| File name: | f_0000c3 |
| Full analysis: | https://app.any.run/tasks/cade741d-bb02-49e0-b81a-3d7c2799b27f |
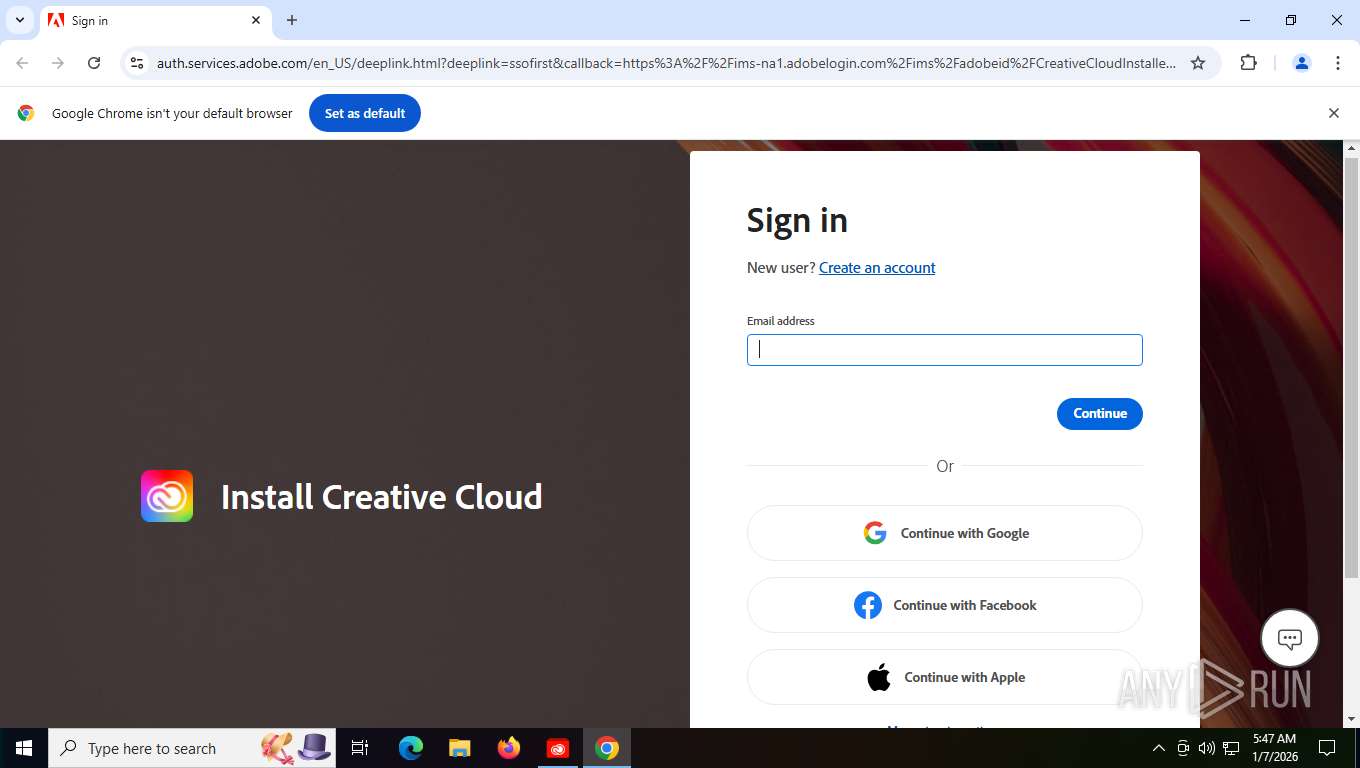
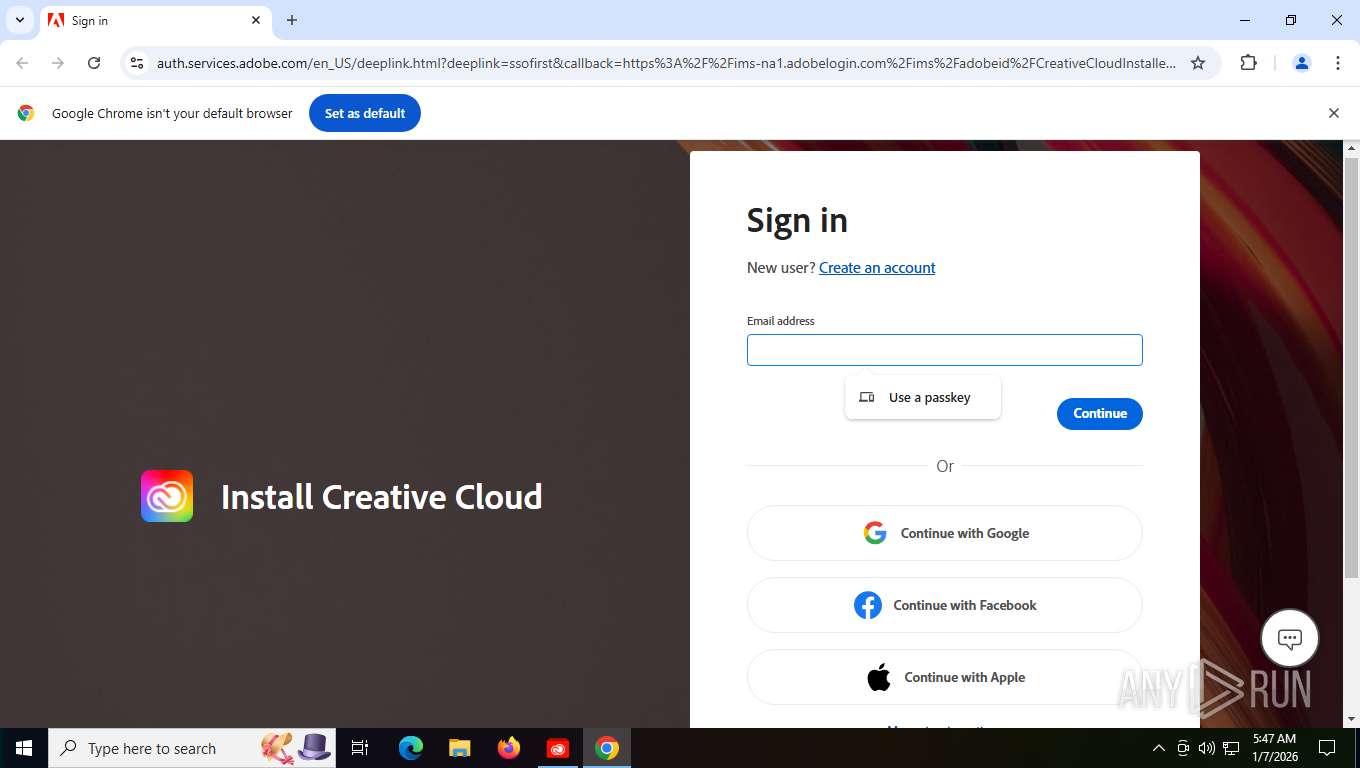
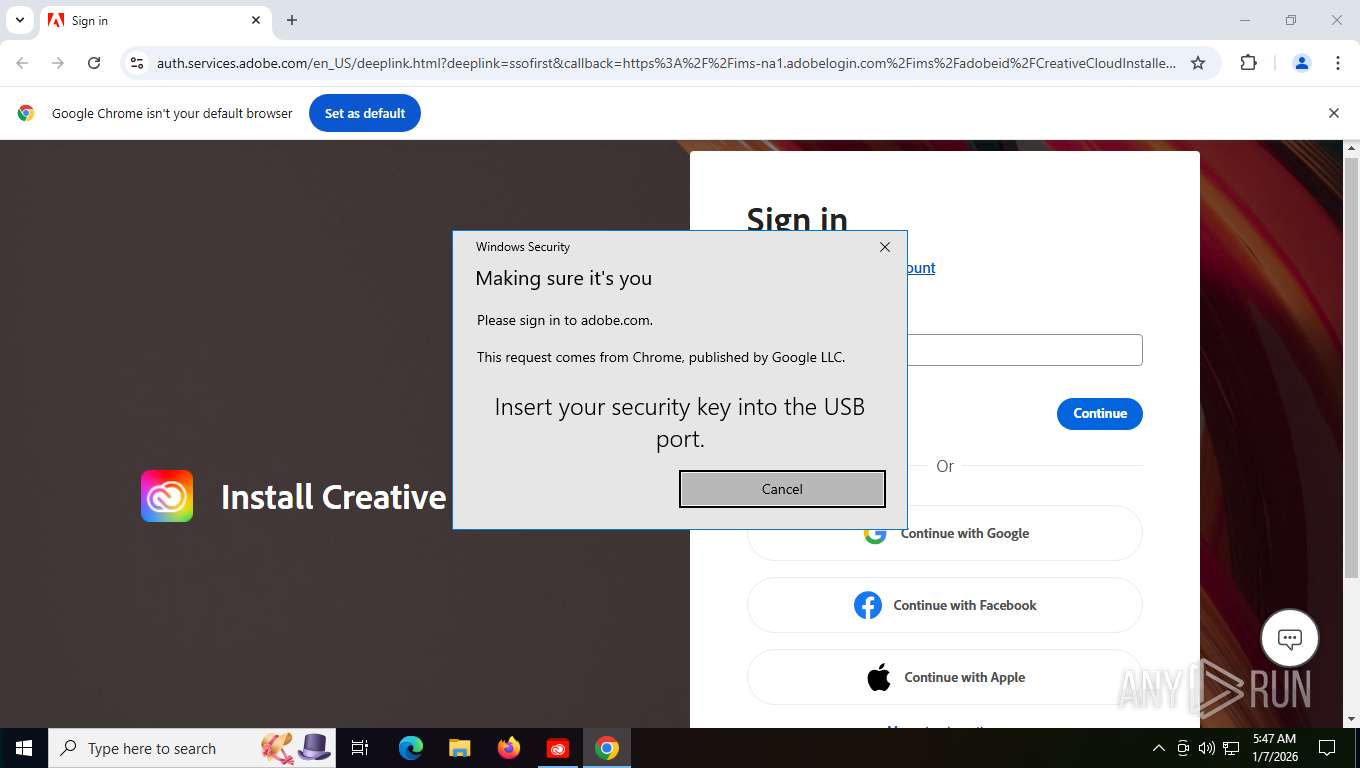
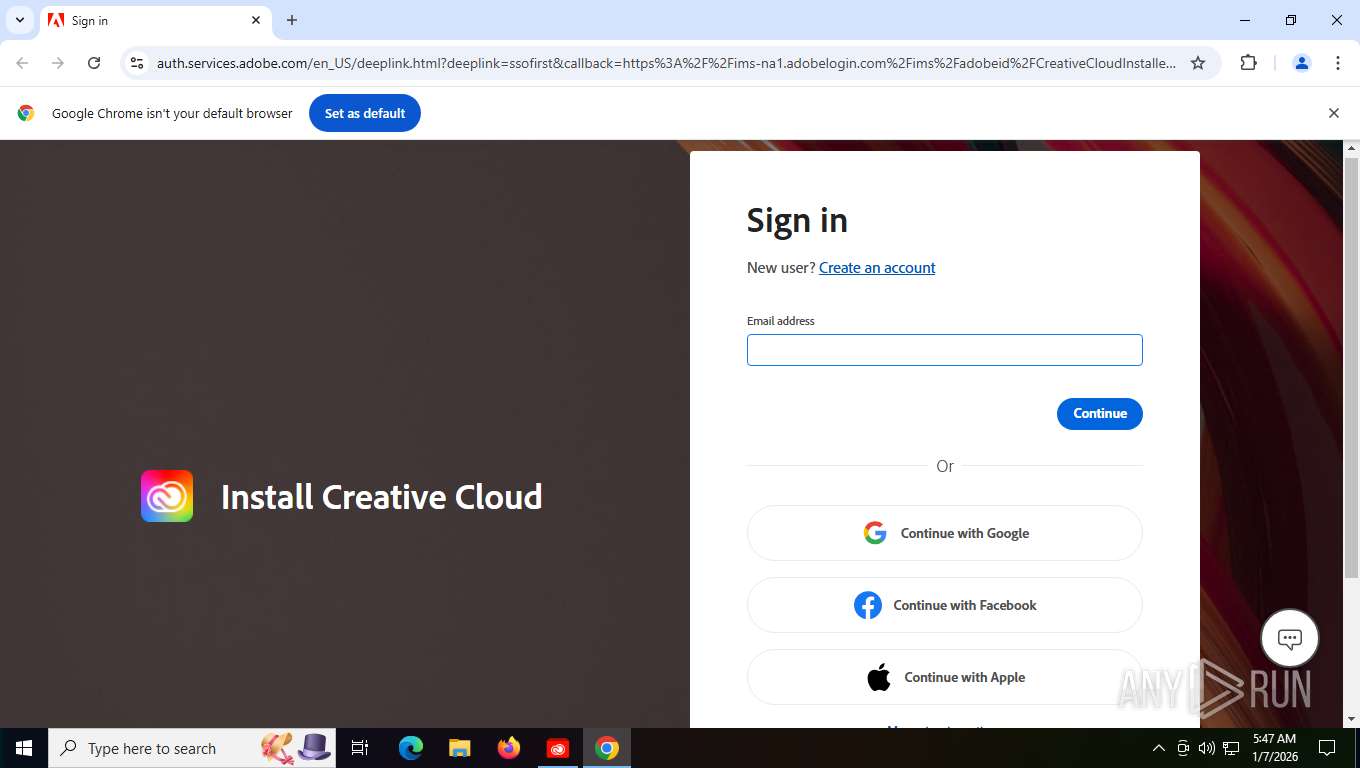
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2026, 10:46:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 1DDBF8FBDE2A2E8195744A1B178EF098 |
| SHA1: | 6C5011CFE6569EB473E592A5A2CAE01BC91F1942 |
| SHA256: | 3645F5B037ECD72048AA93274EBF5E28C2CBE7AD0FD8A0D70259AF00B5FFEDA2 |
| SSDEEP: | 98304:R3QTis5LIuMshE3qPuyLKp5Wdq4o3Ebxrv8UjF12EB6nBAnK25HDo7bXGsO3p3Gi:PM9pmvdi |
MALICIOUS
Changes settings of System certificates
- f_0000c3.exe (PID: 7500)
SUSPICIOUS
Reads security settings of Internet Explorer
- f_0000c3.exe (PID: 7500)
Reads Internet Explorer settings
- f_0000c3.exe (PID: 7500)
Reads Microsoft Outlook installation path
- f_0000c3.exe (PID: 7500)
Application launched itself
- f_0000c3.exe (PID: 7500)
Adds/modifies Windows certificates
- f_0000c3.exe (PID: 7500)
Starts CMD.EXE for commands execution
- f_0000c3.exe (PID: 7500)
INFO
The sample compiled with english language support
- f_0000c3.exe (PID: 7500)
Creates files or folders in the user directory
- f_0000c3.exe (PID: 7500)
- f_0000c3.exe (PID: 5160)
Checks supported languages
- f_0000c3.exe (PID: 7500)
- f_0000c3.exe (PID: 5160)
- TextInputHost.exe (PID: 8080)
Checks proxy server information
- f_0000c3.exe (PID: 7500)
Process checks whether UAC notifications are on
- f_0000c3.exe (PID: 7500)
Reads the computer name
- f_0000c3.exe (PID: 7500)
- f_0000c3.exe (PID: 5160)
- TextInputHost.exe (PID: 8080)
UPX packer has been detected
- f_0000c3.exe (PID: 7500)
- f_0000c3.exe (PID: 5160)
Reads the machine GUID from the registry
- f_0000c3.exe (PID: 7500)
Create files in a temporary directory
- f_0000c3.exe (PID: 5160)
- f_0000c3.exe (PID: 7500)
Reads CPU info
- f_0000c3.exe (PID: 7500)
- f_0000c3.exe (PID: 5160)
Process checks computer location settings
- f_0000c3.exe (PID: 7500)
Application launched itself
- chrome.exe (PID: 7248)
Reads security settings of Internet Explorer
- CredentialUIBroker.exe (PID: 4280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:09:11 15:26:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 3321856 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | 7786496 |
| EntryPoint: | 0xa98ce0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.14.0.57 |
| ProductVersionNumber: | 2.14.0.57 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
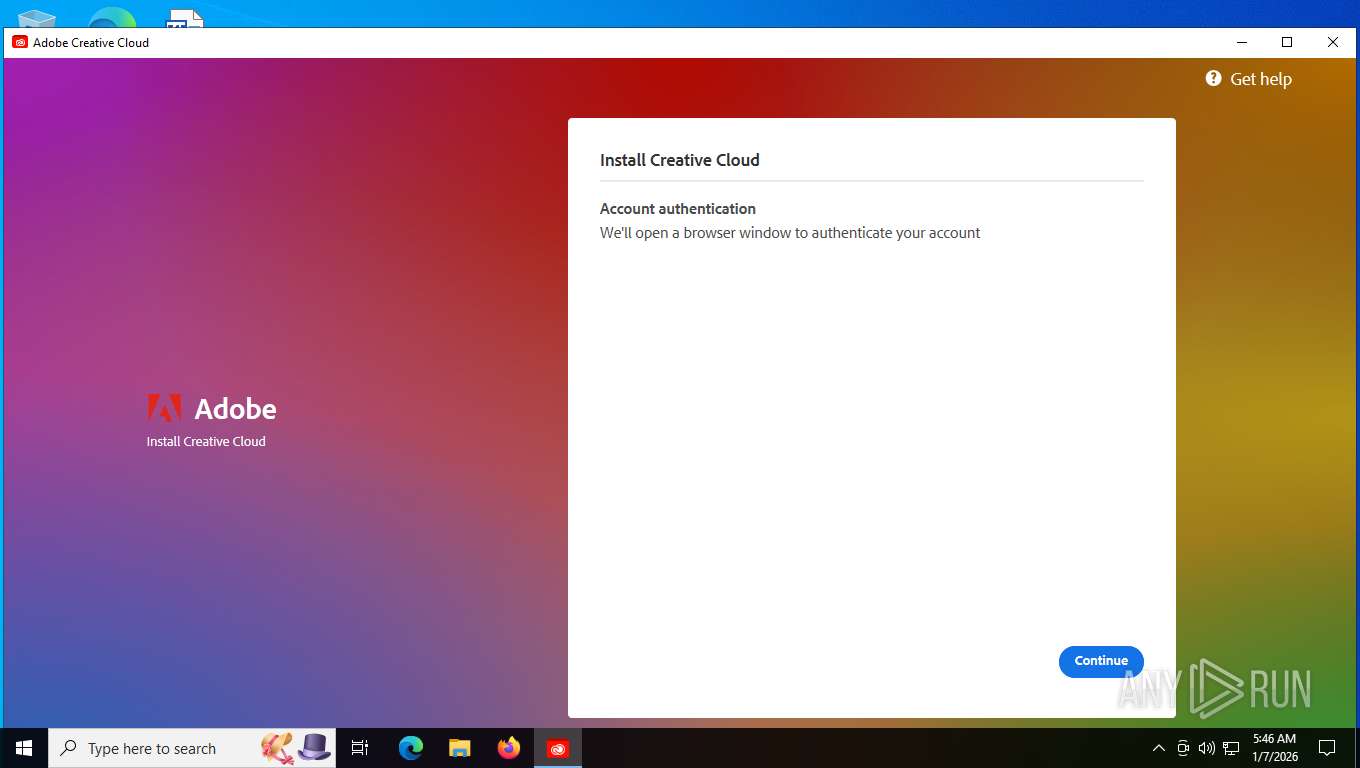
| CompanyName: | Adobe Inc. |
| FileDescription: | Adobe Installer |
| FileVersion: | 2.14.0.57 |
| InternalName: | Adobe Installer |
| LegalCopyright: | © 2015-2024 Adobe. All rights reserved. |
| OriginalFileName: | Adobe Installer |
| ProductName: | Adobe Installer |
| ProductVersion: | 2.14.0.57 |
Total processes
183
Monitored processes
37
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2376,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5812,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5836,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --string-annotations --field-trial-handle=6396,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3076 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
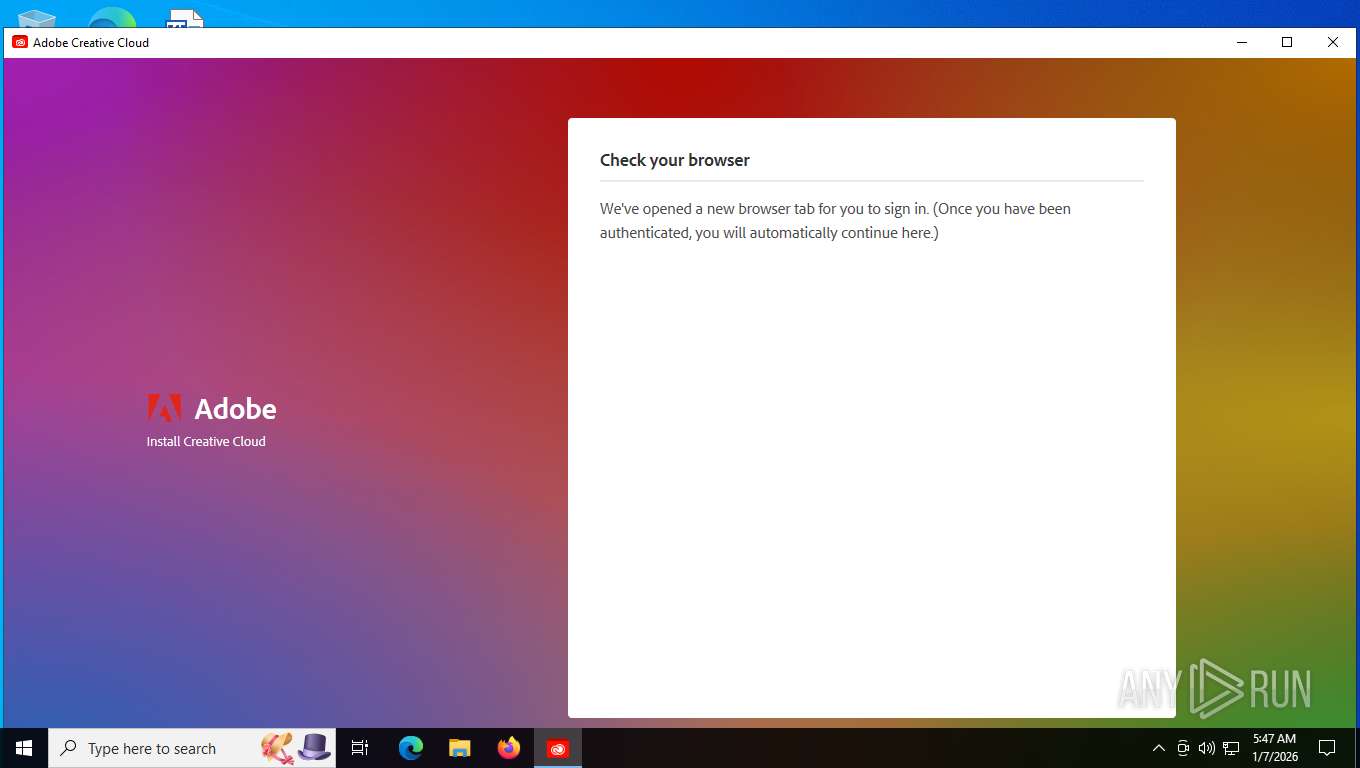
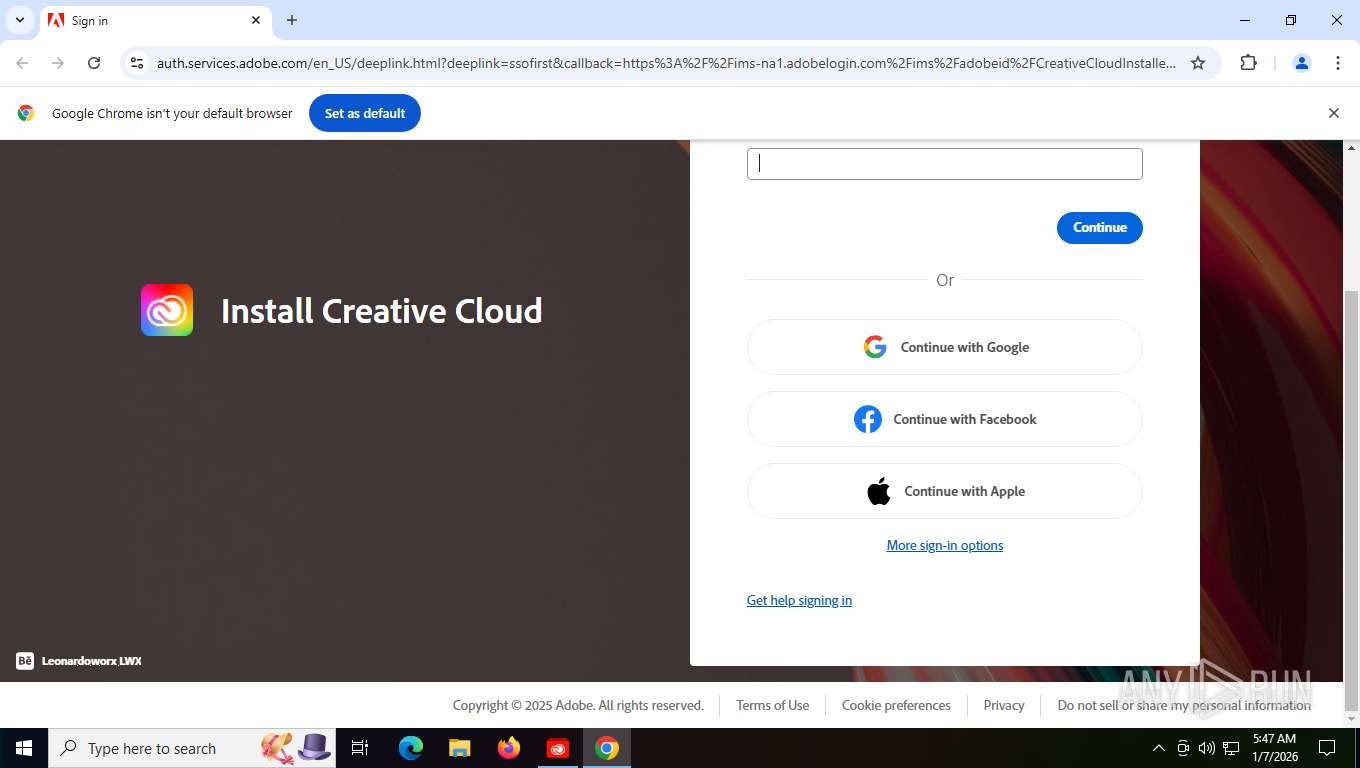
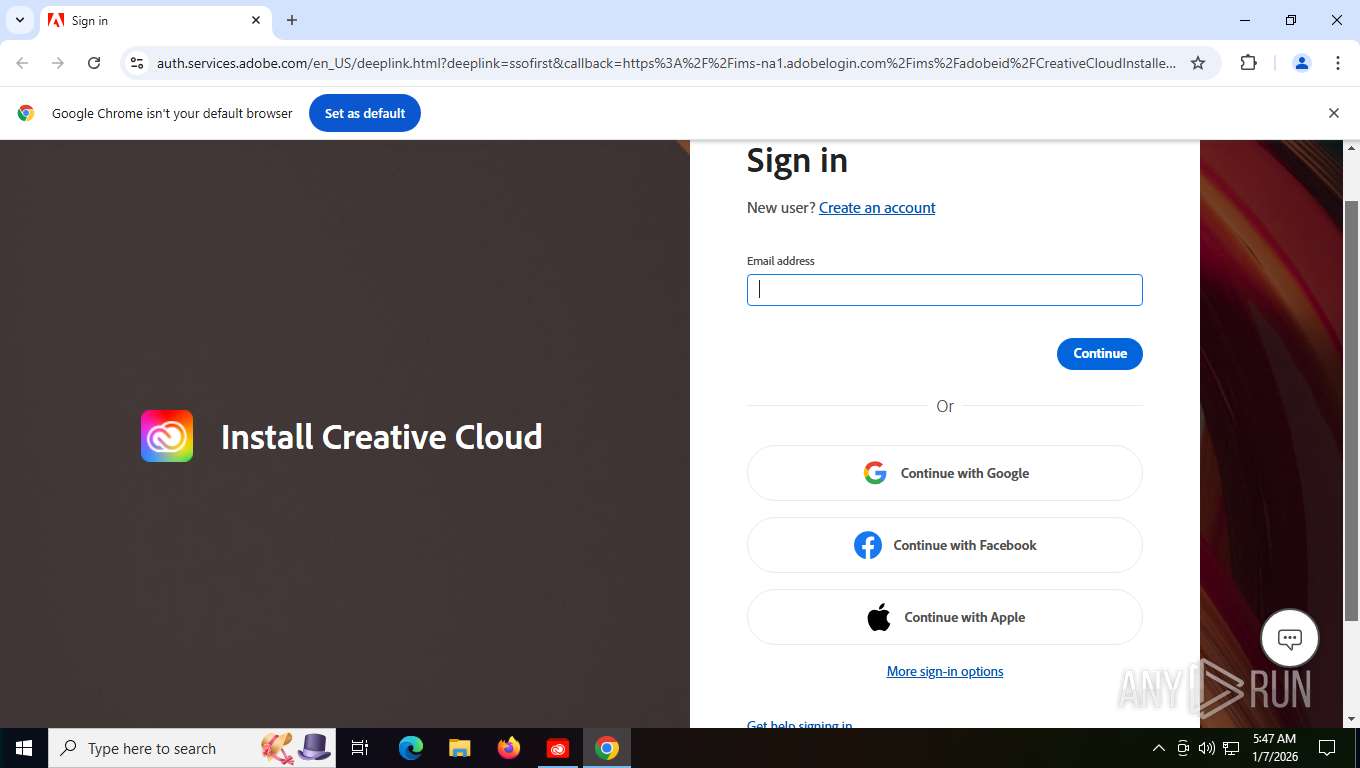
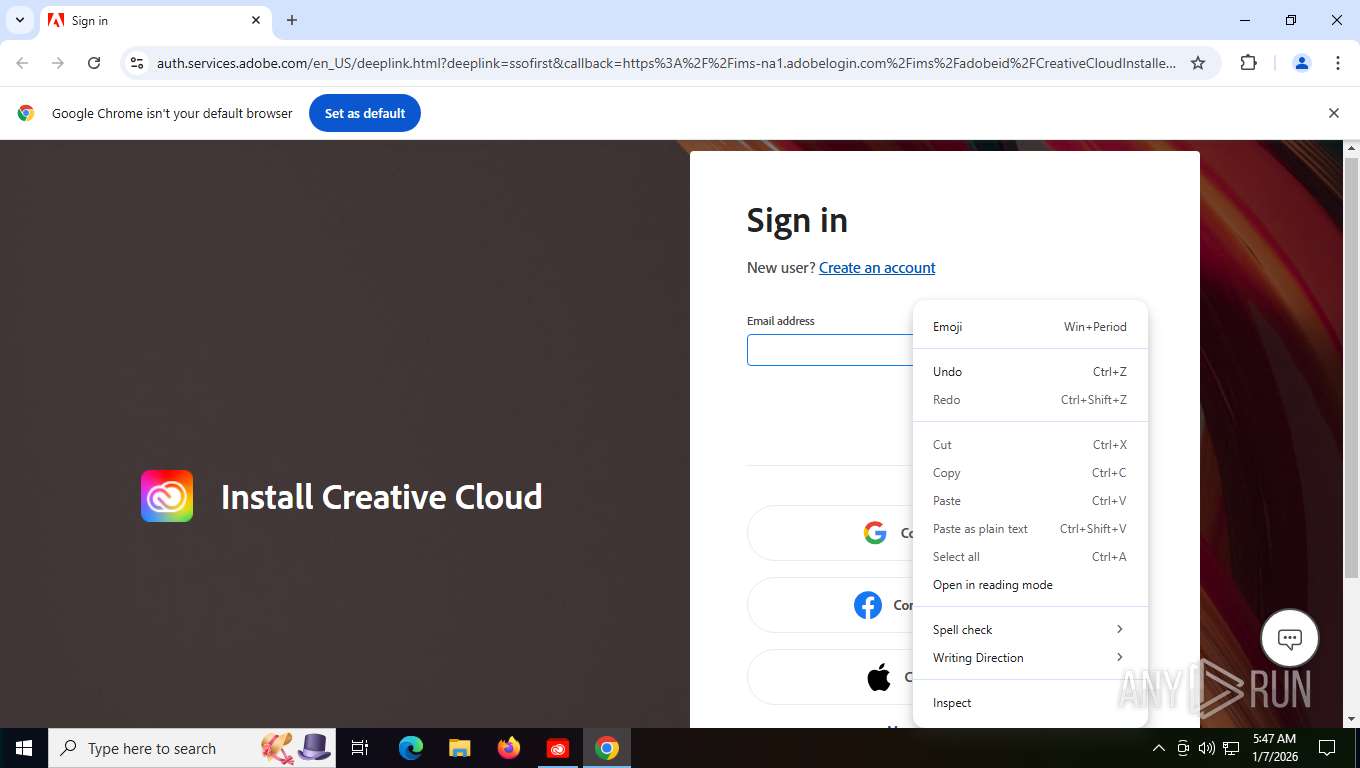
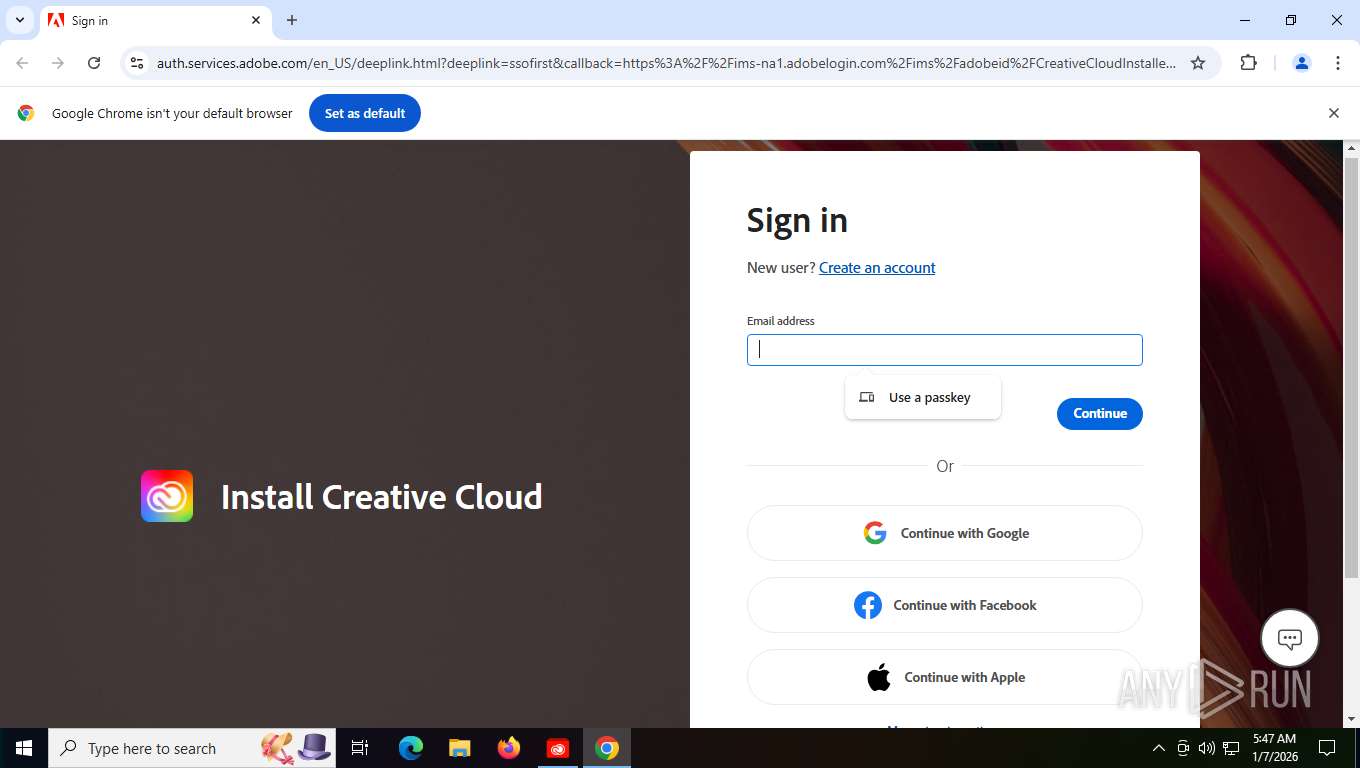
| 2740 | "C:\Windows\System32\cmd.exe" /C start chrome "https://ims-na1.adobelogin.com/ims/authorize?client_id=CreativeCloudInstallerWeb_v1_0&scope=allow_ac_dt_exchange%2Copenid%2CAdobeID%2Ccreative_cloud%2Ccreative_sdk%2Cread_organizations%2Csao.cce_private%2Cadditional_info.account_type&locale=en_US&redirect_uri=https%3A%2F%2Fauth.services.adobe.com%2Fen_US%2Fdeeplink.html%3Fdelegated_request_id%3Dac4d0694-b186-400d-9709-089d0a25b98f%26client_id%3DCreativeCloudInstallerWeb_v1_0%26deeplink%3Ddelegation&ctx_id=WAM2_KCCC_5_1" | C:\Windows\SysWOW64\cmd.exe | — | f_0000c3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3888,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3864 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4996,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3256,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 4280 | "C:\Windows\System32\CredentialUIBroker.exe" NonAppContainer -Embedding | C:\Windows\System32\CredentialUIBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Credential Manager UI Host Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6280,i,11706766811282802374,14003463983879467656,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
7 556
Read events
7 541
Write events
11
Delete events
4
Modification events
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates |
| Operation: | delete value | Name: | 686DF0A4A89F7CB6BFB4D33C6A48E2EE5FB6C4FB |
Value: | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates\686DF0A4A89F7CB6BFB4D33C6A48E2EE5FB6C4FB |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000686DF0A4A89F7CB6BFB4D33C6A48E2EE5FB6C4FB2000000001000000C3050000308205BF308203A7A003020102020401CFBD1C300D06092A864886F70D01010D050030818E310B30090603550406130255533113301106035504080C0A43616C69666F726E69613111300F06035504070C0853616E204A6F736531163014060355040A0C0D41646F62652053797374656D7331193017060355040B0C10436C6F756420546563686E6F6C6F67793124302206035504030C1B41646F626520496E7465726D6564696174652043412031302D3139301E170D3233303830373135313132375A170D3330303830353135313132355A308191310B30090603550406130255533113301106035504080C0A43616C69666F726E69613111300F06035504070C0853616E204A6F736531163014060355040A0C0D41646F62652053797374656D7331193017060355040B0C10436C6F756420546563686E6F6C6F67793127302506035504030C1E41646F626520436F6E74656E742043657274696669636174652031302D3830820222300D06092A864886F70D01010105000382020F003082020A0282020100D119F9B8D2D41D892ABF9F1F3CD1F947141B9867E9BE6D96E479C74C87E42F61F5B927BCCB7CAEBE27B26465B8E2F1118C2041980B88D7F559B8F9D041110E19F29CE5033FE9B8184D47982257E97D1B62744521BC329A7861A2376EEB8F3248EB031A7B43B1F22174FCC3C642033770137CAD8329B240970127EDD3030D9A69AF242FC7405B5867D0F5950BB0B79F702E84180EE43CA21F46ADCE07AD014F5CFD7BE25E735EB0431889BCCE40A4E94791FCA5A65DA24838D189B85218C9961EB1BCE8DB4CB2FFC7A2C3419788E68098350CACC6AA61DFB3D8476454927F9AB767037A84ED4E39862B3F386A065B169403259617150679E34AF188035D8BEBD9F4F22544CBF81F0D0516799D39A17A56C12E5C151945D65084367647C6F6A78ADE46F7BCC0B8ACA7D8ABFE3EB34AB2D1FB7800A98DA86C8DA956B267E309634D55FF7F6570F9B926BD602D4A94E77C662D1479C576B972D87BB35EA634B5F676774D40E04A0A908948C269C7DC71778ED5D15D9B8F4519EE858BC273A49AFC7A206AFD97286716B832E64154A074305D7BBCB7F2205017D1ED5CA6E42EDC6D35FABC88DD188028B15E5AA5296E12C03486A80A6E3CB0C001E4742B1EDF02FA70C2EBDCBEC606480054FC467729E99D1EB80BEE04B36FB17C722068079146FDE54B06C3EC5C4BAFAF113D2000EF36AEBE8454560E81D0CF982A798BAE3C39CD430203010001A320301E300E0603551D0F0101FF040403020780300C0603551D130101FF04023000300D06092A864886F70D01010D050003820201006BF0137EE63D74F0DF4EE19376625AC33574898A025B764E9BD69F8C7D9FA1C7F9B58F0355F206CAB84927D626275A8FD0D1C6A3B9A7811B361A68523AD86199EC1188922CE525246BFEF1B4DD23EB5B8EE0894D4495CEB1C0F27BCA3812C7C02432F9A693C7A331C53162A76C687C0FF60B31389A0E11F9DA1FD8CEAE91FF671222083643E0A7C0B97F170AB051856AB58C8B3278D16753CFAAC05CEC9A08C0FCC2E993AAEA79225D70E9EC8BFB53C93BE8915B2026A35BF05D3C9E5E417FABC5648D9FD8F153E8787F1E3CDD637FE2ABD8C8A5D1C9171C342E588A77FF2739DC6B88C79DC933DEDF535C496BA652A184B6B65B831AA7706251494108D58F8565624E37A343696F2E42C029333DAB8B1A9E34BDA64B58546906E9BD3F0D67F3CB830E8B6BF3B01F653C938DA93B53A6878A14FE75550B546D580FA40F0E6E6FAC25113513F48C9FC79B27689B906AFD59D11ABBDF4FDE466D2A93431606DB3938D9E9F7505D1A0CD91E4F116A2F3E1837BA0C1AB0CC74724916A65D9B2C09B00EEF96BDA7156F789449923371B5AAC2A6728B0B3E71AC656EBC820BAD65977CEBAF56611C8D322C78AF95C5DC1C2E56D95ECA6EFB5664010860DD6C82FAF60A9CD493EECC6B013449633928D96BB0D38F28F838564DB989958ECFD5325FA51F8EC4148545C5A94705BEB7200B427F978959CC7A031FE58F7E2F42AD48E3BB82 | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates |
| Operation: | delete value | Name: | 85E2C5B0D9CFF505363FA62A5E8B8C1D76A60B46 |
Value: | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates\85E2C5B0D9CFF505363FA62A5E8B8C1D76A60B46 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000085E2C5B0D9CFF505363FA62A5E8B8C1D76A60B462000000001000000BC050000308205B8308203A0A003020102020426C66CD0300D06092A864886F70D01010D0500308185310B30090603550406130255533113301106035504080C0A43616C69666F726E69613111300F06035504070C0853616E204A6F736531163014060355040A0C0D41646F62652053797374656D7331193017060355040B0C10436C6F756420546563686E6F6C6F6779311B301906035504030C1241646F626520526F6F742043412031302D333020170D3138303831373137333831395A180F32303638303830343137333831395A30818E310B30090603550406130255533113301106035504080C0A43616C69666F726E69613111300F06035504070C0853616E204A6F736531163014060355040A0C0D41646F62652053797374656D7331193017060355040B0C10436C6F756420546563686E6F6C6F67793124302206035504030C1B41646F626520496E7465726D6564696174652043412031302D313930820222300D06092A864886F70D01010105000382020F003082020A0282020100B533B875034A0E7563110700E026D838B4ED1369EE54D6DB09EBF764A4778EF8A7DC7DFBA9386A78E61BE8FF8722D2CA1535CC02C111F9FAE54FDC09698D22D9D936B3133AAB757B596A1C093CF3559F351D3F10DC44FB0F9787E1F685E83DC775C74D0E563F1509071A1D4BCD919D0B9EBAF925867A85E7E5B9B13040760DFBE2A9BD70E028963DD69631E9CF2F5CA3A6634AC8BFE2DAE5CDE9DF35E935B4F88A17FC78786052BADF6E5A378E34A16D16EC7EEB69BF0917FD7210AE129AE2B5F3473E28EA73E25E81176229F0AD99B74069CF6C30413AB85D86F7FEC519E01806A928CF2E5EA9C9AAE9F57A60401E76313FD017BBE23541B455DA6C7D49E39F6B451A67EA2160056781067C489526D297410AC05E87FBECA66D75BDA1EAEEC9652891598957F4C19FB53EC491B1D600D1AD75D7C164D613BA6CE275682F44399515C247D11D72DC440FD800225A13AE8D16494EAA9F1F82120D2F51243683D2AA62CDCF5BE075720B7D566EADB5E46EE3299B43296A49BF3FBE2E672E72E42E7918E608466028DE4F215CD362CFD921200FF946168717D09AF99095950812F5A4DE4073E2C5697A318B9EB51A585A36E74DBD8FB7277C8AEB7DDD42FFBEB32C181F9EDADDC1480B95F16E7EA37D0DAB3F2F5009D570AA4624B66A7017C75F1CAA7C544E15DEF0C6E6CF6A4F26312B68F633B7A5A4203C97E77A32141E7CF4970203010001A3233021300E0603551D0F0101FF040403020204300F0603551D130101FF040530030101FF300D06092A864886F70D01010D050003820201005BD66C82CA184490136B886EF3B5F5B6866768C8CFD13F701025AEB8DC8B7B4539C071032663327F1B55D773E062EA01551038BC12895B4A760A23EC0EF1E24C1D25649B12DAD880B576A952BA1F9D1ED0C5BDF45E8A9F9465C091E22FF7165912FBA642B3E2979897339AB2AE511615D3E20B27E3E60E13FE188C7C7119F14029CCFAF1E9FEF5C7E53CE1C0D1CFCB8507131C446AF5B7F67B701E1EE4151CADD14048737CF0EC86F8964D75B8509BF07A984441641622568D5EA1B9124101DB76C578BEE86ACDB651A90B5C3ABDAB541F3A41E82CBFC0D30319E1975924540A71E8D1A3603CAADE3CEFCF0B362B62FA09EFE97827276B0B79F58553136C89AA72A9F3F7FDAA87E5789978ABE6AF28C04F7D673954594329ACE012159C5EE6B2CB43B55F507E0E0F68233E8A3C6FE13A2CB23B4F38DDECAEAE21E99BD6E152793AD59B8286256EDE041654CB8A7C069D773868F8BDDEA44FCCDCFC4C0CFEC6F9357093024D88519A40BDB3B77B0988051418FCBA0A67C5CAABC66F21D094E5D612DD7F951291892A4F8EF35EFDB2C9D940FCBDDFDB75D19B1B215A36DEC147C9D716BB4A06047E90D0D0FAD64A56F24A6B650843D5CDD2ABA7E8894B4693D775AEBC8D65063D1813B0BE5C9C6357C43BE7AEA9B3B6021935ACC2B8F38746AEAB5EAA06F447BE0CFFF20B38811E273023CD035F14AD3A7BABEE646909282CC3EF | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates |
| Operation: | delete value | Name: | 4C7C2E87F0BC79A039D39B05F899A1CC521FDE99 |
Value: | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates\4C7C2E87F0BC79A039D39B05F899A1CC521FDE99 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000004C7C2E87F0BC79A039D39B05F899A1CC521FDE992000000001000000C3050000308205BF308203A7A00302010202046E271780300D06092A864886F70D01010D050030818E310B30090603550406130255533113301106035504080C0A43616C69666F726E69613111300F06035504070C0853616E204A6F736531163014060355040A0C0D41646F62652053797374656D7331193017060355040B0C10436C6F756420546563686E6F6C6F67793124302206035504030C1B41646F626520496E7465726D6564696174652043412031302D3135301E170D3233303830373133343834335A170D3330303830353133343834315A308191310B30090603550406130255533113301106035504080C0A43616C69666F726E69613111300F06035504070C0853616E204A6F736531163014060355040A0C0D41646F62652053797374656D7331193017060355040B0C10436C6F756420546563686E6F6C6F67793127302506035504030C1E41646F626520436F6E74656E742043657274696669636174652031302D3730820222300D06092A864886F70D01010105000382020F003082020A0282020100AD280D5CFB35F4129A580996209E83CD117CAB917F7F8B85E353C39899FA07BC7050077DB622FE4B43C477C0ABB8325A1EE90F76416E2AF5CB76ED9CCEC153694C6ADD14358E1C5C45D32DB721654781BA134E981AE3B21D56FE739AFD397DB8101FA65554AD67D9B808D45487D9913BD7CF30E094A948546DA75F51395AB7B0F122244976683D87CE6797AAEA3D5EE468553FC658B2B9530E33E2AA418950458D4147270F8773E3D93DA7DF6A1E8F58E439218236D110A658BF5037260D3F596E1F06B9E963F758ECA3F99FAA454640628E3BC66C16E914AAD9BEA5A47F954CA0FF73CF4237E8545E5E82F66795493508A6852F4564EF44DBB31B23C27D6DCC54E749094BB404073ED05AB6BF54AFADEC8EA7B58CE2D935C4B0EC8A054BEF86CEBFD63FAAB8FAE41104E8BDAF1F3F2474D78E050C8F33510C80ABBA83C0DA198107E47B40CD119B71827A510AE65E9B97D5E617B397CF517CFECBC47A890BBC350C5B631A50F254151D4D84CD512E0F57241E10B1BD1569287A900D4BF4A23532556266BC1C8B1014972F126B20A2E2E7DB73774EB822669FC2BCF56D817EE3F5D20F9B029EC62D377D5328000CE5D921C965337C500416A6C3E828ED27AD8ED370F8B9035C322CE75ED6DE25002E363475F95E24AD6E30B9350EB2934A431BF09C8B4DF073213FD6393192D796022B4275A73E5B4A2BF3B226D6A537E96C450203010001A320301E300E0603551D0F0101FF040403020780300C0603551D130101FF04023000300D06092A864886F70D01010D05000382020100315188A437CB6A526AB679D888EF1051EA301191B36FF818D3E7E1B8CBC8E1C078FC058E0D7BD61B11FD8EFEF27B411C3F494F6734C286008FFB39D2EECF012929913628C5B160F6CA24FAB63068FC48CB91293FC302F3D16F5DE8DBDFE3A57ABCA9A081C4CFA82FA3E06F36A318251A351C5E08FE4F4A286D1EBB4BF87278F7E54FAF53E1B37148F19F210136C5F3B5981A89A3AAF8351490555D001AEE6C9AB2BD27CC13D162EF6314C47FCE2C668E16ED641D2B6871EF3B0AFBC8E5E2B93D775049061496057A361C2CD1ED7CBDADD143A0F114E9D5066C6E2F2BFD771B44C8979CF0F094D2D89E104C935EF362EABCCCDA4559BB33E640B3C1920CF314688FDC639665E8E81F6B9312516D937A6DB751FD39E044271432D0E83BFCB5E8DF5CBE2A7C15E272E09AA96F939AC7B6655FCFE91E59474B3A4CECF12490CB1F3AA2A80AE53CBE867CCAEFF9CA84D487BF438F4213B253148FF8BE54CAEE1E4AA157353F707A966F946E89A8FC8964849EB948BD54B2B2E6D1DD85BA7DF45208206472A5AA93860C5EE8F6460739EA3231EC590F09602FF29F09ECEDBDBD635CB42670C8288B3F051DD6C393240D0A668B9A2C20BD70F182CE58D152089385AB717C7C624826EC39424050AD45048927D2E771BE6F6693055589F3612DF47C206D6AE8600F9D60F7AEBC5567458D8A423B76D6082AB213FFF88584909E76B458AB | |||
| (PID) Process: | (7500) f_0000c3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\SystemCertificates\AdobeCertStore\Certificates |
| Operation: | delete value | Name: | A5C8D928986EC17FCC7D5F2353885D1709B73A29 |
Value: | |||
Executable files
0
Suspicious files
89
Text files
63
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Roaming\com.adobe.dunamis\f65a88c9-12b3-4201-a633-87cf11b91fa8\v1\0\meta_events\4445ee8f-4b39-4162-8638-1bacbb618aa3 | — | |
MD5:— | SHA256:— | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Roaming\com.adobe.dunamis\f65a88c9-12b3-4201-a633-87cf11b91fa8\v1\0\anon_events\69923123-b9cb-4dad-8b93-3a107a8b0ab8 | — | |
MD5:— | SHA256:— | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Local\Temp\CreativeCloud\ACC\WAM.log | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Local\Temp\Adobe\com.adobe.dunamis\dunamis-2026-01-07_10-46-35.log | text | |
MD5:256A465B529EE03FD21A3C219D9F67D6 | SHA256:95E705F0027AB27A968030B3E2234926566C78F2BC1C840E62F3F60DD21165E1 | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Roaming\com.adobe.dunamis\f65a88c9-12b3-4201-a633-87cf11b91fa8\v1\0\anon_events\manifest | binary | |
MD5:45971D4E3A47775BB5A7260BB5EA3C36 | SHA256:81C611F35BFF79491538B2F7CF201C7597A661A5C549633541C62BDC8AF1613F | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Local\Temp\{21D4A988-97AB-473F-88E0-DFD8CCF7F87E}\index.html | html | |
MD5:A28AB17B18FF254173DFEEF03245EFD0 | SHA256:886C0AB69E6E9D9D5B5909451640EA587ACCFCDF11B8369CAD8542D1626AC375 | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Local\Temp\{21D4A988-97AB-473F-88E0-DFD8CCF7F87E}\index.css | text | |
MD5:E09F799BB69CECAF3987BC12CF65DD24 | SHA256:CDD337F639E76F36FA41002B26E9A4F8C819D196747983283E25E3049FE5028E | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:0532FE3D4E1EFEF410E3965647EFEEC3 | SHA256:B02A5F4614CD8A5CFD5A2EE17837F44D841C070CD847C4A813F08D19EED666BB | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Roaming\com.adobe.dunamis\f65a88c9-12b3-4201-a633-87cf11b91fa8\v1\0\meta_events\manifest | binary | |
MD5:45971D4E3A47775BB5A7260BB5EA3C36 | SHA256:81C611F35BFF79491538B2F7CF201C7597A661A5C549633541C62BDC8AF1613F | |||
| 7500 | f_0000c3.exe | C:\Users\admin\AppData\Local\Adobe\OOBE\temp_lbs_wid | text | |
MD5:8032F09FCA1CD4894CE84D933D9330D3 | SHA256:543DBE6E677579D06C6A36F7D8BBD5F69AA258BE3E08D0A1DC120D7775F6E95B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
155
TCP/UDP connections
85
DNS requests
80
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7500 | f_0000c3.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7500 | f_0000c3.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAmKLzE6ssKc1CsGKg5Geww%3D | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
7500 | f_0000c3.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7500 | f_0000c3.exe | POST | 200 | 52.73.45.44:443 | https://cc-api-data.adobe.io/ingest | unknown | — | — | unknown |
7500 | f_0000c3.exe | GET | 200 | 13.33.187.19:443 | https://client.messaging.adobe.com/latest/AdobeMessagingClient.js | unknown | text | 128 Kb | whitelisted |
7500 | f_0000c3.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
7500 | f_0000c3.exe | GET | 200 | 13.33.187.19:443 | https://client.messaging.adobe.com/latest/AdobeMessagingClient.css | unknown | text | 56.7 Kb | whitelisted |
7500 | f_0000c3.exe | GET | 200 | 107.22.247.231:443 | https://p13n.adobe.io/fg/api/v2/feature?clientId=NglBaseFeatureClient&meta=true&nglLocale=en_US&nglLibRunTimeMode=NAMED_USER_ONLINE&nglOsPlatform=WIN_X86_32&nglPlatformID=9f8d6c3956377ee884e33ee8c5858fa463e0fe6770a974e3a5f5a0c8809c47f0 | unknown | text | 723 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5436 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2900 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7500 | f_0000c3.exe | 107.22.247.231:443 | p13n.adobe.io | AMAZON-AES | US | whitelisted |
7500 | f_0000c3.exe | 52.73.45.44:443 | cc-api-data.adobe.io | AMAZON-AES | US | whitelisted |
7500 | f_0000c3.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
7500 | f_0000c3.exe | 13.33.187.19:443 | client.messaging.adobe.com | AMAZON-02 | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
cc-api-data.adobe.io |
| whitelisted |
p13n.adobe.io |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.messaging.adobe.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |