| File name: | Fortect.exe |
| Full analysis: | https://app.any.run/tasks/67507893-673c-42d8-903a-e29f26360f1c |
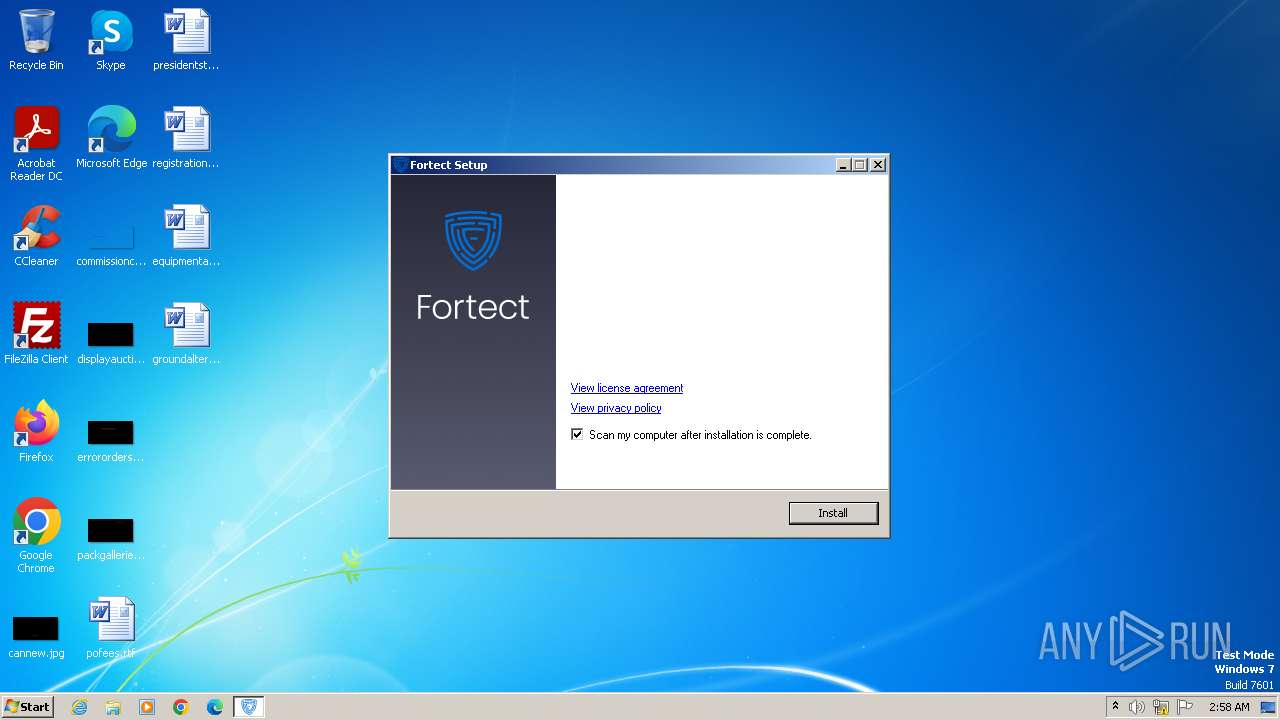
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 02:58:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 97EFEED6FABC973A25FCD0F30BCD3501 |
| SHA1: | D66FCBD6F014F0BC277A0E012EA1D457BB01D352 |
| SHA256: | 368A2DF3827AABEE0802B118E5C6077970399A33C58AE68AA4B6534E989ADA20 |
| SSDEEP: | 24576:WJ8RjOjN19zYDV+Wt61fRacruQ7LyH7eVN:WJ8R6jN19zYDVJt61fRacruQ7LybeVN |
MALICIOUS
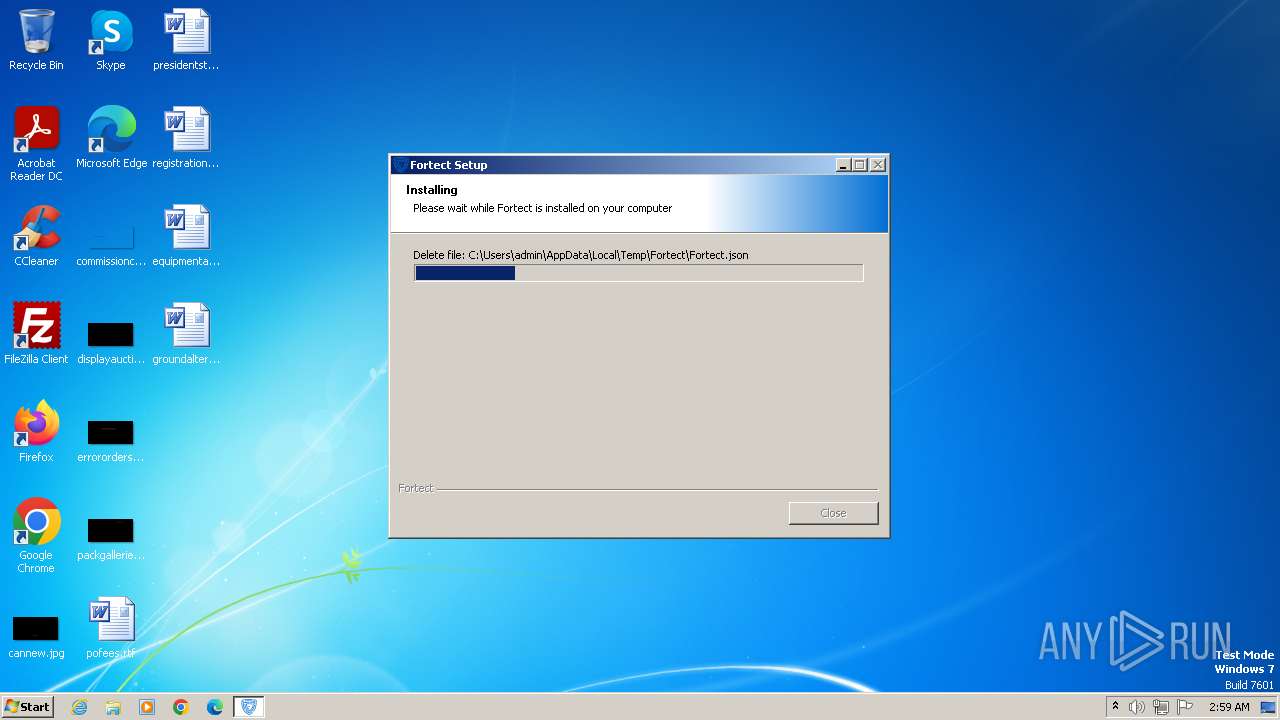
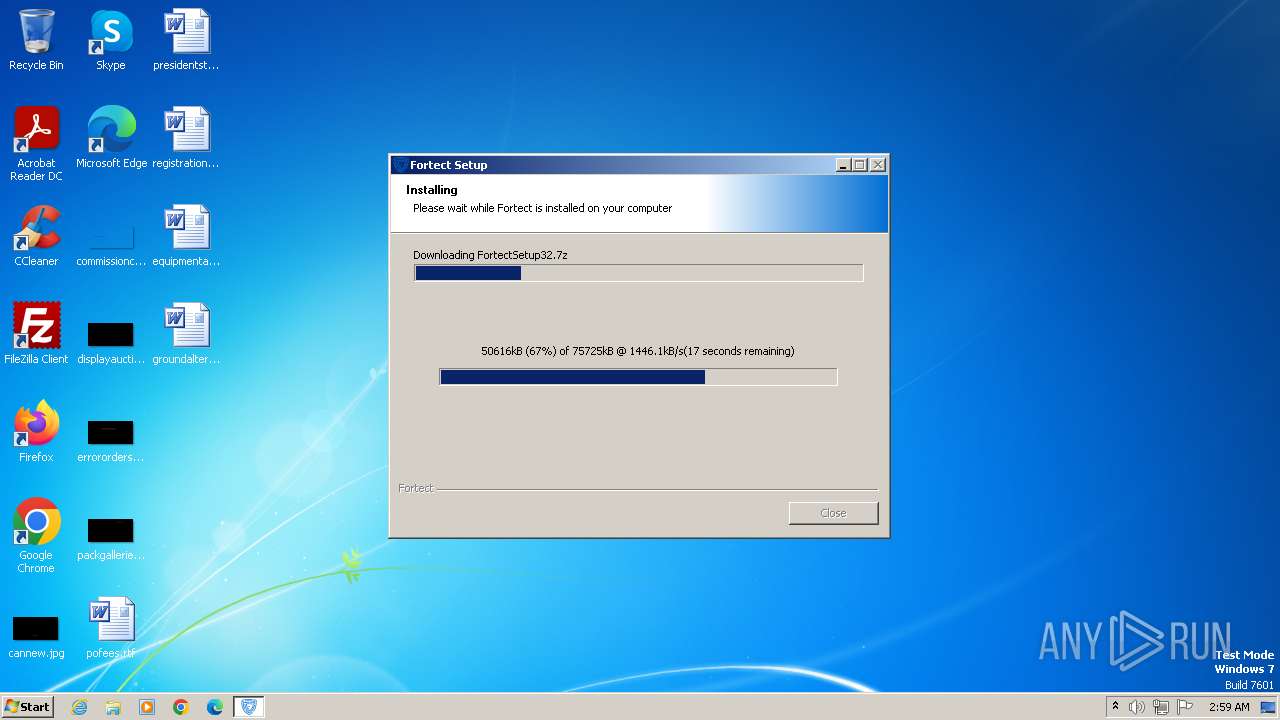
Drops the executable file immediately after the start
- Fortect.exe (PID: 2684)
SUSPICIOUS
The process creates files with name similar to system file names
- Fortect.exe (PID: 2684)
Starts CMD.EXE for commands execution
- Fortect.exe (PID: 2684)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 2308)
Reads the Internet Settings
- WMIC.exe (PID: 1900)
- WMIC.exe (PID: 3136)
- WMIC.exe (PID: 3160)
- WMIC.exe (PID: 1936)
- Fortect.exe (PID: 2684)
Uses WMIC.EXE to obtain data on the partitioned areas of a physical disk
- Fortect.exe (PID: 2684)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 3136)
Uses WMIC.EXE to obtain physical disk drive information
- Fortect.exe (PID: 2684)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2336)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 1936)
Checks Windows Trust Settings
- Fortect.exe (PID: 2684)
Reads security settings of Internet Explorer
- Fortect.exe (PID: 2684)
Reads settings of System Certificates
- Fortect.exe (PID: 2684)
INFO
Checks supported languages
- Fortect.exe (PID: 2684)
- wmpnscfg.exe (PID: 2896)
Create files in a temporary directory
- Fortect.exe (PID: 2684)
Reads the computer name
- Fortect.exe (PID: 2684)
- wmpnscfg.exe (PID: 2896)
Reads Environment values
- Fortect.exe (PID: 2684)
Reads the machine GUID from the registry
- Fortect.exe (PID: 2684)
- wmpnscfg.exe (PID: 2896)
Checks proxy server information
- Fortect.exe (PID: 2684)
Creates files or folders in the user directory
- Fortect.exe (PID: 2684)
Manual execution by a user
- wmpnscfg.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 23:56:47+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.0.3 |
| ProductVersionNumber: | 6.0.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Fortect |
| FileDescription: | Fortect Setup |
| FileVersion: | 6.0.0.3 |
| InternalName: | Fortect.exe |
| LegalCopyright: | © Fortect |
| LegalTrademarks: | © Fortect |
| OriginalFileName: | Fortect.exe |
| ProductName: | Fortect |
| ProductVersion: | 6.0.0.3 |
Total processes
53
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1900 | C:\Windows\System32\wbem\wmic.exe path Win32_BIOS get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | C:\Windows\System32\wbem\wmic.exe path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_BIOS get SerialNumber | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\AppData\Local\Temp\Fortect.exe" | C:\Users\admin\AppData\Local\Temp\Fortect.exe | explorer.exe | ||||||||||||
User: admin Company: Fortect Integrity Level: HIGH Description: Fortect Setup Exit code: 0 Version: 6.0.0.3 Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\Temp\Fortect.exe" | C:\Users\admin\AppData\Local\Temp\Fortect.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortect Integrity Level: MEDIUM Description: Fortect Setup Exit code: 3221226540 Version: 6.0.0.3 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\Windows\system32\wbem\wmic.exe" logicaldisk where "DeviceID='C:'" ASSOC /assocclass:Win32_LogicalDiskToPartition | C:\Windows\System32\wbem\WMIC.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3160 | "C:\Windows\system32\wbem\wmic.exe" diskdrive where "DeviceID like '%%PHYSICALDRIVE0'" get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 903
Read events
6 876
Write events
24
Delete events
3
Modification events
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2684) Fortect.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2896) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{4C4AFF0F-0EEB-41B9-BB19-06644BDDFE1D}\{ED130A6A-2A23-461E-B4B7-FEDD0B73B674} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
10
Suspicious files
8
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\Crypto.dll | executable | |
MD5:5F8DDDD0537CF9D33230C5F690C0ECA0 | SHA256:09140B70AA226CCD3C4EB0EA5DB056E4774004A96B4A32EEB1E51ECD799FDAEA | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:ECCDEDCEF2F818C7B63CD67A690C0E4C | SHA256:B32B4E7A1DA4BA13EF3AD297ED7F9C4C9871C61F5E5F034F4334D6C185CB5518 | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\UserInfo.dll | executable | |
MD5:921AE5351F80D55CCE56054622F5ADD9 | SHA256:EAEB1C53743C3540DBAACEEAB03A57A0F16D43BE593D87E16A5695298205AD04 | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\Banner.dll | executable | |
MD5:F26199DD8E7CC2B8746F686B8546ACDE | SHA256:140A563D234E73FFEE1EE3C2C76AE03D4966F57B7E4363622C002709EB8495CE | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:387963DCE3243463F11714A651C83AC2 | SHA256:FF731A381231E2495AB9AB5E3EE985595F599A1FA51DE665E36A000EBDD01939 | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\LogEx.dll | executable | |
MD5:065130BD4BC3B4D769FFB0050A5464D0 | SHA256:568871B5048CF3E9A9C200C6527938FC616139353E084C43D283F96BA16B4EBB | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:661823414EF3B0A5C8EBF1316B2AF0B7 | SHA256:92FC9A2FB09A7BC7D12B8001736CFA88B9DC545FC07EC732DAE0CA706FCB1165 | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\nsProcess.dll | executable | |
MD5:92E43D9E657A2366B412475683AD7B07 | SHA256:1093622EA8E01F5614F343603D8C622193EAFA5B35773E5BD2C2DC0911F22A48 | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\INetC.dll | executable | |
MD5:9F3C809A6F525A8EF0C981C84113560E | SHA256:4D7A2D9151E02B971F38D10FFE8937F34227AD5A2CE11E7879DF094482DECA72 | |||
| 2684 | Fortect.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5Y49MEIG.txt | text | |
MD5:1EDE27CF4E3E656438EDC48BE0A929B4 | SHA256:39724C3A5D3467C32DB0561F213536D4D16D1959C188E4C664A12D86A064F4A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2684 | Fortect.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
1080 | svchost.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?60b2f43ad8cf70d9 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?049ef7e64aa6ea1a | unknown | compressed | 61.6 Kb | unknown |
2684 | Fortect.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?94fdaa8127c2a93a | unknown | compressed | 4.66 Kb | unknown |
2684 | Fortect.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2684 | Fortect.exe | 104.26.3.16:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
2684 | Fortect.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
2684 | Fortect.exe | 142.250.185.163:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1080 | svchost.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.fortect.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
cloud.fortect.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2684 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2684 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |