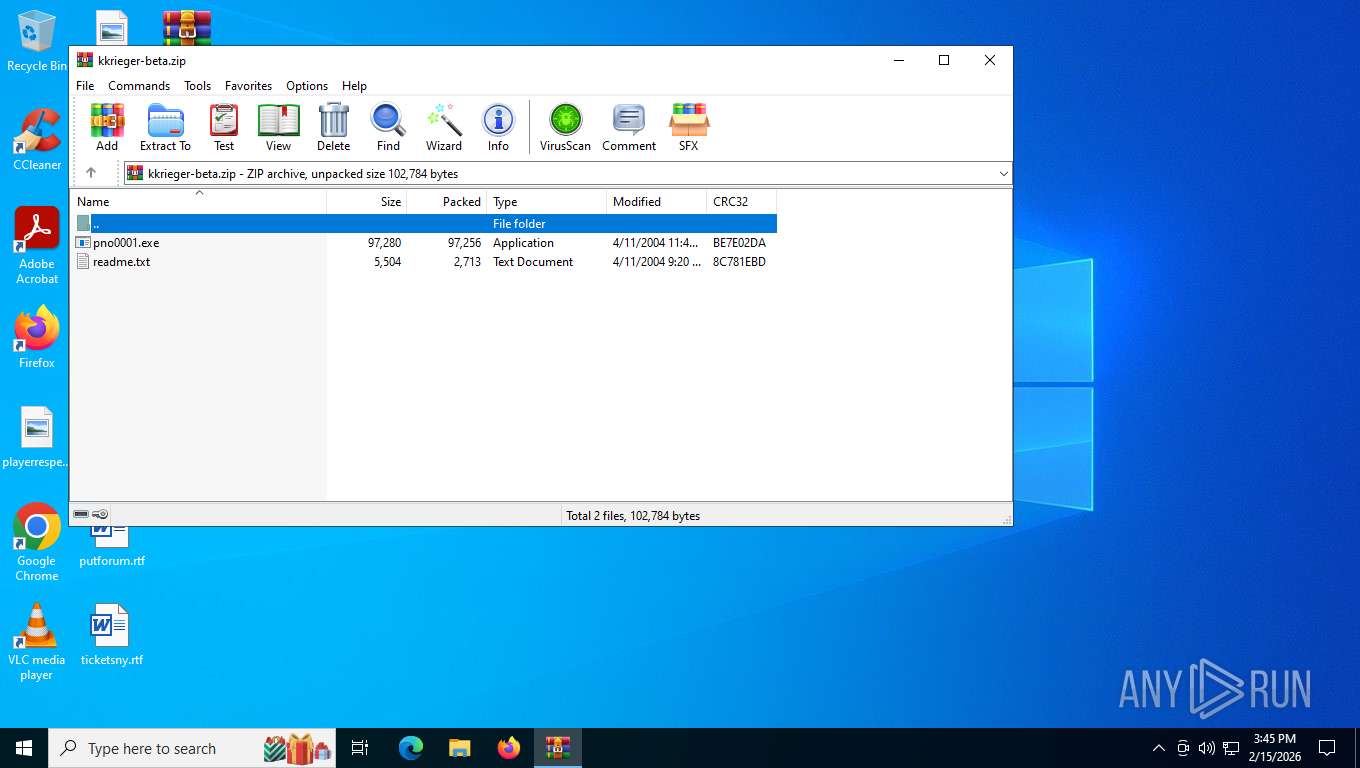
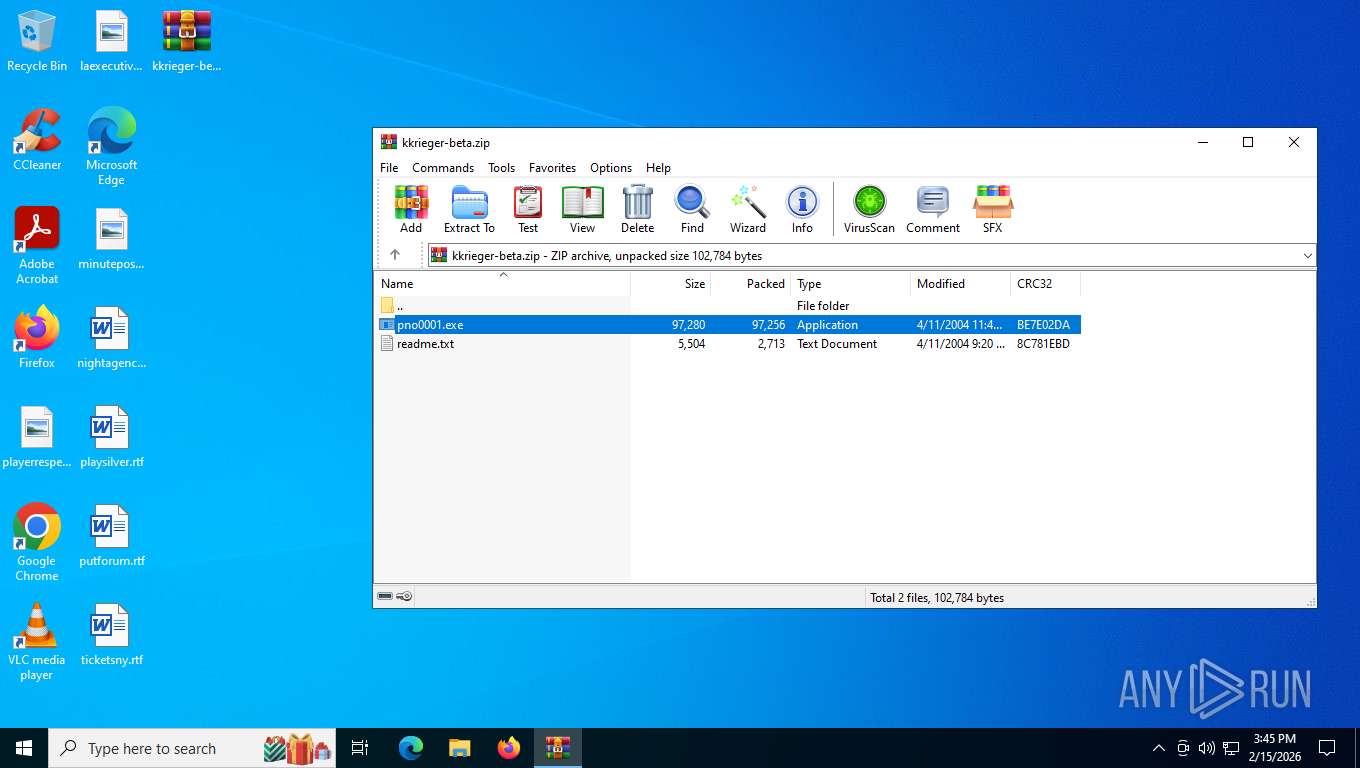
| File name: | kkrieger-beta.zip |
| Full analysis: | https://app.any.run/tasks/7060d380-30cf-44f8-8bf3-a694885faaed |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2026, 20:45:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
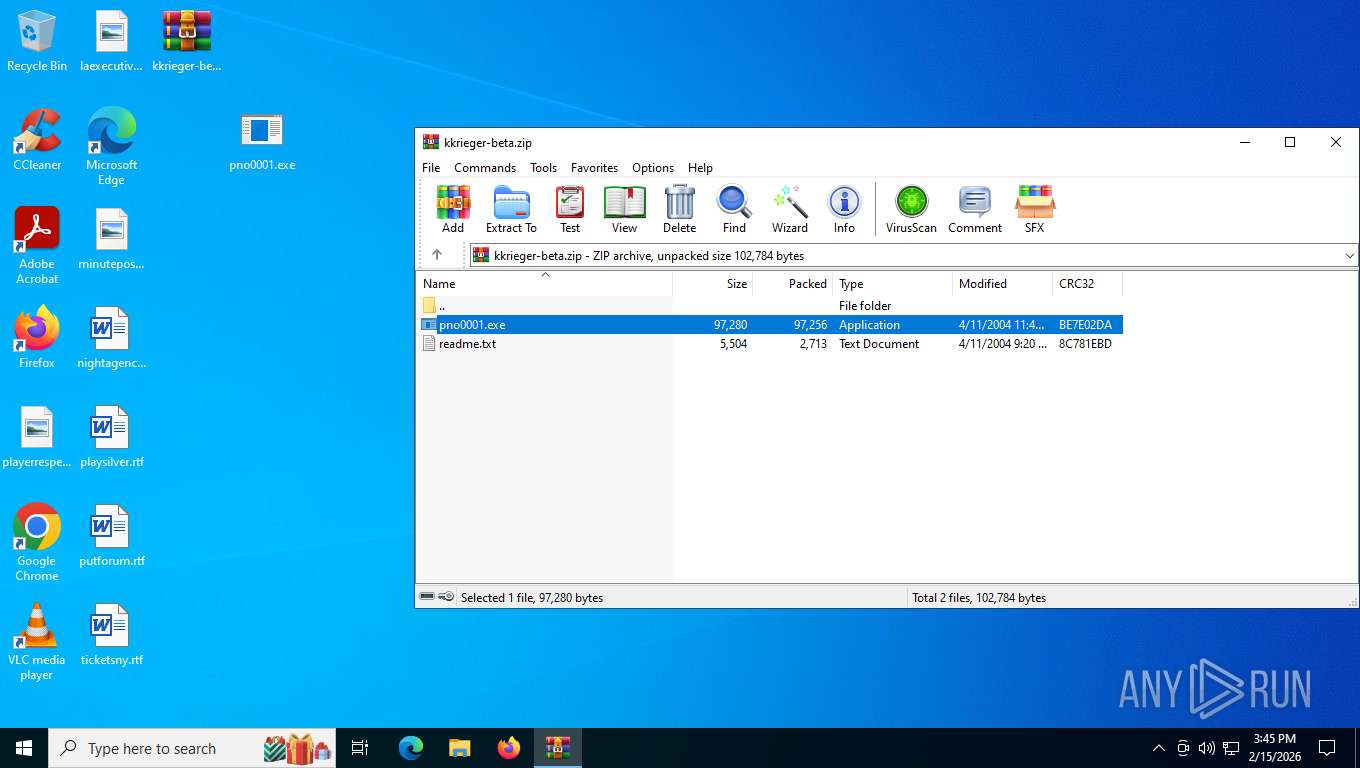
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5798F6ACB9910D3E0CC42816EEC514A0 |
| SHA1: | 987959E7CC59071C9733A80AC4D3DAA42C67473A |
| SHA256: | 367F28C37B8B4ED006205DCBDEAE825E5341671D4B8F610DB22C071ACA379445 |
| SSDEEP: | 3072:UaXJD9xT6qPRcoOHHbu1HiYPPMYXAbWLaMaGgcZY:pXJraFnbCPNXAWLaTUe |
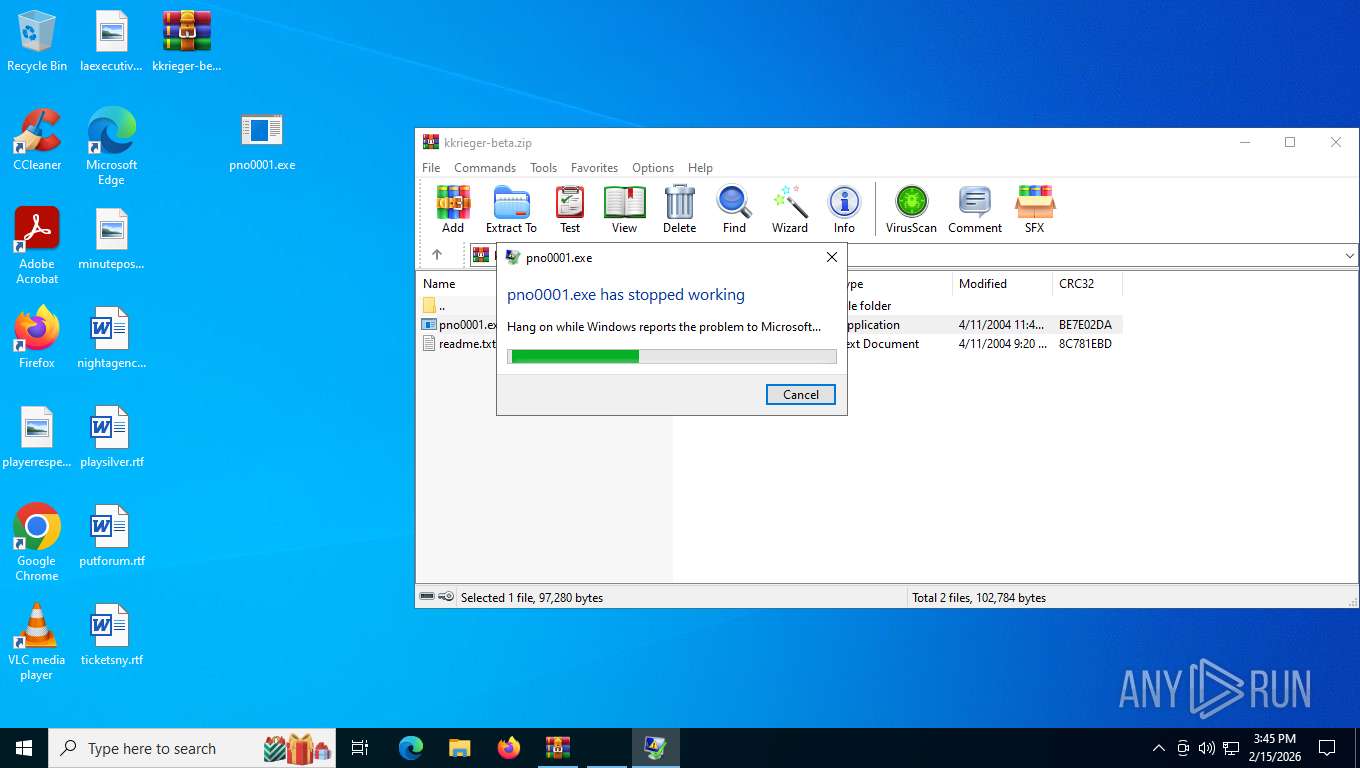
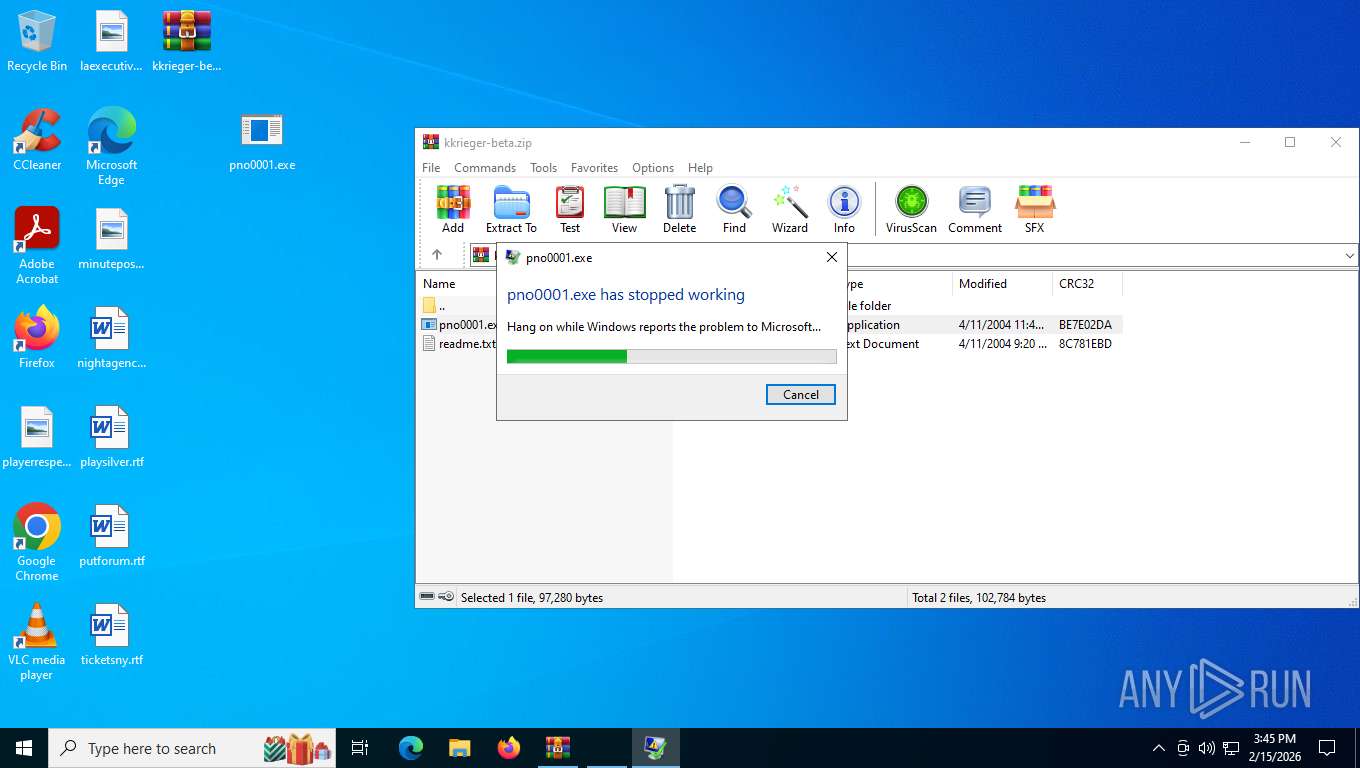
MALICIOUS
Application was injected by another process
- csrss.exe (PID: 652)
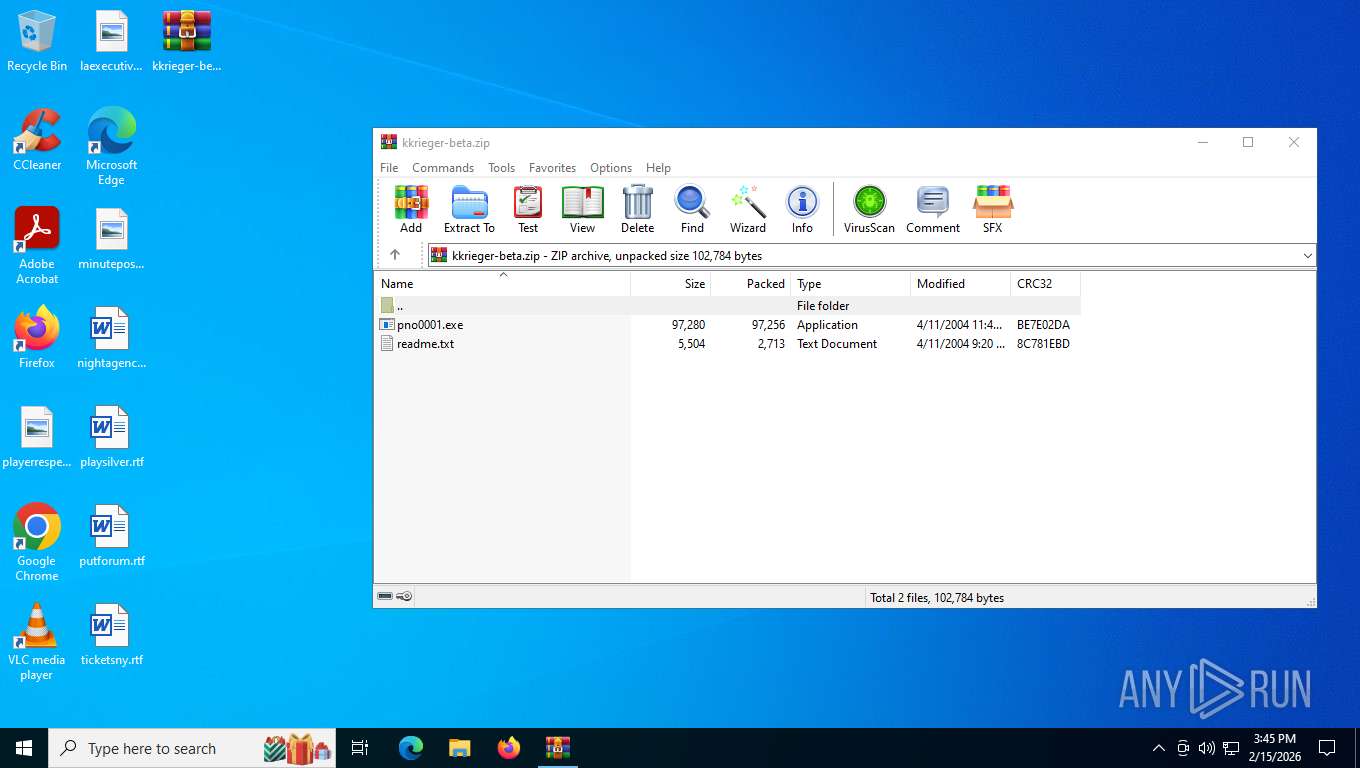
Generic archive extractor
- WinRAR.exe (PID: 8952)
Runs injected code in another process
- WerFault.exe (PID: 8512)
- pno0001.exe (PID: 3516)
SUSPICIOUS
Executes application which crashes
- pno0001.exe (PID: 3516)
INFO
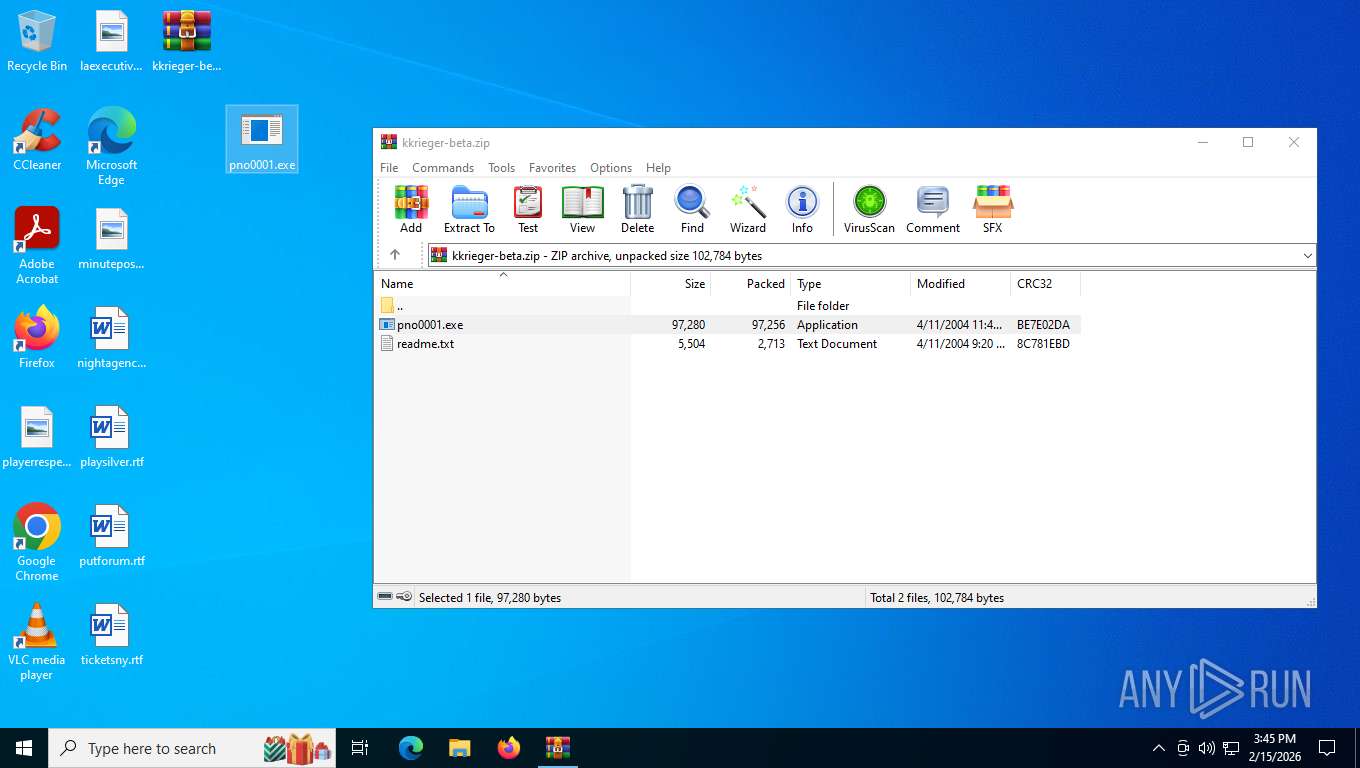
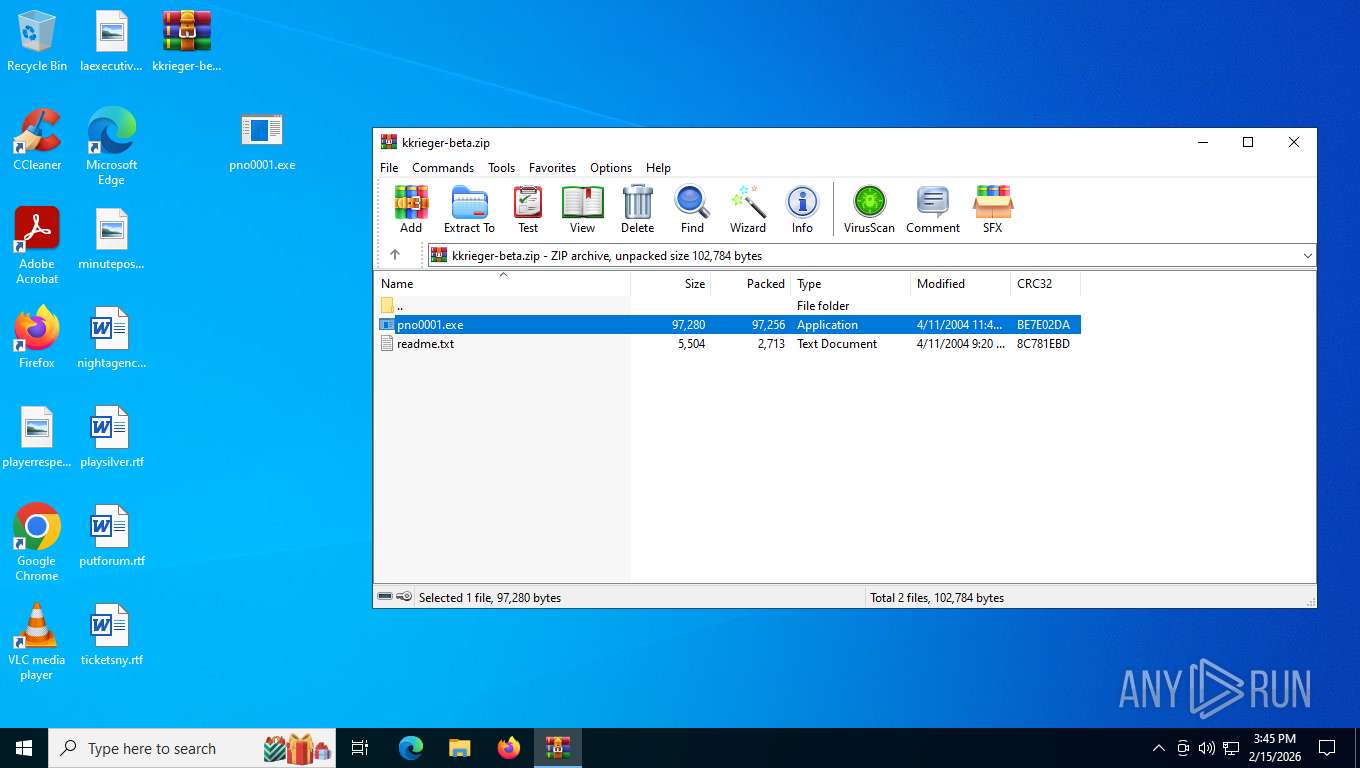
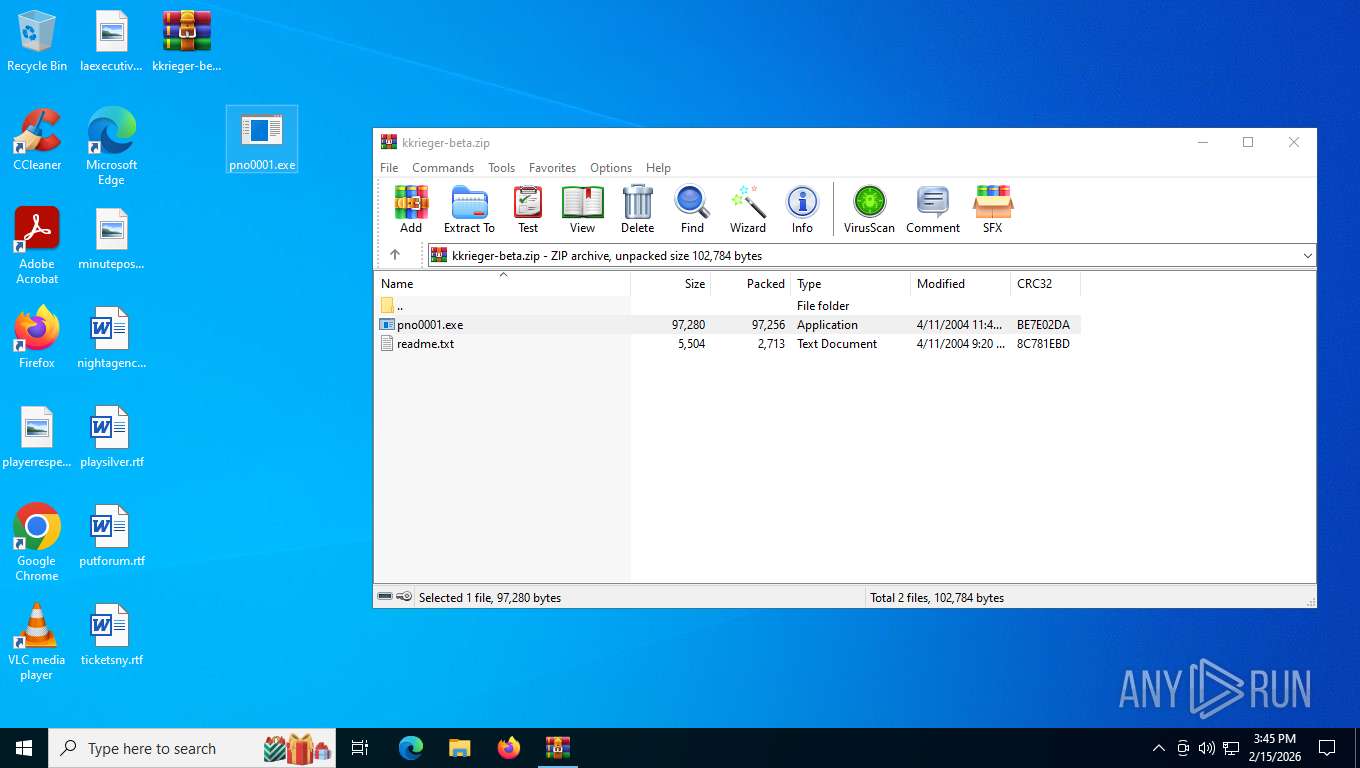
Manual execution by a user
- pno0001.exe (PID: 3516)
Checks supported languages
- pno0001.exe (PID: 3516)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8952)
There is functionality for taking screenshot (YARA)
- pno0001.exe (PID: 3516)
Reads the computer name
- pno0001.exe (PID: 3516)
Checks proxy server information
- WerFault.exe (PID: 8512)
Creates files or folders in the user directory
- WerFault.exe (PID: 8512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2004:04:11 23:45:16 |
| ZipCRC: | 0xbe7e02da |
| ZipCompressedSize: | 97256 |
| ZipUncompressedSize: | 97280 |
| ZipFileName: | pno0001.exe |
Total processes
153
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 652 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\Desktop\pno0001.exe" | C:\Users\admin\Desktop\pno0001.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 5772 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8512 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3516 -s 1256 | C:\Windows\SysWOW64\WerFault.exe | pno0001.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8952 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\kkrieger-beta.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 488
Read events
5 478
Write events
10
Delete events
0
Modification events
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\kkrieger-beta.zip | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8952) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_pno0001.exe_e3301bbc52d5456019ecb4f19a268fe330ac26_744fa4da_52022989-c502-44c2-ab87-122dd6342c01\Report.wer | — | |
MD5:— | SHA256:— | |||
| 8512 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\pno0001.exe.3516.dmp | — | |
MD5:— | SHA256:— | |||
| 8512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7780.tmp.WERInternalMetadata.xml | xml | |
MD5:F671A984E068F8EF7FA8BB19FB23D602 | SHA256:99A8780E74084311BFEB9747F5C604D800D41E9FF2AFA5F6D7266C11F6FFC978 | |||
| 8512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER76F3.tmp.dmp | binary | |
MD5:01D7C51E2EC270D573CFBC46987FE71F | SHA256:ACD5D3DBB16E0A59ADF8E99B8BEEB50837F16DC7BC8824AECCE1F9B10A2BA6F6 | |||
| 8512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7791.tmp.xml | xml | |
MD5:B20B0A6F52645DAFC5F8A8FC82BF2077 | SHA256:EA217A50885B0F508EBB21F32AC456B365583FEF96FA3A878A1BD6A0E47DFFF9 | |||
| 8512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:05DDF56FC804F432398703E32AF90A79 | SHA256:7193D01CF9580401784B76B581FABC0D63B97D49977EDD15370DF6967EF2F443 | |||
| 8512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:1A3A08F5EC73273F18F9F94289DDA6B7 | SHA256:2E306230AA41D2C40649BBB57E2F1EB54E6ACF15C6206B0AAABBDBA47A387462 | |||
| 8952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8952.46533\pno0001.exe | executable | |
MD5:0630F5F61BBD95DD28C2558C7092BC07 | SHA256:AC2192B740C57125067A29D2E0EA6D95B222543398188C5F67BBF01157622685 | |||
| 8512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:418ADCE992929F5EDA1FBF1FAAB9E677 | SHA256:1F4C84588EC6CD0639316CAF5391C619375970838DB3495880D33A859E0270D1 | |||
| 8512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:808BB621D40EF48DE994F2AC993EC835 | SHA256:B9C8558A9F5E6DDA6DA0121EE748F38C1B79FB0DDCB8B3DE179CAC06E9BB6117 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
23
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3208 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
2780 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
2780 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
2780 | SIHClient.exe | GET | 200 | 135.233.95.144:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
2780 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
3208 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.70 Kb | whitelisted |
8512 | WerFault.exe | POST | 200 | 135.233.45.222:443 | https://watson.events.data.microsoft.com/Telemetry.Request | US | xml | 636 b | whitelisted |
3208 | svchost.exe | GET | 200 | 184.24.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8512 | WerFault.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3208 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6936 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3208 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3208 | svchost.exe | 184.24.77.30:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8512 | WerFault.exe | 135.233.45.222:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8512 | WerFault.exe | 2.16.168.114:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8512 | WerFault.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3208 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |