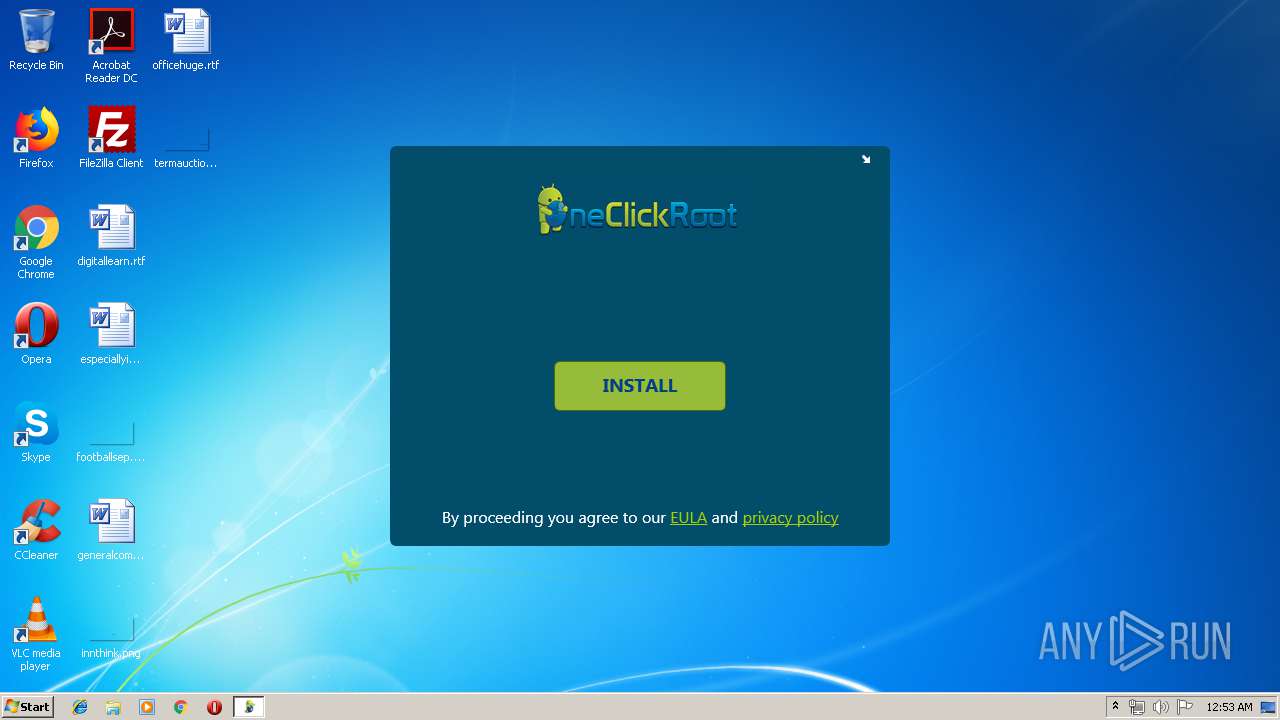
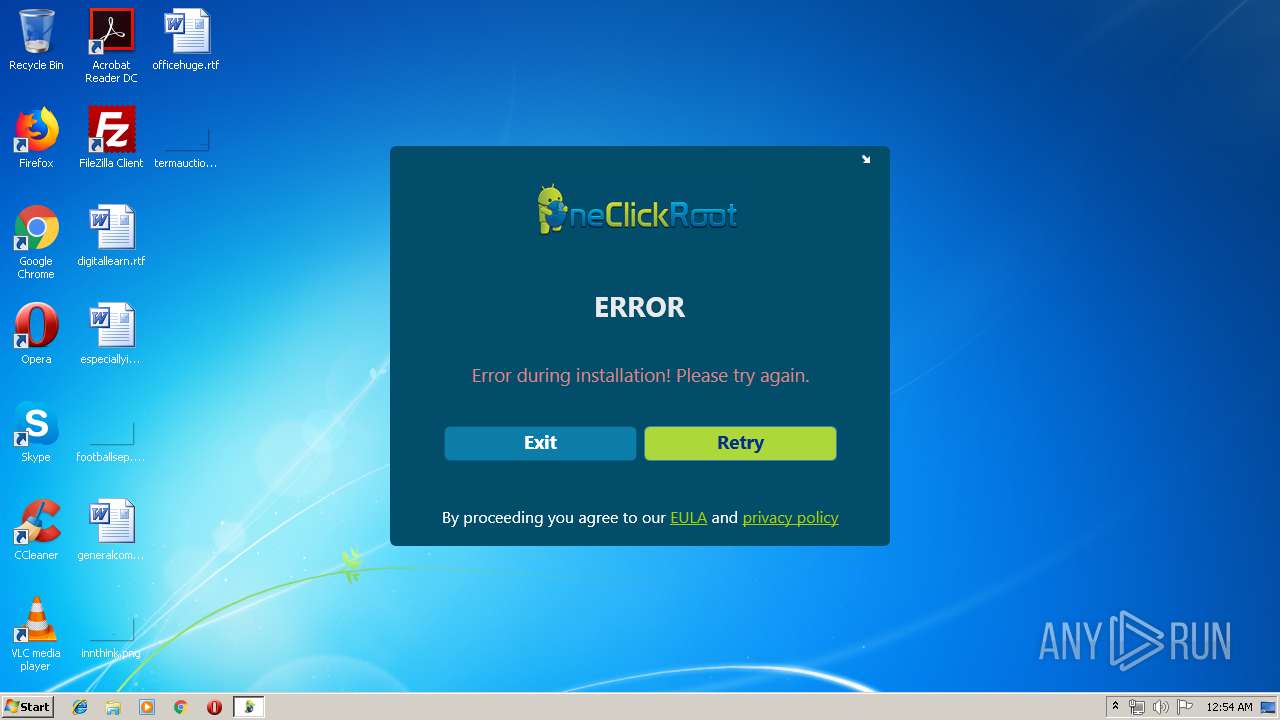
| File name: | OneClickRoot.exe |
| Full analysis: | https://app.any.run/tasks/79fd4197-50b9-454b-8758-3db979701da8 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 23:53:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 99E964AC25F56A0661C9F7BC92746FA5 |
| SHA1: | E93A5A0269F0CE7E6F34E8025E33AD6A3473D6B2 |
| SHA256: | 364CD6AE3AB10E8382560E7F07084F69EB5251A9564C0D60F23DF7613A0619AF |
| SSDEEP: | 24576:siPIjEz01QJvOyLVRYH0ofC0h0004QgIukoj:siQi7VRYUWBh0004QFA |
MALICIOUS
Changes settings of System certificates
- OneClickRoot.exe (PID: 1520)
SUSPICIOUS
Reads Environment values
- OneClickRoot.exe (PID: 1520)
Adds / modifies Windows certificates
- OneClickRoot.exe (PID: 1520)
Searches for installed software
- OneClickRoot.exe (PID: 1520)
INFO
Reads settings of System Certificates
- OneClickRoot.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:13 10:18:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1009152 |
| InitializedDataSize: | 20992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf84f6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.3 |
| ProductVersionNumber: | 1.0.0.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WebInstaller |
| FileVersion: | 1.0.0.3 |
| InternalName: | WebInstaller.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | WebInstaller.exe |
| ProductName: | WebInstaller |
| ProductVersion: | 1.0.0.3 |
| AssemblyVersion: | 1.0.0.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Dec-2017 09:18:30 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WebInstaller |
| FileVersion: | 1.0.0.3 |
| InternalName: | WebInstaller.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | WebInstaller.exe |
| ProductName: | WebInstaller |
| ProductVersion: | 1.0.0.3 |
| Assembly Version: | 1.0.0.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Dec-2017 09:18:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000F64FC | 0x000F6600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53411 |
.rsrc | 0x000FA000 | 0x00004EA4 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01836 |
.reloc | 0x00100000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.4562 | 3820 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.35911 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.19914 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.45849 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Users\admin\AppData\Local\Temp\OneClickRoot.exe" | C:\Users\admin\AppData\Local\Temp\OneClickRoot.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WebInstaller Exit code: 3221226540 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Temp\OneClickRoot.exe" | C:\Users\admin\AppData\Local\Temp\OneClickRoot.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WebInstaller Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 3956 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
503
Read events
477
Write events
26
Delete events
0
Modification events
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: OneClickRoot.exe | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000001400000085FEF11B4F47FE3952F98301C9F98976FEFEE0CE09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C01400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB5748501D00000001000000100000005B3B67000EEB80022E42605B6B3B72400B000000010000000E000000740068006100770074006500000003000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000DC73F9B71E16D51D26527D32B11A6A3D03000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B810B000000010000000E00000074006800610077007400650000001D00000001000000100000005B3B67000EEB80022E42605B6B3B72401400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB57485053000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C009000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B060105050703030F000000010000001400000085FEF11B4F47FE3952F98301C9F98976FEFEE0CE2000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OneClickRoot_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OneClickRoot_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OneClickRoot_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OneClickRoot_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OneClickRoot_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1520) OneClickRoot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OneClickRoot_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
5
Text files
10
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\Cab4032.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\Tar4033.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\Cab4044.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\Tar4045.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\Cab40D3.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\Tar40D4.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\Temp\OneClickRoot Installer\Yandex.Metrica.CriticalConfig.json | text | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 1520 | OneClickRoot.exe | C:\Users\admin\AppData\Local\IsolatedStorage\mogk2t2c.5hh\u1zwgpet.l2j\Publisher.gy4q2b5oaxhxajef0mxqxe3jqgyjaqwu\Publisher.gy4q2b5oaxhxajef0mxqxe3jqgyjaqwu\identity.dat | pi2 | |
MD5:9013E447D03BDD5309AE938474E38D46 | SHA256:B85E2BB404B65DCD987B2A74C7917D136742EC911E43BEBBE4005B06E03AC607 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1520 | OneClickRoot.exe | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
1520 | OneClickRoot.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | OneClickRoot.exe | 213.180.204.244:443 | startup.mobile.yandex.net | YANDEX LLC | RU | whitelisted |
1520 | OneClickRoot.exe | 23.111.11.204:80 | repository.certum.pl | netDNA | US | unknown |
1520 | OneClickRoot.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
1520 | OneClickRoot.exe | 87.250.250.207:443 | report.appmetrica.yandex.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
startup.mobile.yandex.net |
| whitelisted |
report.appmetrica.yandex.net |
| whitelisted |
repository.certum.pl |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |