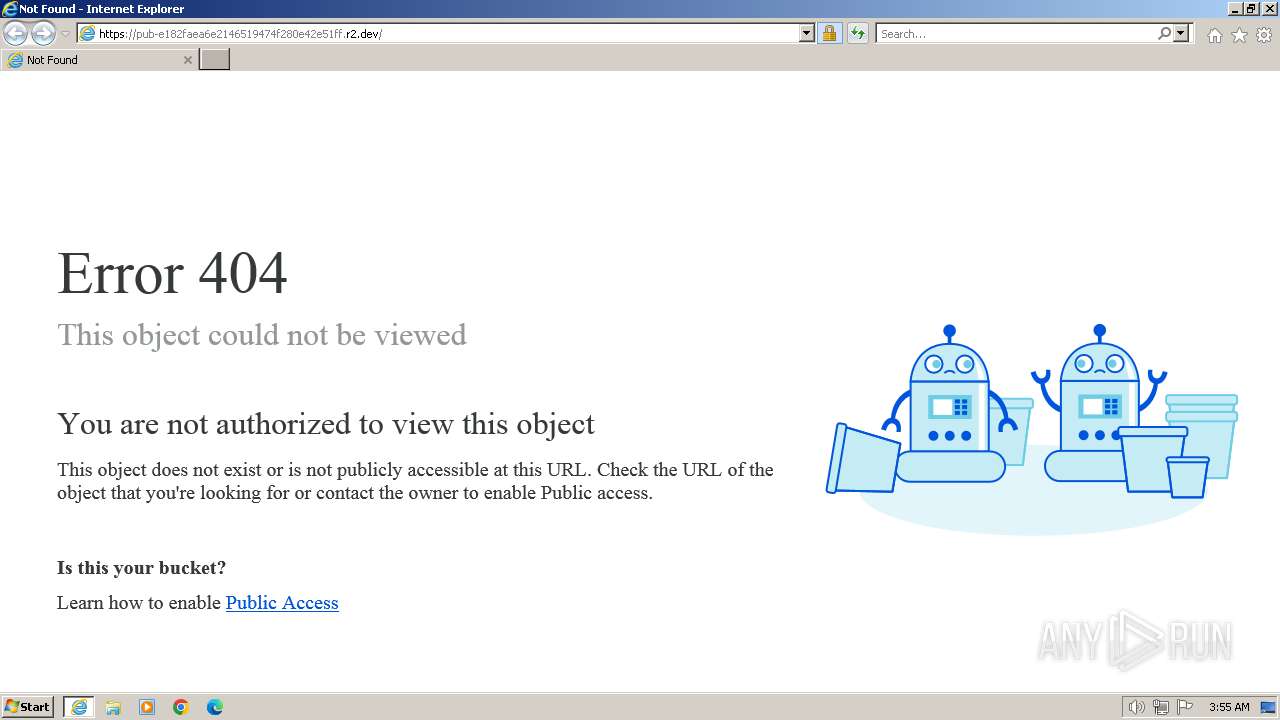
| URL: | https://pub-e182faea6e2146519474f280e42e51ff.r2.dev |
| Full analysis: | https://app.any.run/tasks/4496972e-1a09-4035-a52b-219d7047cde5 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2024, 03:55:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 32243EEA6725E844C86895D67C57EFE8 |
| SHA1: | 58DDE216BCBA3DEDD86736C5AA5250677BA1BA33 |
| SHA256: | 362A870DBDE26C2A7594F6319F91C383EE7097194E7BA2E202B9BDA879DAE7DF |
| SSDEEP: | 3:N8UdeURTqRSlNfHl2:2UMIGeFY |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3672 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://pub-e182faea6e2146519474f280e42e51ff.r2.dev" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 745
Read events
8 690
Write events
47
Delete events
8
Modification events
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31094010 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31094010 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4BD9.tmp | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4BDA.tmp | binary | |
MD5:DD73CEAD4B93366CF3465C8CD32E2796 | SHA256:A6752B7851B591550E4625B832A393AABCC428DE18D83E8593CD540F7D7CAE22 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:F219E1FA832E770B8BD220871B600195 | SHA256:9296B3CDCB70D800A82658FF34EA27B6A0C0DF55E8E01E529920A065436BC13F | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:A39FBA97D941C54FA645CEAF564867A1 | SHA256:DE993D4E9FAAAD9A1223AAFFB37DD713B605176FF569680125FF61CF8A432949 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:6168B0573D3246E1923E013395AB209F | SHA256:9129638B65E4A594789D5A0E599845CCB6A77E5A4B7B1712BC2D58F5F447A3ED | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:5AE8478AF8DD6EEC7AD4EDF162DD3DF1 | SHA256:FE42AC92EAE3B2850370B73C3691CCF394C23AB6133DE39F1697A6EBAC4BEDCA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
24
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3692 | iexplore.exe | GET | 200 | 23.32.238.171:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?46a3771404230298 | unknown | compressed | 67.5 Kb | unknown |
3692 | iexplore.exe | GET | 304 | 23.32.238.169:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?64db15c300a7b163 | unknown | — | — | unknown |
3692 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x2.c.lencr.org/ | unknown | binary | 299 b | unknown |
3692 | iexplore.exe | GET | 200 | 23.32.238.169:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f78d505714a595e3 | unknown | compressed | 67.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3692 | iexplore.exe | 104.18.3.35:443 | pub-e182faea6e2146519474f280e42e51ff.r2.dev | CLOUDFLARENET | — | unknown |
3692 | iexplore.exe | 23.32.238.241:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3672 | iexplore.exe | 104.126.37.178:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3692 | iexplore.exe | 104.18.2.35:443 | pub-e182faea6e2146519474f280e42e51ff.r2.dev | CLOUDFLARENET | — | unknown |
3692 | iexplore.exe | 23.32.238.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3692 | iexplore.exe | 23.32.238.169:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pub-e182faea6e2146519474f280e42e51ff.r2.dev |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3692 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Public R2.dev Bucket Abuse to Phishing in TLS (Greatness) |
3692 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Public R2.dev Bucket Abuse to Phishing in TLS (Greatness) |