| File name: | phishing8-afe2091705f0a26aa1e76958ae713e00.eml |
| Full analysis: | https://app.any.run/tasks/06dc0d2a-8a06-4157-8528-fd8add73f102 |
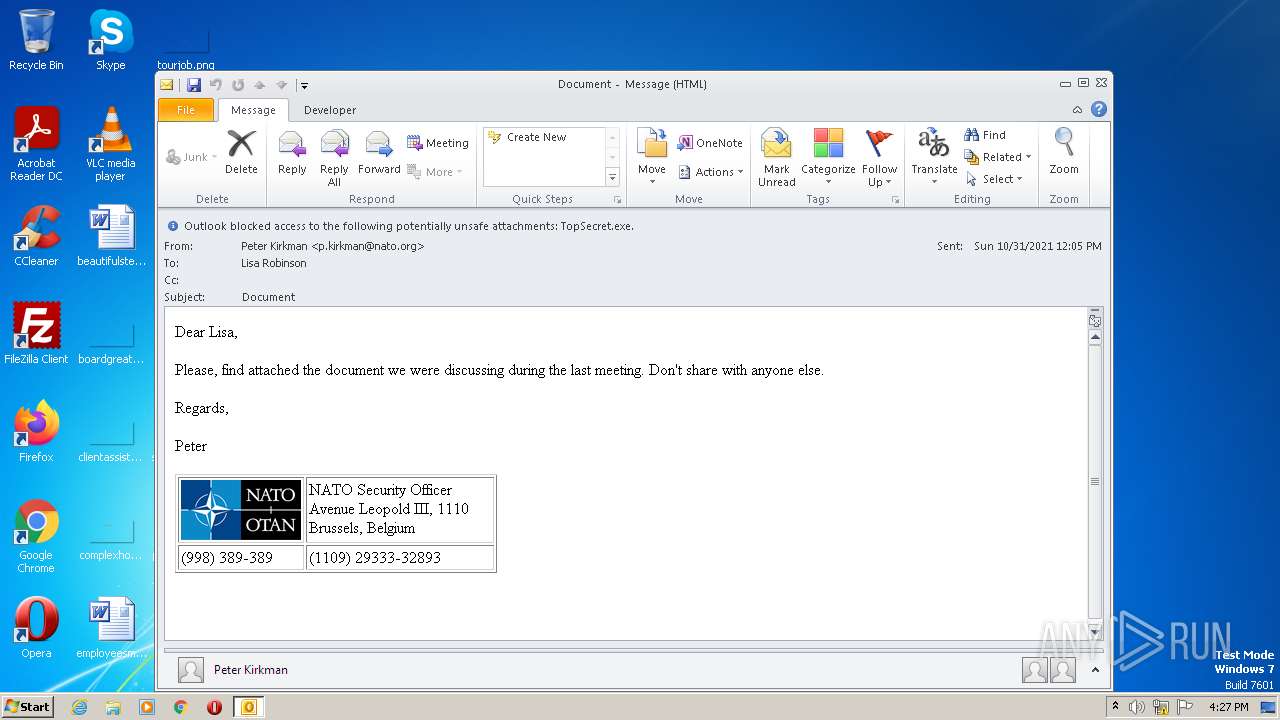
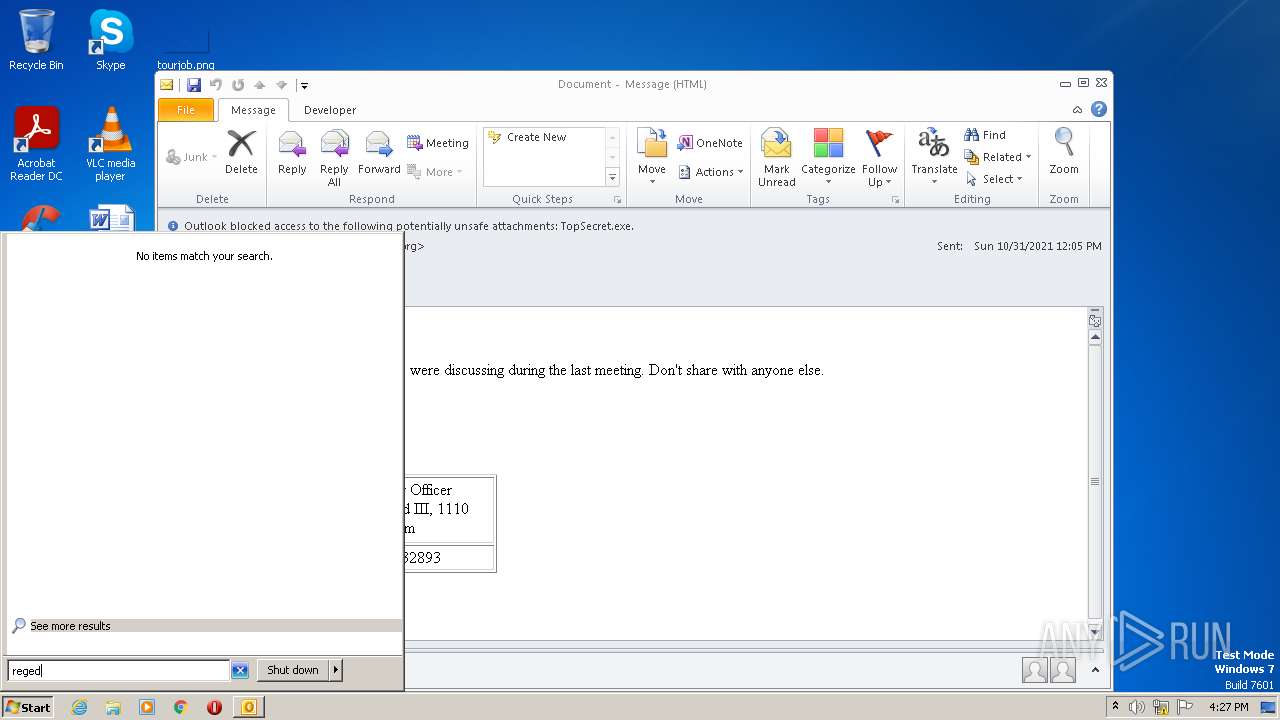
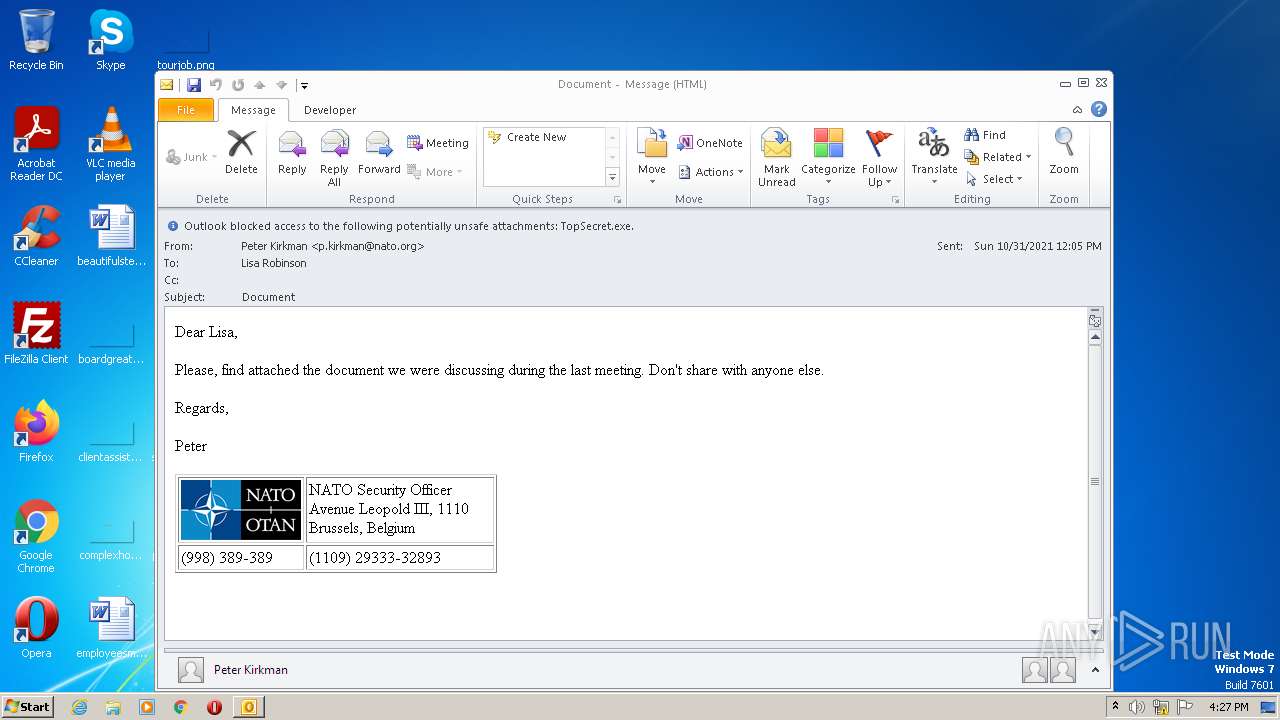
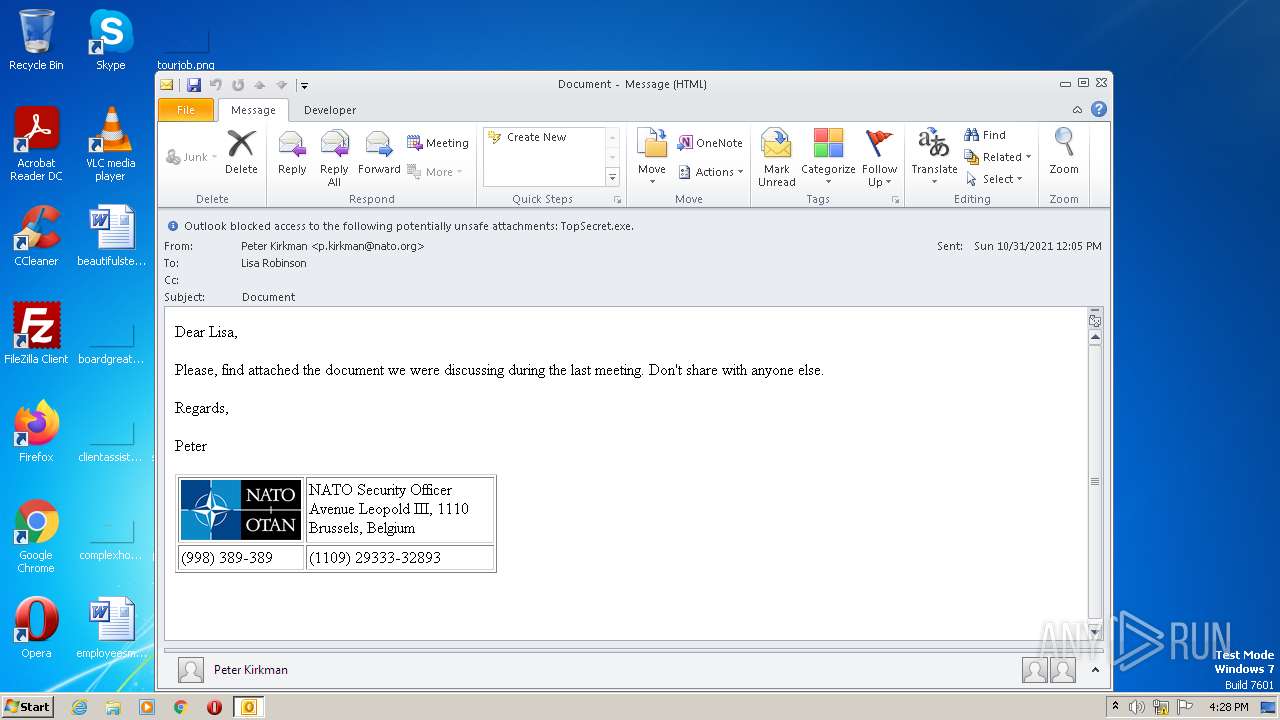
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 15:27:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | AFE2091705F0A26AA1E76958AE713E00 |
| SHA1: | 2204CF36A23F1CE9684FE3CF8DA2B6FD53C0D67D |
| SHA256: | 369EF820AFED1705822B91057C8EE67BAD02A4B3836978FE172D03F4111E73DC |
| SSDEEP: | 49152:yNb5ZjGPQ4fe8XA441UO8CroU/v9hIoQcYm4:b |
MALICIOUS
No malicious indicators.SUSPICIOUS
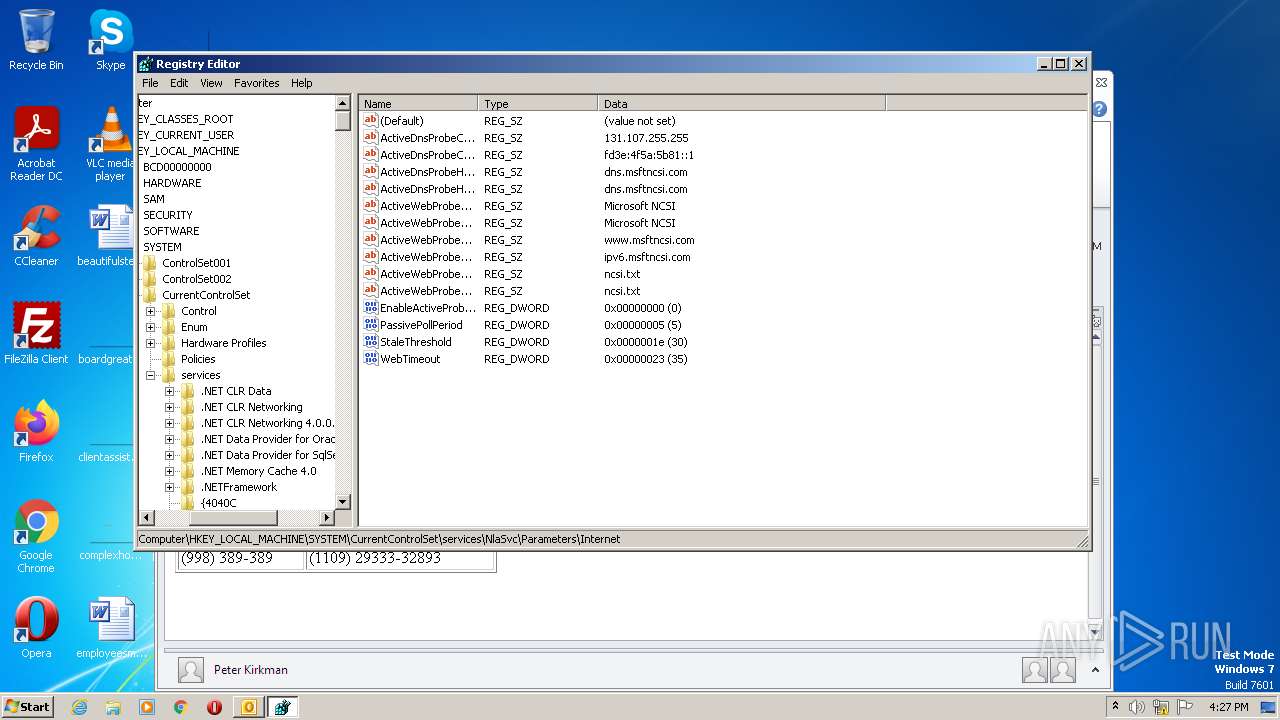
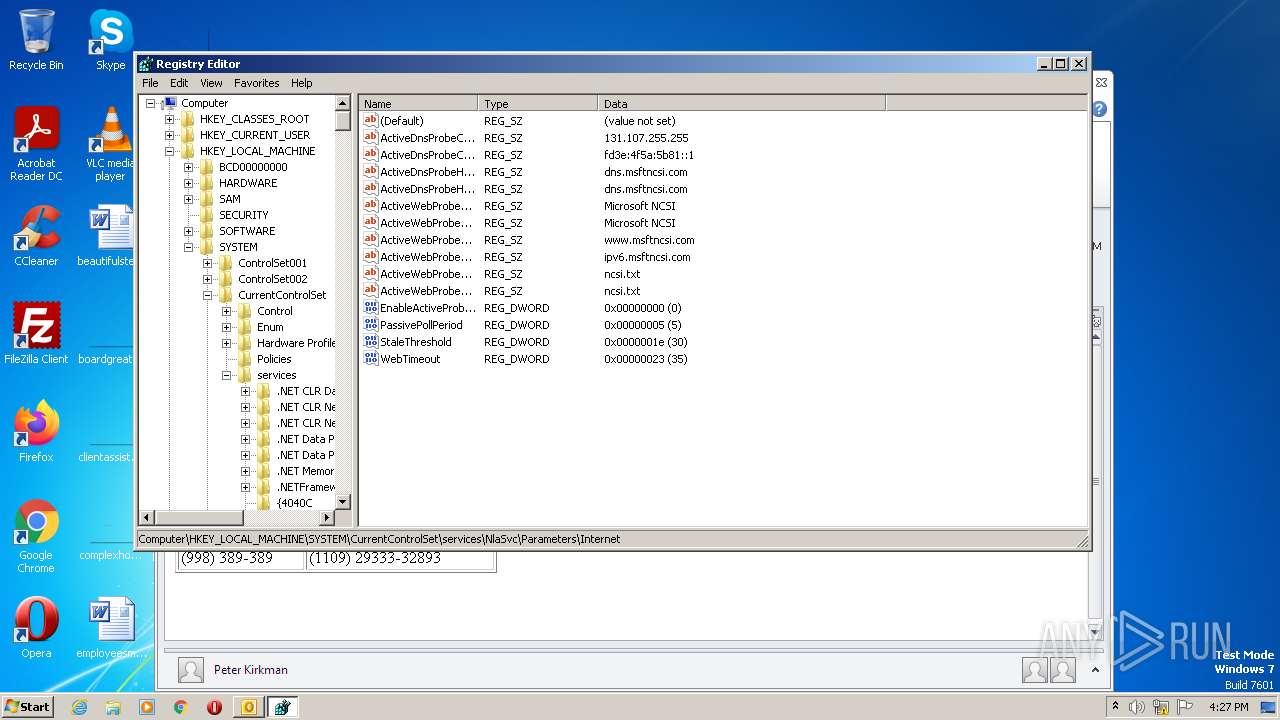
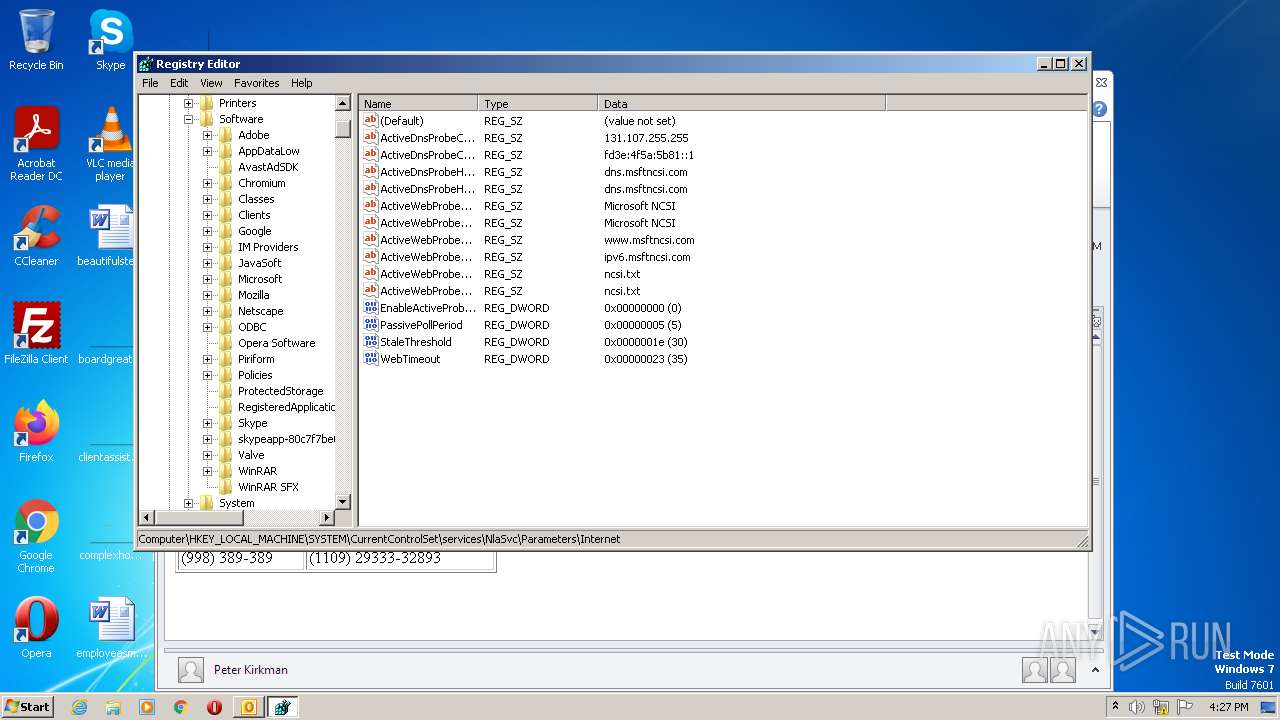
Searches for installed software
- OUTLOOK.EXE (PID: 2512)
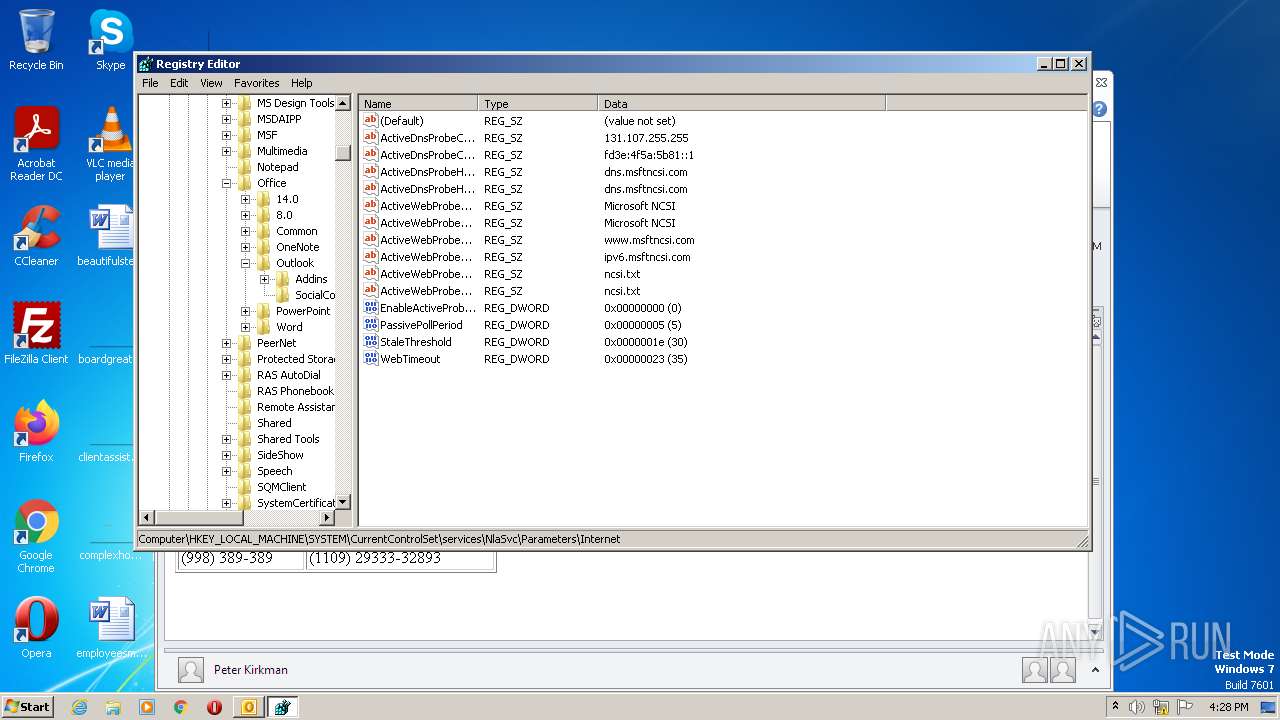
Reads the Internet Settings
- OUTLOOK.EXE (PID: 2512)
INFO
Create files in a temporary directory
- OUTLOOK.EXE (PID: 2512)
Reads the computer name
- OUTLOOK.EXE (PID: 2512)
The process checks LSA protection
- OUTLOOK.EXE (PID: 2512)
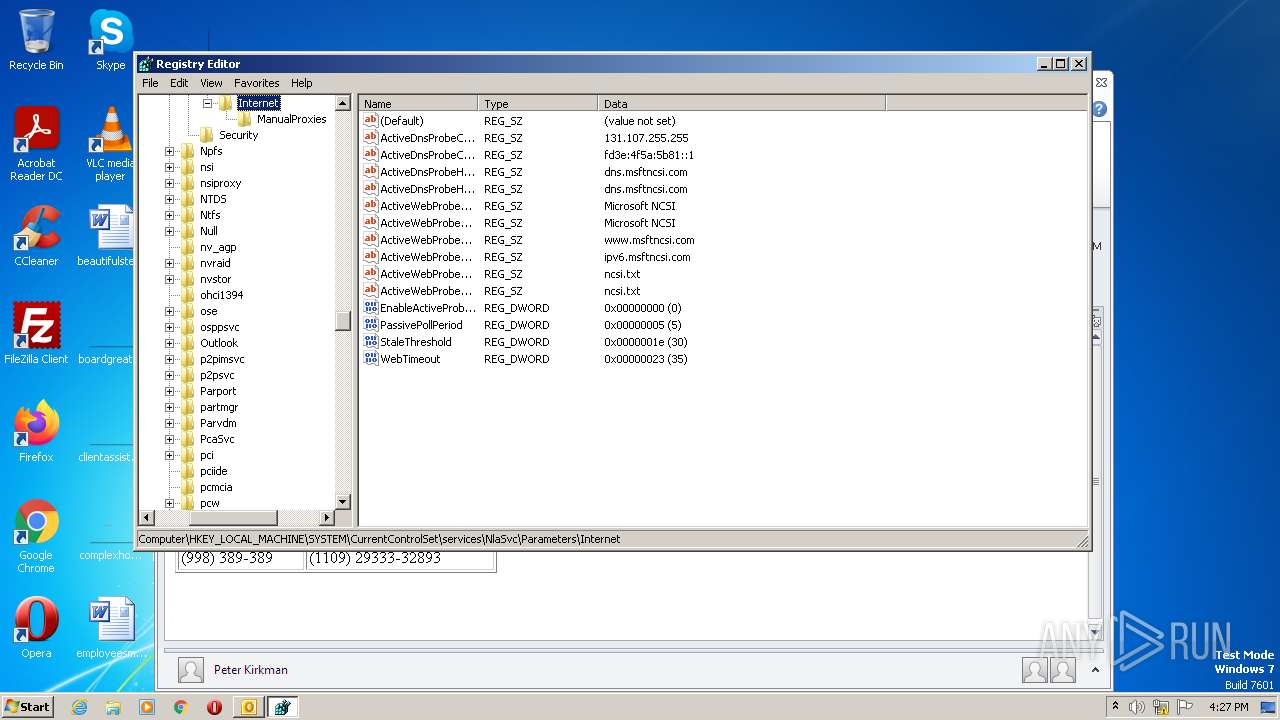
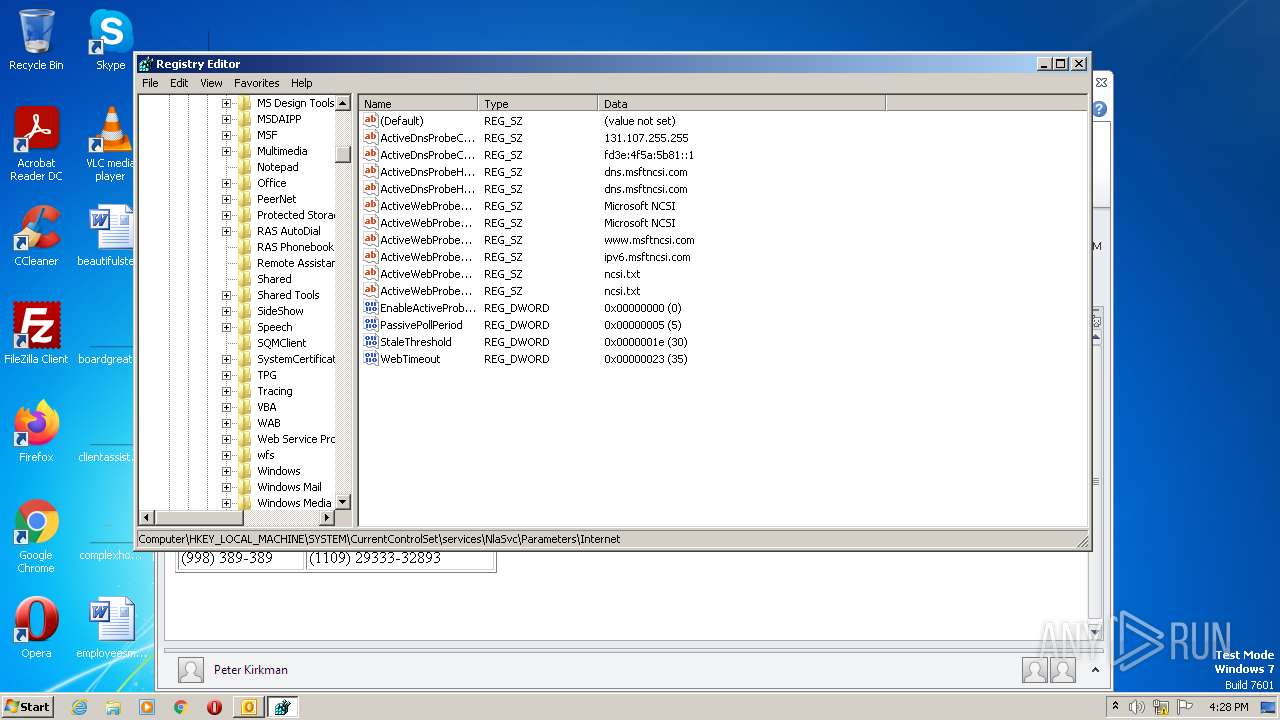
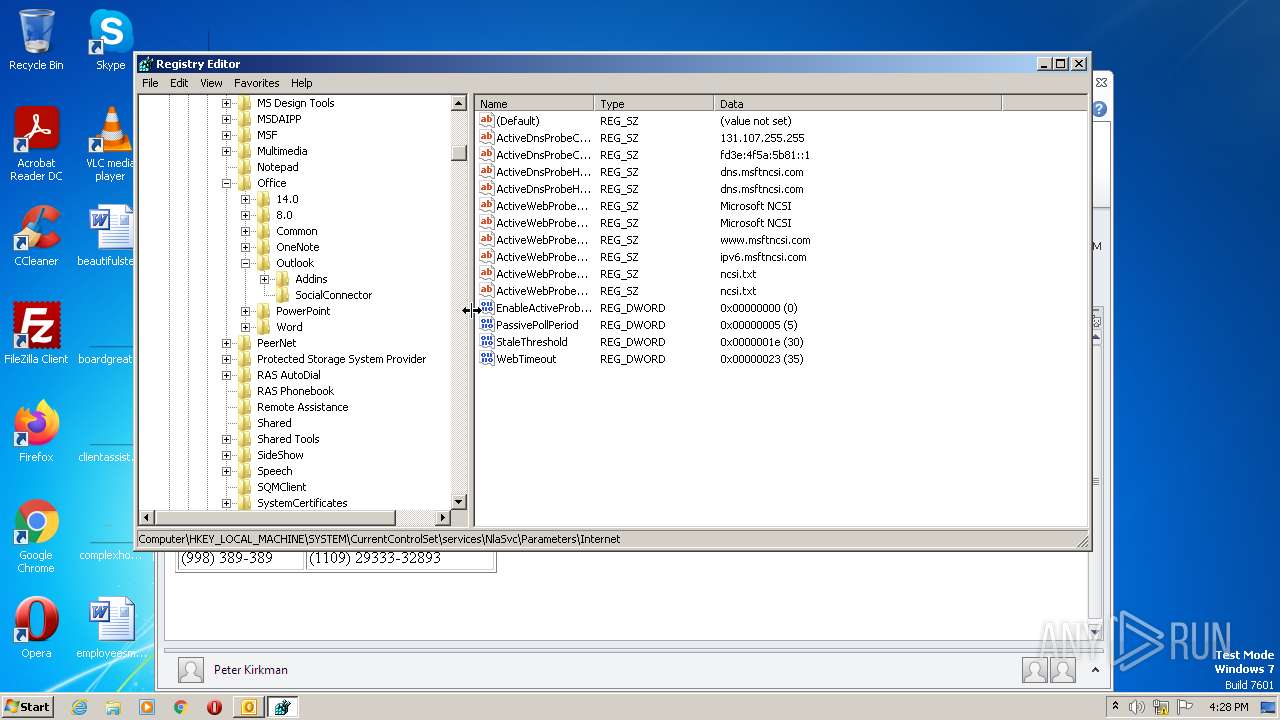
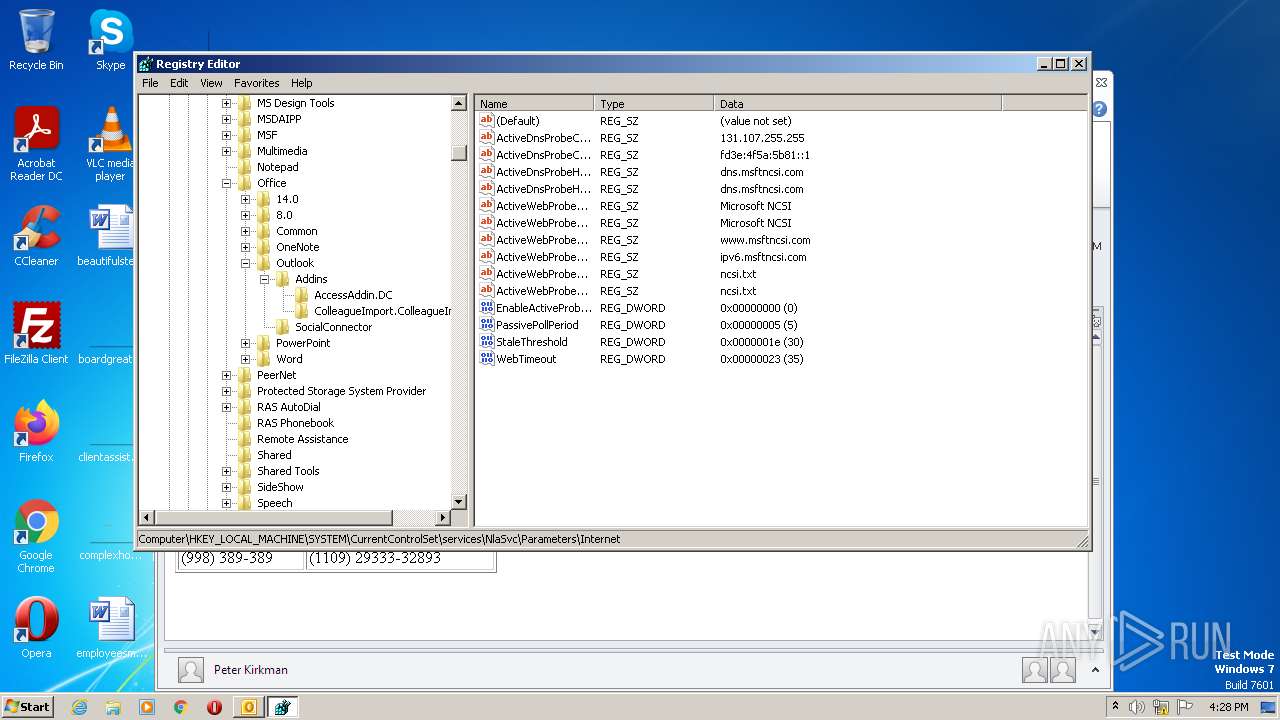
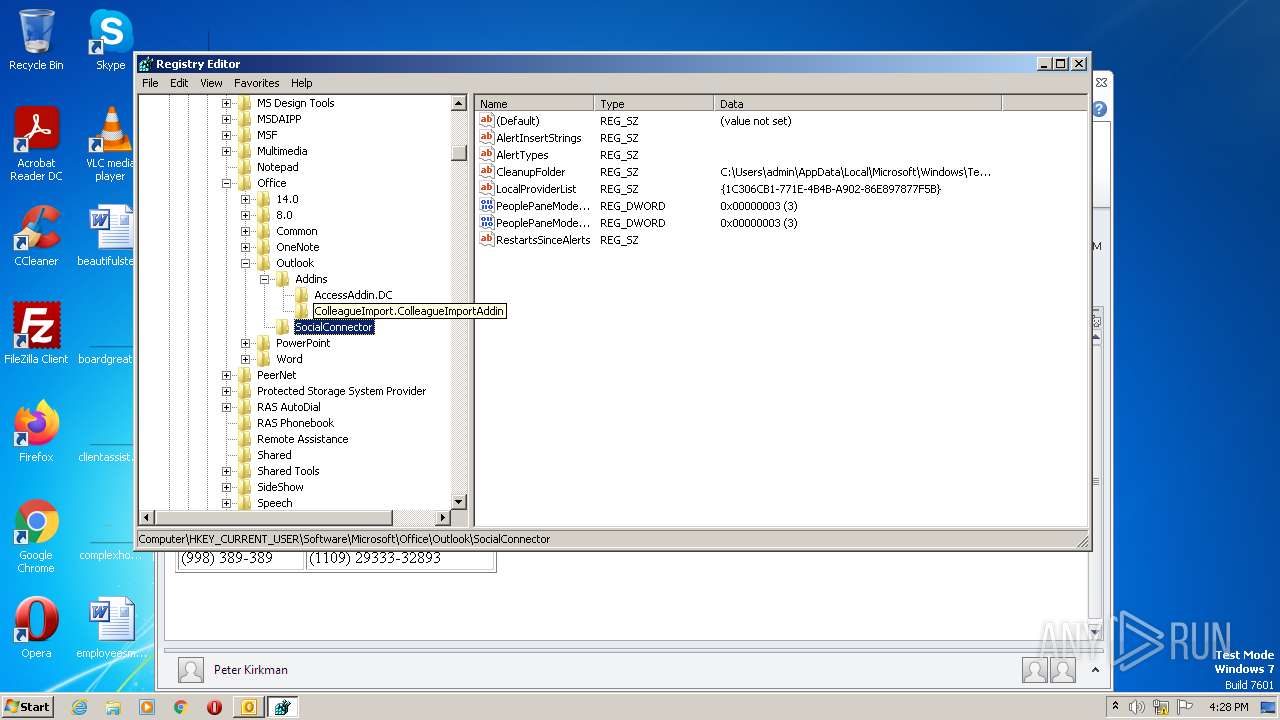
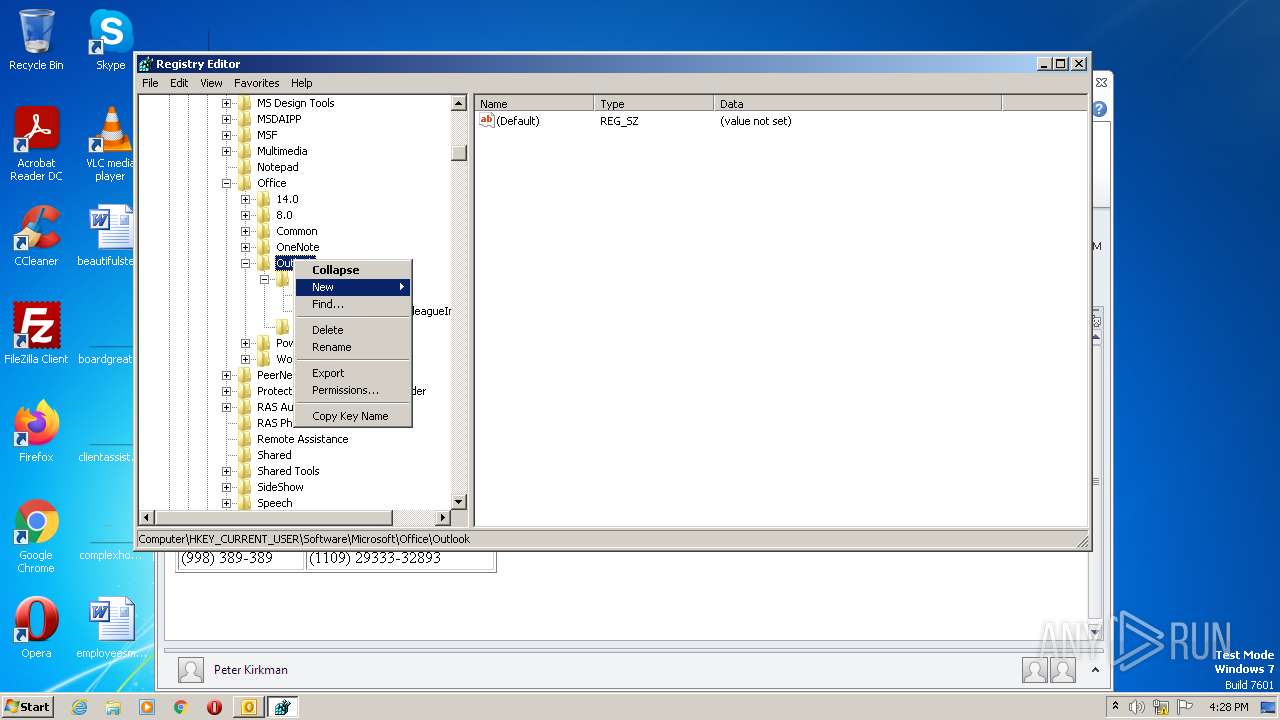
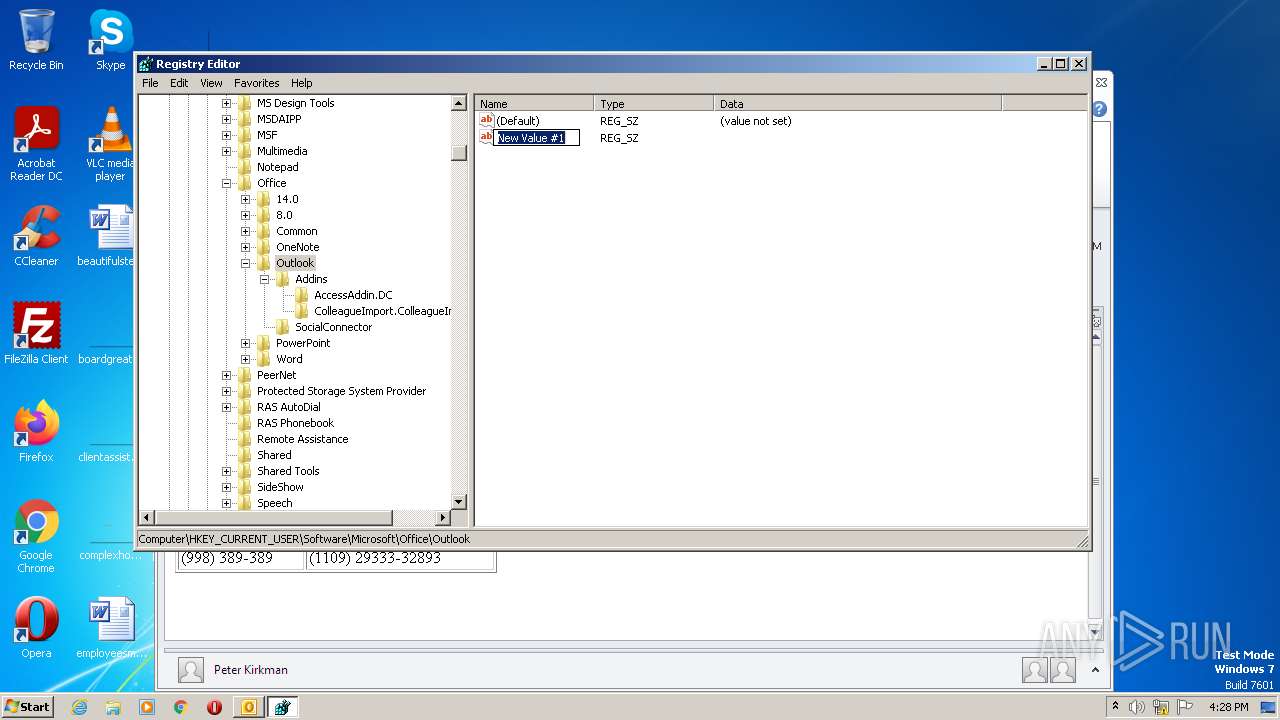
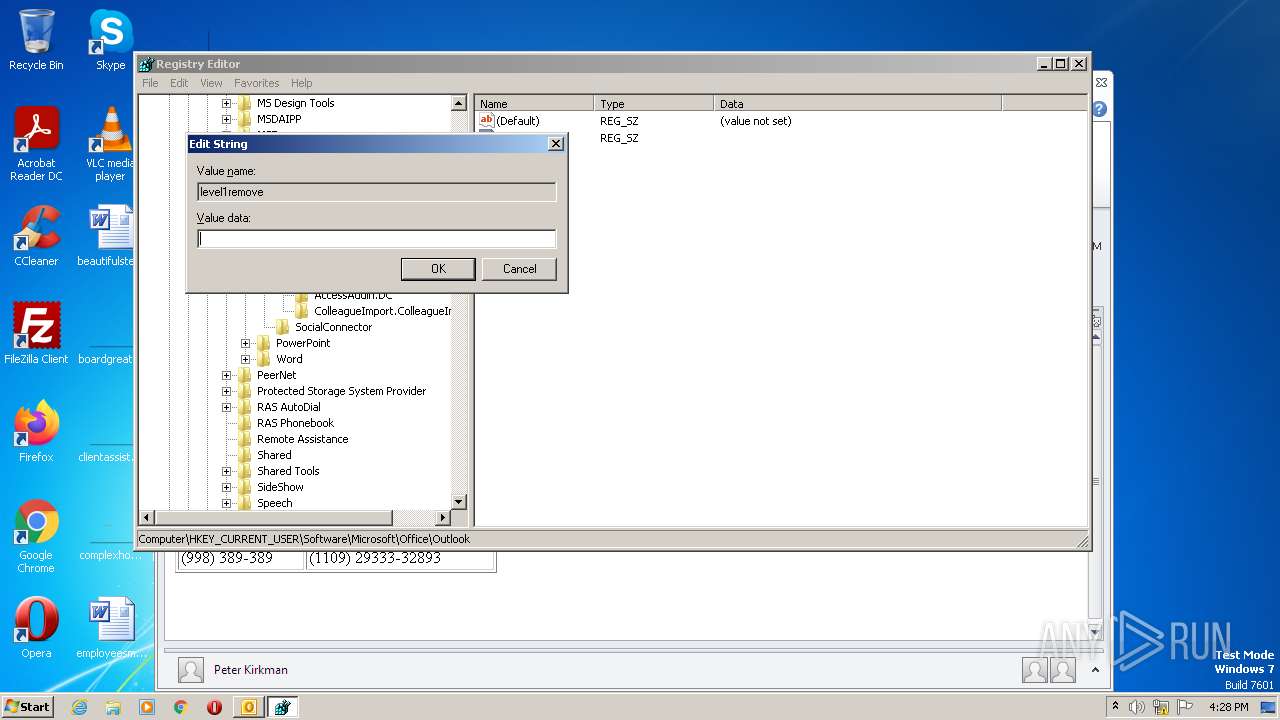
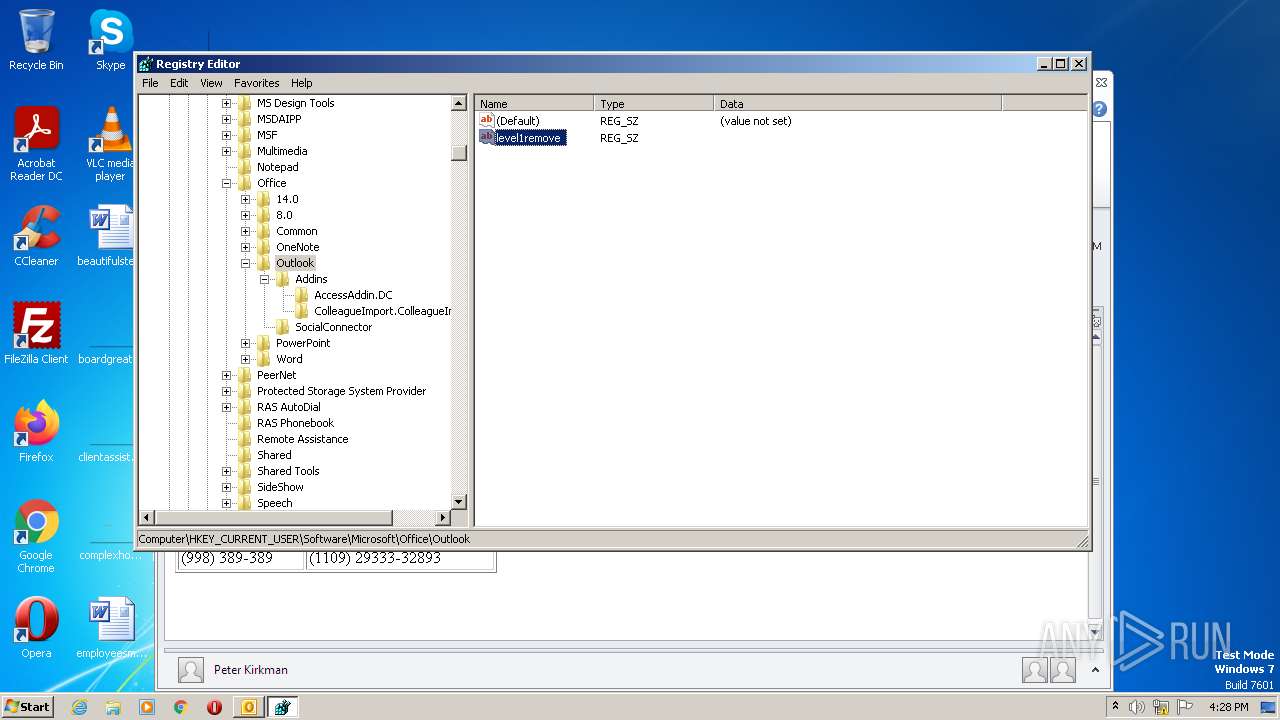
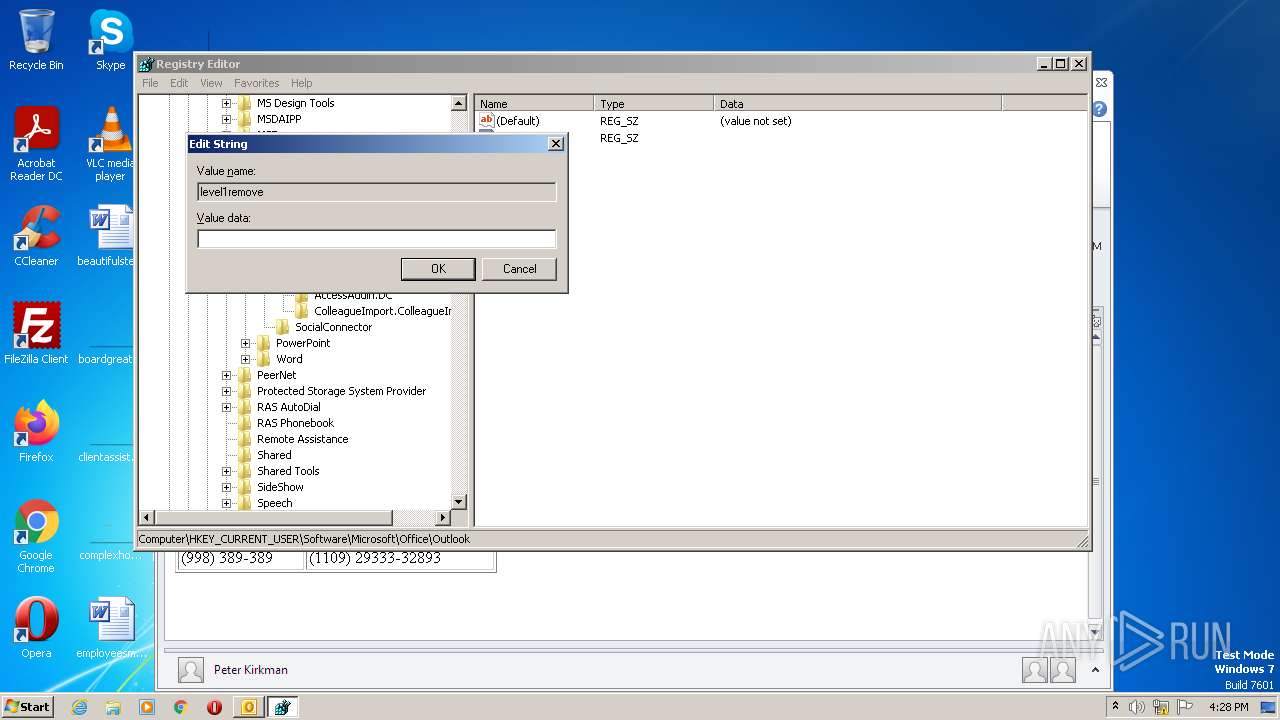
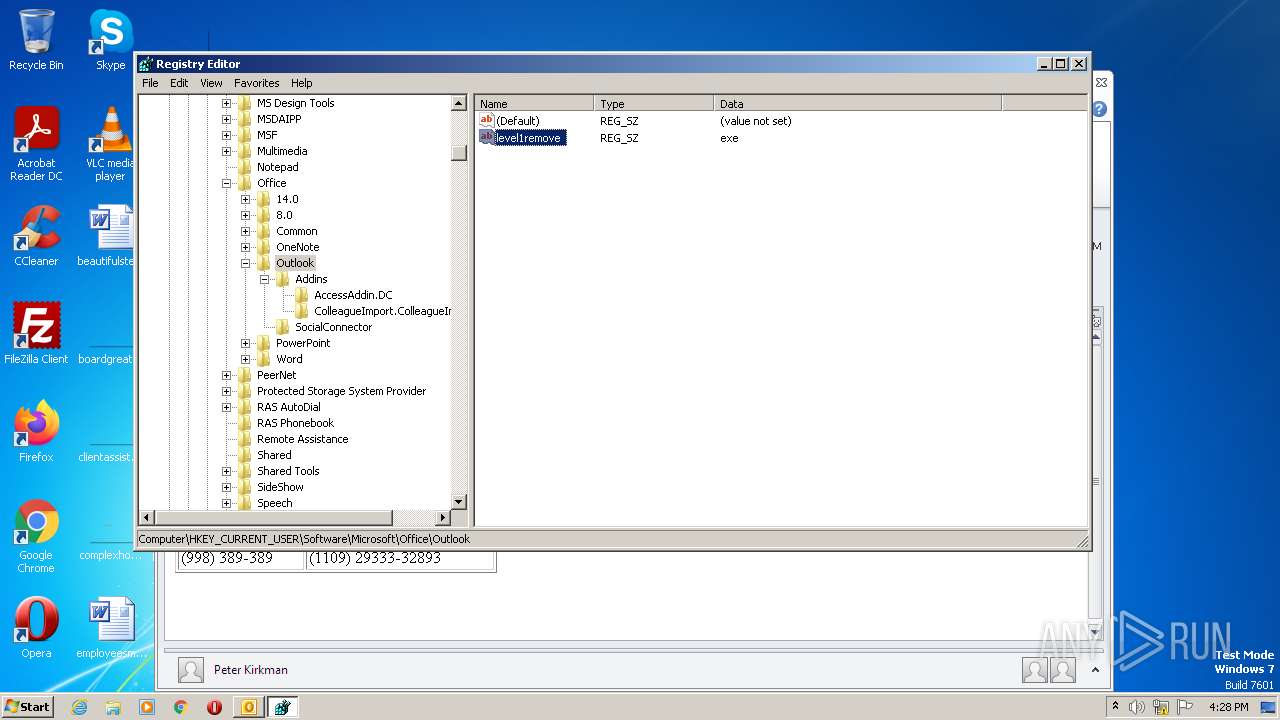
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2512)
- regedit.exe (PID: 3540)
Checks supported languages
- OUTLOOK.EXE (PID: 2512)
Process checks computer location settings
- OUTLOOK.EXE (PID: 2512)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2512)
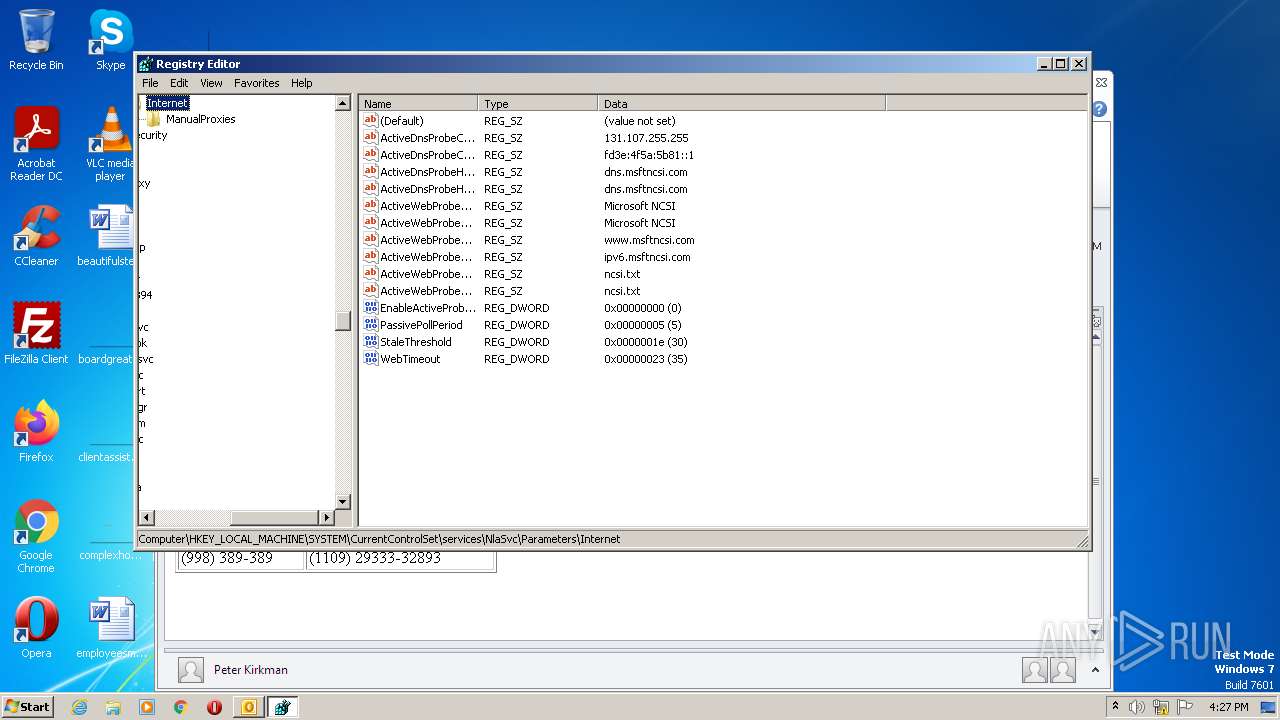
Checks proxy server information
- OUTLOOK.EXE (PID: 2512)
Manual execution by a user
- regedit.exe (PID: 900)
- regedit.exe (PID: 3540)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 2512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\phishing8-afe2091705f0a26aa1e76958ae713e00.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3540 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 616
Read events
7 844
Write events
732
Delete events
40
Modification events
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (2512) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
12
Text files
22
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF638.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{320F3D50-1C9D-4AAA-952E-BDBF50563789}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~WRD0000.tmp | document | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Outlook\NoMail.srs | srs | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\NormalEmail.dotm | document | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | binary | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2512 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_920BF5E299ED894D9FE17619CCD197E7.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2512 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |