows 7 Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4020) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4020) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2988) Wintup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2988) Wintup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | Windows 7 Loader.exe | C:\Users\admin\AppData\Roaming\Windows_Activator\Windows Activator.exe | executable | |
MD5:3976BD5FCBB7CD13F0C12BB69AFC2ADC | SHA256:BF5070EF8CF03A11D25460B3E09A479183CC0FA03D0EA32E4499998F509B1A40 | |||
| 2316 | Windows Activator.exe | C:\System Volume Information\MountPointManagerRemoteDatabase | binary | |
MD5:— | SHA256:— | |||
| 2316 | Windows Activator.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\CZYKN | binary | |
MD5:— | SHA256:— | |||
| 2316 | Windows Activator.exe | C:\Dell.XRM-MS | xml | |
MD5:18B1E45BF56F40C3C4BBE65831178216 | SHA256:D072A059D3ED3E75C98B85B41E4319E8D5CFAE0E0C239B62436A3AD34003AB4A | |||
| 2660 | Windows 7 Loader.exe | C:\Users\admin\AppData\Roaming\Wintup.exe | executable | |
MD5:B71F374128323E381618E5F1768BF128 | SHA256:817A5A1BC851977D0779CD389AA6FB06EAB96F9A42D4D2C3DE7587CFA7A3AA6A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.58:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | unknown | der | 313 b | whitelisted |
— | — | GET | 200 | 178.255.83.1:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | GB | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | Wintup.exe | 104.31.87.97:443 | megambu.pw | Cloudflare Inc | US | shared |
— | — | 178.255.83.1:80 | ocsp.trust-provider.com | CCANET Limited | GB | unknown |
— | — | 2.16.186.58:80 | ocsp.comodoca4.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
megambu.pw |
| malicious |
ocsp.trust-provider.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |