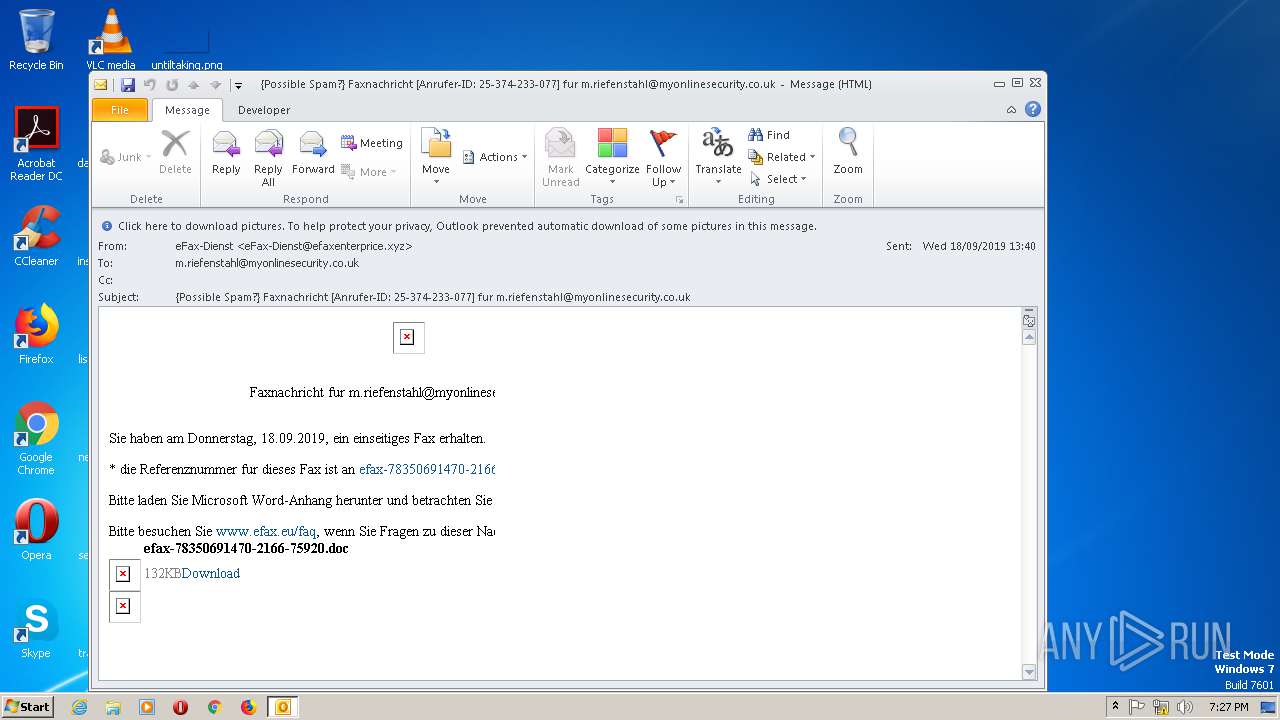
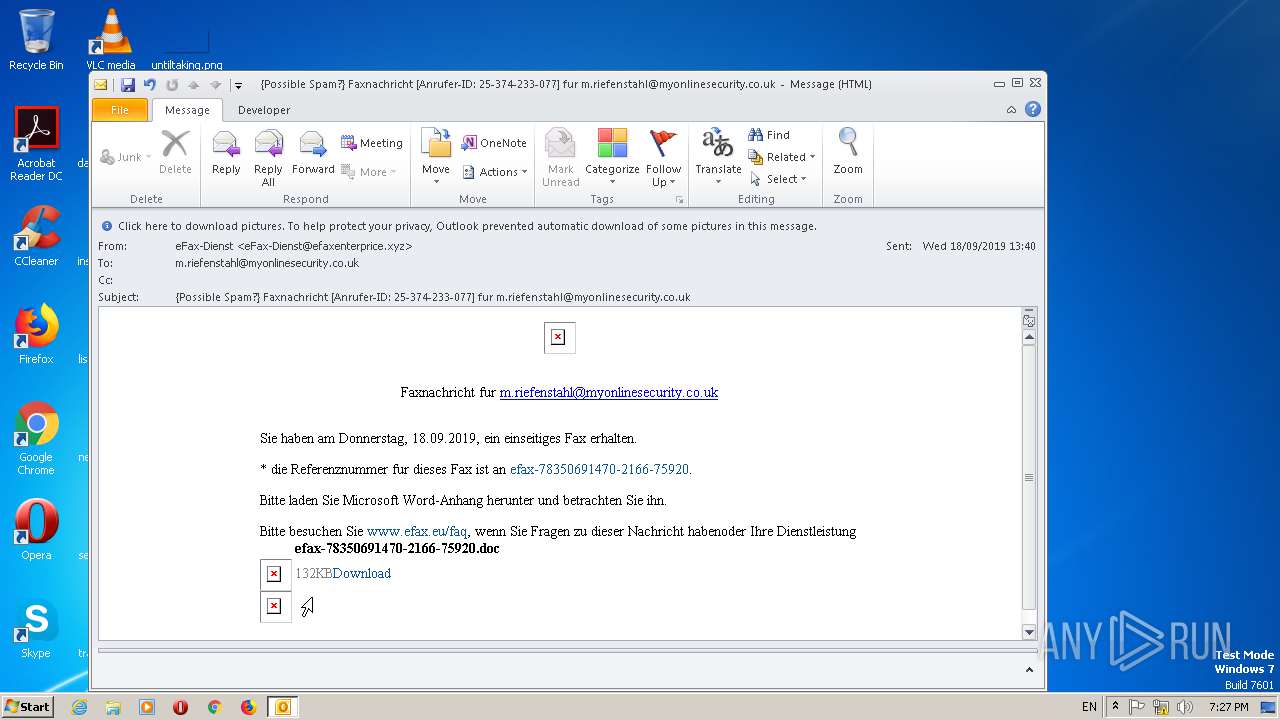
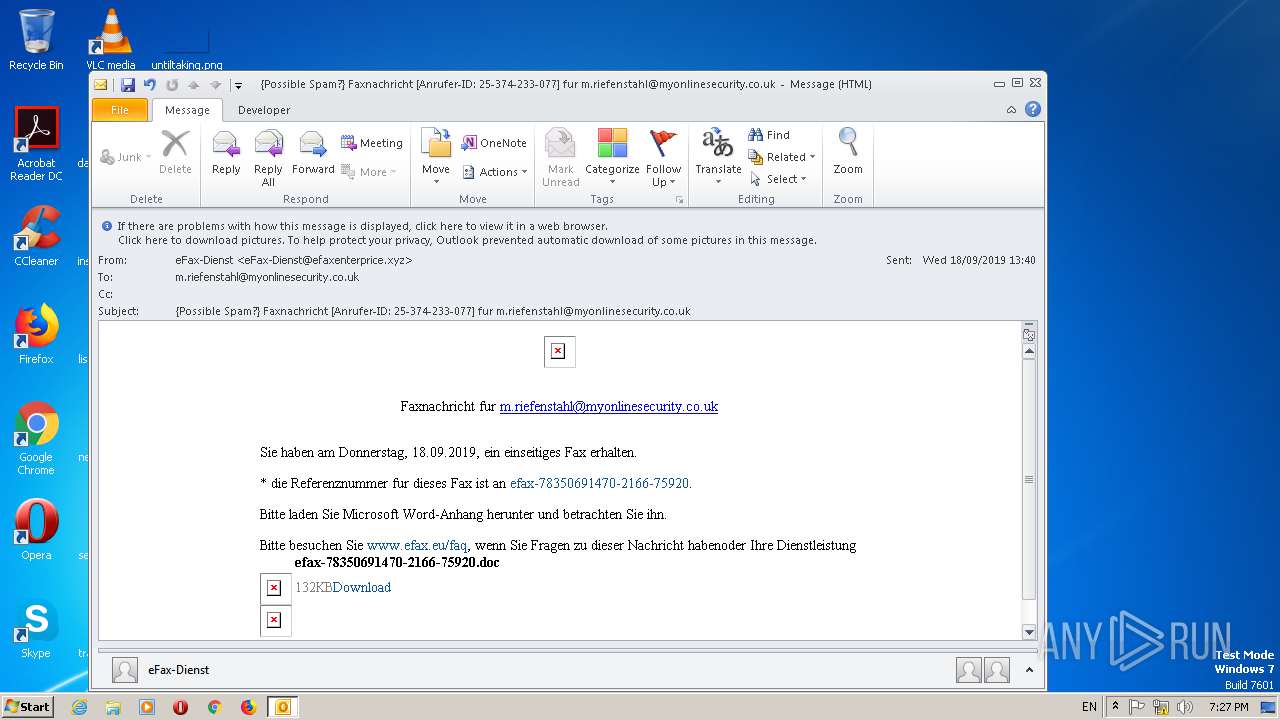
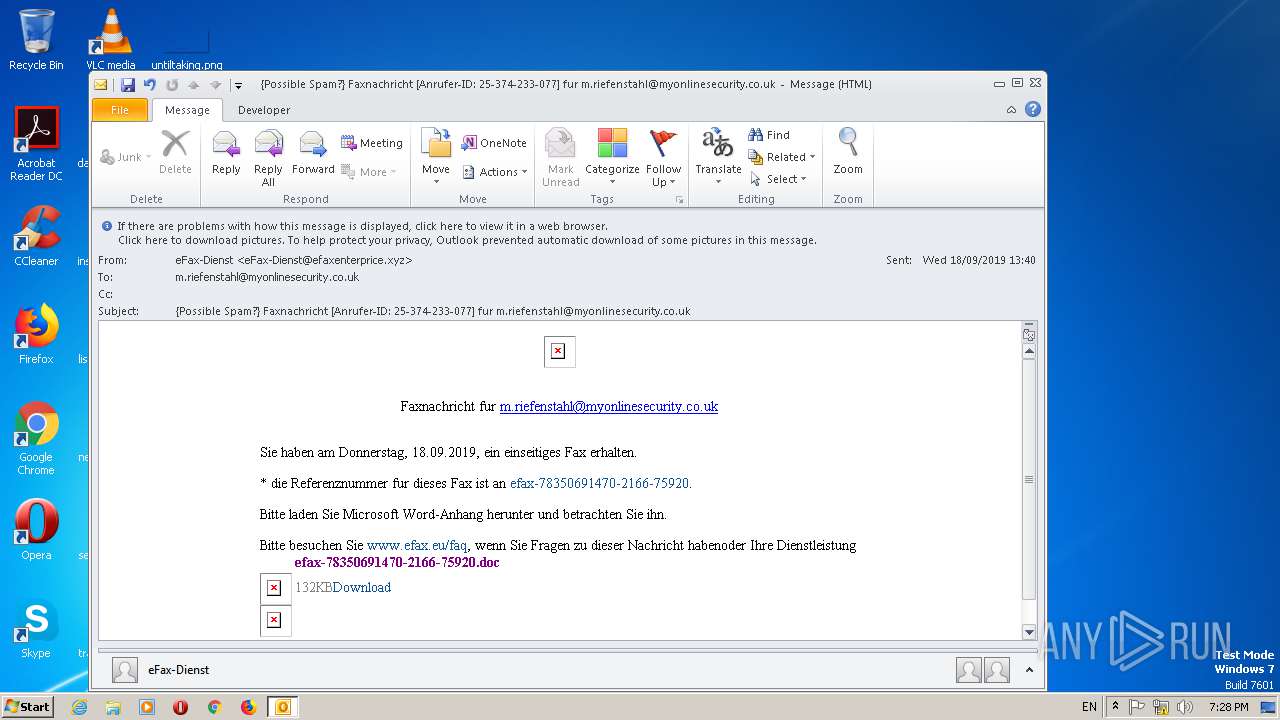
| File name: | {Possible Spam} Faxnachricht Anrufer-ID 25-374-233-077 fur m.riefenstahl@myonlinesecurity.co.uk.msg |
| Full analysis: | https://app.any.run/tasks/0c3e03ef-a101-439a-8347-cef4a278165a |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 18:26:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | CC809ECAAD5DD3108D33CEFD0978F36F |
| SHA1: | 7CAEEAD36101B58EA78C908901DC0AEE04C44BA6 |
| SHA256: | 366D209A9CA9C2D6D8BCF80469A04E5F86D5F1BBBD63DB6F34824AEC709FE13D |
| SSDEEP: | 1536:qoi9rpcGCEEGoZw8FwPdxqAL9P1PHjEwoMIMdzApJUOPU1/nt8SwHqS+f5:qoi9xCq8uzqsXPHboMppANPU/8T |
MALICIOUS
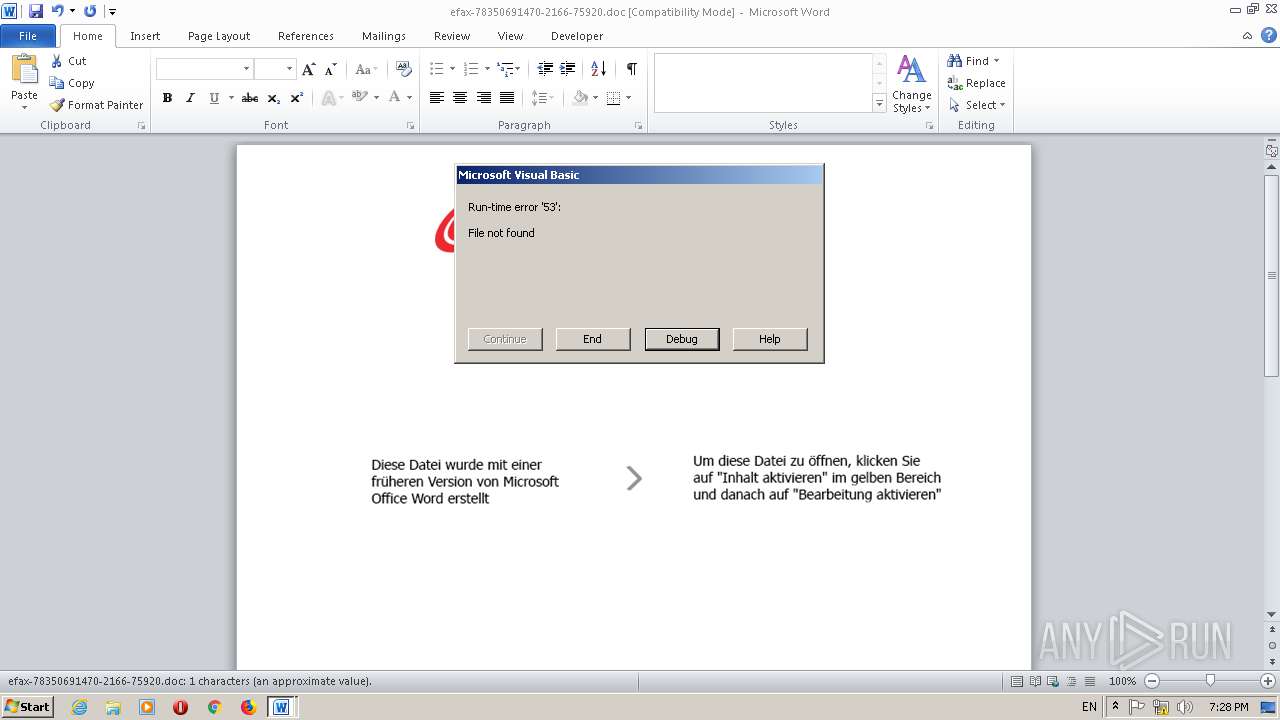
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2248)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2248)
- WINWORD.EXE (PID: 580)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2248)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2248)
INFO
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2248)
- iexplore.exe (PID: 2872)
- WINWORD.EXE (PID: 580)
Reads Internet Cache Settings
- iexplore.exe (PID: 2872)
Creates files in the user directory
- IEXPLORE.EXE (PID: 2544)
- WINWORD.EXE (PID: 580)
Changes internet zones settings
- iexplore.exe (PID: 2872)
Manual execution by user
- WINWORD.EXE (PID: 580)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 580)
- OUTLOOK.EXE (PID: 2248)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2544)
Reads settings of System Certificates
- iexplore.exe (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
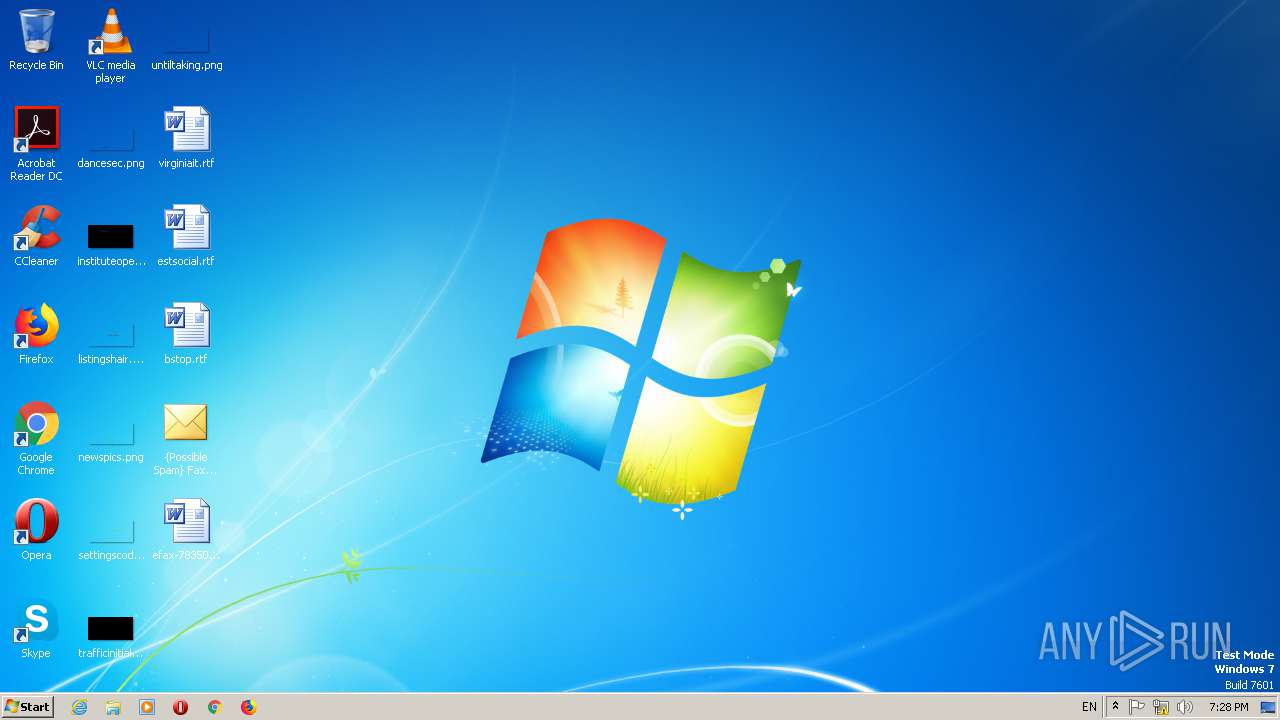
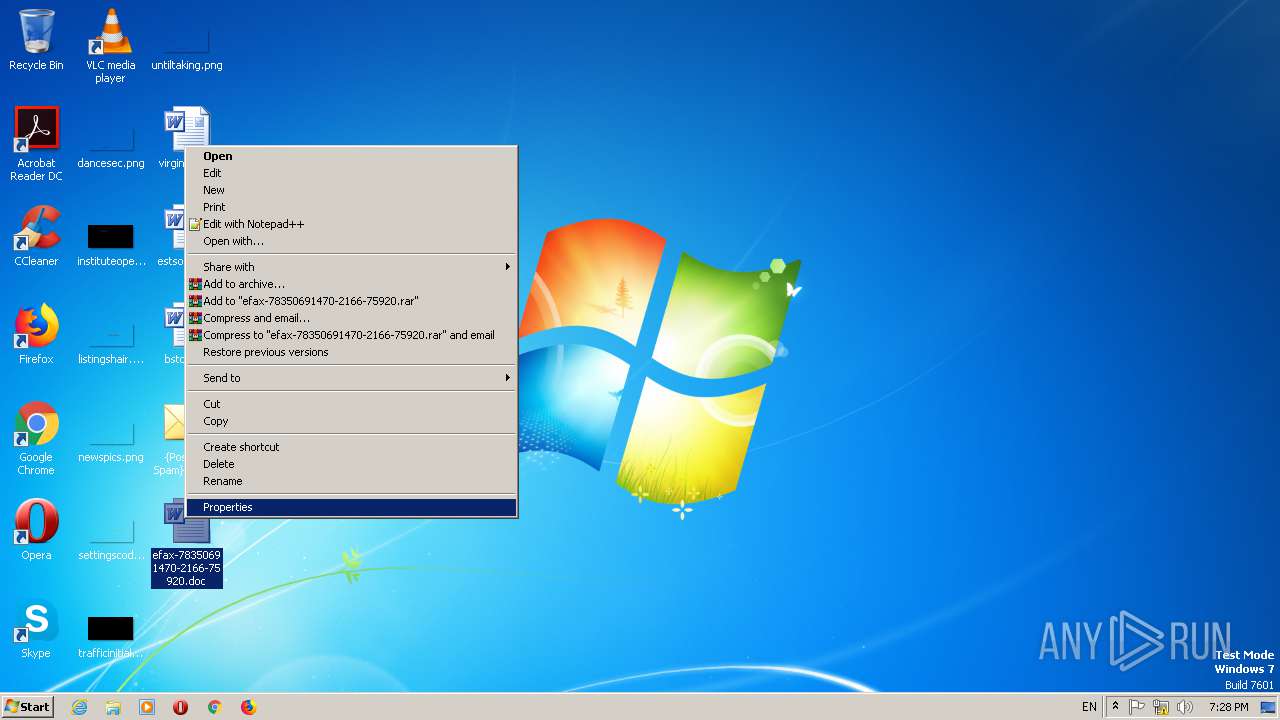
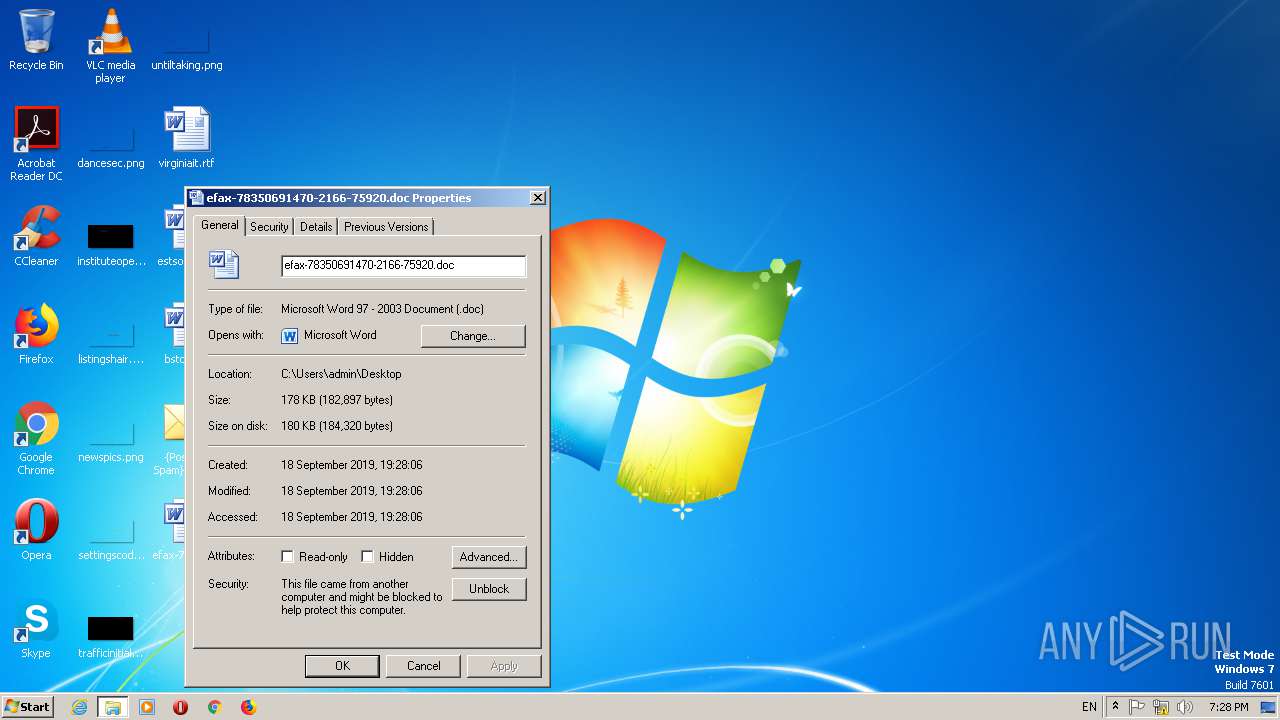
| 580 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\efax-78350691470-2166-75920.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Desktop\{Possible Spam} Faxnachricht Anrufer-ID 25-374-233-077 fur m.riefenstahl@myonlinesecurity.co.uk.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.4760.1000 Modules
| |||||||||||||||
| 2544 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2872 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
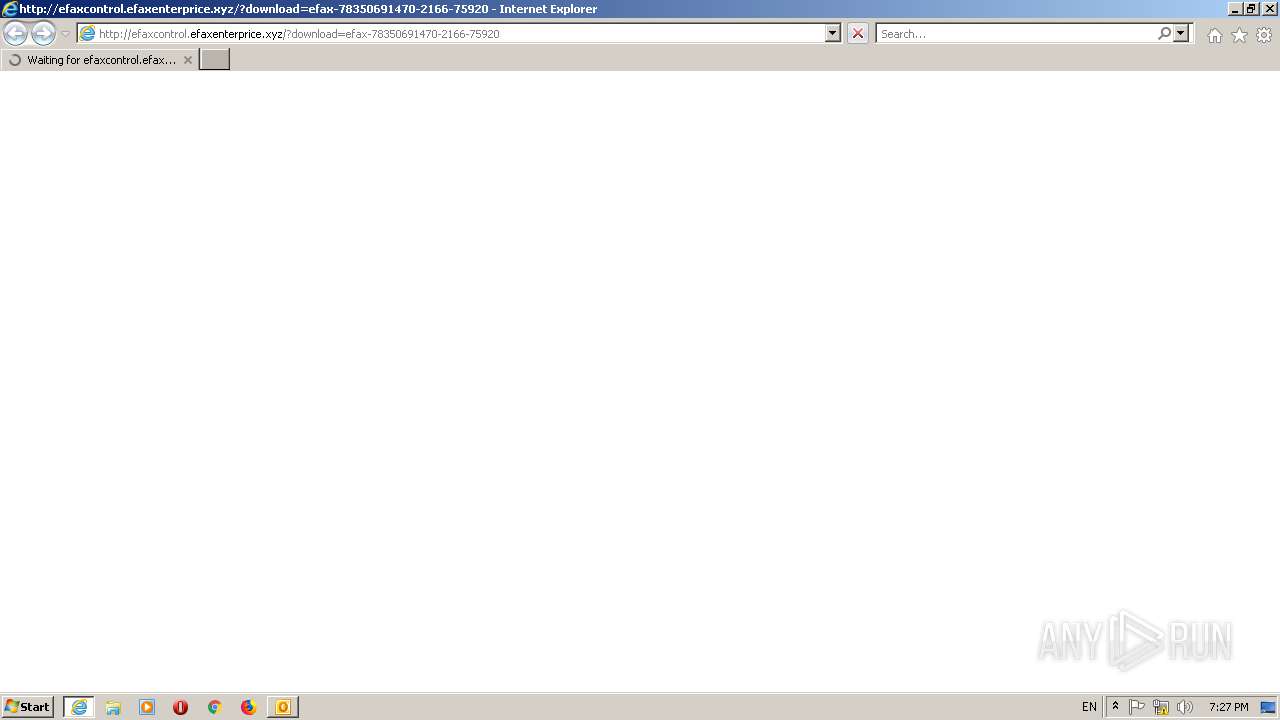
| 2872 | "C:\Program Files\Internet Explorer\iexplore.exe" http://efaxcontrol.efaxenterprice.xyz/?download=efax-78350691470-2166-75920 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 874
Read events
4 766
Write events
1 079
Delete events
29
Modification events
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 2057 |
Value: On | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 59 |
Value: 7F353900C8080000010000000000000000000000 | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C808000038A105AB4E6ED50100000000 | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220220640 | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1400000000000000 | |||
Executable files
0
Suspicious files
8
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR815F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2U1WPAC\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2544 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\GN2Z5UTK.txt | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2350F1436C4CAFF9.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF44BE3CF502756486.TMP | — | |
MD5:— | SHA256:— | |||
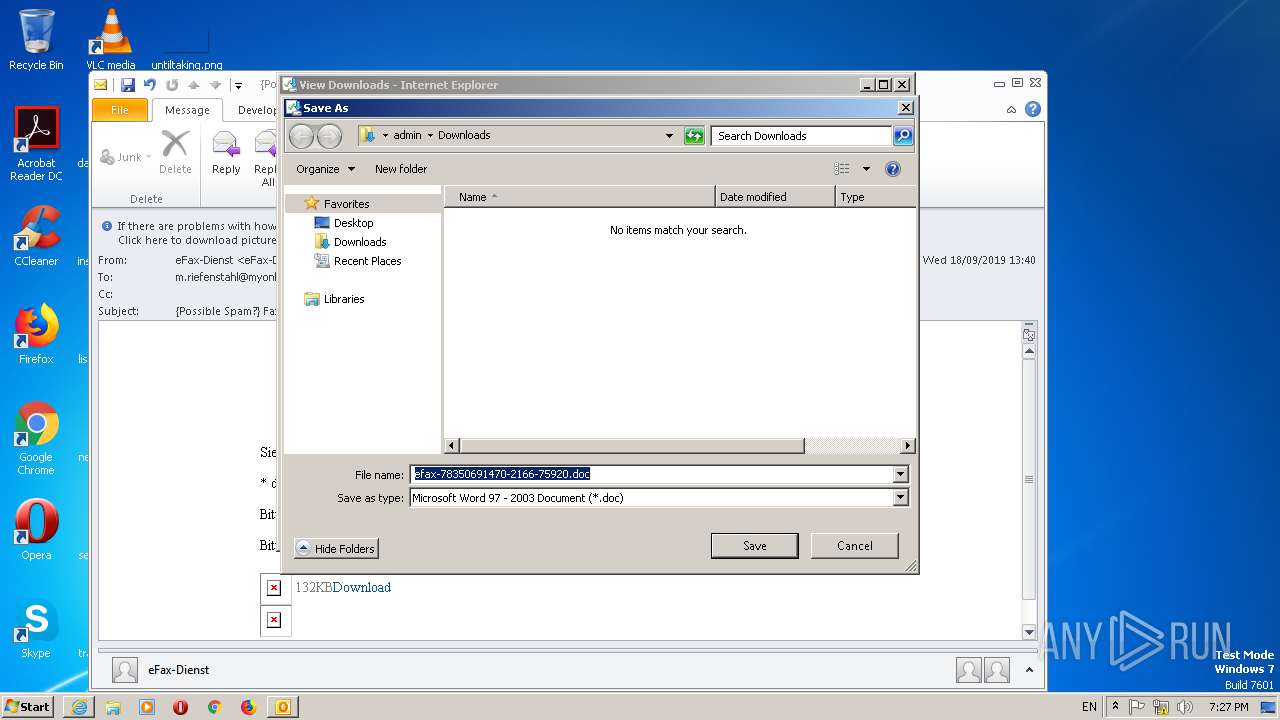
| 2872 | iexplore.exe | C:\Users\admin\Desktop\efax-78350691470-2166-75920.doc.kjzffhl.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\IECompatData\iecompatdata.xml | xml | |
MD5:— | SHA256:— | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B18CA973-09C0-4420-A422-EDC003D48D5D}.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFF76637827ED1A00B.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
12
DNS requests
13
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblocklist.bin | US | — | — | whitelisted |
580 | WINWORD.EXE | GET | 404 | 108.174.199.10:80 | http://108.174.199.10/wordupd3.tmp | US | html | 210 b | suspicious |
2872 | iexplore.exe | GET | 304 | 152.199.19.161:443 | https://iecvlist.microsoft.com/ie11blocklist/1401746408/versionlistWin7.xml | US | — | — | whitelisted |
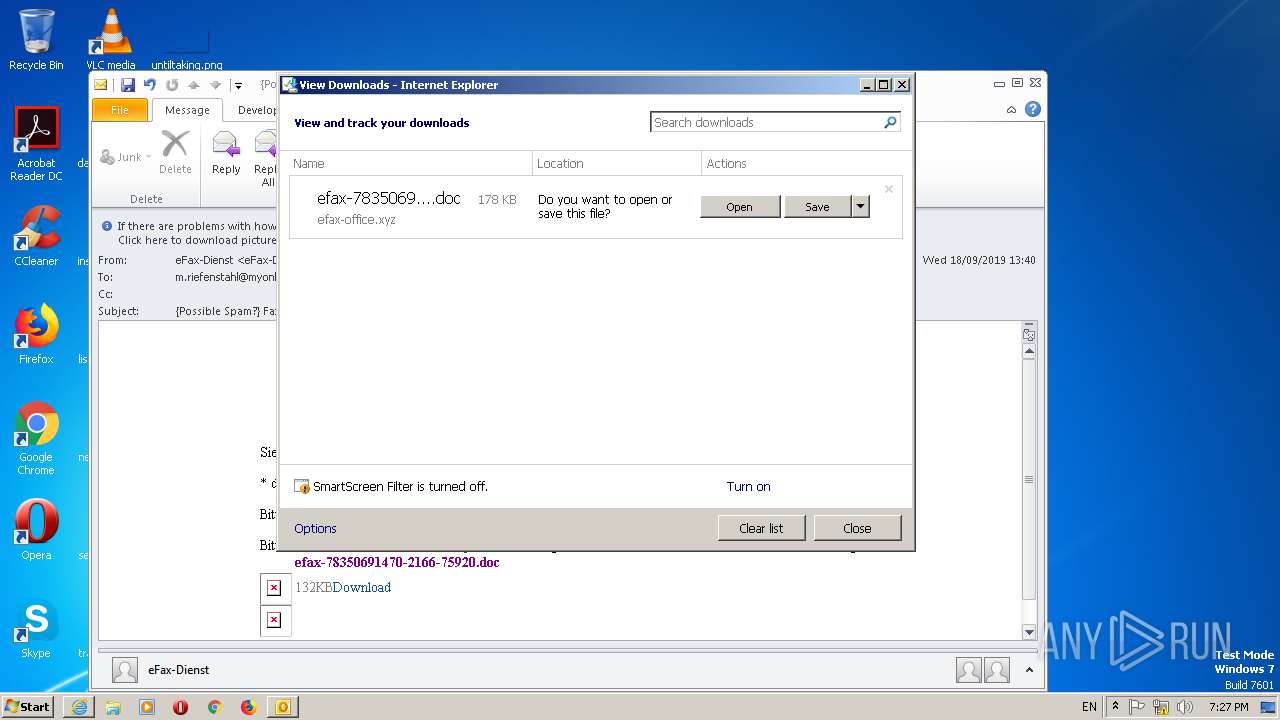
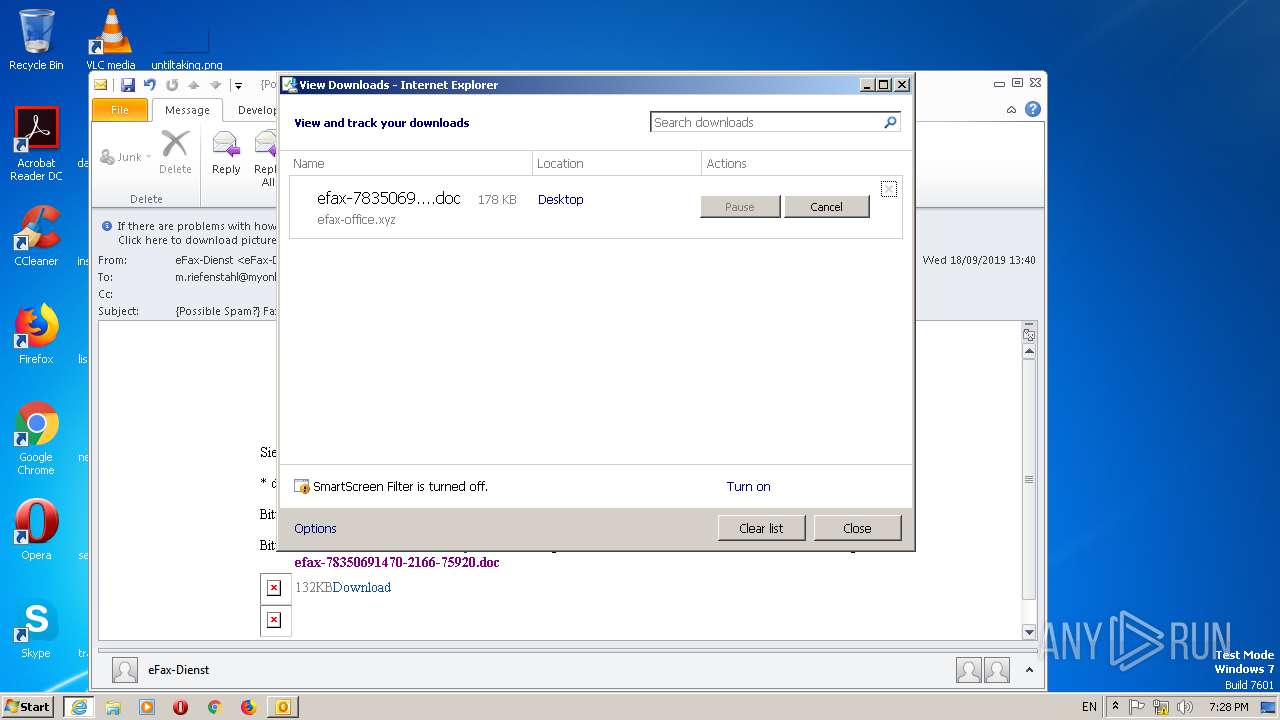
2544 | IEXPLORE.EXE | GET | 200 | 108.174.200.207:80 | http://efax-office.xyz/w.php?download=efax-78350691470-2166-75920 | US | document | 178 Kb | suspicious |
2872 | iexplore.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2872 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblockindex.bin | US | binary | 16 b | whitelisted |
2872 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://iecvlist.microsoft.com/IE11/1479242656000/iecompatviewlist.xml | US | xml | 352 Kb | whitelisted |
2872 | iexplore.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2248 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2544 | IEXPLORE.EXE | 108.174.199.105:80 | efaxcontrol.efaxenterprice.xyz | Hostwinds LLC. | US | suspicious |
580 | WINWORD.EXE | 108.174.199.10:80 | — | Hostwinds LLC. | US | suspicious |
2544 | IEXPLORE.EXE | 108.174.200.207:80 | efax-office.xyz | Hostwinds LLC. | US | suspicious |
2872 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
efaxcontrol.efaxenterprice.xyz |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
efax-office.xyz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | IEXPLORE.EXE | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2544 | IEXPLORE.EXE | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2544 | IEXPLORE.EXE | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project |