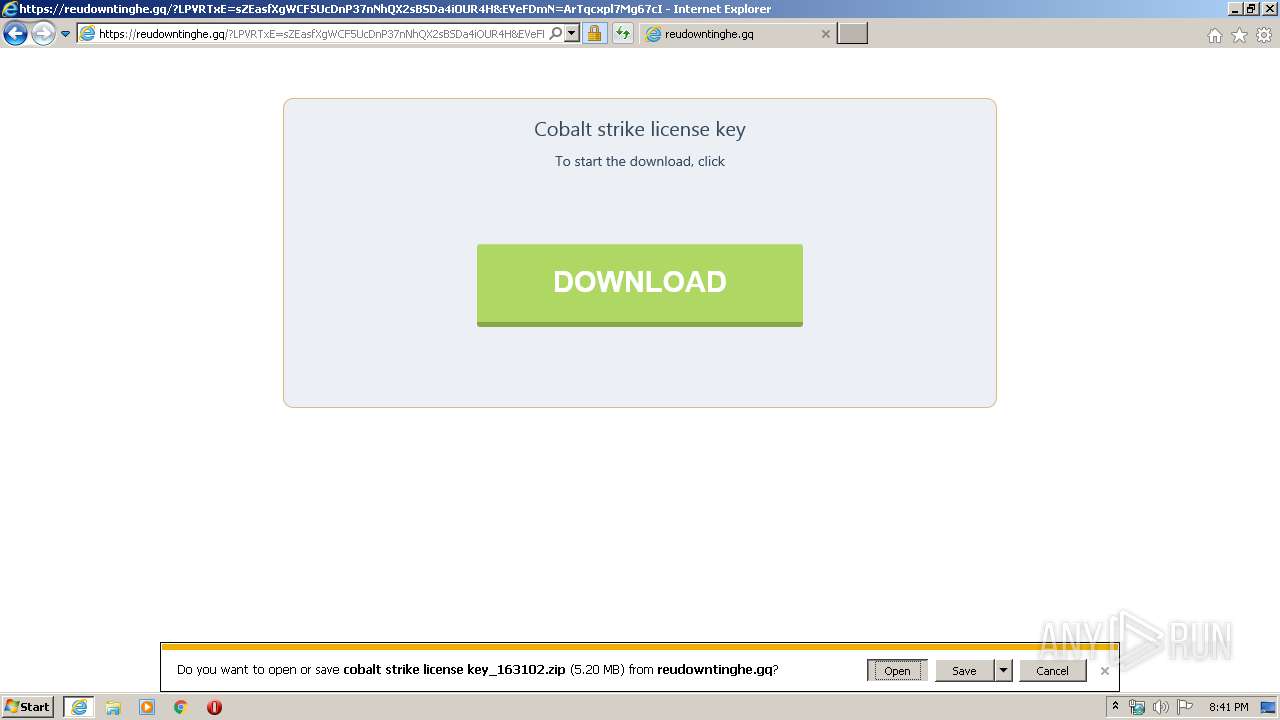
| URL: | http://prkrls.info/wprt41?x=Cobalt+strike+license+key |
| Full analysis: | https://app.any.run/tasks/0e0248cd-eb0a-49b5-b002-155f48428a4e |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2020, 20:41:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 71BF3DB257273AADFA9918DE76C1E1B3 |
| SHA1: | 5733DF7F3B633B9198DA5DC084A01F05C618AECD |
| SHA256: | 3664ADF632035D5B645F9B73183B9840F2E5E3B324B5ED1517ED5A0F3CC10DE9 |
| SSDEEP: | 3:N1KOX47RgRkwrJH+n:COXnSwrc |
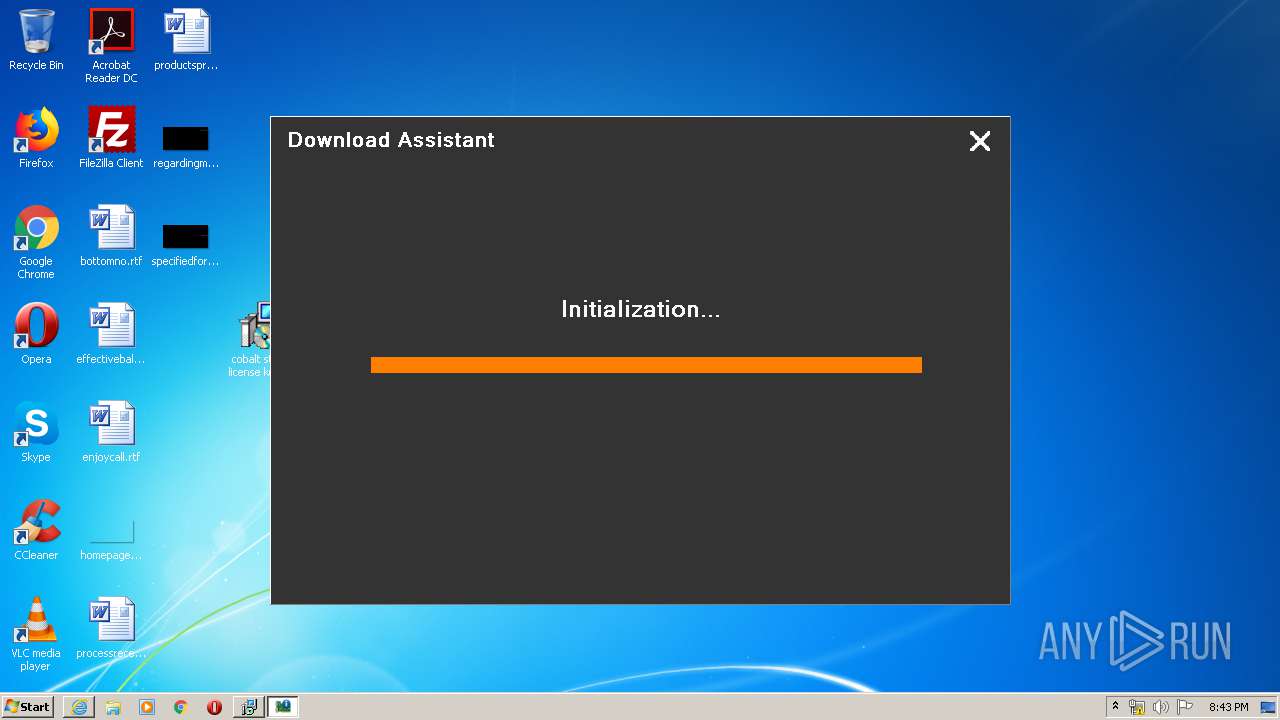
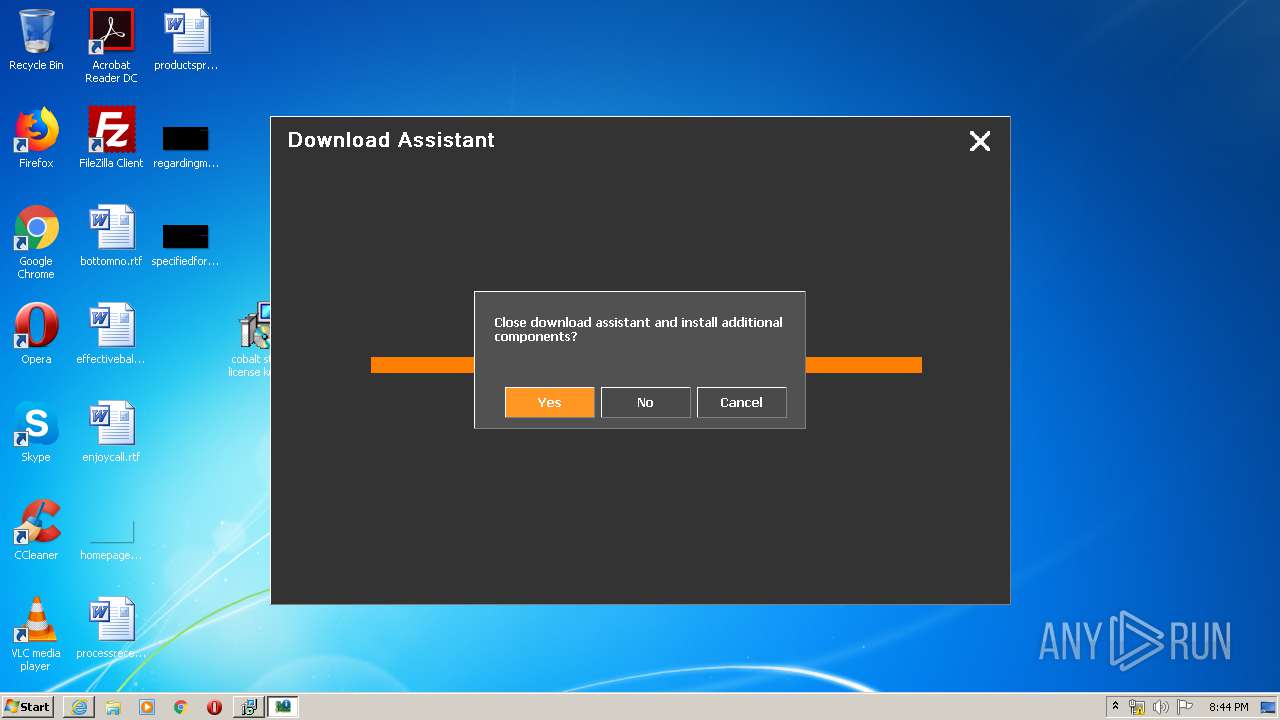
MALICIOUS
Application was dropped or rewritten from another process
- cobalt strike license key_163102.exe (PID: 3140)
- cobalt strike license key_163102.exe (PID: 3760)
- cobalt strike license key_163102.exe (PID: 4012)
- cobalt strike license key_163102.exe (PID: 2640)
SUSPICIOUS
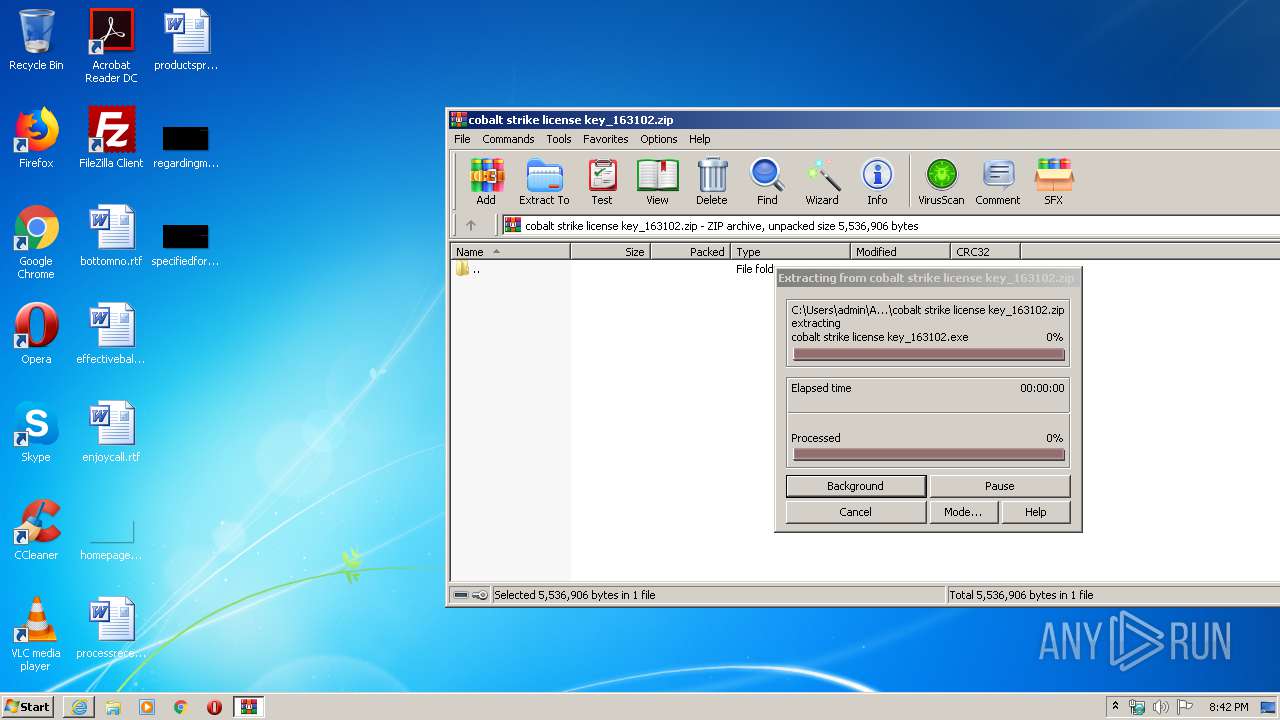
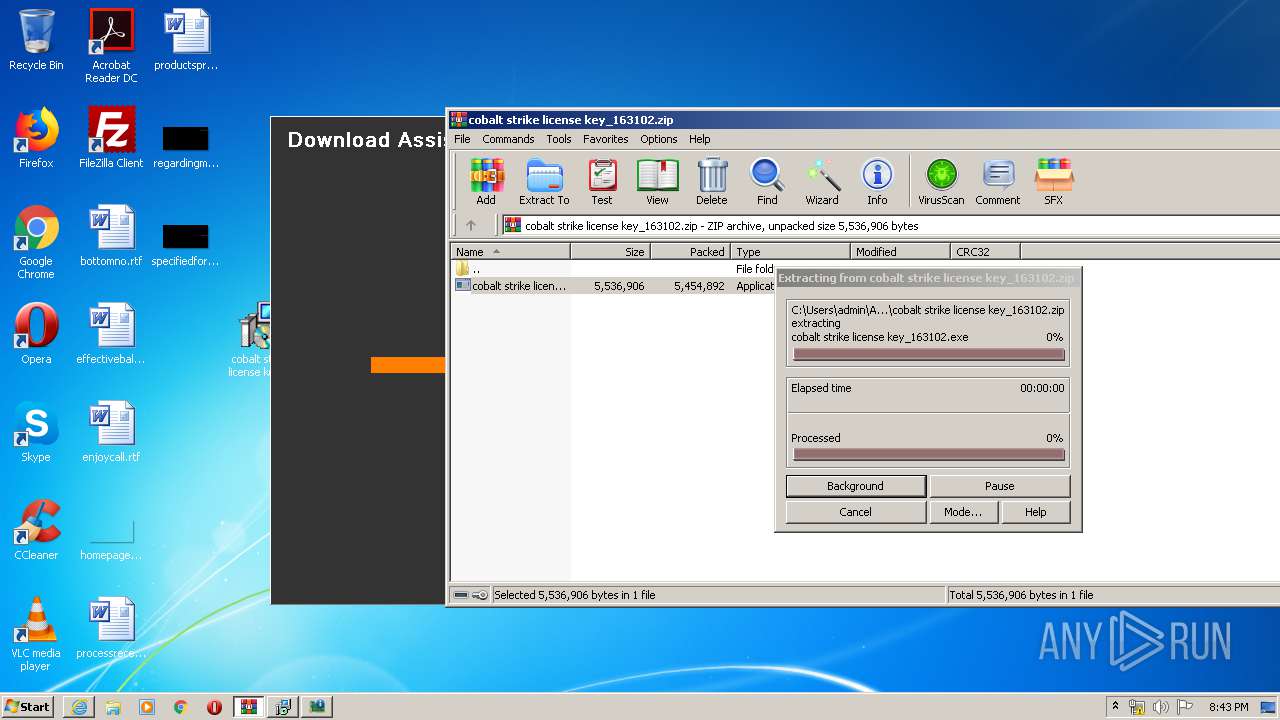
Executable content was dropped or overwritten
- cobalt strike license key_163102.exe (PID: 3140)
- cobalt strike license key_163102.exe (PID: 3760)
- cobalt strike license key_163102.tmp (PID: 3304)
- WinRAR.exe (PID: 3720)
- cobalt strike license key_163102.exe (PID: 4012)
- cobalt strike license key_163102.exe (PID: 2640)
- cobalt strike license key_163102.tmp (PID: 3536)
Reads Windows owner or organization settings
- cobalt strike license key_163102.tmp (PID: 3304)
- cobalt strike license key_163102.tmp (PID: 3536)
Reads the Windows organization settings
- cobalt strike license key_163102.tmp (PID: 3304)
- cobalt strike license key_163102.tmp (PID: 3536)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 3824)
Changes internet zones settings
- iexplore.exe (PID: 780)
Creates files in the user directory
- iexplore.exe (PID: 3824)
- iexplore.exe (PID: 780)
Reads internet explorer settings
- iexplore.exe (PID: 3824)
Modifies the phishing filter of IE
- iexplore.exe (PID: 780)
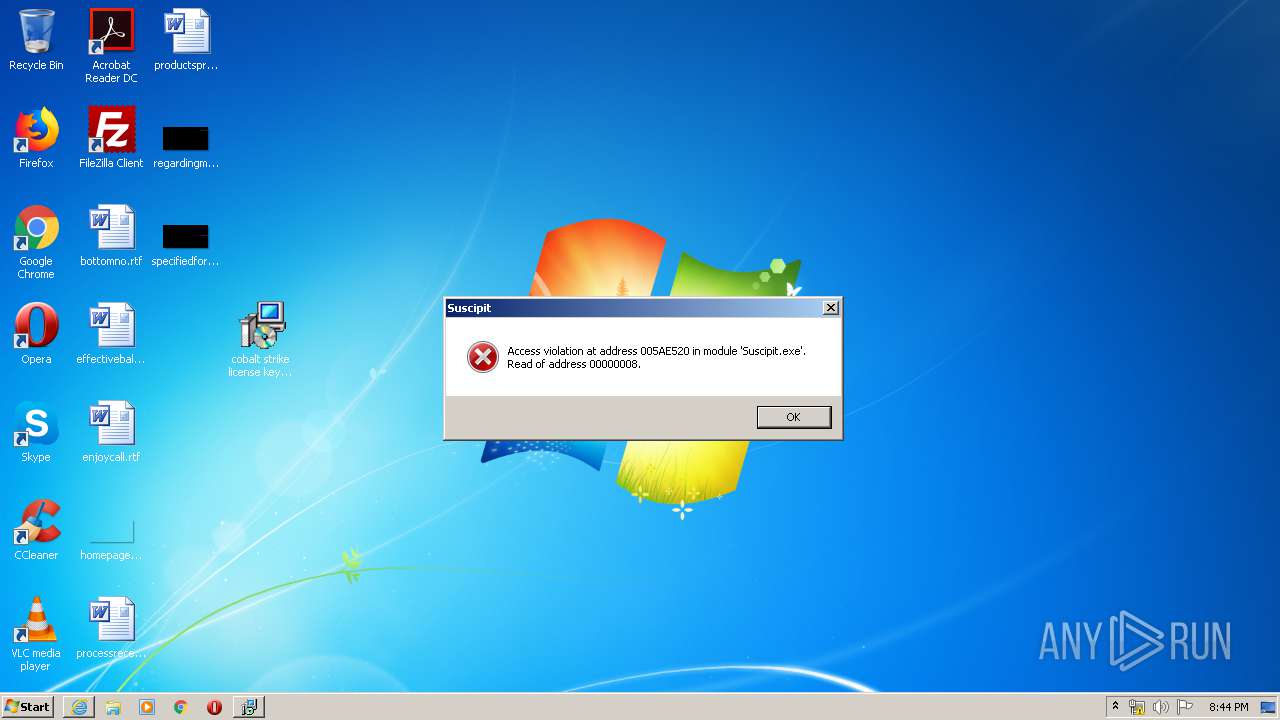
Application was dropped or rewritten from another process
- cobalt strike license key_163102.tmp (PID: 3972)
- cobalt strike license key_163102.tmp (PID: 3304)
- Suscipit.exe (PID: 2820)
- cobalt strike license key_163102.tmp (PID: 2364)
- cobalt strike license key_163102.tmp (PID: 3536)
- Suscipit.exe (PID: 3764)
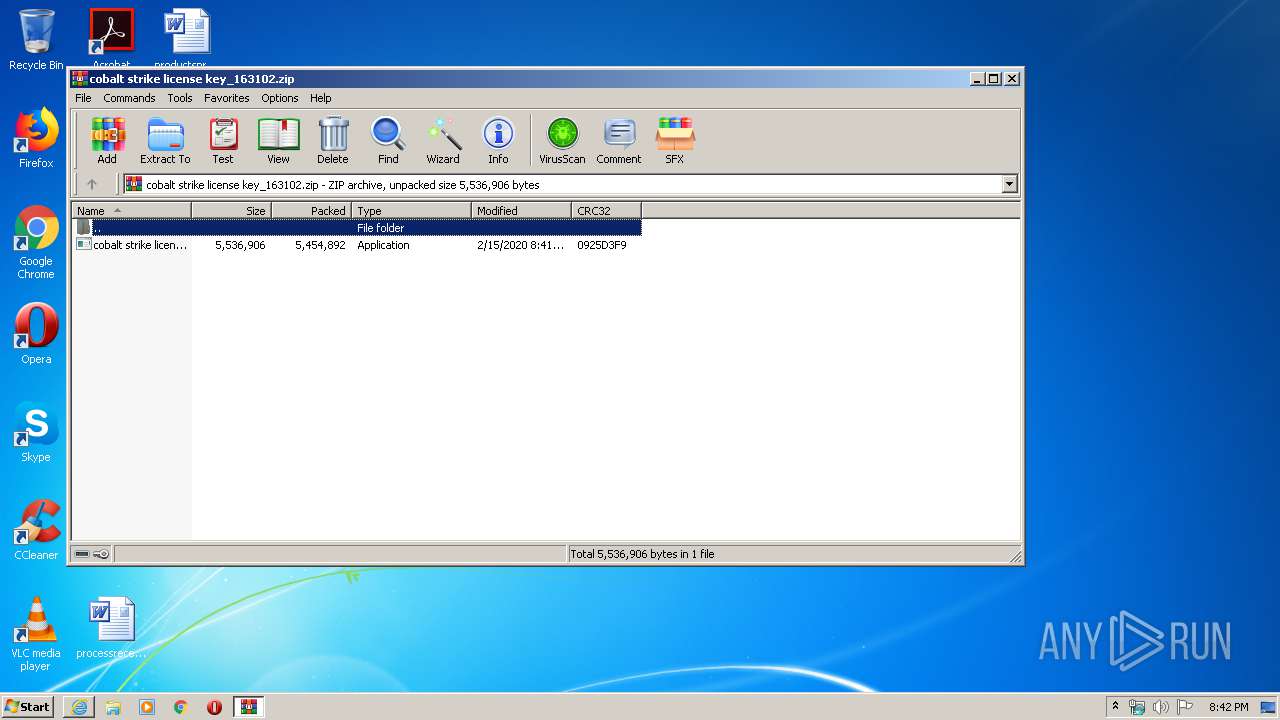
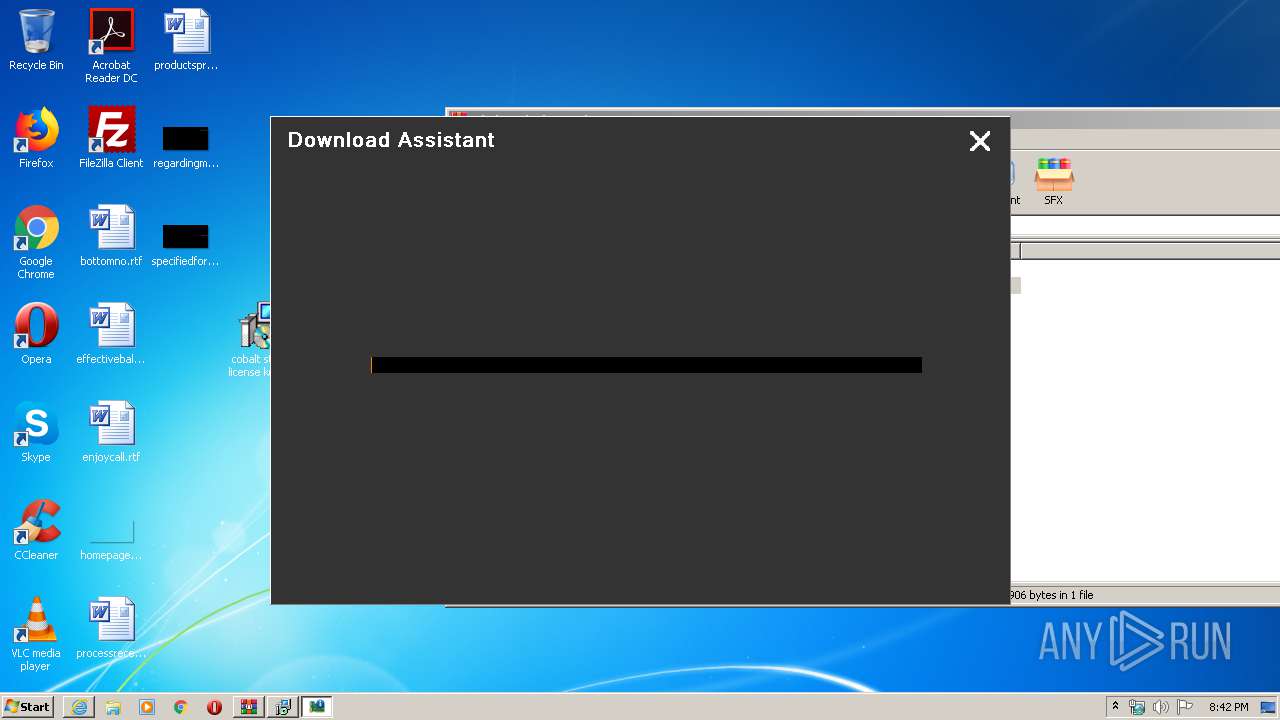
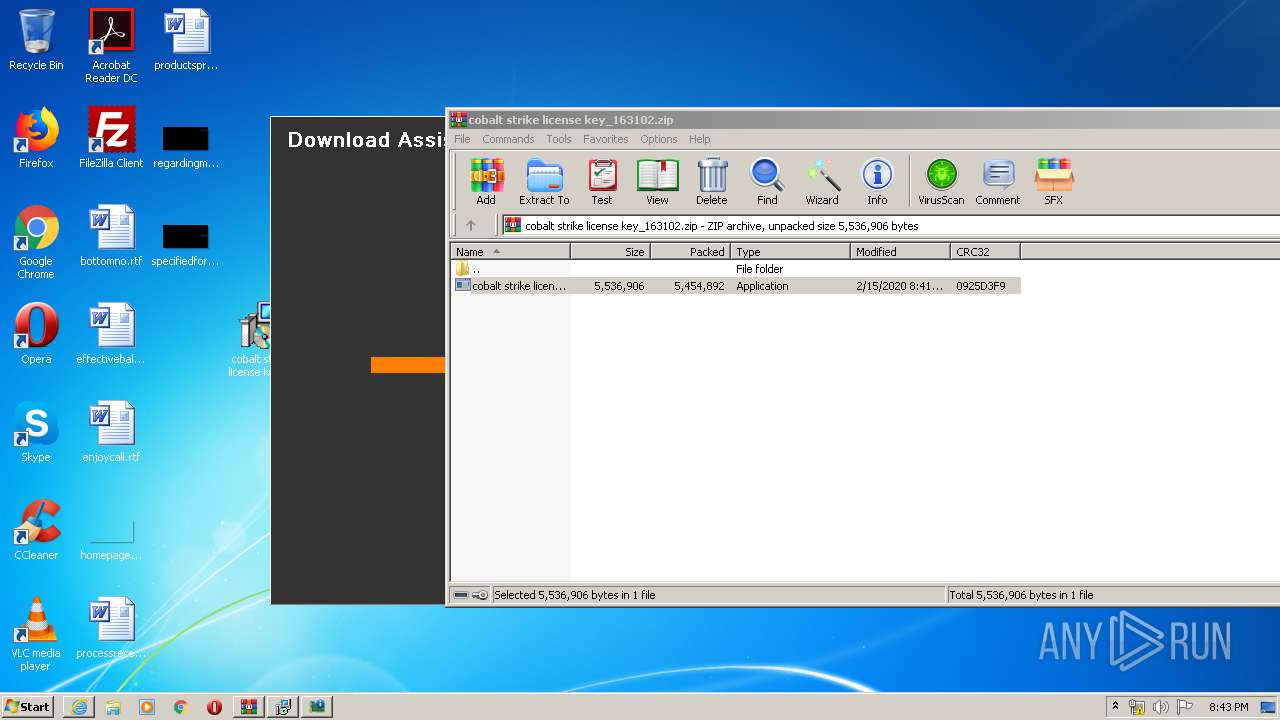
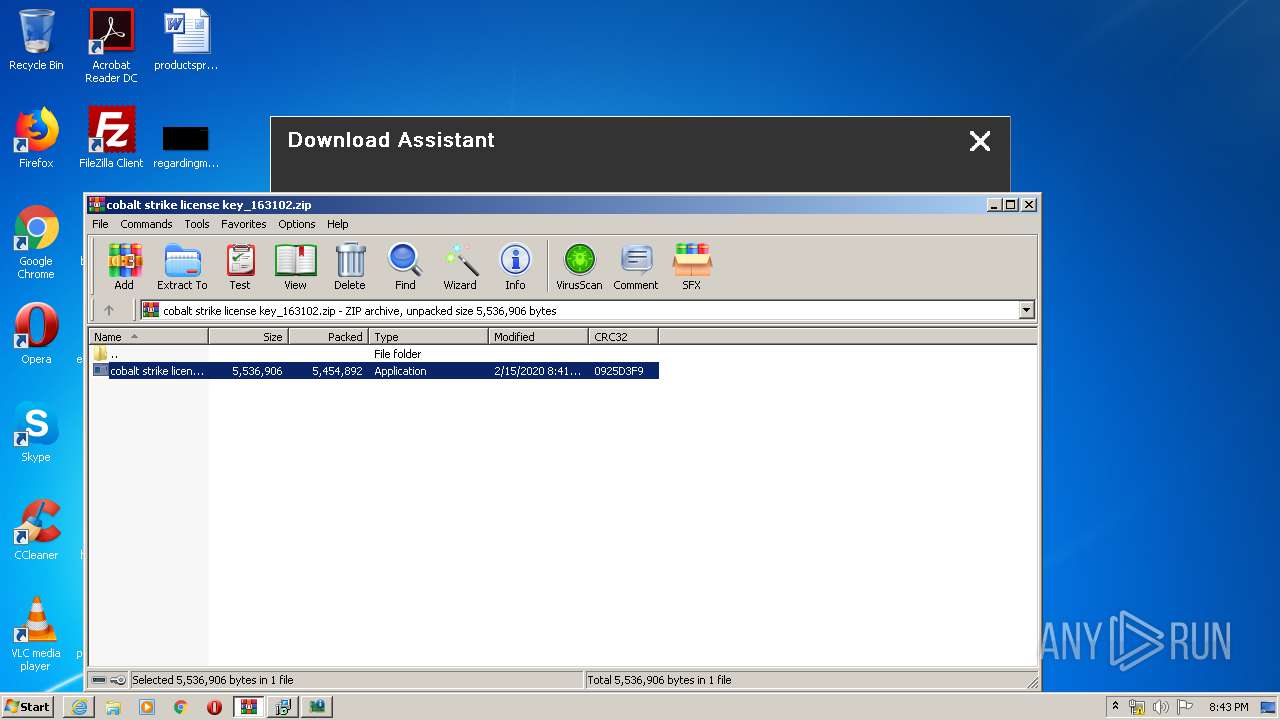
Manual execution by user
- cobalt strike license key_163102.exe (PID: 3140)
Loads dropped or rewritten executable
- cobalt strike license key_163102.tmp (PID: 3304)
- cobalt strike license key_163102.tmp (PID: 3536)
Reads settings of System Certificates
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 3824)
Changes settings of System certificates
- iexplore.exe (PID: 780)
Adds / modifies Windows certificates
- iexplore.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
13
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://prkrls.info/wprt41?x=Cobalt+strike+license+key" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Temp\is-1N8O1.tmp\cobalt strike license key_163102.tmp" /SL5="$701F2,5138411,119296,C:\Users\admin\AppData\Local\Temp\Rar$EXa3720.42777\cobalt strike license key_163102.exe" | C:\Users\admin\AppData\Local\Temp\is-1N8O1.tmp\cobalt strike license key_163102.tmp | — | cobalt strike license key_163102.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2640 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3720.42777\cobalt strike license key_163102.exe" /SPAWNWND=$901DC /NOTIFYWND=$701F2 | C:\Users\admin\AppData\Local\Temp\Rar$EXa3720.42777\cobalt strike license key_163102.exe | cobalt strike license key_163102.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Magni ipsam 644bd10f09e78140c6fd43c8748de0e5 vero quam Exit code: 1 Version: Modules
| |||||||||||||||
| 2820 | "C:\Users\admin\AppData\Local\Temp\is-OL3SV.tmp\Suscipit.exe" 644bd10f09e78140c6fd43c8748de0e5 | C:\Users\admin\AppData\Local\Temp\is-OL3SV.tmp\Suscipit.exe | cobalt strike license key_163102.tmp | ||||||||||||
User: admin Company: Nanogi Upalo Integrity Level: HIGH Description: Holierty Exit code: 0 Version: 2.25.6.41 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\Desktop\cobalt strike license key_163102.exe" | C:\Users\admin\Desktop\cobalt strike license key_163102.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Magni ipsam 644bd10f09e78140c6fd43c8748de0e5 vero quam Exit code: 0 Version: Modules
| |||||||||||||||
| 3304 | "C:\Users\admin\AppData\Local\Temp\is-8AE6C.tmp\cobalt strike license key_163102.tmp" /SL5="$901AE,5138411,119296,C:\Users\admin\Desktop\cobalt strike license key_163102.exe" /SPAWNWND=$801FC /NOTIFYWND=$50292 | C:\Users\admin\AppData\Local\Temp\is-8AE6C.tmp\cobalt strike license key_163102.tmp | cobalt strike license key_163102.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3536 | "C:\Users\admin\AppData\Local\Temp\is-5FP5K.tmp\cobalt strike license key_163102.tmp" /SL5="$14025A,5138411,119296,C:\Users\admin\AppData\Local\Temp\Rar$EXa3720.42777\cobalt strike license key_163102.exe" /SPAWNWND=$901DC /NOTIFYWND=$701F2 | C:\Users\admin\AppData\Local\Temp\is-5FP5K.tmp\cobalt strike license key_163102.tmp | cobalt strike license key_163102.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
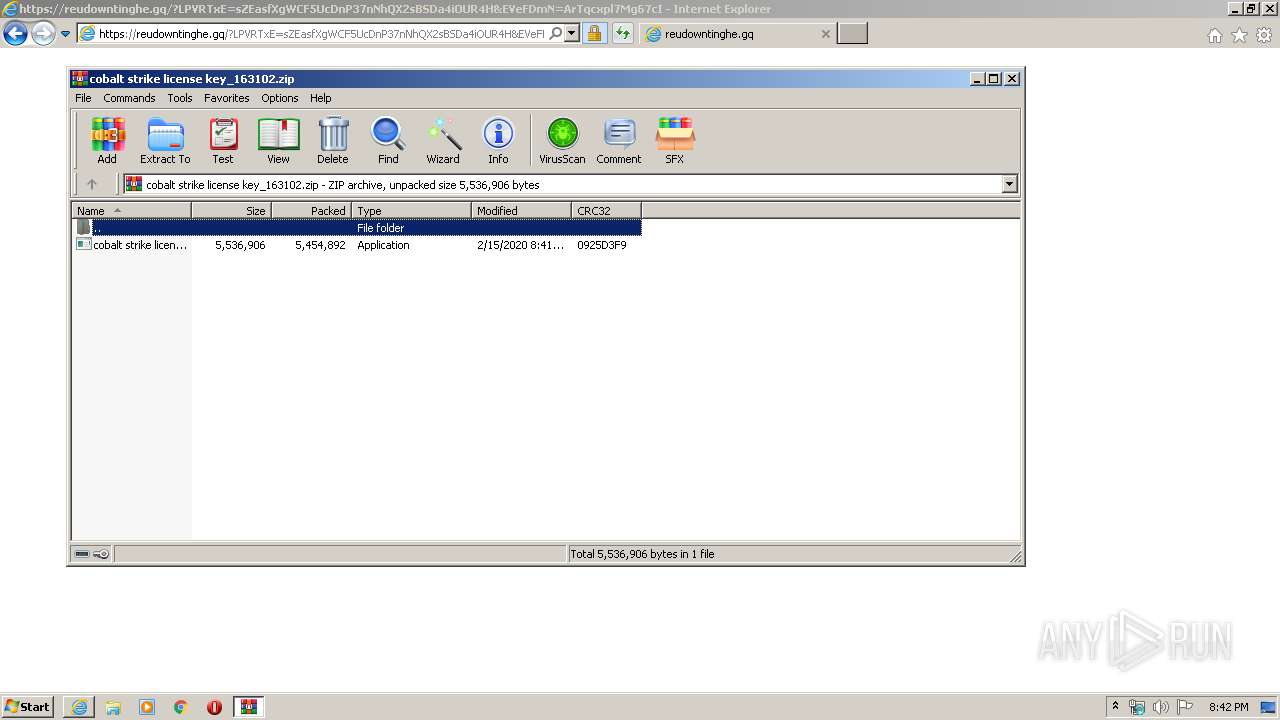
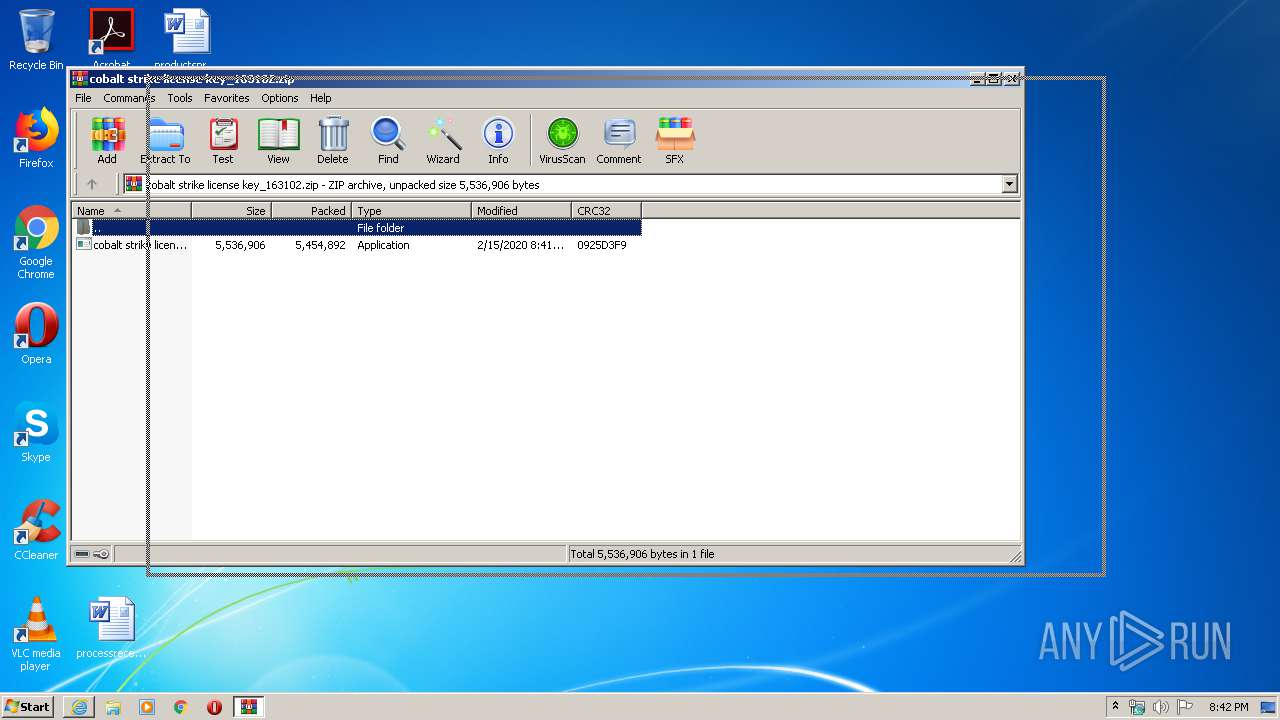
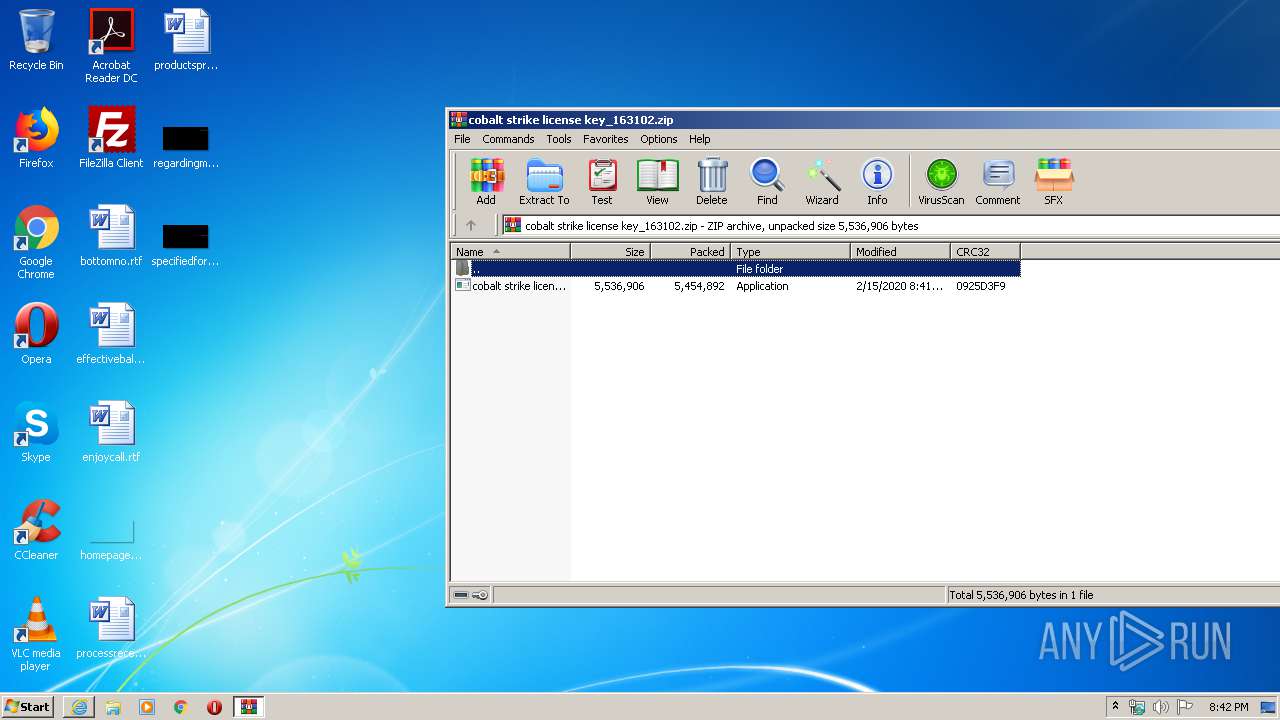
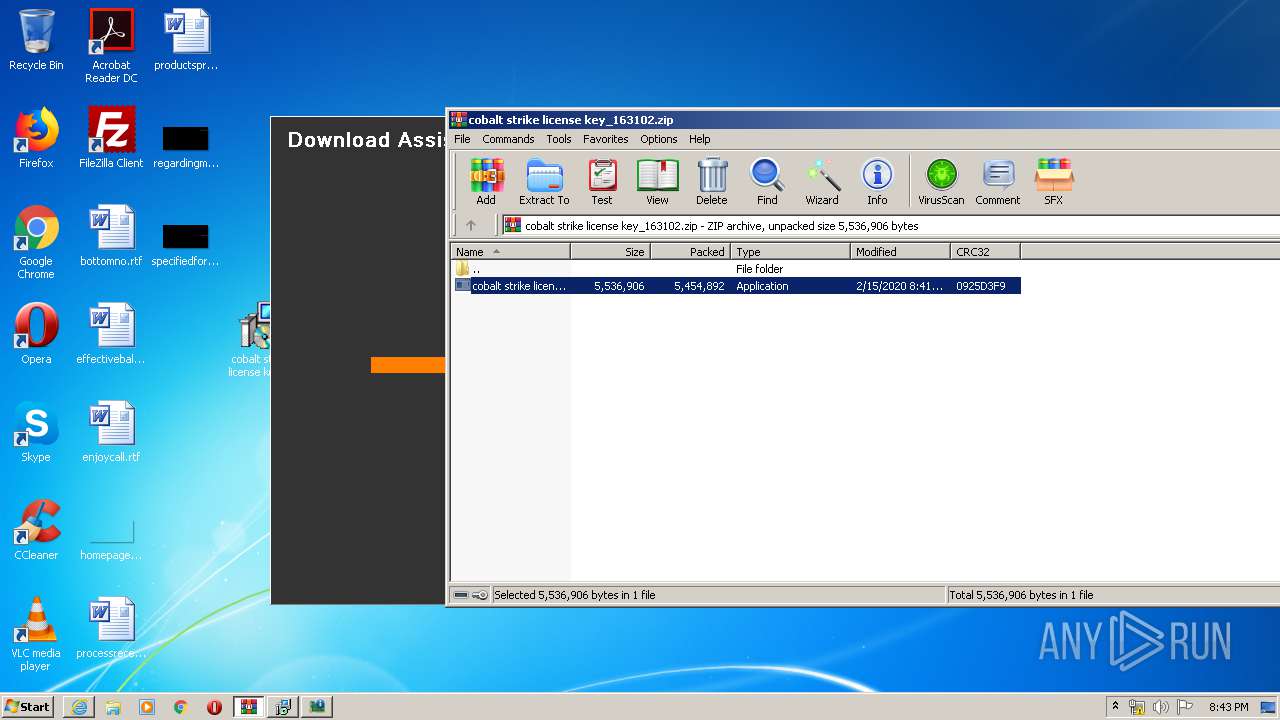
| 3720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\cobalt strike license key_163102.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\Desktop\cobalt strike license key_163102.exe" /SPAWNWND=$801FC /NOTIFYWND=$50292 | C:\Users\admin\Desktop\cobalt strike license key_163102.exe | cobalt strike license key_163102.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Magni ipsam 644bd10f09e78140c6fd43c8748de0e5 vero quam Exit code: 0 Version: Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\AppData\Local\Temp\is-5UKDD.tmp\Suscipit.exe" 644bd10f09e78140c6fd43c8748de0e5 | C:\Users\admin\AppData\Local\Temp\is-5UKDD.tmp\Suscipit.exe | — | cobalt strike license key_163102.tmp | |||||||||||
User: admin Company: Nanogi Upalo Integrity Level: HIGH Description: Holierty Exit code: 0 Version: 2.25.6.41 Modules
| |||||||||||||||
Total events
6 727
Read events
1 979
Write events
3 184
Delete events
1 564
Modification events
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1753447464 | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30794816 | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
9
Suspicious files
23
Text files
13
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7150.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7151.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WQ37RWQU.txt | — | |
MD5:— | SHA256:— | |||
| 780 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ER989HF8.htm | — | |
MD5:— | SHA256:— | |||
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\B22DG3N0.htm | — | |
MD5:— | SHA256:— | |||
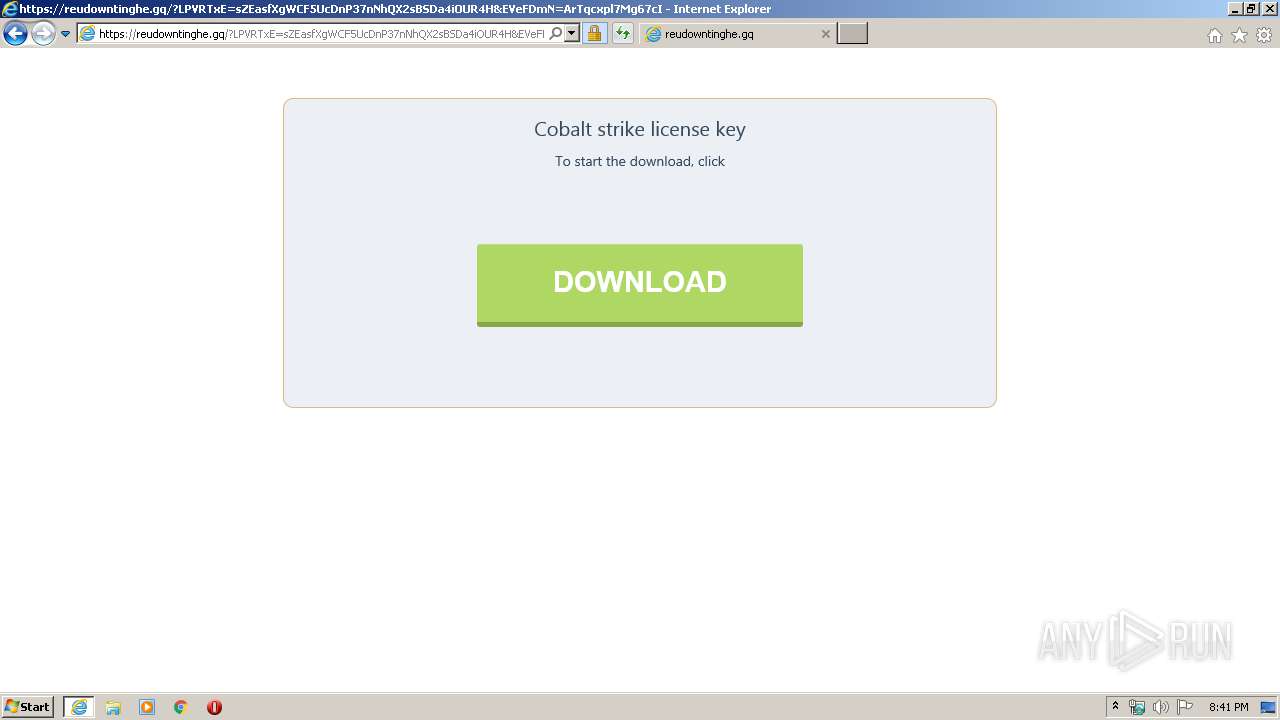
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cobalt strike license key_163102[1].zip | — | |
MD5:— | SHA256:— | |||
| 780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\cobalt strike license key_163102.zip.bhbvdjo.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\mmd[1].htm | html | |
MD5:— | SHA256:— | |||
| 3824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
27
DNS requests
15
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | iexplore.exe | GET | 302 | 100.24.195.233:80 | http://prkrls.info/wprt41?x=Cobalt+strike+license+key | US | html | 431 b | unknown |
3824 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
780 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgOkv4FlA8k2KsOr6Tra9uWvPg%3D%3D | unknown | der | 527 b | whitelisted |
3824 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgOkv4FlA8k2KsOr6Tra9uWvPg%3D%3D | unknown | der | 527 b | whitelisted |
3824 | iexplore.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
780 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPs2qYwYnR%2FfYhFYXGPJOCkCA%3D%3D | unknown | der | 527 b | whitelisted |
2820 | Suscipit.exe | POST | — | 104.18.45.18:80 | http://giliafundation.life/v2/events | US | — | — | malicious |
3824 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | iexplore.exe | 100.24.195.233:80 | prkrls.info | — | US | unknown |
3824 | iexplore.exe | 78.140.165.14:443 | bestlout1on.space | Webzilla B.V. | NL | malicious |
3824 | iexplore.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3824 | iexplore.exe | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
3824 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3824 | iexplore.exe | 88.85.69.166:443 | 1getbestf1le3.xyz | Webzilla B.V. | NL | suspicious |
3824 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3824 | iexplore.exe | 104.18.37.141:443 | reudowntinghe.gq | Cloudflare Inc | US | shared |
780 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
780 | iexplore.exe | 104.18.37.141:443 | reudowntinghe.gq | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prkrls.info |
| unknown |
bestlout1on.space |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
1getbestf1le3.xyz |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
reudowntinghe.gq |
| suspicious |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3824 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
3824 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.gq) in TLS SNI |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
2820 | Suscipit.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2820 | Suscipit.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |