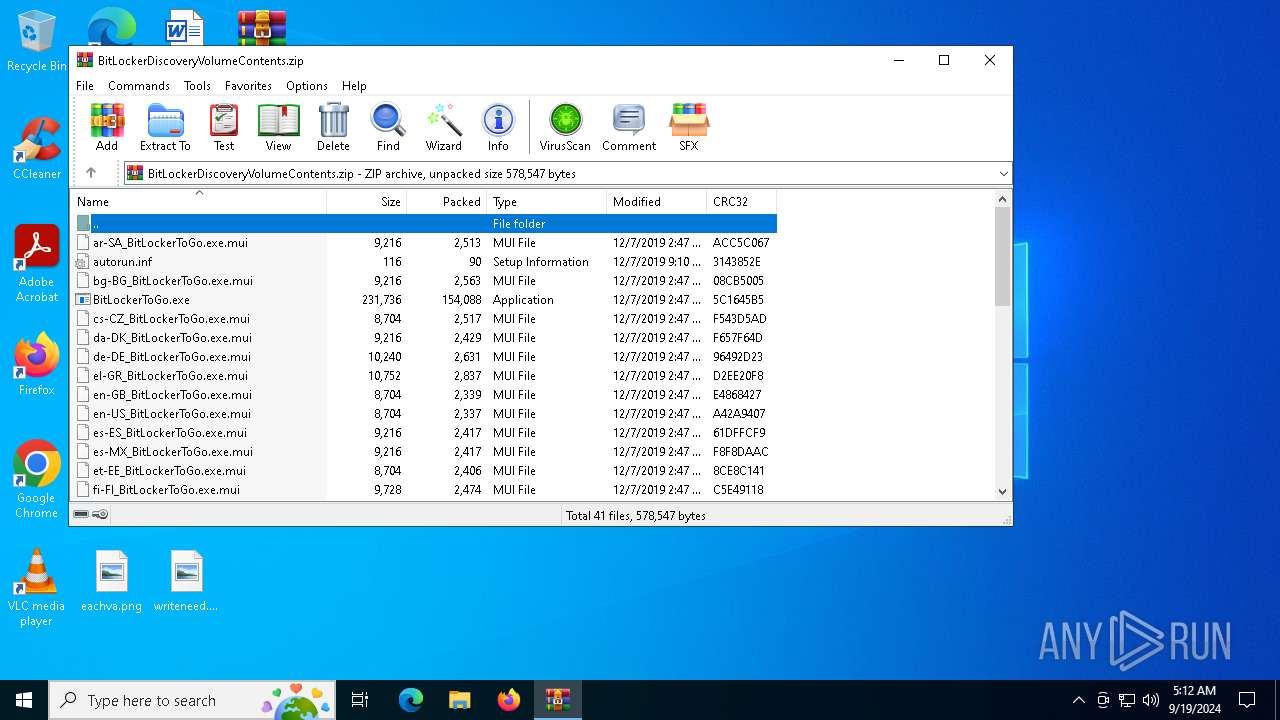
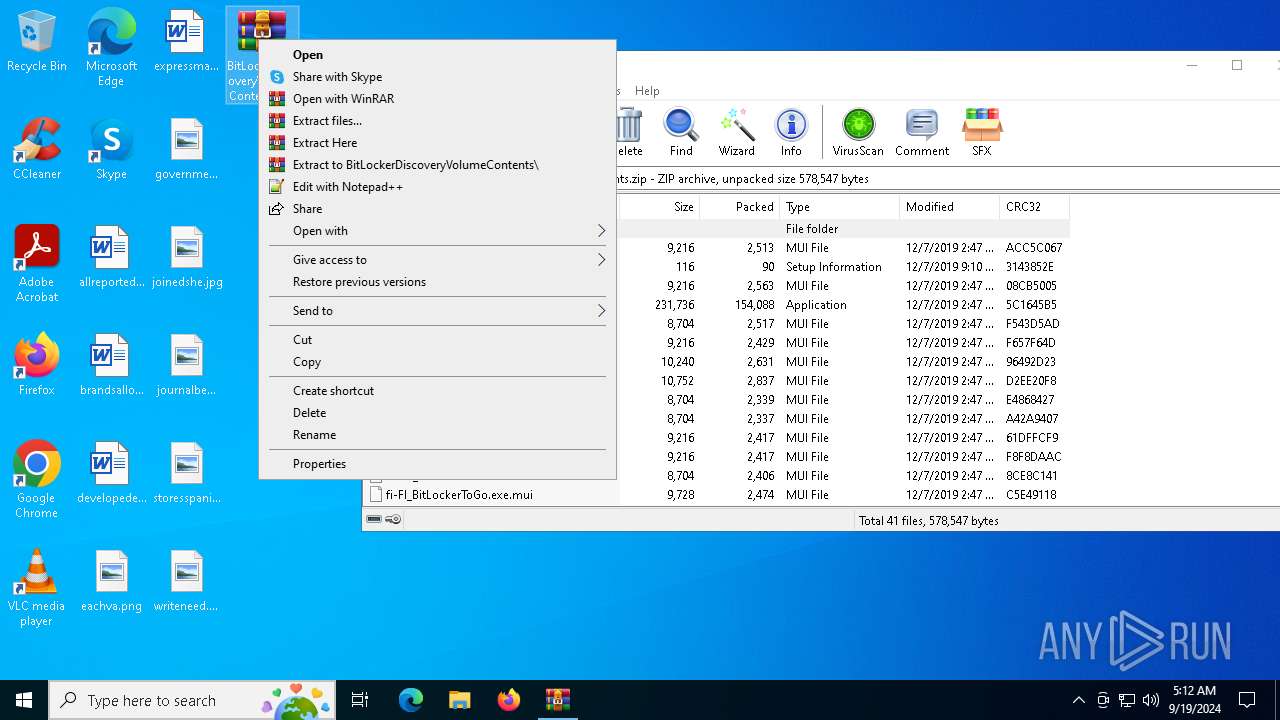
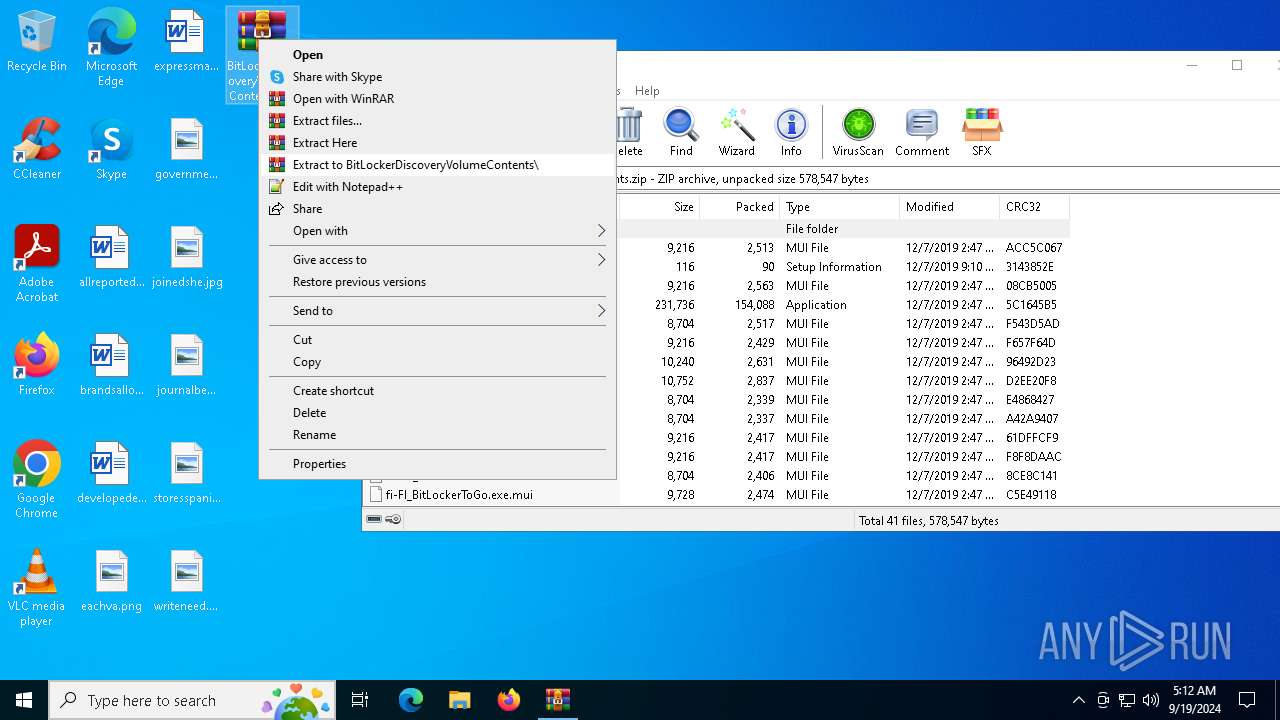
| File name: | BitLockerDiscoveryVolumeContents.zip |
| Full analysis: | https://app.any.run/tasks/d51d8668-bb0b-426a-b5b8-cd881406e10a |
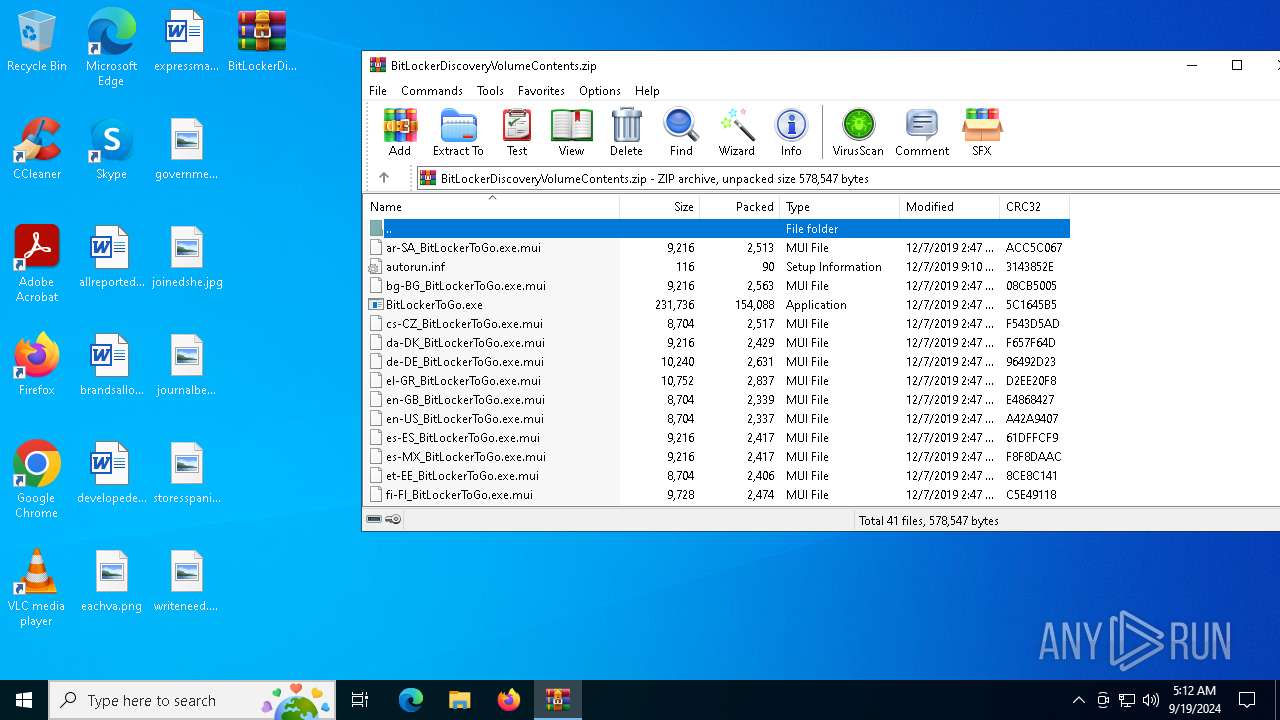
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2024, 05:12:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 51CEB7BD5C372908F4D670BB368C968F |
| SHA1: | FFFD00E619149F88C3D00E491635233AB3E19AED |
| SHA256: | 367D75A825863BEB16E88CBAB1438C943AFE47679E264EB7E59C65450947B984 |
| SSDEEP: | 6144:iIJa5rCJp/Z1KtWF8Z4n4luC2GNpwWbtEhvg0qilgnl:ile3xot8+/EC2GNjbYgalgl |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:07 22:47:28 |
| ZipCRC: | 0xacc5c067 |
| ZipCompressedSize: | 2513 |
| ZipUncompressedSize: | 9216 |
| ZipFileName: | ar-SA_BitLockerToGo.exe.mui |
Total processes
130
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
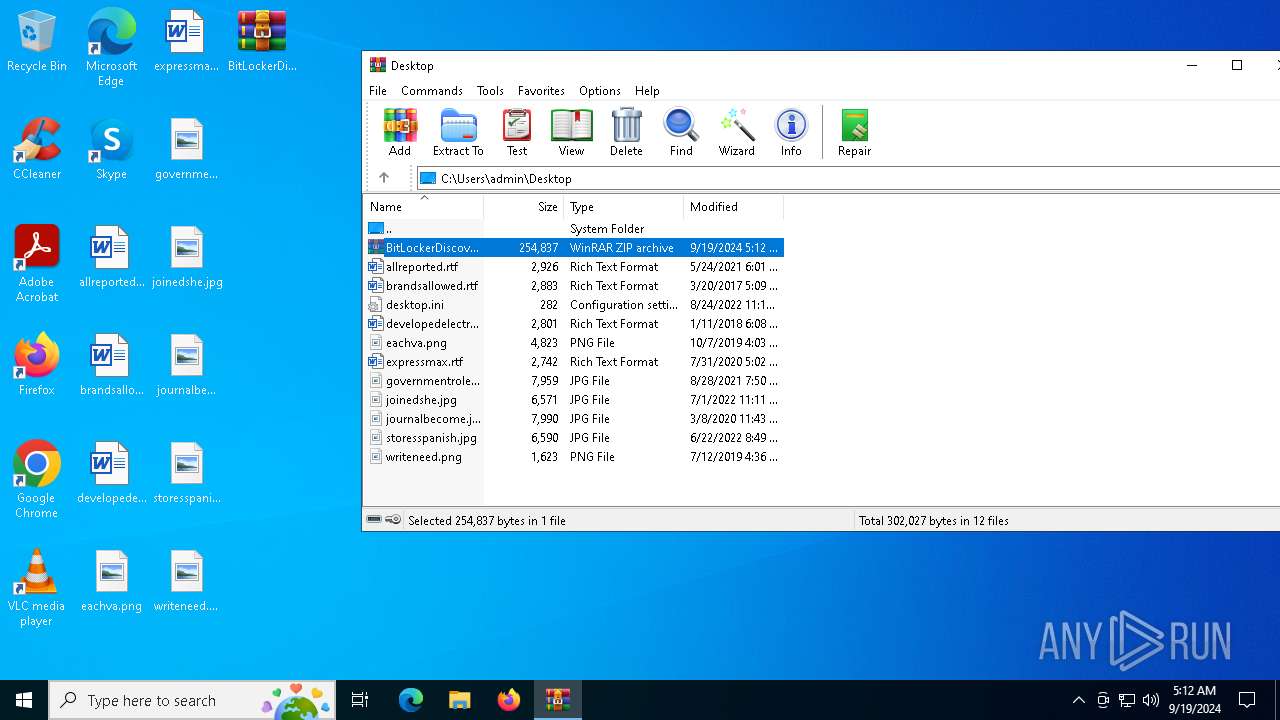
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
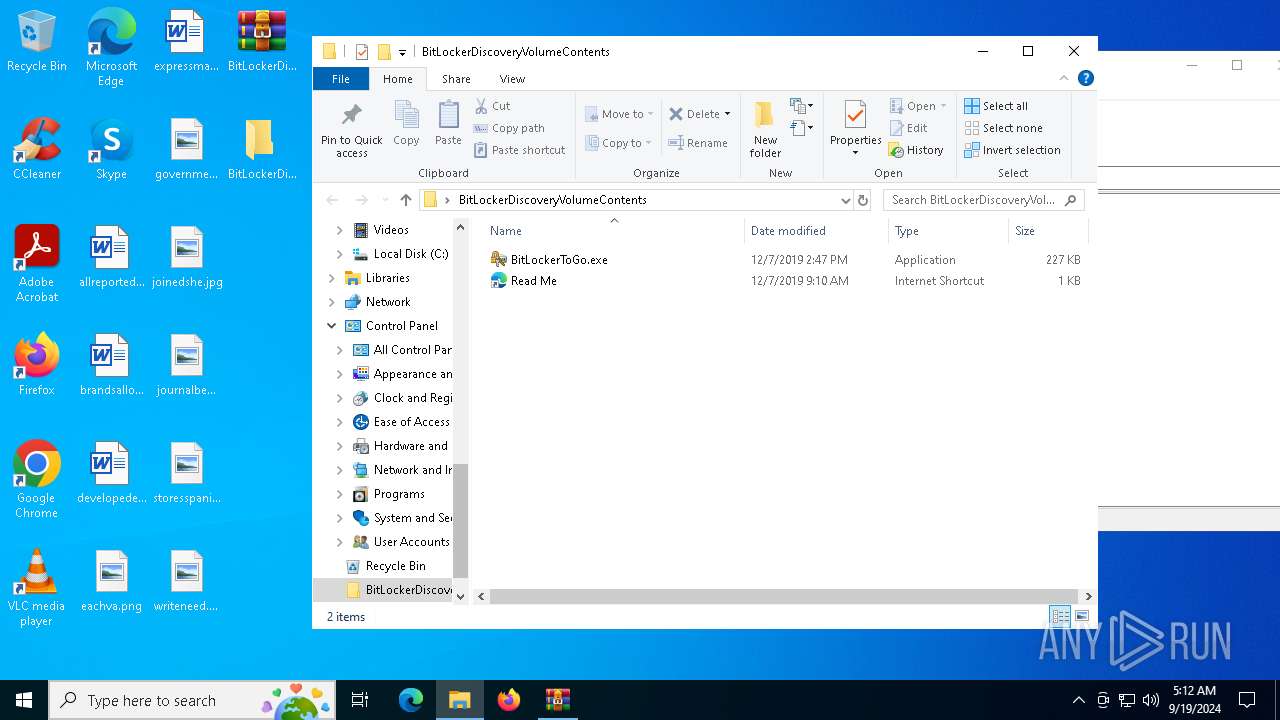
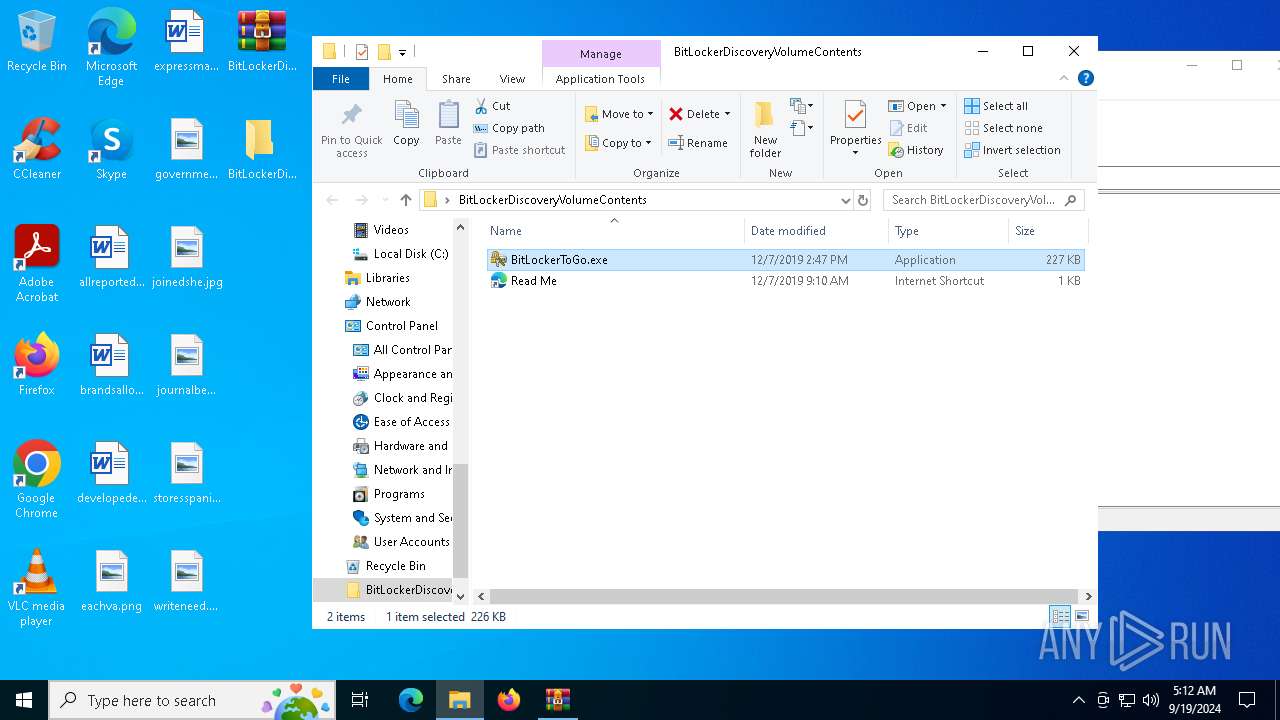
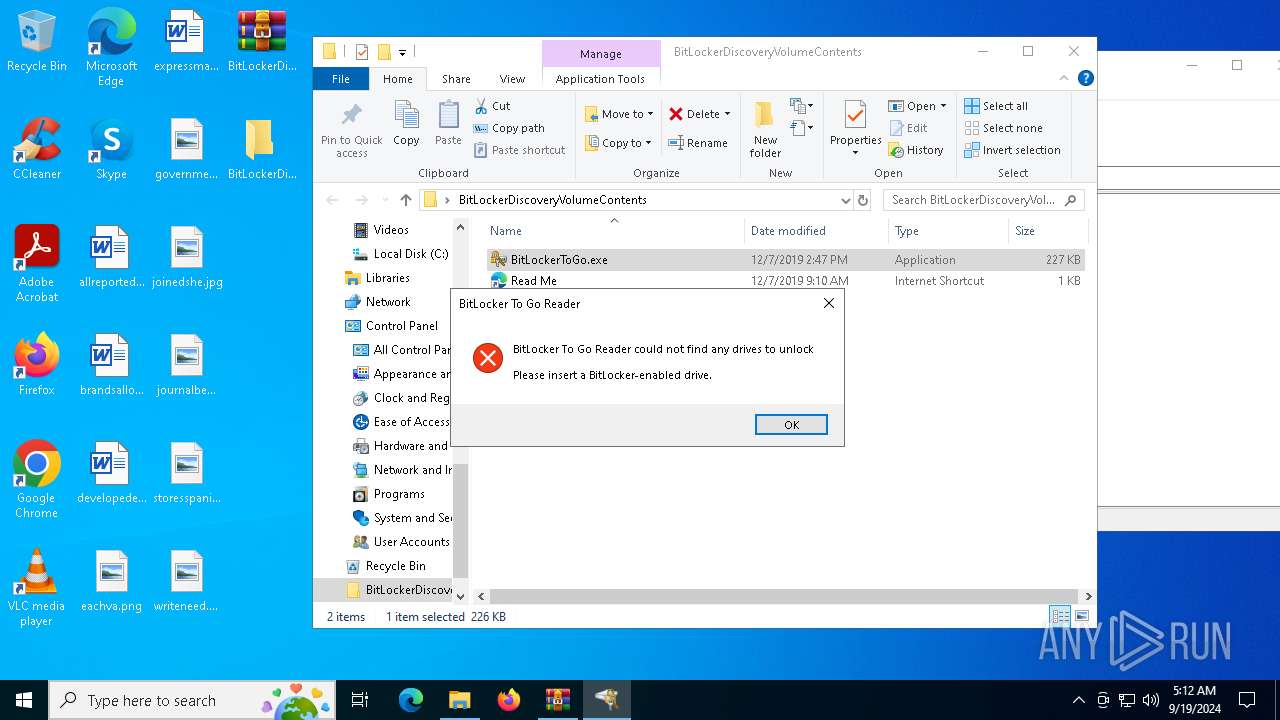
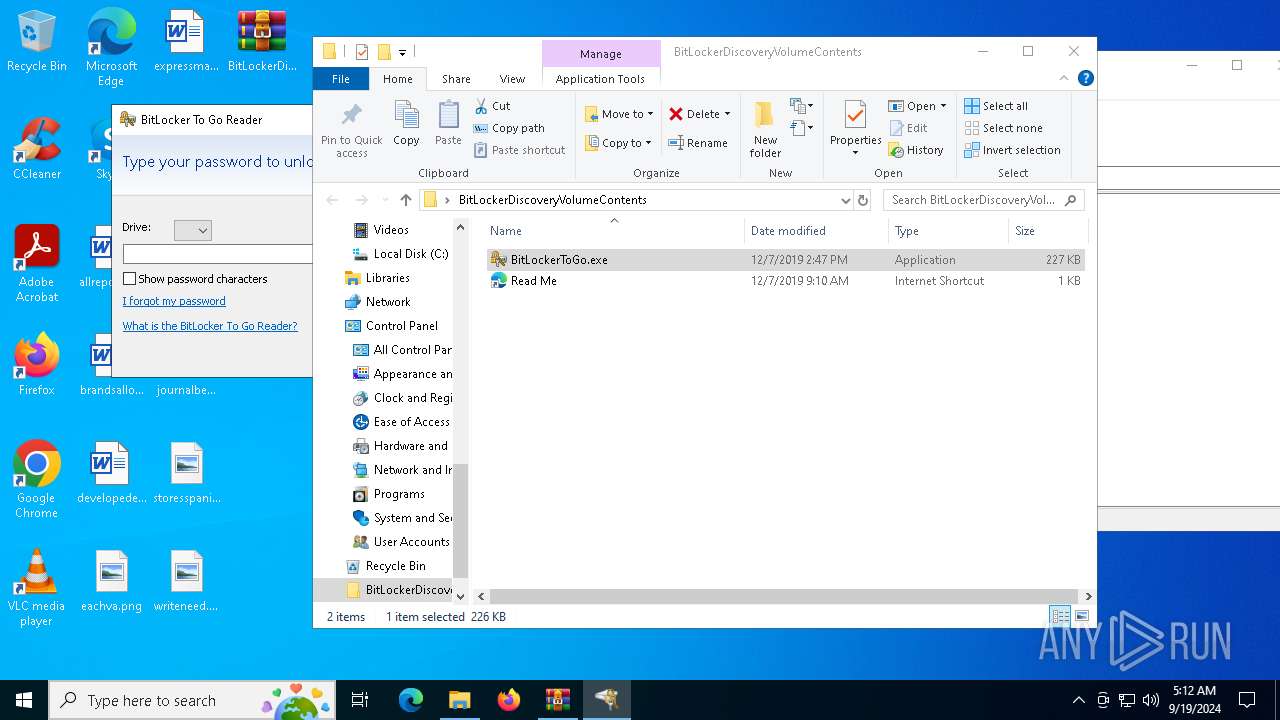
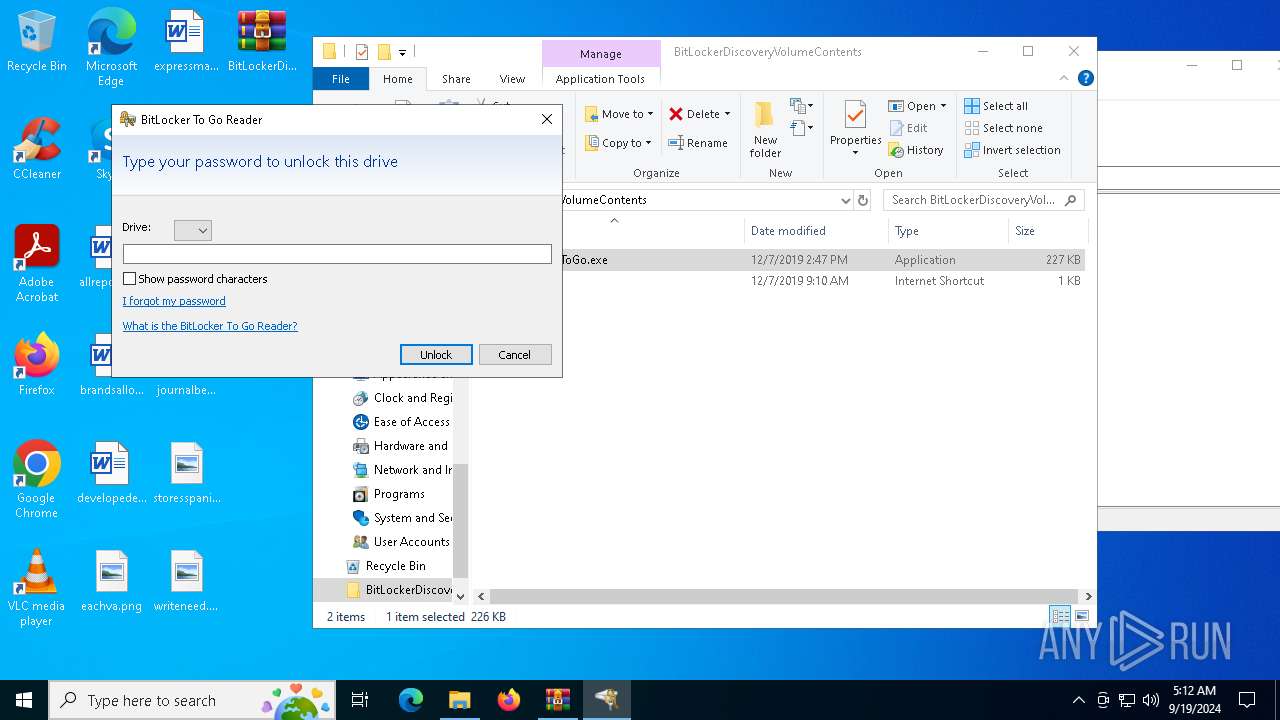
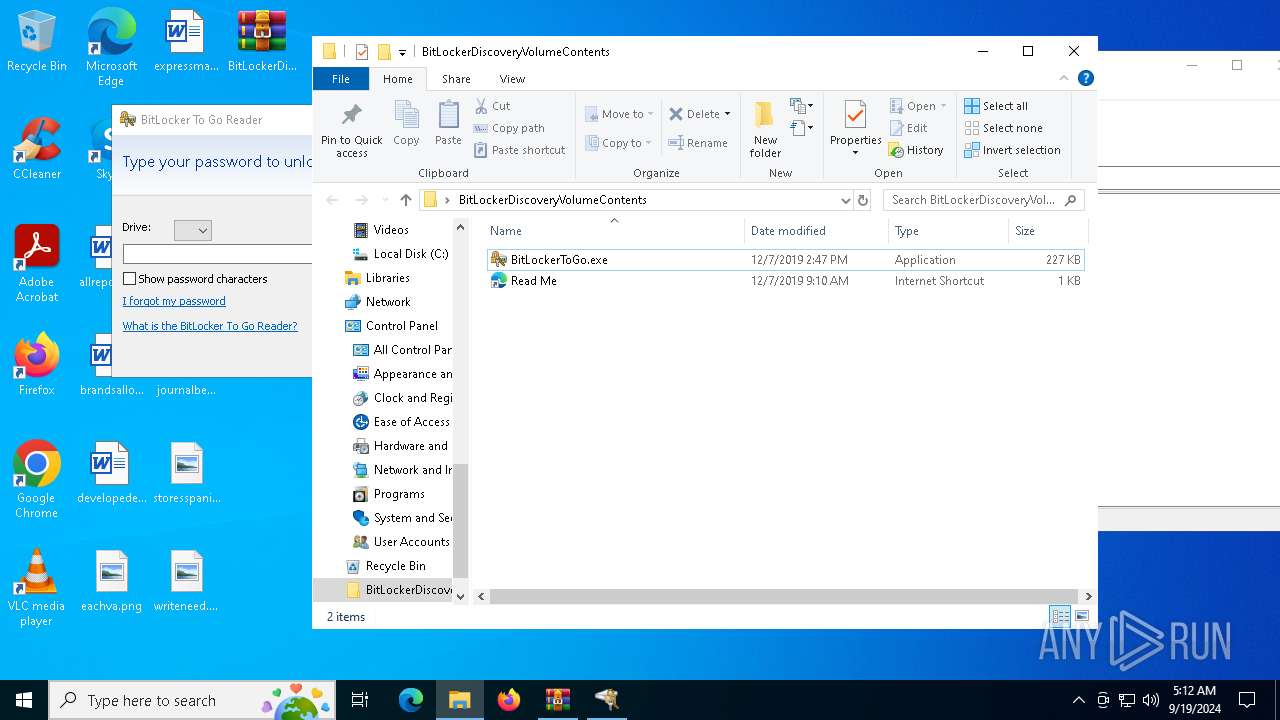
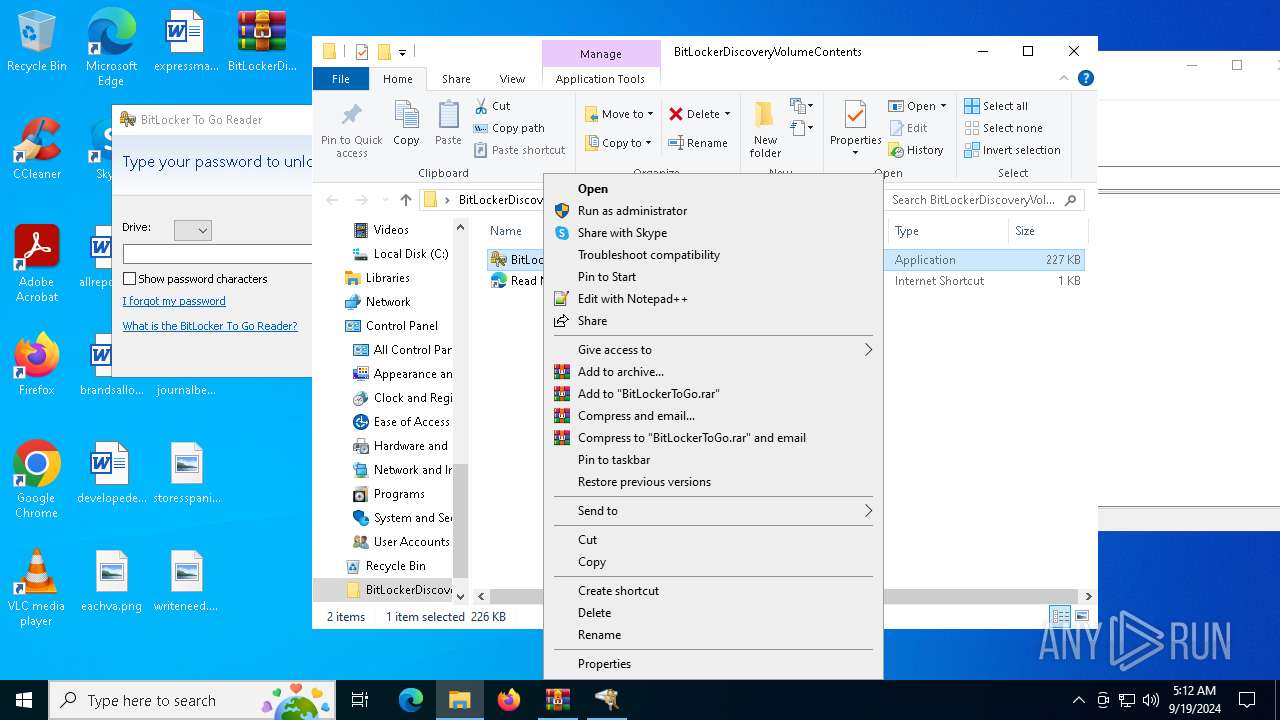
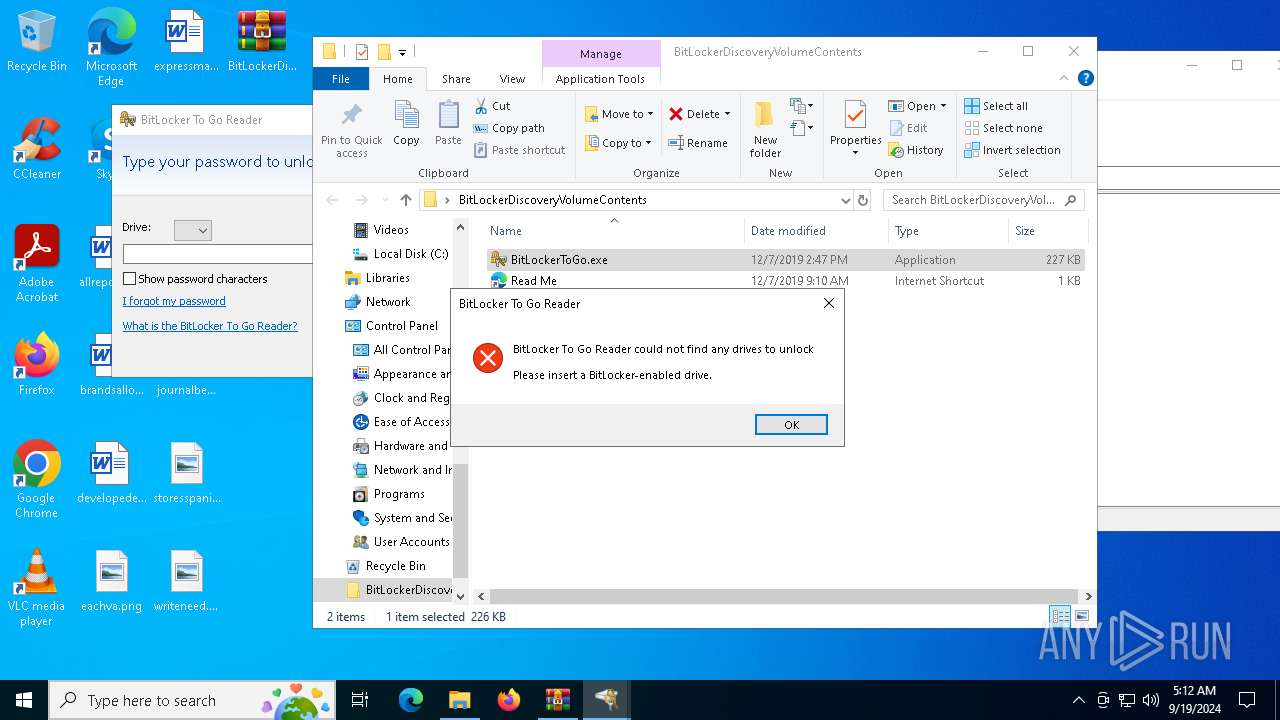
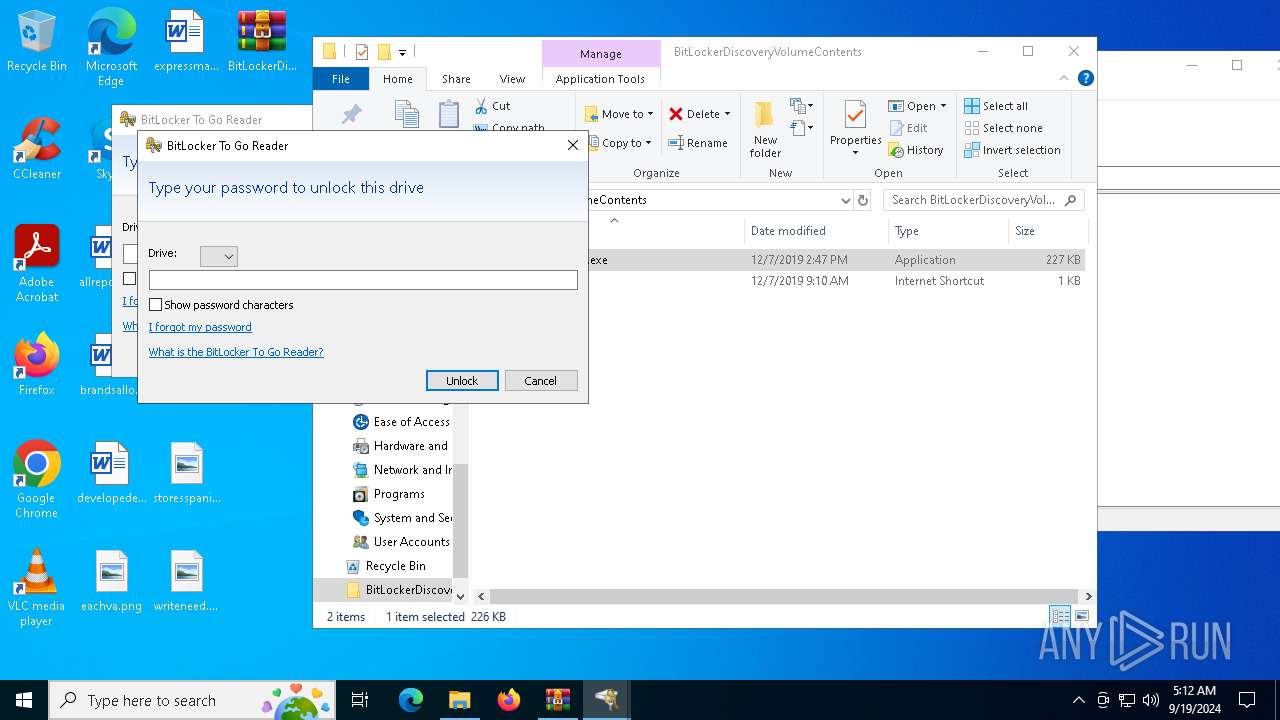
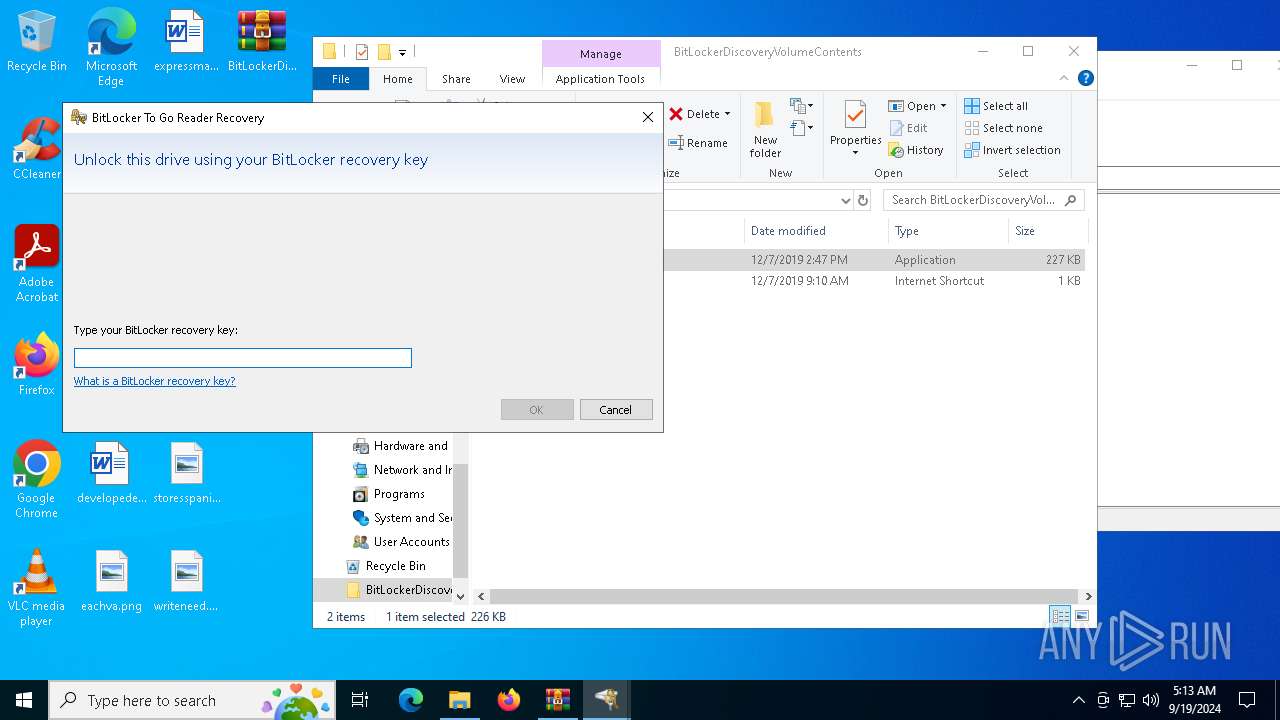
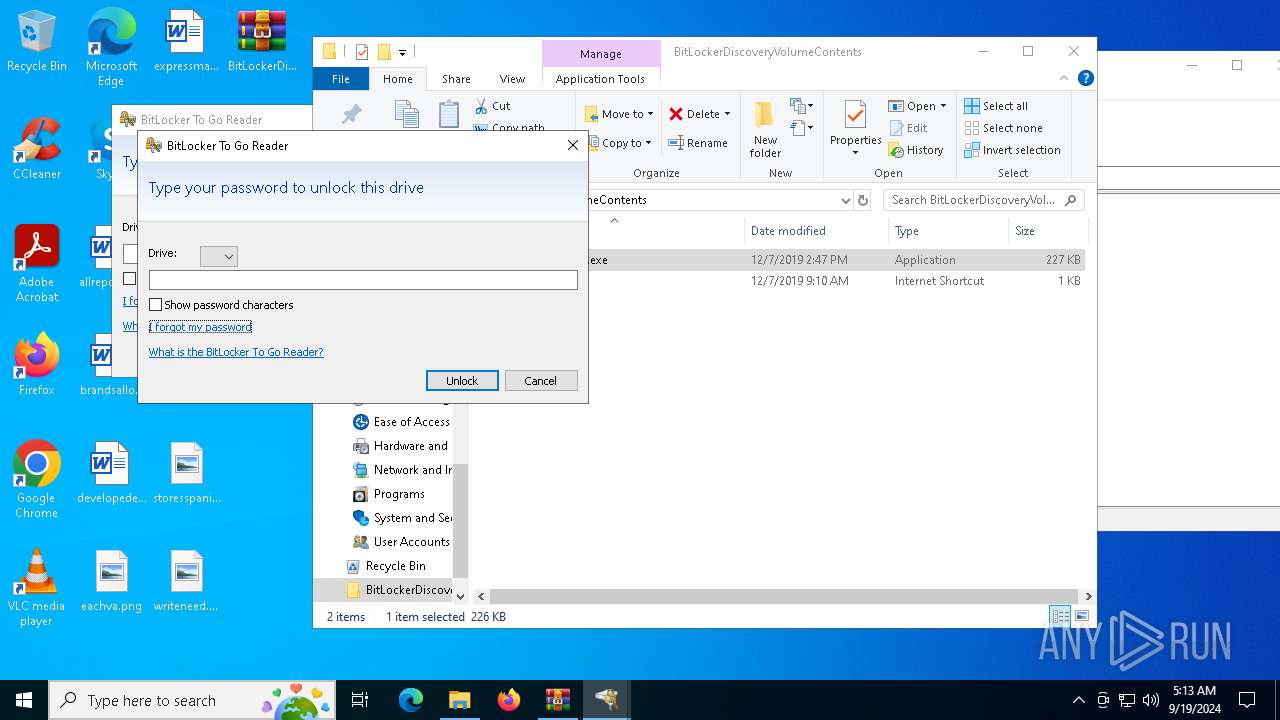
| 1644 | "C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5064 | "C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: BitLocker To Go Reader Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 6640 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6644 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents.zip" C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6876 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 708
Read events
1 687
Write events
21
Delete events
0
Modification events
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents.zip | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (6640) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
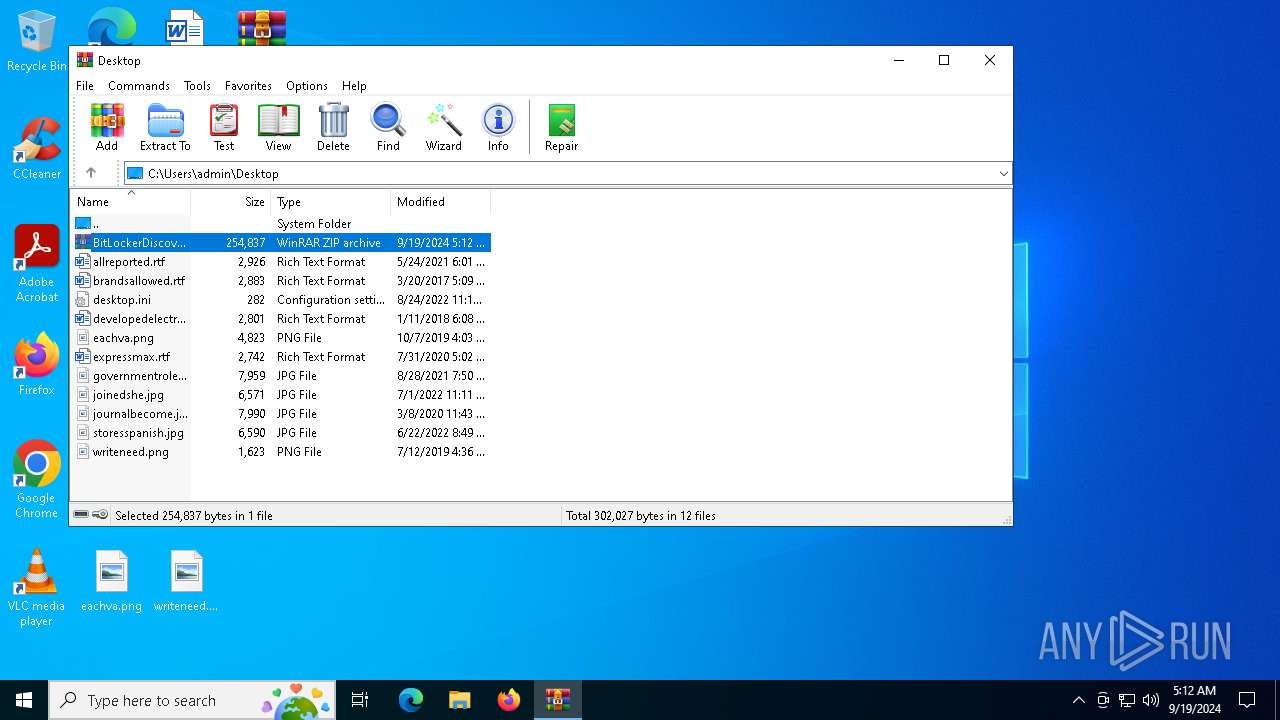
Executable files
39
Suspicious files
0
Text files
1
Unknown types
1
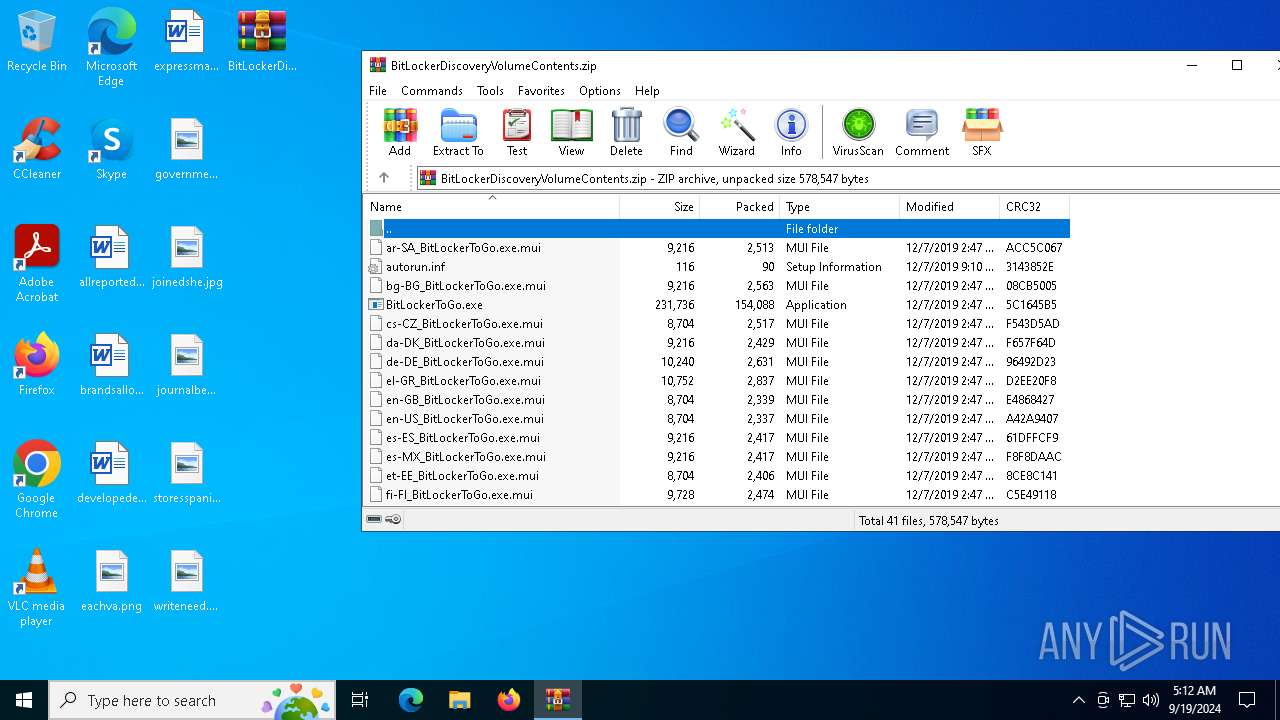
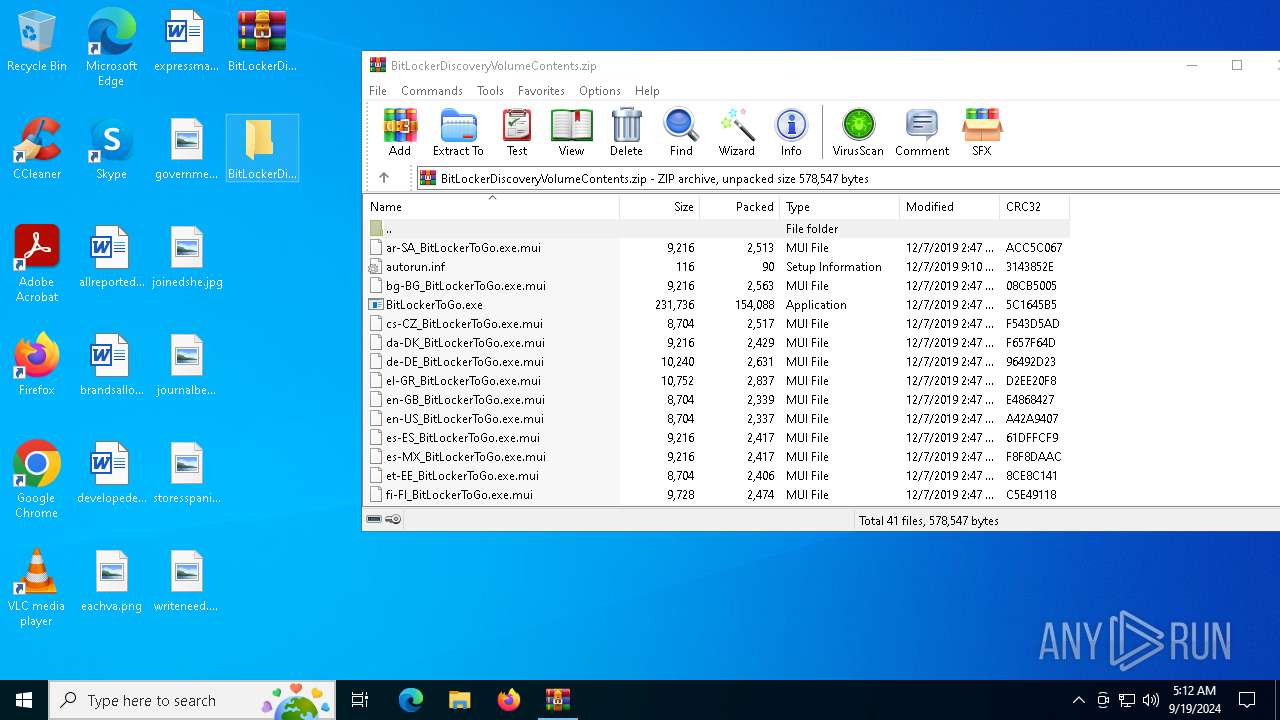
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
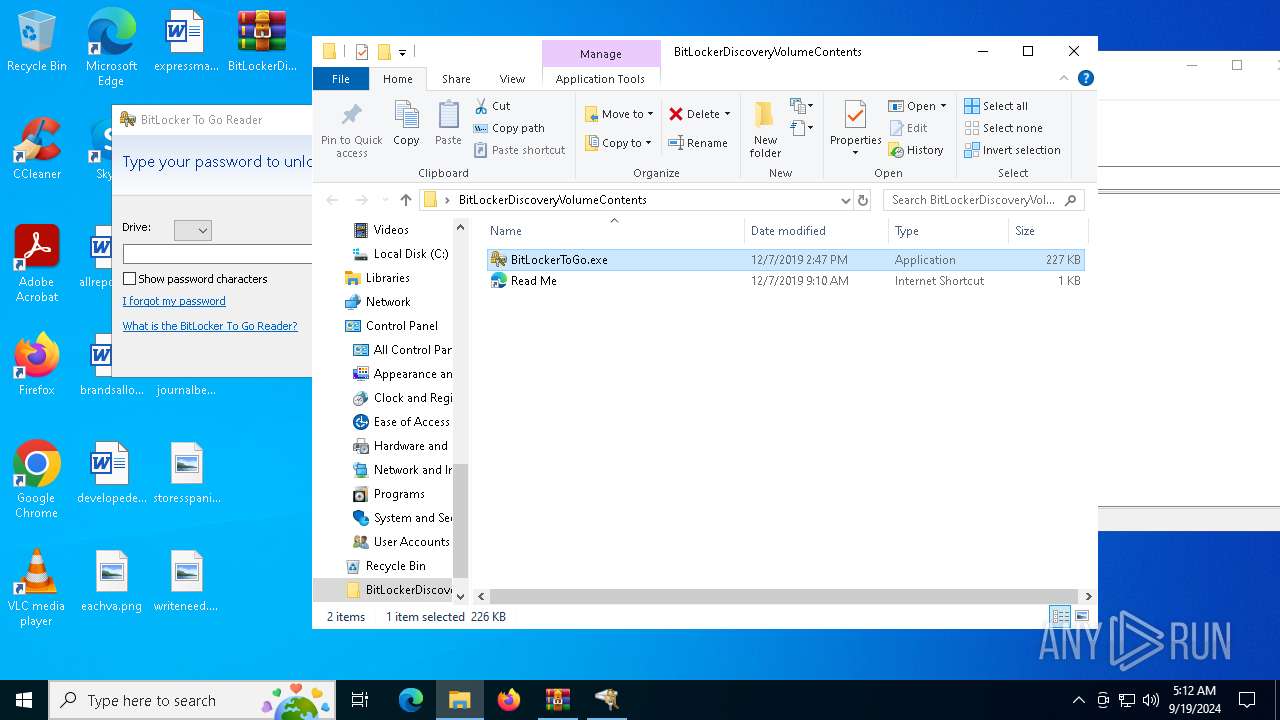
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | executable | |
MD5:A64BEAB5D4516BECA4C40B25DC0C1CD8 | SHA256:36FB87F4E3048659D91FB4250D07582BBBEDA35A7A5839CA61AA0D85DC1BD63C | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\de-DE_BitLockerToGo.exe.mui | executable | |
MD5:69FF34FF79384955AA88B86EAFA22EBF | SHA256:38D2FBAD739C84023BA2F5FEA969F510D45C399633E786D4A9C33098B80EA8BD | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\en-GB_BitLockerToGo.exe.mui | executable | |
MD5:2FC4401A4ADAB9BCF1A0398160C41A05 | SHA256:85A450FB83B93B589E4C693A9ED3148717E2B7490BB2D539137ED1E080236DC2 | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\ar-SA_BitLockerToGo.exe.mui | executable | |
MD5:950B8DF6809B5E89117698E9ED4F2D1D | SHA256:558364D68DC2B745A5308650BFA92D1EFD5B7E1FC4754C019327E80119C782F9 | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\el-GR_BitLockerToGo.exe.mui | executable | |
MD5:4C07F74E0FA93F87FD7CF2E490BDF919 | SHA256:D7F47EAF9E8D41F44C038CB0DA69EFA406A3B6DF10EFDE1EF91E9048B9AA1E24 | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\en-US_BitLockerToGo.exe.mui | executable | |
MD5:F87833A3D8CB289E1AB042DFDB43ED72 | SHA256:8BA28D8844AED14E32B3665948B9511790BAF733FC31855B5778996B24FA58D3 | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\da-DK_BitLockerToGo.exe.mui | executable | |
MD5:63C10101B9B3E32E370276ACA348C165 | SHA256:6E0187EB61308F327F955B17E06240D819C9E2EA90DD6C00BE84A96003384F19 | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\autorun.inf | ini | |
MD5:58835871E57FA4900939E252DAE4090F | SHA256:AC4575B872EC10A0EC86A33CBB235E0F3682407A08C53A9DCAF44A9C2151530A | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\es-MX_BitLockerToGo.exe.mui | executable | |
MD5:4A2F30F5FD69CF7B338942B3CEAA9C4C | SHA256:040218ED56799B7920DB4C9CD218FA47F336D42A1C692D007BC4AAD778233676 | |||
| 6644 | WinRAR.exe | C:\Users\admin\Desktop\BitLockerDiscoveryVolumeContents\fr-CA_BitLockerToGo.exe.mui | executable | |
MD5:2C9EC6F6A9A44963E963BBDC1825DA3B | SHA256:E2B2B10645713180839CC255BEF73AF39F4C1ACC13ABA91AD8D0A32B34612E6C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4152 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3108 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4152 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6932 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2532 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3108 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3108 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5336 | SearchApp.exe | 13.89.179.13:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |