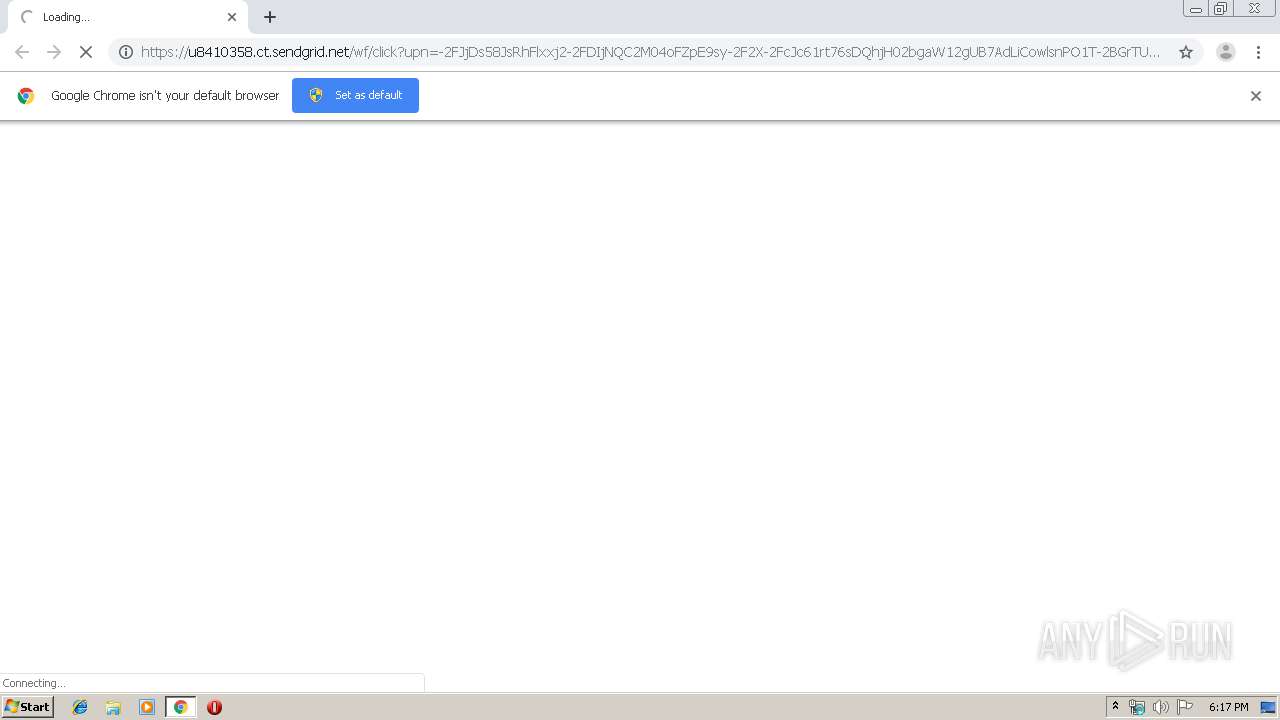
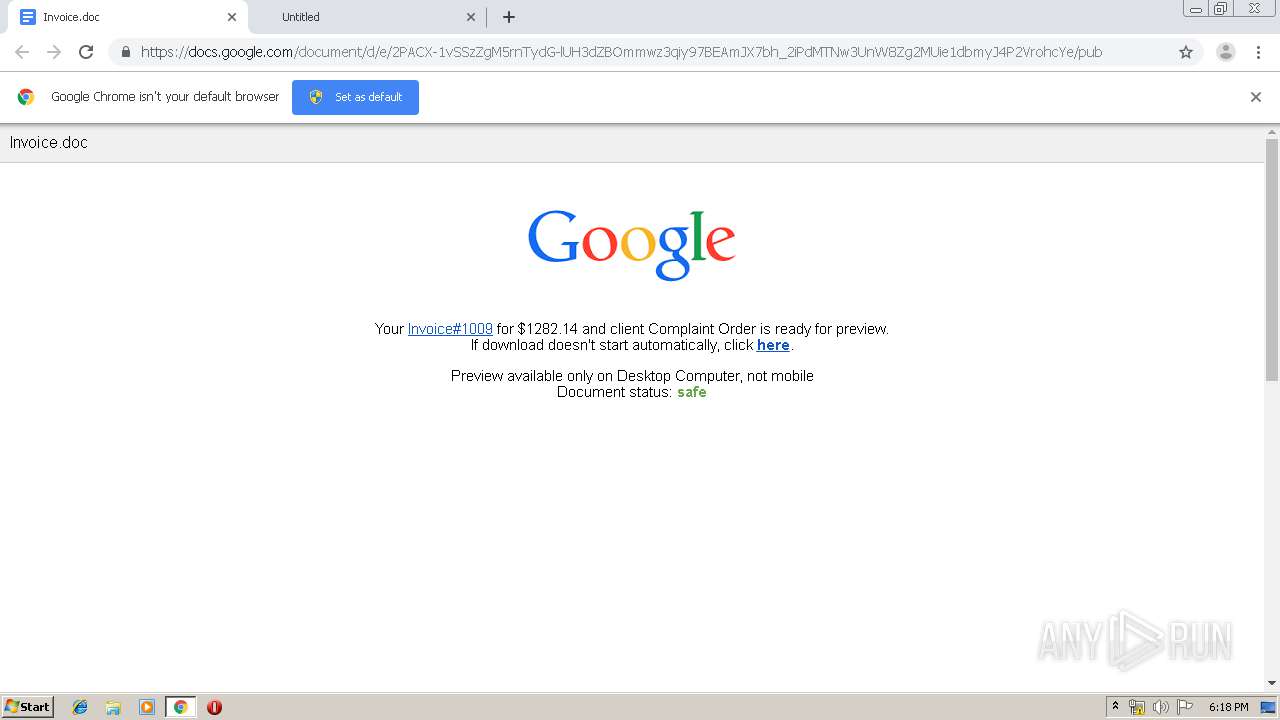
| URL: | https://u8410358.ct.sendgrid.net/wf/click?upn=-2FJjDs58JsRhFlxxj2-2FDIjNQC2M04oFZpE9sy-2F2X-2FcJc61rt76sDQhjH02bgaW12gUB7AdLiCowlsnPO1T-2BGrTUayjyqVmThVNtm-2BM9IFssuouDiyLK2aFS8UsXWrqYeFSsLwhklJsINKOkBoZM1e4WAtcCnmOiZ-2BT6LeQG-2BY7UJETezoQBzkLpJJ8C-2BksAGc_UZ-2Fw3Bg8EOda-2F-2BSazO07kac45x4IIkK9-2FYprQxHVDdIcXL0U0EYPOFdiqPXEo4amselS9GaXK9n9E4L-2Bv8kJG4u6Gt8knyCoWmeThS-2FPEImMGY3gK2d8vj1HfbulOPkOw6NJfmtubRMicZo-2B-2F8jMFk8z1tzVFZ-2FMxVbmM8lVb0n0WTbBqqnD-2FRNAMceX80swYGTbIeT2VKrtQWmxazQN6rbRPtgM065ihEcTknQWQKCbHPXp9V5qHOfrQllKGwWN |
| Full analysis: | https://app.any.run/tasks/7f2bdff5-e794-45e9-a448-10116a709475 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 17:16:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EE9C0B41CEE86DB2452596E1A12BCB9D |
| SHA1: | 3EFB4CCD63055829106B62EED683A36D393EE887 |
| SHA256: | 3625D6D4F21AEAA1ED2389D4F9A2F0E5A1C8823B7CA3D66E8F80453BFE566683 |
| SSDEEP: | 12:2PDSpc01cKhvaa+q7Mn/axrGbYM+OtrKWG4HEeEomuLmtz347:27lm3vEq7saBGOvigEmBW |
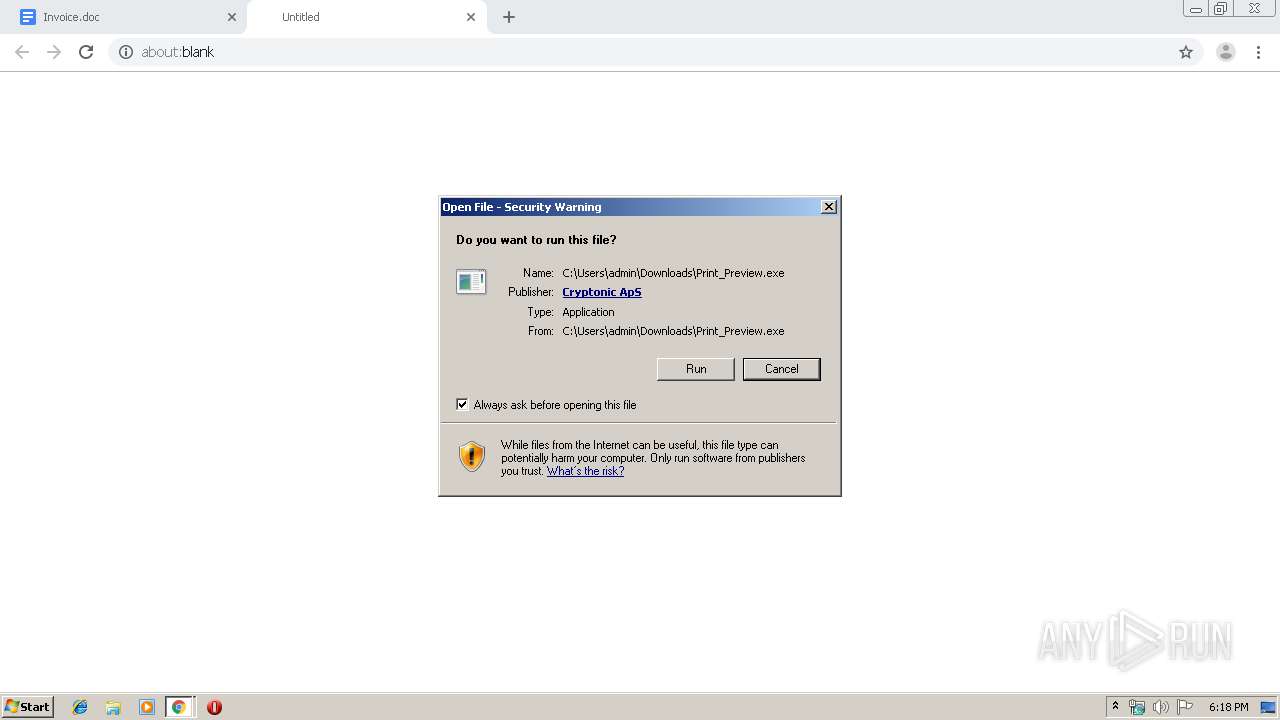
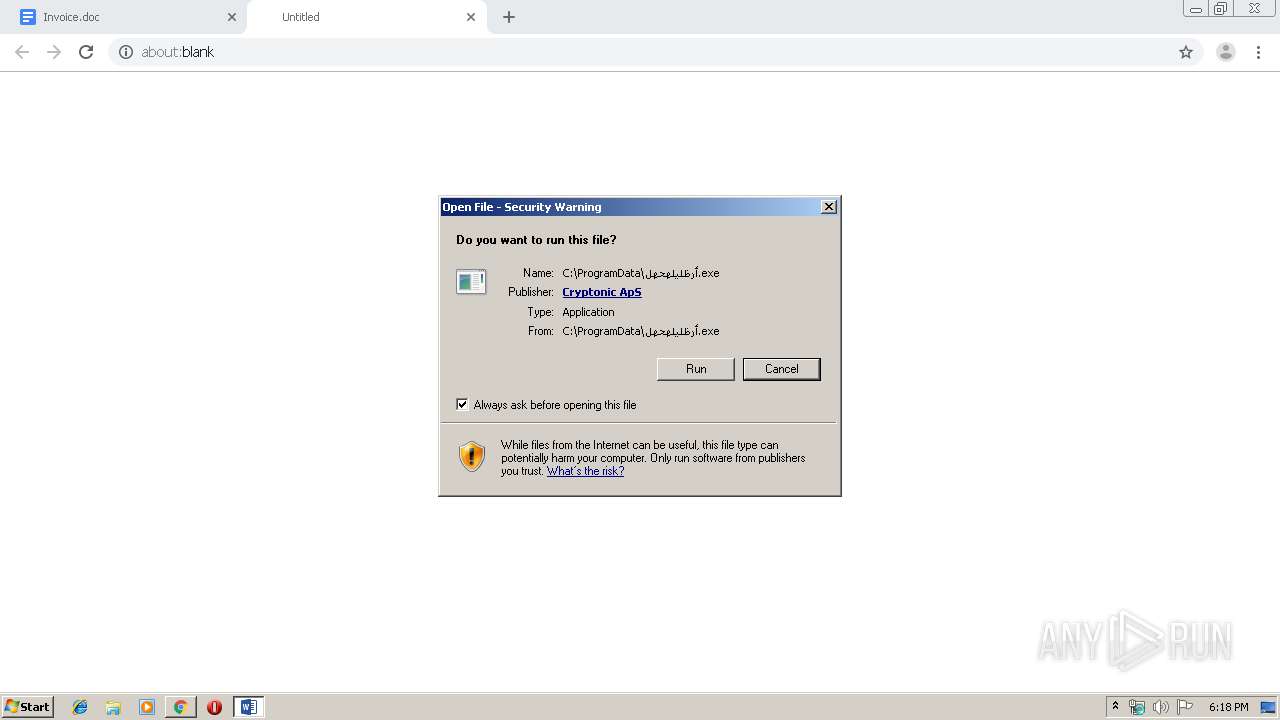
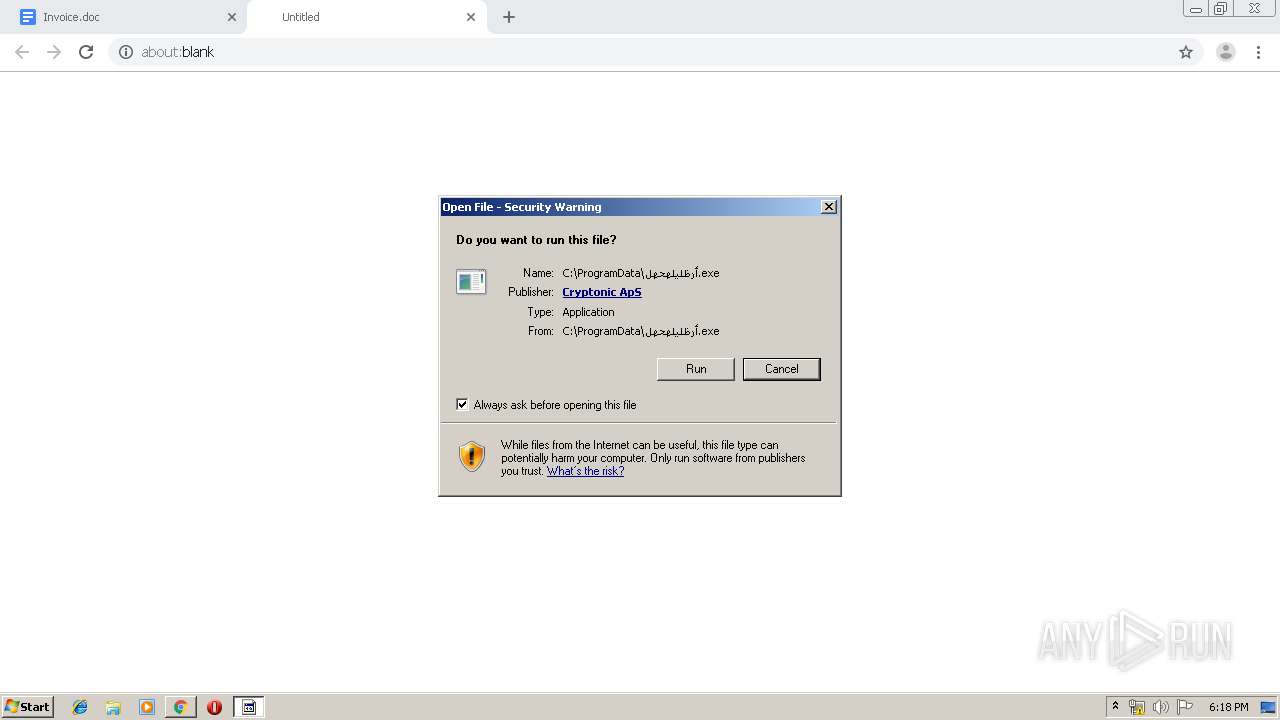
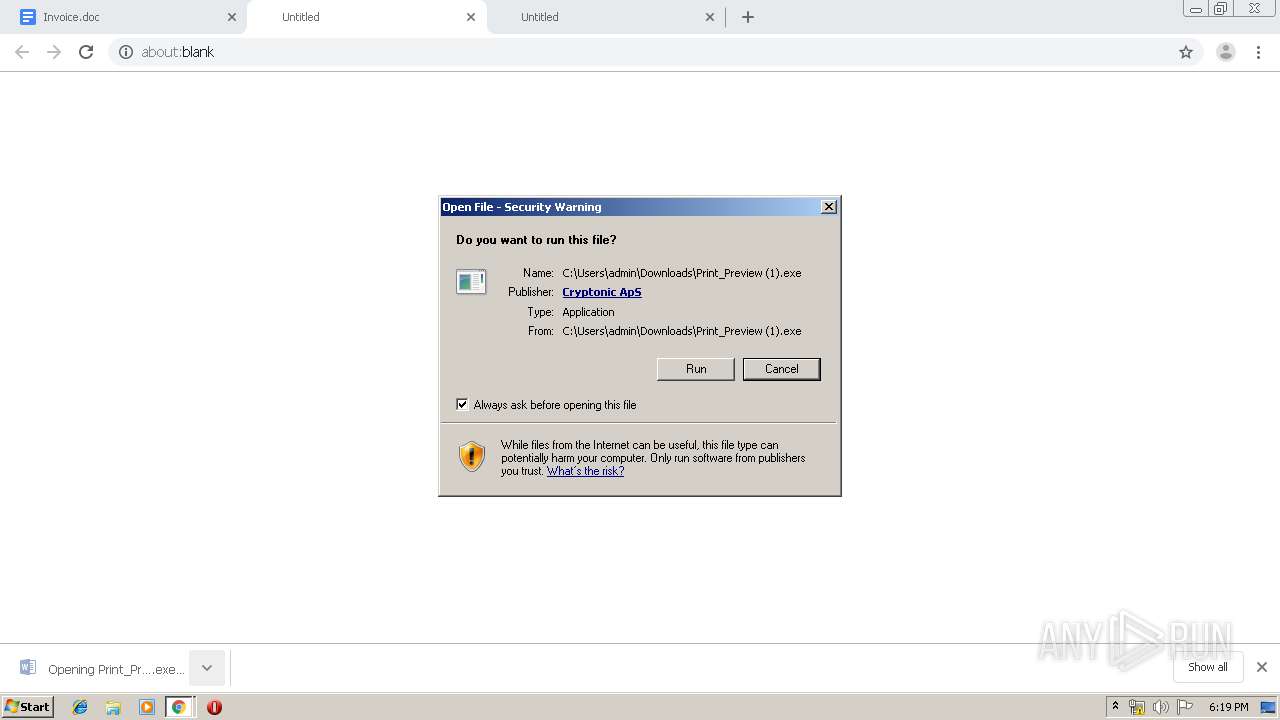
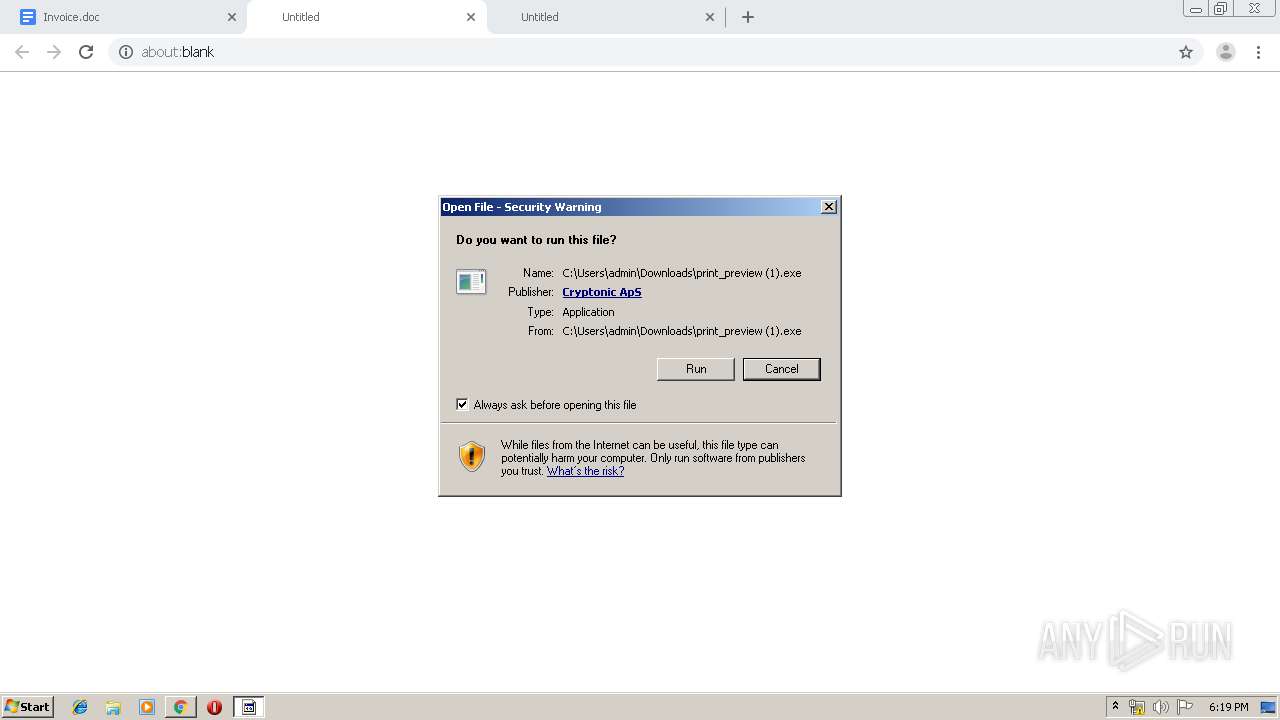
MALICIOUS
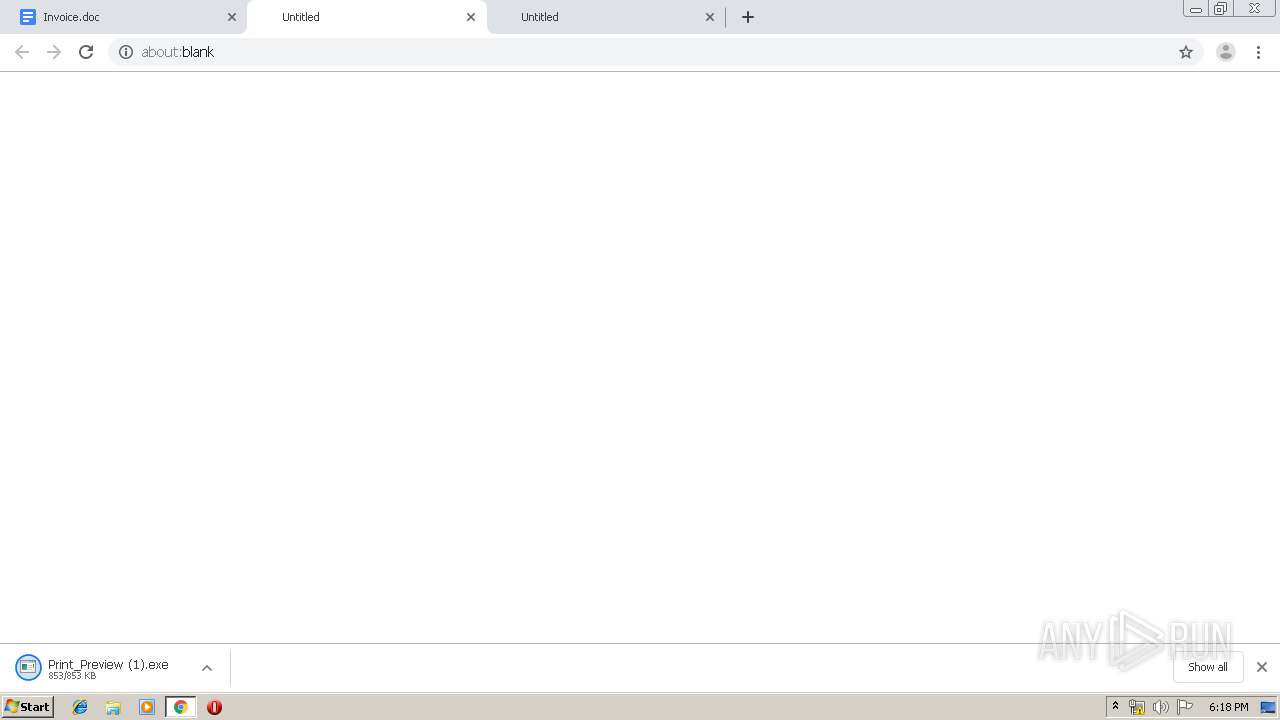
Application was dropped or rewritten from another process
- أرظليلهحهل.exe (PID: 2716)
- Print_Preview.exe (PID: 3516)
- أرظليلهحهل.exe (PID: 3384)
- Print_Preview (1).exe (PID: 3696)
- print_preview (1).exe (PID: 3084)
- أرظليلهحهل.exe (PID: 2140)
Known privilege escalation attack
- DllHost.exe (PID: 3656)
- DllHost.exe (PID: 596)
Loads the Task Scheduler COM API
- أرظليلهحهل.exe (PID: 3384)
- print_preview (1).exe (PID: 3084)
- أرظليلهحهل.exe (PID: 2140)
SUSPICIOUS
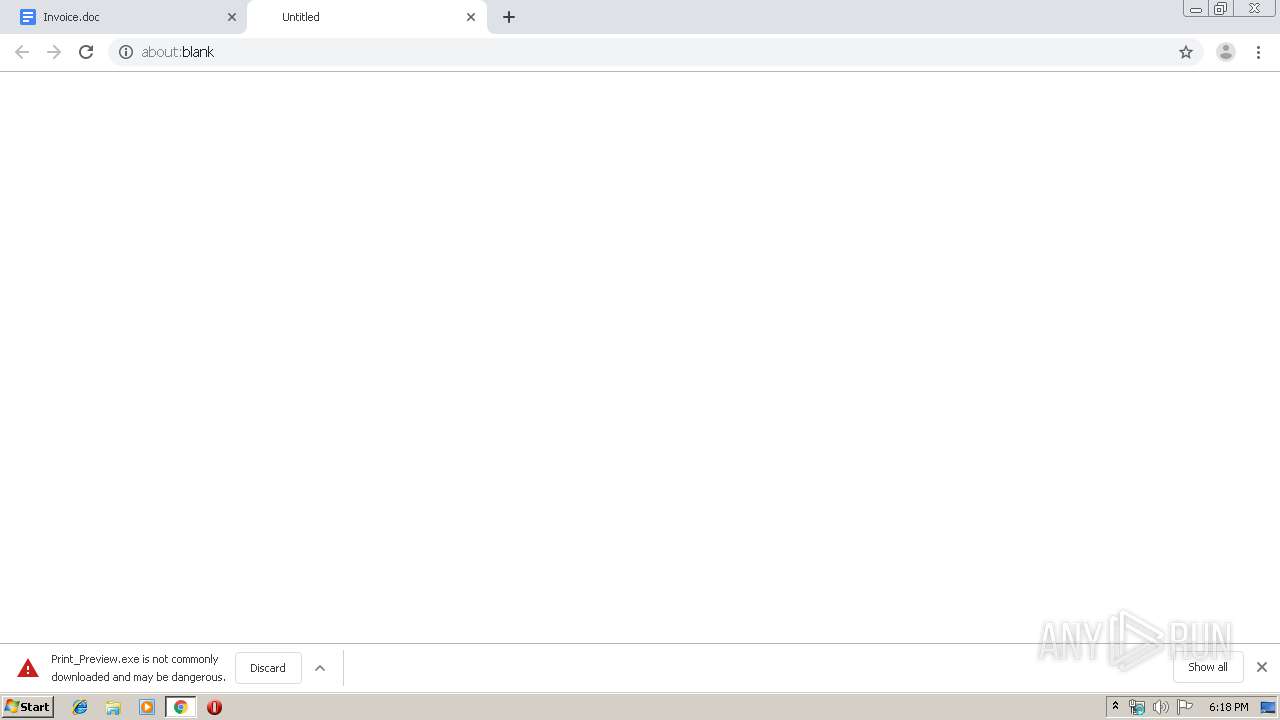
Executable content was dropped or overwritten
- Print_Preview.exe (PID: 3516)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 1440)
- أرظليلهحهل.exe (PID: 3384)
- print_preview (1).exe (PID: 3084)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2864)
Executed via COM
- DllHost.exe (PID: 3656)
- DllHost.exe (PID: 596)
Creates files in the program directory
- Print_Preview.exe (PID: 3516)
Starts itself from another location
- Print_Preview.exe (PID: 3516)
Creates files in the user directory
- أرظليلهحهل.exe (PID: 3384)
- print_preview (1).exe (PID: 3084)
- أرظليلهحهل.exe (PID: 2140)
Executed via Task Scheduler
- أرظليلهحهل.exe (PID: 2140)
INFO
Application launched itself
- chrome.exe (PID: 2864)
Reads the hosts file
- chrome.exe (PID: 1440)
- chrome.exe (PID: 2864)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2864)
- Print_Preview.exe (PID: 3516)
- chrome.exe (PID: 1440)
- أرظليلهحهل.exe (PID: 3384)
- print_preview (1).exe (PID: 3084)
Reads Internet Cache Settings
- chrome.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
37
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4562919201573891692 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=355144838309302473 --mojo-platform-channel-handle=4324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | C:\Users\admin\AppData\Roaming\netRest\أرظليلهحهل.exe | C:\Users\admin\AppData\Roaming\netRest\أرظليلهحهل.exe | taskeng.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17335486506186868324 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13337269340099484284 --mojo-platform-channel-handle=3780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5653016443620466431 --mojo-platform-channel-handle=4264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5060553940325991033 --mojo-platform-channel-handle=2300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15105849817201114084 --mojo-platform-channel-handle=3792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,274919302934120462,3366698548099467712,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3371623437059361985 --mojo-platform-channel-handle=4228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 554
Read events
1 412
Write events
137
Delete events
5
Modification events
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2864-13215115038528750 |
Value: 259 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
11
Suspicious files
29
Text files
252
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf16bb.TMP | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\62e2fd5b-f1fd-4e6d-8719-1885189c69d1.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf169c.TMP | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
29
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1440 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
1440 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
1440 | chrome.exe | GET | 200 | 173.194.137.72:80 | http://r3---sn-aigzrn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.43.110.19&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1570641382&mv=m&mvi=2&pl=27&shardbypass=yes | US | crx | 862 Kb | whitelisted |
1440 | chrome.exe | GET | 200 | 173.194.135.105:80 | http://r4---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.43.110.19&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1570641382&mv=m&mvi=3&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1440 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
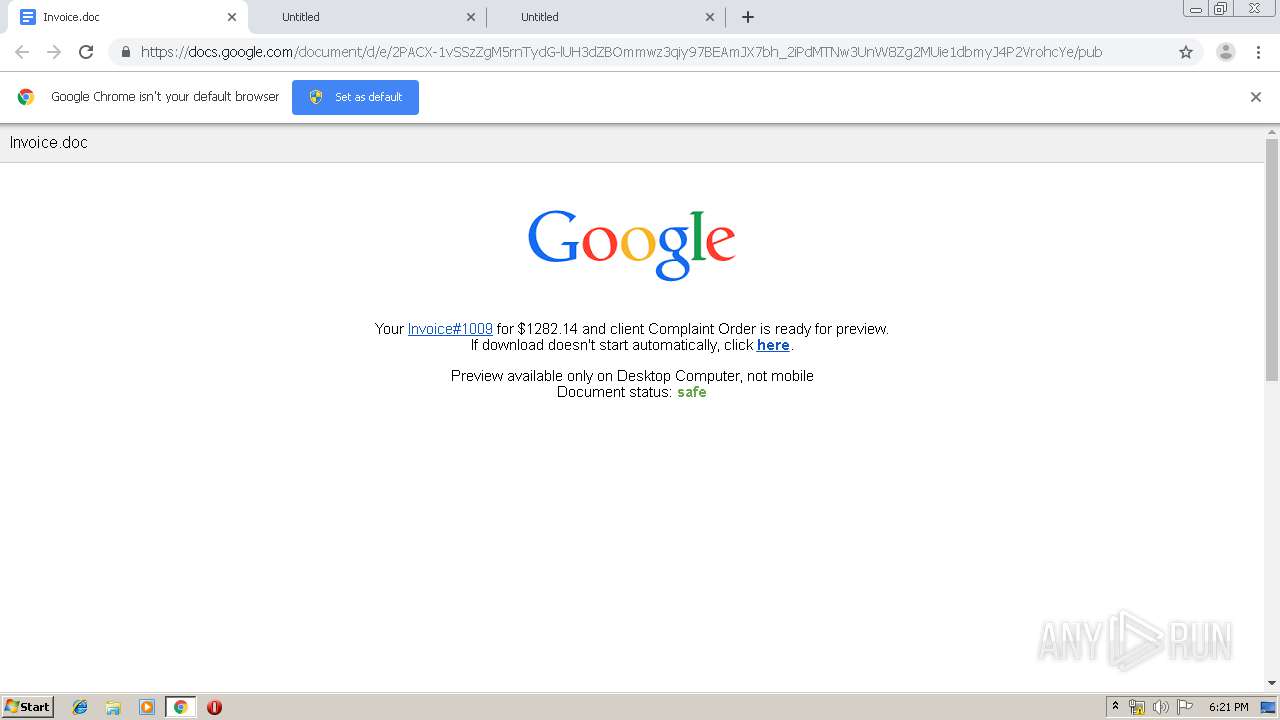
1440 | chrome.exe | 167.89.115.54:443 | u8410358.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
1440 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
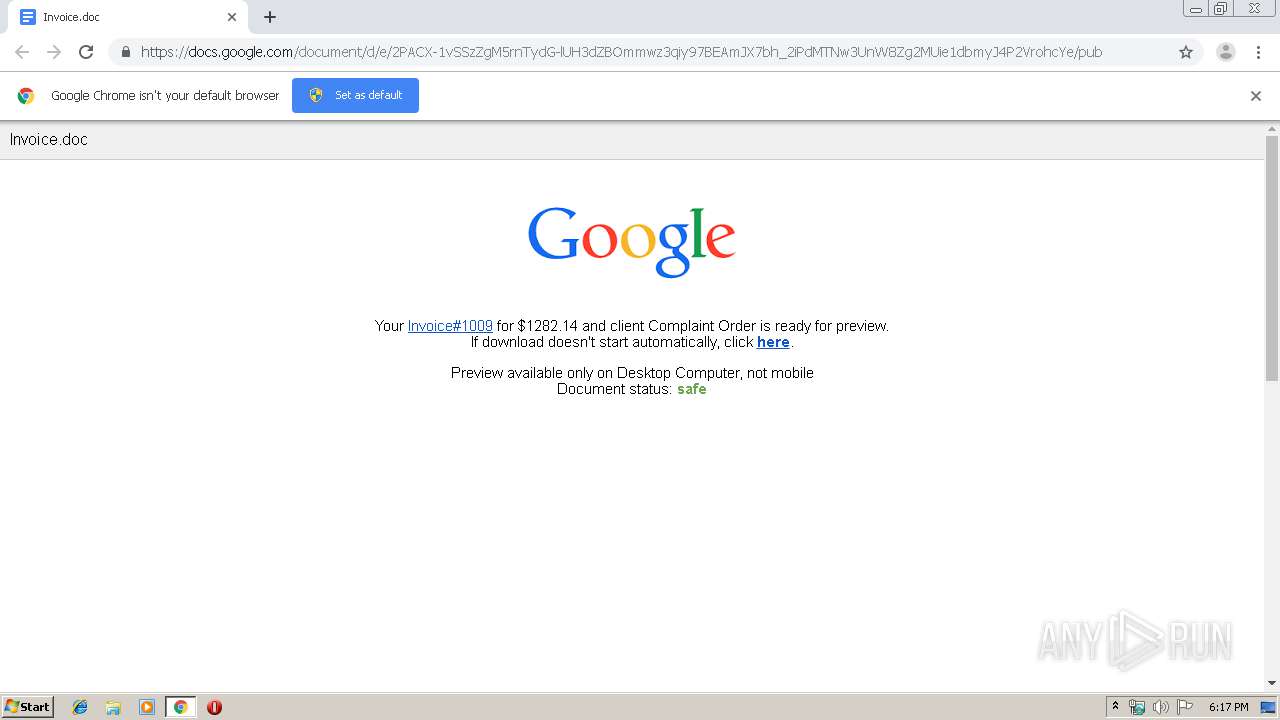
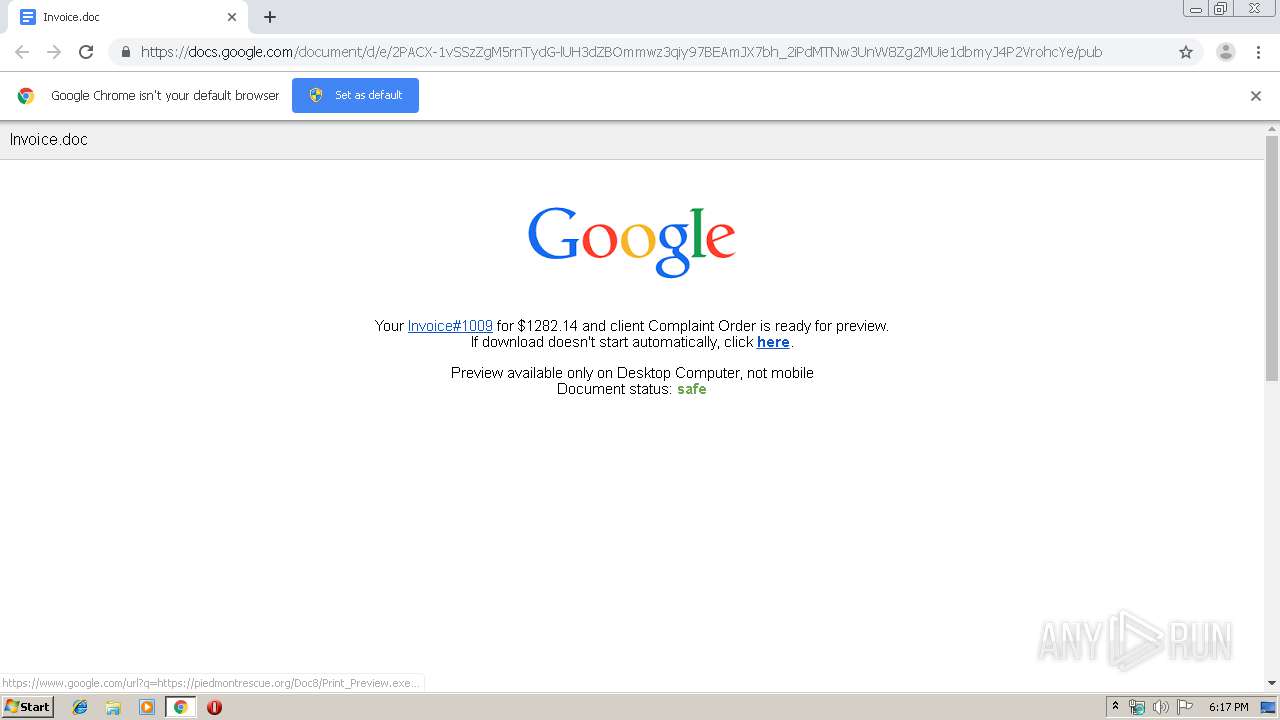
1440 | chrome.exe | 172.217.18.174:443 | docs.google.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.18.1:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 70.40.217.118:443 | piedmontrescue.org | Unified Layer | US | suspicious |
1440 | chrome.exe | 172.217.16.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u8410358.ct.sendgrid.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
docs.google.com |
| shared |
www.google.com |
| malicious |
lh3.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
piedmontrescue.org |
| suspicious |
redirector.gvt1.com |
| whitelisted |