| File name: | Linkvertise-Bypassed-Link_620382.exe |
| Full analysis: | https://app.any.run/tasks/b8b9e5c9-253c-4593-904a-e0acdc857907 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2023, 22:27:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 25BF828EB7F8E63E0AF77F391A34BEC5 |
| SHA1: | CF0607BCBFD85508114CF71B95186875764BBCFC |
| SHA256: | 364144AA26B5BE6DC9BF399CF33F4A1CC64C82EDD70369512B134D64BEC10F4B |
| SSDEEP: | 49152:U7F6yA5Bneq5lGXEn8R8/iq2ir7SaJeq12X3ht5jHvisWMjqzTy8IPcd5T:U7WGXb8amYBHj5W1FIPcdZ |
MALICIOUS
Application was dropped or rewritten from another process
- AdventurousiUtility.exe (PID: 1984)
SUSPICIOUS
Application launched itself
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
Reads the Internet Settings
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Adds/modifies Windows certificates
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
Reads settings of System Certificates
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Executable content was dropped or overwritten
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
INFO
The process checks LSA protection
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Checks supported languages
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
- AdventurousiUtility.exe (PID: 1984)
Reads product name
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Reads the computer name
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Reads Environment values
- Linkvertise-Bypassed-Link_620382.exe (PID: 1116)
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Creates files in the program directory
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Reads the machine GUID from the registry
- Linkvertise-Bypassed-Link_620382.exe (PID: 3192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| OriginalFileName: | AdventurousClothTool.exe |
|---|---|
| LegalCopyright: | Adventurous Cloth LLC. |
| InternalName: | AdventurousClothTool.exe |
| CompanyName: | Adventurous Cloth LLC. |
| ProductVersion: | 1.0.0.0 |
| ProductName: | AdventurousClothTool |
| ProgramID: | com.Adventurous.tool |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Adventurous Cloth Tool |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x2a35b4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 567808 |
| CodeSize: | 2761728 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2023:01:27 19:15:18+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jan-2023 19:15:18 |
| Detected languages: |
|
| FileDescription: | Adventurous Cloth Tool |
| FileVersion: | 1.0.0.0 |
| ProgramID: | com.Adventurous.tool |
| ProductName: | AdventurousClothTool |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | Adventurous Cloth LLC. |
| InternalName: | AdventurousClothTool.exe |
| LegalCopyright: | Adventurous Cloth LLC. |
| OriginalFilename: | AdventurousClothTool.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 27-Jan-2023 19:15:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0029FAB4 | 0x0029FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36779 |
.itext | 0x002A1000 | 0x00002608 | 0x00002800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.13784 |
.data | 0x002A4000 | 0x00021410 | 0x00021600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.26842 |
.bss | 0x002C6000 | 0x00006FAC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x002CD000 | 0x000031FE | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.2906 |
.didata | 0x002D1000 | 0x00000DF6 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.50079 |
.edata | 0x002D2000 | 0x00000095 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.80124 |
.tls | 0x002D3000 | 0x00000058 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x002D4000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.36114 |
.reloc | 0x002D5000 | 0x00043D6C | 0x00043E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72834 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31806 | 1505 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.80231 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4058 | 3.218 | 1040 | UNKNOWN | UNKNOWN | RT_STRING |
4059 | 3.32296 | 880 | UNKNOWN | UNKNOWN | RT_STRING |
4060 | 3.32993 | 792 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
netapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x002C9640 |
__dbk_fcall_wrapper | 2 | 0x0000FE40 |
TMethodImplementationIntercept | 3 | 0x000B541C |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | "C:\Users\admin\AppData\Local\Temp\Linkvertise-Bypassed-Link_620382.exe" | C:\Users\admin\AppData\Local\Temp\Linkvertise-Bypassed-Link_620382.exe | — | explorer.exe | |||||||||||
User: admin Company: Adventurous Cloth LLC. Integrity Level: MEDIUM Description: Adventurous Cloth Tool Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
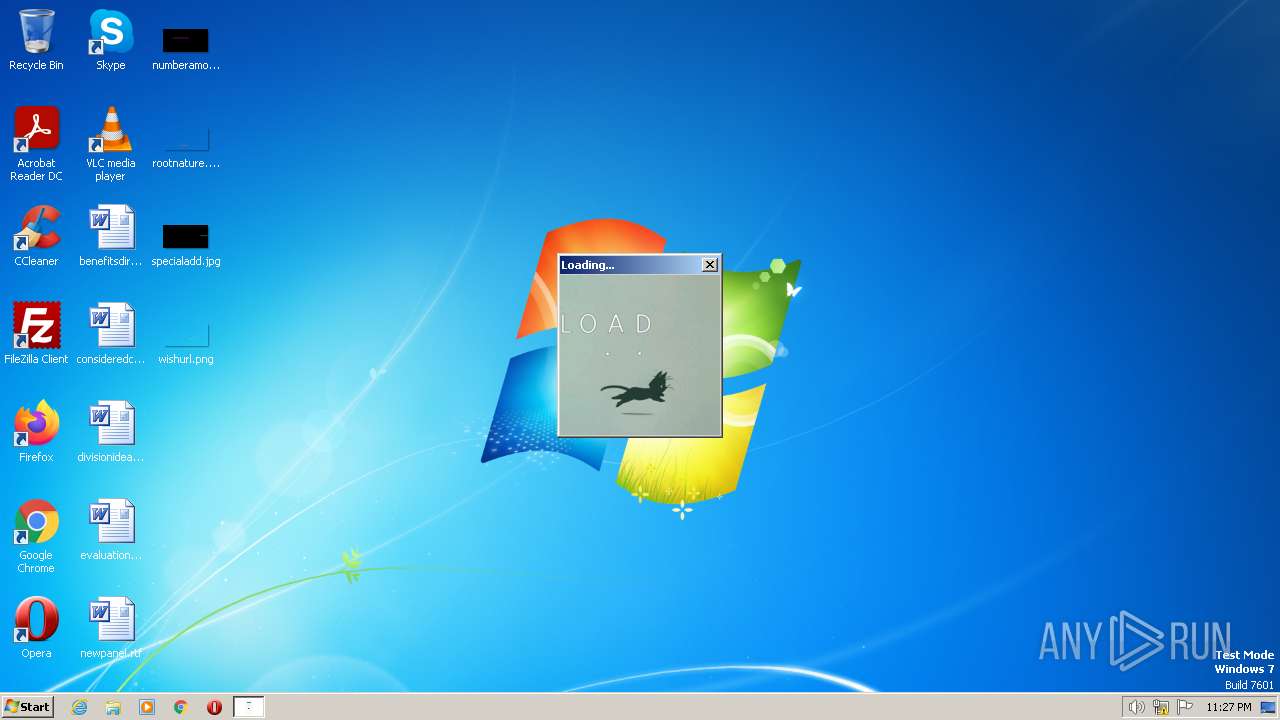
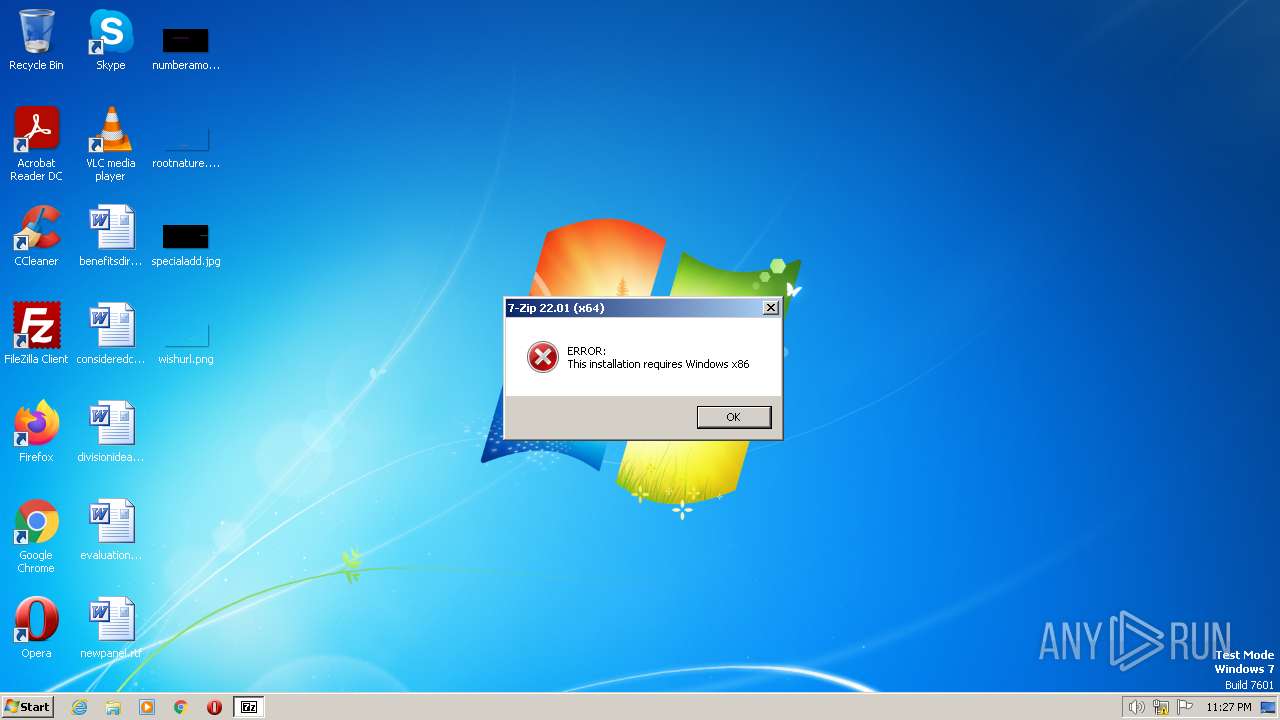
| 1984 | "C:\Program Files\AdventurousClothvrmUtility\AdventurousiUtility.exe" | C:\Program Files\AdventurousClothvrmUtility\AdventurousiUtility.exe | — | Linkvertise-Bypassed-Link_620382.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 1 Version: 22.01 Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\AppData\Local\Temp\Linkvertise-Bypassed-Link_620382.exe" /lap /toaq | C:\Users\admin\AppData\Local\Temp\Linkvertise-Bypassed-Link_620382.exe | Linkvertise-Bypassed-Link_620382.exe | ||||||||||||
User: admin Company: Adventurous Cloth LLC. Integrity Level: HIGH Description: Adventurous Cloth Tool Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
3 890
Read events
3 858
Write events
32
Delete events
0
Modification events
| (PID) Process: | (1116) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1116) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1116) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1116) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3192) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3192) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\E1C950E6EF22F84C5645728B922060D7D5A7A3E8 |
| Operation: | write | Name: | Blob |
Value: 09000000010000002A000000302806082B0601050507030206082B0601050507030406082B0601050507030106082B060105050703080F0000000100000030000000E4C58A0A499480862DB093ADA2B299298D57D1C586BEE12C4B74D5E13DD4BCBDA6D57BE981EEE012E984E6B83D0B4C7B030000000100000014000000E1C950E6EF22F84C5645728B922060D7D5A7A3E81D0000000100000010000000AFEC13F04D331040C81E81D2B3EC2E24140000000100000014000000E4AF2B26711A2B4827852F52662CEFF08913713E0B0000000100000018000000470054005300200052006F006F00740020005200310000006200000001000000200000002A575471E31340BC21581CBD2CF13E158463203ECE94BCF9D3CC196BF09A5472190000000100000010000000E6FEE6521C735BC60C74EBB251DA386620000000010000005E0500003082055A30820342A00302010202106E47A9C54B470C0DEC33D089B91CF4E1300D06092A864886F70D01010C05003047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F74205231301E170D3136303632323030303030305A170D3336303632323030303030305A3047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F7420523130820222300D06092A864886F70D01010105000382020F003082020A0282020100B611028B1EE3A1779B3BDCBF943EB795A7403CA1FD82F97D32068271F6F68C7FFBE8DBBC6A2E9797A38C4BF92BF6B1F9CE841DB1F9C597DEEFB9F2A3E9BC12895EA7AA52ABF82327CBA4B19C63DBD7997EF00A5EEB68A6F4C65A470D4D1033E34EB113A3C8186C4BECFC0990DF9D6429252307A1B4D23D2E60E0CFD20987BBCD48F04DC2C27A888ABBBACF5919D6AF8FB007B09E31F182C1C0DF2EA66D6C190EB5D87E261A45033DB079A49428AD0F7F26E5A808FE96E83C689453EE833A882B159609B2E07A8C2E75D69CEBA756648F964F68AE3D97C2848FC0BC40C00B5CBDF687B3356CAC18507F84E04CCD92D320E933BC5299AF32B529B3252AB448F972E1CA64F7E682108DE89DC28A88FA38668AFC63F901F978FD7B5C77FA7687FAECDFB10E799557B4BD26EFD601D1EB160ABB8E0BB5C5C58A55ABD3ACEA914B29CC19A432254E2AF16544D002CEAACE49B4EA9F7C83B0407BE743ABA76CA38F7D8981FA4CA5FFD58EC3CE4BE0B5D8B38E45CF76C0ED402BFD530FB0A7D53B0DB18AA203DE31ADCC77EA6F7B3ED6DF912212E6BEFAD832FC1063145172DE5DD61693BD296833EF3A66EC078A26DF13D757657827DE5E491400A2007F9AA821B6A9B195B0A5B90D1611DAC76C483C40E07E0D5ACD563CD19705B9CB4BED394B9CC43FD255136E24B0D671FAF4C1BACCED1BF5FE8141D800983D3AC8AE7A98371805950203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414E4AF2B26711A2B4827852F52662CEFF08913713E300D06092A864886F70D01010C0500038202010038960AEE3DB4961E5FEF9D9C0B339F2BE0CAFDD28E0A1F4174A57CAA84D4E5F21EE63752329C0BD1611DBF28C1B6442935757798B27CD9BD74AC8A68E3A9310929016073E3477C53A8904A27EF4BD79F93E78236CE9A680C82E7CFD410166F5F0E995CF61F717DEFEF7B2F7EEA36D697700B15EED75C566A33A5E349380CB87DFB8D85A4B1595EF46AE1DDA1F66444AEE651832166C6113EF3CE47EE9C281F25DAFFAC6695DD350F5CEF202C62FD91BAA9CCFC5A9C93818329974A7C5A72B439D0B777CB79FD693A9237ED6E3865467EE960BD7988975F3812F4EEAF5B82C886D5E1996D8C04F276BA49F66EE96D1E5FA0EF27827640F8A6D3585C0F2C42DA42C67B8834C7C1D8459BC13EC5611DD9635049F634856AE018C56E47AB4142299BF6600DD231D3639823935A008148B4EFCD8ACDC9CF99EED99EAA36E1684B71491436283A3D1DCE9A8F25E68071612BB57BCCF9251681E1315FA1A37E16A49C166A9718BD7672A50B9E1D36E62FA12FBE70910FA8E6DAF8C492406C257E7BB309DCB217AD8044F068A58F9475FF745AE8A8027C0C09E2A94B0BA0850B62B9EFA13192FBEFF65104896CE8A974A1BB17B3B5FD490F7C3CEC831820434ED593BAB434B11F16361F0CE66439164CDCE0FE1DC8A9623D40EACAC53402B4AE89883335DC2C1373D827F1D072EE753B22DE9868665BF1C66347551CBAA5085175A64825 | |||
| (PID) Process: | (3192) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\E1C950E6EF22F84C5645728B922060D7D5A7A3E8 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000821AEFD4D24AF29FE23D970614707285190000000100000010000000E6FEE6521C735BC60C74EBB251DA38666200000001000000200000002A575471E31340BC21581CBD2CF13E158463203ECE94BCF9D3CC196BF09A54720B0000000100000018000000470054005300200052006F006F0074002000520031000000140000000100000014000000E4AF2B26711A2B4827852F52662CEFF08913713E1D0000000100000010000000AFEC13F04D331040C81E81D2B3EC2E24030000000100000014000000E1C950E6EF22F84C5645728B922060D7D5A7A3E80F0000000100000030000000E4C58A0A499480862DB093ADA2B299298D57D1C586BEE12C4B74D5E13DD4BCBDA6D57BE981EEE012E984E6B83D0B4C7B09000000010000002A000000302806082B0601050507030206082B0601050507030406082B0601050507030106082B0601050507030820000000010000005E0500003082055A30820342A00302010202106E47A9C54B470C0DEC33D089B91CF4E1300D06092A864886F70D01010C05003047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F74205231301E170D3136303632323030303030305A170D3336303632323030303030305A3047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F7420523130820222300D06092A864886F70D01010105000382020F003082020A0282020100B611028B1EE3A1779B3BDCBF943EB795A7403CA1FD82F97D32068271F6F68C7FFBE8DBBC6A2E9797A38C4BF92BF6B1F9CE841DB1F9C597DEEFB9F2A3E9BC12895EA7AA52ABF82327CBA4B19C63DBD7997EF00A5EEB68A6F4C65A470D4D1033E34EB113A3C8186C4BECFC0990DF9D6429252307A1B4D23D2E60E0CFD20987BBCD48F04DC2C27A888ABBBACF5919D6AF8FB007B09E31F182C1C0DF2EA66D6C190EB5D87E261A45033DB079A49428AD0F7F26E5A808FE96E83C689453EE833A882B159609B2E07A8C2E75D69CEBA756648F964F68AE3D97C2848FC0BC40C00B5CBDF687B3356CAC18507F84E04CCD92D320E933BC5299AF32B529B3252AB448F972E1CA64F7E682108DE89DC28A88FA38668AFC63F901F978FD7B5C77FA7687FAECDFB10E799557B4BD26EFD601D1EB160ABB8E0BB5C5C58A55ABD3ACEA914B29CC19A432254E2AF16544D002CEAACE49B4EA9F7C83B0407BE743ABA76CA38F7D8981FA4CA5FFD58EC3CE4BE0B5D8B38E45CF76C0ED402BFD530FB0A7D53B0DB18AA203DE31ADCC77EA6F7B3ED6DF912212E6BEFAD832FC1063145172DE5DD61693BD296833EF3A66EC078A26DF13D757657827DE5E491400A2007F9AA821B6A9B195B0A5B90D1611DAC76C483C40E07E0D5ACD563CD19705B9CB4BED394B9CC43FD255136E24B0D671FAF4C1BACCED1BF5FE8141D800983D3AC8AE7A98371805950203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414E4AF2B26711A2B4827852F52662CEFF08913713E300D06092A864886F70D01010C0500038202010038960AEE3DB4961E5FEF9D9C0B339F2BE0CAFDD28E0A1F4174A57CAA84D4E5F21EE63752329C0BD1611DBF28C1B6442935757798B27CD9BD74AC8A68E3A9310929016073E3477C53A8904A27EF4BD79F93E78236CE9A680C82E7CFD410166F5F0E995CF61F717DEFEF7B2F7EEA36D697700B15EED75C566A33A5E349380CB87DFB8D85A4B1595EF46AE1DDA1F66444AEE651832166C6113EF3CE47EE9C281F25DAFFAC6695DD350F5CEF202C62FD91BAA9CCFC5A9C93818329974A7C5A72B439D0B777CB79FD693A9237ED6E3865467EE960BD7988975F3812F4EEAF5B82C886D5E1996D8C04F276BA49F66EE96D1E5FA0EF27827640F8A6D3585C0F2C42DA42C67B8834C7C1D8459BC13EC5611DD9635049F634856AE018C56E47AB4142299BF6600DD231D3639823935A008148B4EFCD8ACDC9CF99EED99EAA36E1684B71491436283A3D1DCE9A8F25E68071612BB57BCCF9251681E1315FA1A37E16A49C166A9718BD7672A50B9E1D36E62FA12FBE70910FA8E6DAF8C492406C257E7BB309DCB217AD8044F068A58F9475FF745AE8A8027C0C09E2A94B0BA0850B62B9EFA13192FBEFF65104896CE8A974A1BB17B3B5FD490F7C3CEC831820434ED593BAB434B11F16361F0CE66439164CDCE0FE1DC8A9623D40EACAC53402B4AE89883335DC2C1373D827F1D072EE753B22DE9868665BF1C66347551CBAA5085175A64825 | |||
| (PID) Process: | (3192) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3192) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3192) Linkvertise-Bypassed-Link_620382.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | Linkvertise-Bypassed-Link_620382.exe | C:\Program Files\AdventurousClothvrmUtility\AdventurousiUtility.exe | executable | |
MD5:A6A0F7C173094F8DAFEF996157751ECF | SHA256:B055FEE85472921575071464A97A79540E489C1C3A14B9BDFBDBAB60E17F36E4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | Linkvertise-Bypassed-Link_620382.exe | 172.67.72.44:443 | apptorrentcompany.com | CLOUDFLARENET | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4008 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
apptorrentcompany.com |
| unknown |