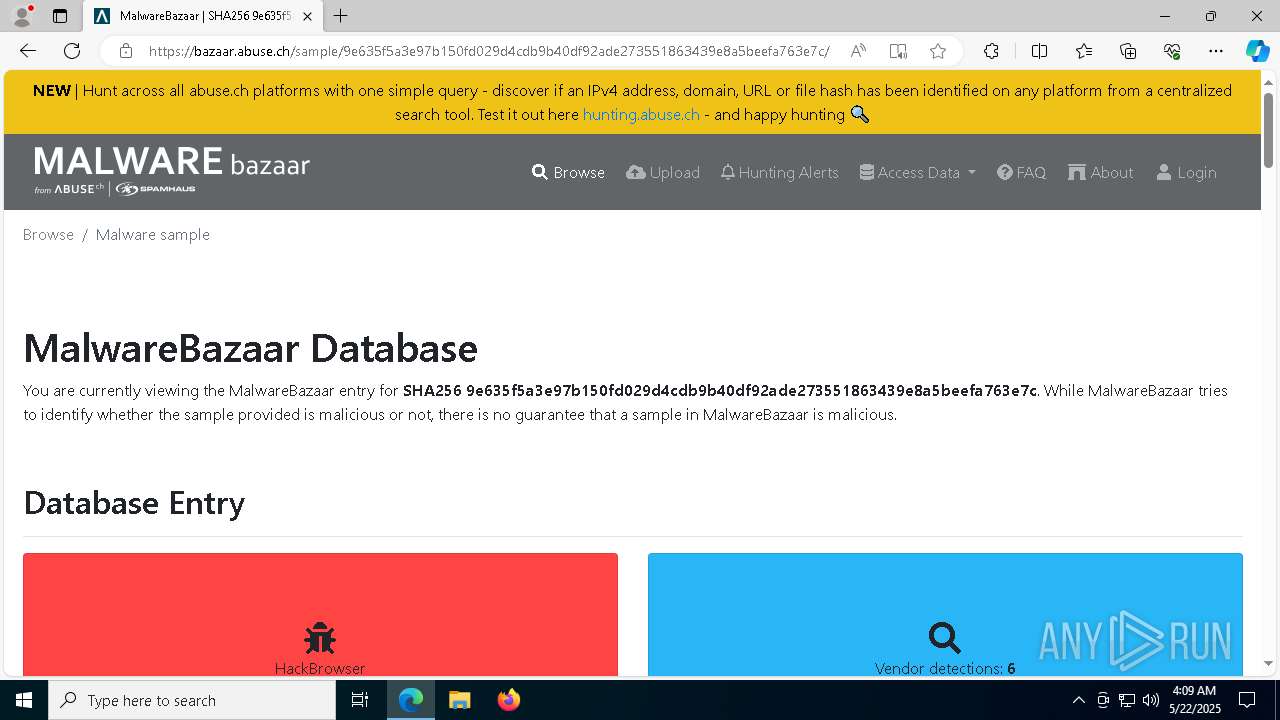
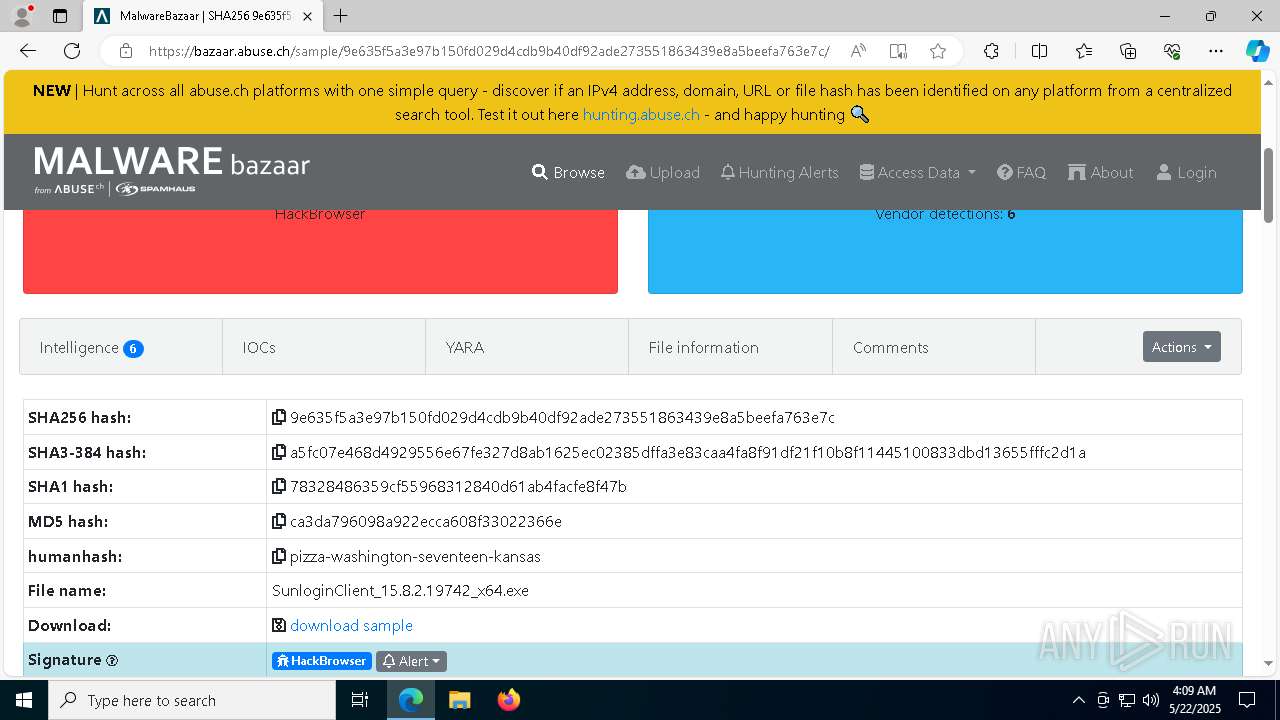
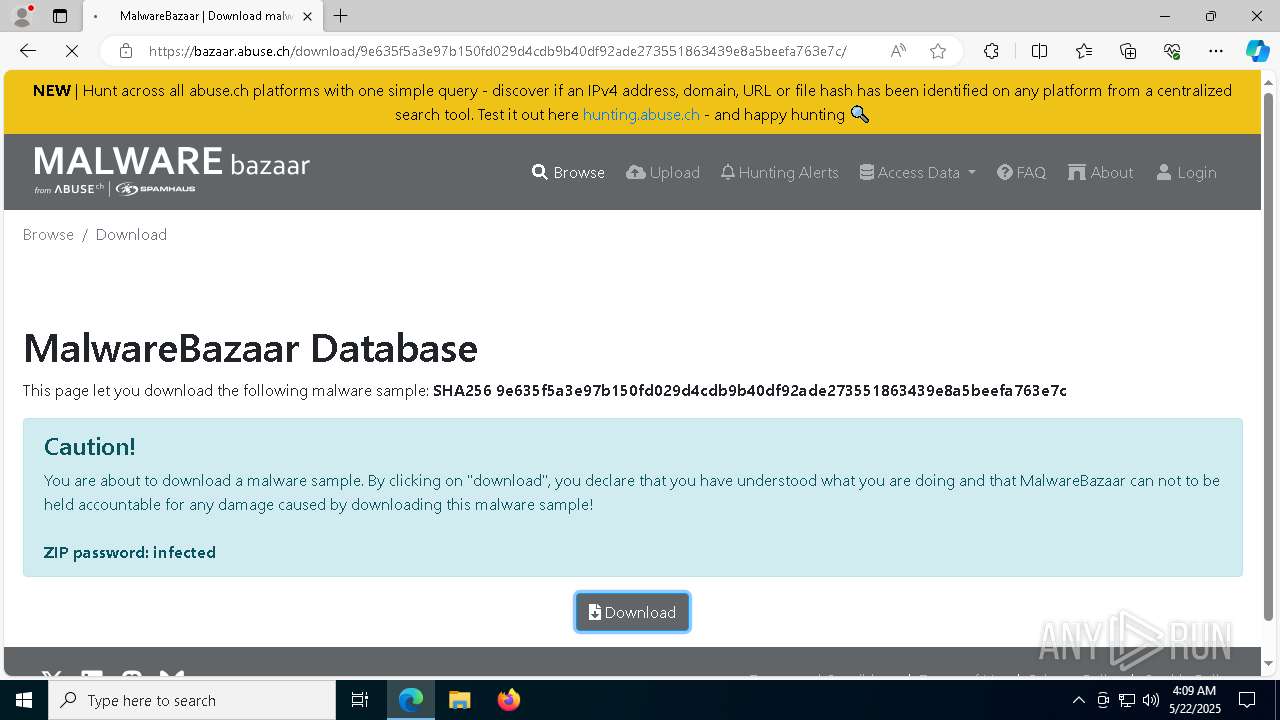
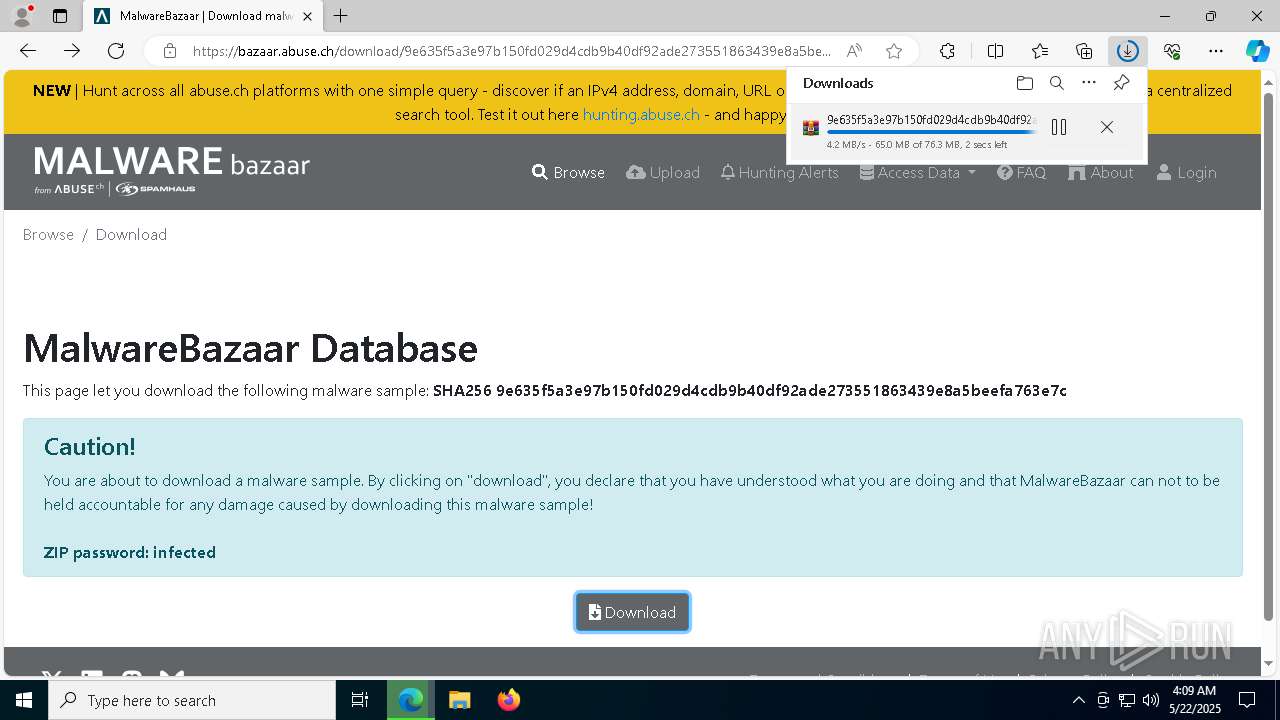
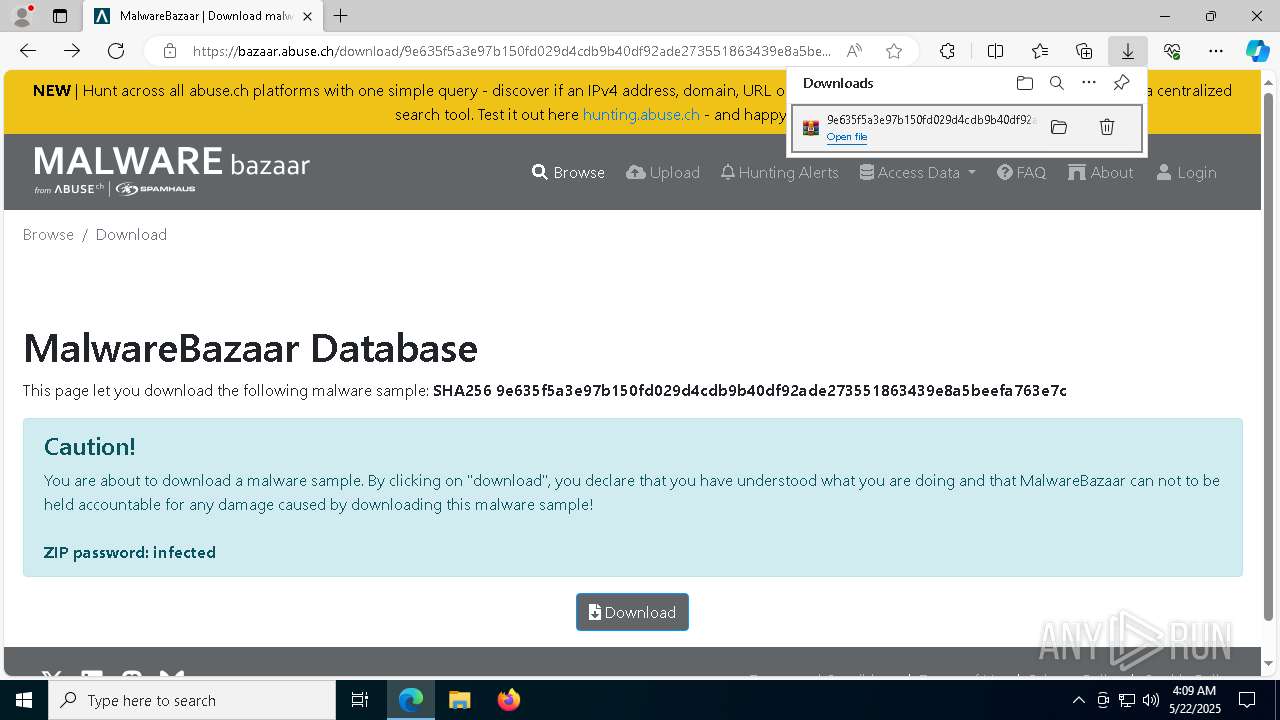
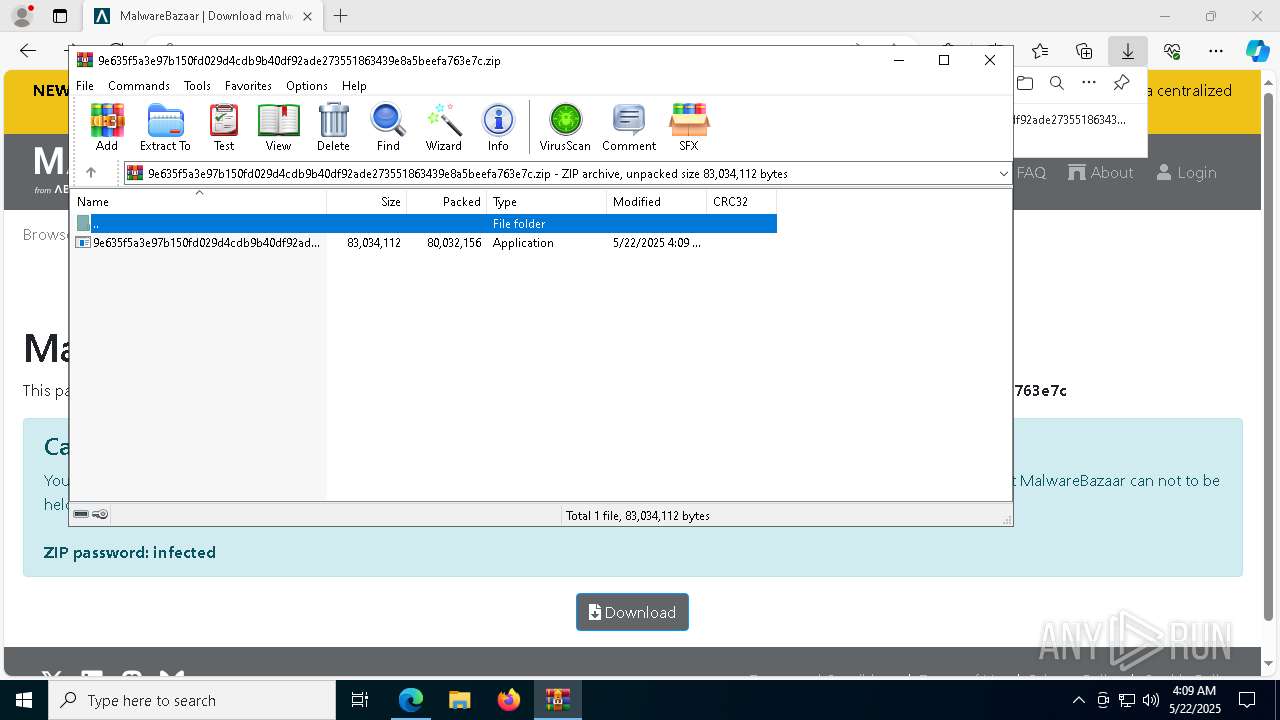
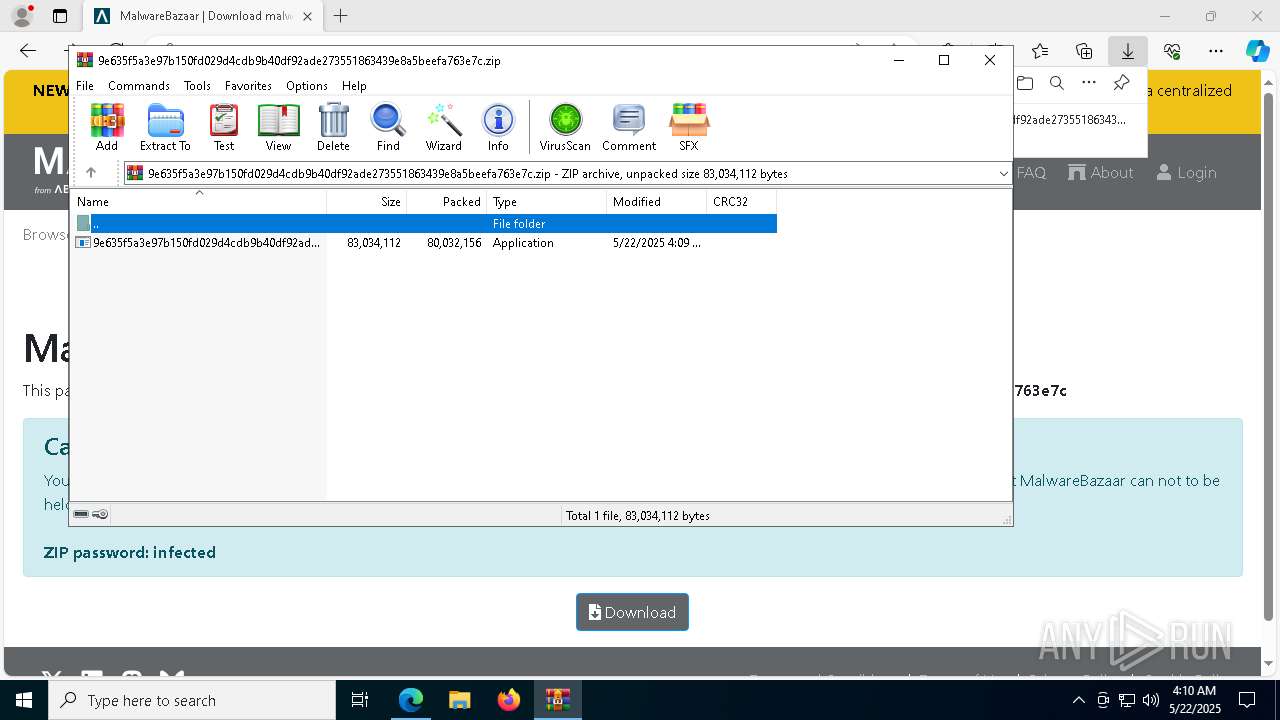
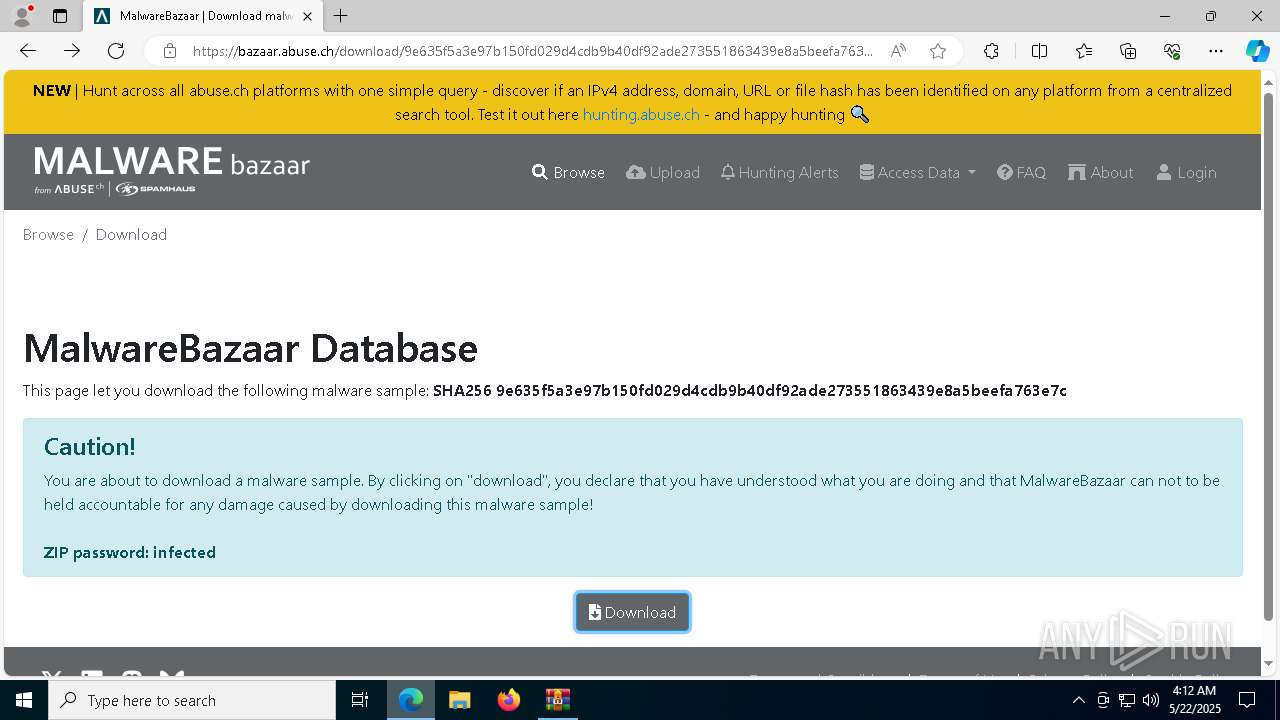
| URL: | https://bazaar.abuse.ch/sample/9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c/ |
| Full analysis: | https://app.any.run/tasks/2df5124d-bbf8-4367-9077-f9f072748fde |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 04:08:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E876C0A291DEC873C848AE5DD61FDE21 |
| SHA1: | 70E73E35EA9BD05A26865133F11E786DC4B936FE |
| SHA256: | 363BD43864D2DF92EB8CE1FFE59E94398C80303C44AF53E7791B50DB36703666 |
| SSDEEP: | 3:N8N0uDWWncaBVJ5dCXBdaSZlZK:23eKVJ5dCxdaS/0 |
MALICIOUS
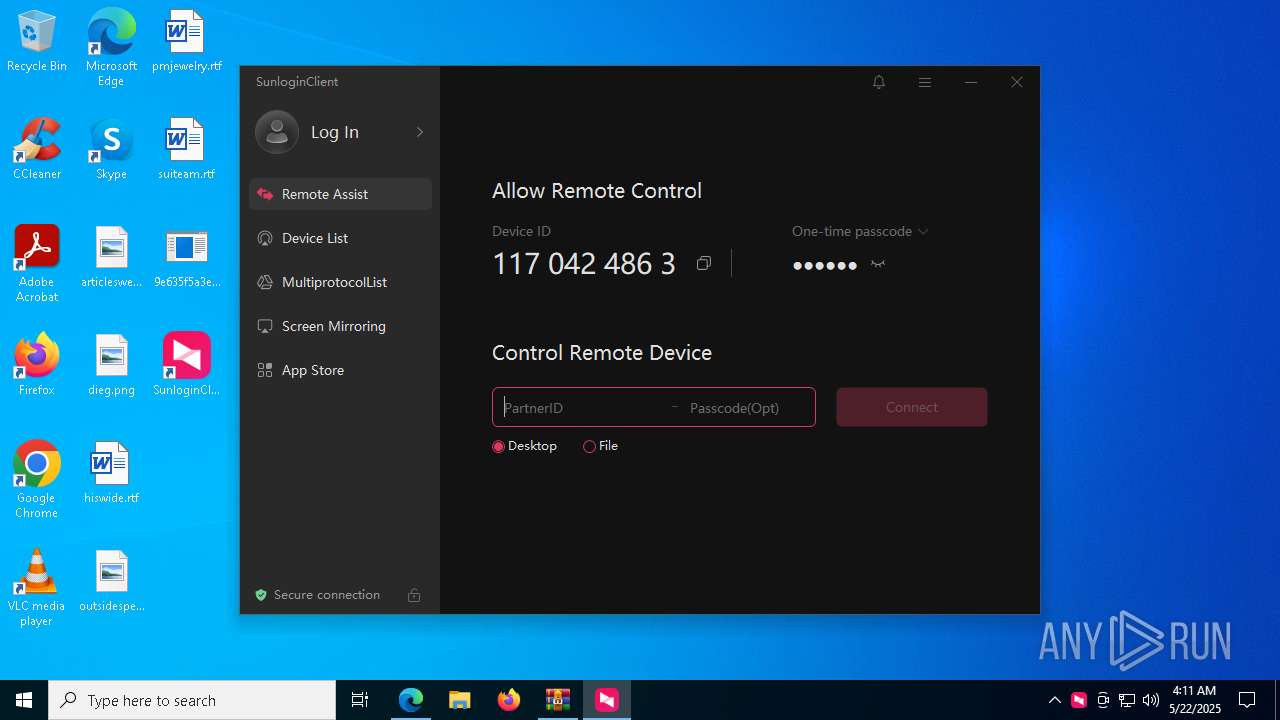
Changes the autorun value in the registry
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
SUSPICIOUS
Reads the date of Windows installation
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
Application launched itself
- SunloginClient_15.8.2.19742_x64.exe (PID: 7144)
- wuying_helper.exe (PID: 920)
- wuying_helper.exe (PID: 4428)
- wuying_helper.exe (PID: 7868)
- cmd.exe (PID: 3012)
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
- SunloginClient.exe (PID: 6148)
- SunloginClient.exe (PID: 5024)
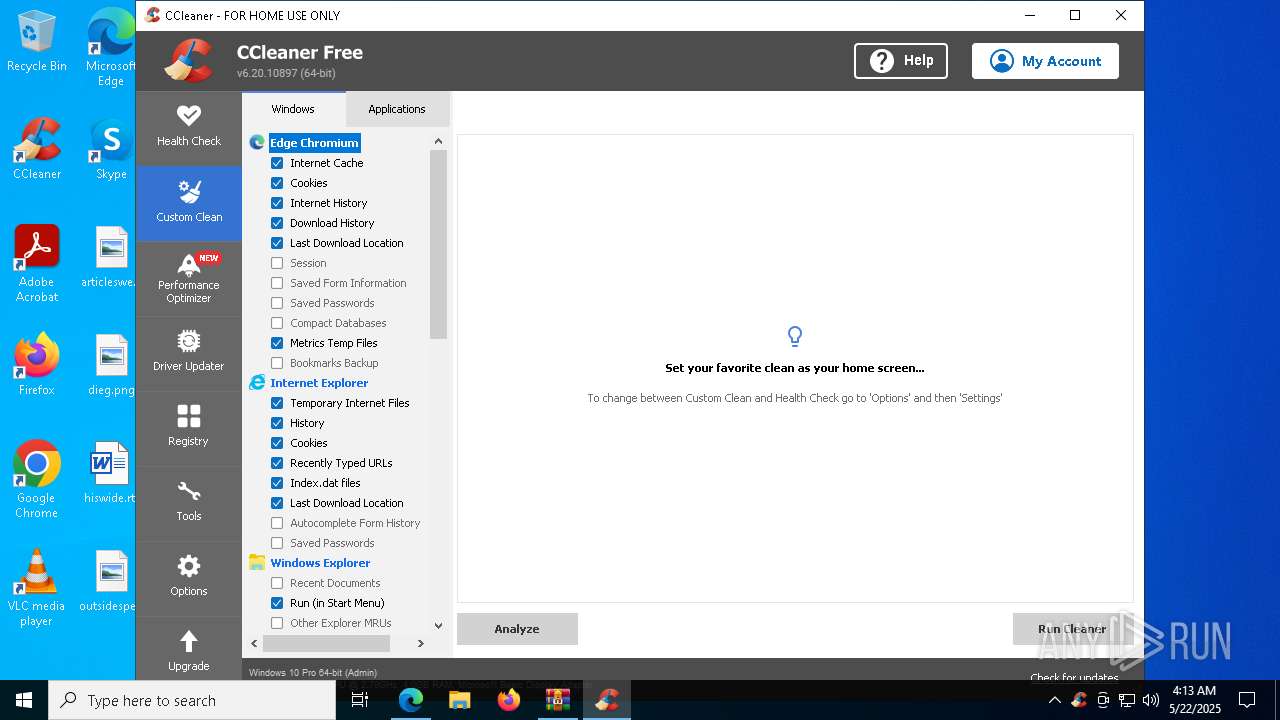
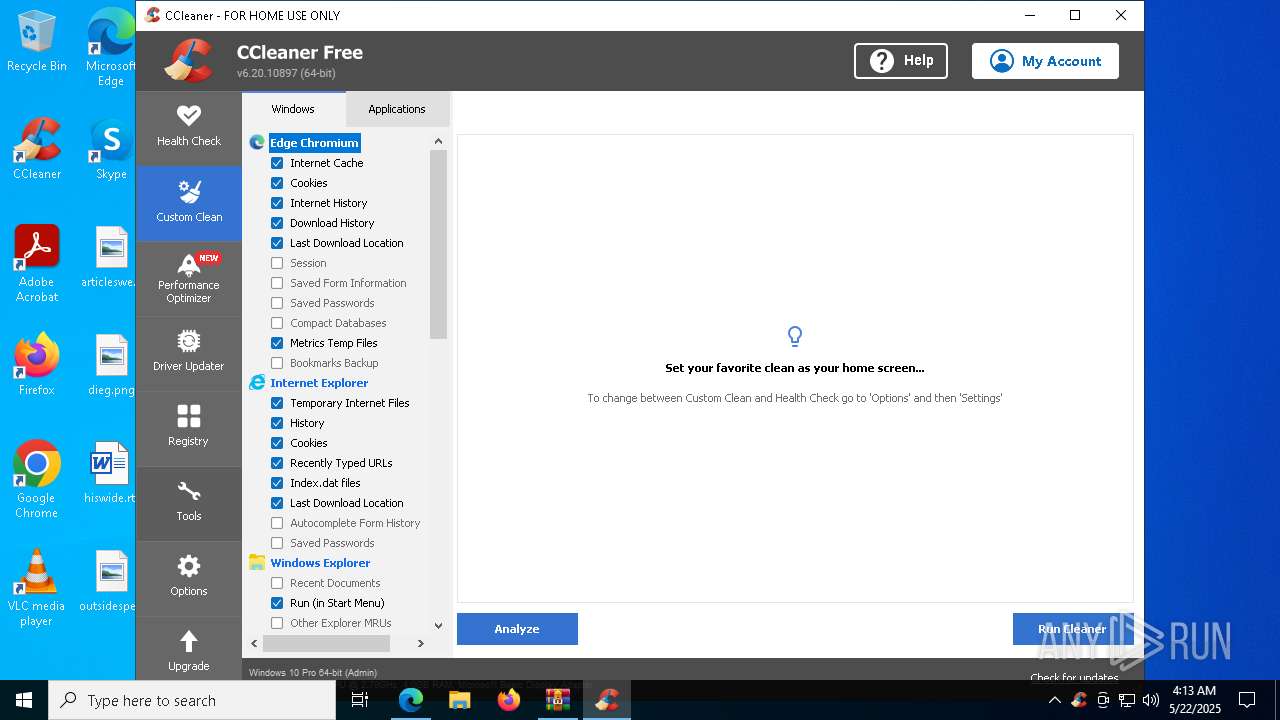
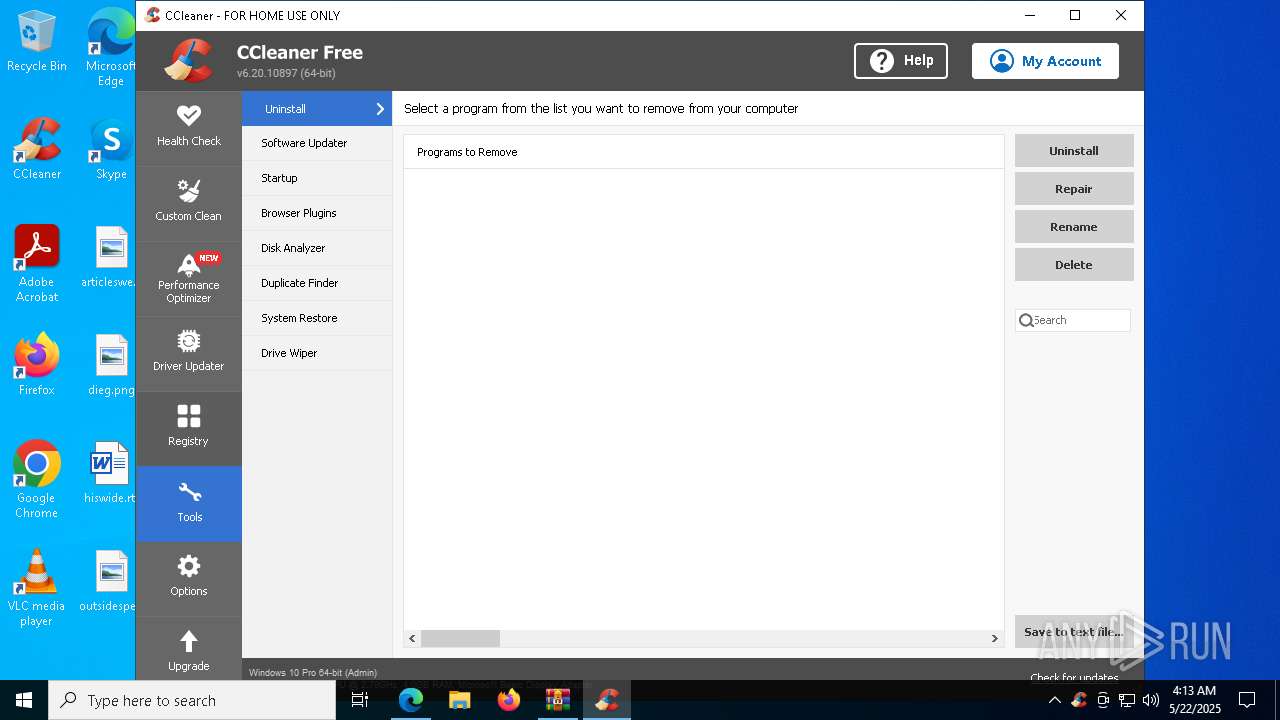
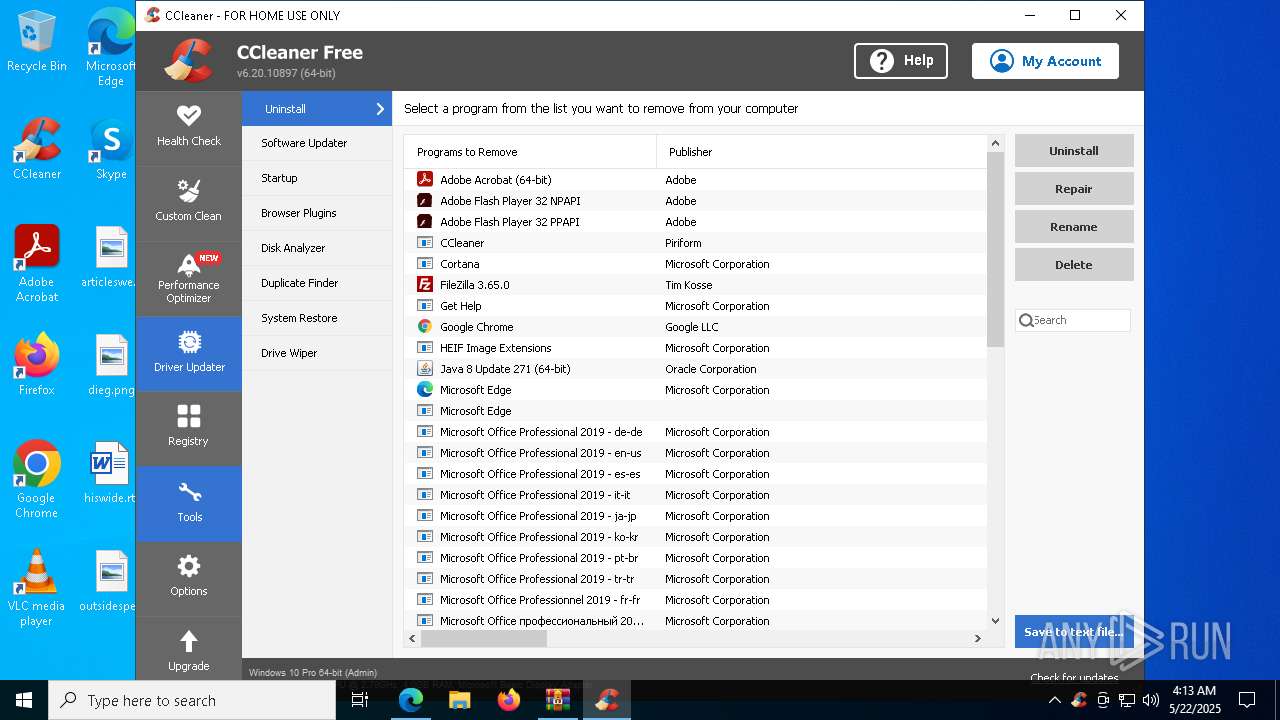
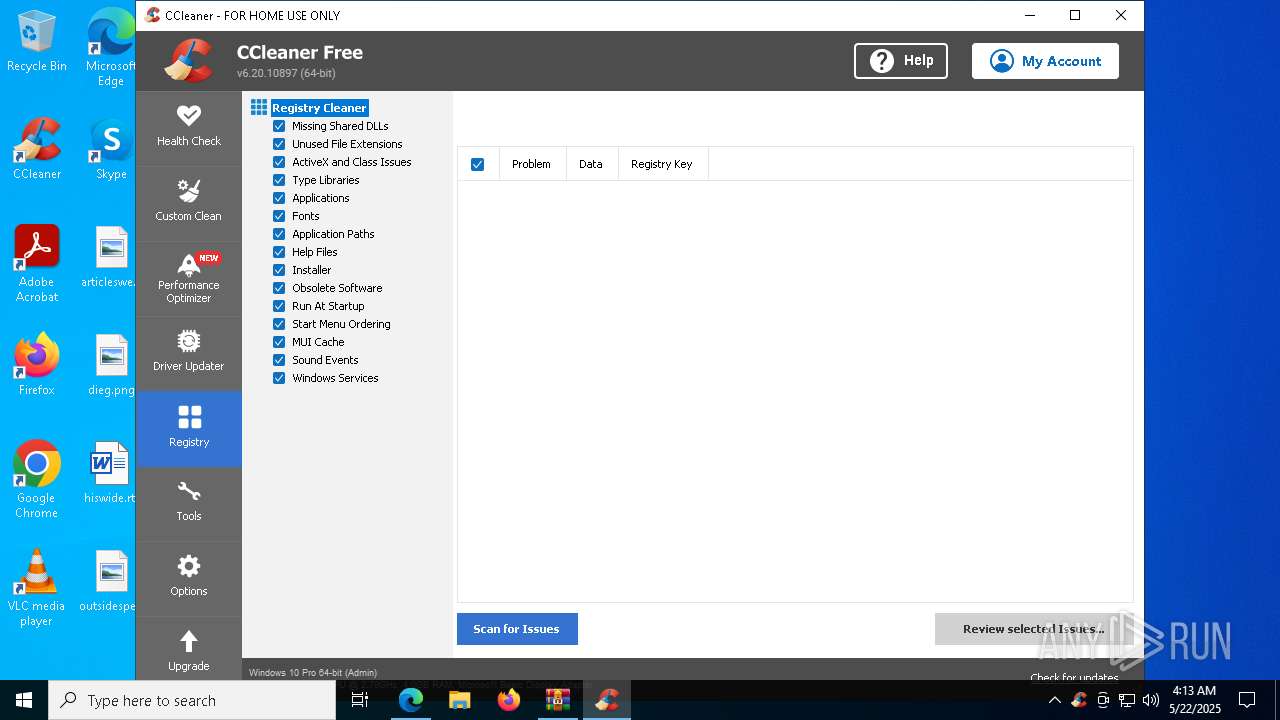
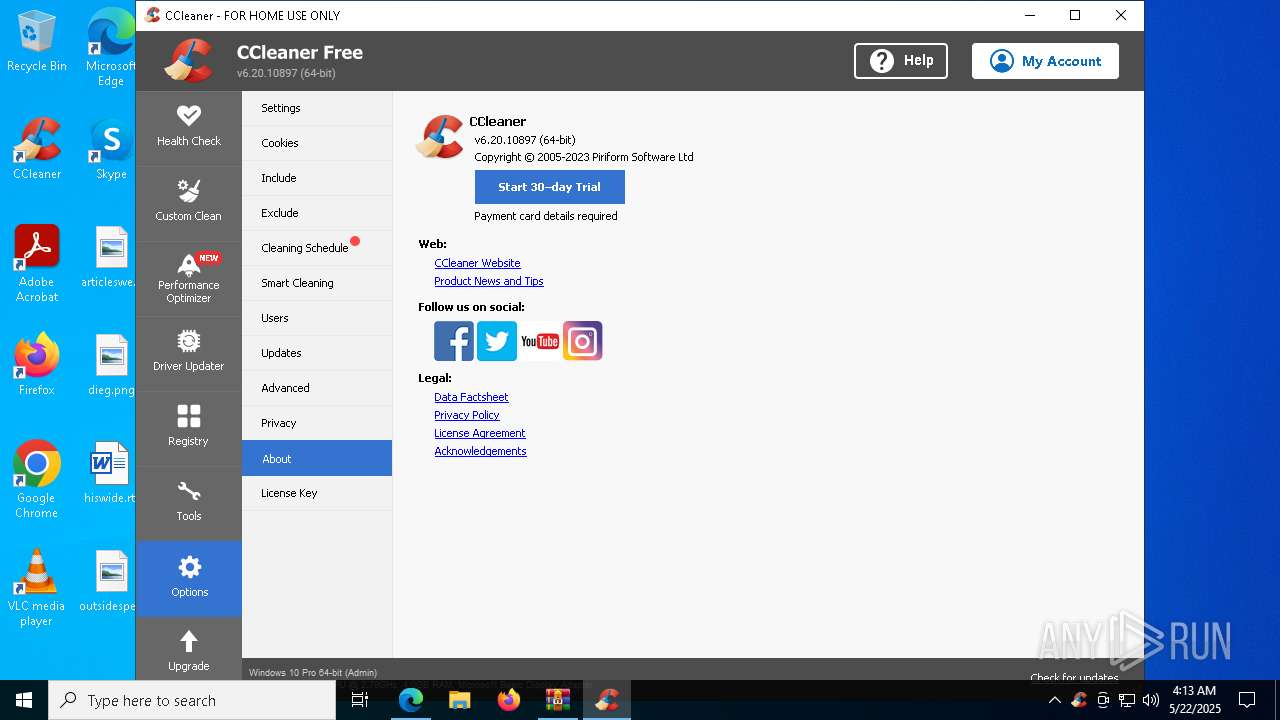
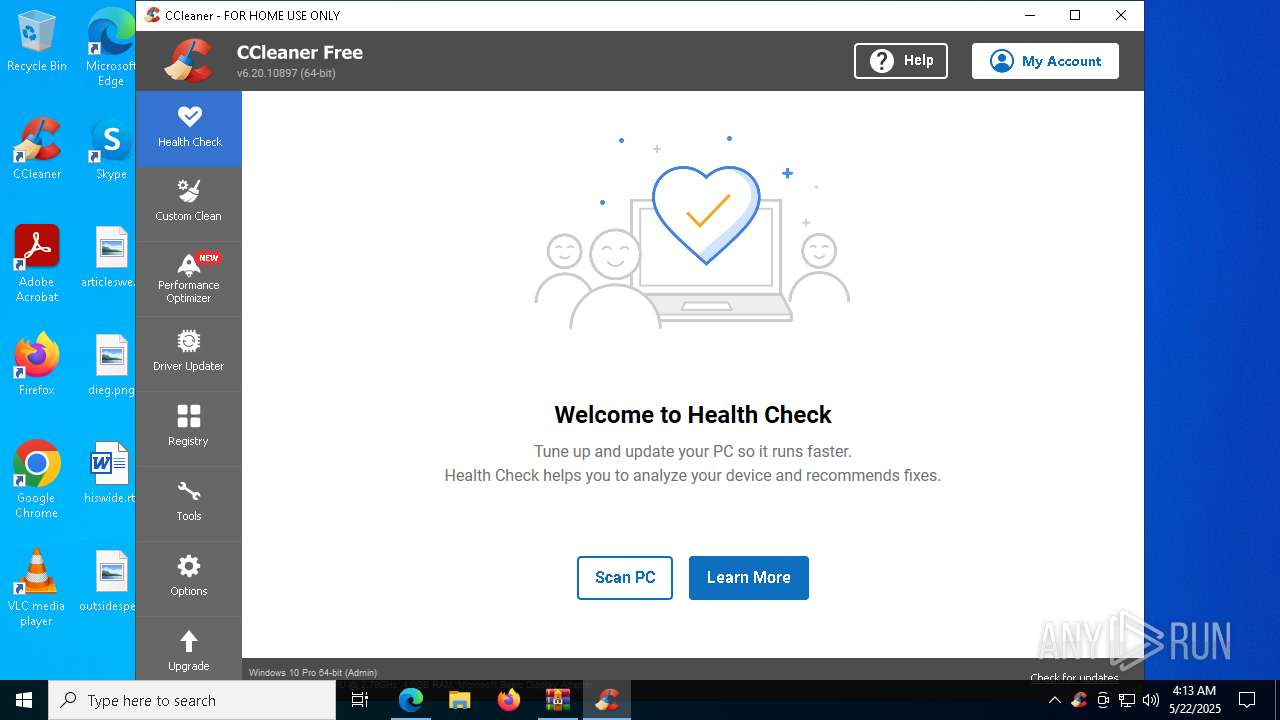
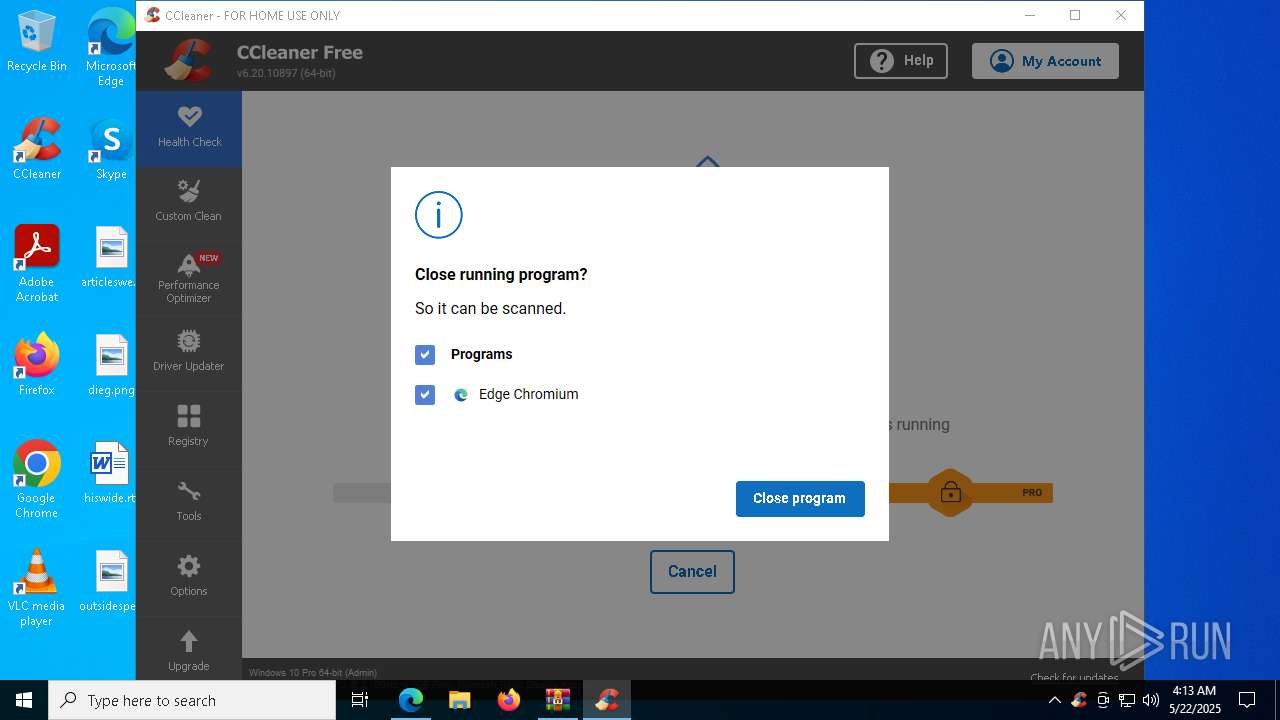
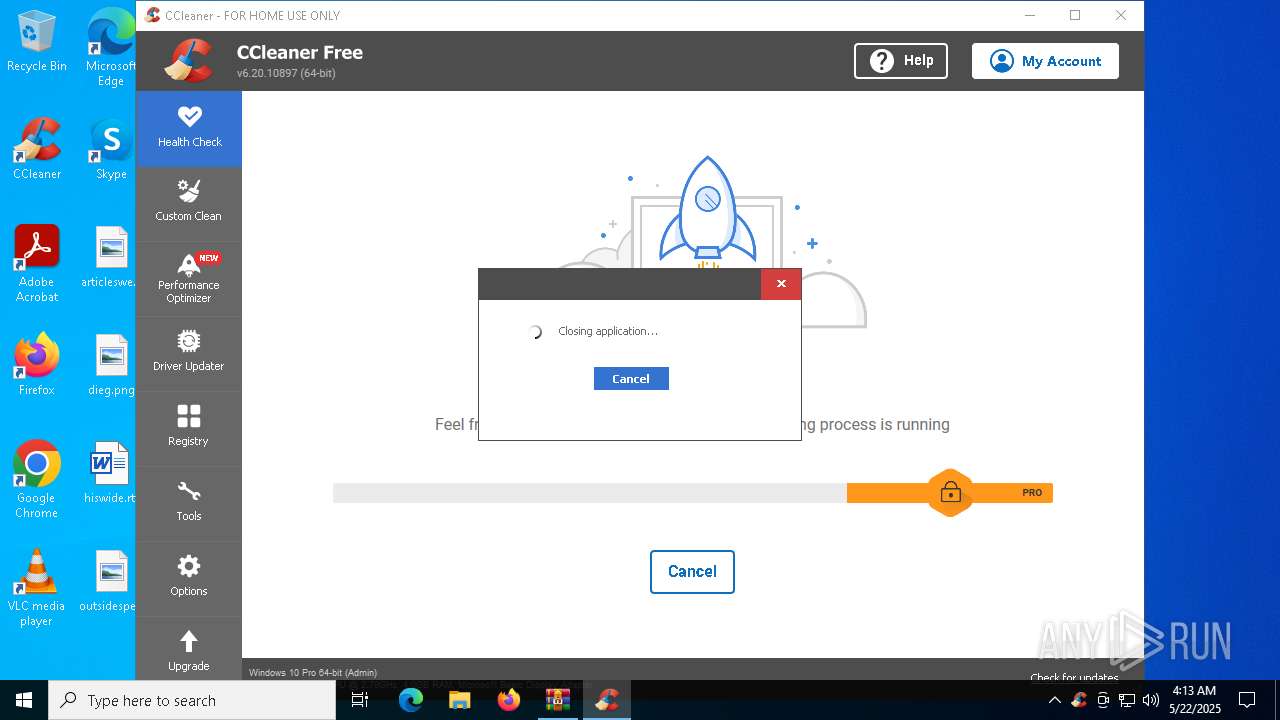
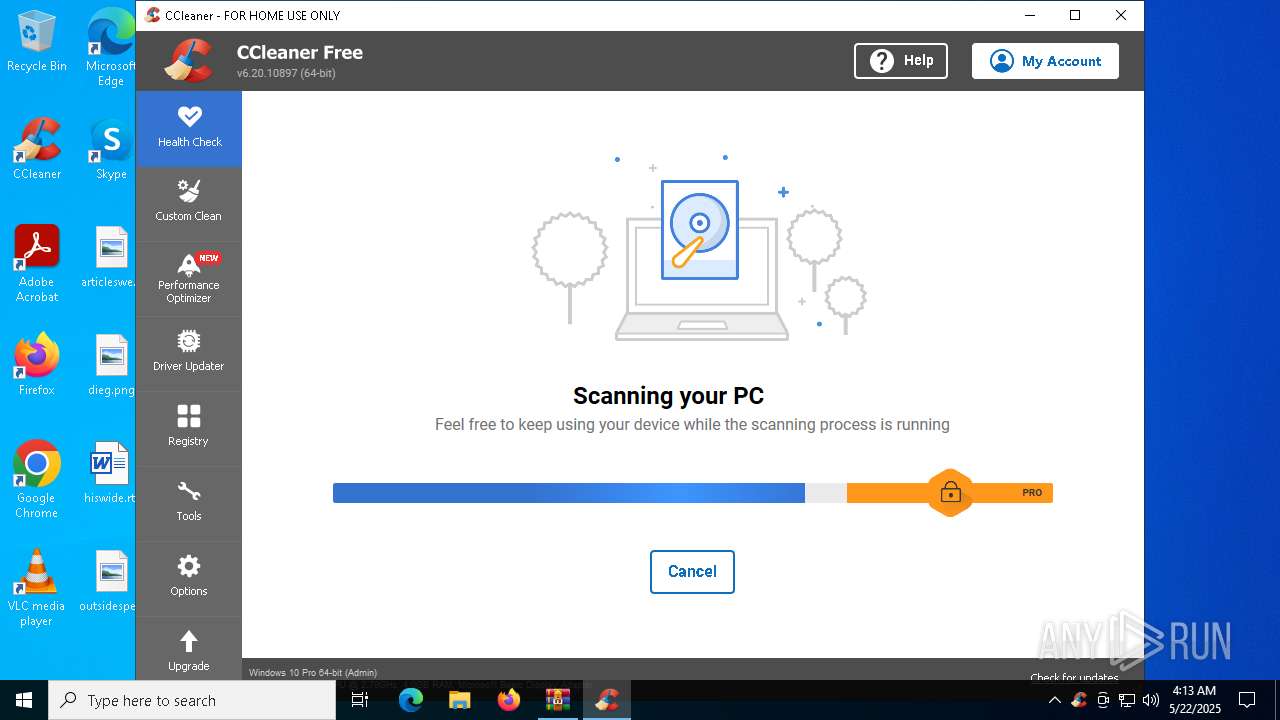
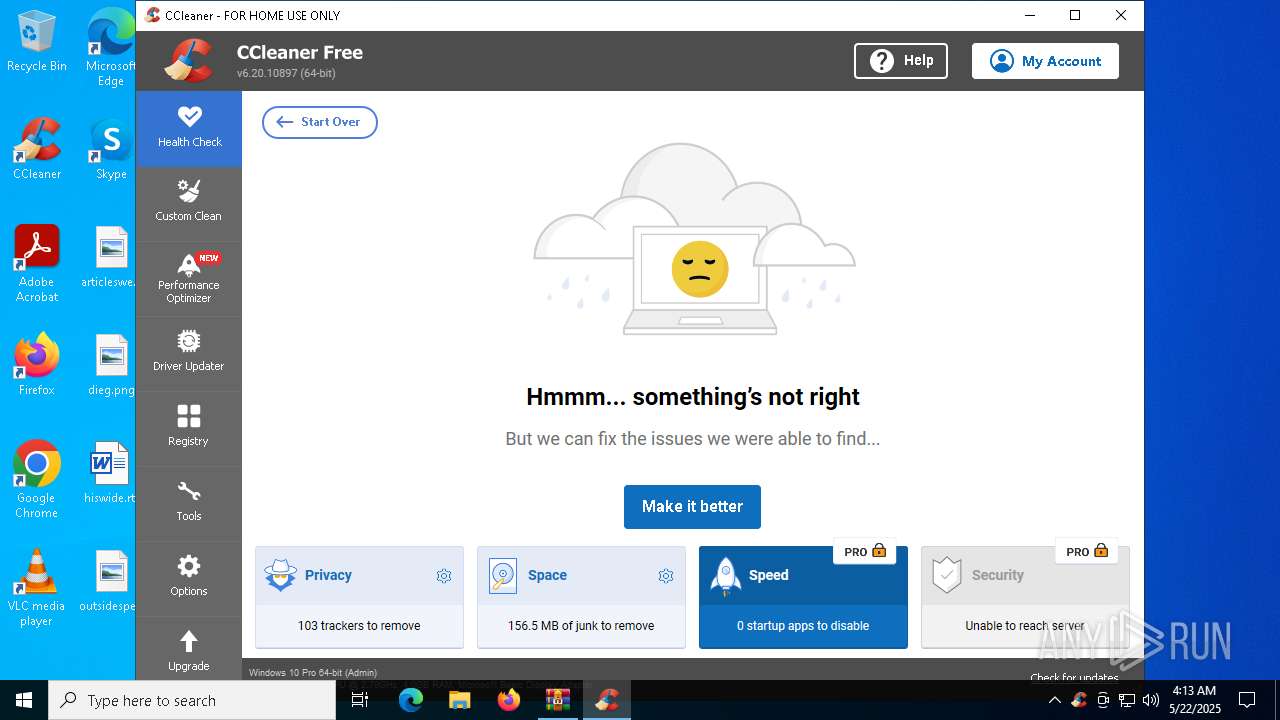
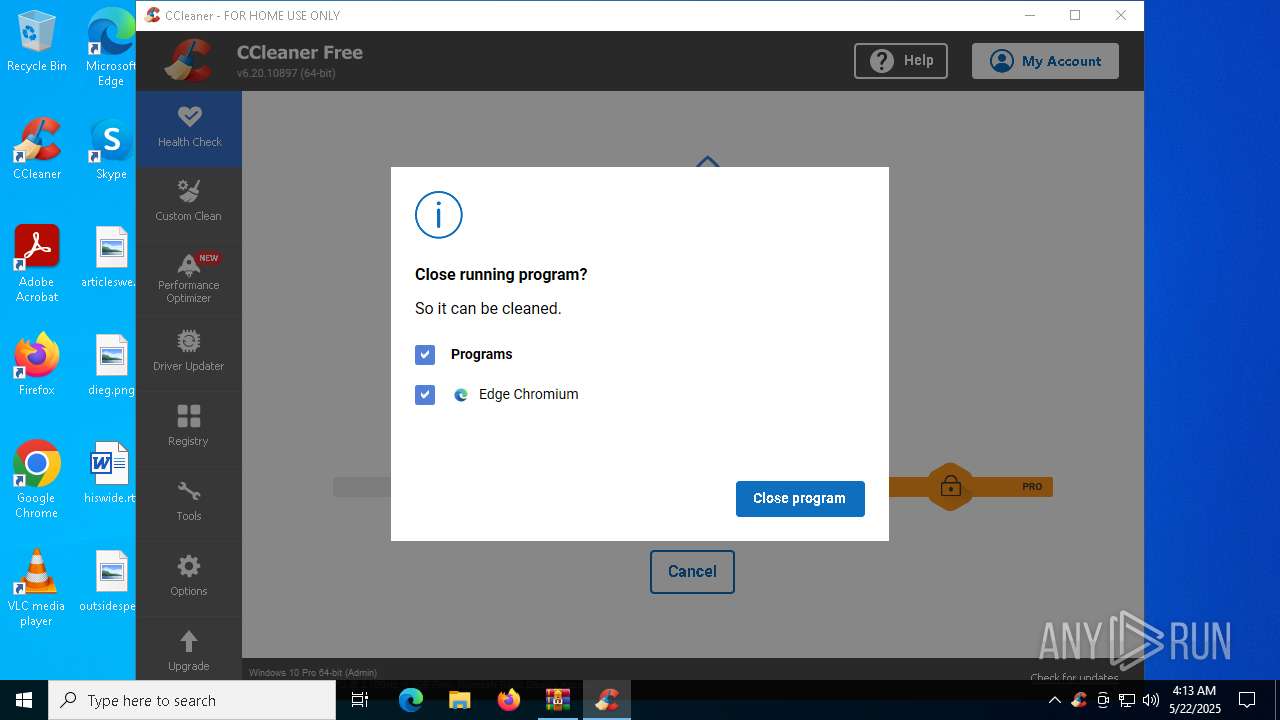
- CCleaner64.exe (PID: 8844)
- CCleaner64.exe (PID: 7784)
Process drops legitimate windows executable
- main.exe (PID: 3176)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
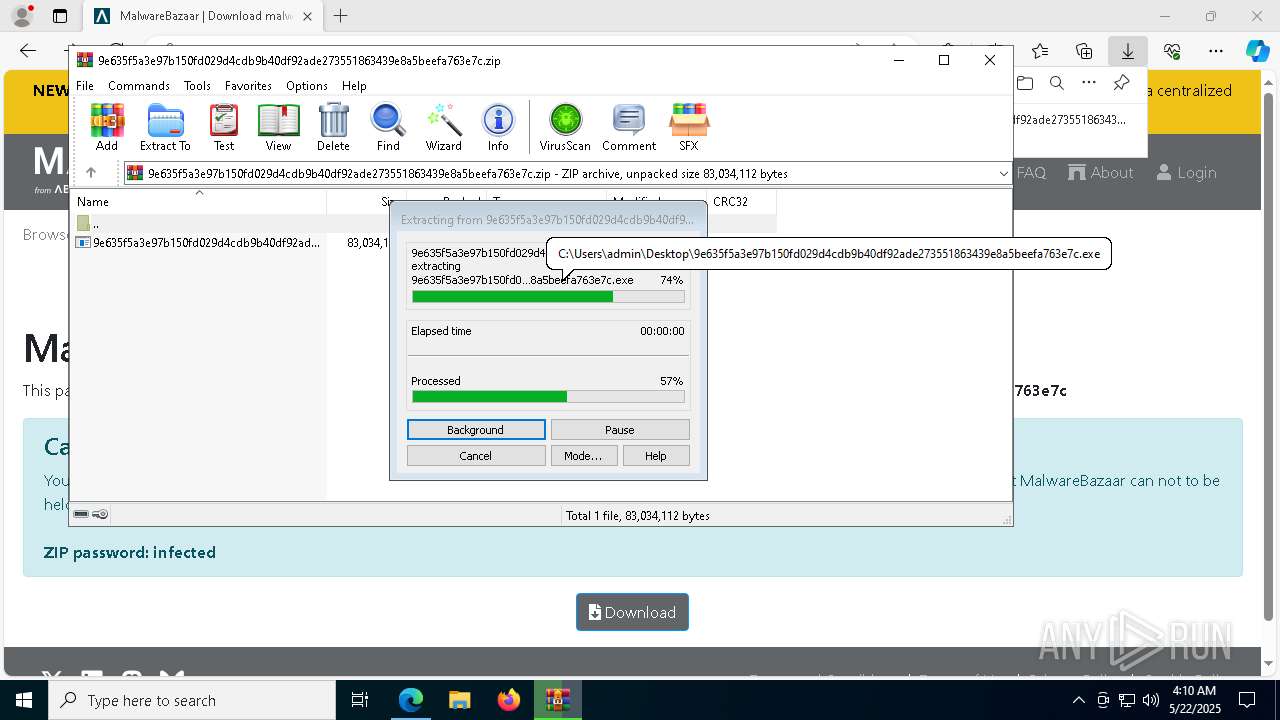
Executable content was dropped or overwritten
- main.exe (PID: 3176)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 3032)
- devcon.exe (PID: 4336)
- drvinst.exe (PID: 7020)
- devcon.exe (PID: 6480)
- drvinst.exe (PID: 3396)
- SunloginClient.exe (PID: 1804)
- drvinst.exe (PID: 7332)
- drvinst.exe (PID: 4488)
- SunloginClient.exe (PID: 6148)
- CCleaner64.exe (PID: 4628)
- CCleaner64.exe (PID: 8844)
The process drops C-runtime libraries
- main.exe (PID: 3176)
Drops a system driver (possible attempt to evade defenses)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- devcon.exe (PID: 6480)
- SunloginClient.exe (PID: 1804)
- drvinst.exe (PID: 3396)
- drvinst.exe (PID: 4488)
- drvinst.exe (PID: 7332)
The process executes via Task Scheduler
- wuying_helper.exe (PID: 4428)
Starts itself from another location
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
The process creates files with name similar to system file names
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
There is functionality for taking screenshot (YARA)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
Starts CMD.EXE for commands execution
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- cmd.exe (PID: 3012)
Executing commands from a ".bat" file
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 8020)
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 8156)
- cmd.exe (PID: 8016)
Connects to unusual port
- wuying_helper.exe (PID: 5044)
- wuying_helper.exe (PID: 7764)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3272)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 4028)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 6068)
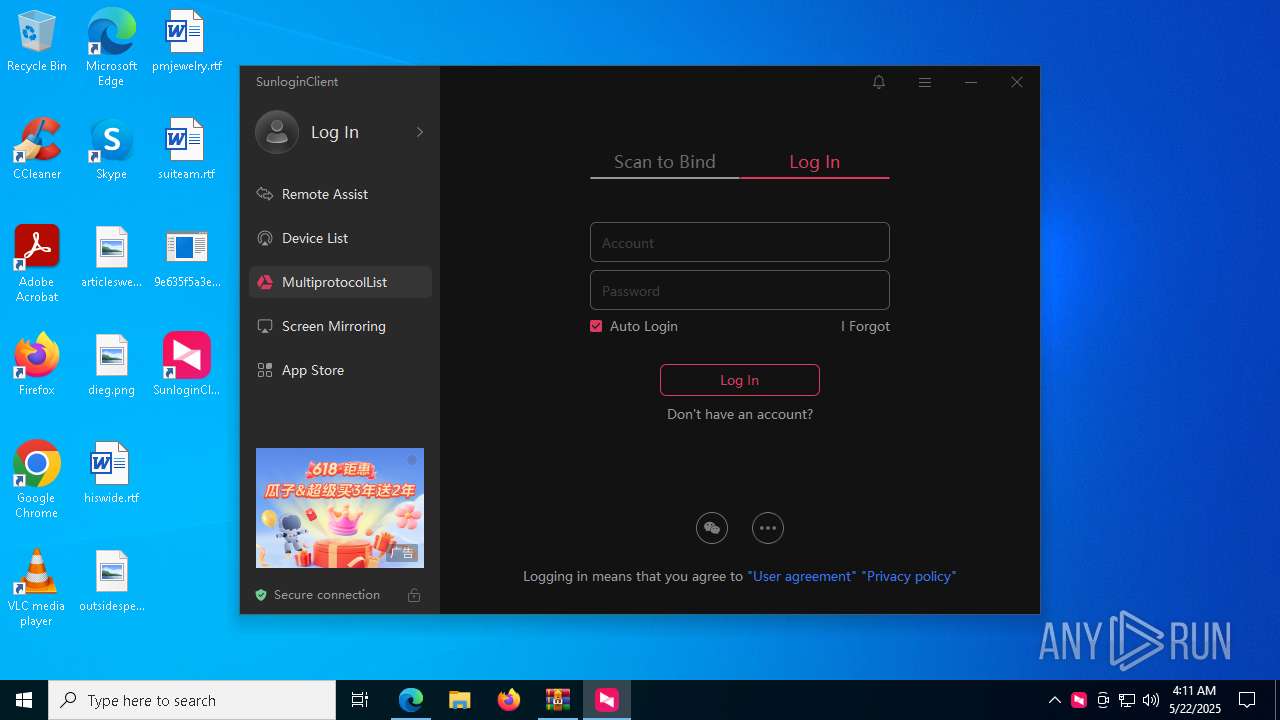
Executes as Windows Service
- WUDFHost.exe (PID: 6048)
- SunloginClient.exe (PID: 6148)
Uses TASKKILL.EXE to kill process
- SunloginClient.exe (PID: 5024)
Process uses ARP to discover network configuration
- SunloginClient.exe (PID: 5024)
Checks for external IP
- svchost.exe (PID: 2196)
- CCleaner64.exe (PID: 8844)
- SunloginClient.exe (PID: 5024)
INFO
Application launched itself
- msedge.exe (PID: 4400)
- msedge.exe (PID: 8380)
Reads the computer name
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7144)
- main.exe (PID: 3176)
- identity_helper.exe (PID: 4736)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- wuying_helper.exe (PID: 7868)
- SunloginClient.exe (PID: 5796)
- wuying_helper.exe (PID: 7764)
- wuying_helper.exe (PID: 5044)
- ShellExperienceHost.exe (PID: 8020)
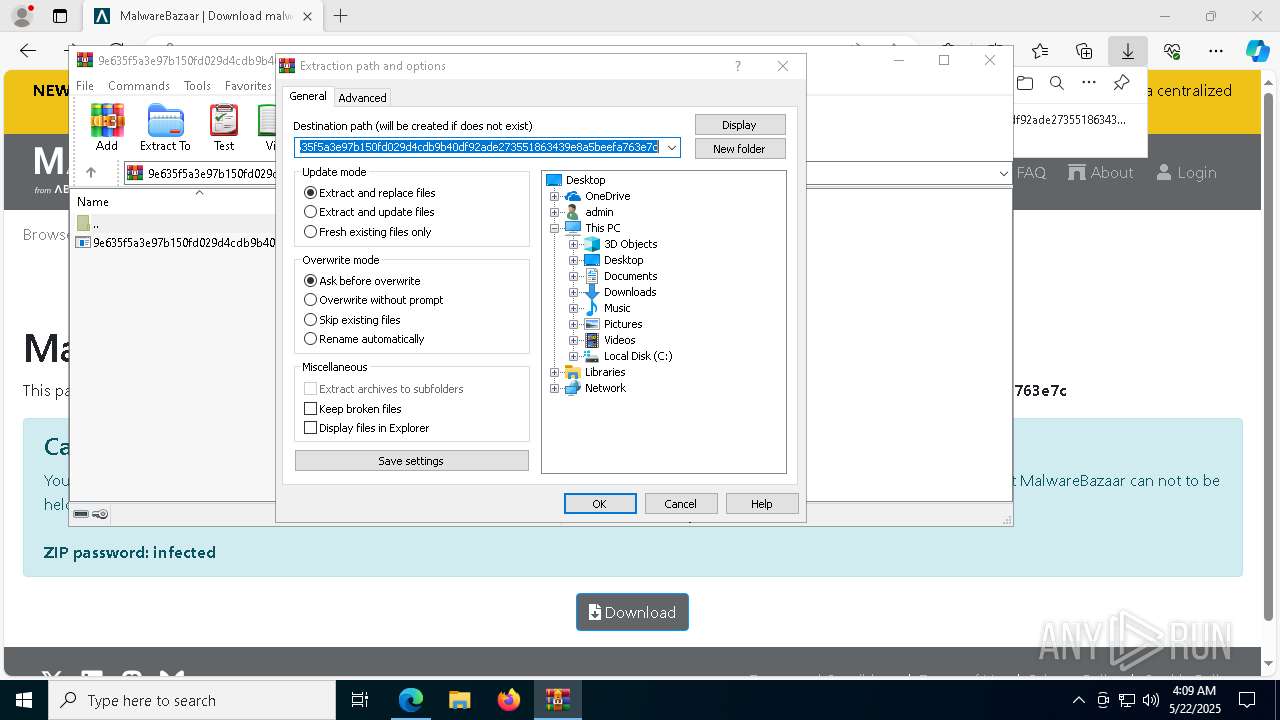
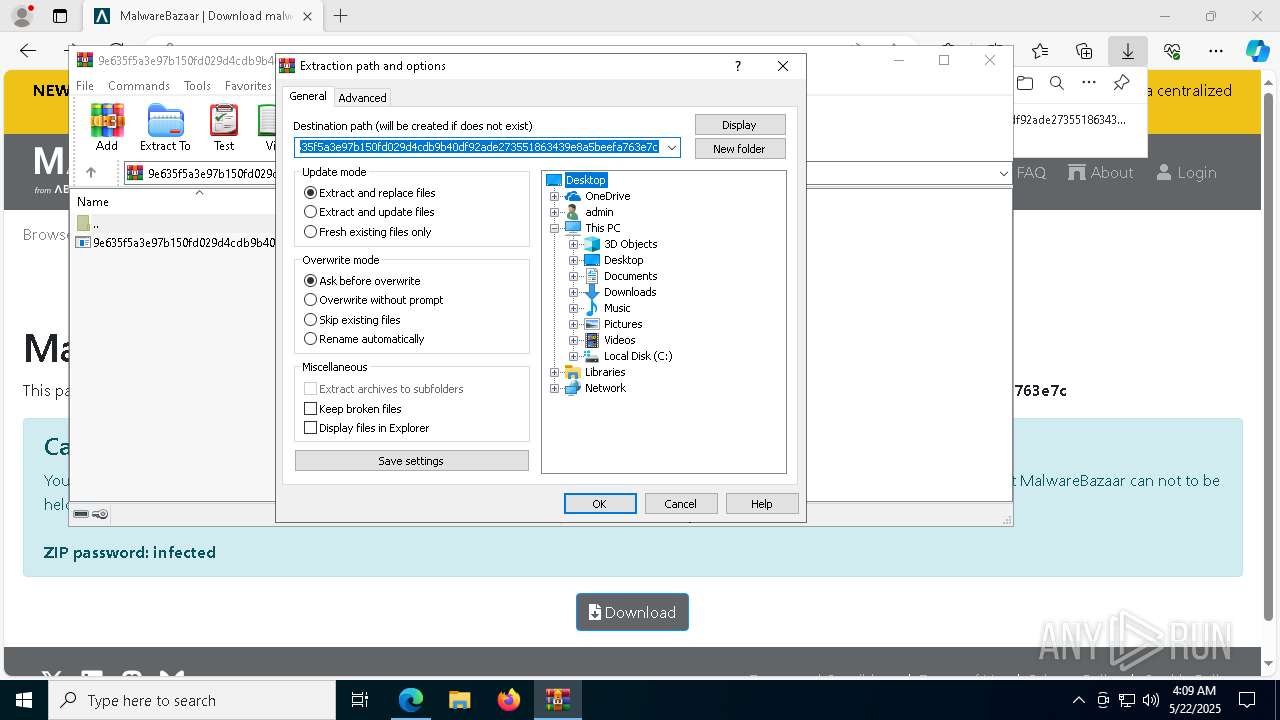
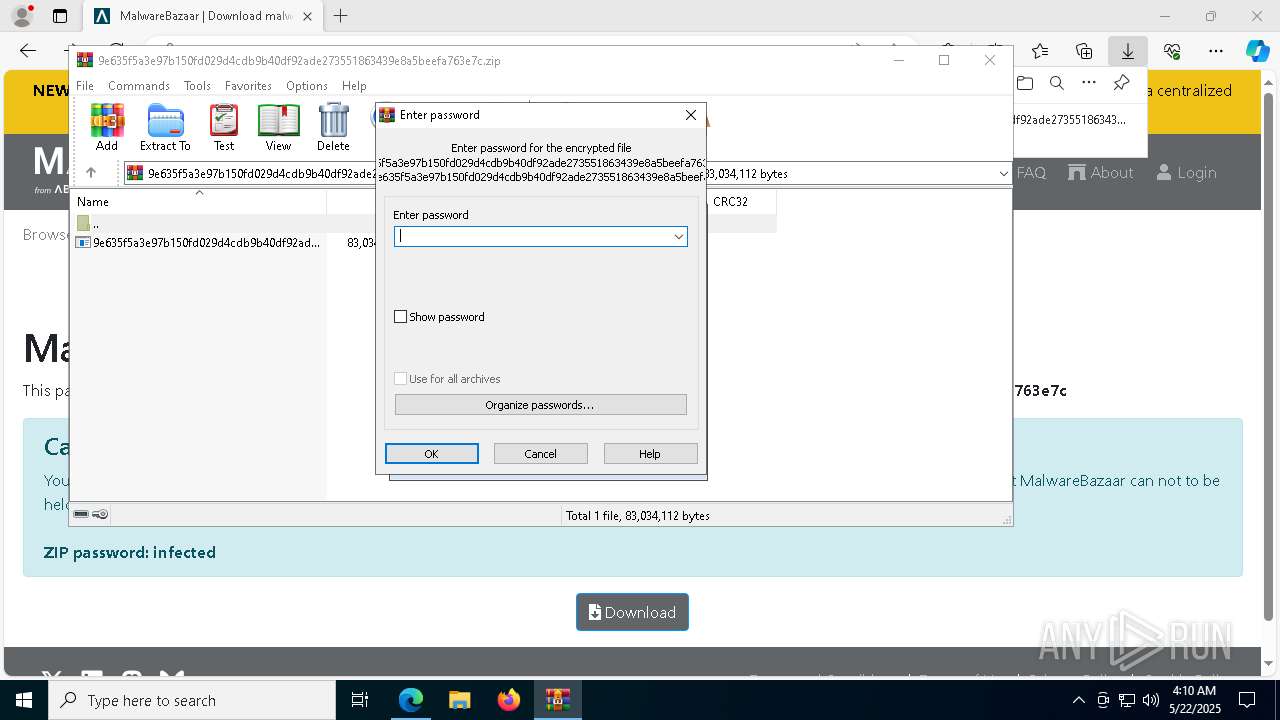
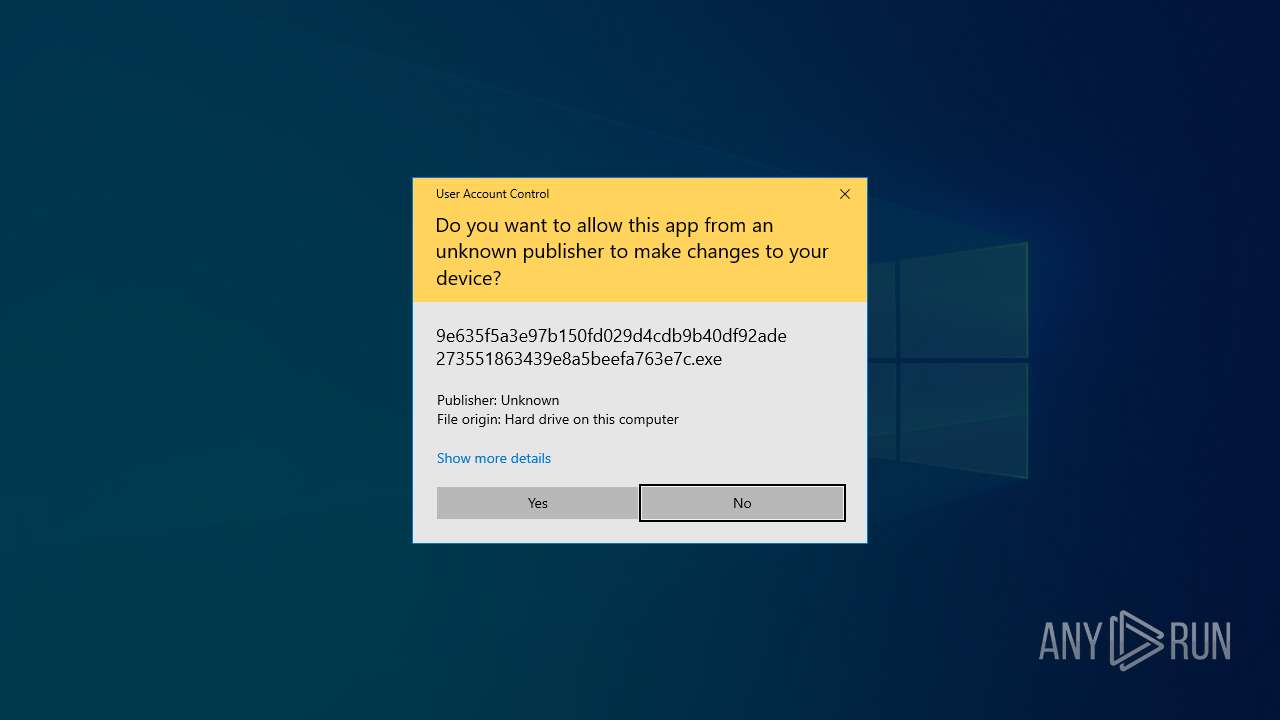
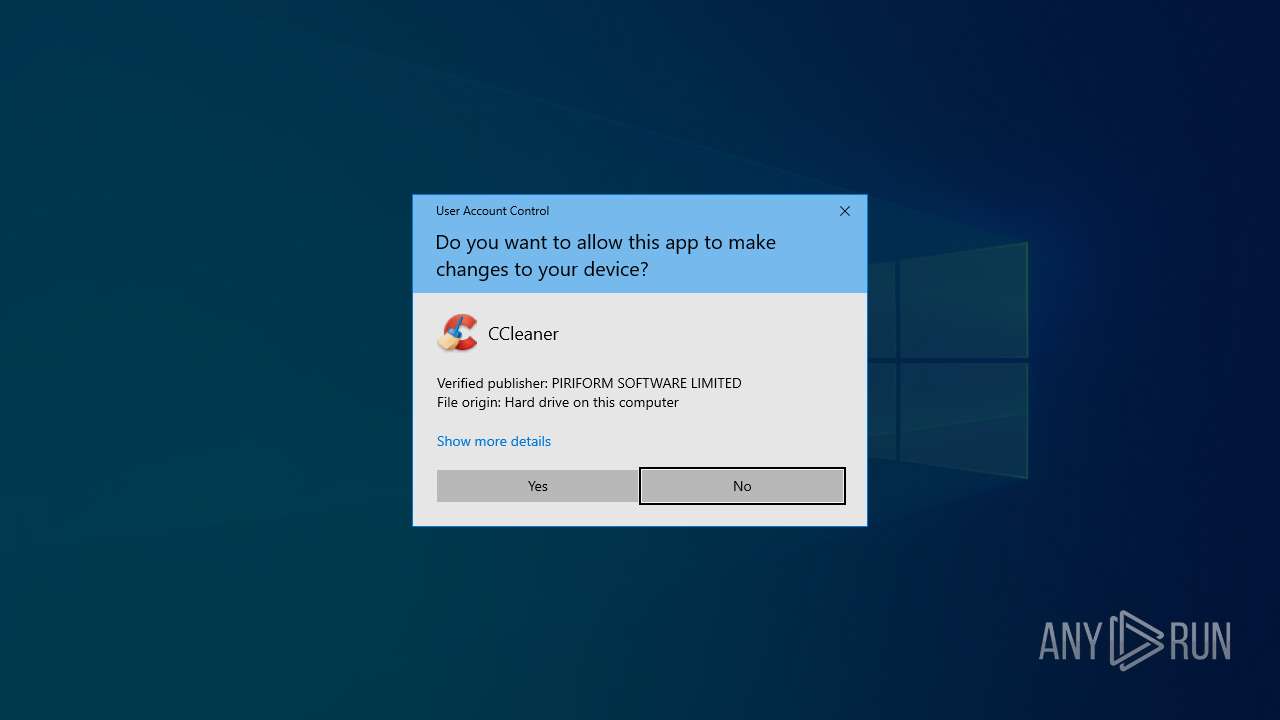
Manual execution by a user
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
- CCleaner64.exe (PID: 7784)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4400)
Checks supported languages
- identity_helper.exe (PID: 4736)
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7144)
- wuying_helper.exe (PID: 7868)
- wuying_helper.exe (PID: 4428)
- wuying_helper.exe (PID: 920)
- wuying_helper.exe (PID: 7764)
- wuying_helper.exe (PID: 5044)
- SunloginClient.exe (PID: 5796)
- ShellExperienceHost.exe (PID: 8020)
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 3032)
- main.exe (PID: 3176)
Application based on Golang
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 3032)
- wuying_helper.exe (PID: 920)
- wuying_helper.exe (PID: 4428)
Reads the software policy settings
- slui.exe (PID: 7700)
Reads Environment values
- identity_helper.exe (PID: 4736)
Process checks computer location settings
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 4892)
Create files in a temporary directory
- SunloginClient_15.8.2.19742_x64.exe (PID: 7144)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- main.exe (PID: 3176)
- SunloginClient.exe (PID: 5796)
- wuying_helper.exe (PID: 5044)
- 9e635f5a3e97b150fd029d4cdb9b40df92ade273551863439e8a5beefa763e7c.exe (PID: 3032)
Creates files in the program directory
- SunloginClient_15.8.2.19742_x64.exe (PID: 7144)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
Reads the machine GUID from the registry
- SunloginClient_15.8.2.19742_x64.exe (PID: 7144)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- SunloginClient.exe (PID: 5796)
The sample compiled with english language support
- main.exe (PID: 3176)
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- devcon.exe (PID: 4336)
- drvinst.exe (PID: 7020)
- drvinst.exe (PID: 3396)
- devcon.exe (PID: 6480)
- drvinst.exe (PID: 7332)
- SunloginClient.exe (PID: 1804)
- drvinst.exe (PID: 4488)
- CCleaner64.exe (PID: 8844)
- CCleaner64.exe (PID: 4628)
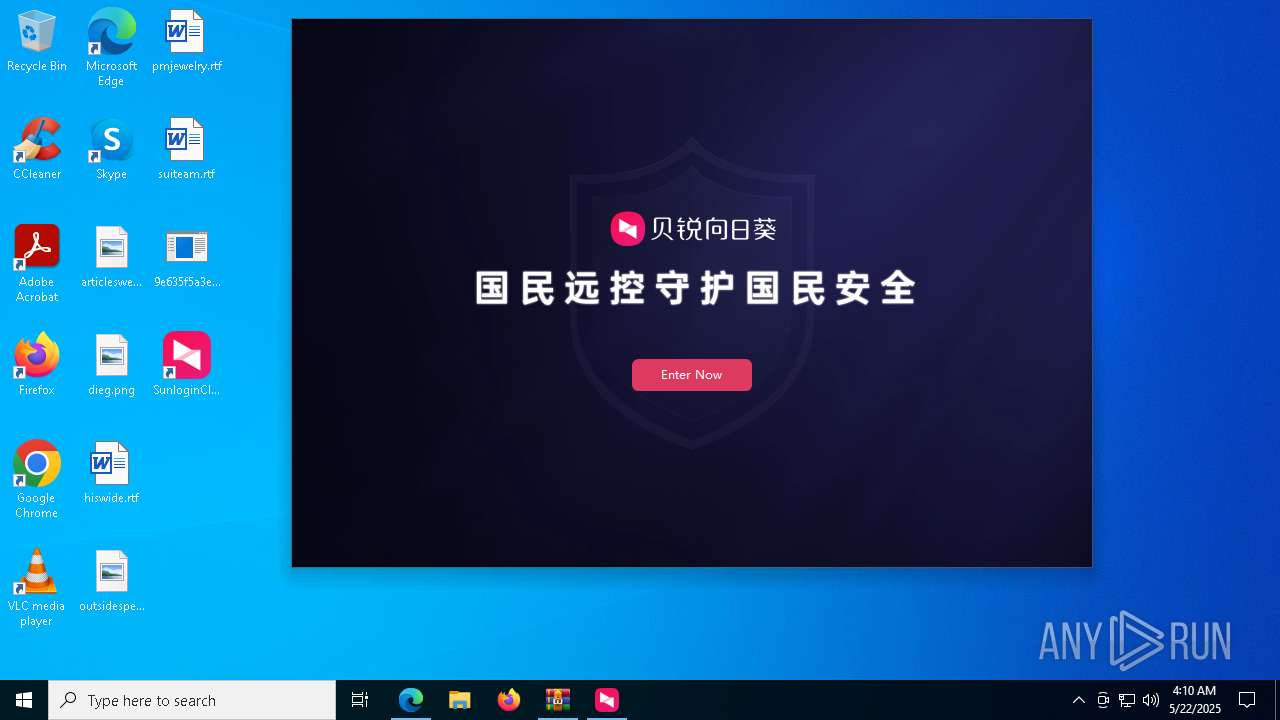
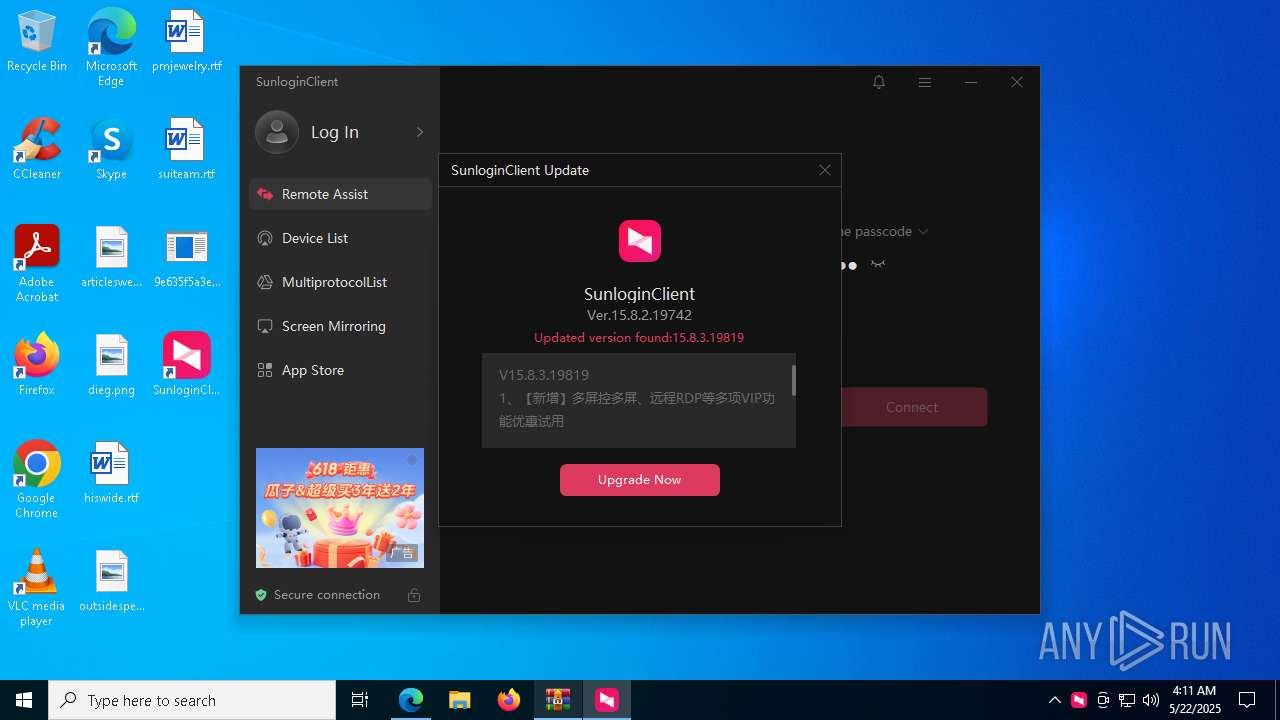
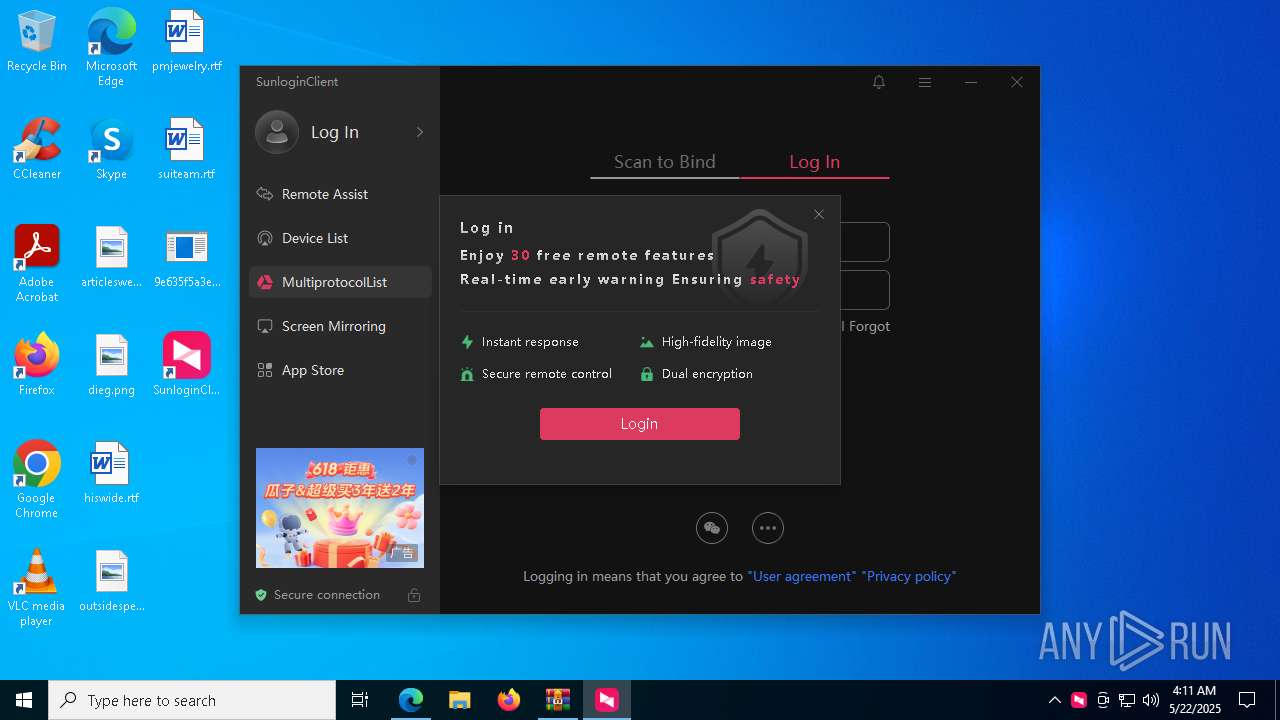
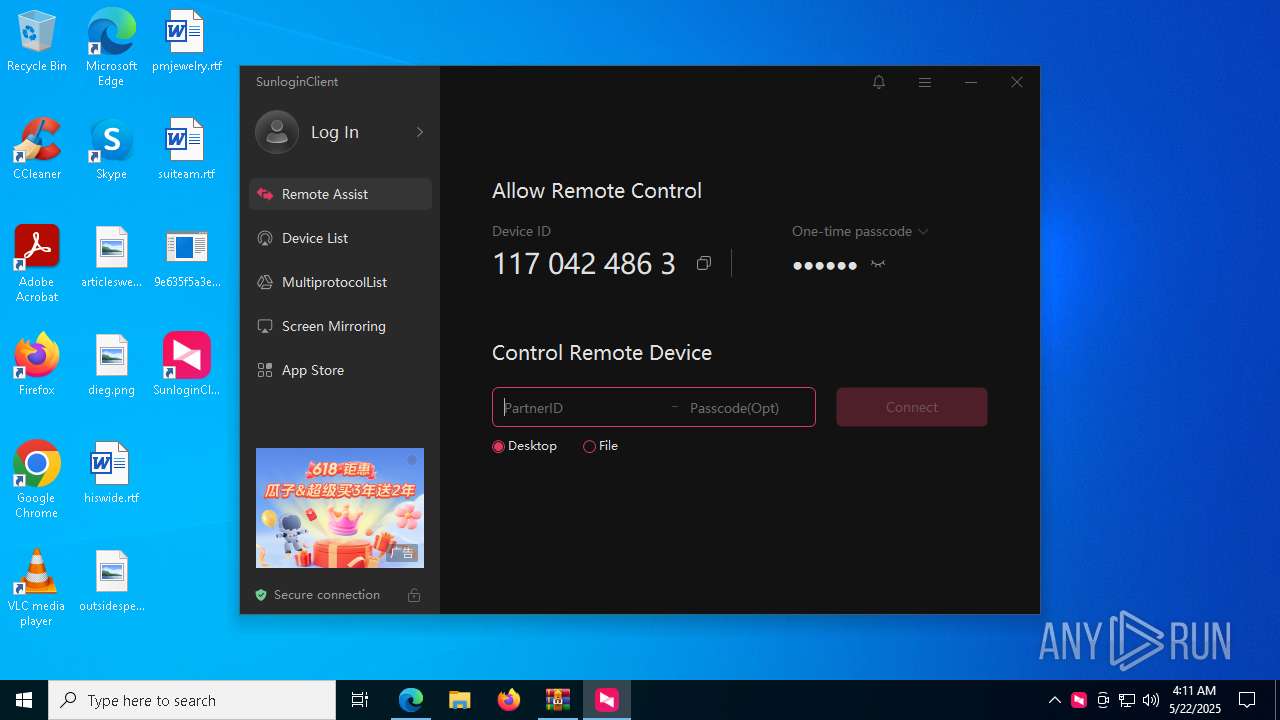
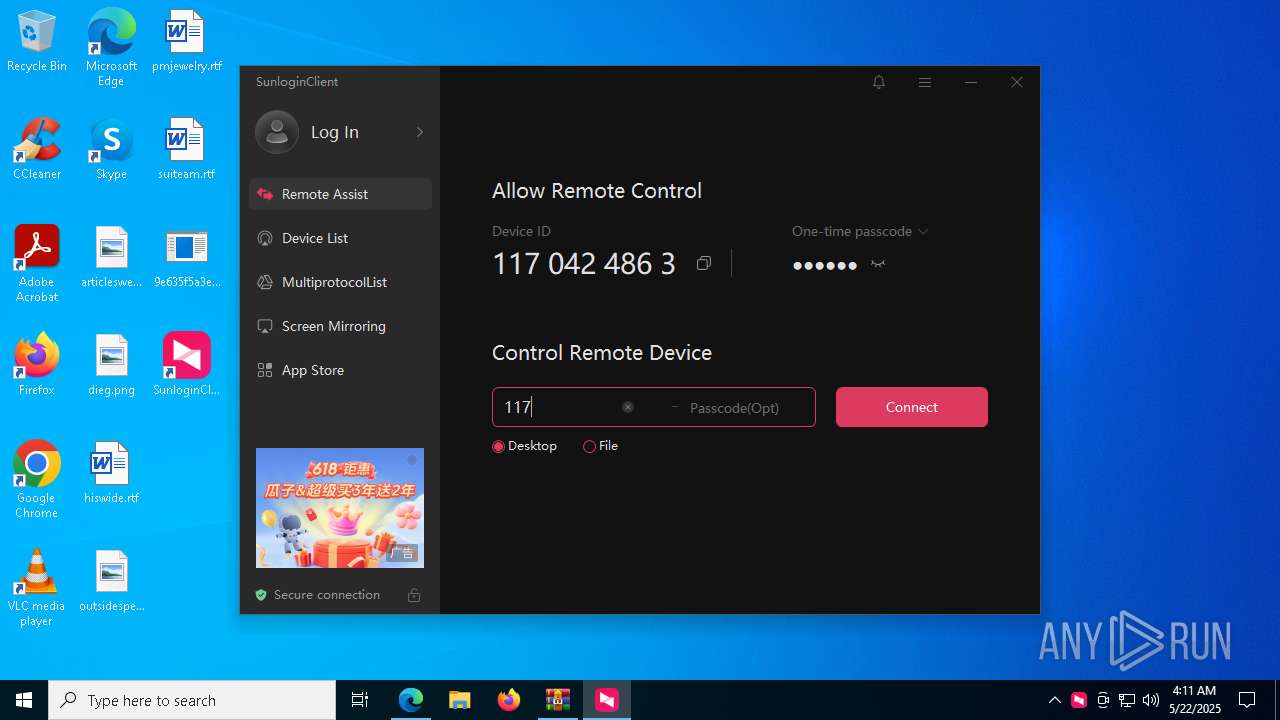
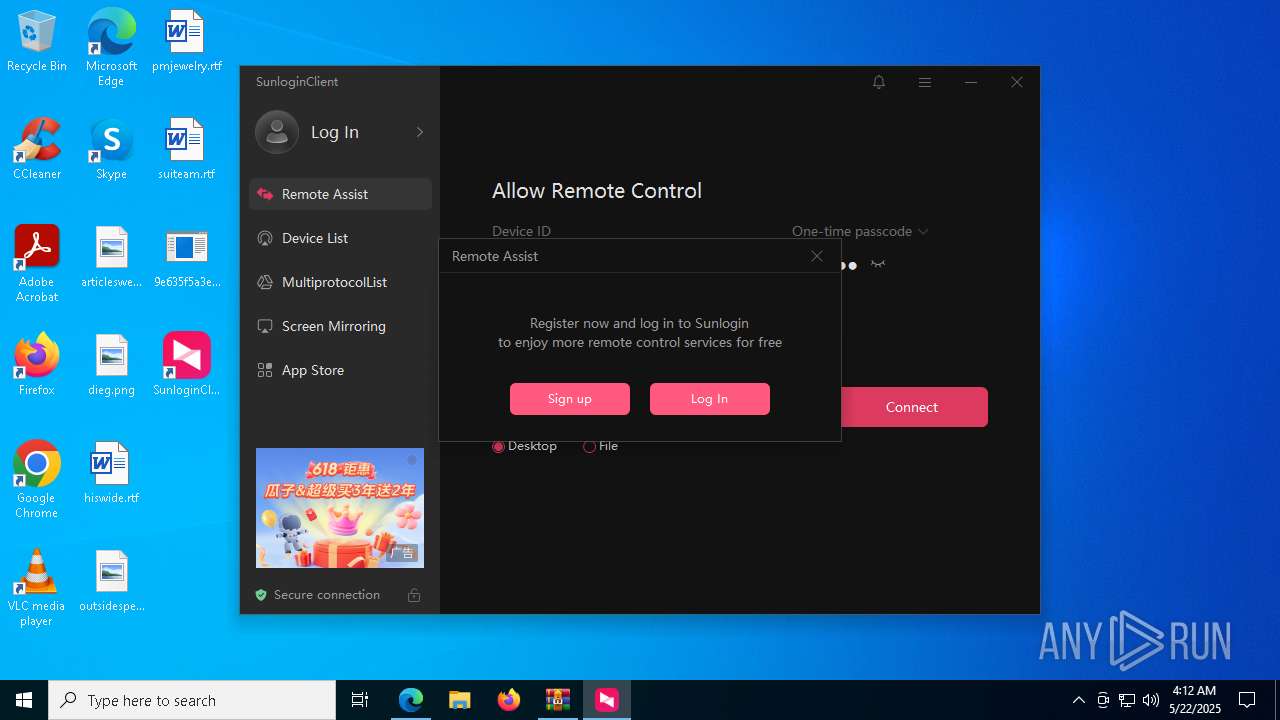
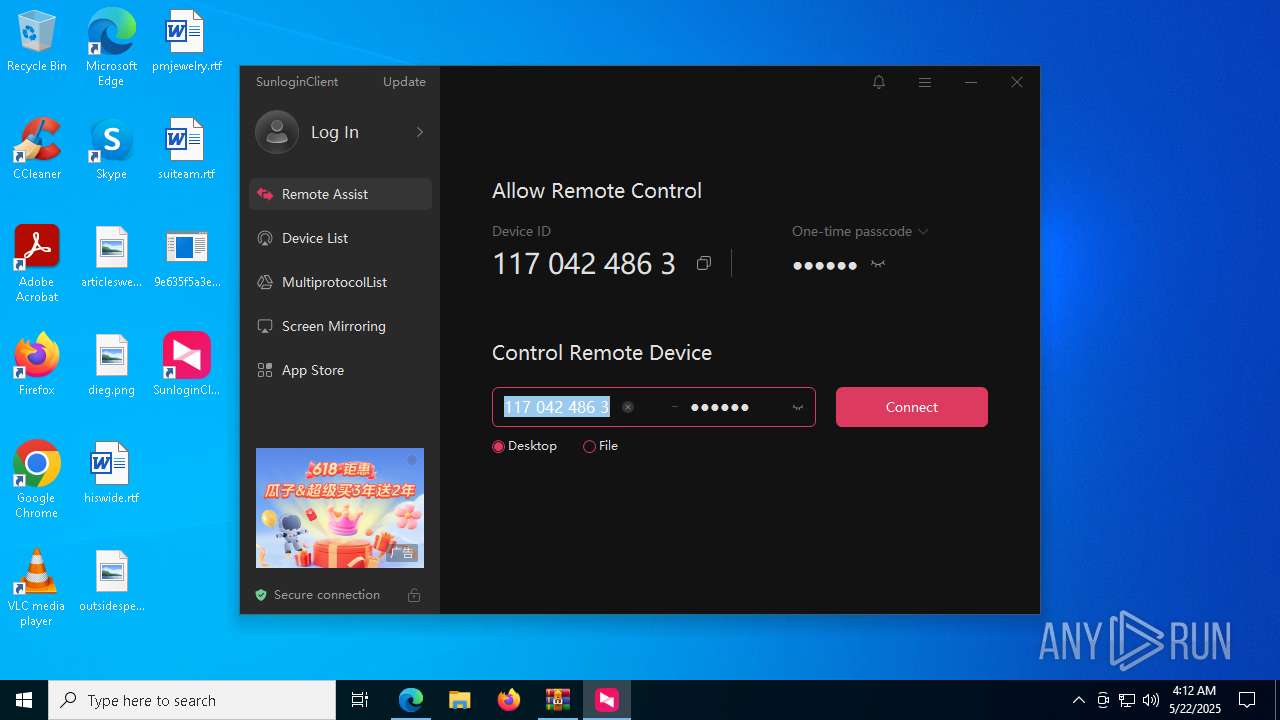
SUNLOGIN has been detected
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- SunloginClient.exe (PID: 5796)
- cmd.exe (PID: 3012)
- conhost.exe (PID: 3132)
- cmd.exe (PID: 7860)
- netsh.exe (PID: 6040)
- cmd.exe (PID: 8156)
The sample compiled with chinese language support
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
- SunloginClient.exe (PID: 6148)
UPX packer has been detected
- SunloginClient_15.8.2.19742_x64.exe (PID: 7616)
Checks operating system version
- cmd.exe (PID: 3012)
Executable content was dropped or overwritten
- msedge.exe (PID: 8728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
337
Monitored processes
185
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6952 --field-trial-handle=2448,i,4242201184105915349,16308317302872019995,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 436 | netsh advfirewall firewall add rule name="SunloginDesktopAgent" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\agent\SunloginClient.exe" protocol=tcp enable=yes profile=public | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | devcon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | netsh advfirewall firewall add rule name="SunloginDesktopAgent" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\agent\SunloginClient.exe" protocol=tcp enable=yes profile=private | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7924 --field-trial-handle=2448,i,4242201184105915349,16308317302872019995,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | C:\Users\admin\AppData\Local\Temp\PxUMubNwKcGPSQ{\wuying_helper.exe | C:\Users\admin\AppData\Local\Temp\PxUMubNwKcGPSQ{\wuying_helper.exe | — | wuying_helper.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 980 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2288 --field-trial-handle=2292,i,1072566223855739713,15576562470647016073,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | DrvInst.exe "2" "211" "ROOT\SYSTEM\0001" "C:\WINDOWS\INF\oem6.inf" "oem6.inf:c14ce884b119bfa2:OrayVGC_Device:1.0.0.0:oray\orayvgc," "4bd6fcd83" "00000000000001E8" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5844 --field-trial-handle=2448,i,4242201184105915349,16308317302872019995,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | netsh advfirewall firewall add rule name="SunloginClient" dir=out action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
99 054
Read events
98 708
Write events
246
Delete events
100
Modification events
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 99B05EEC47942F00 | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 528067EC47942F00 | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852634 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {93618206-EA90-469A-BF51-7CFE3217FFFE} | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852634 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F4D4274D-60DF-46FB-89B6-90908A28D141} | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852634 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {957A0978-D722-403D-93DE-7ECC722A1F19} | |||
| (PID) Process: | (4400) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852634 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2DD411C8-1887-4A7F-AE09-2A2CE04CE934} | |||
Executable files
180
Suspicious files
1 118
Text files
212
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b632.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b632.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b632.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b642.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b680.TMP | — | |
MD5:— | SHA256:— | |||
| 4400 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
371
DNS requests
233
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3240 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748301588&P2=404&P3=2&P4=Gp2F44EfYUdpp1aNyKjk2eH%2bL32B9BDOS8%2fnd4okash8G%2b%2fdcKHrlsJ0ZXjEArK3Uv%2bg2FcafMN29qknIf1j6g%3d%3d | unknown | — | — | whitelisted |
3240 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748301588&P2=404&P3=2&P4=Gp2F44EfYUdpp1aNyKjk2eH%2bL32B9BDOS8%2fnd4okash8G%2b%2fdcKHrlsJ0ZXjEArK3Uv%2bg2FcafMN29qknIf1j6g%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3240 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748301588&P2=404&P3=2&P4=Gp2F44EfYUdpp1aNyKjk2eH%2bL32B9BDOS8%2fnd4okash8G%2b%2fdcKHrlsJ0ZXjEArK3Uv%2bg2FcafMN29qknIf1j6g%3d%3d | unknown | — | — | whitelisted |
3300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3300 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3240 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748301588&P2=404&P3=2&P4=Gp2F44EfYUdpp1aNyKjk2eH%2bL32B9BDOS8%2fnd4okash8G%2b%2fdcKHrlsJ0ZXjEArK3Uv%2bg2FcafMN29qknIf1j6g%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3240 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748301588&P2=404&P3=2&P4=Gp2F44EfYUdpp1aNyKjk2eH%2bL32B9BDOS8%2fnd4okash8G%2b%2fdcKHrlsJ0ZXjEArK3Uv%2bg2FcafMN29qknIf1j6g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4400 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7260 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7260 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7260 | msedge.exe | 151.101.2.49:443 | bazaar.abuse.ch | FASTLY | US | whitelisted |
7260 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
bazaar.abuse.ch |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
5044 | wuying_helper.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 24 |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
5024 | SunloginClient.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ifconfig .me) |
5024 | SunloginClient.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
Process | Message |
|---|---|
SunloginClient.exe | [4572] 2025-05-22 04:10:52.737 - Info - [dpi] SetDPIAwareness isn't support.
|
SunloginClient.exe | [2960] 2025-05-22 04:10:52.737 = Debug = [thread] set thread name Thread-2960 915daf50 / 2960
|
SunloginClient.exe | [2616] 2025-05-22 04:10:52.738 = Debug = [thread] set thread name Thread-2616 6387f9f0 / 2616
|
SunloginClient.exe | [4572] 2025-05-22 04:10:52.738 = Debug = [select_tracker] run ok
|
SunloginClient.exe | CLocalServer::InitConfig @ 1488
|
SunloginClient.exe | SessionId:0, ConnectState:4, ClientProtocolType:0, UserName:, WinStationName:Services| SessionId:5, ConnectState:0, ClientProtocolType:0, UserName:admin, WinStationName:Console| |
SunloginClient.exe | SessionId:0, ConnectState:4, ClientProtocolType:0, UserName:, WinStationName:Services| SessionId:5, ConnectState:0, ClientProtocolType:0, UserName:admin, WinStationName:Console| |
SunloginClient.exe | [2984] 2025-05-22 04:10:53.216 = Debug = [thread] set thread name Thread-2984 915daf50 / 2984
|
SunloginClient.exe | [7856] 2025-05-22 04:10:53.217 - Info - [dpi] SetDPIAwareness isn't support.
|
SunloginClient.exe | [7856] 2025-05-22 04:10:53.219 = Debug = [select_tracker] run ok
|