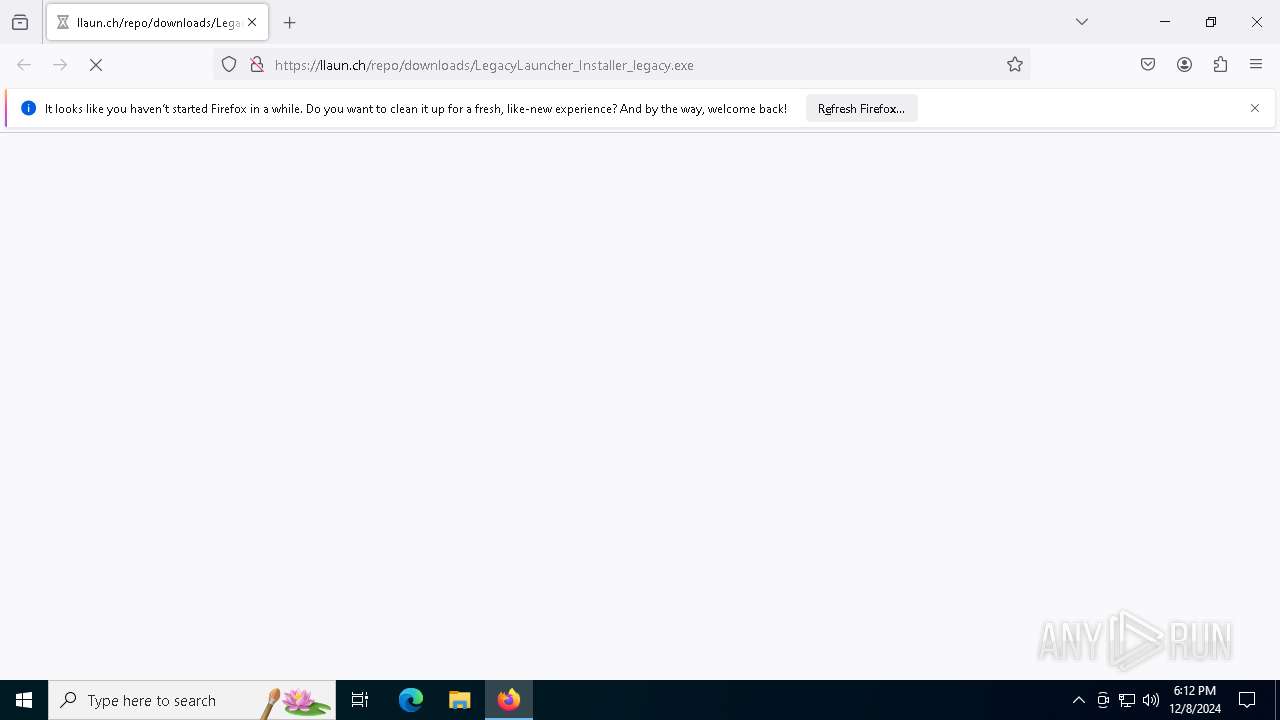
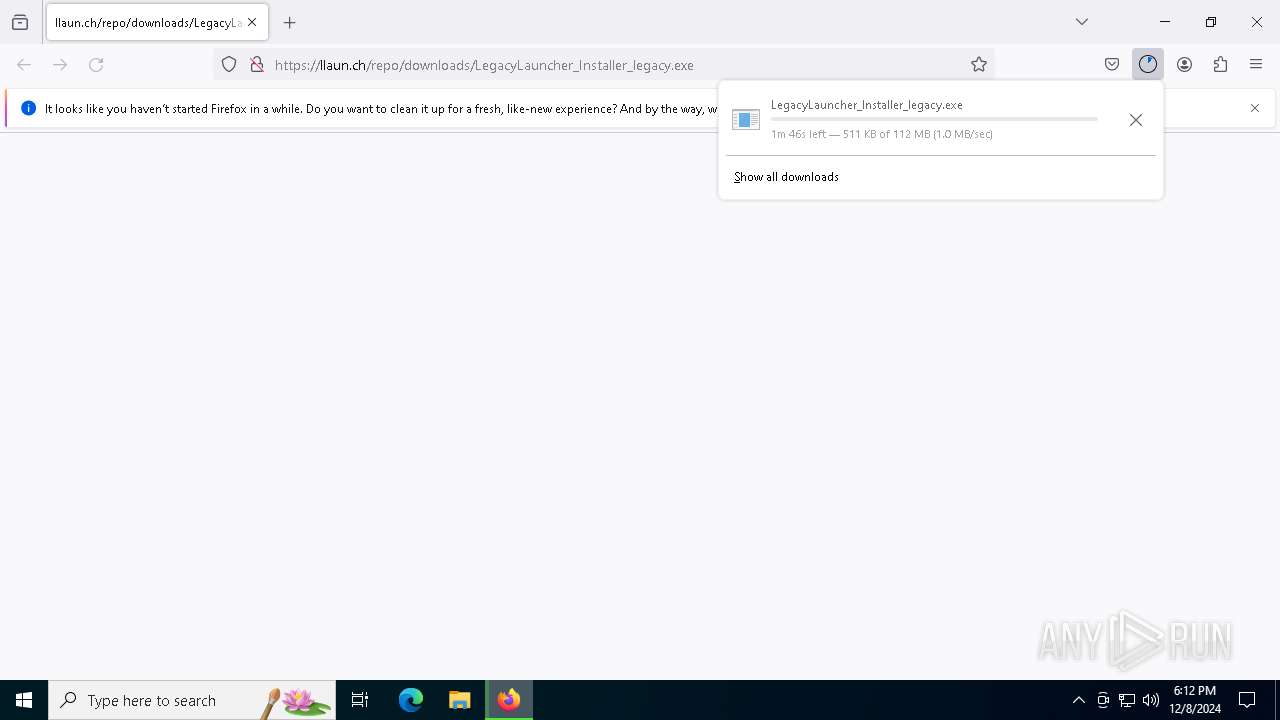
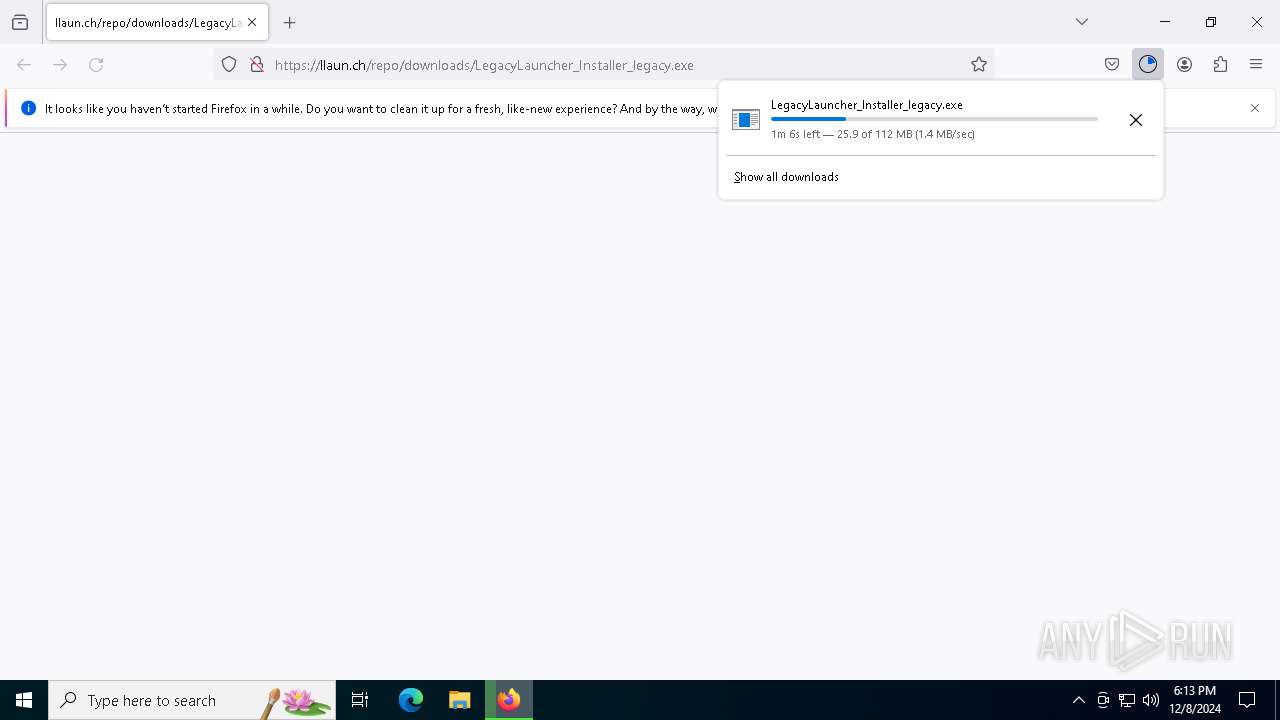
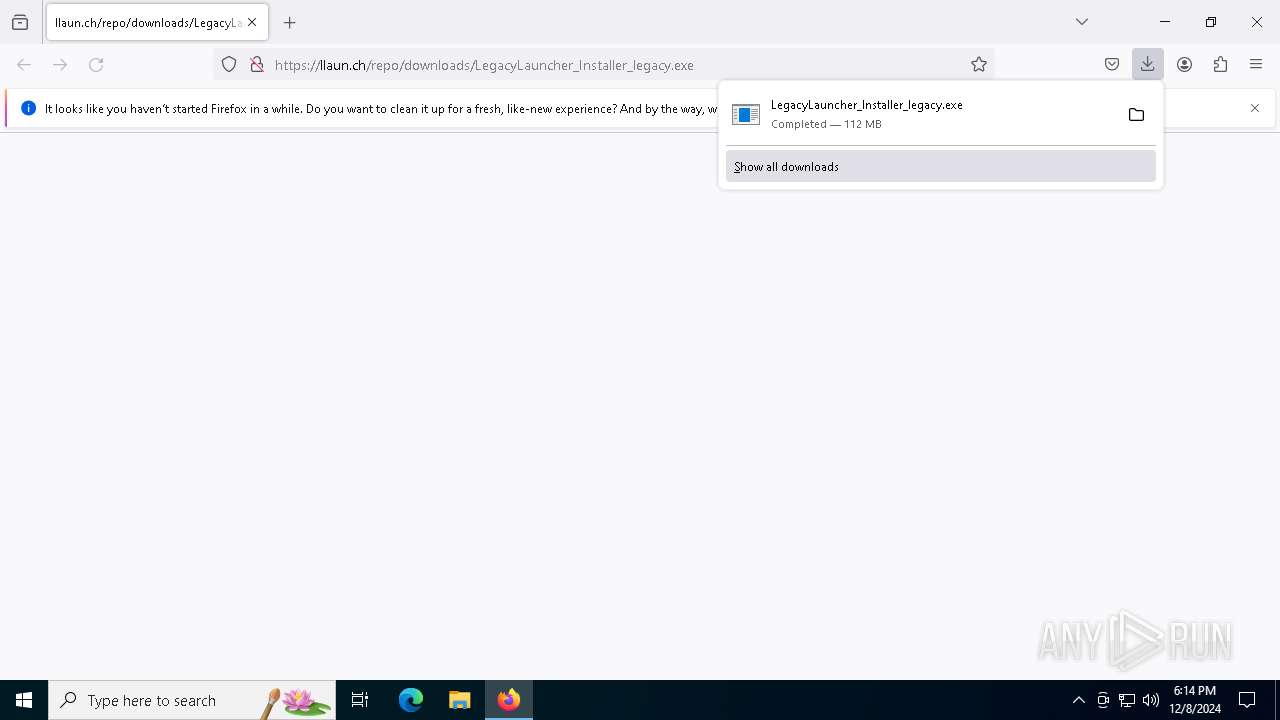
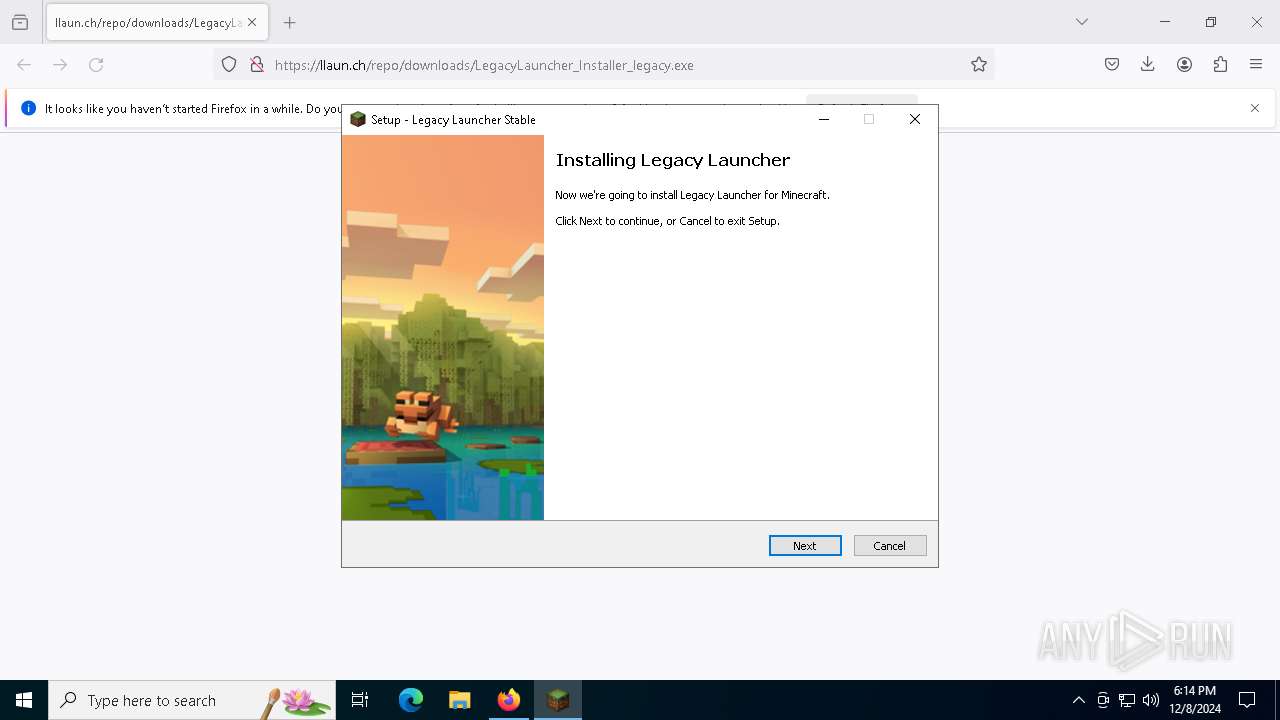
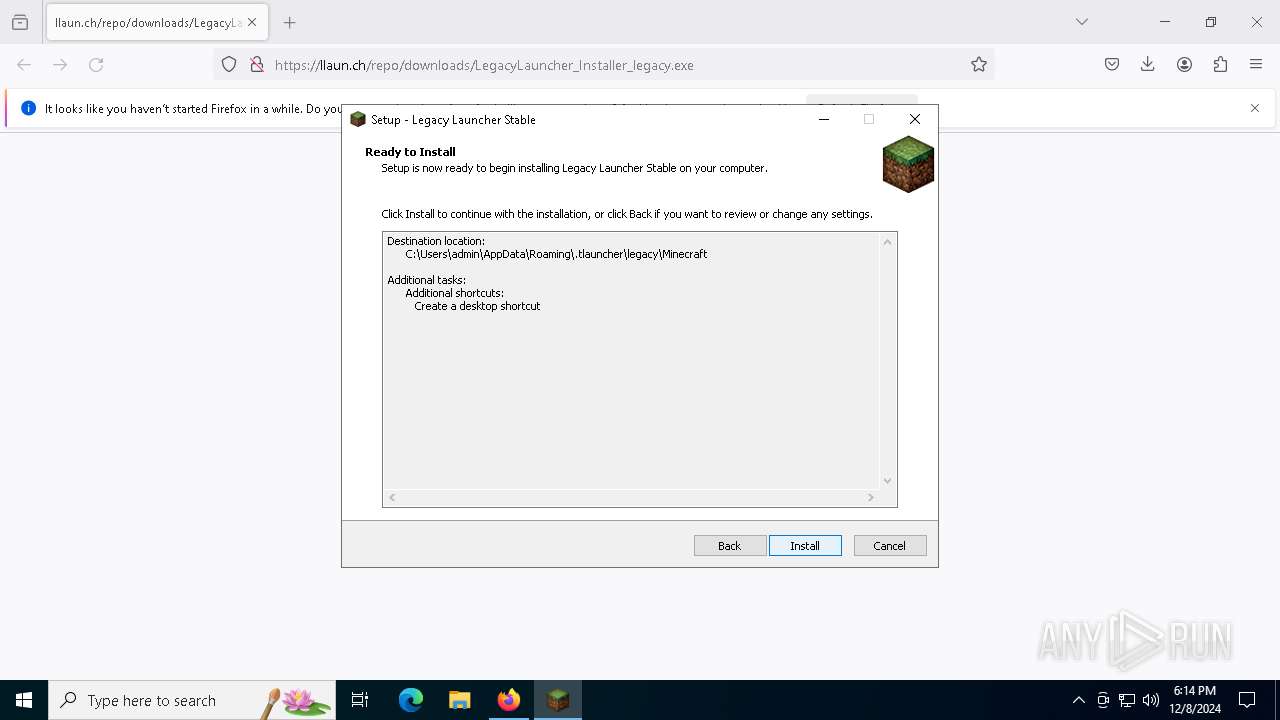
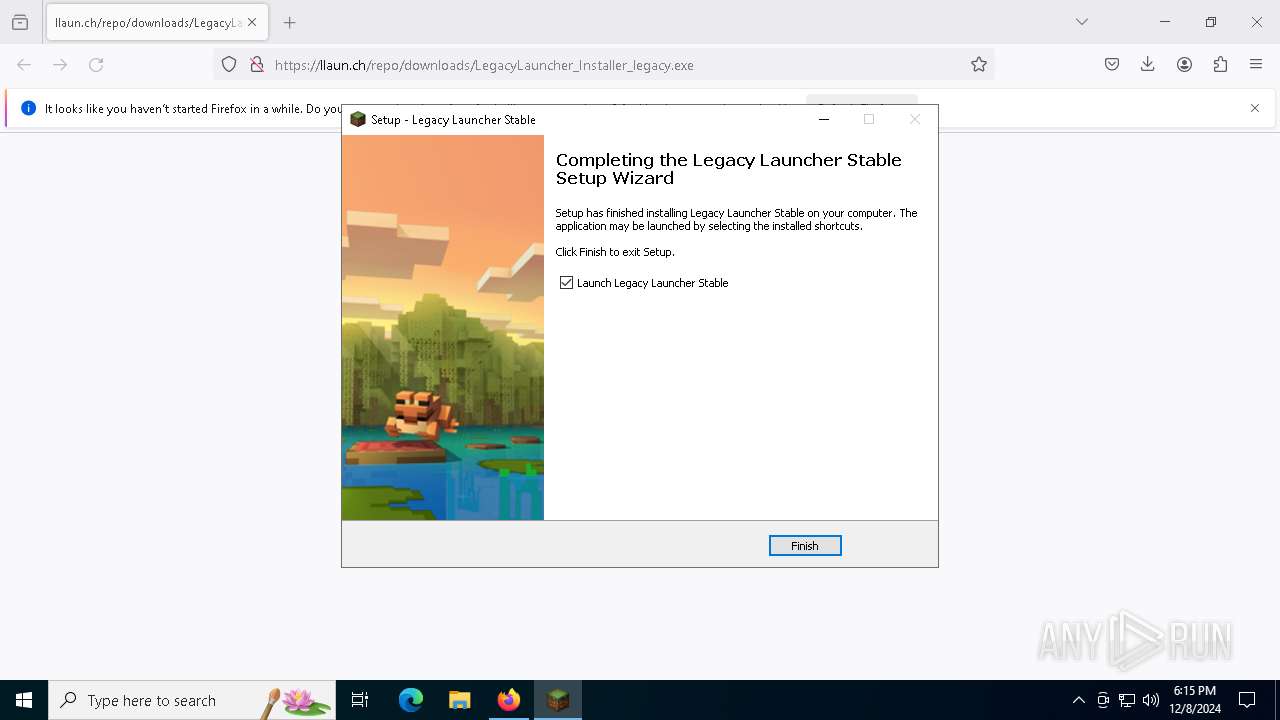
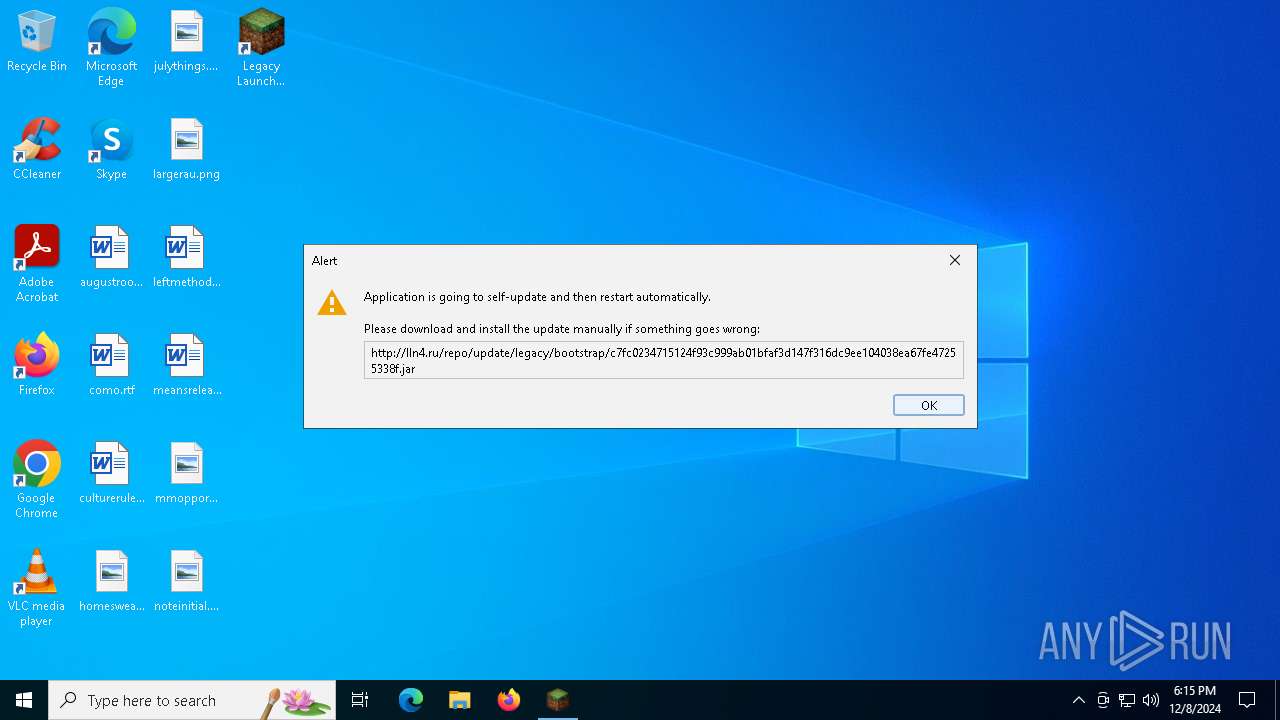
| URL: | https://llaun.ch/repo/downloads/LegacyLauncher_Installer_legacy.exe |
| Full analysis: | https://app.any.run/tasks/0e4ac712-f1f8-4da7-9801-8d74ca562625 |
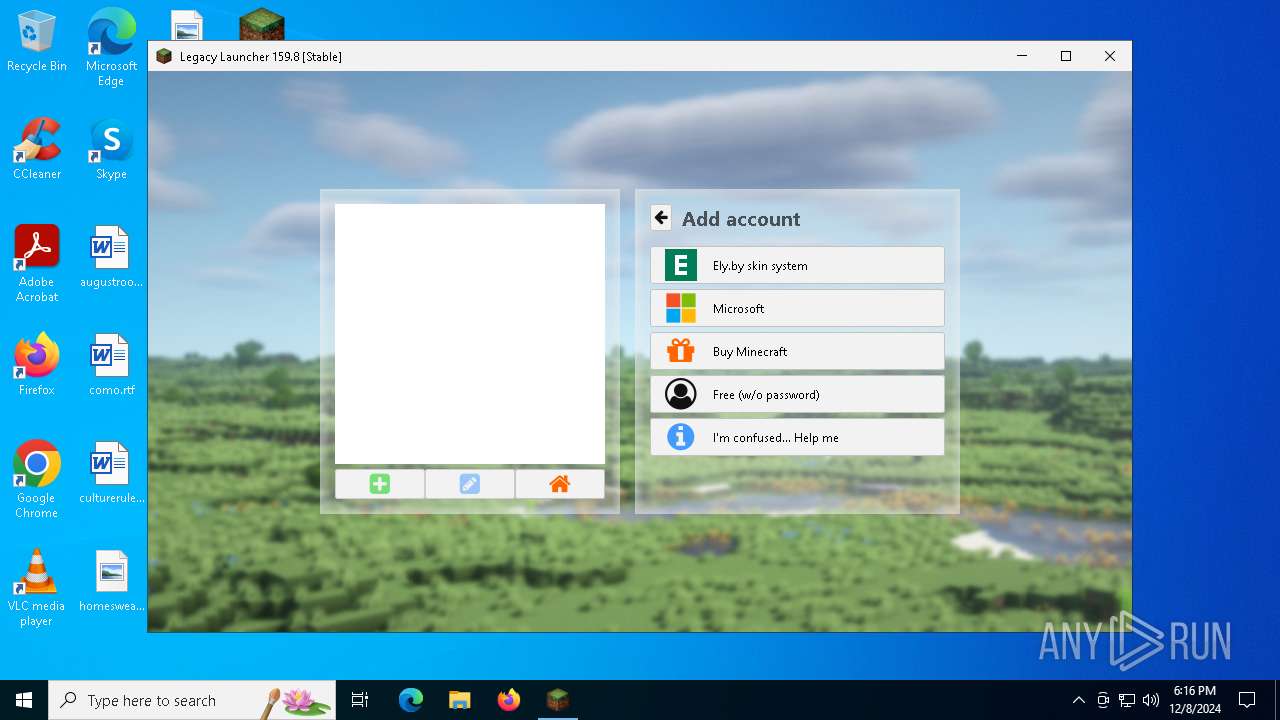
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2024, 18:12:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6EBC87CECDC7FB002927A0015F6C8C87 |
| SHA1: | 030BC2A0110C752DDC2F6DB72C0BDEED28FFA8A3 |
| SHA256: | 3619273BD353D78C1745FBFC58B12BE217C565D6EF2E4688E0B74CAA0495FEA9 |
| SSDEEP: | 3:N8JhGrPqKB0aFBXjHIdA:2DWJLXjodA |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2192)
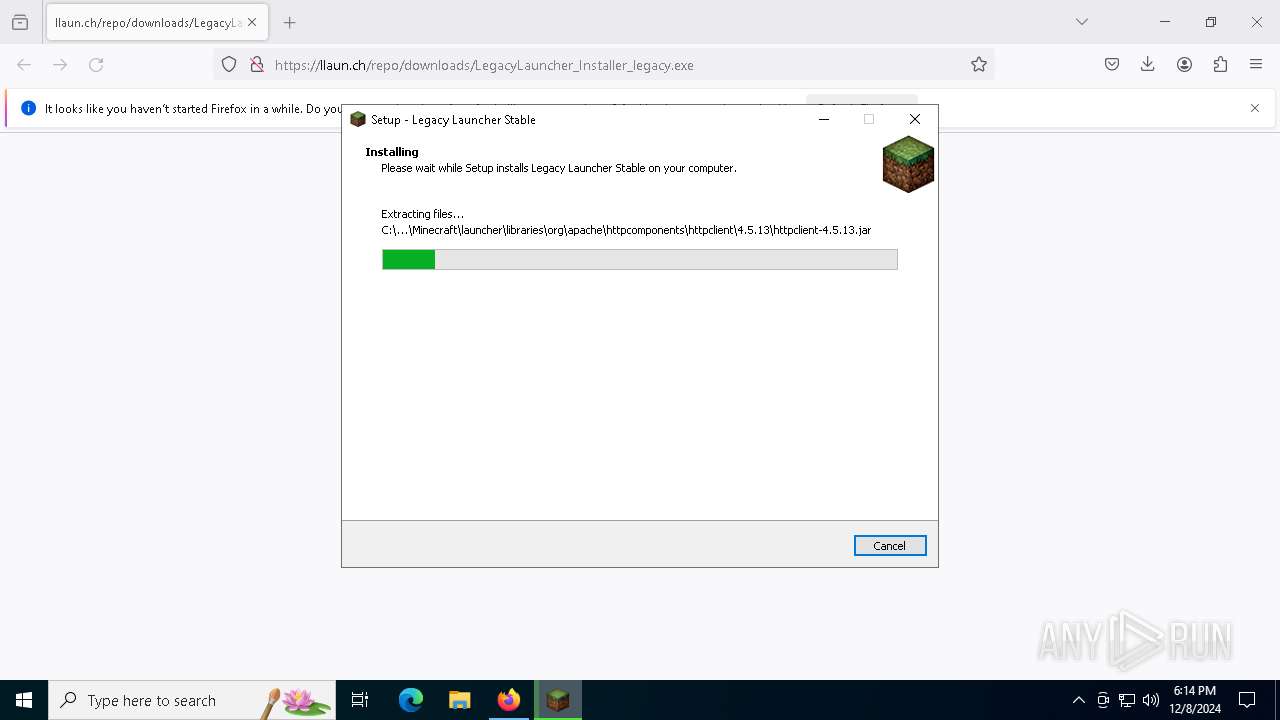
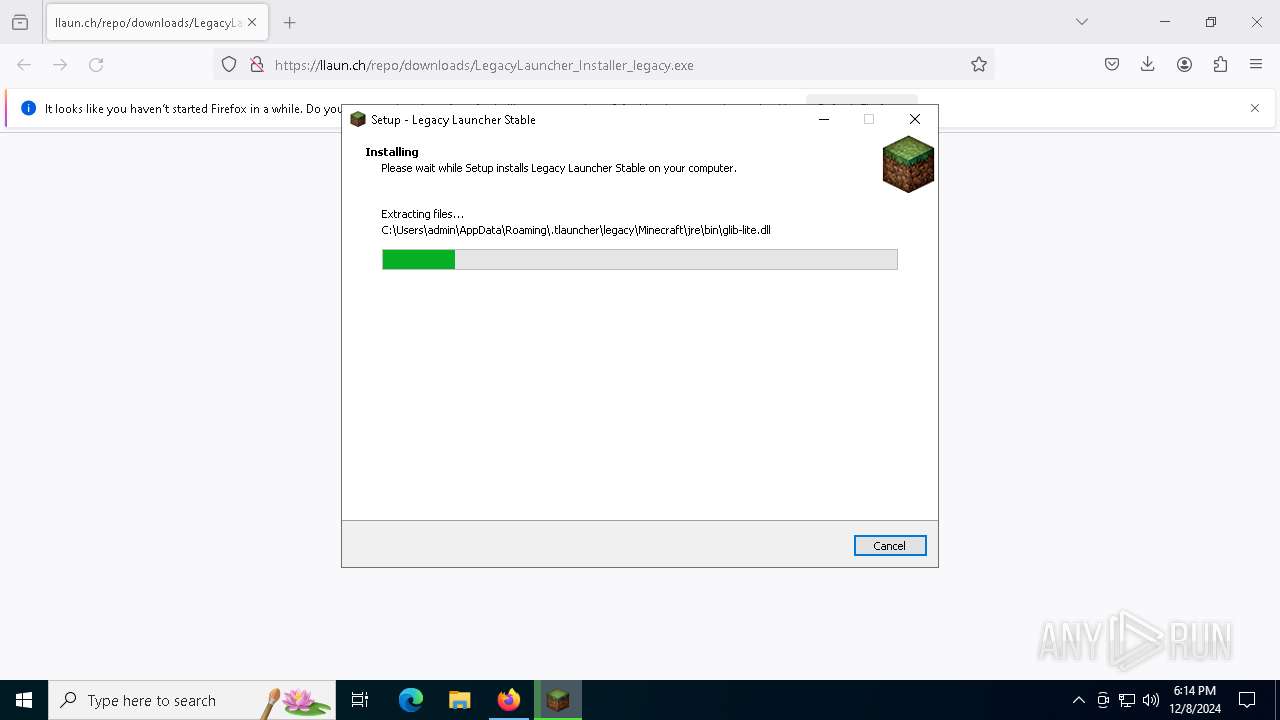
Executable content was dropped or overwritten
- LegacyLauncher_Installer_legacy.exe (PID: 8152)
- java.exe (PID: 396)
- java.exe (PID: 7244)
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
Process drops legitimate windows executable
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
There is functionality for VM detection antiVM strings (YARA)
- java.exe (PID: 7244)
There is functionality for VM detection VMWare (YARA)
- java.exe (PID: 7244)
Reads the Windows owner or organization settings
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
INFO
Application launched itself
- firefox.exe (PID: 6252)
- firefox.exe (PID: 6204)
Executable content was dropped or overwritten
- firefox.exe (PID: 6252)
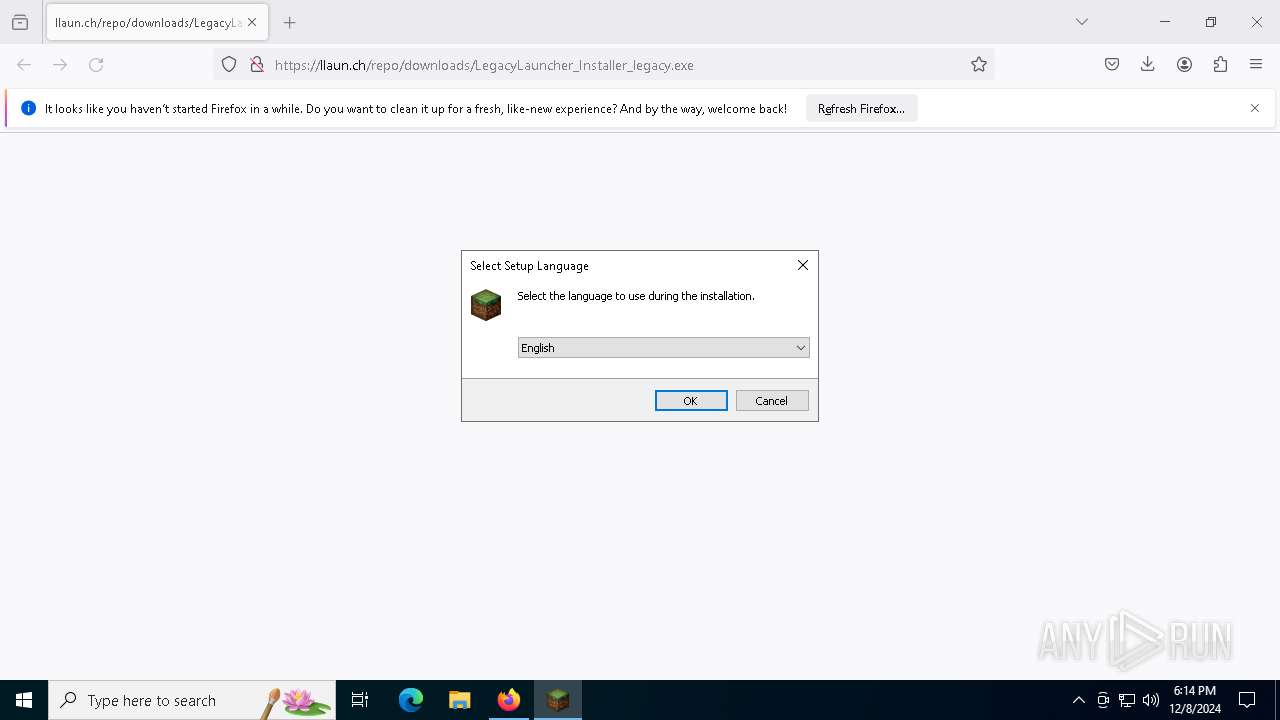
Checks supported languages
- LegacyLauncher_Installer_legacy.exe (PID: 8152)
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
- TL.exe (PID: 3544)
- javaw.exe (PID: 5320)
- java.exe (PID: 396)
- TL.exe (PID: 7672)
- javaw.exe (PID: 4428)
- java.exe (PID: 7244)
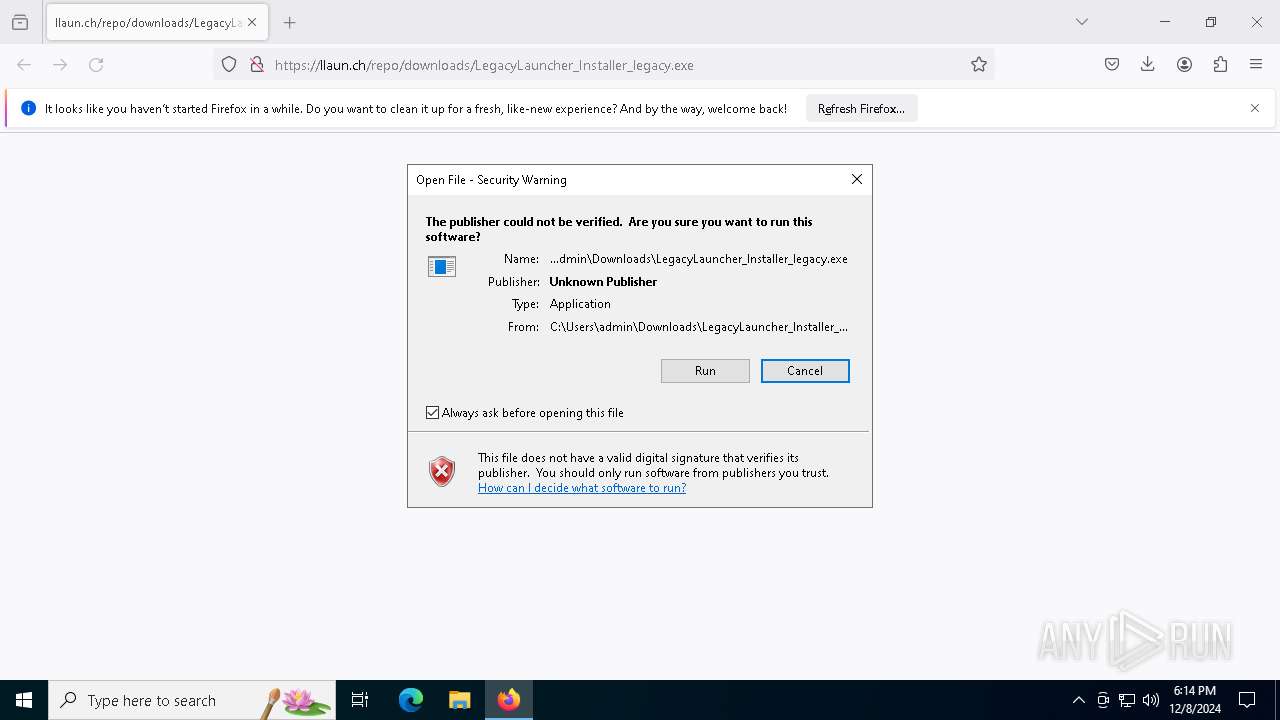
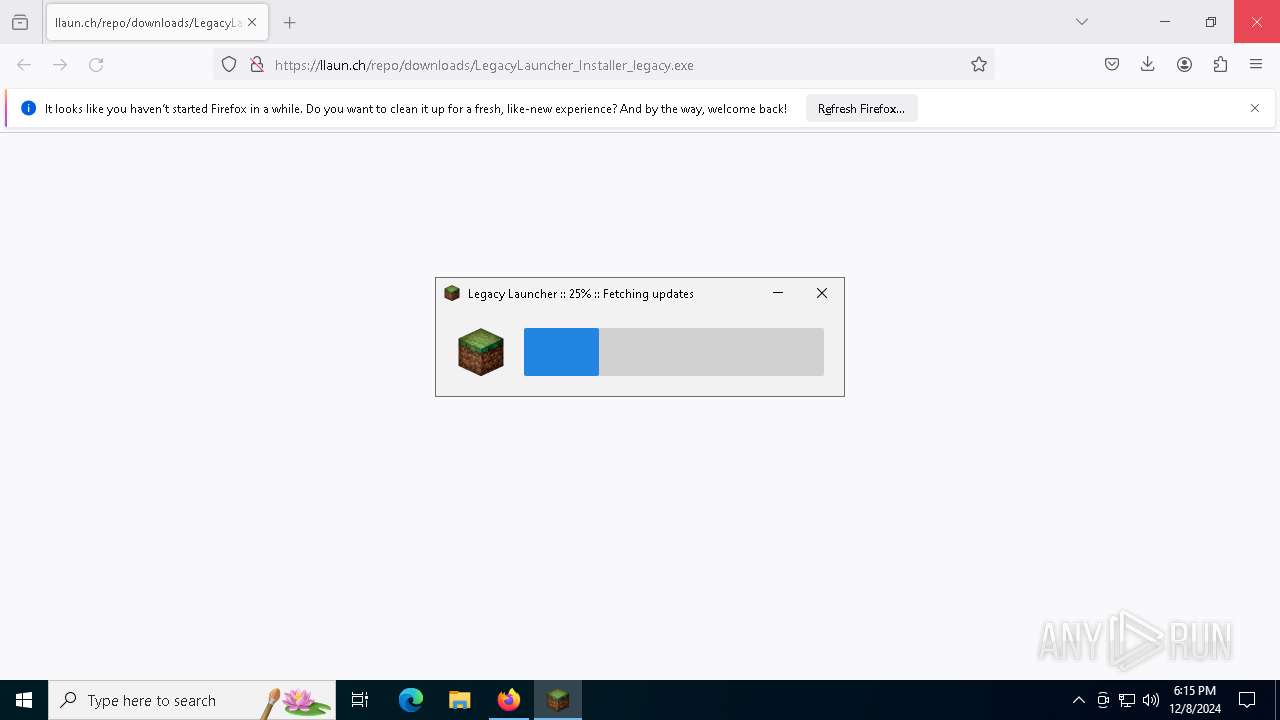
The process uses the downloaded file
- firefox.exe (PID: 6252)
Create files in a temporary directory
- LegacyLauncher_Installer_legacy.exe (PID: 8152)
- javaw.exe (PID: 5320)
- java.exe (PID: 396)
- javaw.exe (PID: 4428)
- java.exe (PID: 7244)
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
Reads CPU info
- javaw.exe (PID: 5320)
- javaw.exe (PID: 4428)
- java.exe (PID: 396)
- java.exe (PID: 7244)
Reads the machine GUID from the registry
- java.exe (PID: 396)
- java.exe (PID: 7244)
Process checks computer location settings
- java.exe (PID: 396)
- java.exe (PID: 7244)
Creates files or folders in the user directory
- java.exe (PID: 396)
- java.exe (PID: 7244)
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
Reads the computer name
- java.exe (PID: 396)
- java.exe (PID: 7244)
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
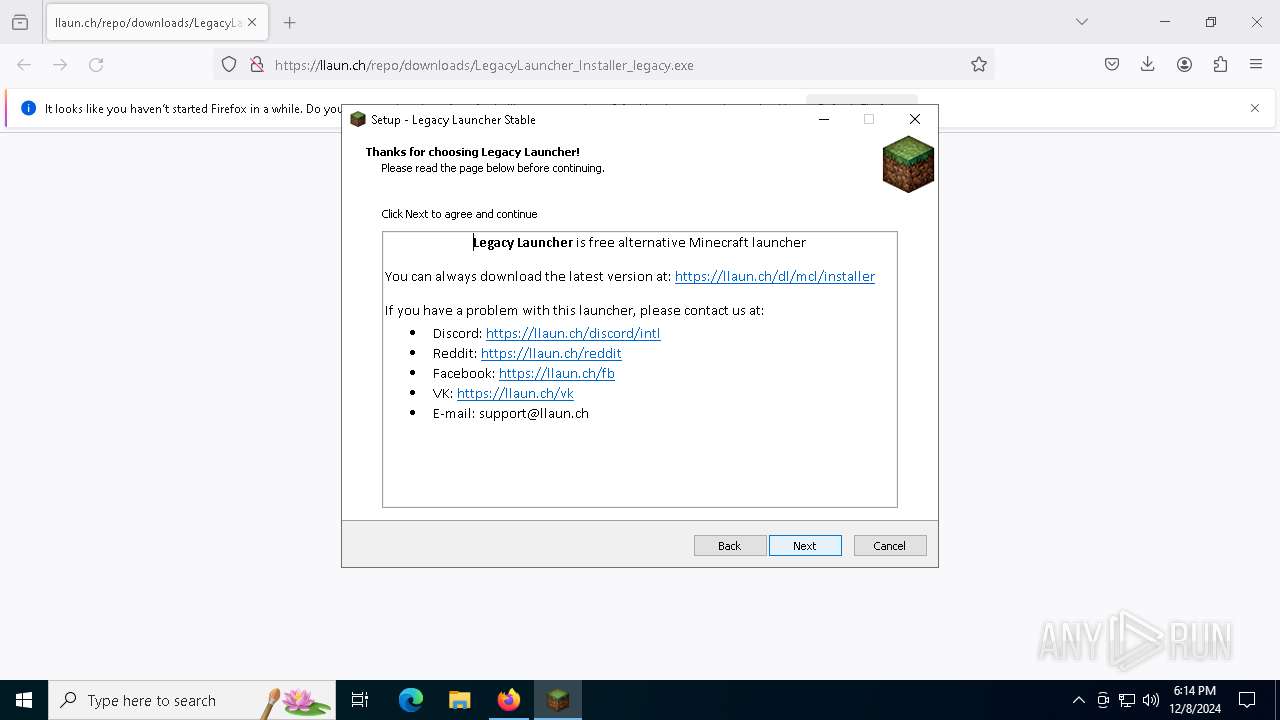
Creates a software uninstall entry
- LegacyLauncher_Installer_legacy.tmp (PID: 8172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
148
Monitored processes
22
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\jre\bin\java.exe -Xmx128m -Dfile.encoding=UTF-8 -Dtlauncher.systemCharset=windows-1252 -Dtlauncher.logFolder=C:\Users\admin\AppData\Roaming\.tlauncher\logs --add-exports java.desktop/sun.awt=javafx.swing -Dtlauncher.bootstrap.restartExec=TL.exe -classpath C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\launcher\bootstrap.jar ru.turikhay.tlauncher.bootstrap.Bootstrap --packageMode windows --targetJar launcher/launcher.jar --targetLibFolder launcher/libraries -- --settings tl.properties | C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\jre\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Azul Systems Inc. Integrity Level: MEDIUM Description: Zulu Platform x64 Architecture Exit code: 0 Version: 17.0.3 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\TL.exe" | C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\TL.exe | — | LegacyLauncher_Installer_legacy.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4428 | "C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\jre\bin\javaw.exe" -Xmx128m -Dtlauncher.bootstrap.restartExec=TL.exe -jar "C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\launcher\bootstrap.jar" | C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\jre\bin\javaw.exe | — | TL.exe | |||||||||||
User: admin Company: Azul Systems Inc. Integrity Level: MEDIUM Description: Zulu Platform x64 Architecture Exit code: 0 Version: 17.0.3 Modules
| |||||||||||||||
| 5320 | "C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\jre\bin\javaw.exe" -Xmx128m -Dtlauncher.bootstrap.restartExec=TL.exe -jar "C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\launcher\bootstrap.jar" | C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\jre\bin\javaw.exe | — | TL.exe | |||||||||||
User: admin Company: Azul Systems Inc. Integrity Level: MEDIUM Description: Zulu Platform x64 Architecture Exit code: 0 Version: 17.0.3 Modules
| |||||||||||||||
| 6204 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://llaun.ch/repo/downloads/LegacyLauncher_Installer_legacy.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6252 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://llaun.ch/repo/downloads/LegacyLauncher_Installer_legacy.exe | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6412 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1816 -parentBuildID 20240213221259 -prefsHandle 1732 -prefMapHandle 1720 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {4868ccbe-7769-48bb-b97f-b97665e154b4} 6252 "\\.\pipe\gecko-crash-server-pipe.6252" 1c0a50f5710 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 6436 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4756 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4772 -prefMapHandle 4676 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {6bde4b94-731b-407b-9103-ec2645de83ae} 6252 "\\.\pipe\gecko-crash-server-pipe.6252" 1c0ad27c710 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
Total events
19 831
Read events
19 809
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6252) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6252) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
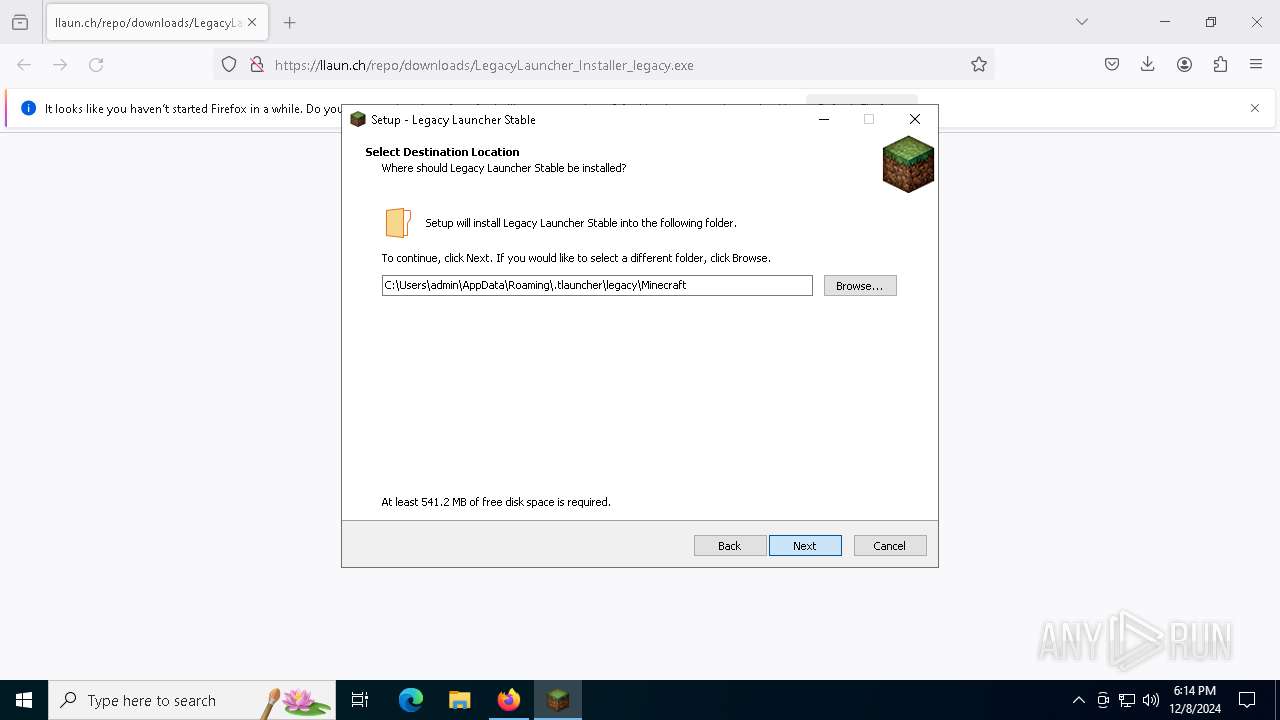
Value: C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Roaming\.tlauncher\legacy\Minecraft\ | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (8172) LegacyLauncher_Installer_legacy.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\71d7e4bb-0c72-3340-984d-9007c5ab9b16_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
Executable files
275
Suspicious files
231
Text files
608
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6252 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6252 | firefox.exe | C:\Users\admin\Downloads\LegacyLauncher_Installer_legacy.vHro6LjL.exe.part | — | |
MD5:— | SHA256:— | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6252 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
83
DNS requests
129
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3568 | svchost.exe | GET | 200 | 23.10.249.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | CH | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.36.225.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CH | binary | 973 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.10.249.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | CH | binary | 1.01 Kb | whitelisted |
3568 | svchost.exe | GET | 200 | 23.36.225.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CH | binary | 973 b | whitelisted |
6252 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6252 | firefox.exe | POST | 200 | 23.10.249.152:80 | http://r11.o.lencr.org/ | CH | binary | 504 b | whitelisted |
6252 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
6252 | firefox.exe | POST | 200 | 23.10.249.152:80 | http://r11.o.lencr.org/ | CH | binary | 504 b | whitelisted |
6252 | firefox.exe | POST | 200 | 142.250.203.99:80 | http://o.pki.goog/wr2 | US | binary | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3568 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3568 | svchost.exe | 23.10.249.24:80 | crl.microsoft.com | Akamai International B.V. | CH | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.10.249.24:80 | crl.microsoft.com | Akamai International B.V. | CH | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.36.225.233:80 | www.microsoft.com | AKAMAI-AS | CH | whitelisted |
3568 | svchost.exe | 23.36.225.233:80 | www.microsoft.com | AKAMAI-AS | CH | whitelisted |
5064 | SearchApp.exe | 2.21.22.144:443 | www.bing.com | Akamai International B.V. | CH | whitelisted |
1944 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
llaun.ch |
| unknown |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2192 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2192 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |