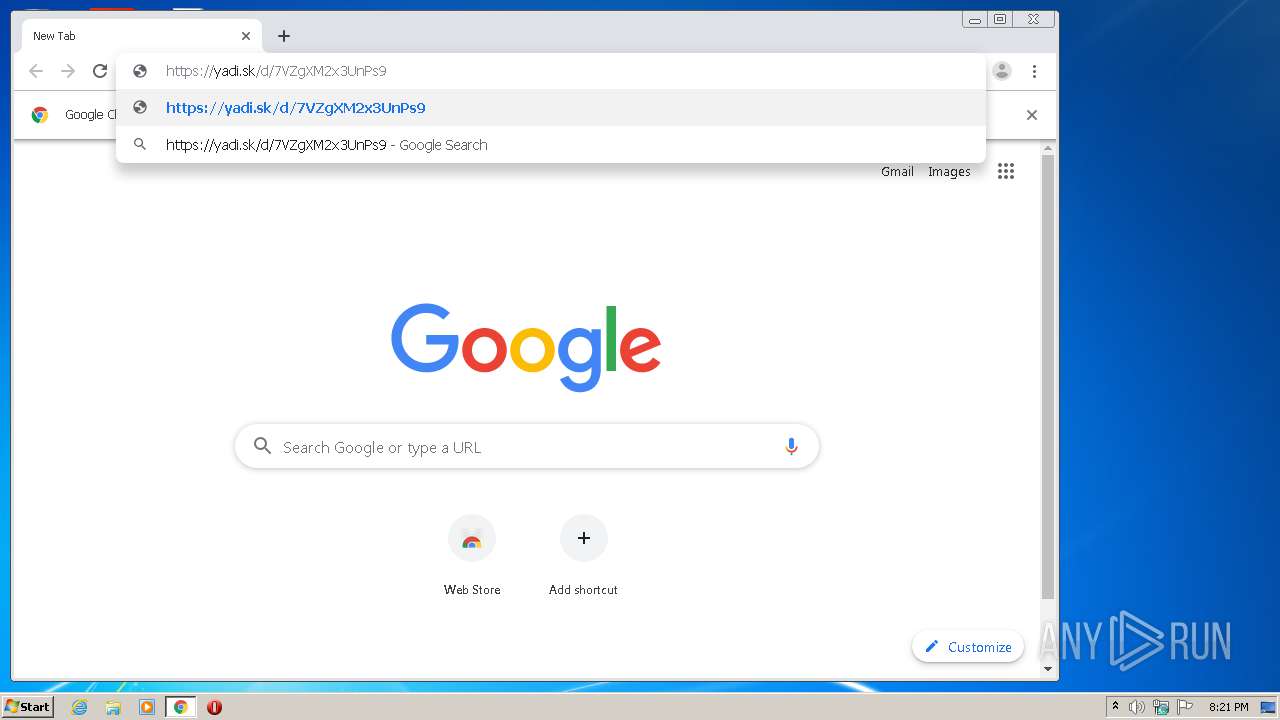
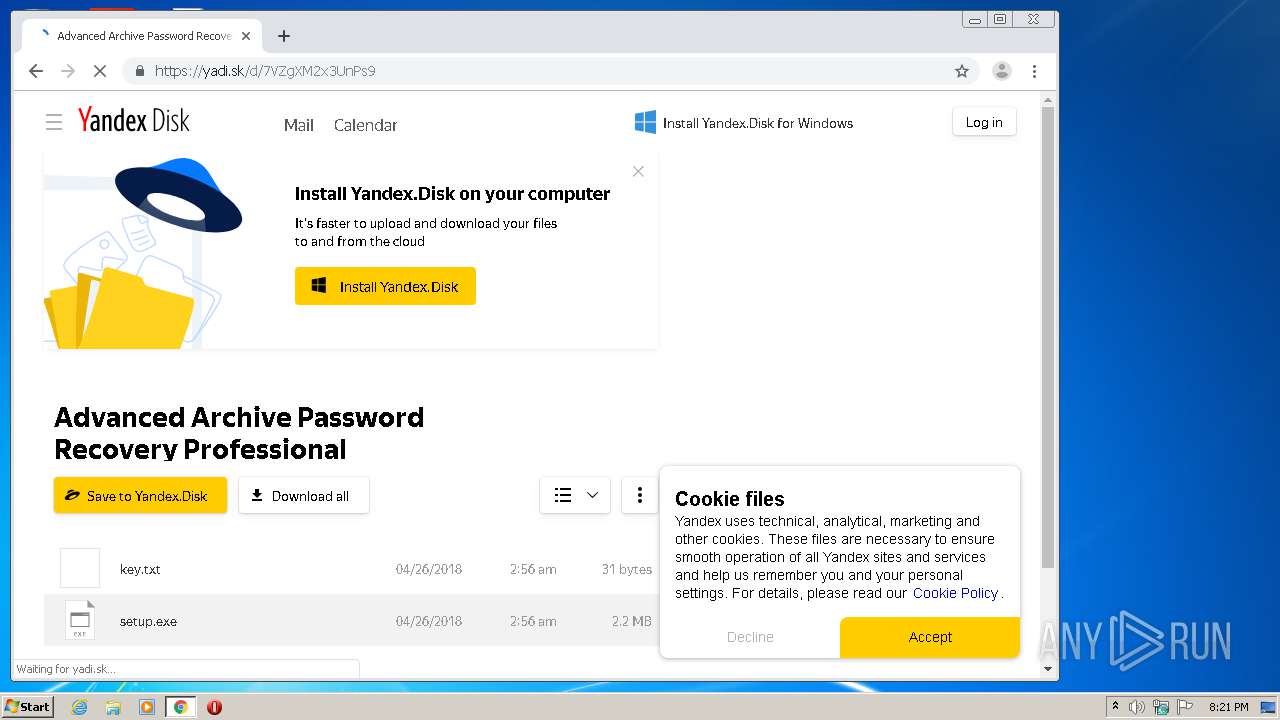
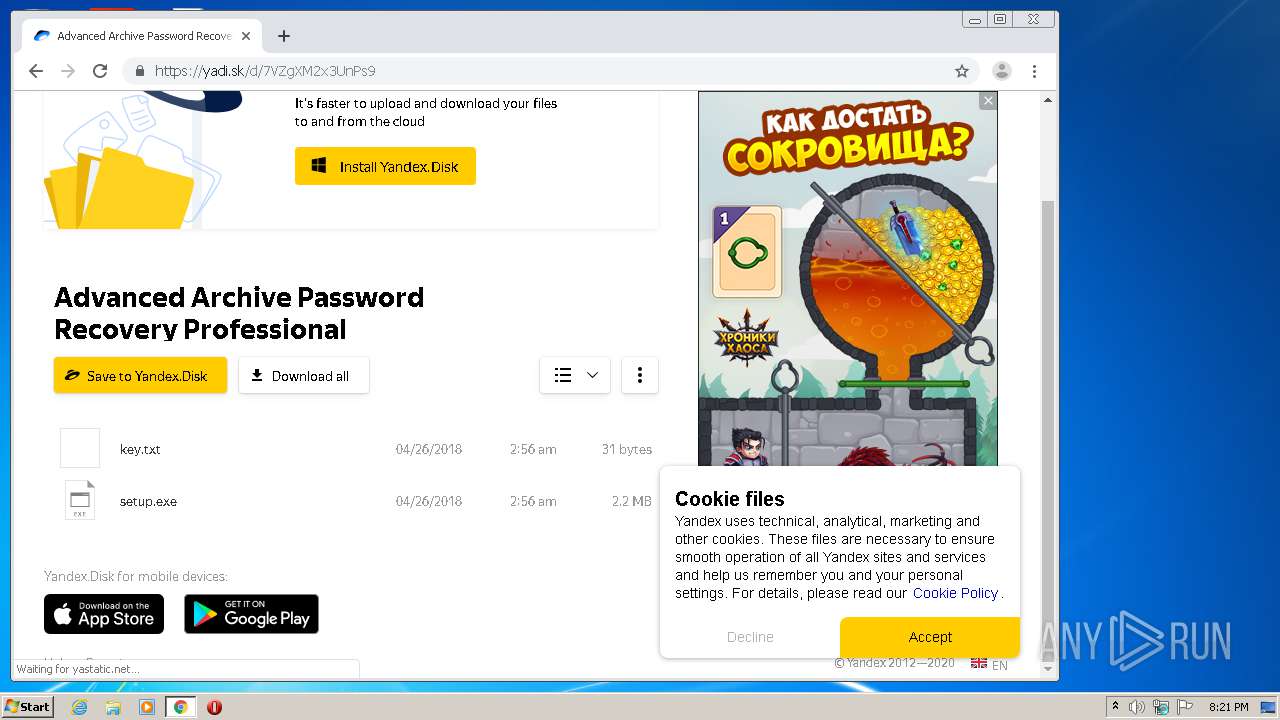
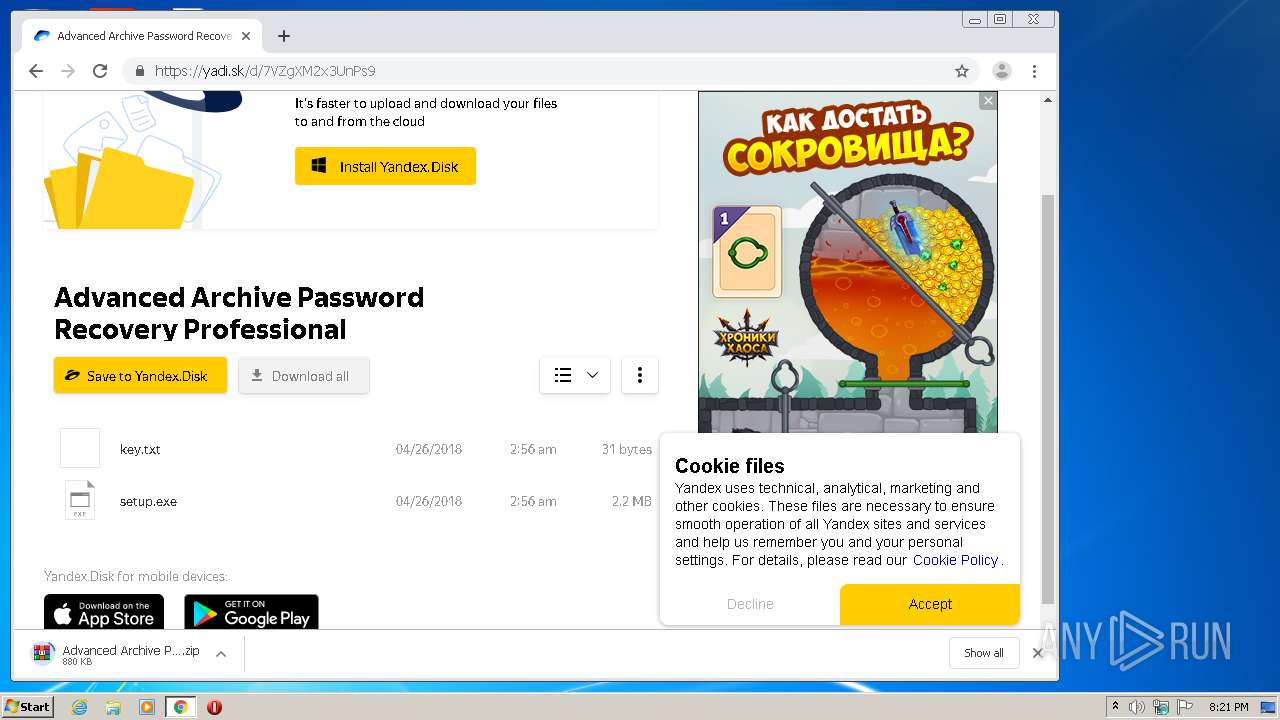
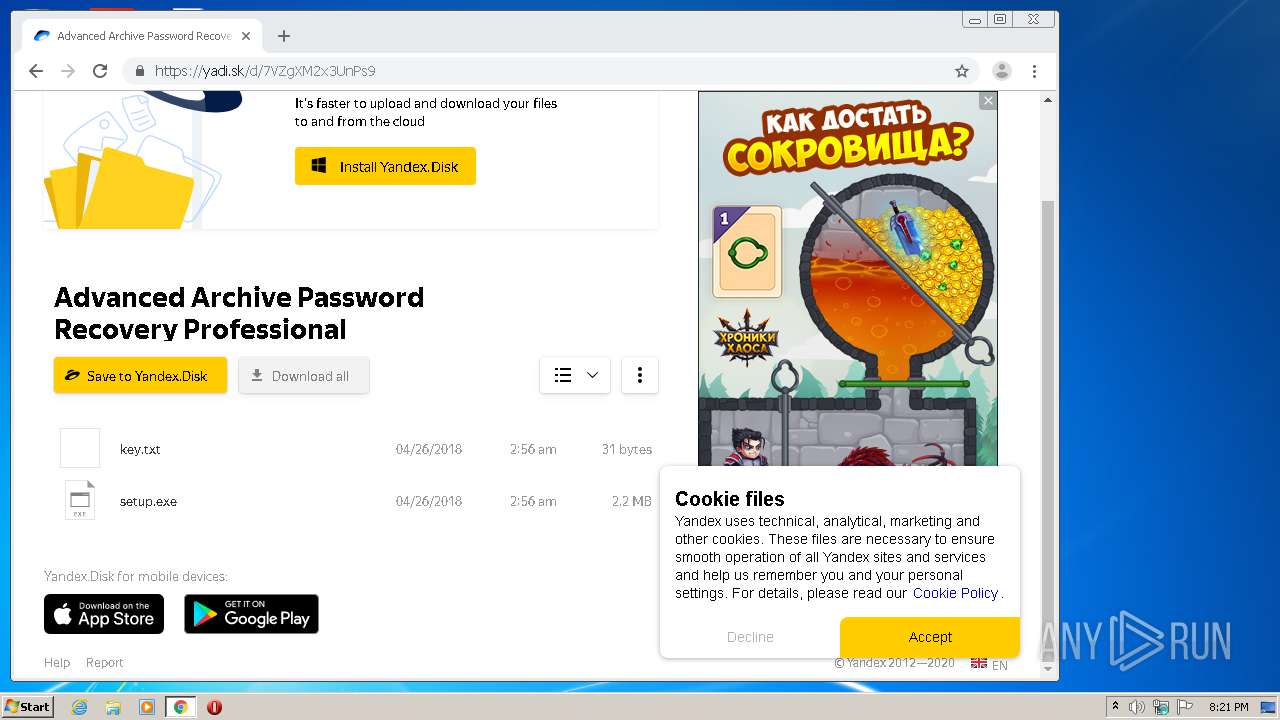
| download: | 7VZgXM2x3UnPs9 |
| Full analysis: | https://app.any.run/tasks/ca2e0d98-e8f2-4ef1-acb2-67ea067871fe |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 19:20:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 0B46323A9868645B65AB2D9A4114EFC4 |
| SHA1: | 6962939E91B449233E59EB3F4E63880F13531CFF |
| SHA256: | 3616E6D6CFB22D5479A3B95BC7723A339F979DBF3213A5CC5E01CD83C45002DC |
| SSDEEP: | 192:6pAenUdOggOUPYnHjBdBdBIAAAqj4SjU4i9eaTWsfrvvkq/:sAiwpgHPQHj33IfQp9ewpfjkq/ |
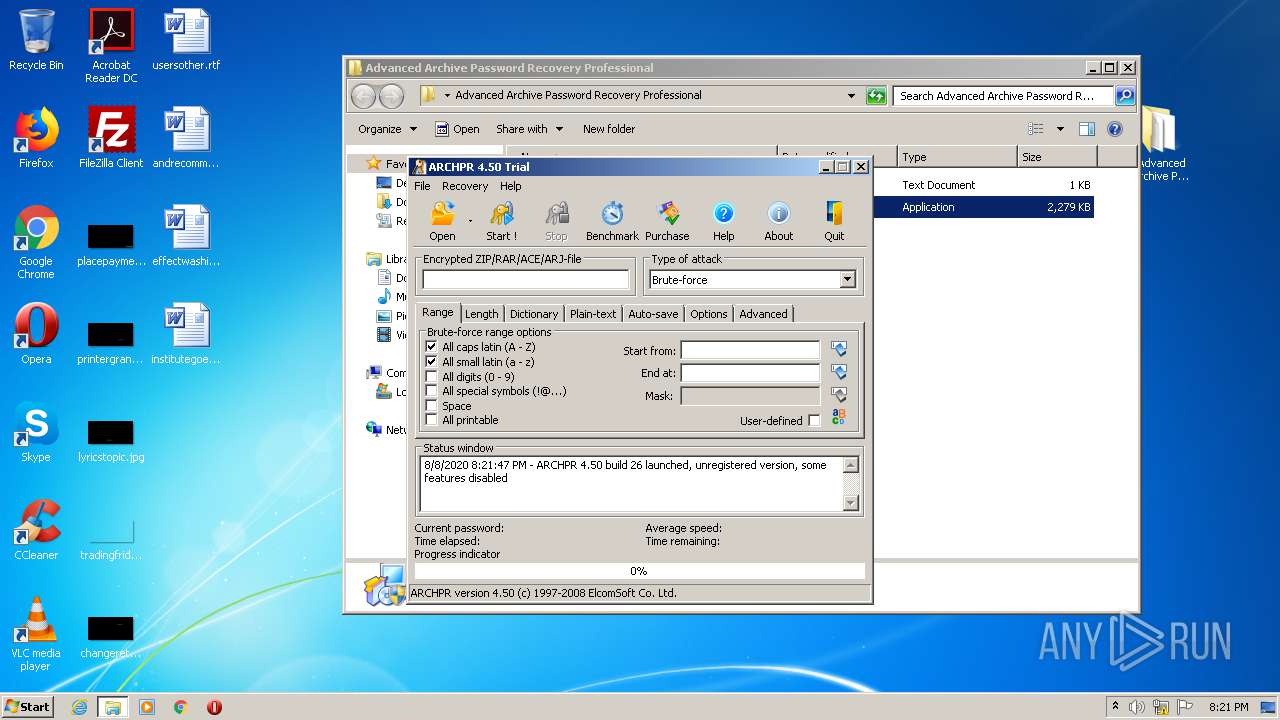
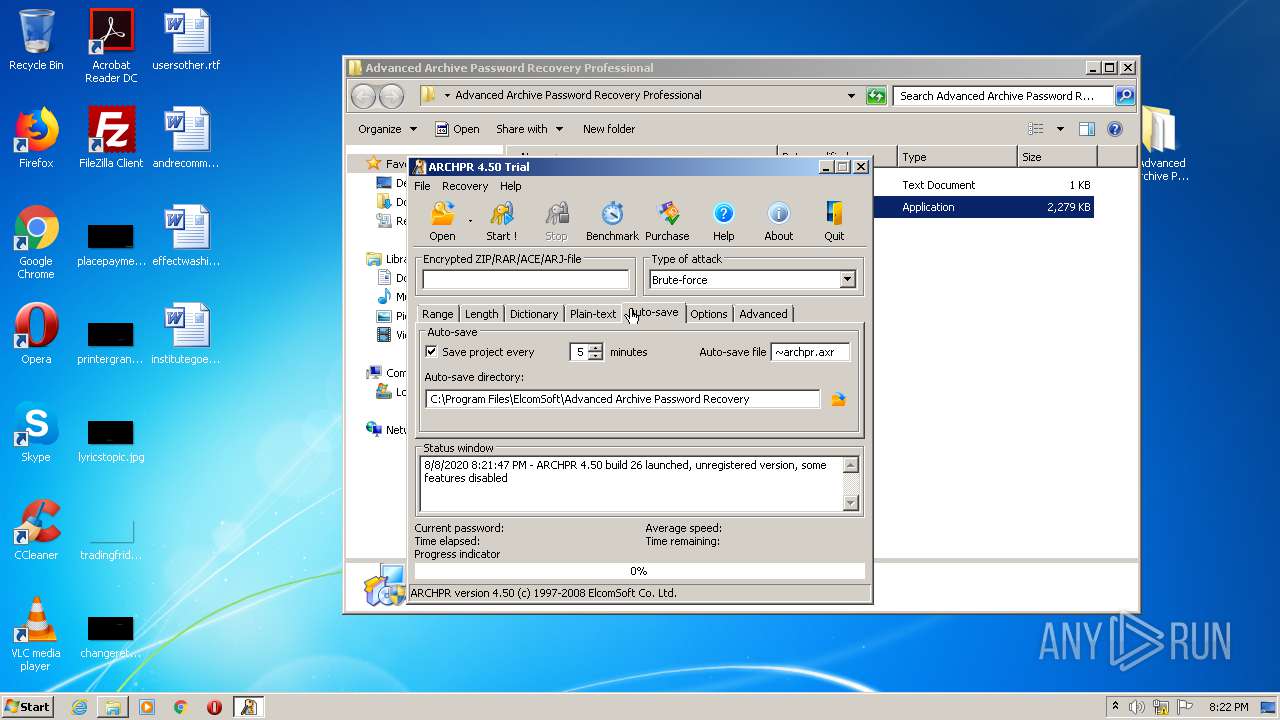
MALICIOUS
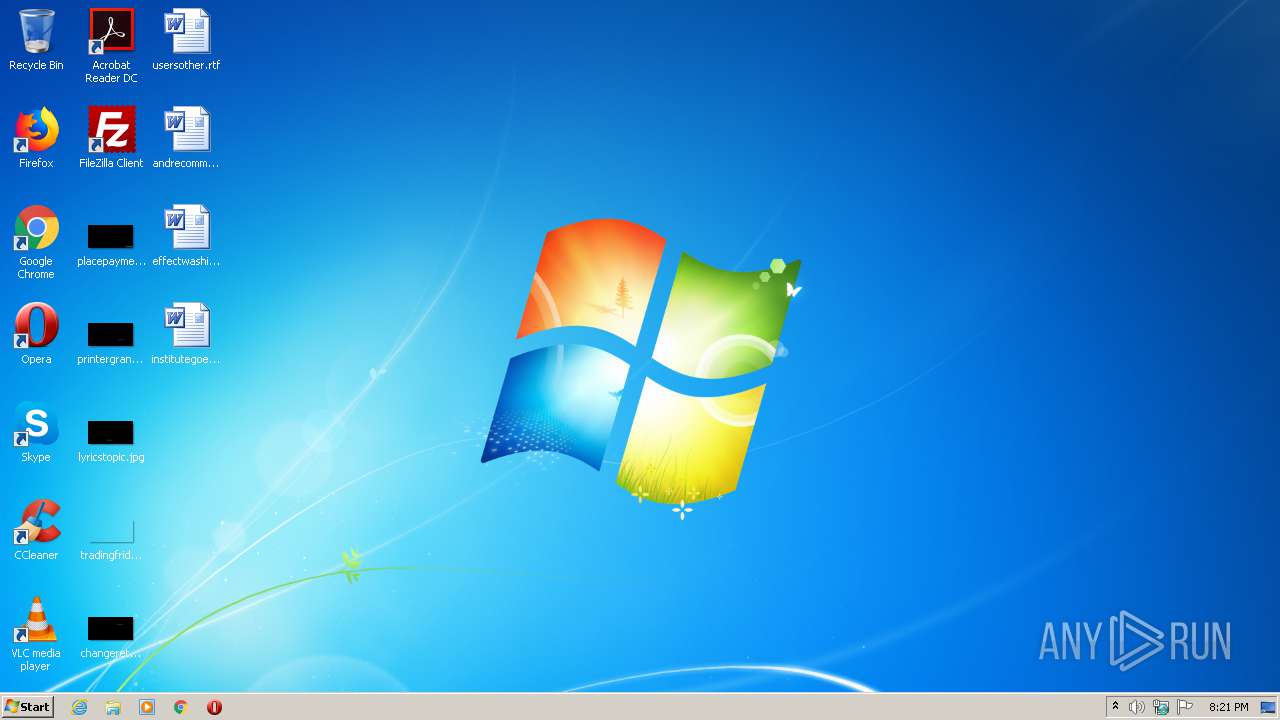
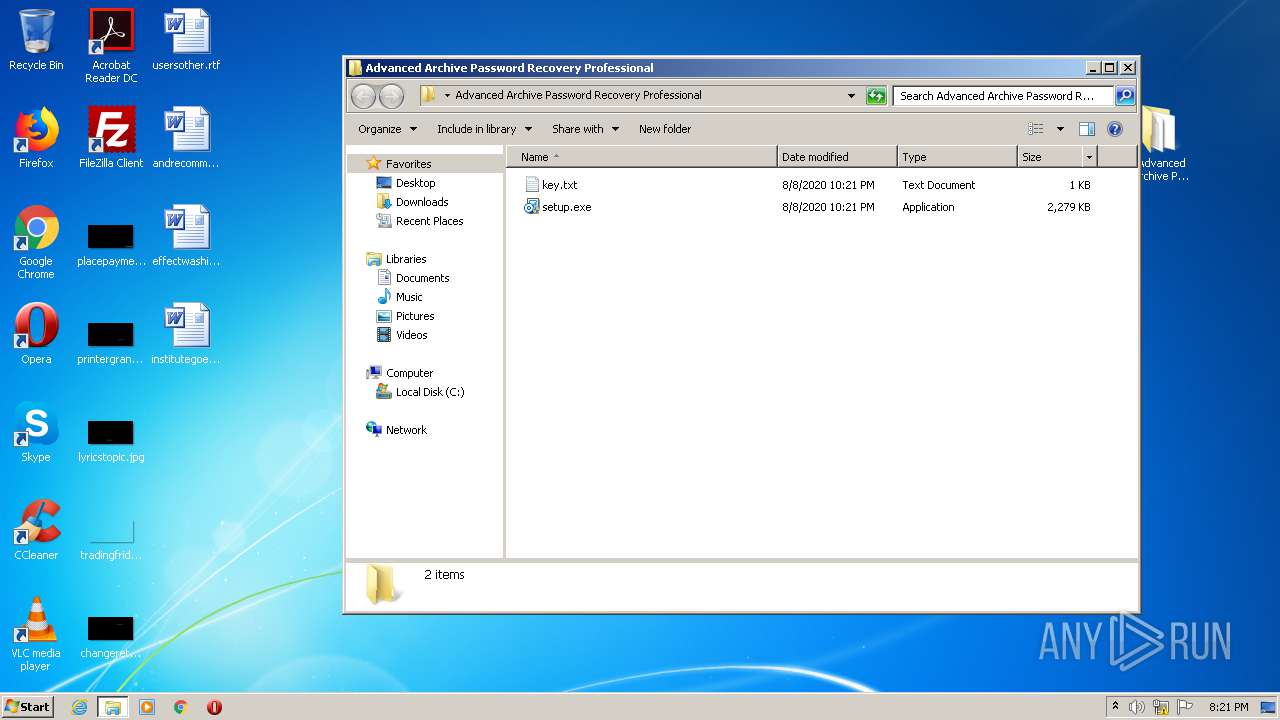
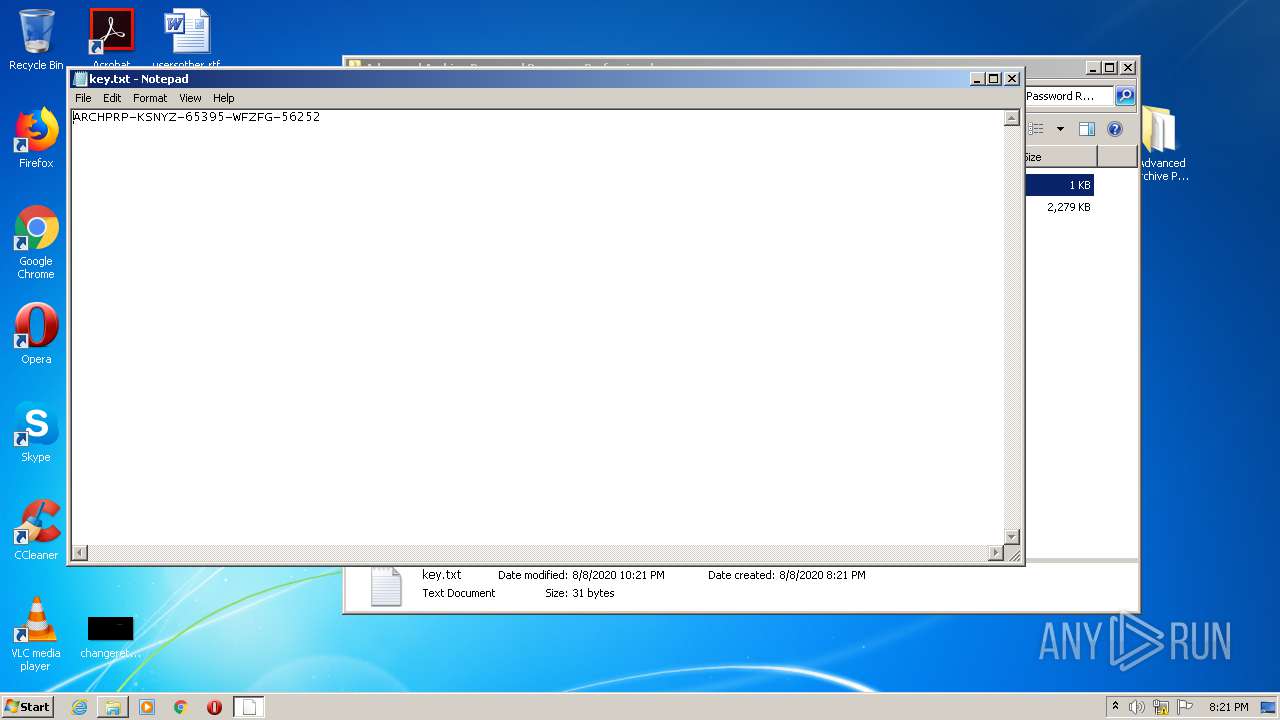
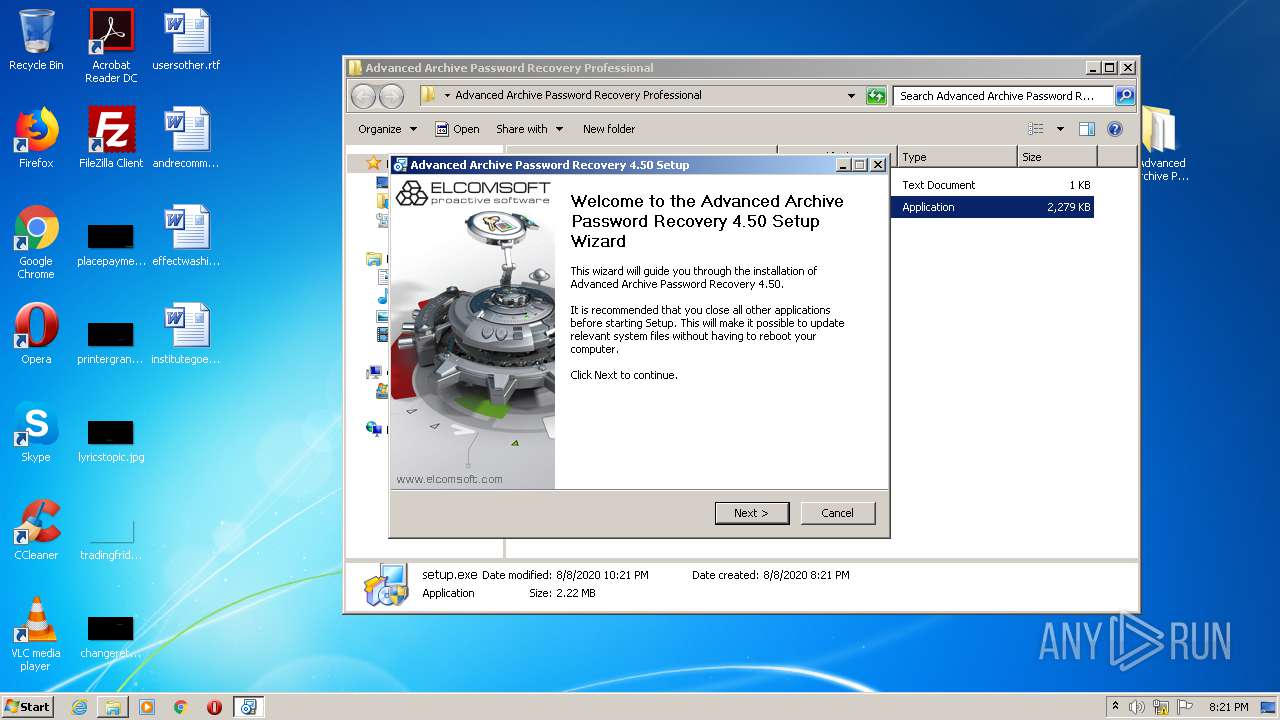
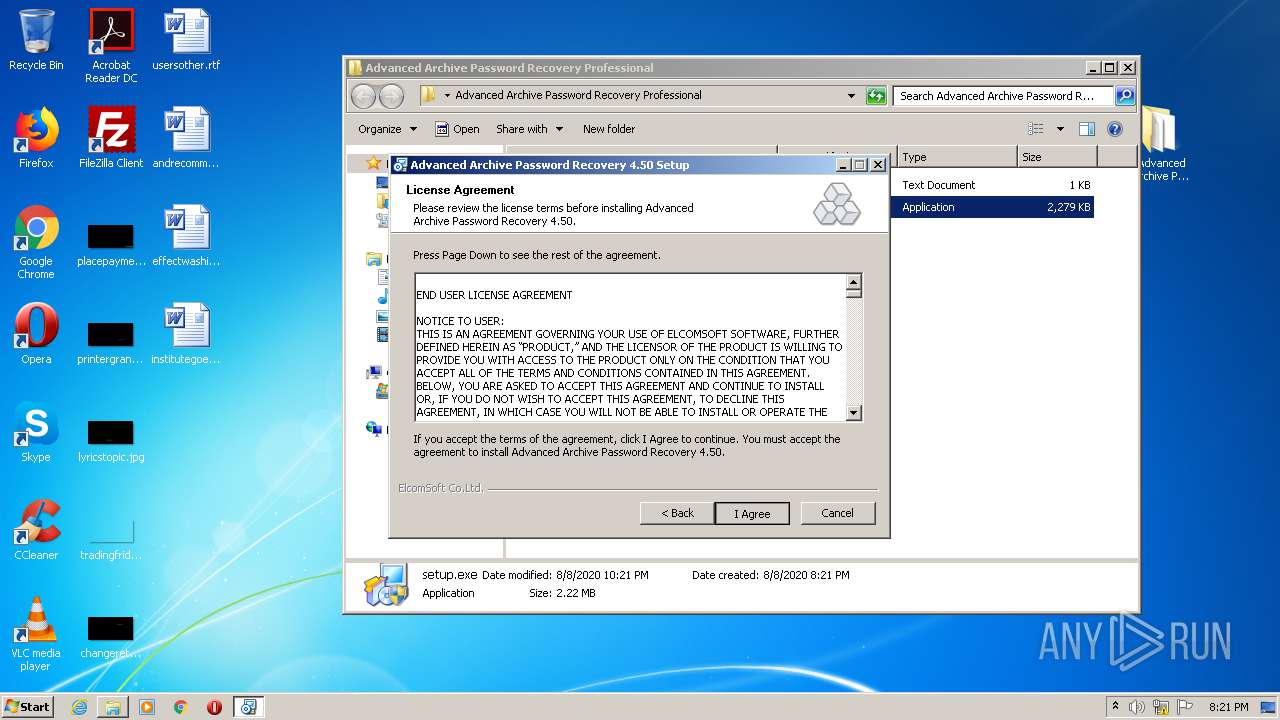
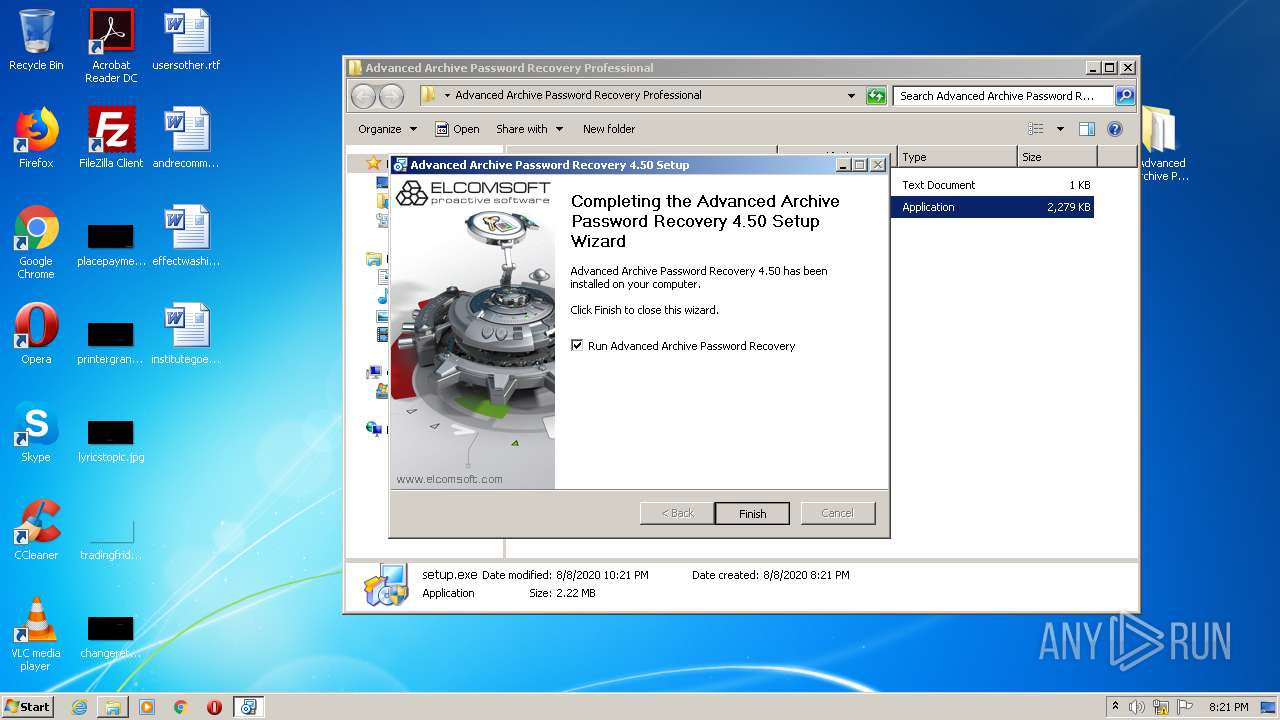
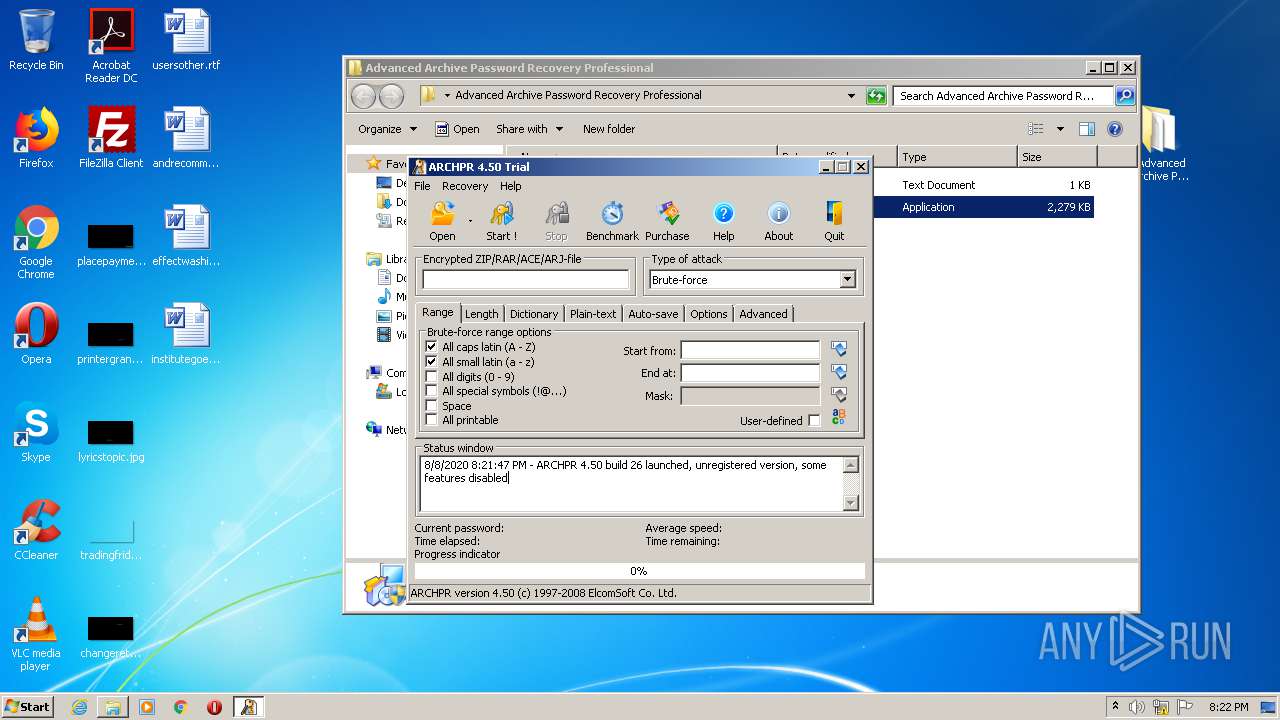
Application was dropped or rewritten from another process
- setup.exe (PID: 3260)
- setup.exe (PID: 3424)
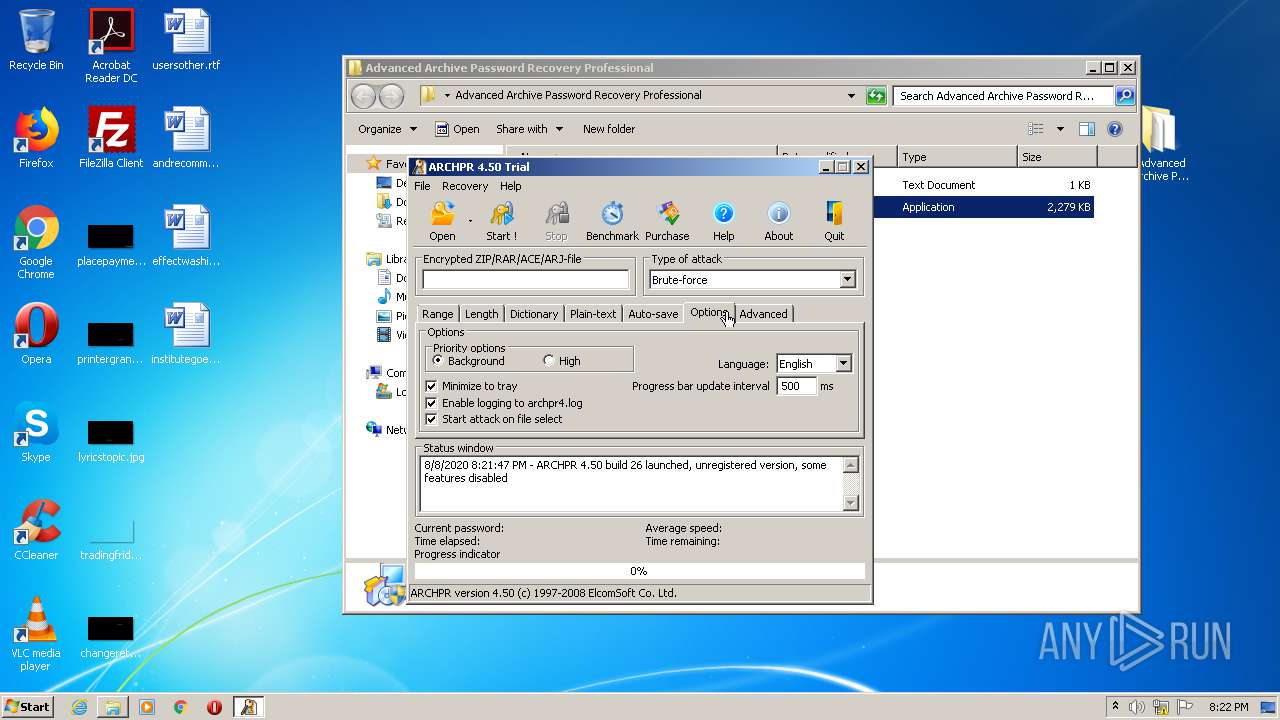
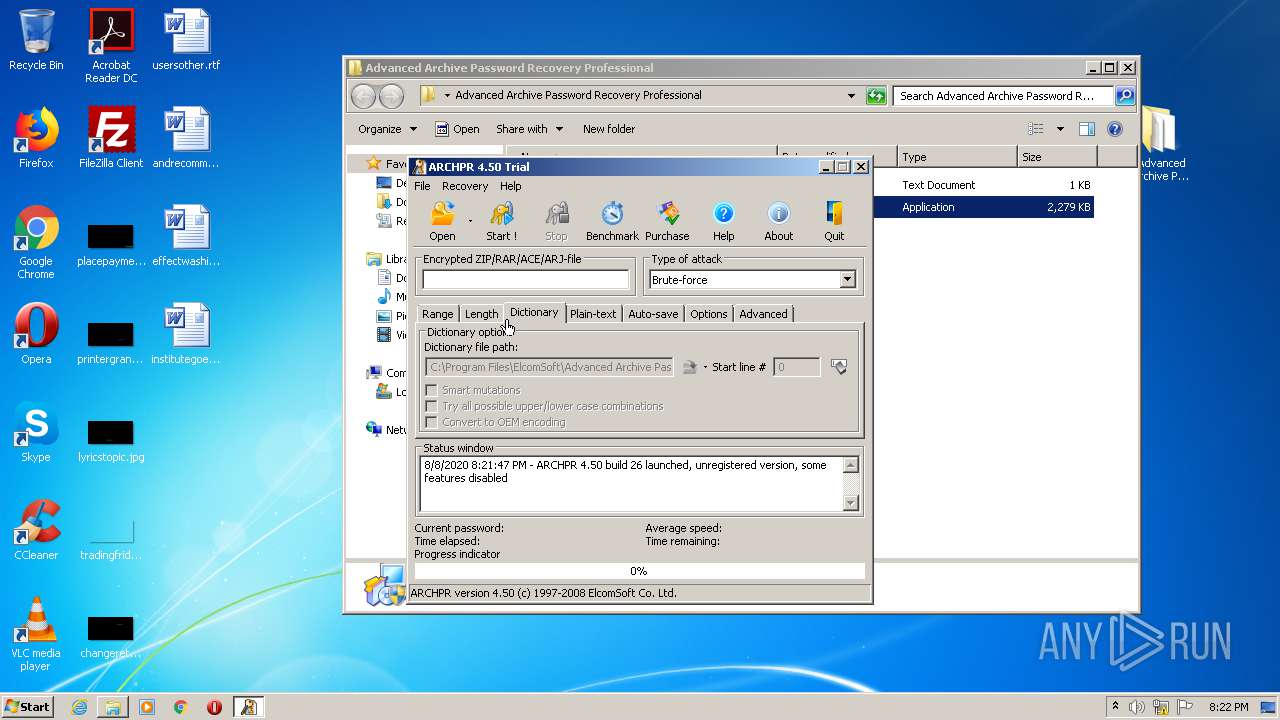
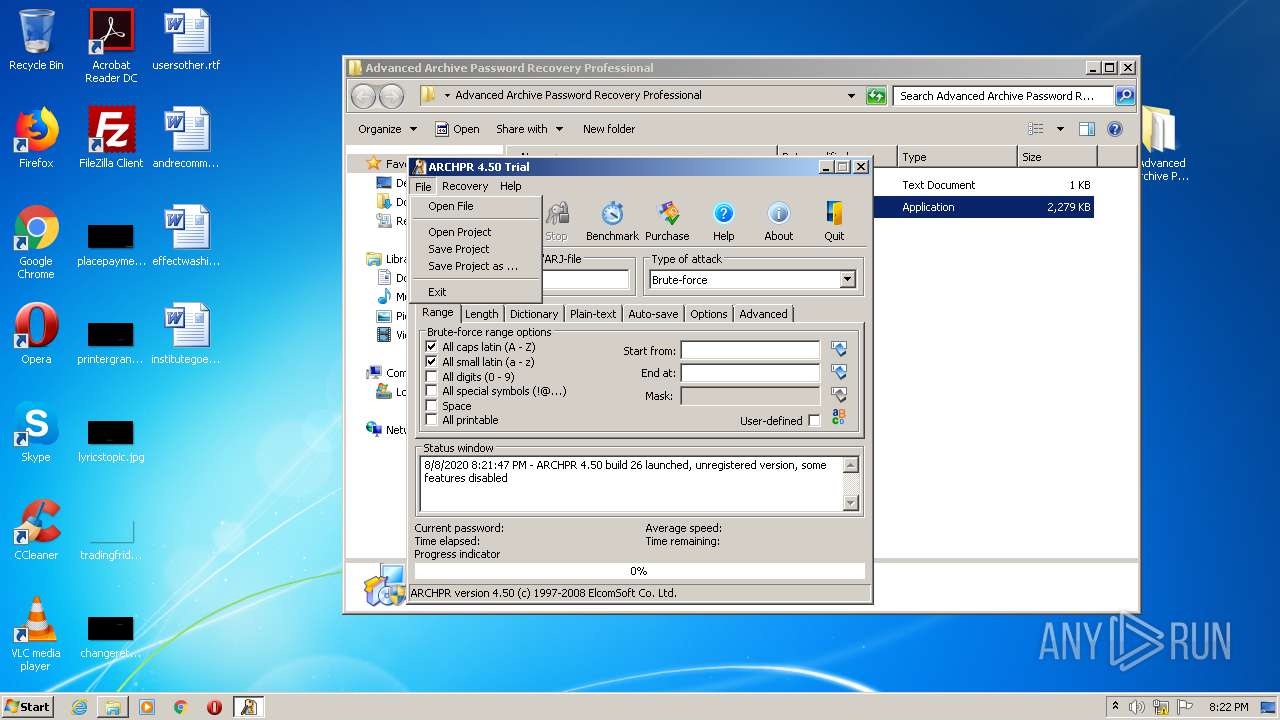
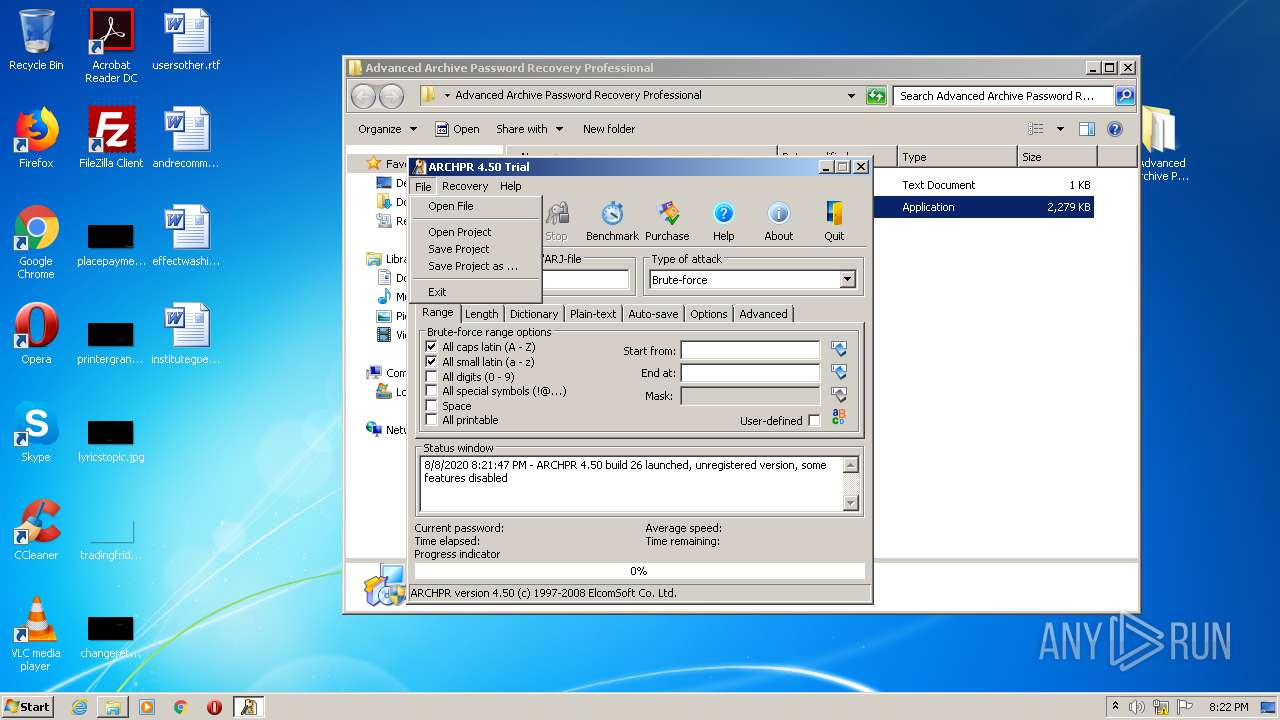
- archpr.exe (PID: 3880)
Loads dropped or rewritten executable
- setup.exe (PID: 3260)
- archpr.exe (PID: 3880)
SUSPICIOUS
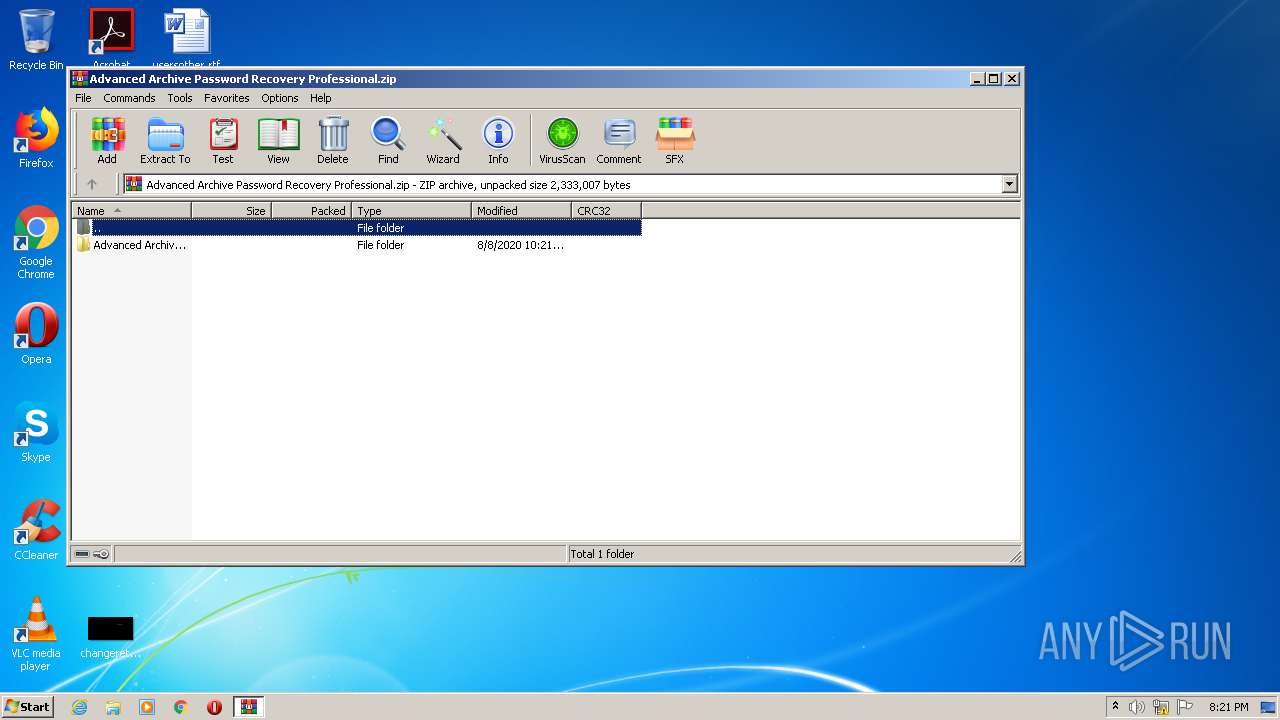
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2284)
- setup.exe (PID: 3260)
Creates files in the program directory
- setup.exe (PID: 3260)
- archpr.exe (PID: 3880)
Low-level read access rights to disk partition
- archpr.exe (PID: 3880)
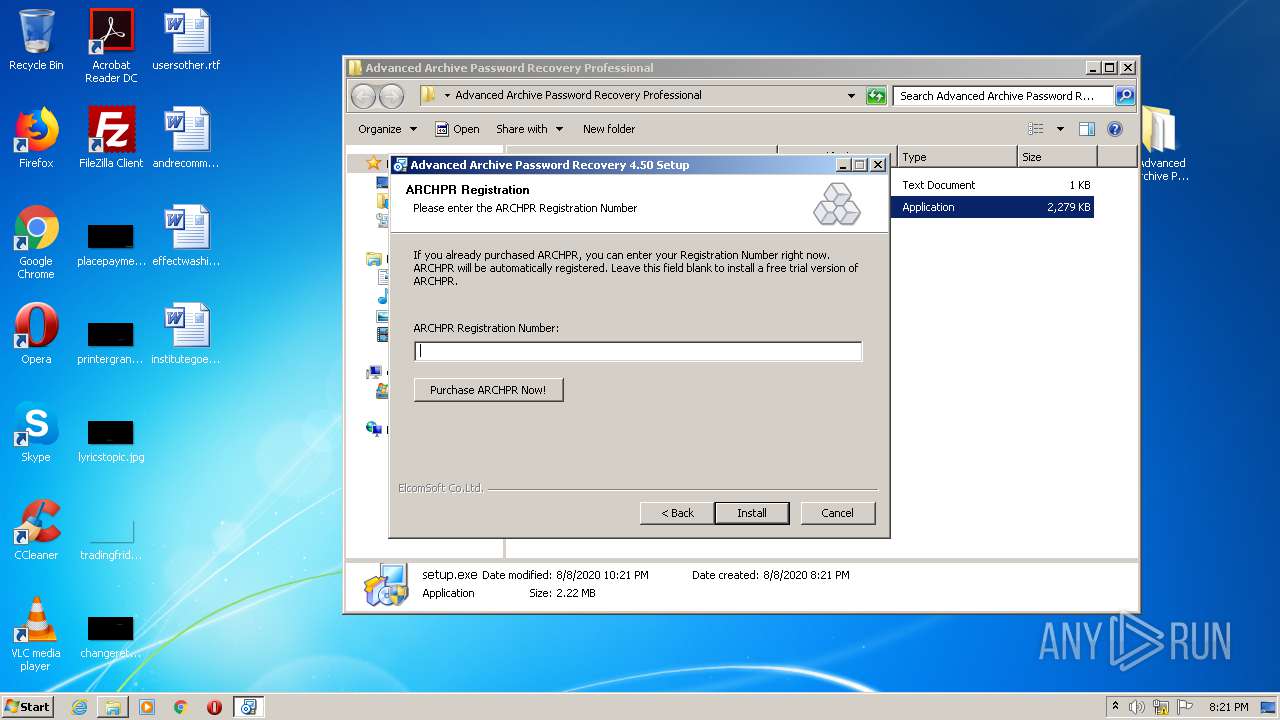
Creates a software uninstall entry
- setup.exe (PID: 3260)
Creates files in the user directory
- setup.exe (PID: 3260)
INFO
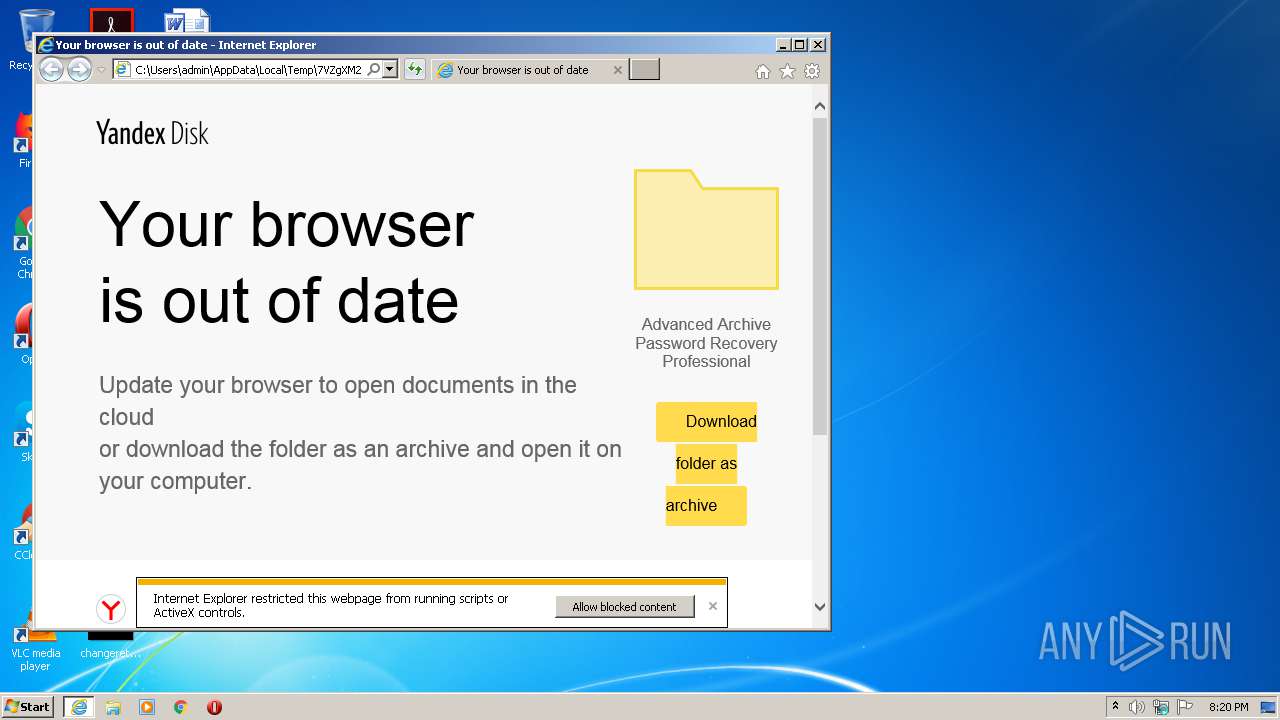
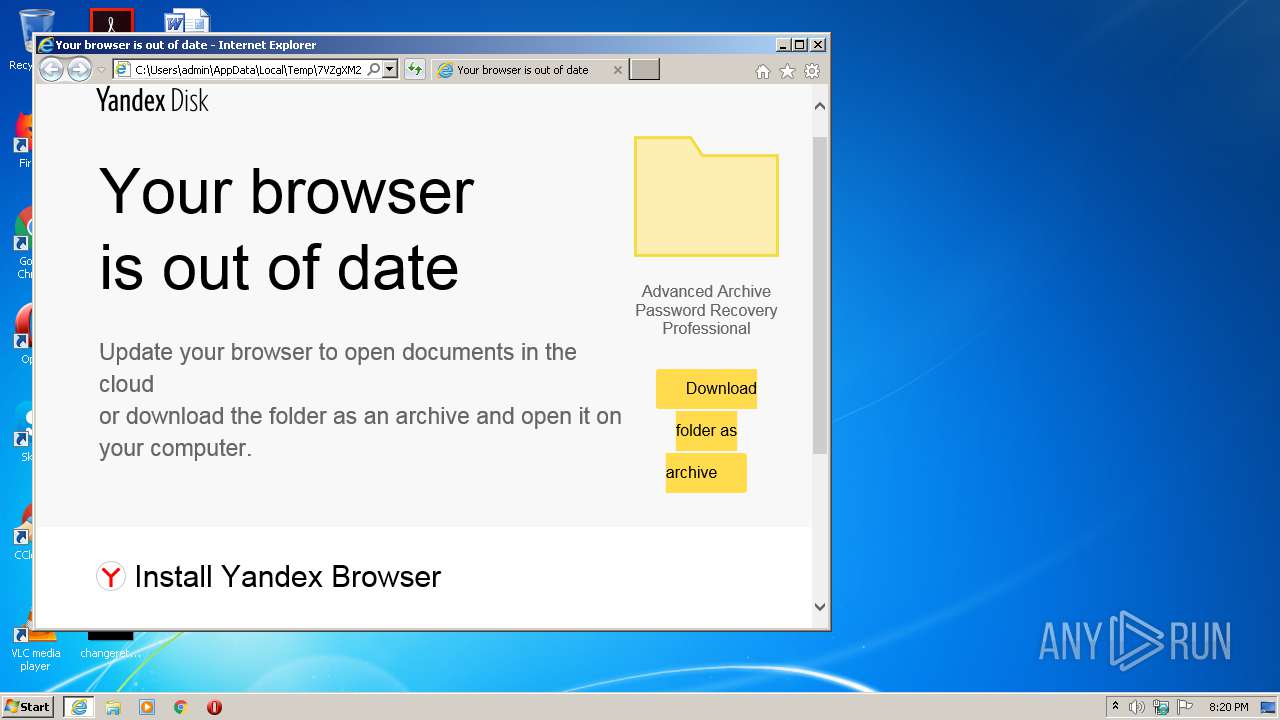
Changes internet zones settings
- iexplore.exe (PID: 900)
Reads Internet Cache Settings
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 900)
- chrome.exe (PID: 780)
Adds / modifies Windows certificates
- iexplore.exe (PID: 684)
- iexplore.exe (PID: 900)
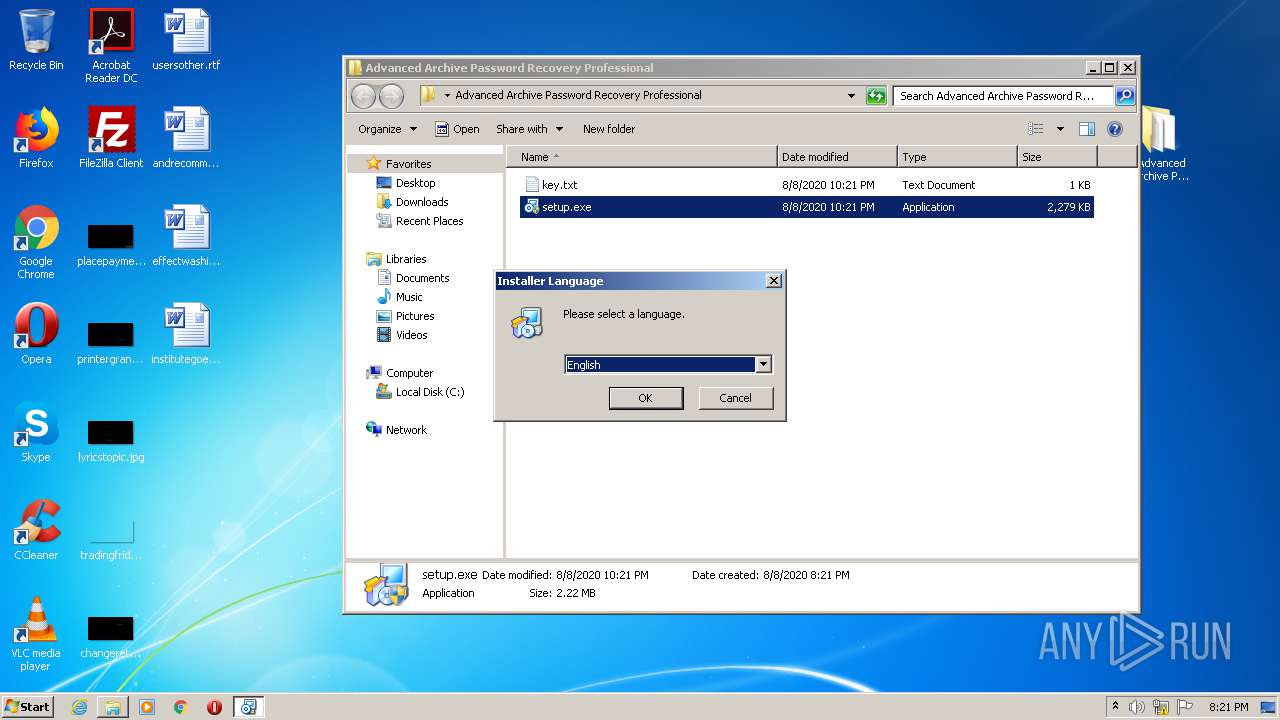
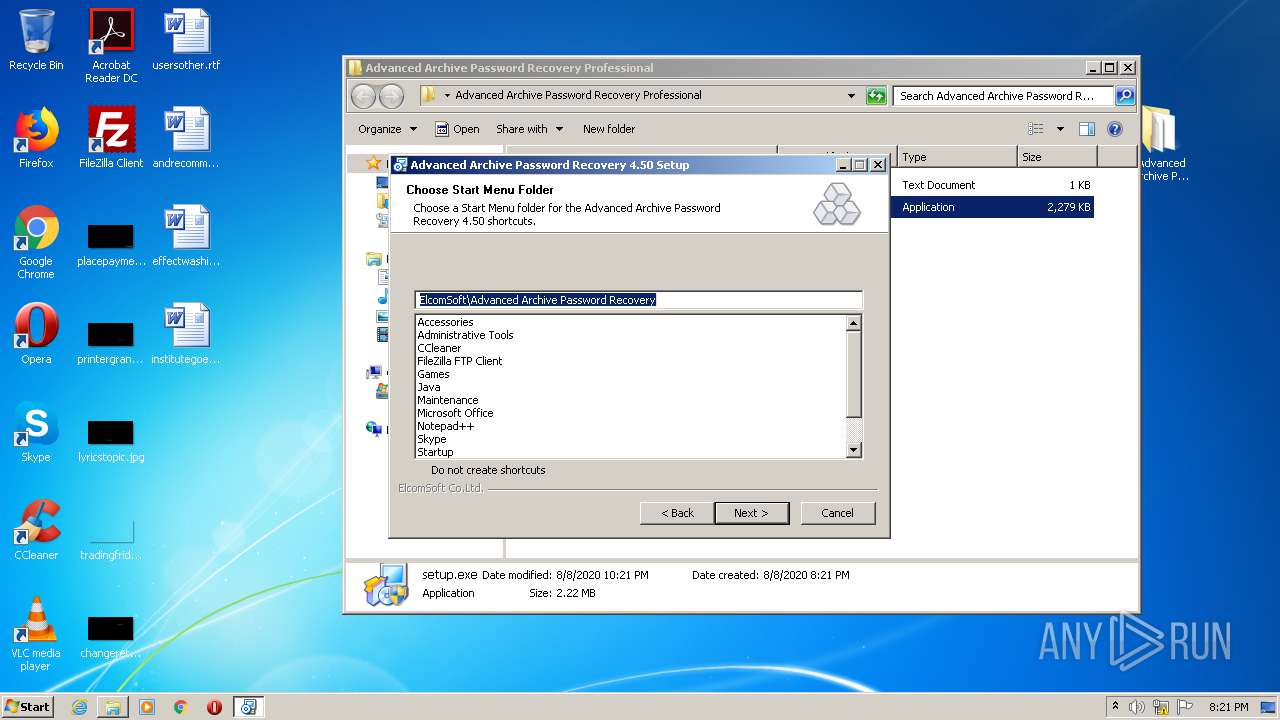
Manual execution by user
- chrome.exe (PID: 780)
- NOTEPAD.EXE (PID: 3636)
- setup.exe (PID: 3424)
- setup.exe (PID: 3260)
Reads settings of System Certificates
- iexplore.exe (PID: 684)
- chrome.exe (PID: 3692)
- iexplore.exe (PID: 900)
Reads the hosts file
- chrome.exe (PID: 3692)
- chrome.exe (PID: 780)
Changes settings of System certificates
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 684)
Application launched itself
- iexplore.exe (PID: 900)
- chrome.exe (PID: 780)
- iexplore.exe (PID: 684)
Reads internet explorer settings
- iexplore.exe (PID: 684)
Creates files in the user directory
- iexplore.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| viewport: | width=device-width,initial-scale=1 |
| Title: | Your browser is out of date |
Total processes
74
Monitored processes
31
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,9732694143685906085,5966124174191942858,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15116183926410070629 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:900 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9732694143685906085,5966124174191942858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11831018919847856421 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\7VZgXM2x3UnPs9.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9732694143685906085,5966124174191942858,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17304371900933103724 --mojo-platform-channel-handle=3424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9732694143685906085,5966124174191942858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8123841137075362829 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9732694143685906085,5966124174191942858,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4139884307695773592 --mojo-platform-channel-handle=3688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9732694143685906085,5966124174191942858,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11526717383662726508 --mojo-platform-channel-handle=3348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
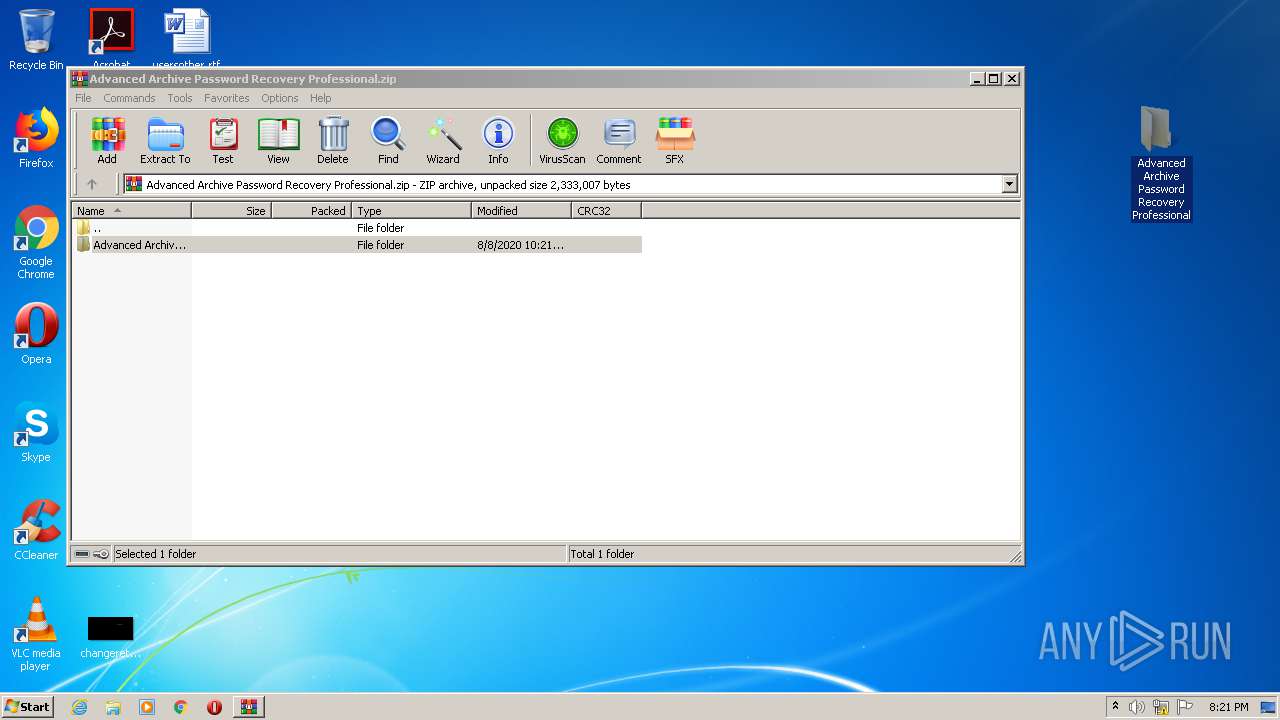
| 2284 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Advanced Archive Password Recovery Professional.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 192
Read events
1 884
Write events
294
Delete events
14
Modification events
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 212171836 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30830009 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
9
Suspicious files
89
Text files
144
Unknown types
25
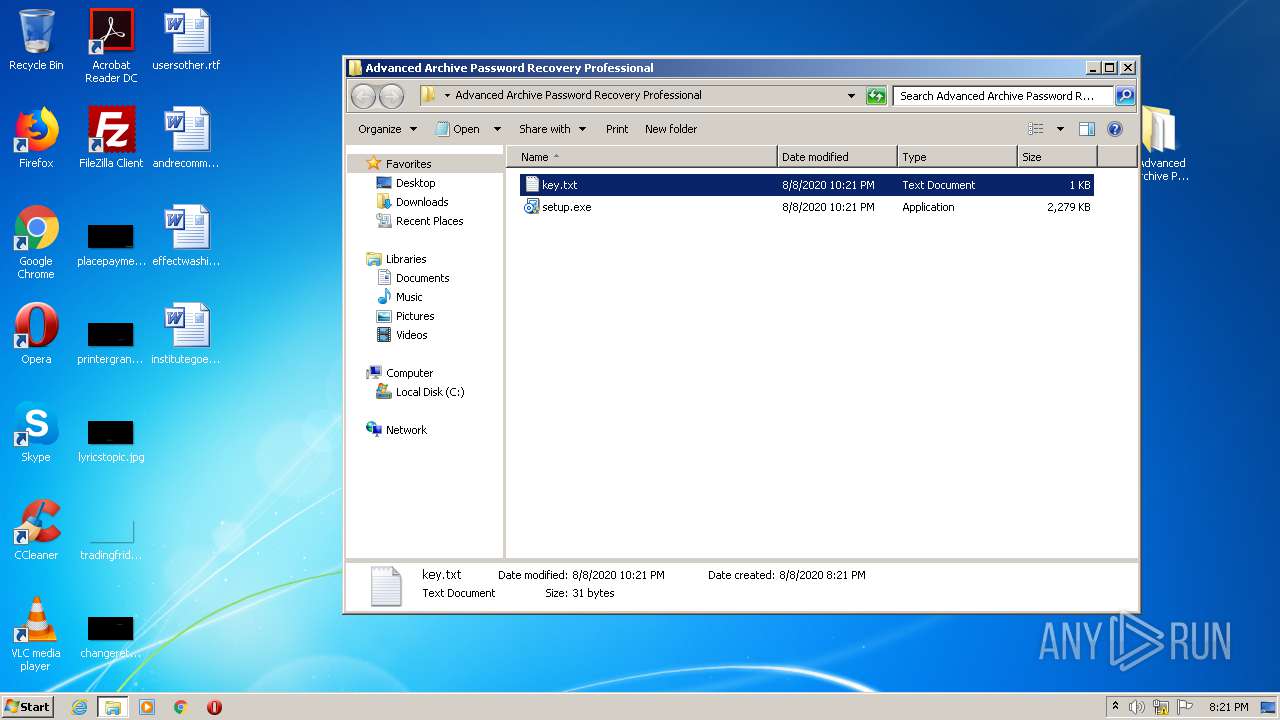
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC573.tmp | — | |
MD5:— | SHA256:— | |||
| 684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC574.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver37D6.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB0A5D0982FEE3E95.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF79D23B0F4DF040C8.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2269651637E41325.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3AB3.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3AB4.tmp | — | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver3AD4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
94
DNS requests
71
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
684 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.58 Kb | whitelisted |
684 | iexplore.exe | GET | 200 | 5.45.205.241:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGo64gHWQVFU7F1yeyNqDBI%3D | RU | der | 1.48 Kb | whitelisted |
684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
684 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | US | der | 1.63 Kb | whitelisted |
684 | iexplore.exe | GET | 200 | 5.45.205.241:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGo64gHWQVFU7F1yeyNqDBI%3D | RU | der | 1.48 Kb | whitelisted |
684 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | US | der | 1.63 Kb | whitelisted |
900 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
684 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.58 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
684 | iexplore.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
684 | iexplore.exe | 5.45.205.241:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
684 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
900 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
900 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3692 | chrome.exe | 77.88.21.127:443 | downloader.disk.yandex.ru | YANDEX LLC | RU | whitelisted |
3692 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3692 | chrome.exe | 87.250.250.50:443 | yadi.sk | YANDEX LLC | RU | whitelisted |
3692 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3692 | chrome.exe | 216.58.207.78:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mc.yandex.ru |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
yandex.ocsp-responder.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |