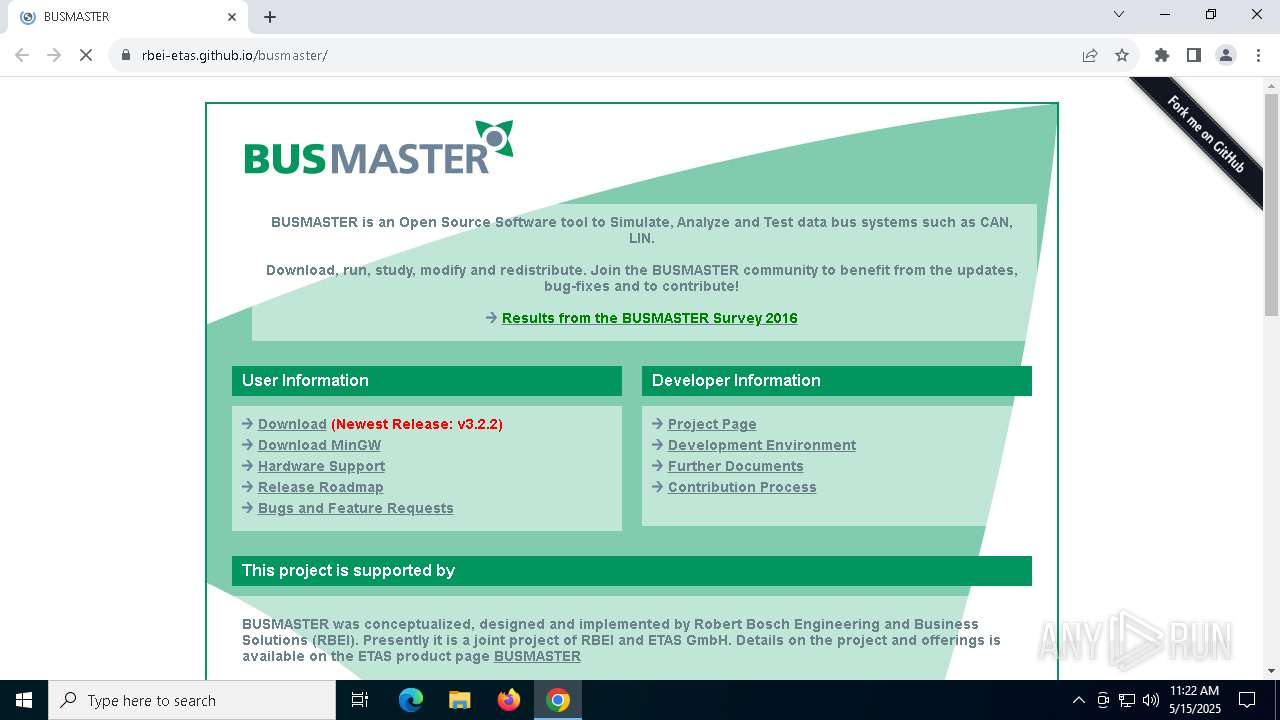
| URL: | https://rbei-etas.github.io/busmaster/ |
| Full analysis: | https://app.any.run/tasks/0ef01b24-3efa-4919-b092-424720da6838 |
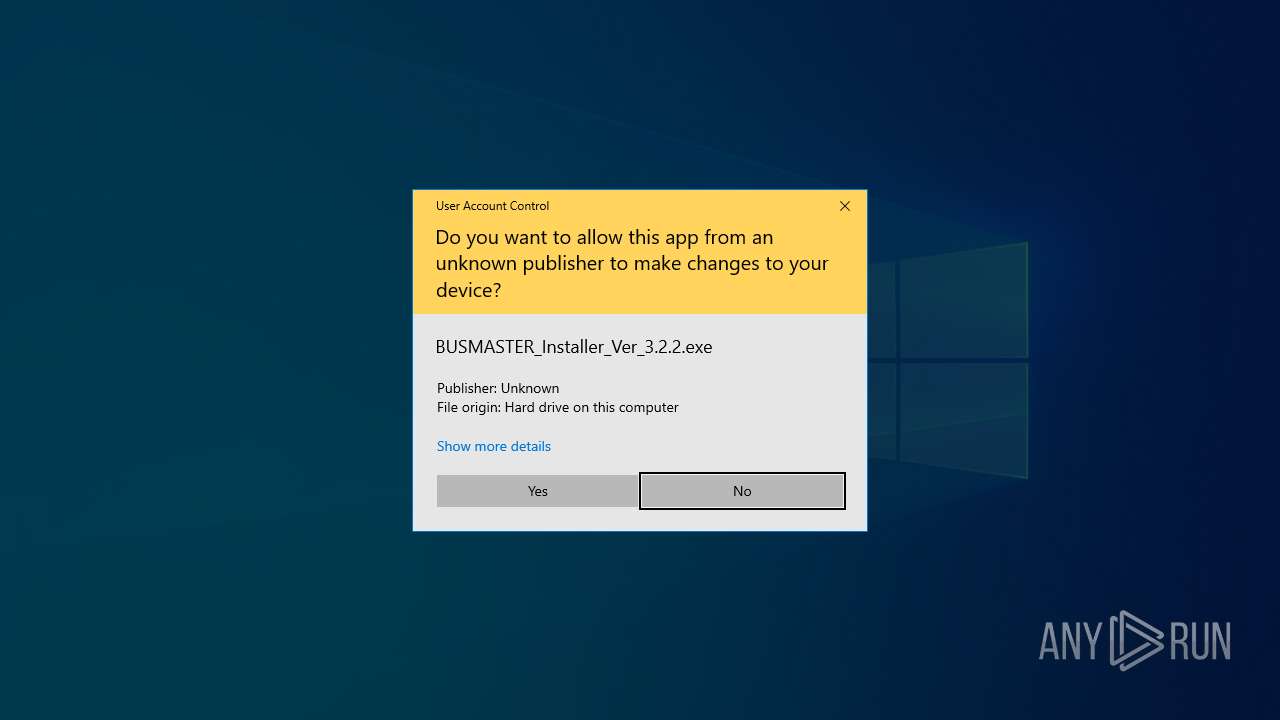
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 11:21:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 4B6BF95C48E3FB9D5B48F7AA00FDFD21 |
| SHA1: | 66C1C4F21F5698AAD68BE508B9E4111CDDA019C8 |
| SHA256: | 3649D5CE3061A050DD9780B4ACDB9FF1599C32940561E683C0FF6DA7235DD277 |
| SSDEEP: | 3:N8sW34UsAXK:2sVbAXK |
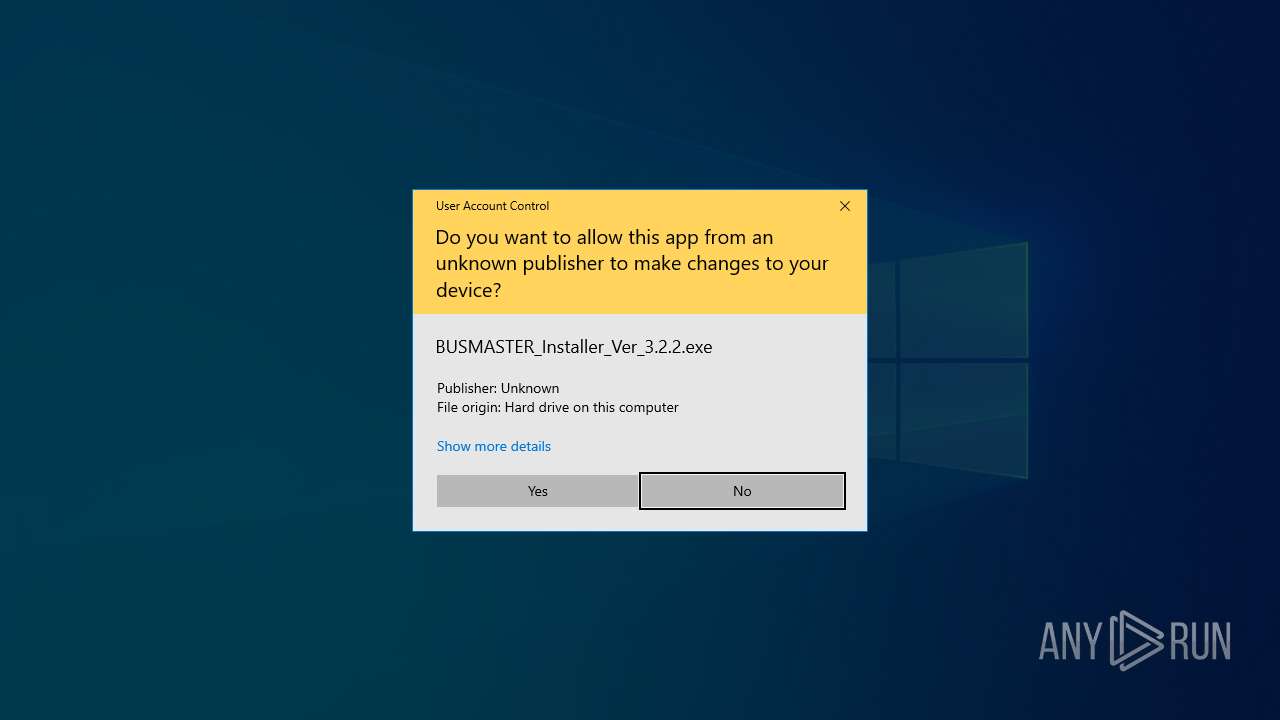
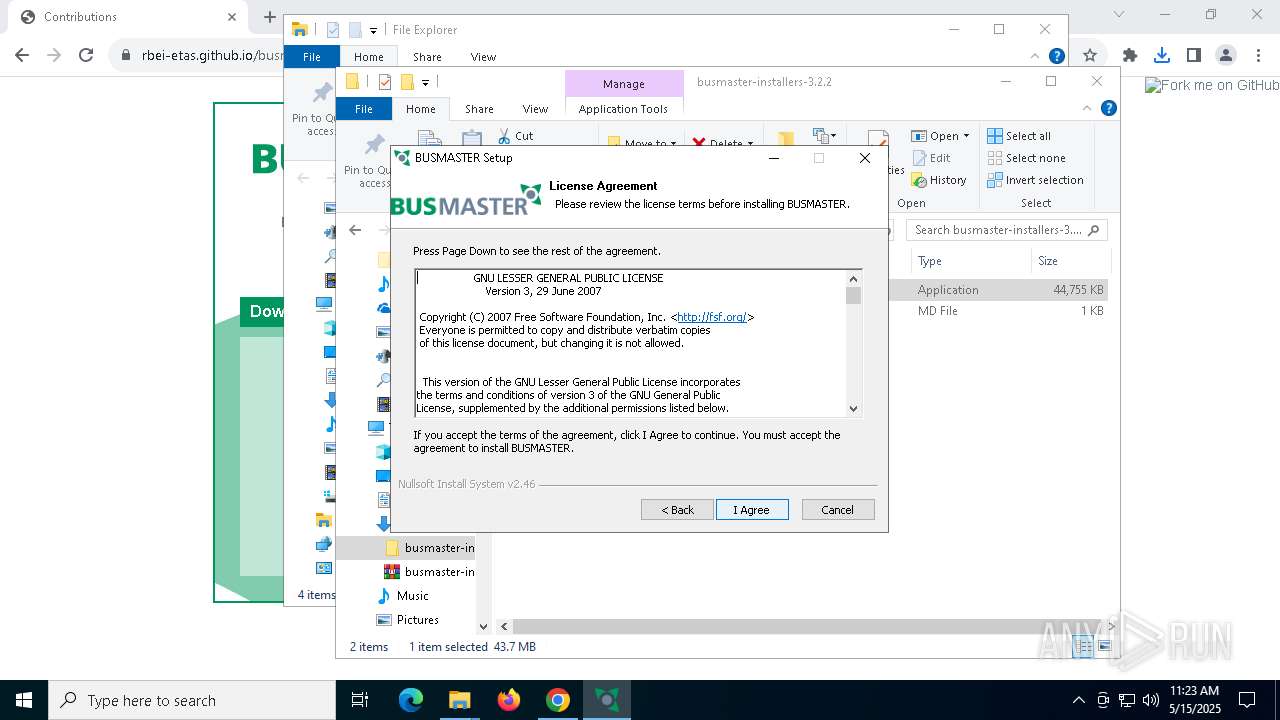
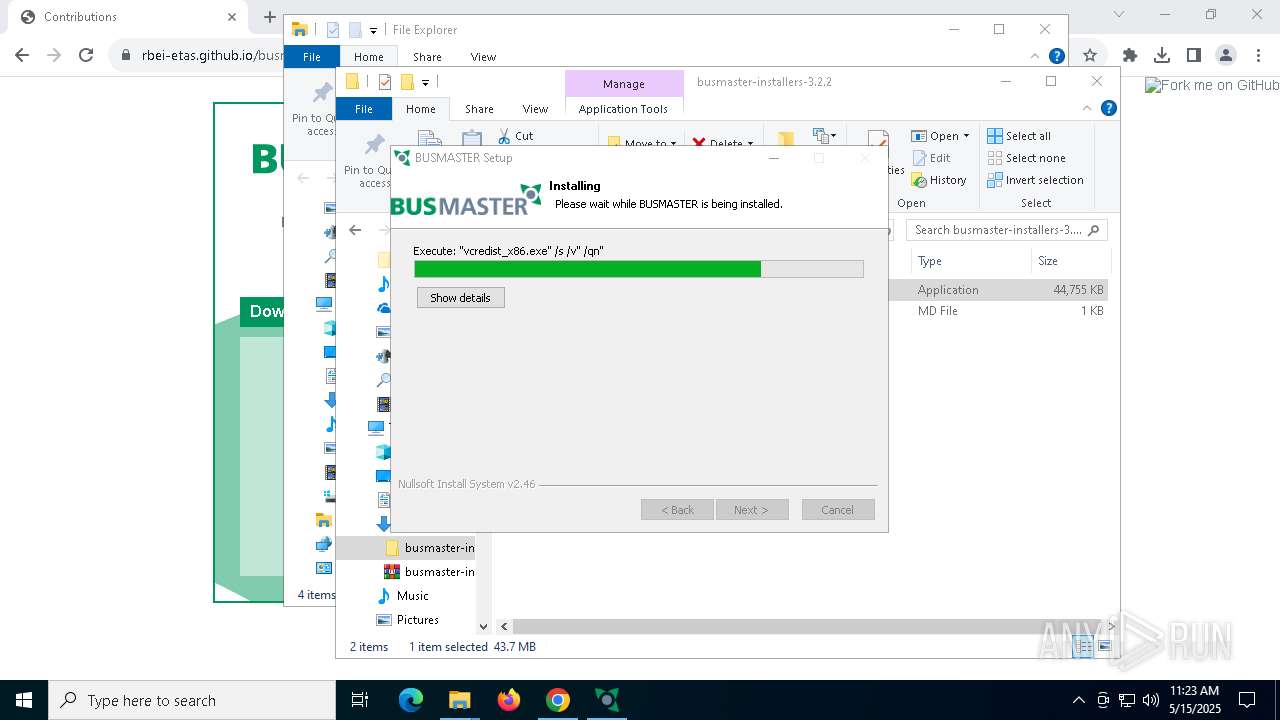
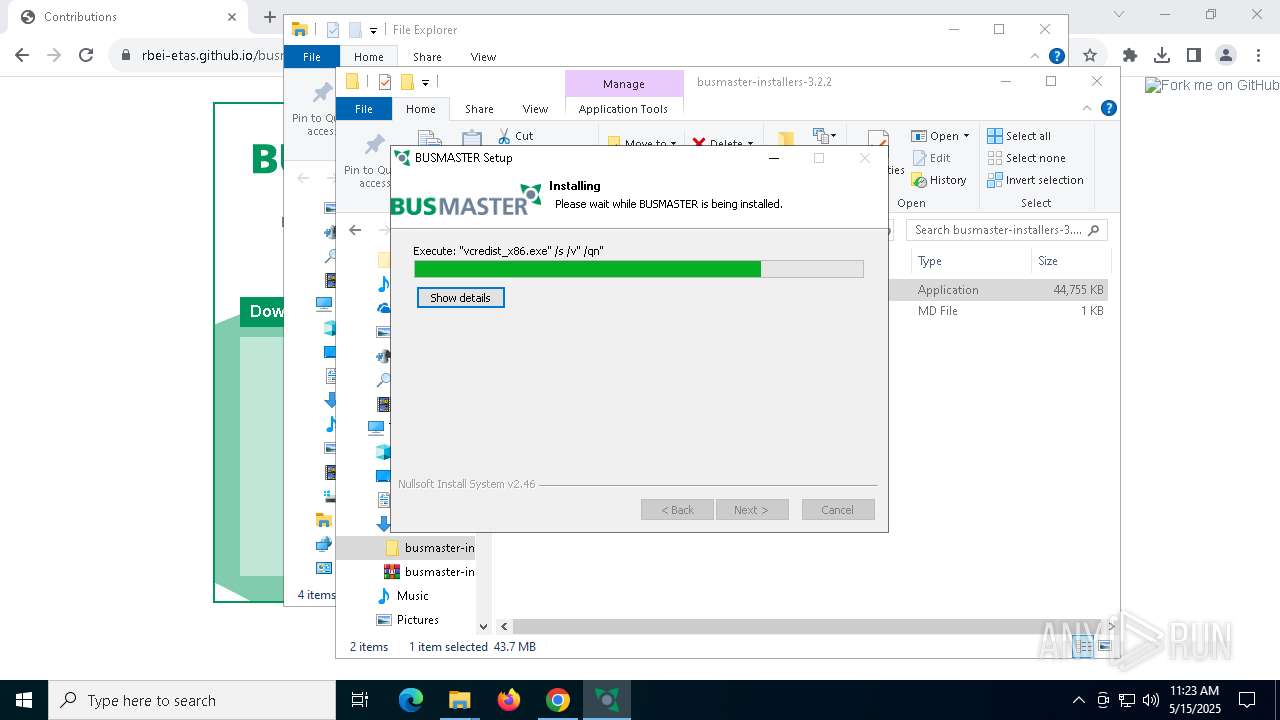
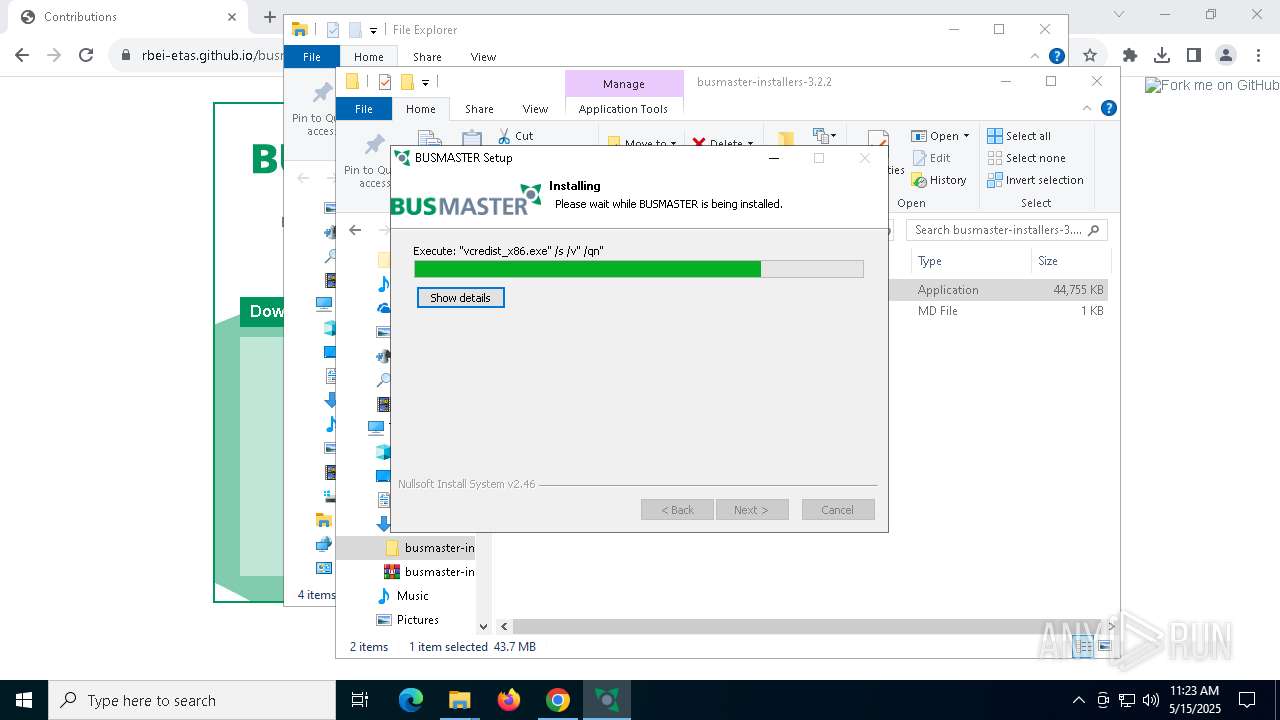
MALICIOUS
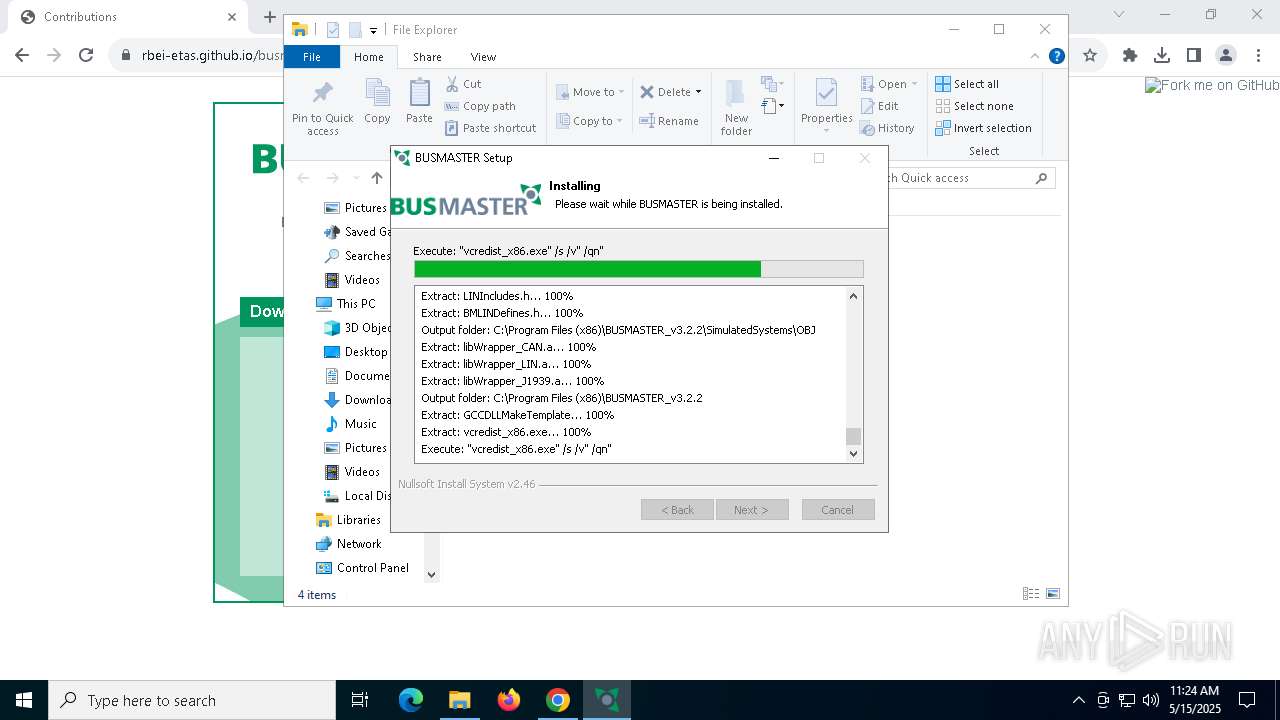
Executing a file with an untrusted certificate
- vcredist_x86.exe (PID: 5428)
- vcredist_x86.exe (PID: 7144)
SUSPICIOUS
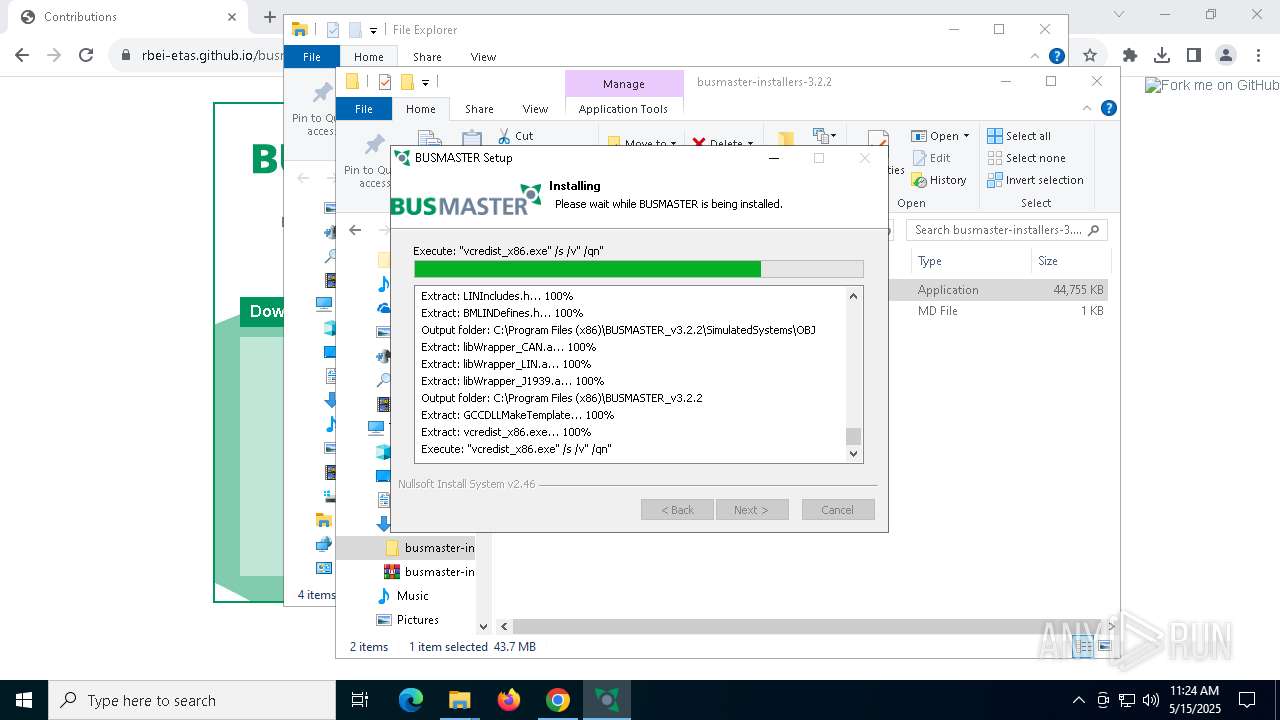
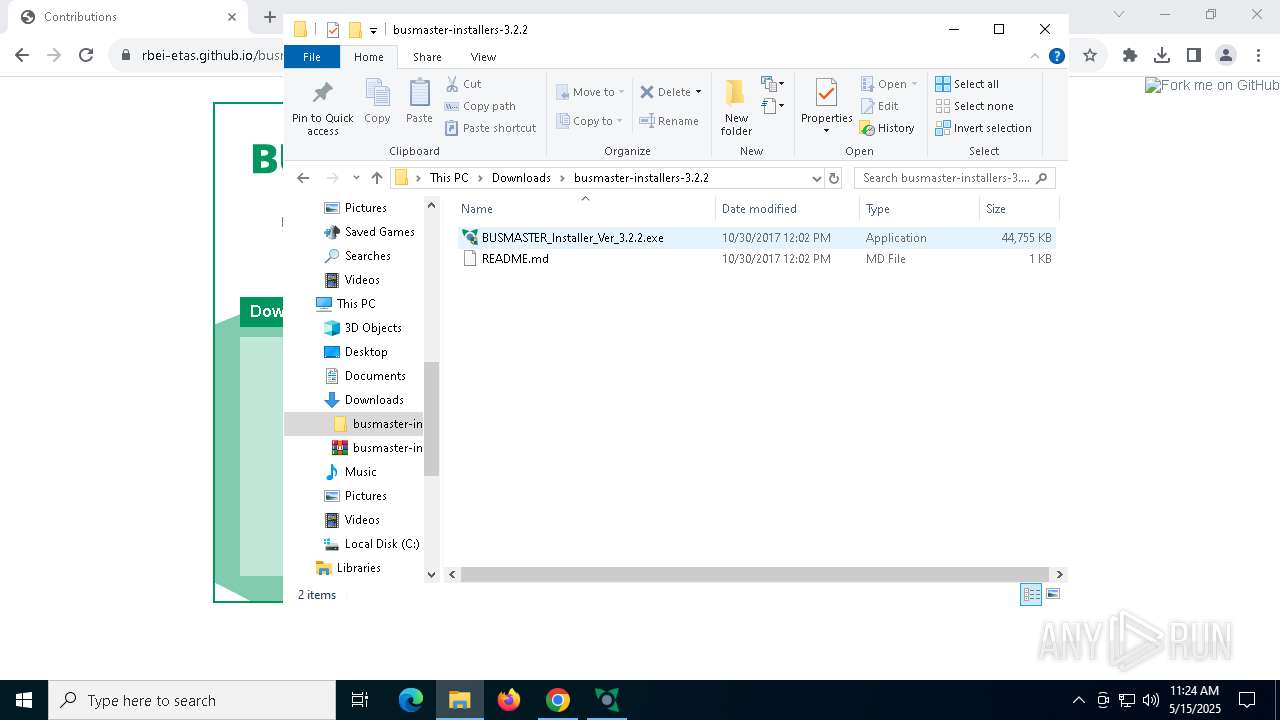
Executable content was dropped or overwritten
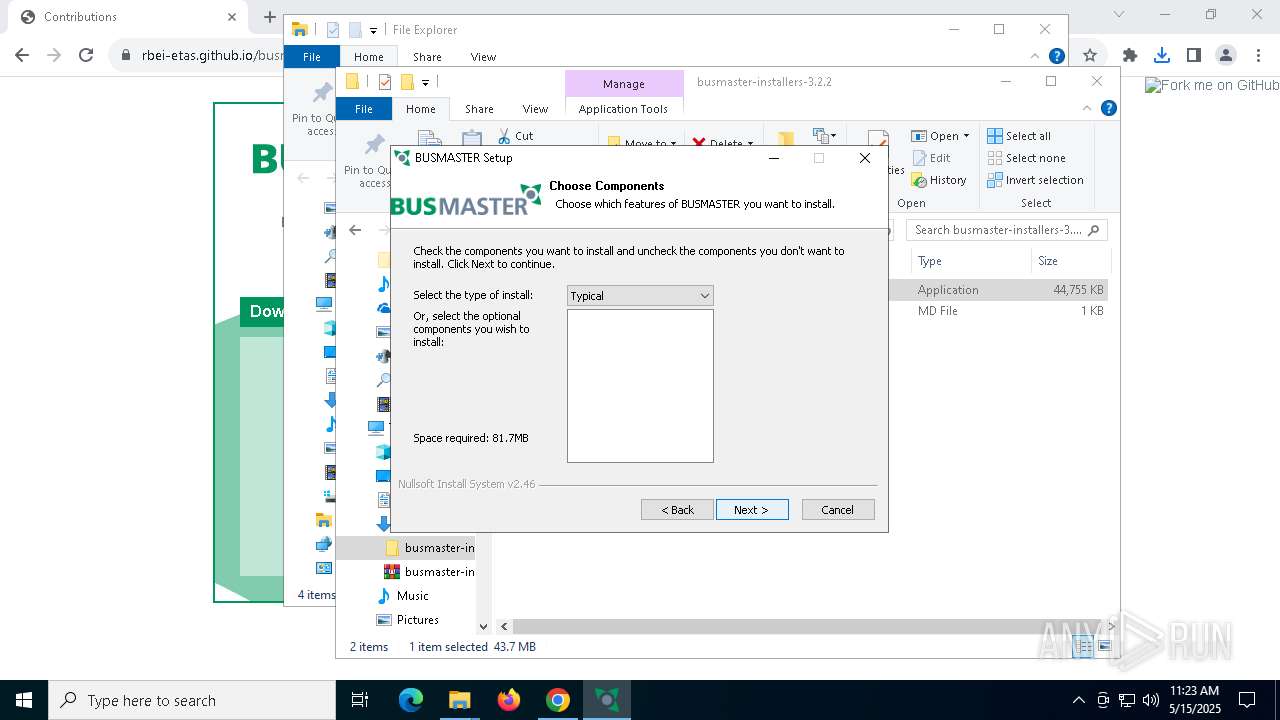
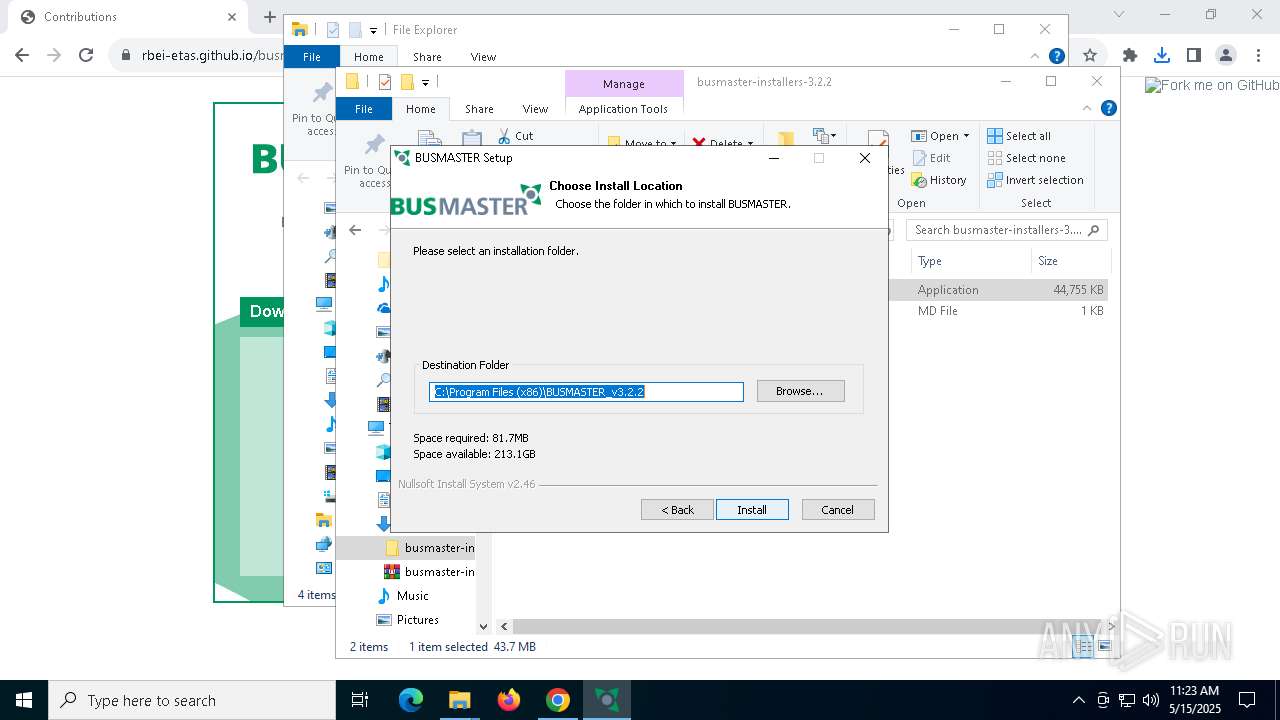
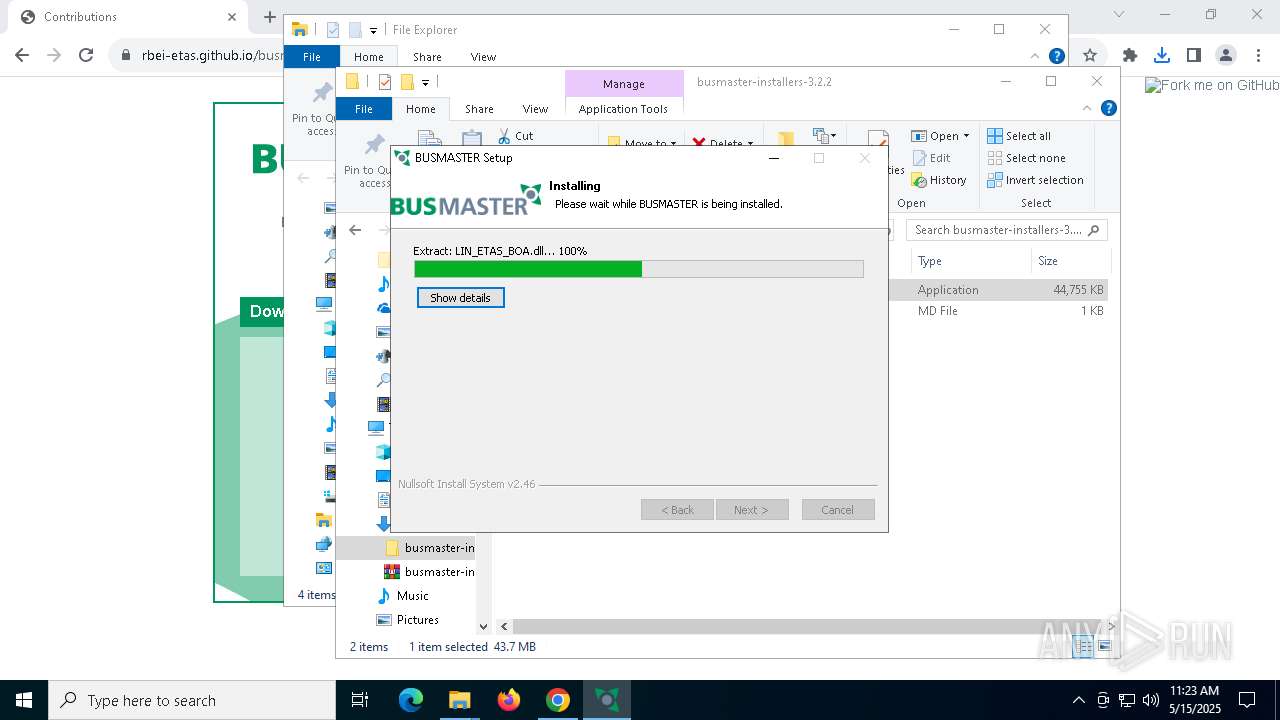
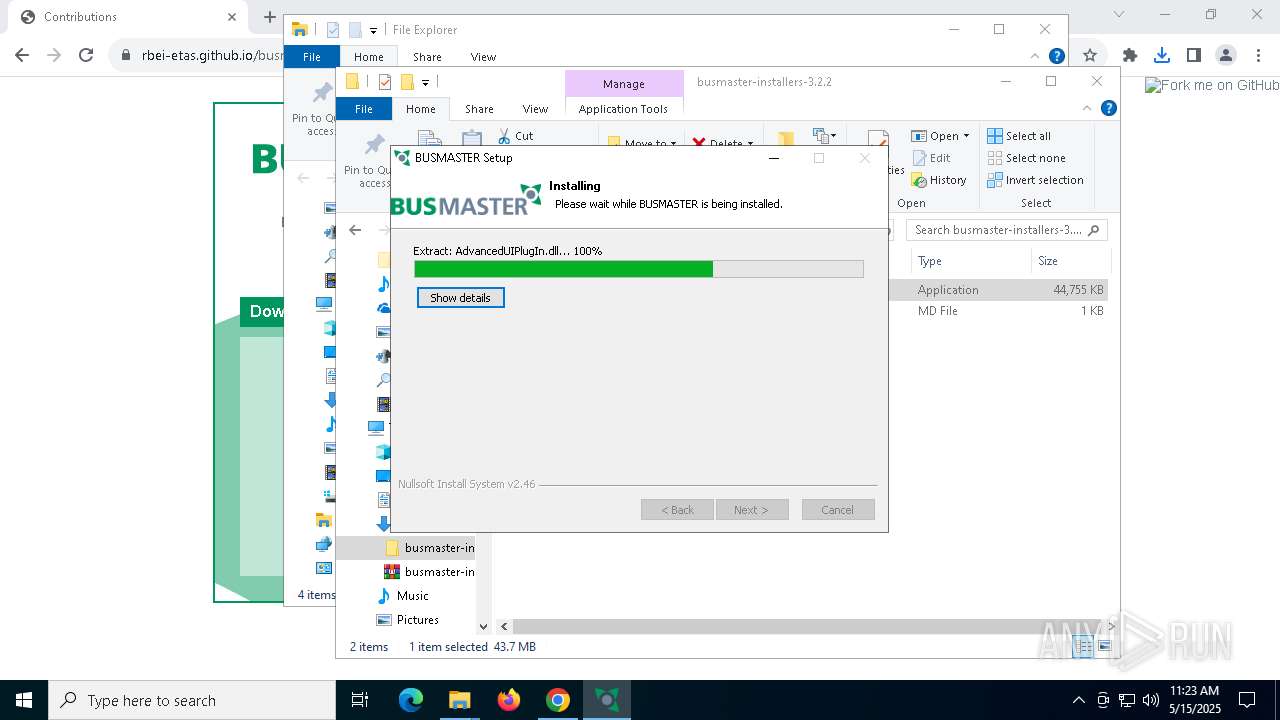
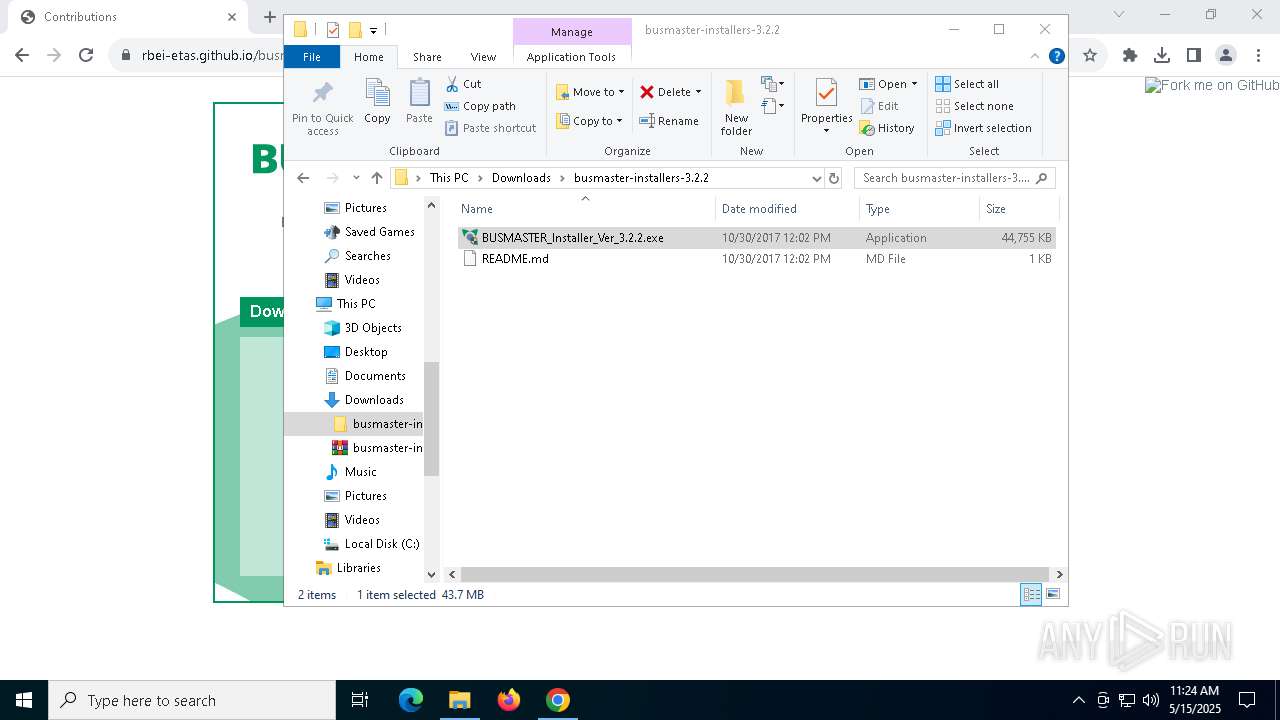
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
- vcredist_x86.exe (PID: 7144)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 6416)
- vcredist_x86.exe (PID: 5428)
Malware-specific behavior (creating "System.dll" in Temp)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 6416)
The process creates files with name similar to system file names
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 4528)
Process drops legitimate windows executable
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
- vcredist_x86.exe (PID: 7144)
- vcredist_x86.exe (PID: 5428)
- msiexec.exe (PID: 7860)
Application launched itself
- vcredist_x86.exe (PID: 5428)
Executes as Windows Service
- VSSVC.exe (PID: 8052)
INFO
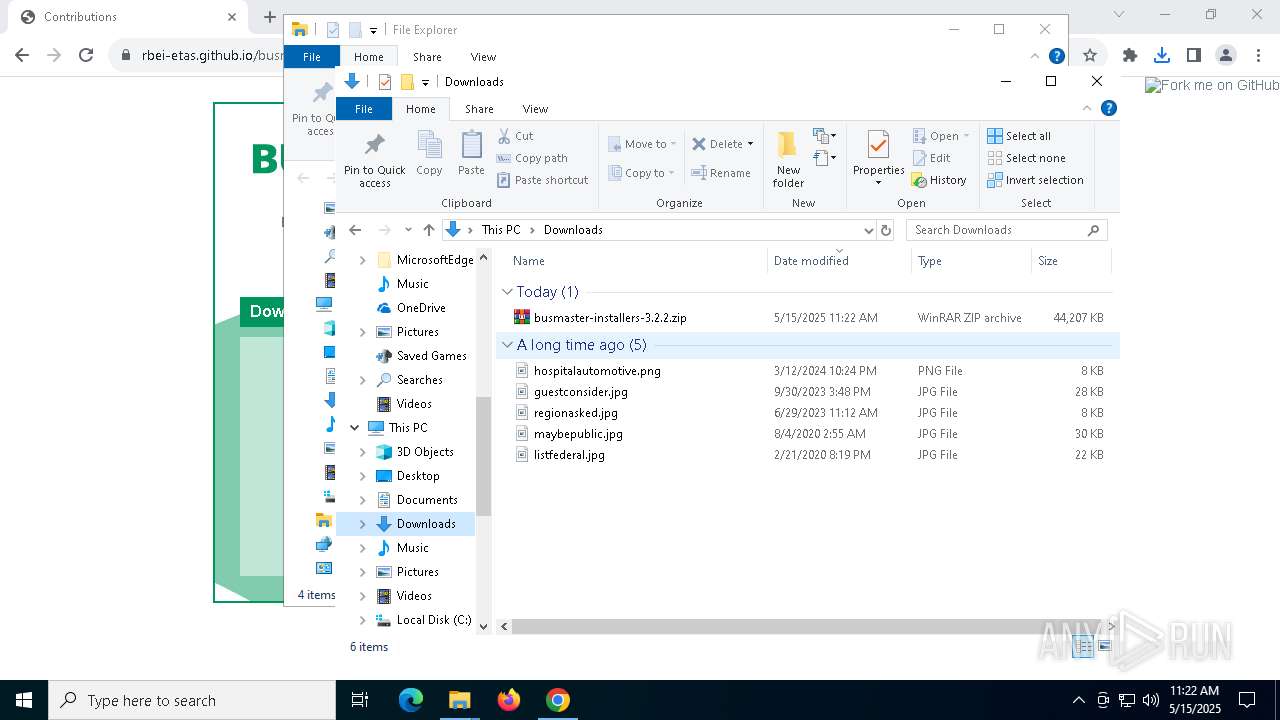
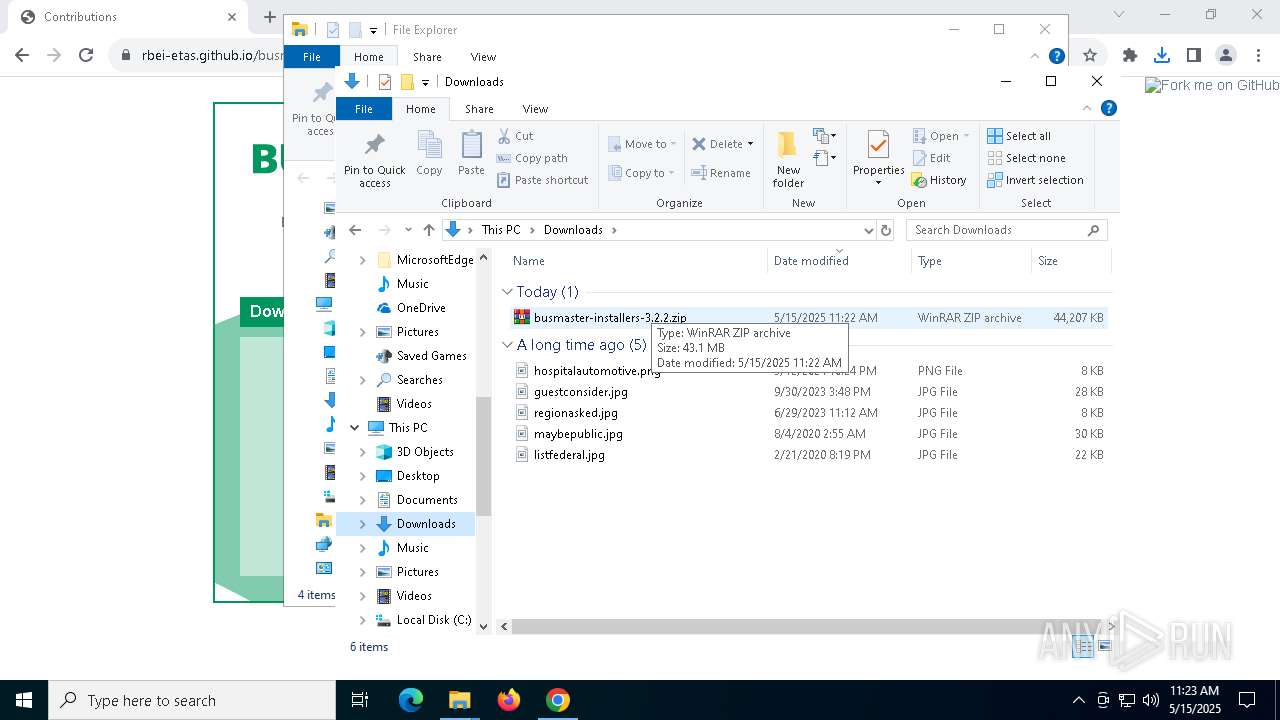
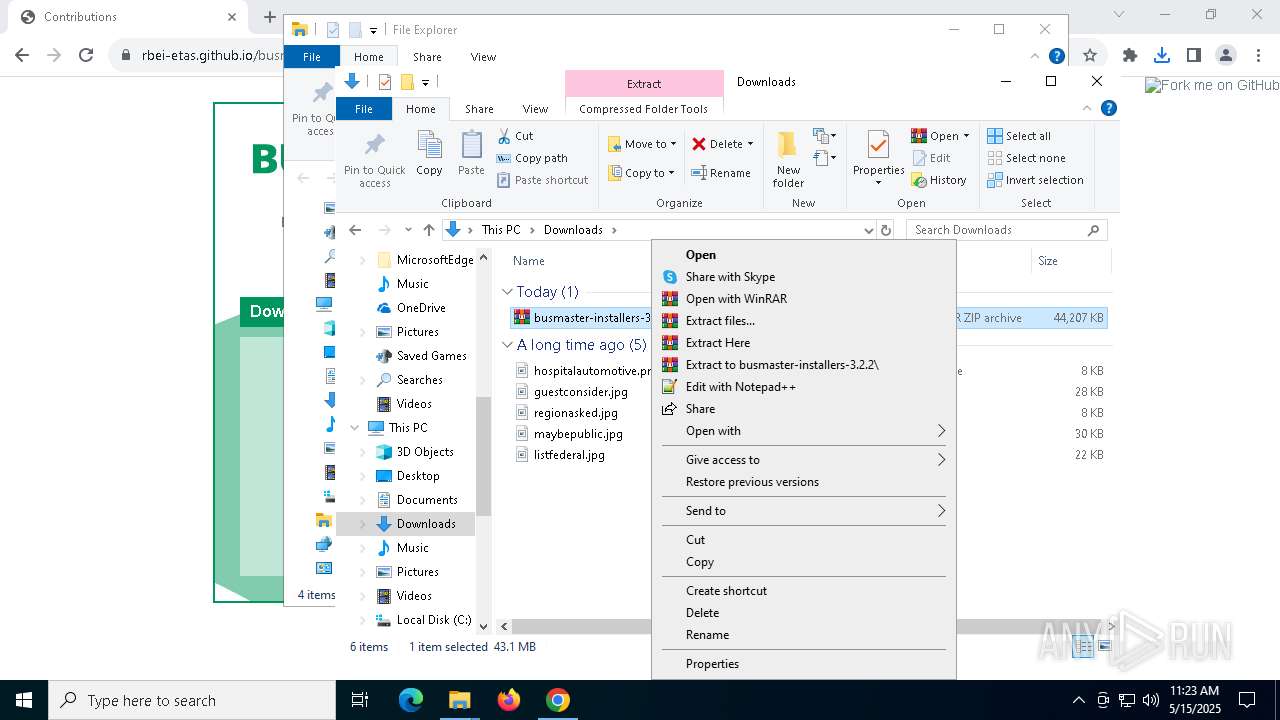
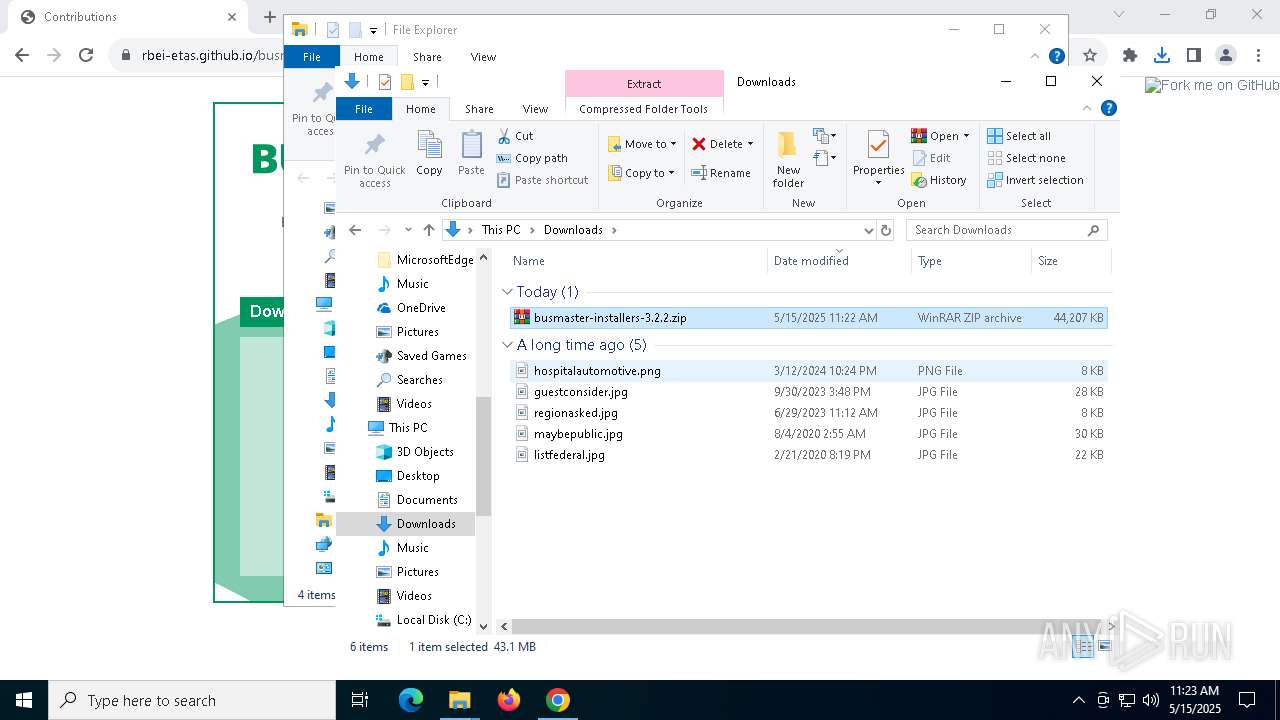
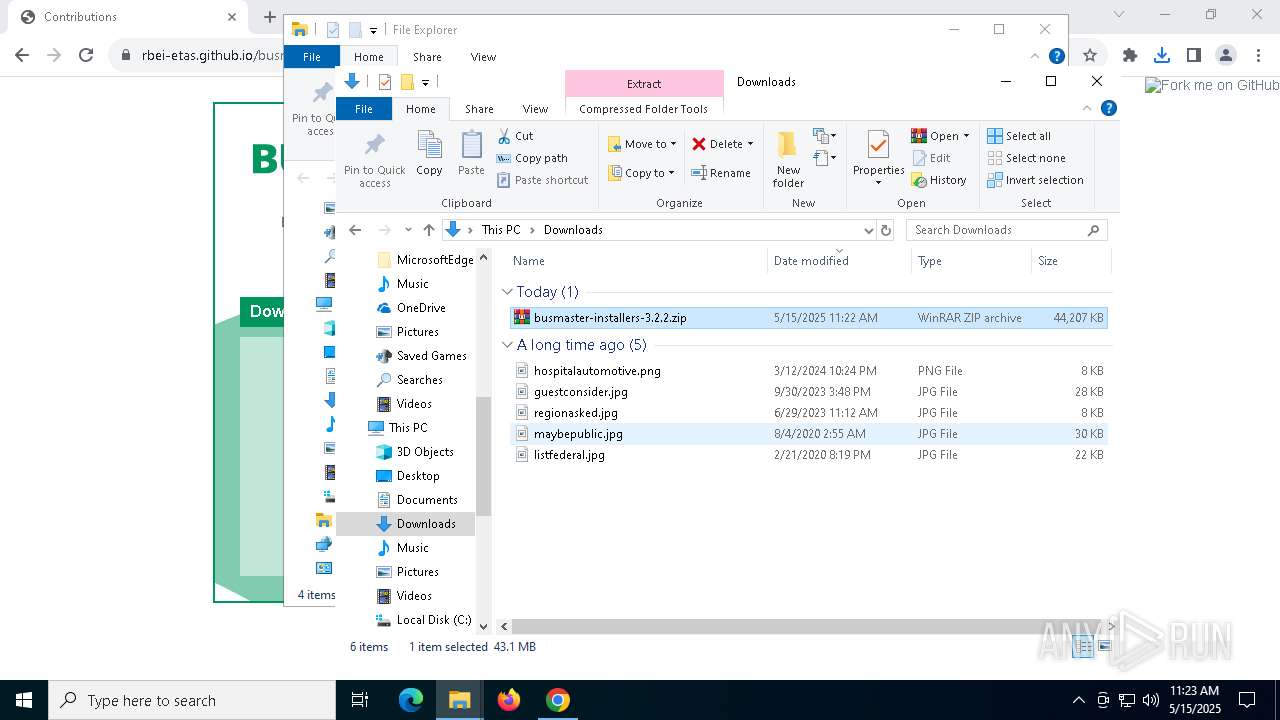
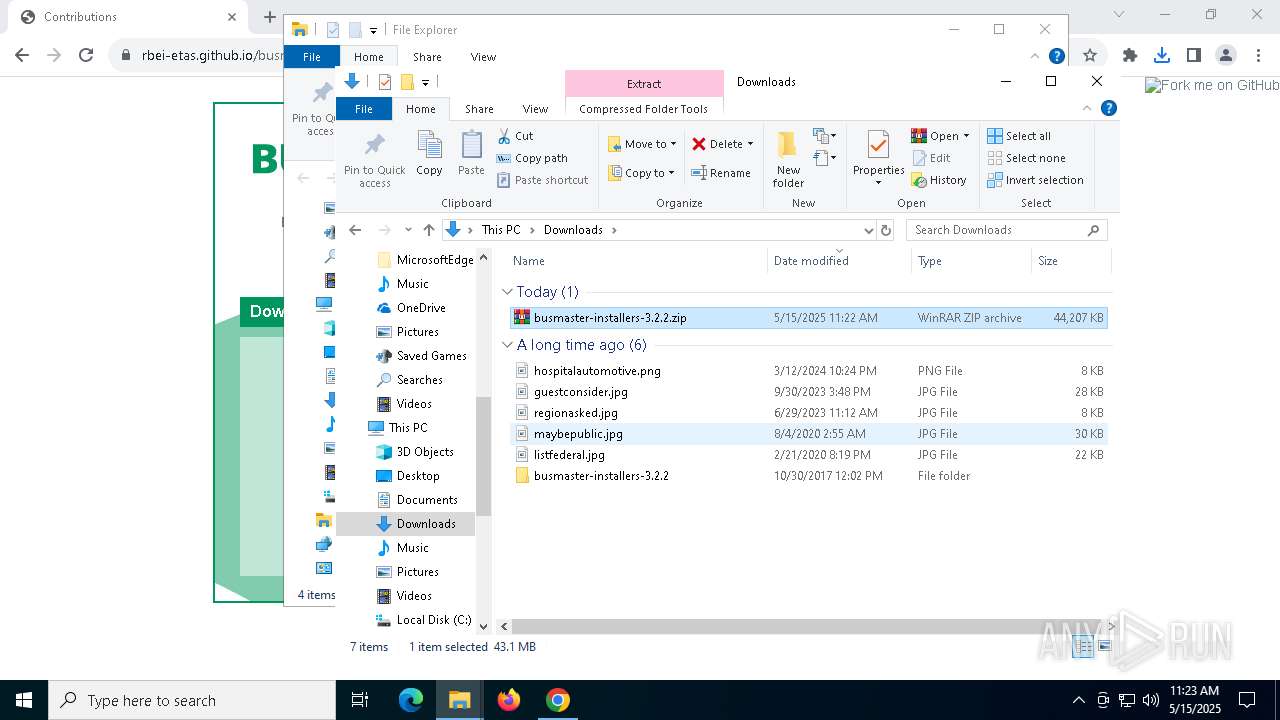
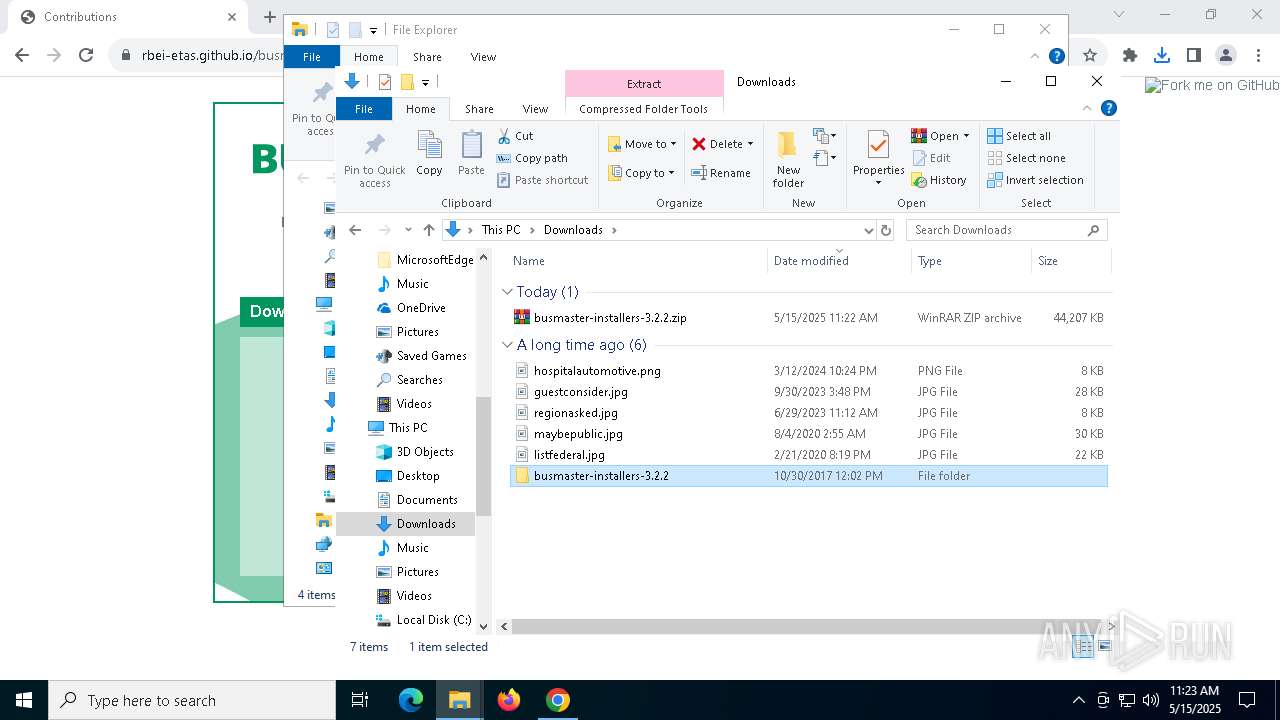
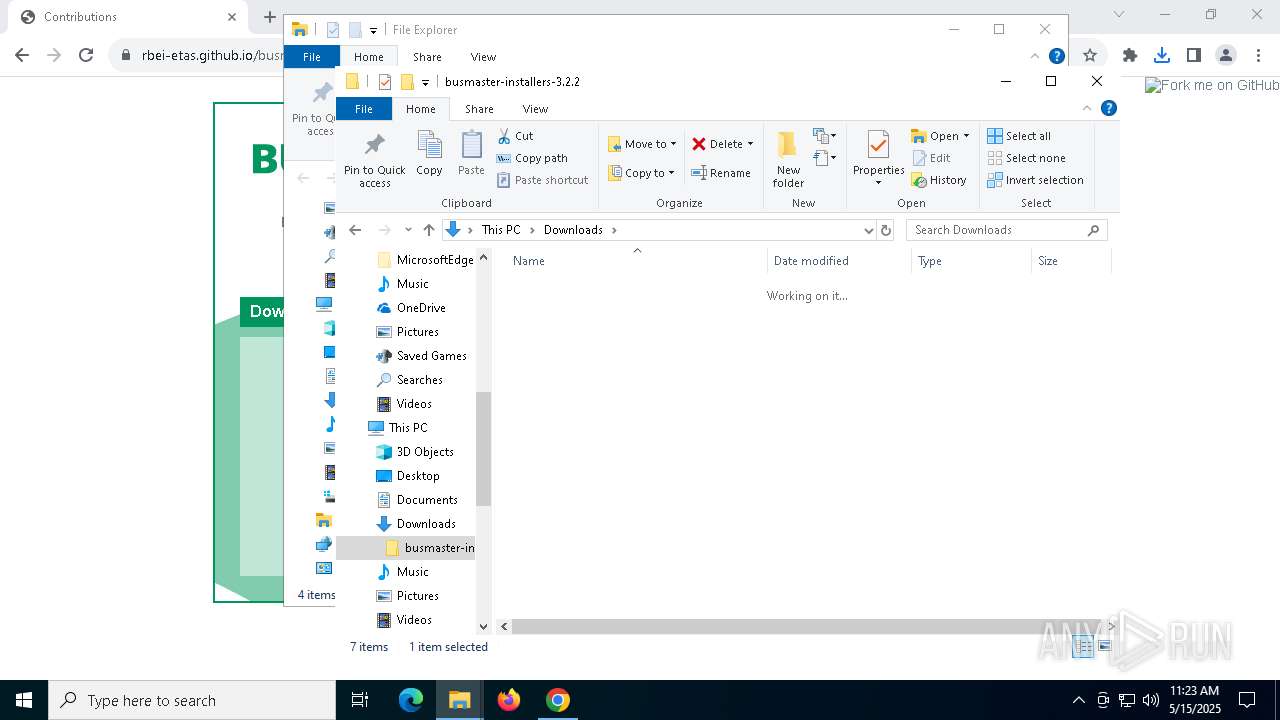
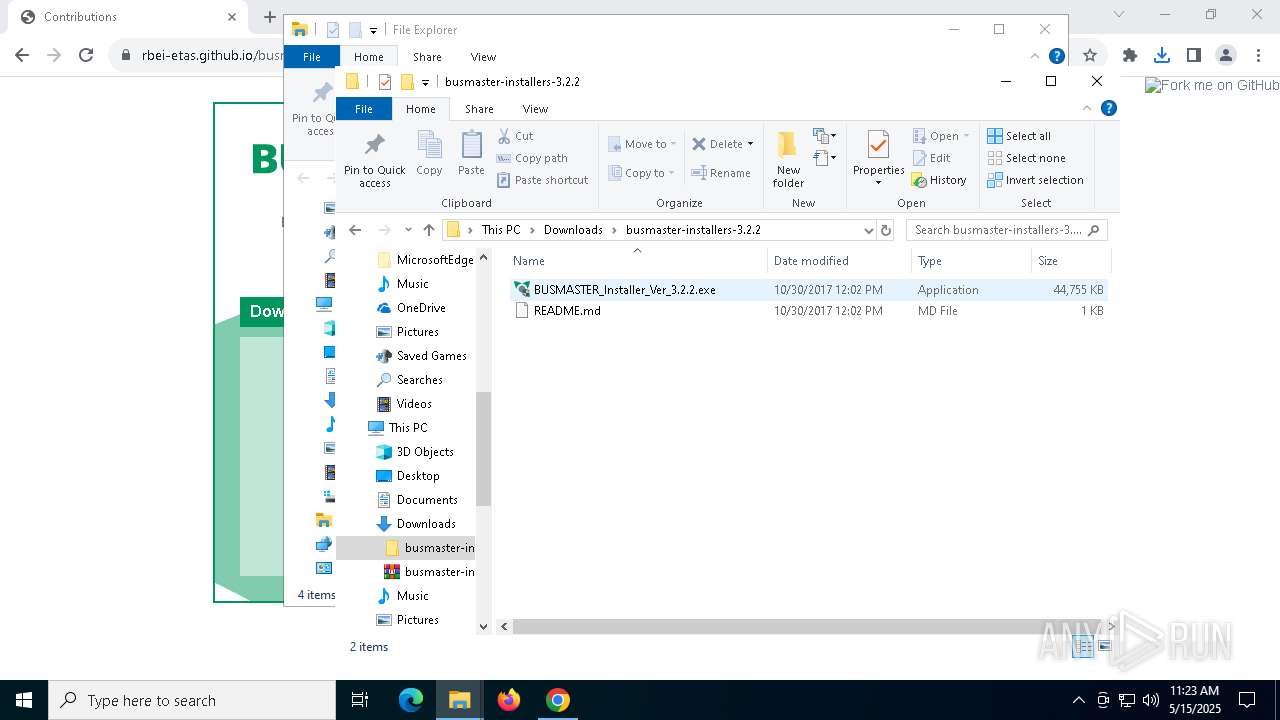
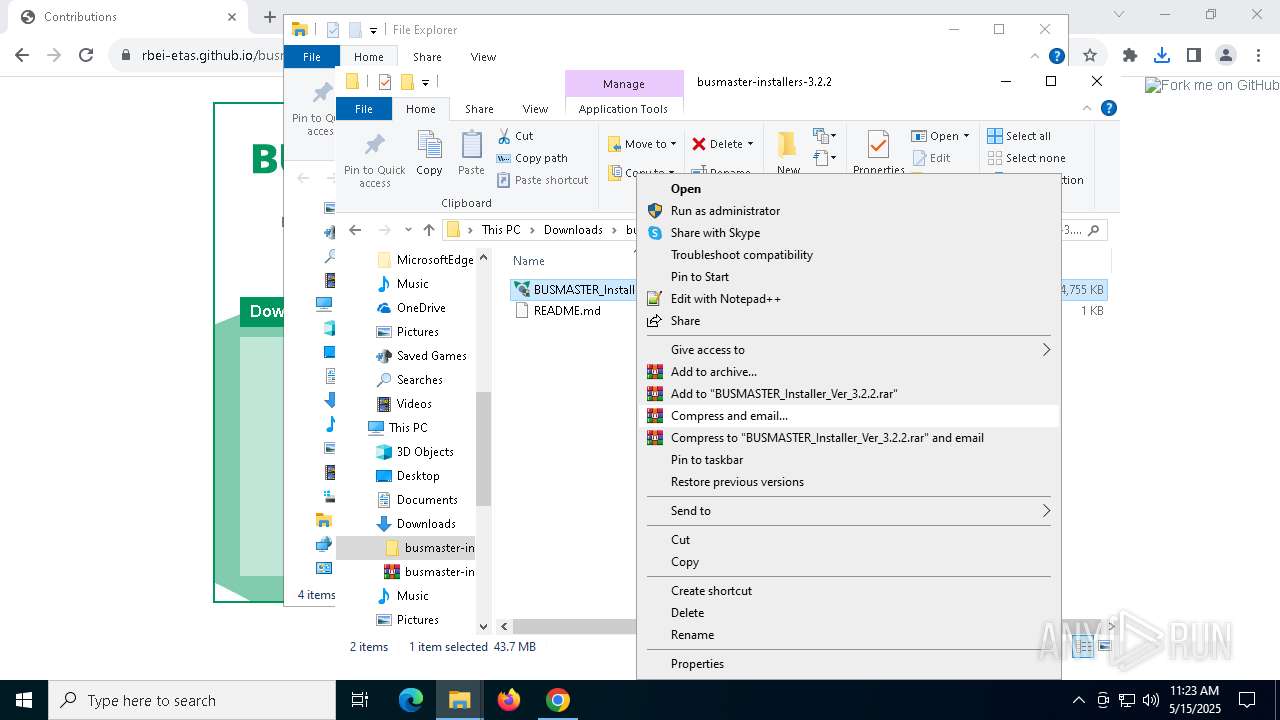
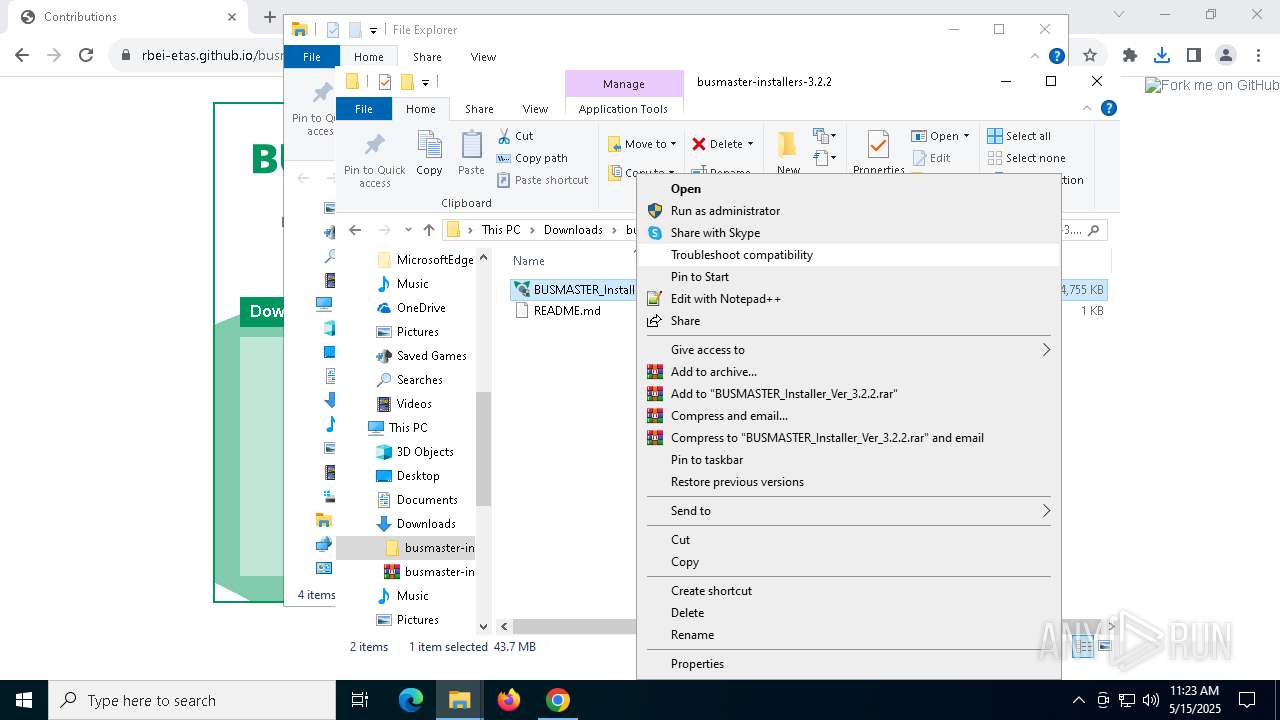
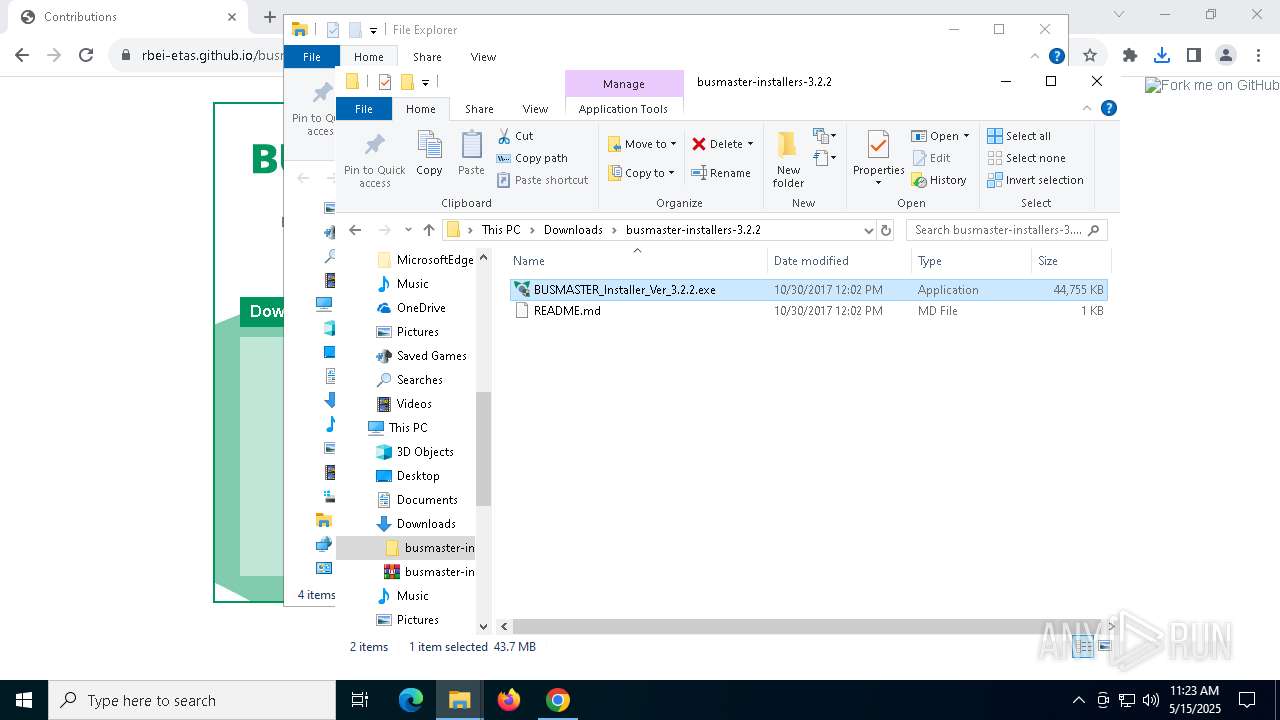
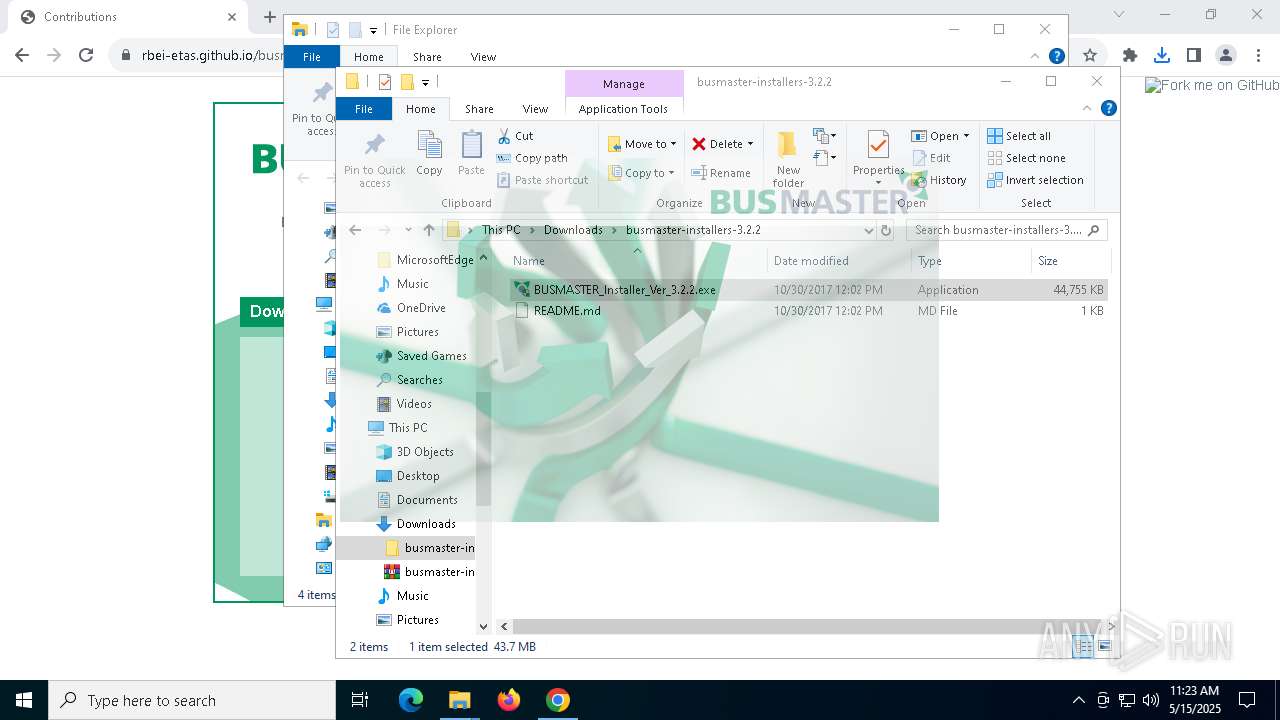
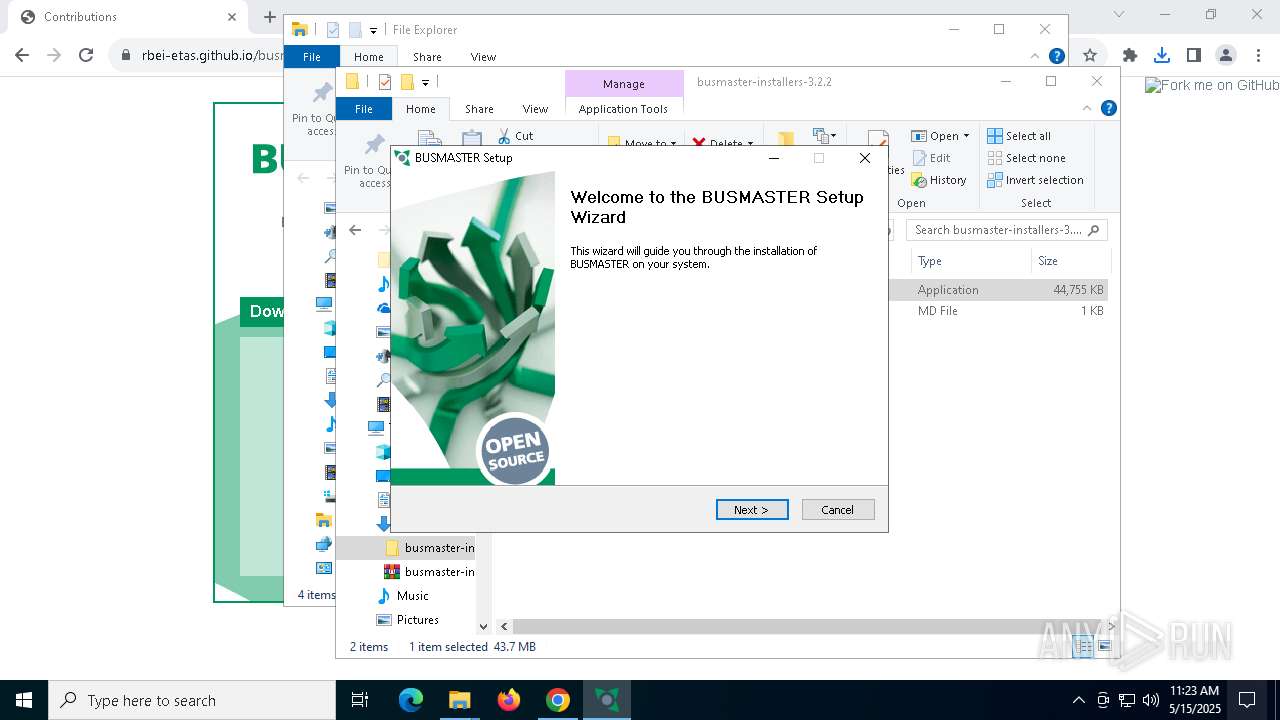
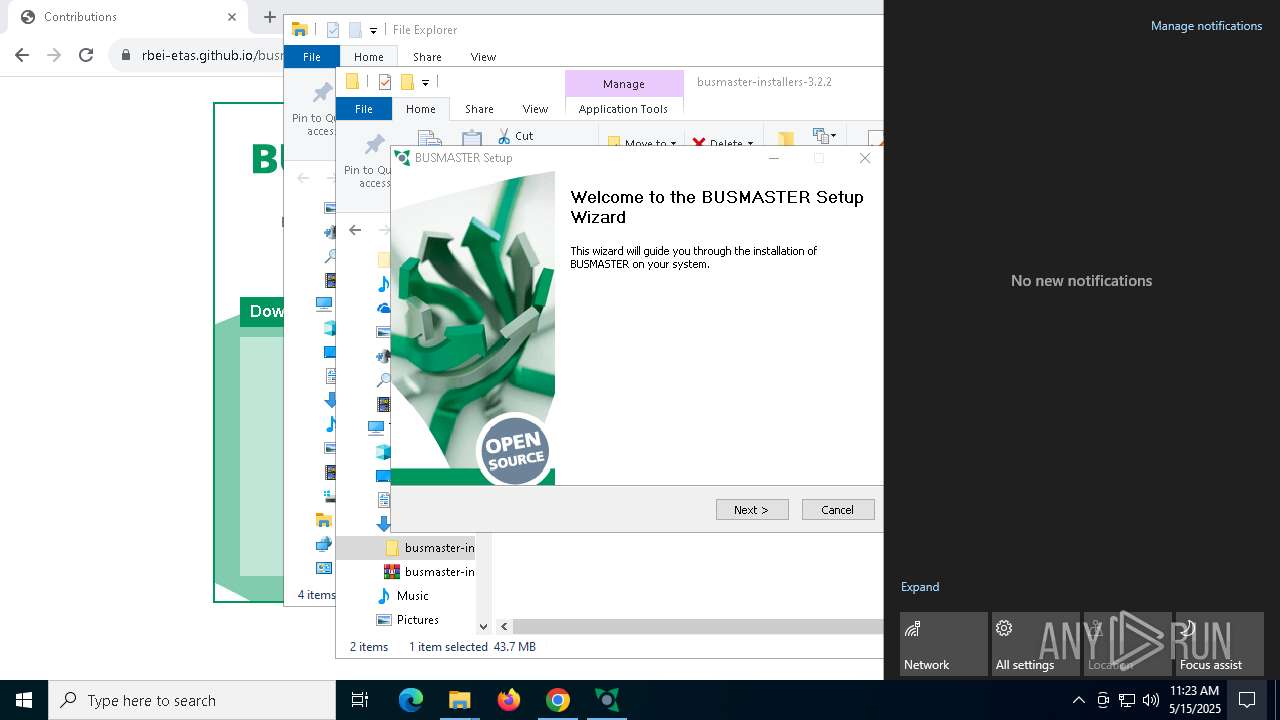
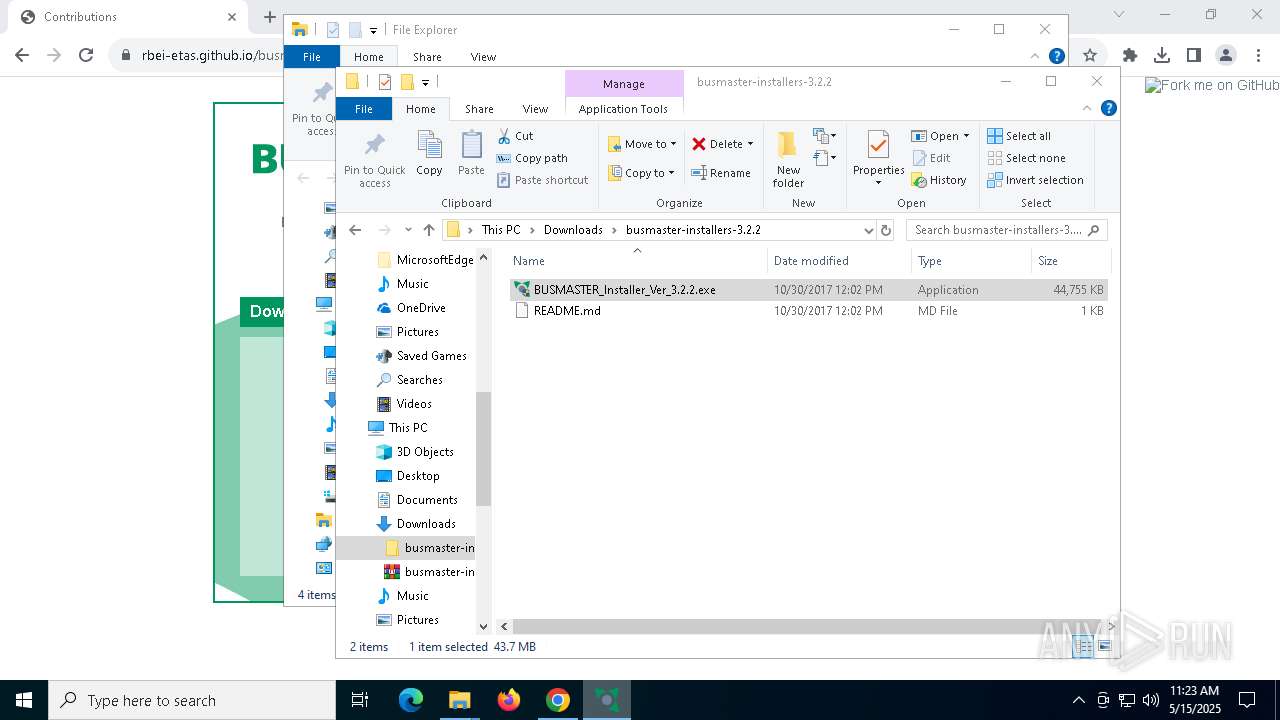
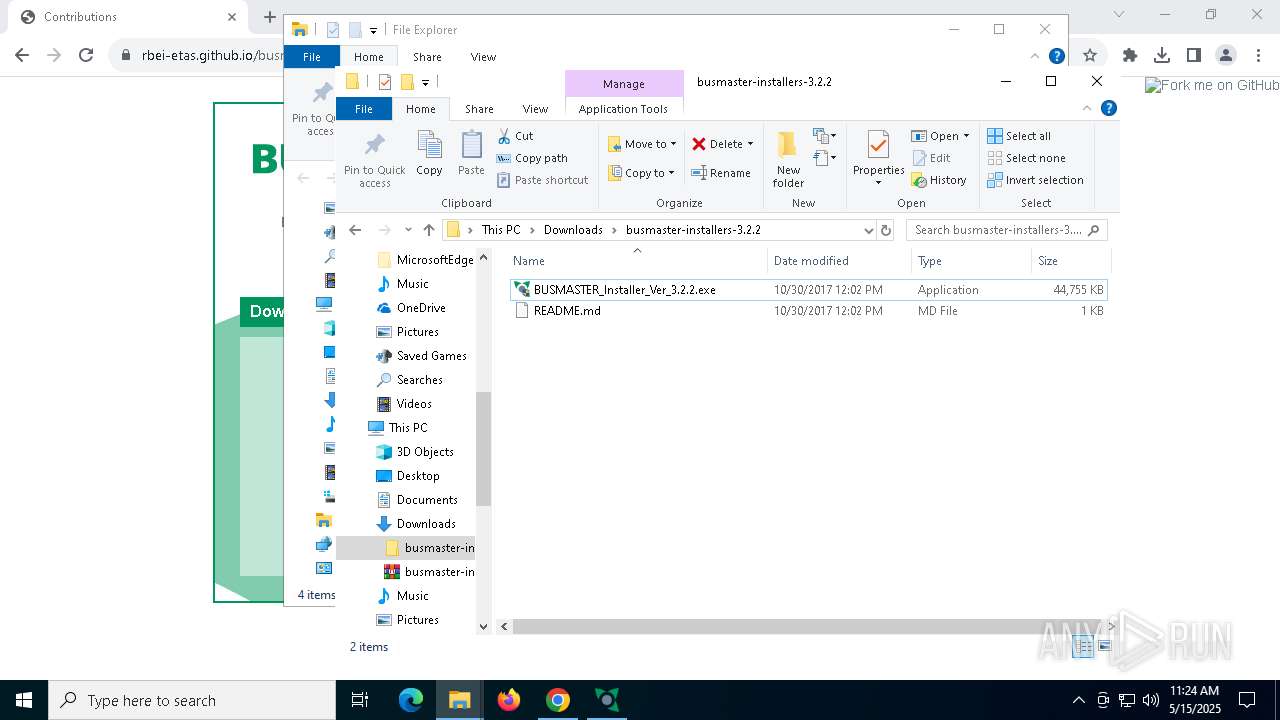
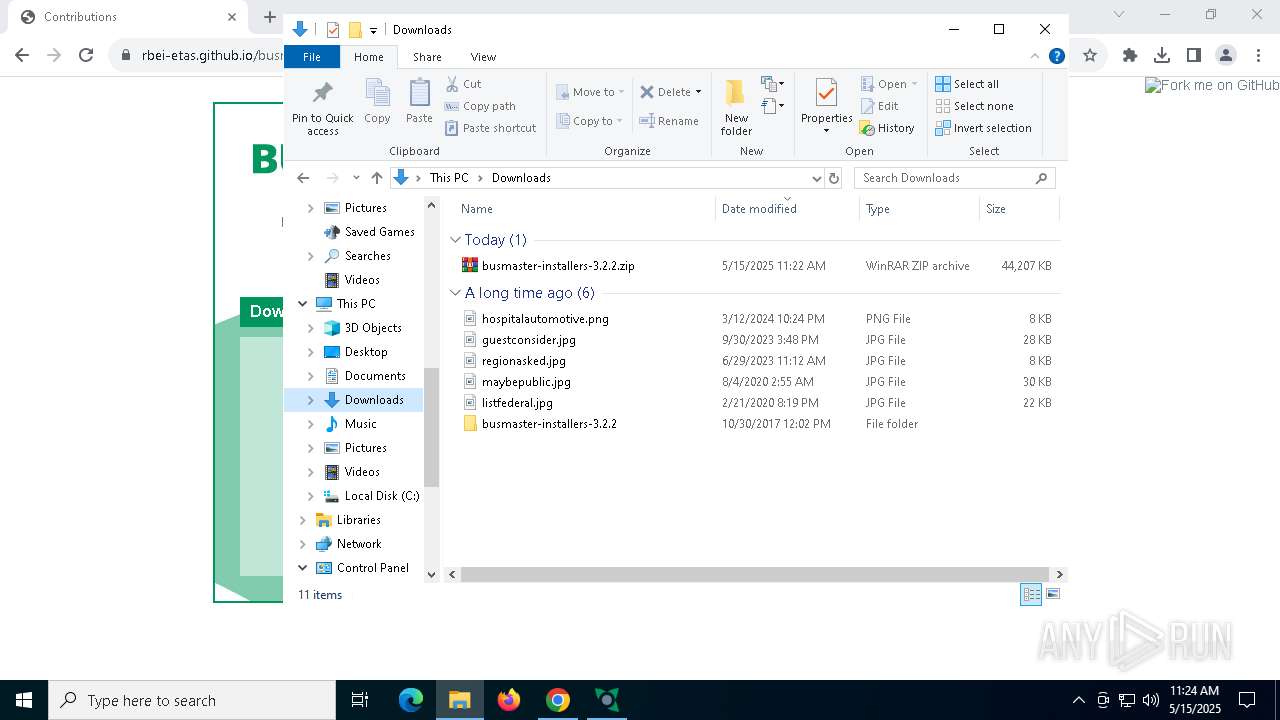
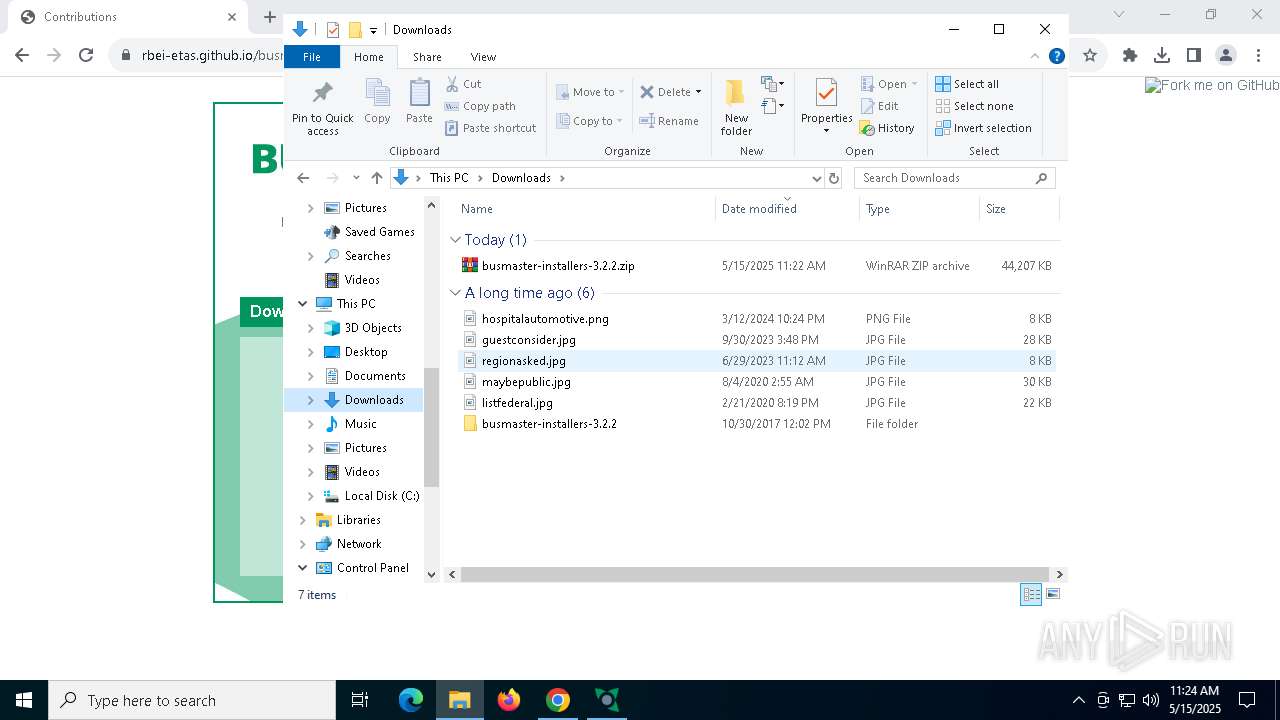
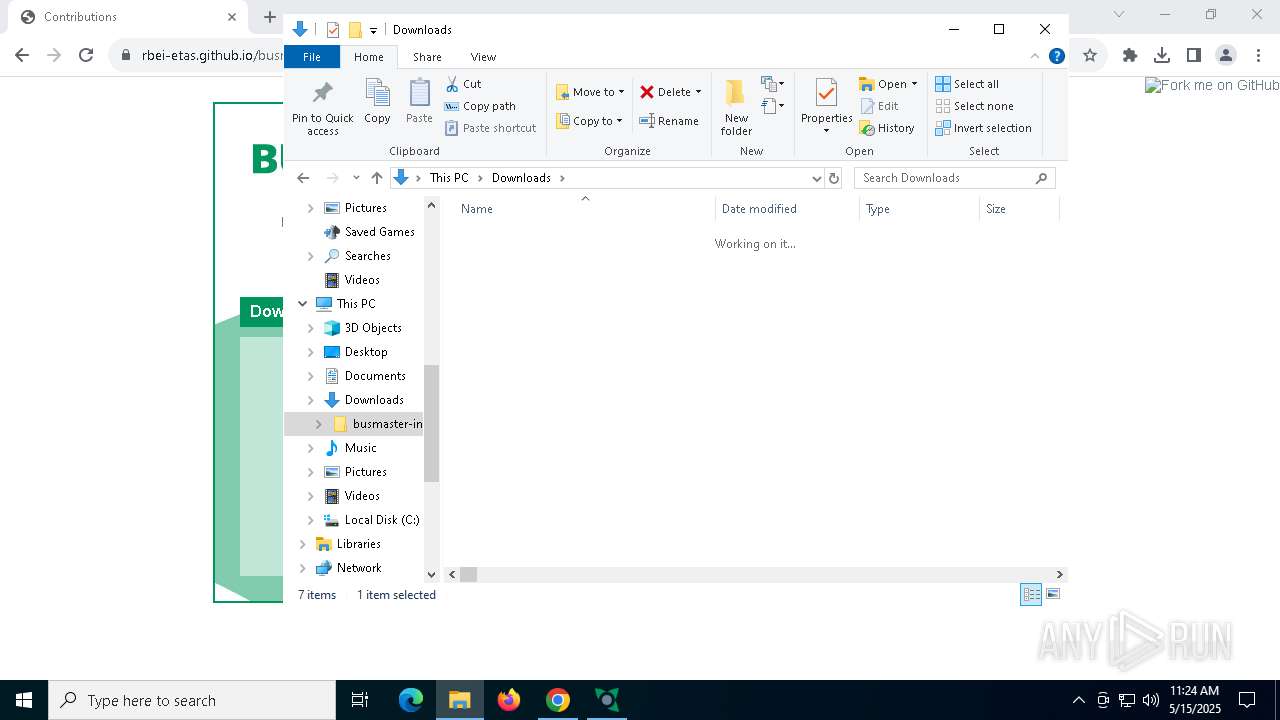
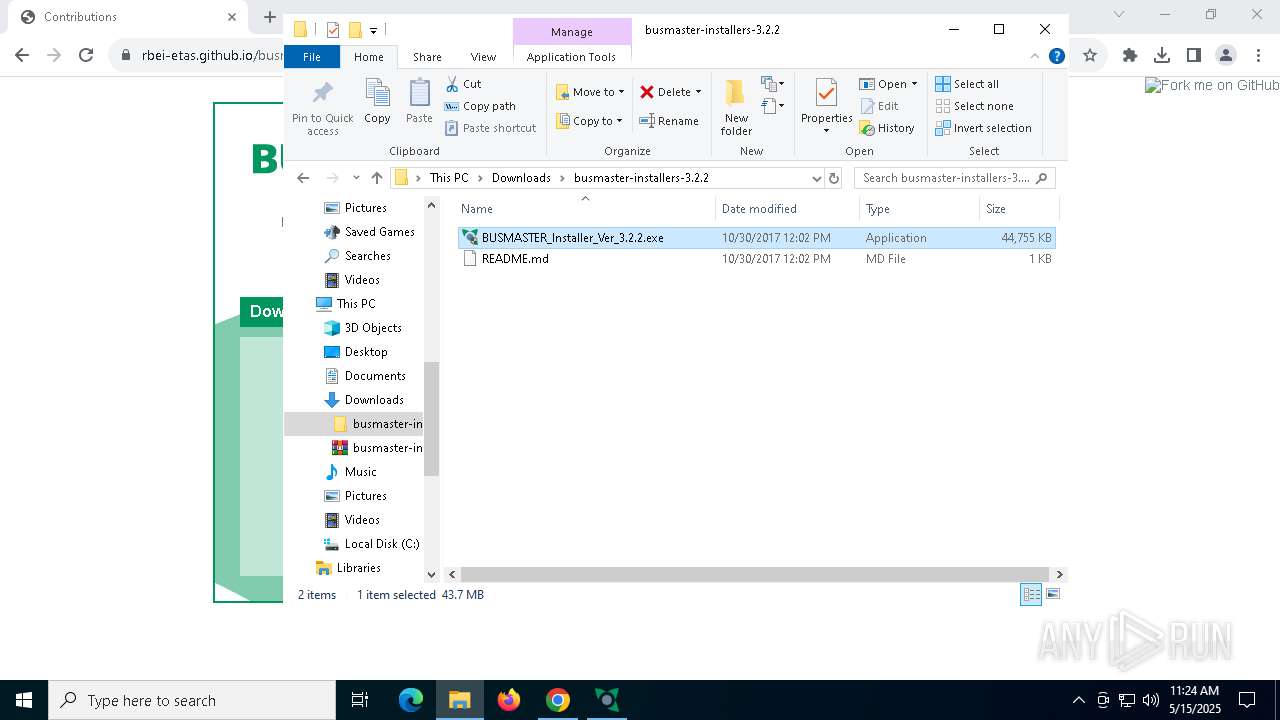
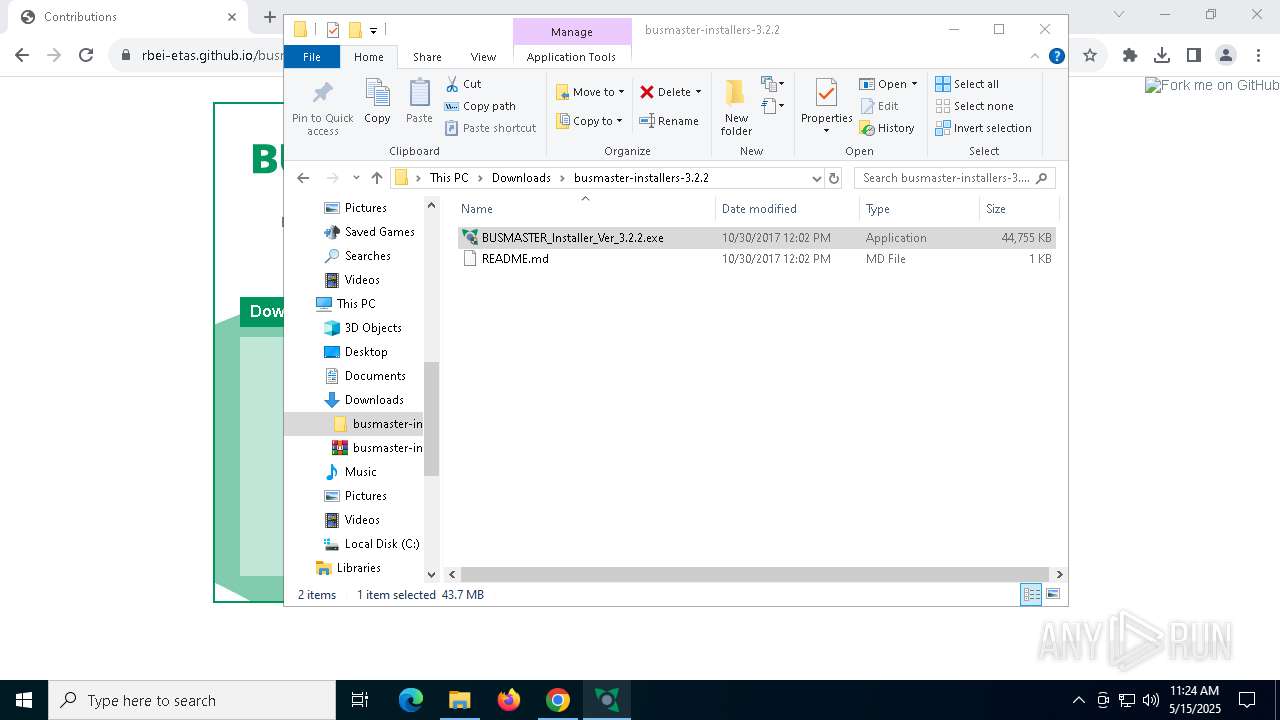
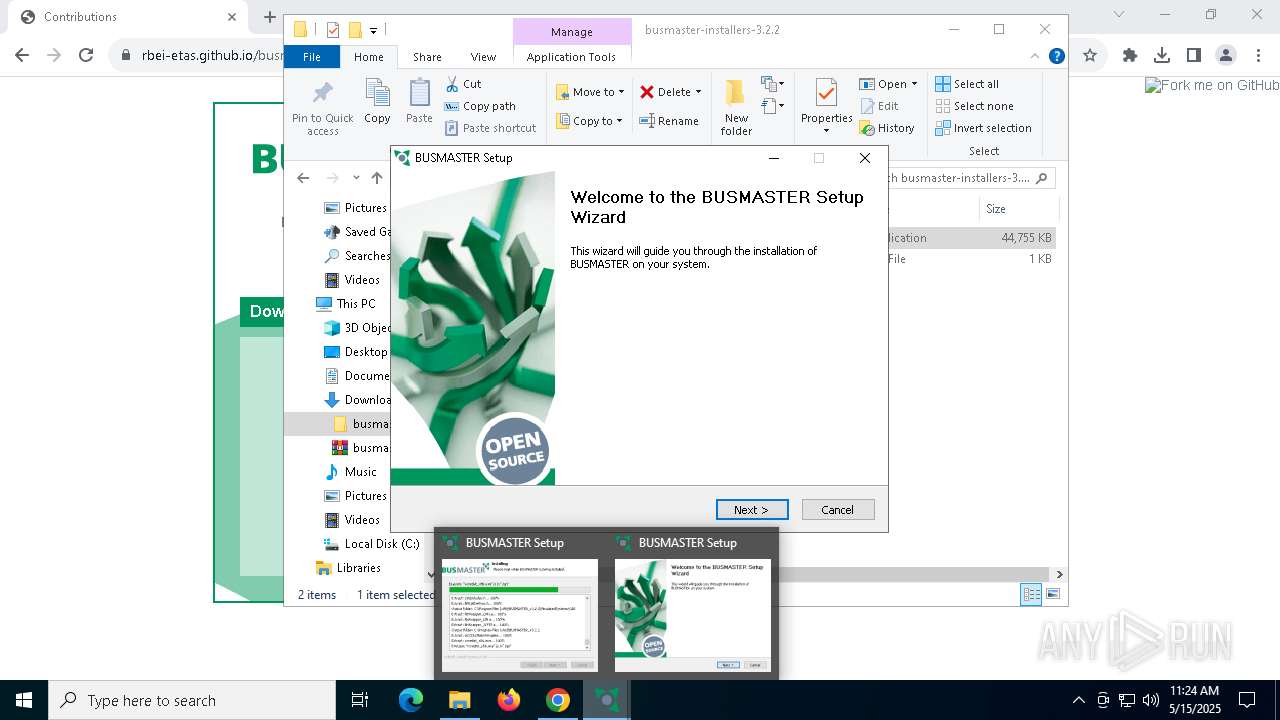
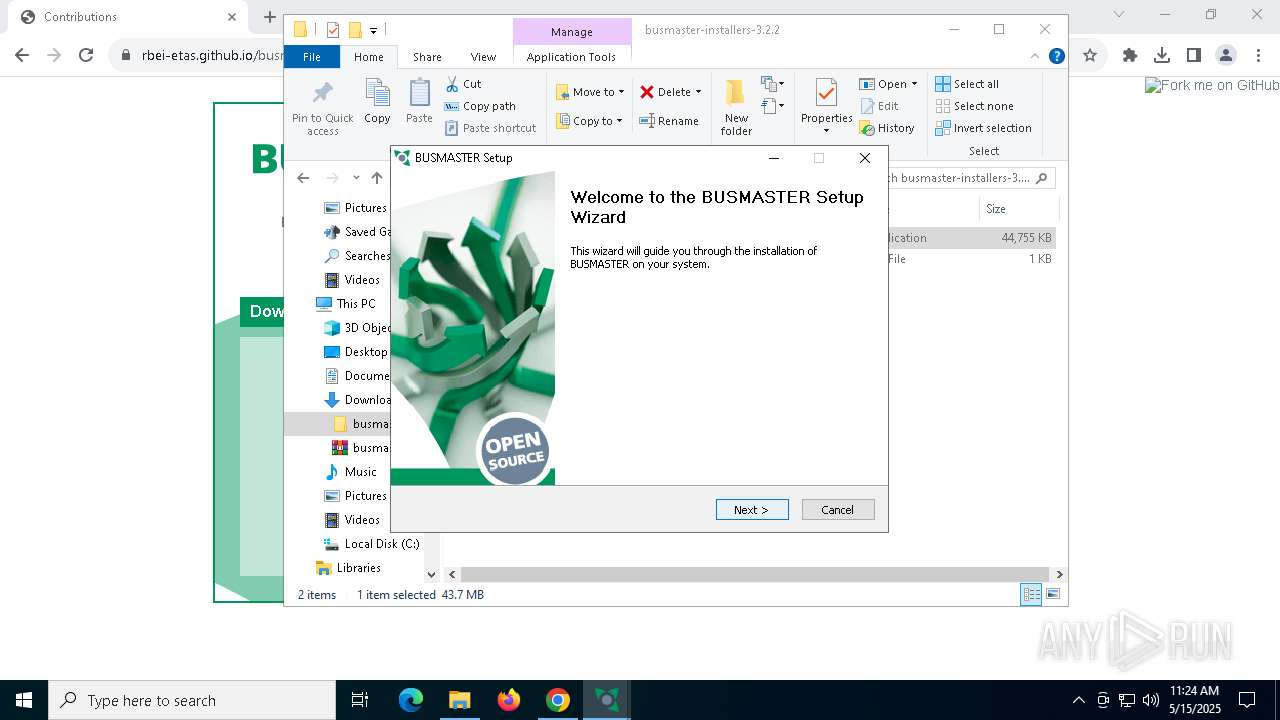
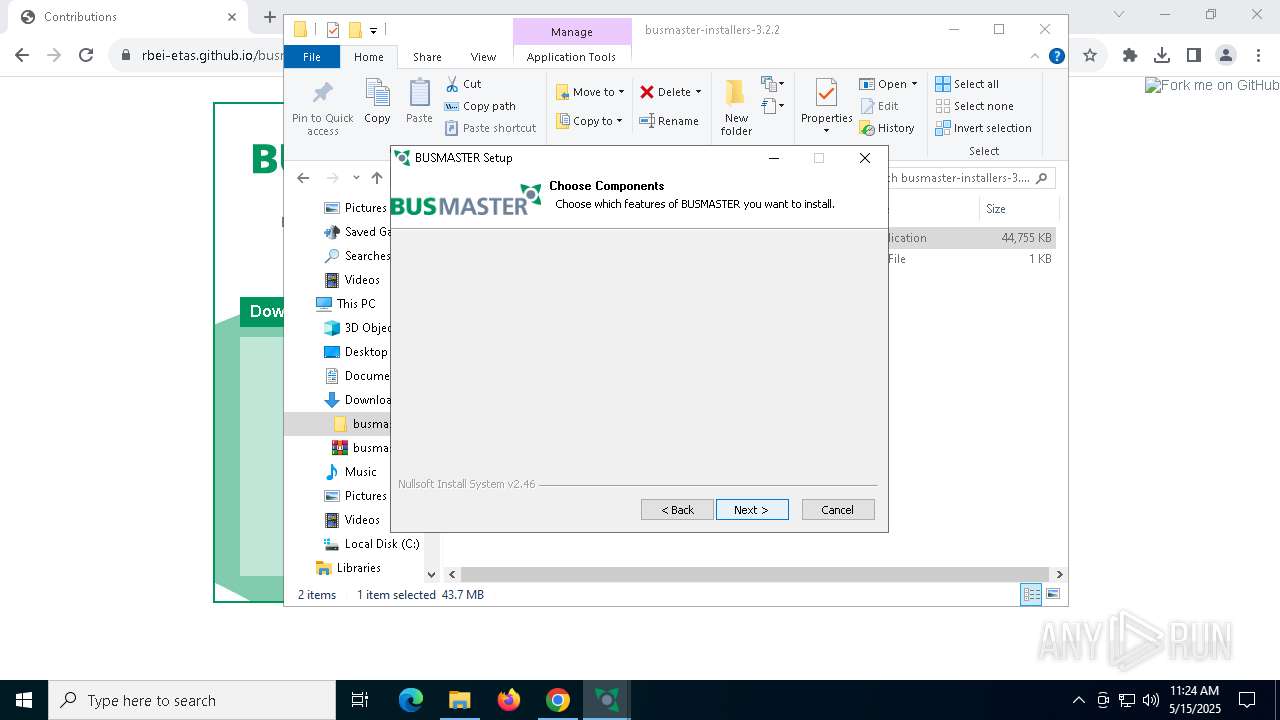
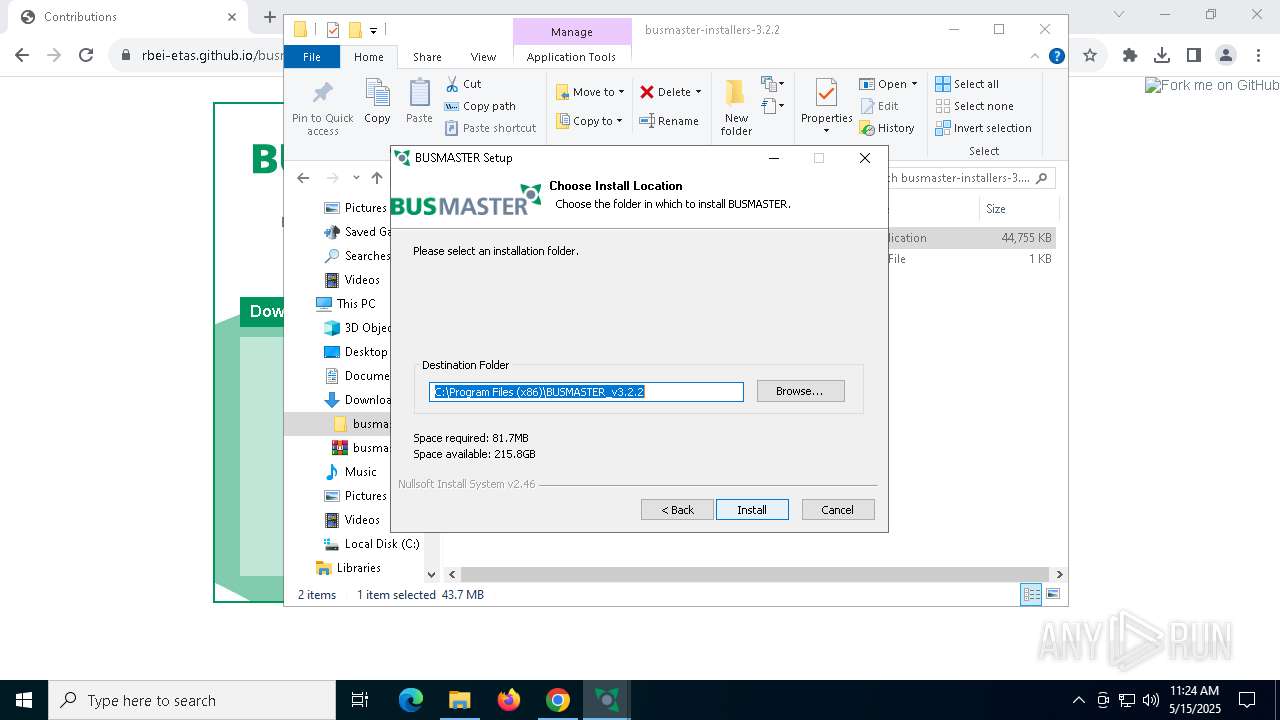
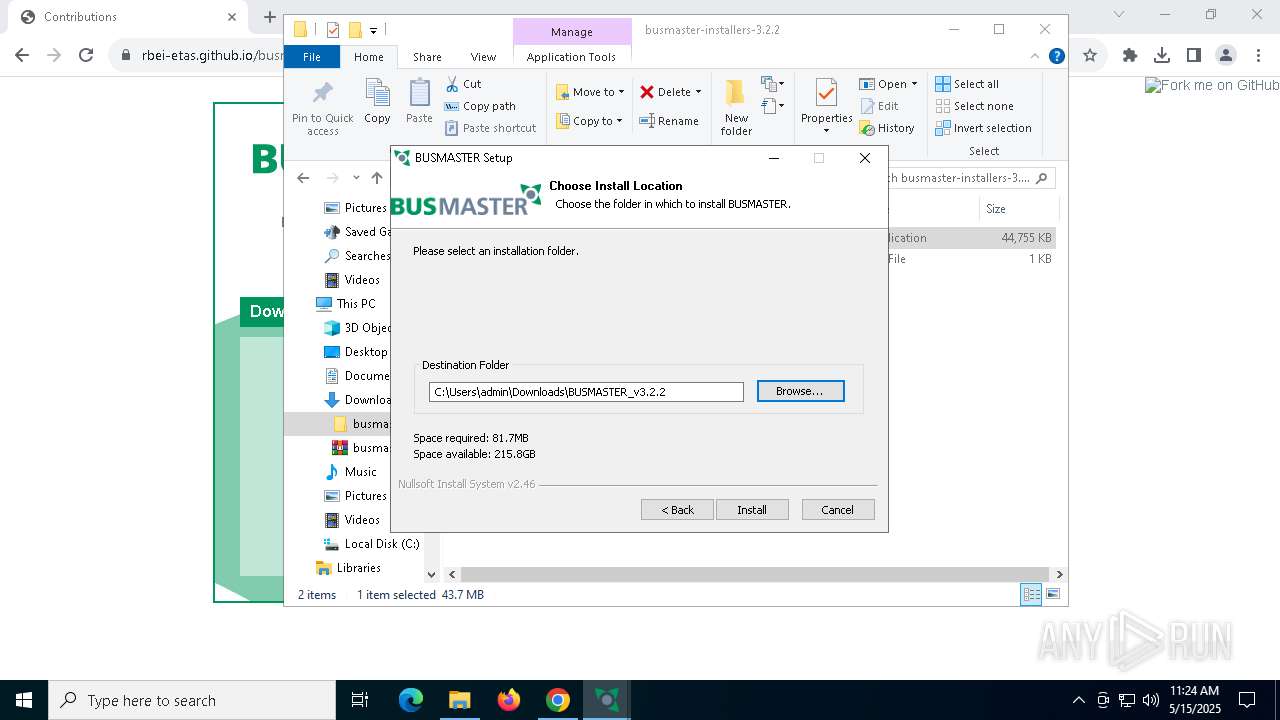
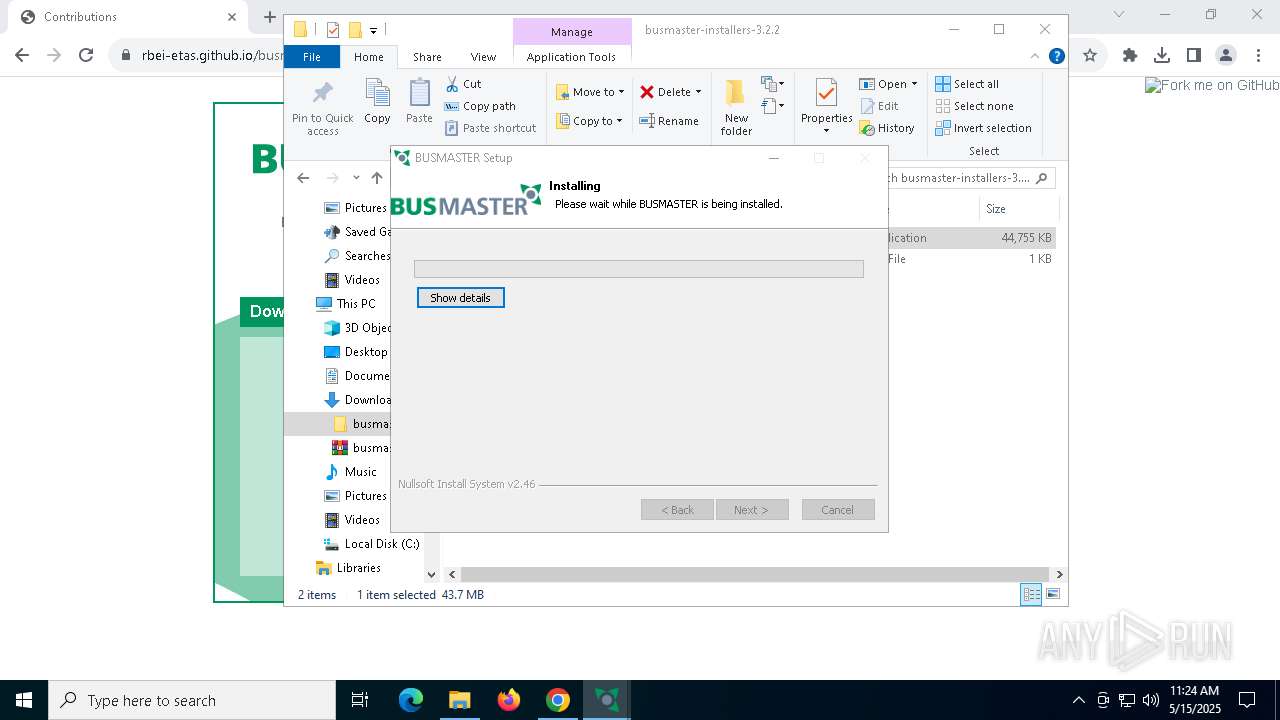
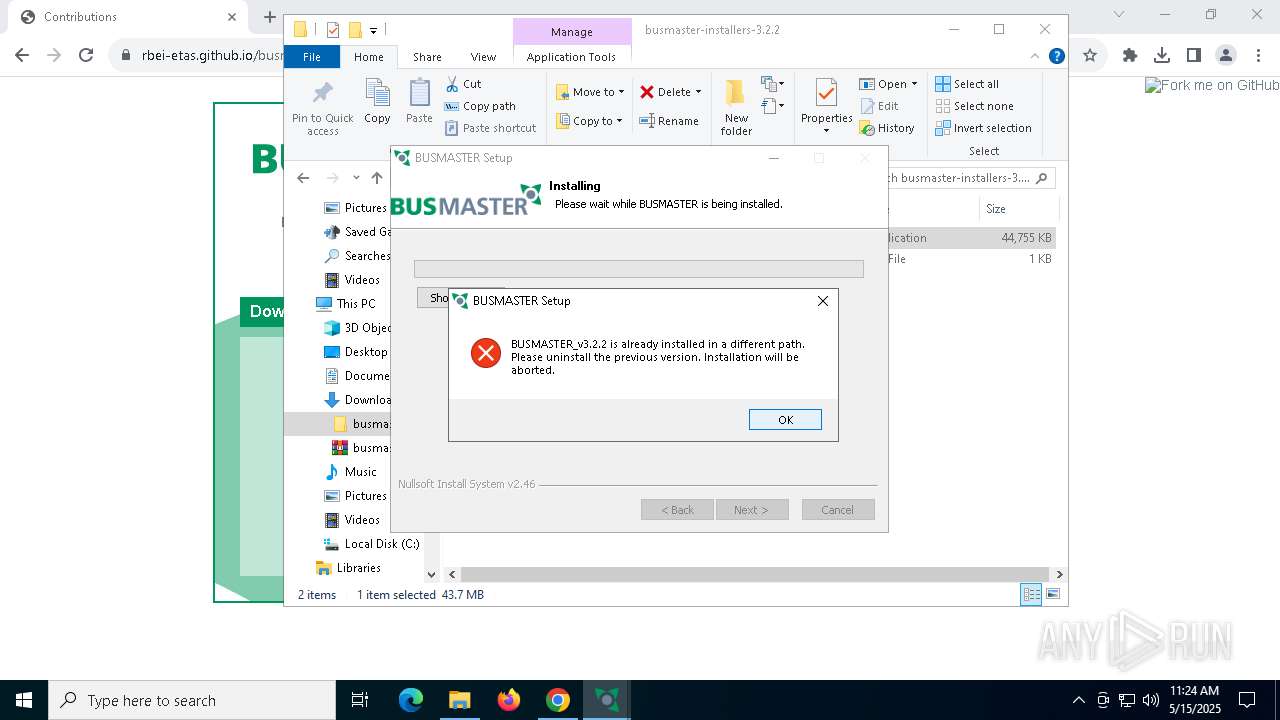
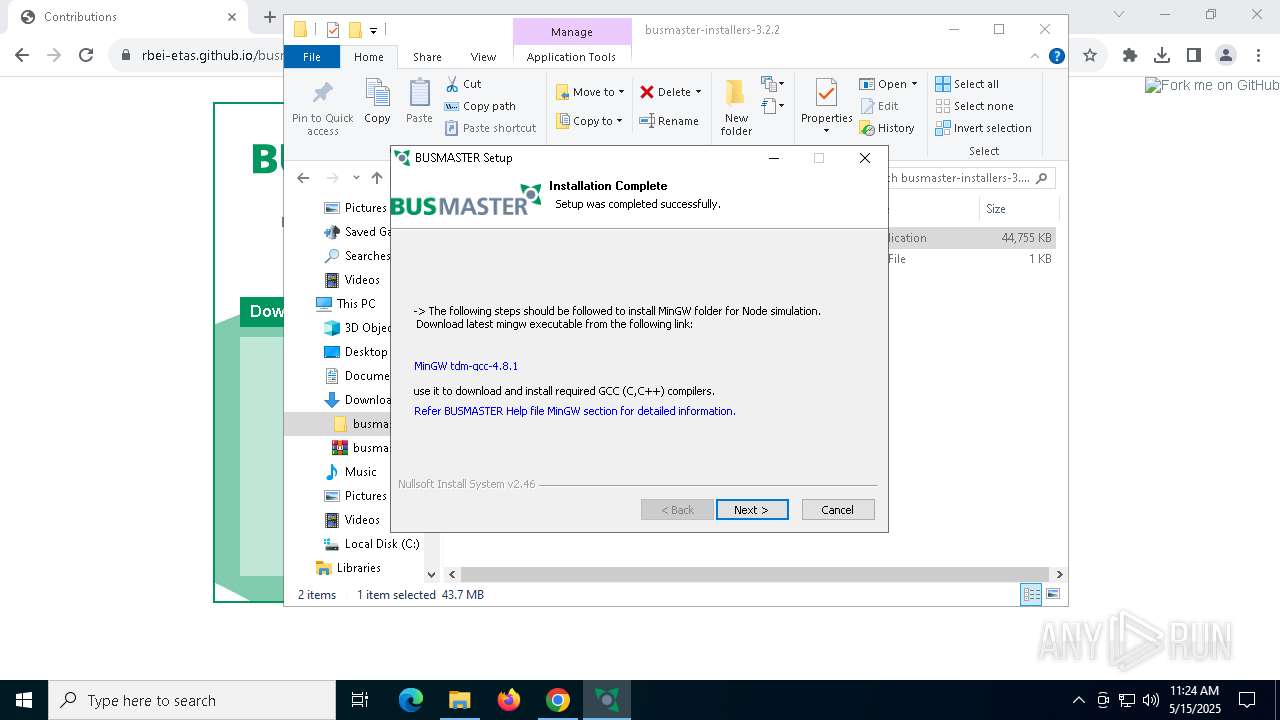
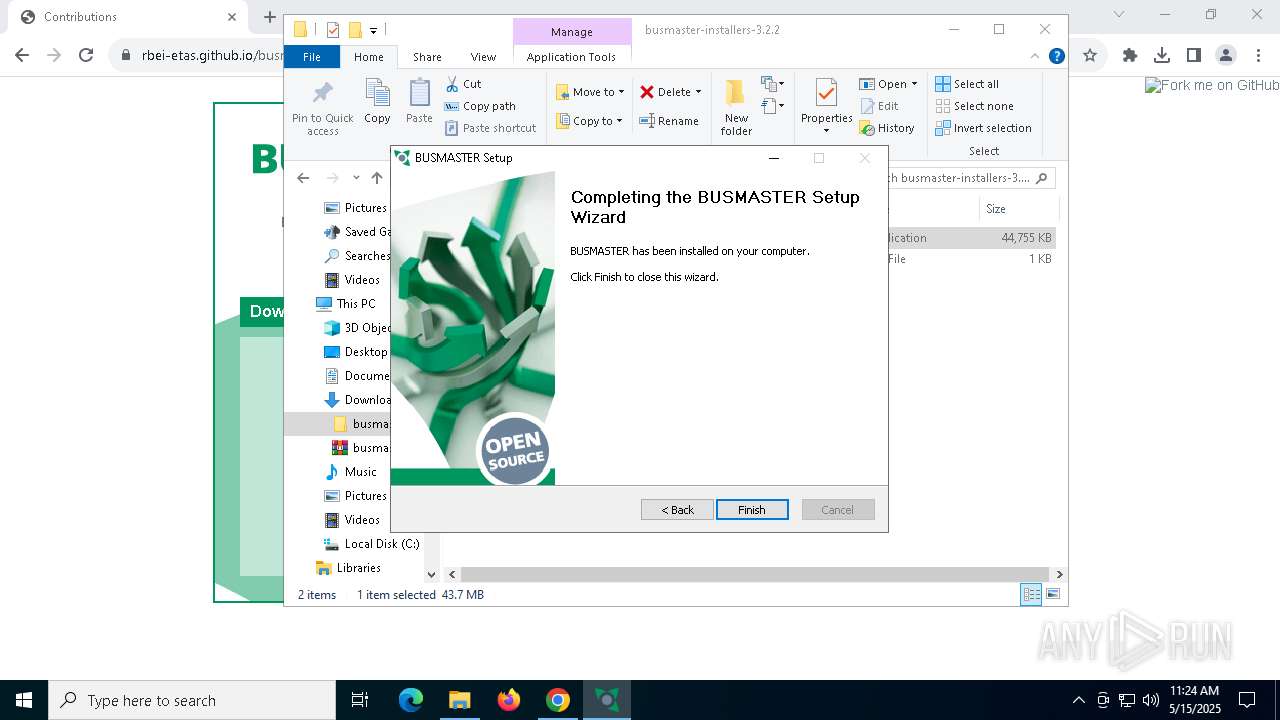
Manual execution by a user
- WinRAR.exe (PID: 1348)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 6816)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 6416)
- BUSMASTER.exe (PID: 928)
Reads the software policy settings
- slui.exe (PID: 8180)
Checks supported languages
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
- ShellExperienceHost.exe (PID: 4528)
Application launched itself
- chrome.exe (PID: 7424)
Create files in a temporary directory
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
Reads the computer name
- ShellExperienceHost.exe (PID: 4528)
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
The sample compiled with english language support
- BUSMASTER_Installer_Ver_3.2.2.exe (PID: 7192)
- vcredist_x86.exe (PID: 5428)
- msiexec.exe (PID: 7860)
- vcredist_x86.exe (PID: 7144)
The sample compiled with spanish language support
- msiexec.exe (PID: 7860)
Manages system restore points
- SrTasks.exe (PID: 3760)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7860)
The sample compiled with chinese language support
- msiexec.exe (PID: 7860)
The sample compiled with Italian language support
- msiexec.exe (PID: 7860)
The sample compiled with german language support
- msiexec.exe (PID: 7860)
The sample compiled with korean language support
- msiexec.exe (PID: 7860)
The sample compiled with french language support
- msiexec.exe (PID: 7860)
The sample compiled with japanese language support
- msiexec.exe (PID: 7860)
The sample compiled with russian language support
- msiexec.exe (PID: 7860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
40
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5896 --field-trial-handle=1928,i,13858019209768812742,12460468094662033101,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 660 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
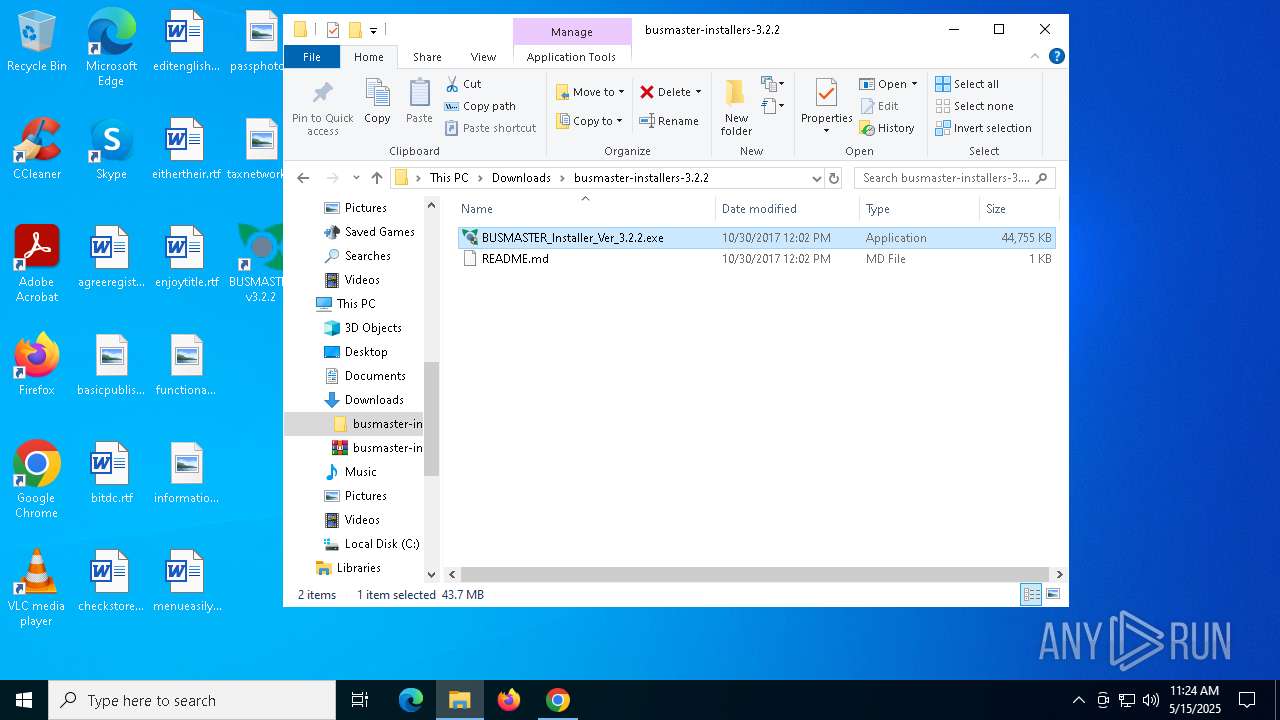
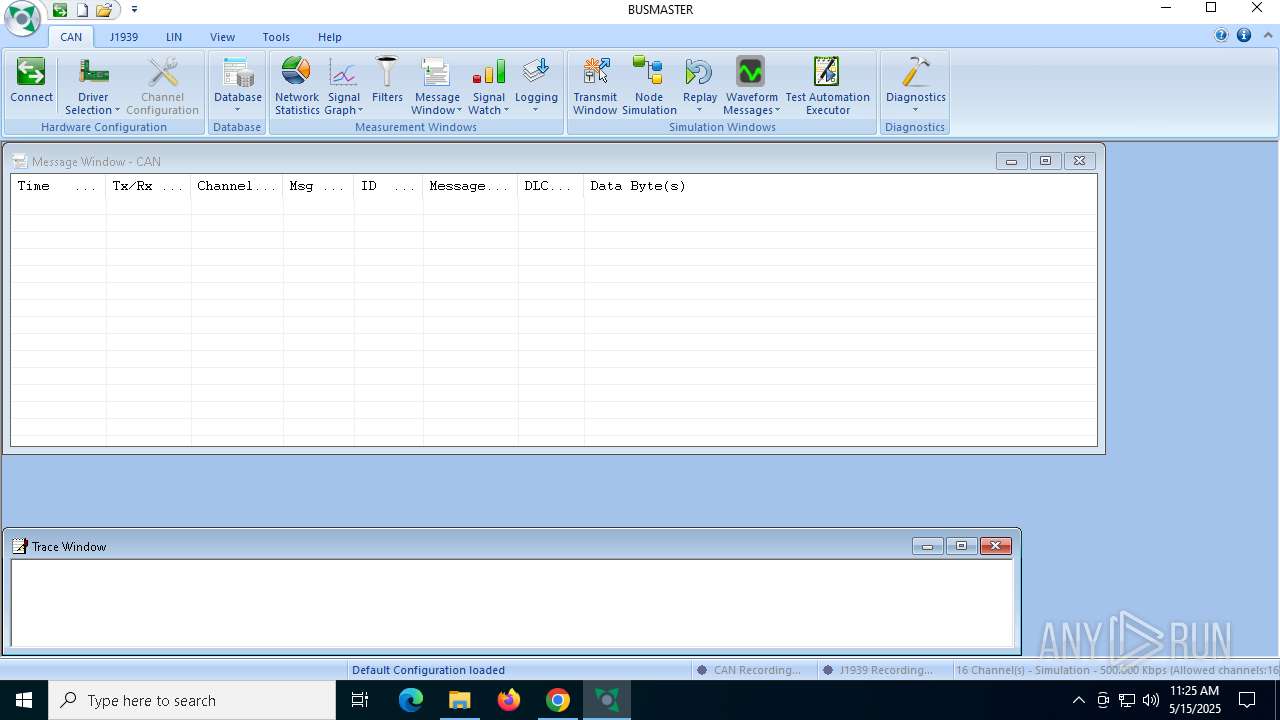
| 928 | "C:\Program Files (x86)\BUSMASTER_v3.2.2\BUSMASTER.exe" | C:\Program Files (x86)\BUSMASTER_v3.2.2\BUSMASTER.exe | — | explorer.exe | |||||||||||
User: admin Company: RBEI, Bangalore Integrity Level: MEDIUM Description: BUSMASTER MFC Application Version: Ver 3.2.2 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5228 --field-trial-handle=1928,i,13858019209768812742,12460468094662033101,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
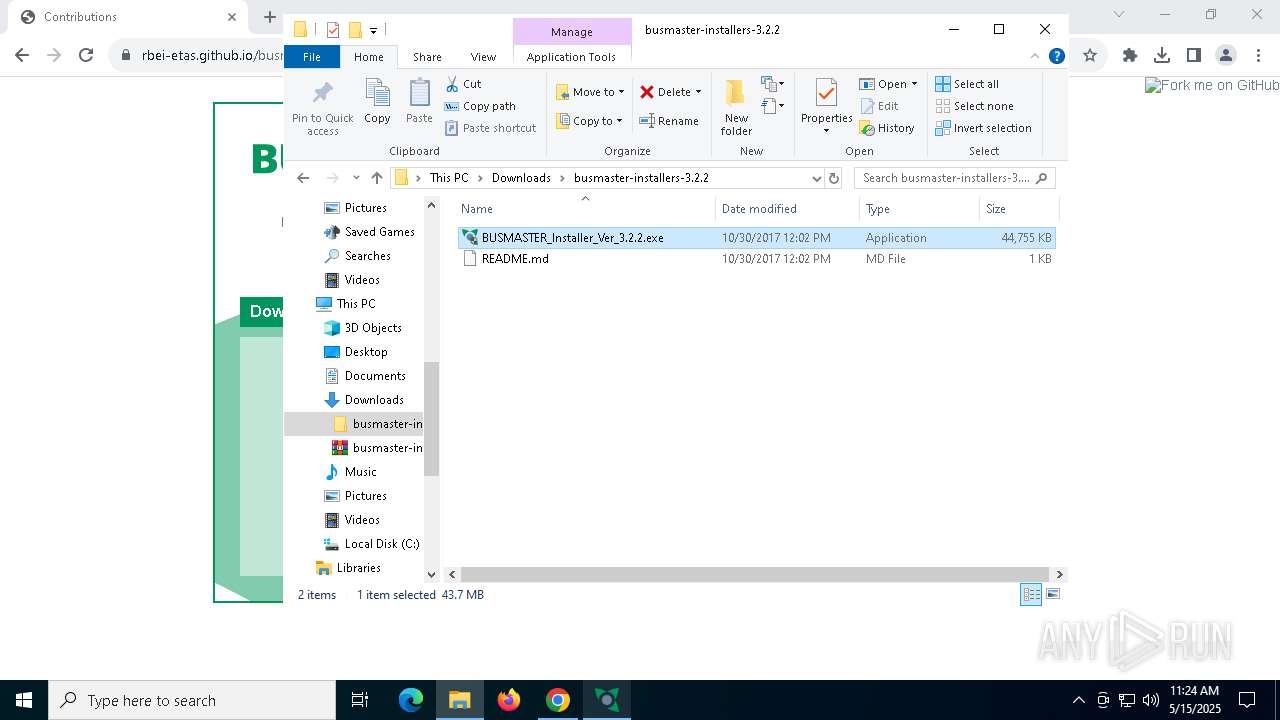
| 1348 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\busmaster-installers-3.2.2.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5560 --field-trial-handle=1928,i,13858019209768812742,12460468094662033101,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5908 --field-trial-handle=1928,i,13858019209768812742,12460468094662033101,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3760 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4528 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 575
Read events
22 954
Write events
573
Delete events
48
Modification events
| (PID) Process: | (7424) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7424) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7424) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7424) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7424) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5504) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000094D846AB8BC5DB01 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
130
Suspicious files
405
Text files
68
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10e244.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10e244.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10e244.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10e244.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10e253.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
68
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7696 | chrome.exe | GET | 301 | 69.16.219.69:80 | http://www.maploco.com/vmap/7413431.png | unknown | — | — | unknown |
7696 | chrome.exe | GET | 301 | 172.67.209.162:80 | http://hitwebcounter.com/counter/counter.php?page=6798093&style=0030&nbdigits=6&type=ip&initCount=97 | unknown | — | — | malicious |
7696 | chrome.exe | GET | 301 | 69.16.219.69:80 | http://www.maploco.com/vmap/7413431.png | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7696 | chrome.exe | GET | 403 | 52.216.42.80:80 | http://s3.amazonaws.com/github/ribbons/forkme_right_darkblue_121621.png | unknown | — | — | whitelisted |
7696 | chrome.exe | GET | 301 | 172.67.209.162:80 | http://hitwebcounter.com/counter/counter.php?page=6798093&style=0030&nbdigits=6&type=ip&initCount=97 | unknown | — | — | malicious |
7696 | chrome.exe | GET | 403 | 52.216.42.80:80 | http://s3.amazonaws.com/github/ribbons/forkme_right_darkblue_121621.png | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7696 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7424 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
rbei-etas.github.io |
| unknown |
accounts.google.com |
| whitelisted |
www.maploco.com |
| unknown |
m.maploco.com |
| shared |
www.google.com |
| whitelisted |