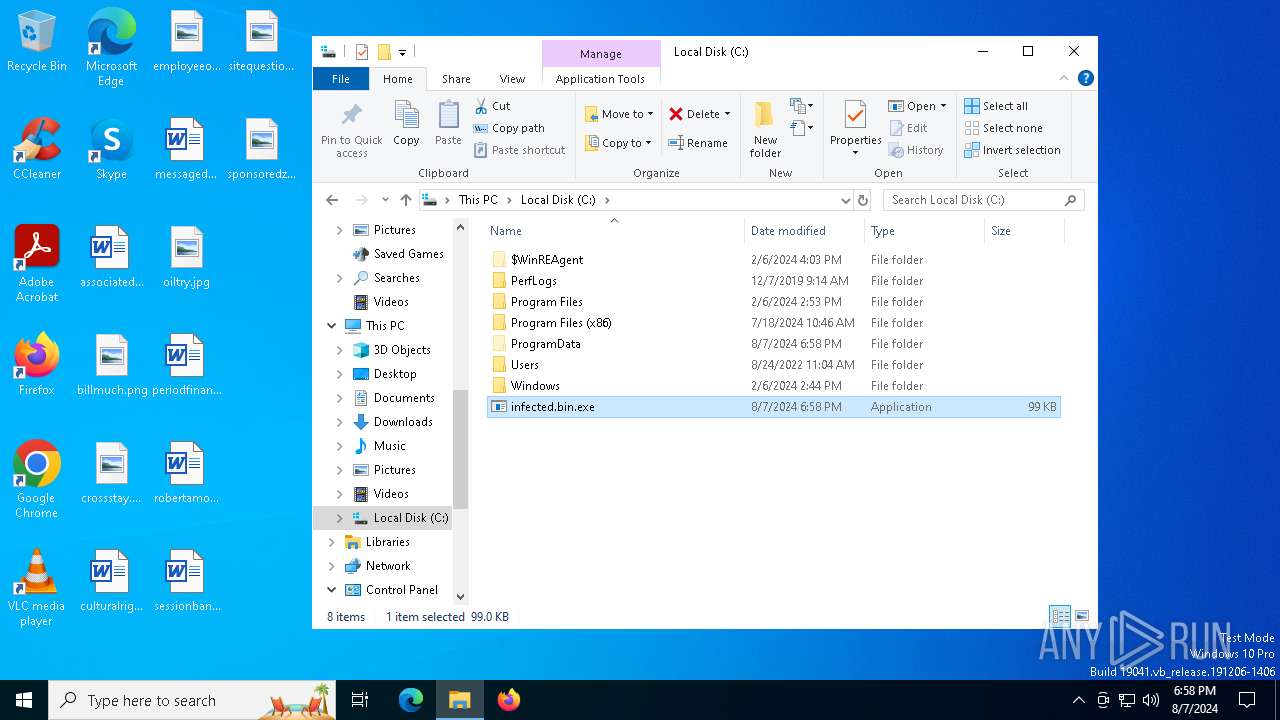
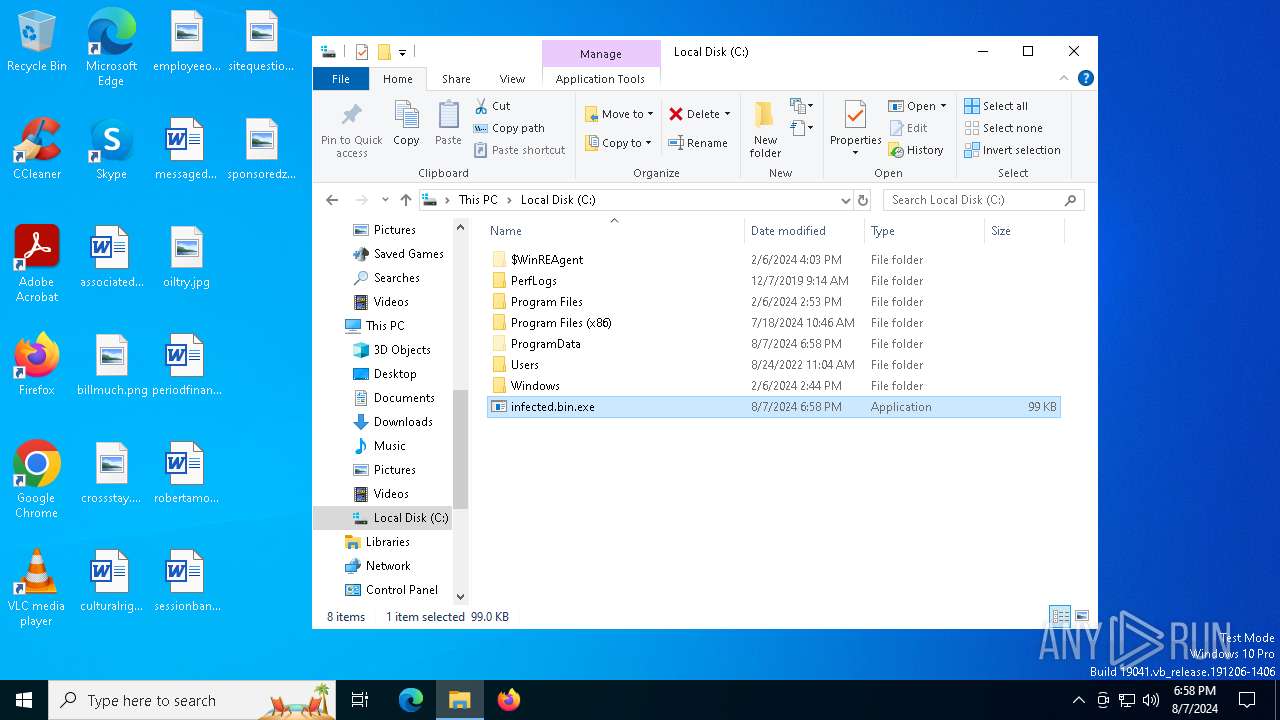
| File name: | infected.bin |
| Full analysis: | https://app.any.run/tasks/ae094b5b-3fa5-40b1-8120-920fe79f2392 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | August 07, 2024, 18:58:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 65F2C6D7A15C17E26F94F9694D4A6AAD |
| SHA1: | 43CC7CEEC1391D6A70E1FBB437EEB00143CD6295 |
| SHA256: | 36117CD17F4E8182C735A53BBC3D00EDA9074D0ADEDED411042A4174D95680BE |
| SSDEEP: | 1536:zDr6f7HDjYUvt3kfyg26BAO9sW6XRyXi81WVkWAI7c4wxKqg7J/tFxuzvk+HM10k:zD2Yl676BU/yXj1W9a4IRg9wzDHM26X |
MALICIOUS
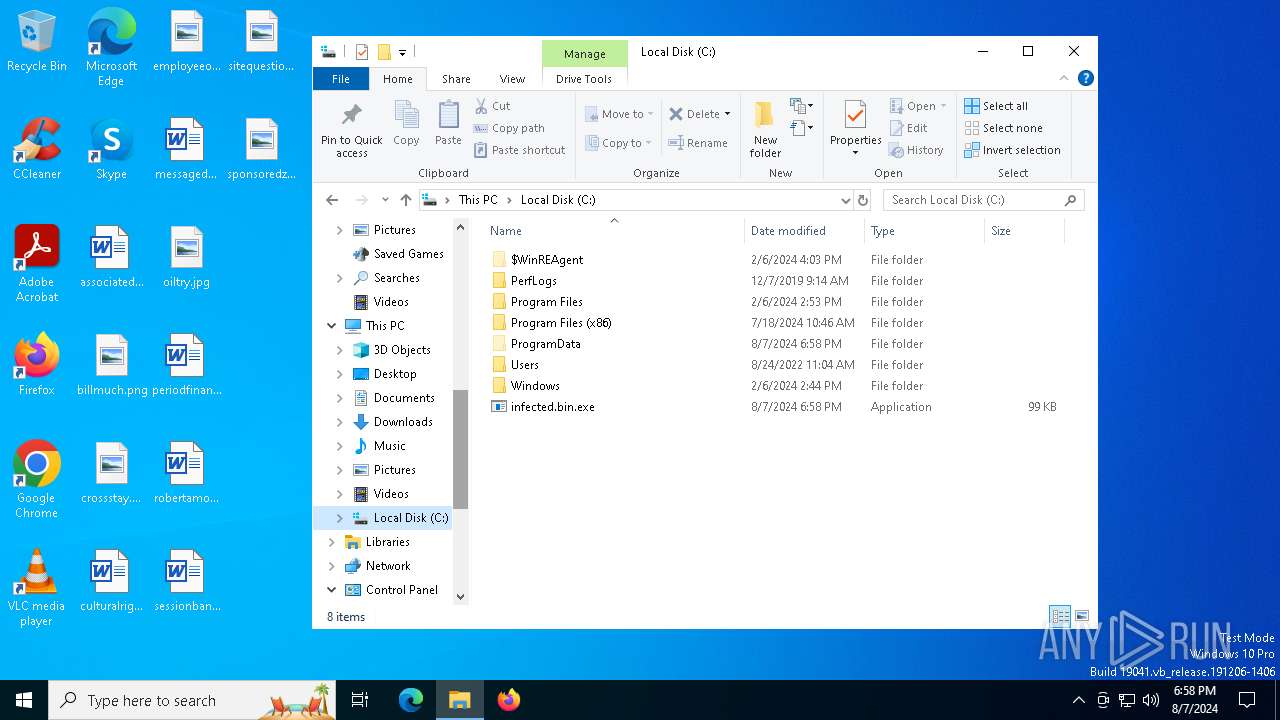
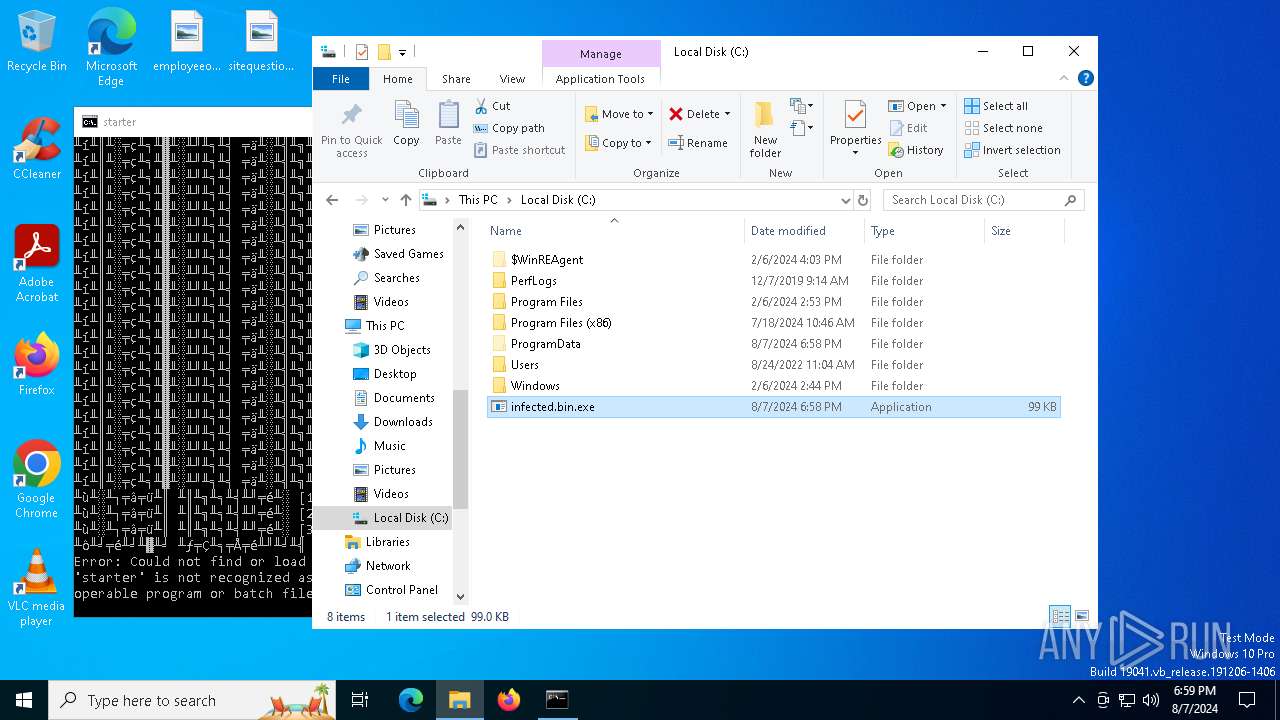
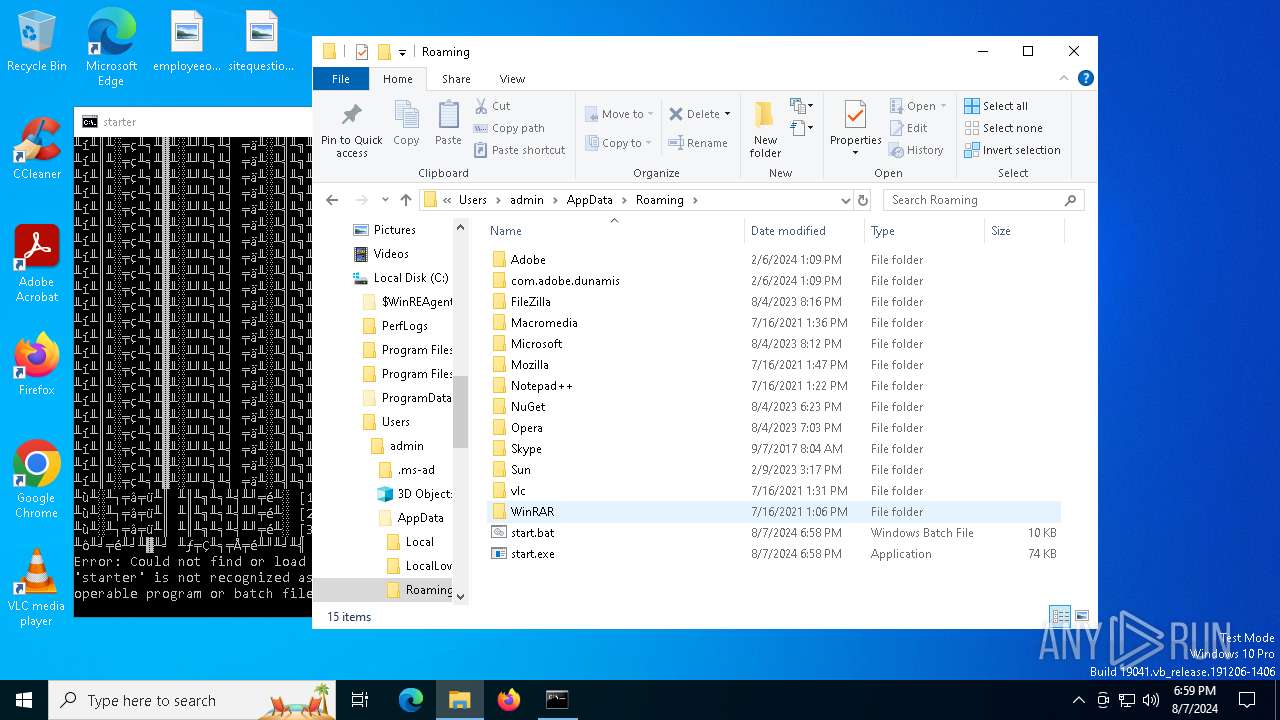
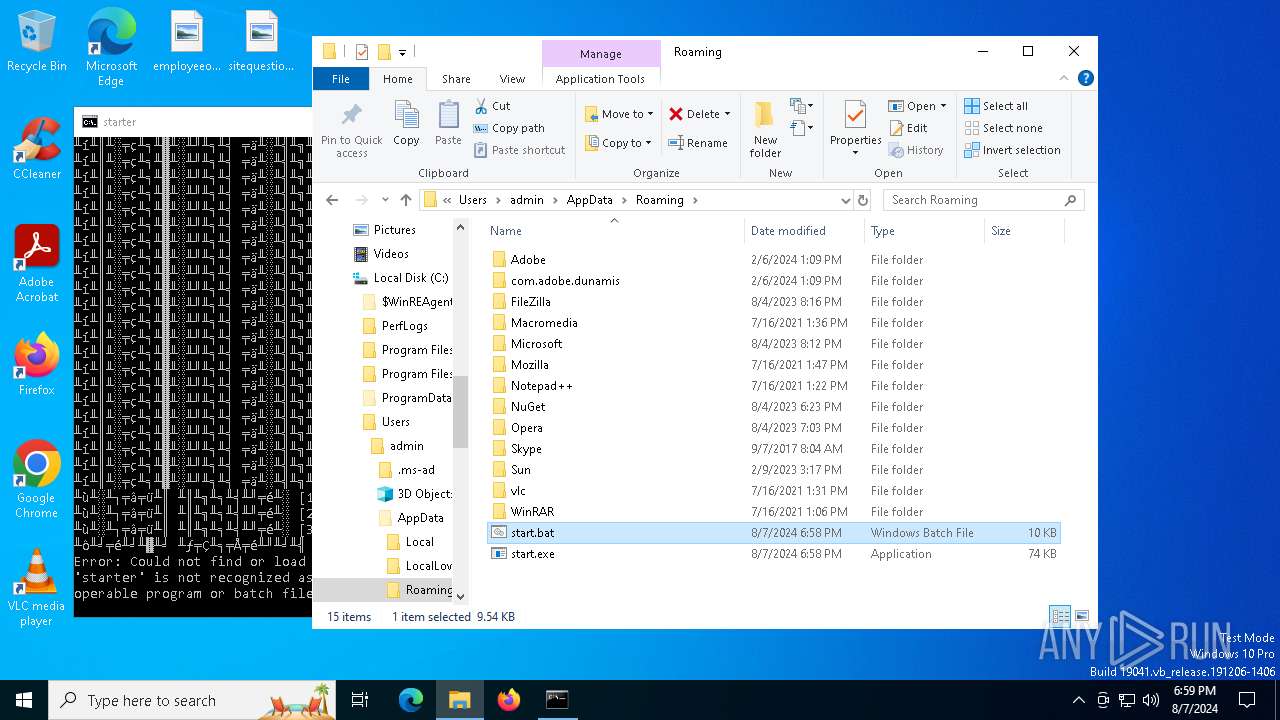
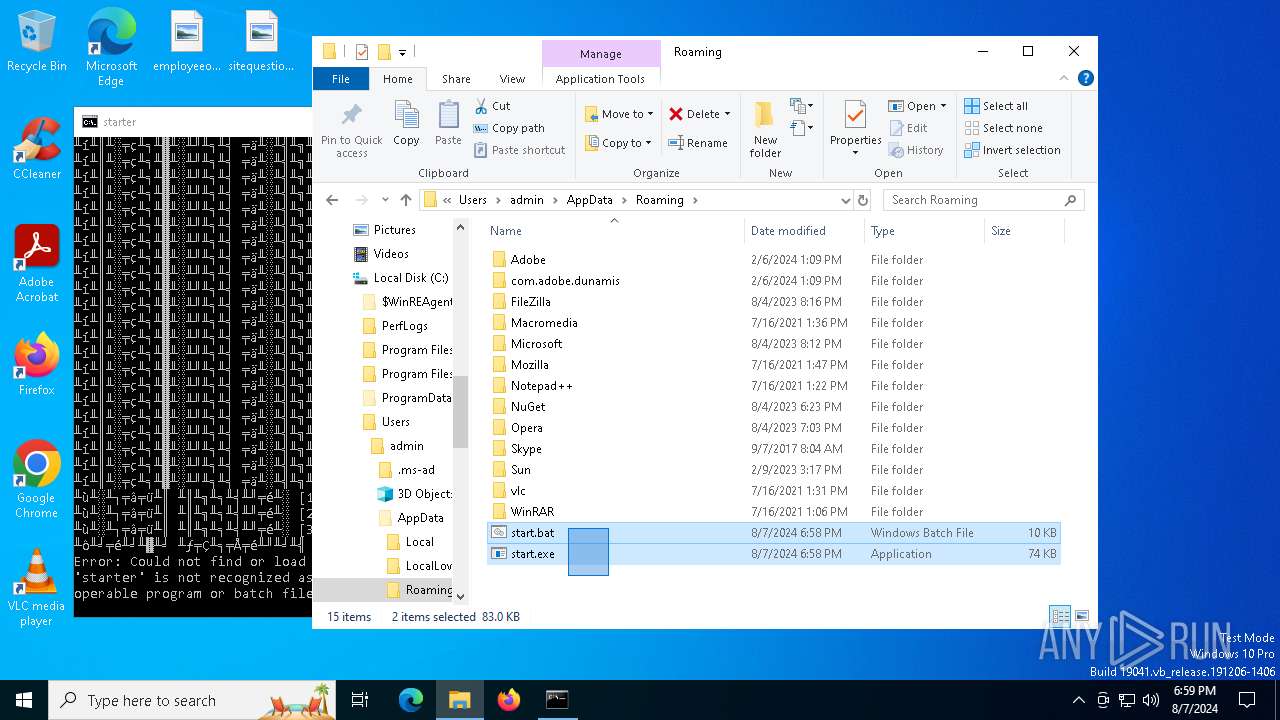
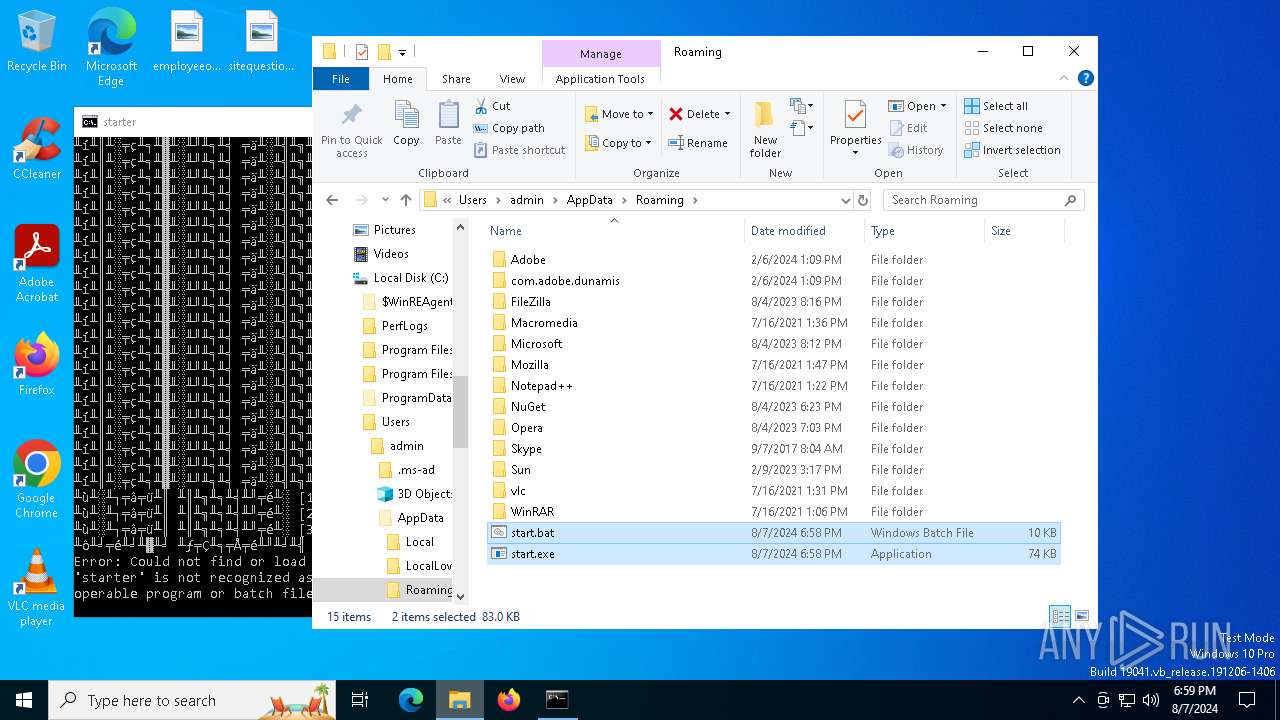
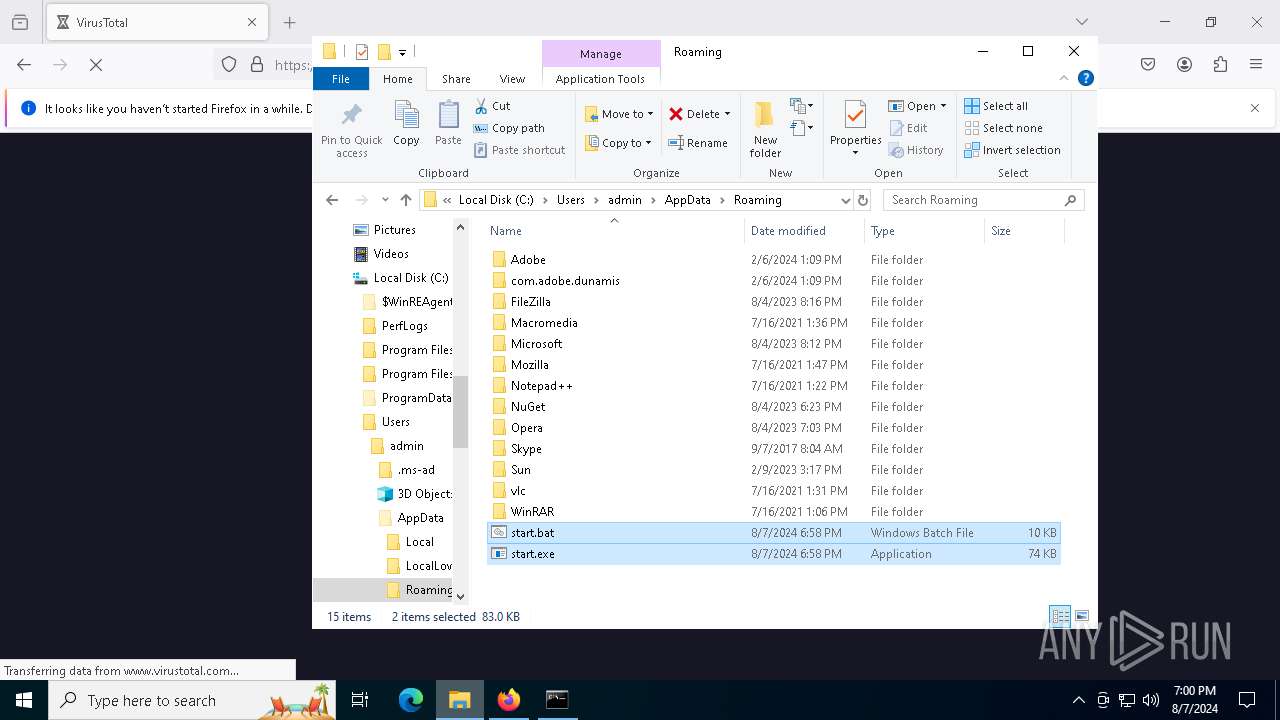
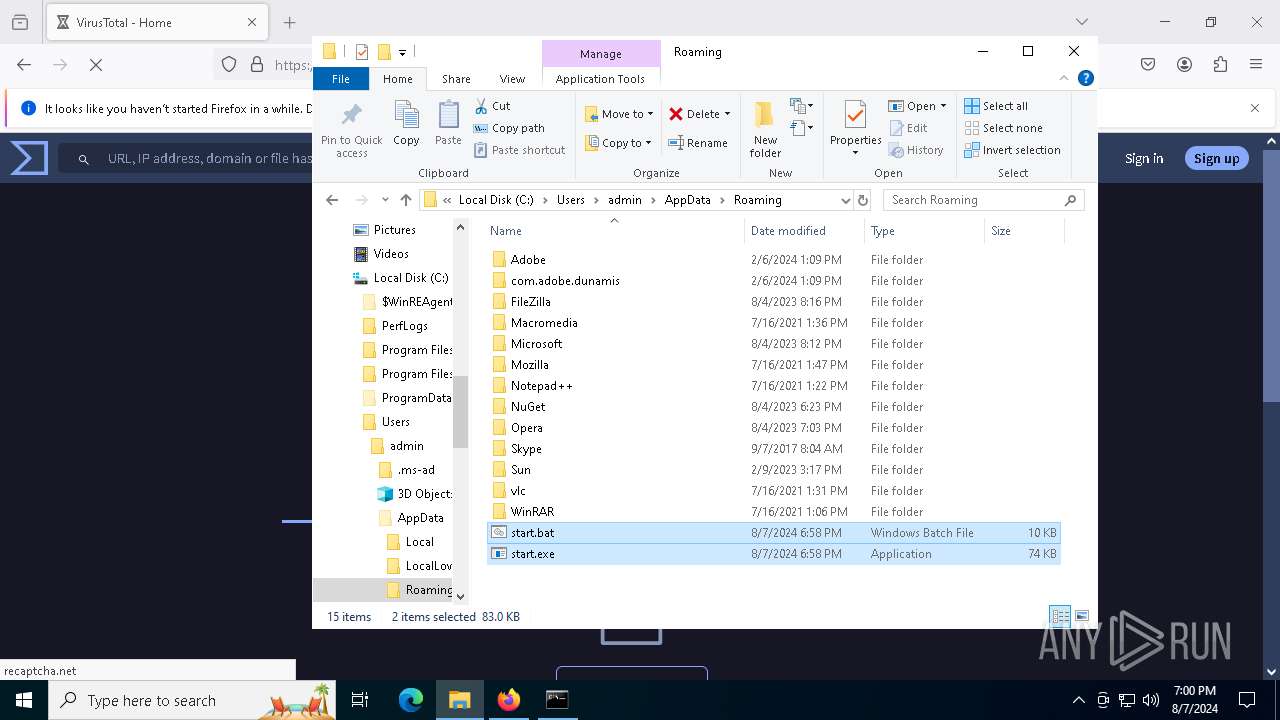
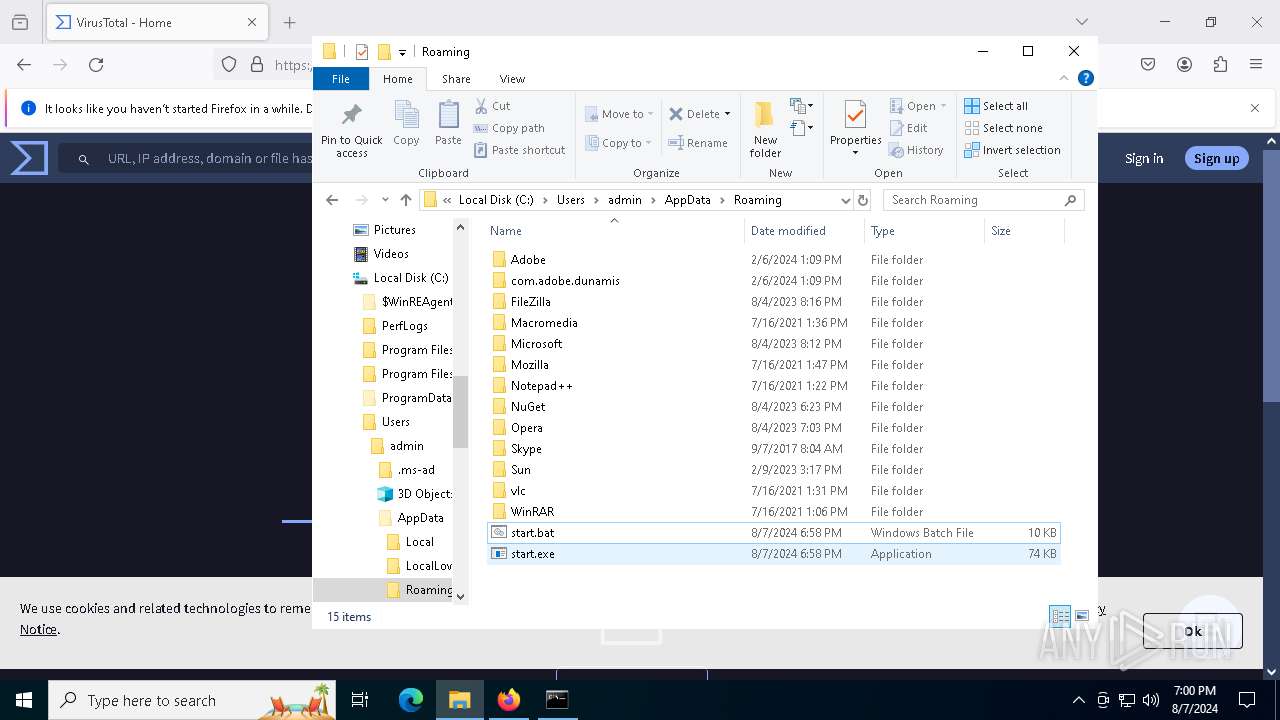
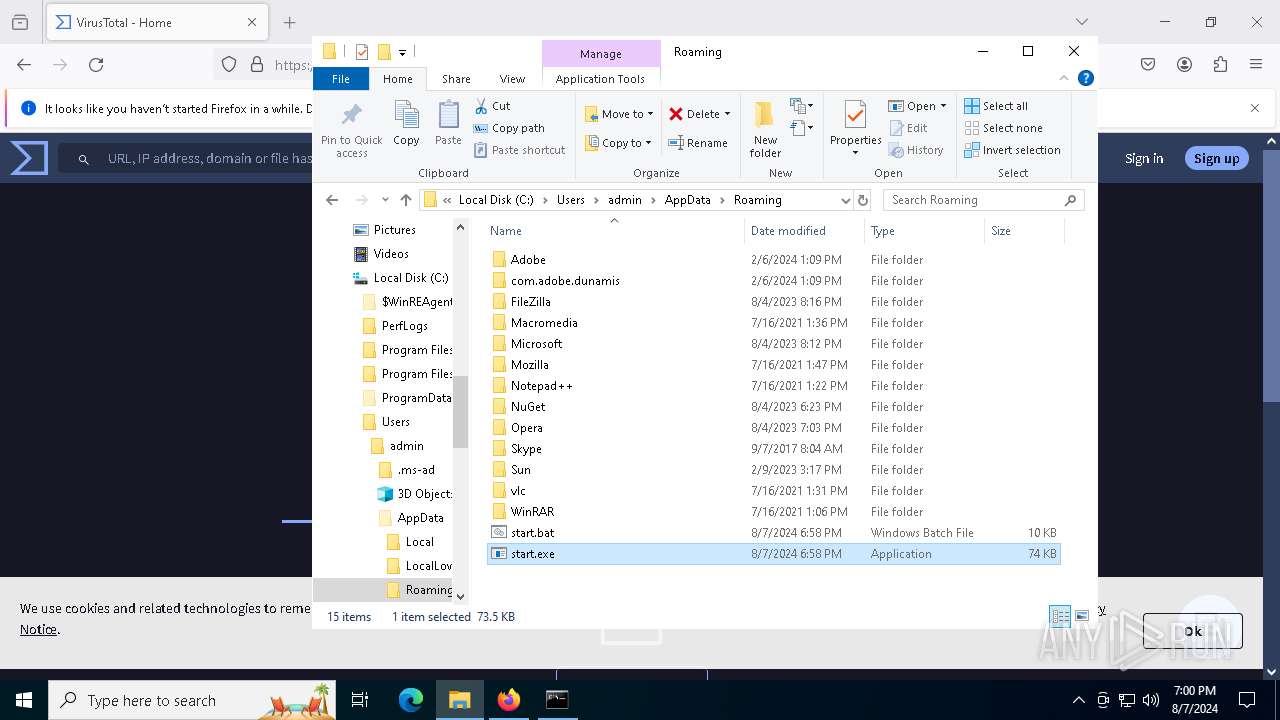
Drops the executable file immediately after the start
- start.exe (PID: 6508)
- infected.bin.exe (PID: 6392)
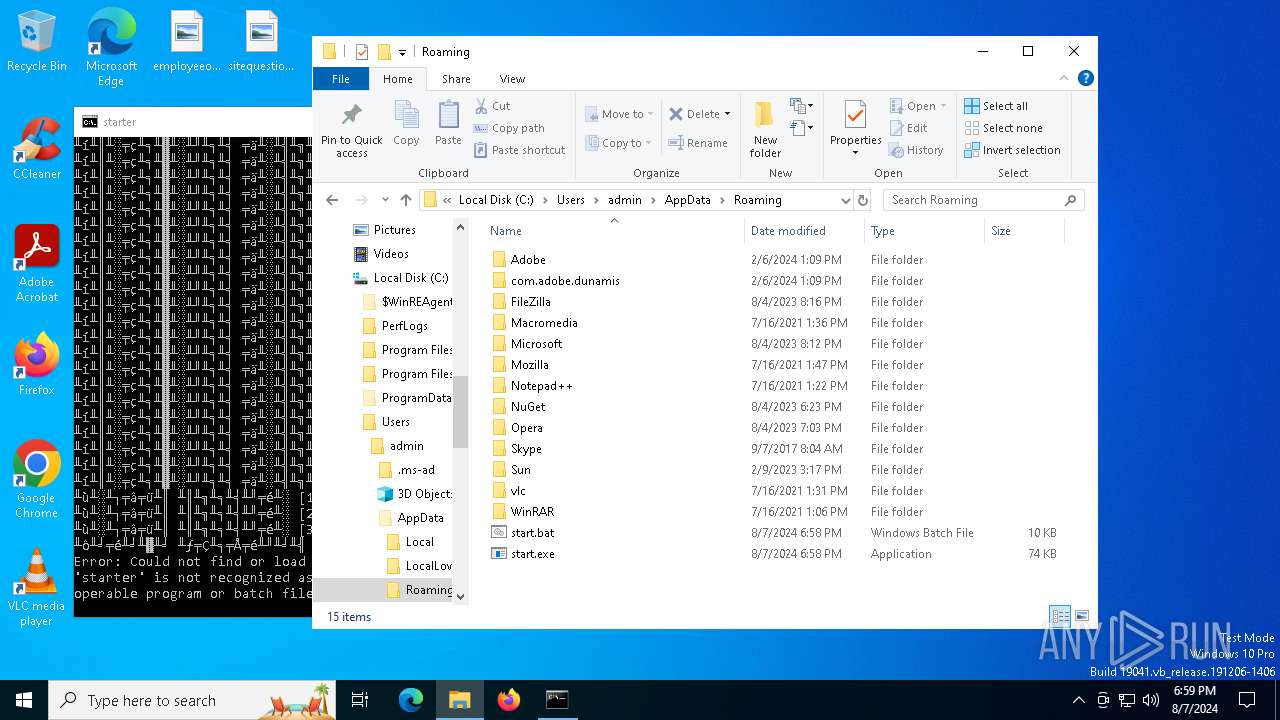
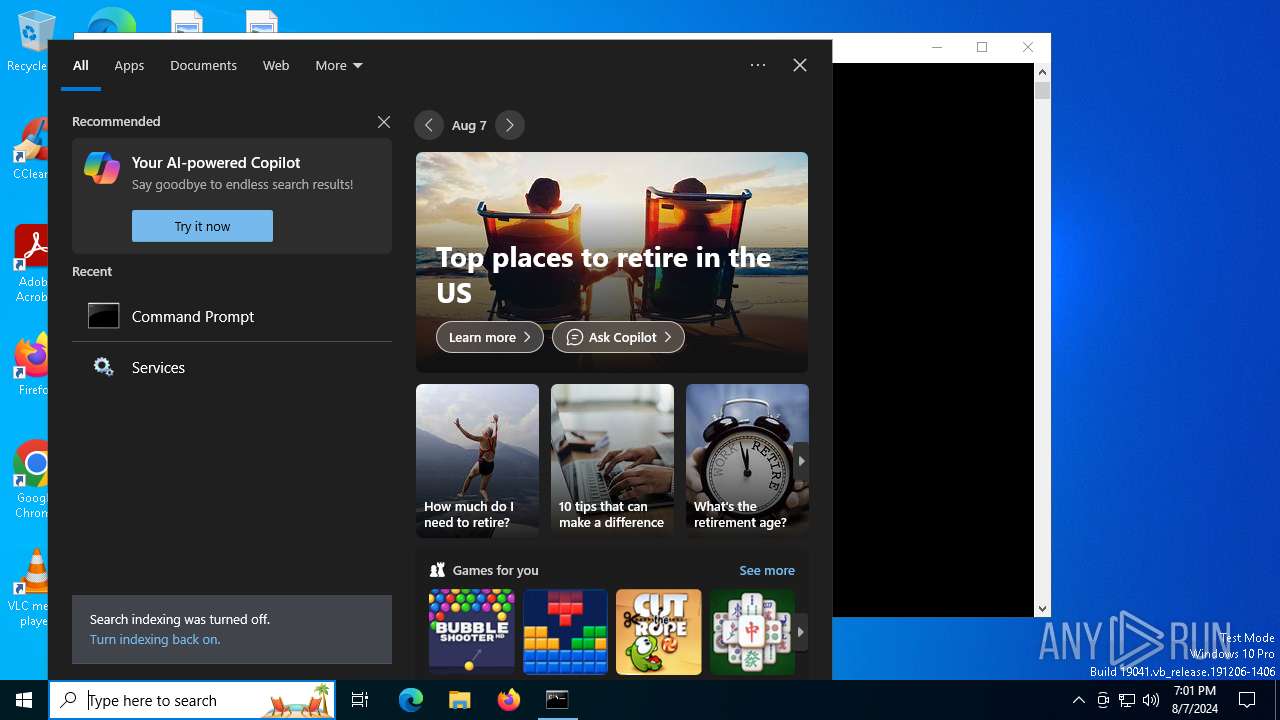
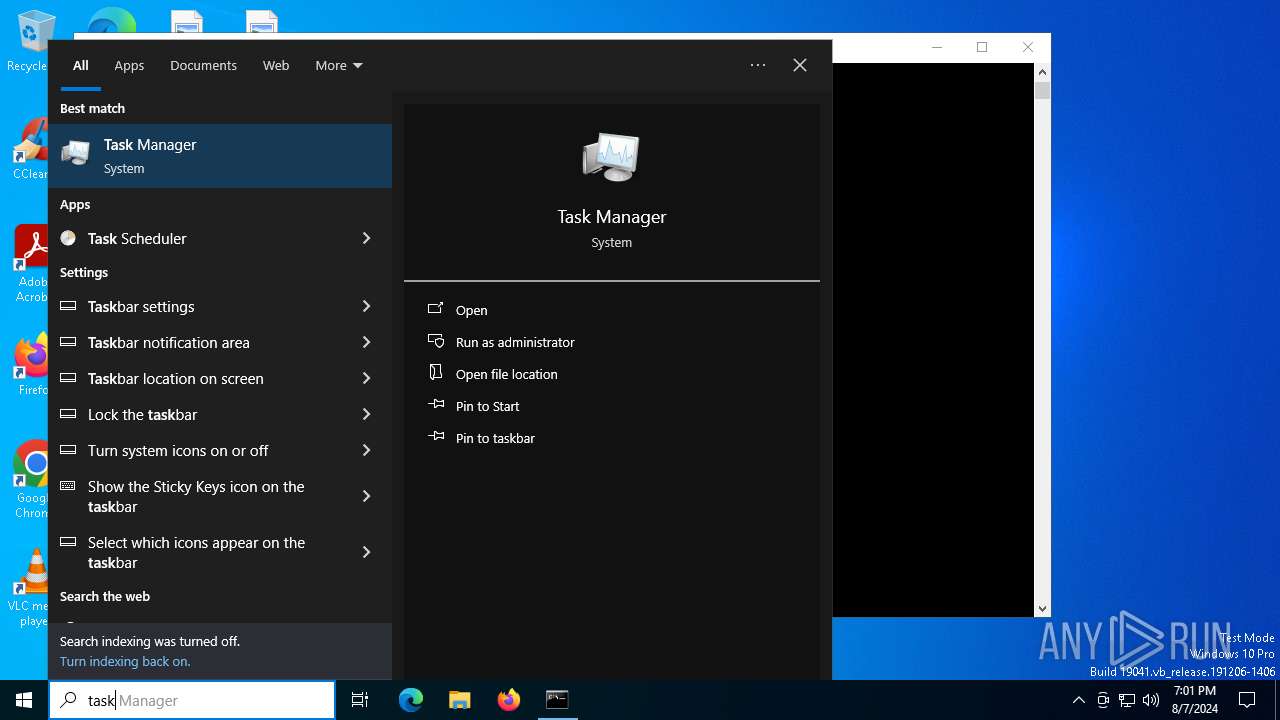
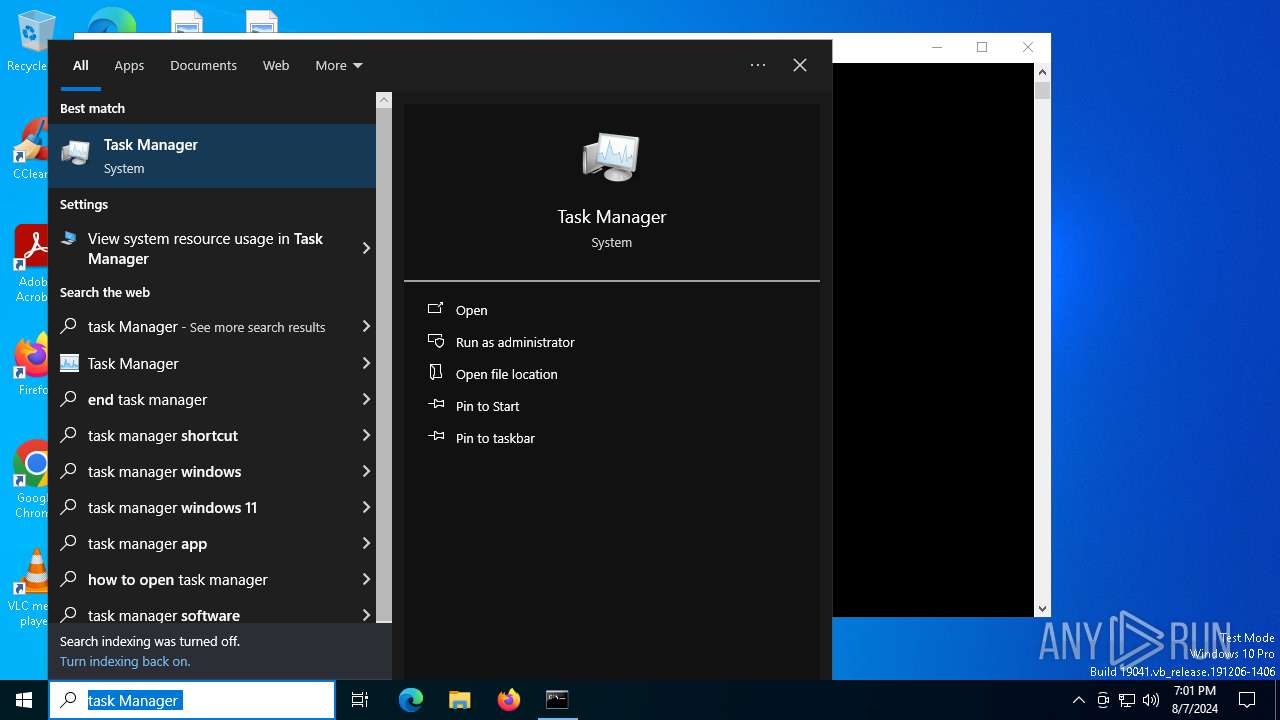
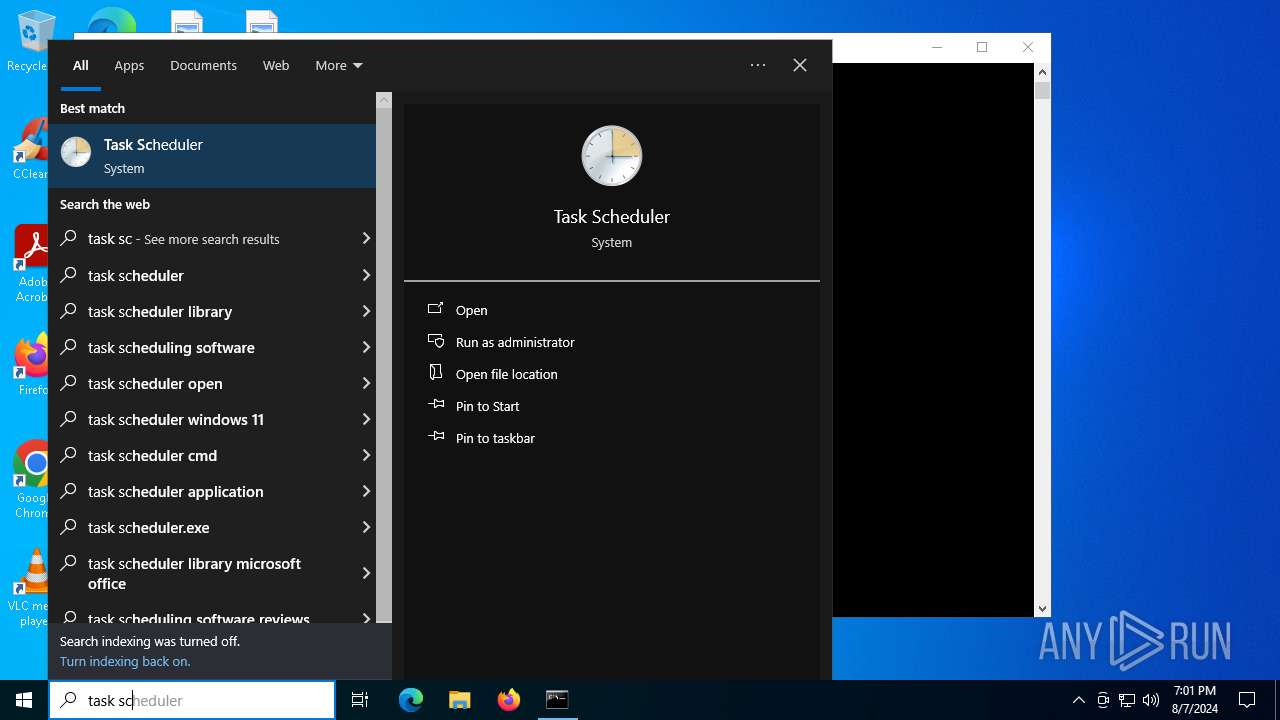
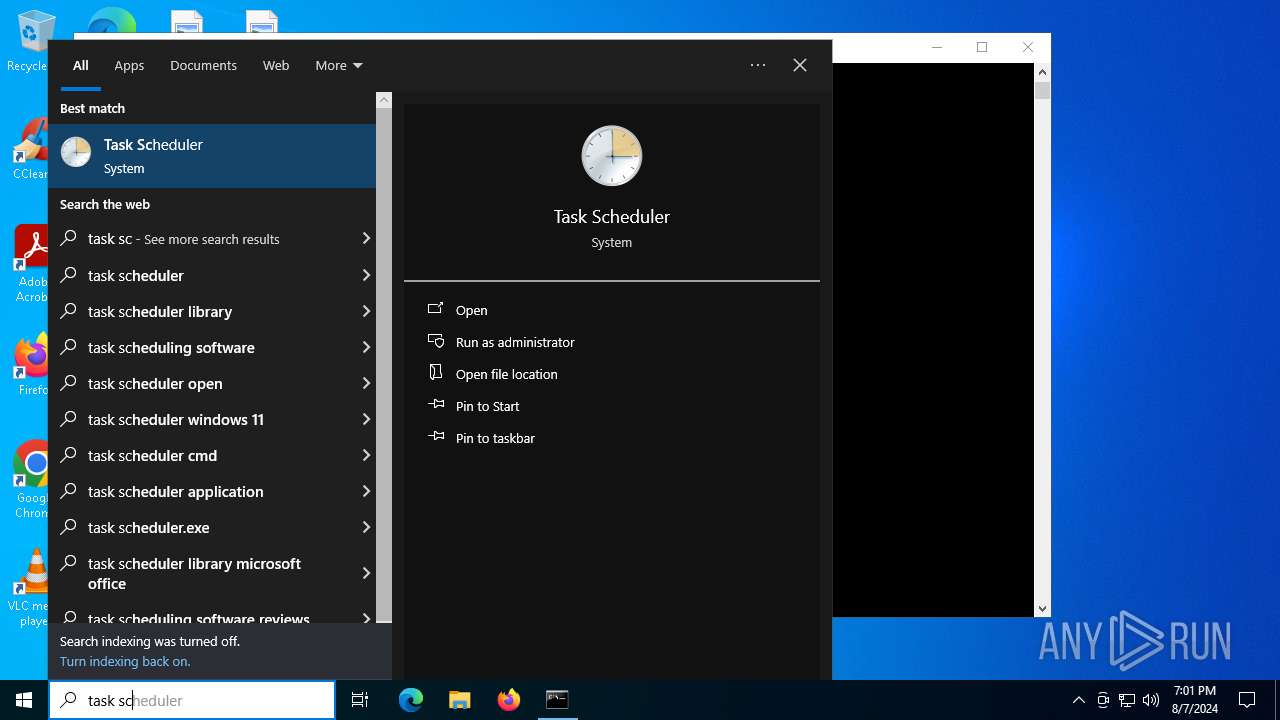
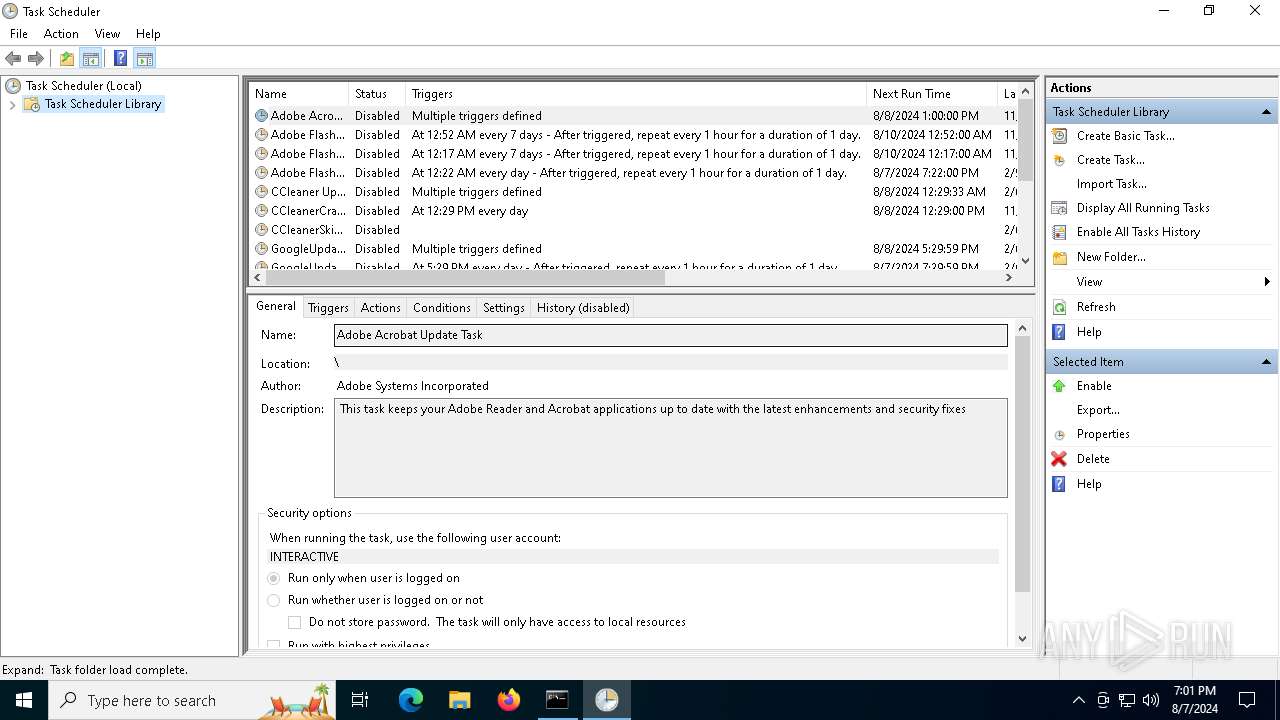
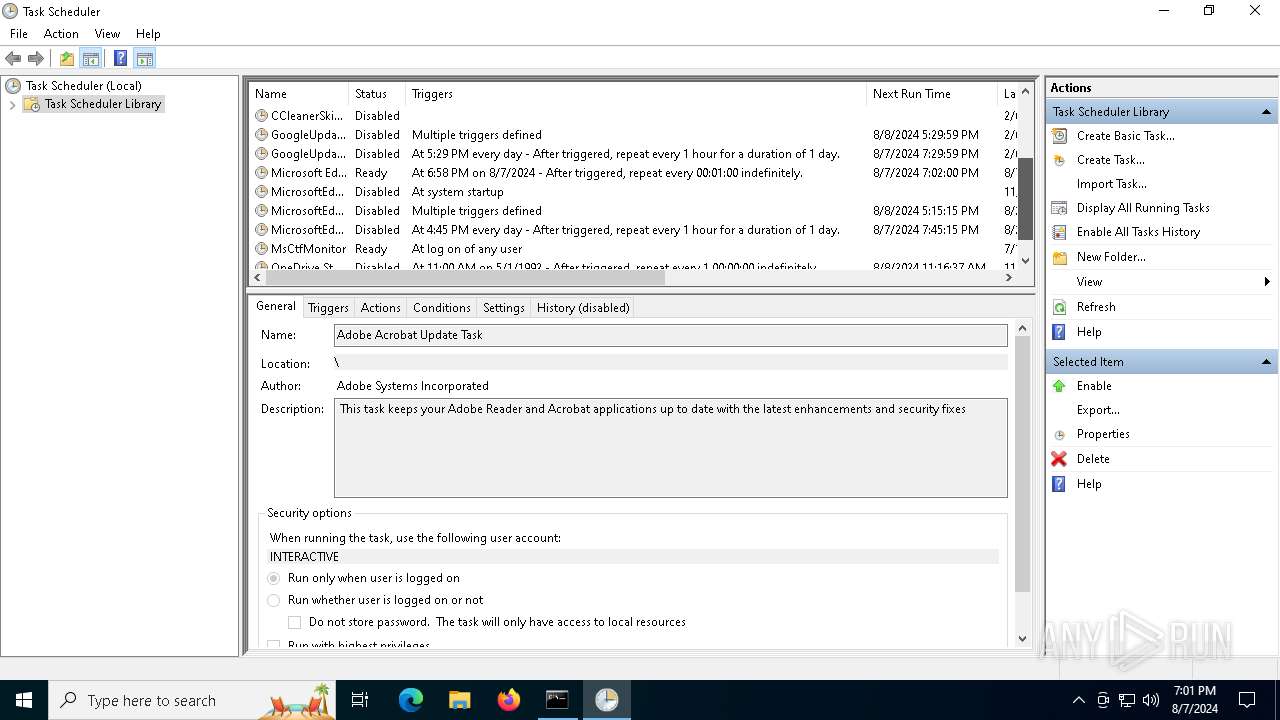
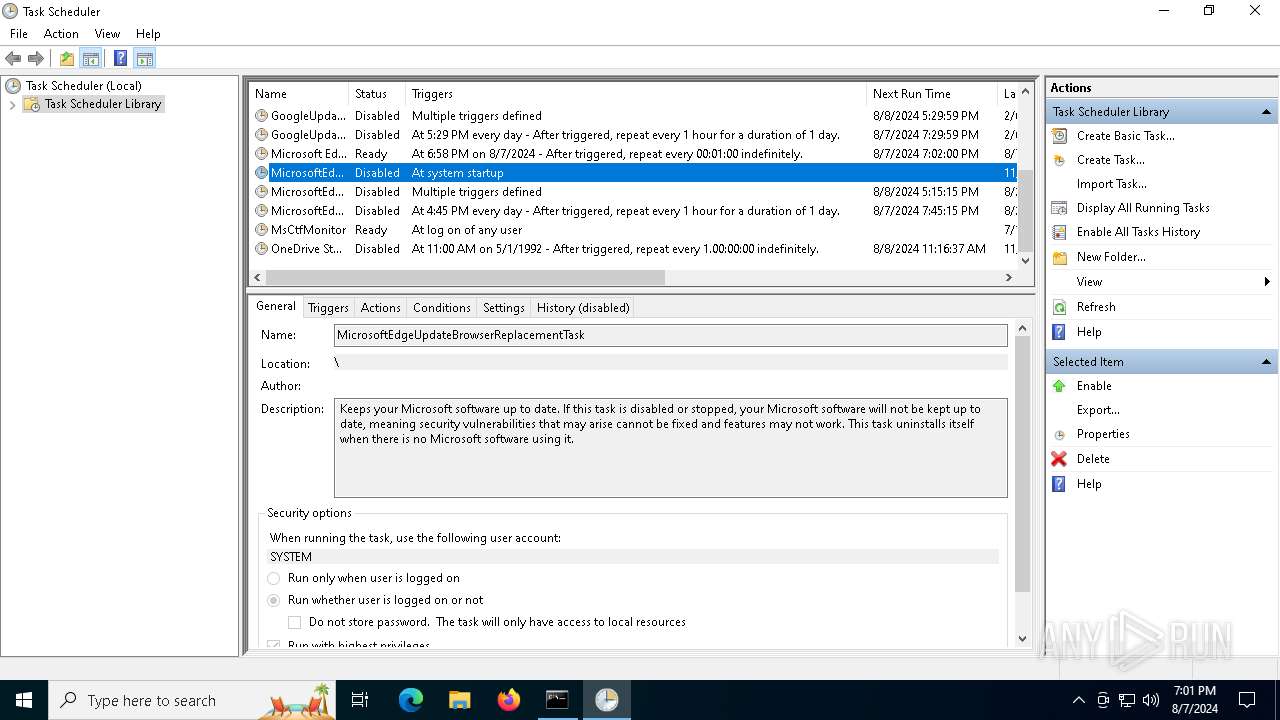
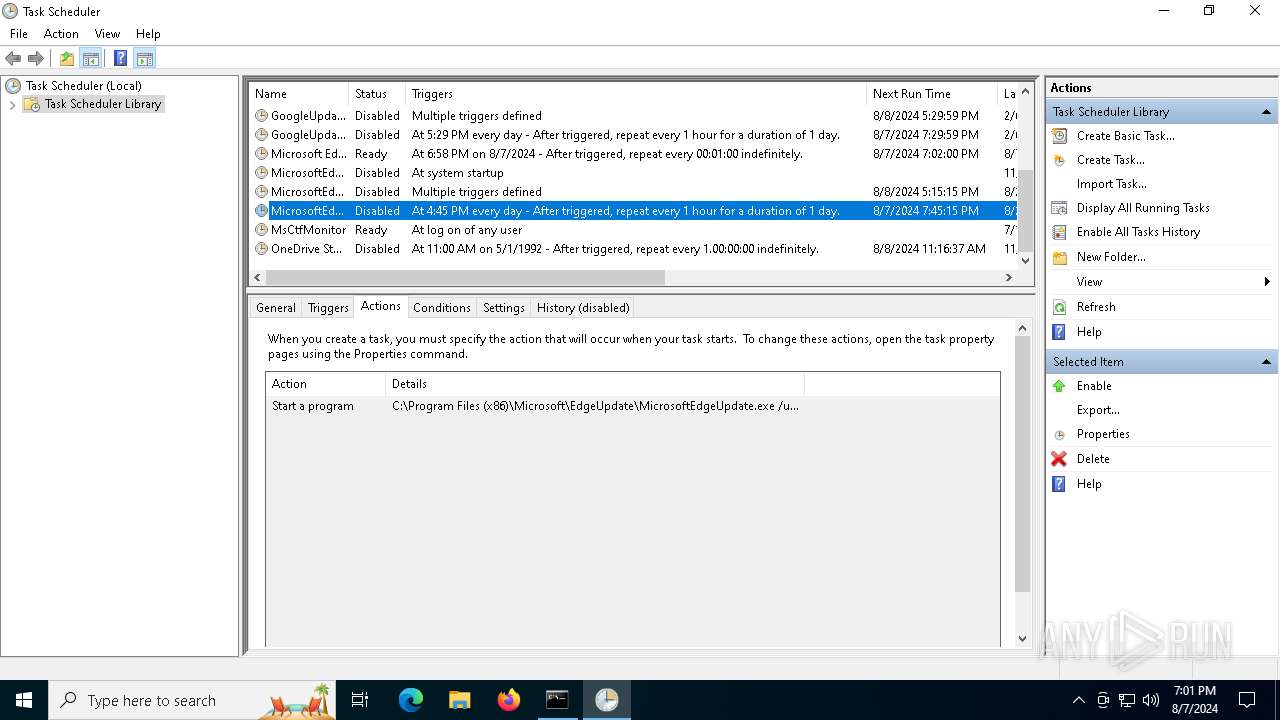
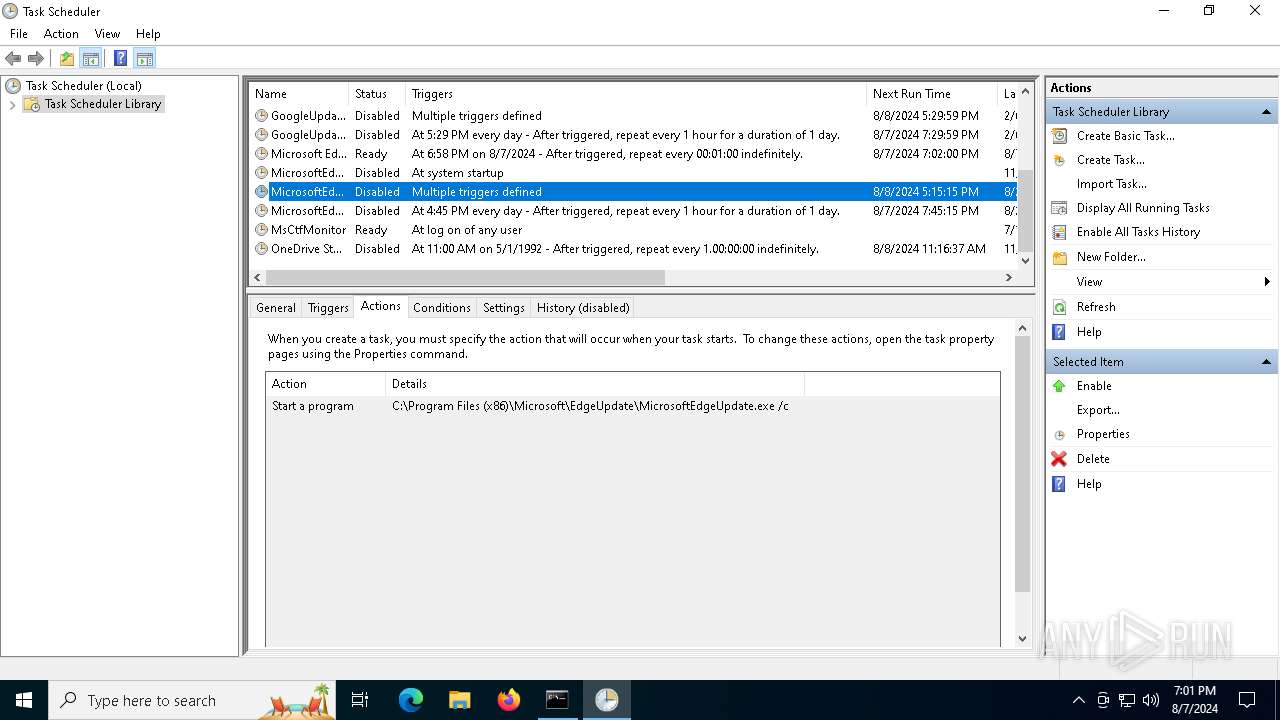
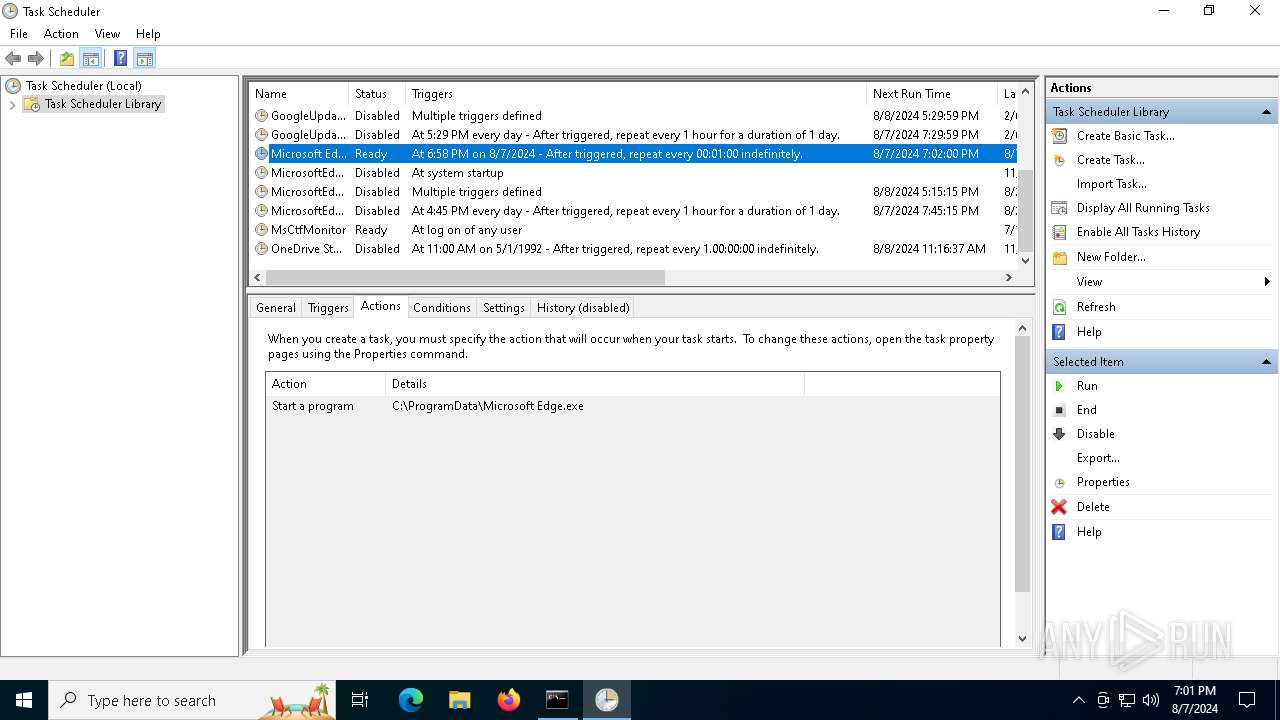
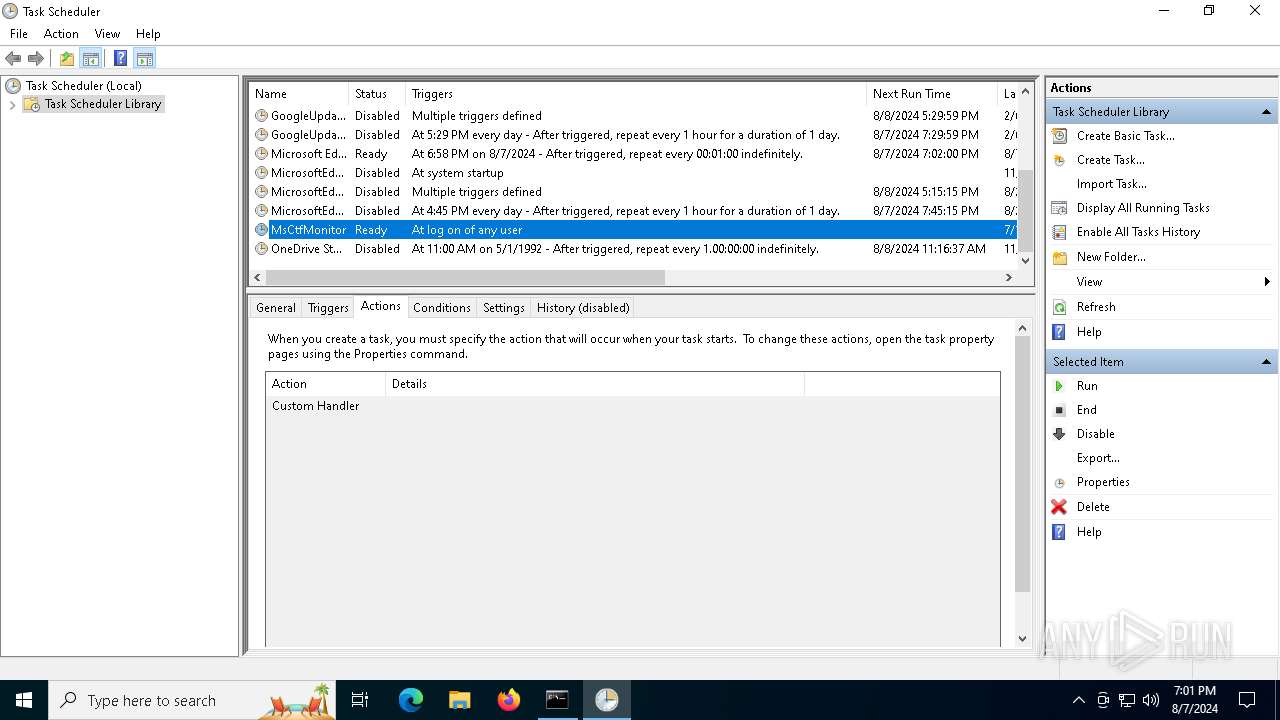
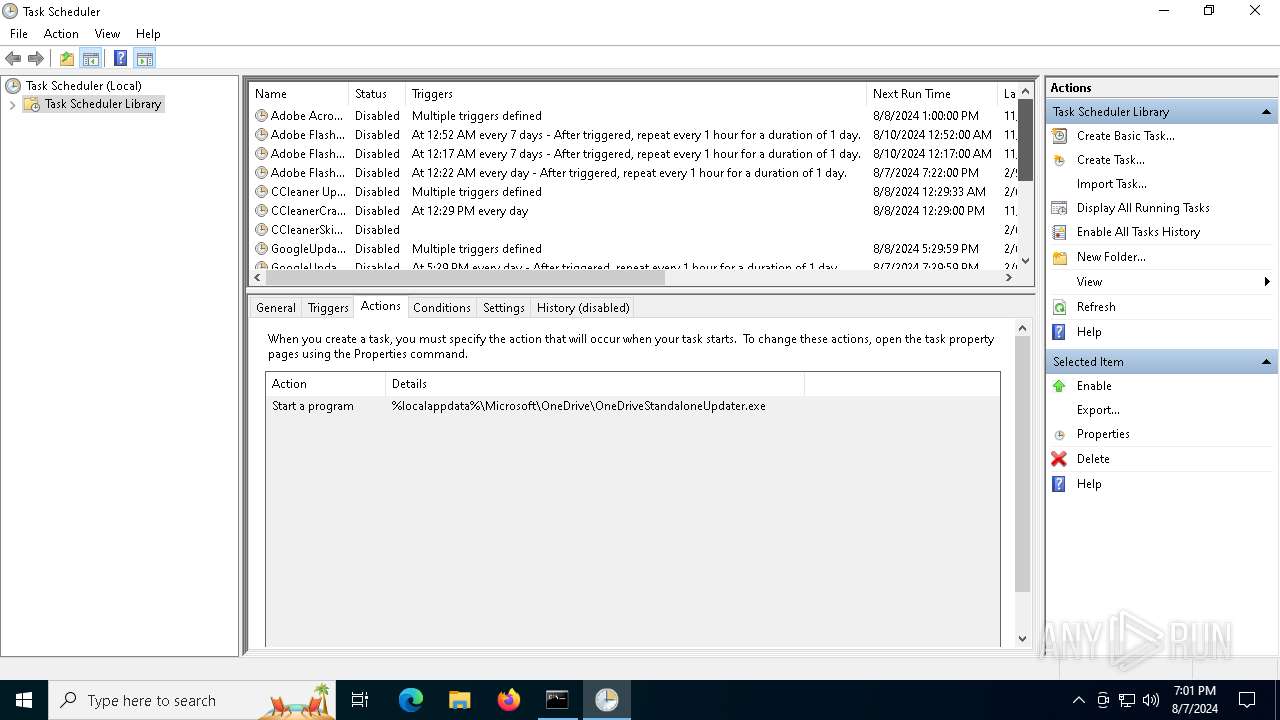
Uses Task Scheduler to run other applications
- start.exe (PID: 6508)
Create files in the Startup directory
- start.exe (PID: 6508)
Changes the autorun value in the registry
- start.exe (PID: 6508)
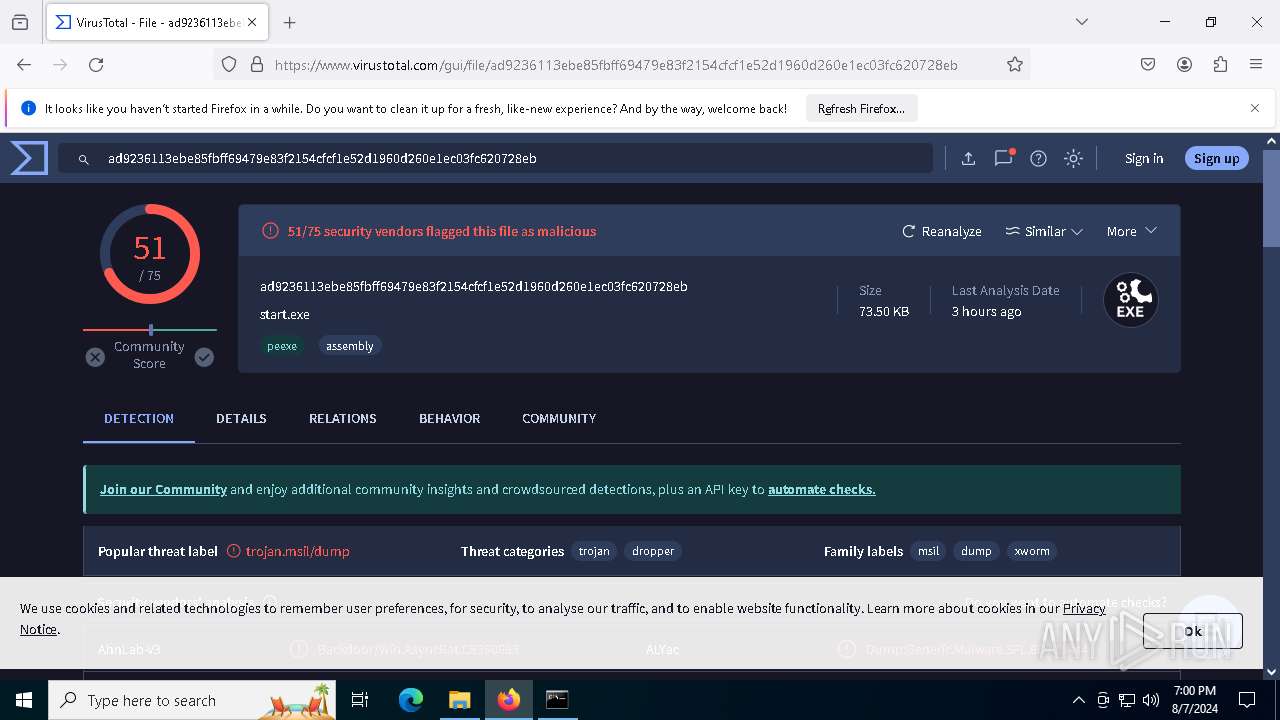
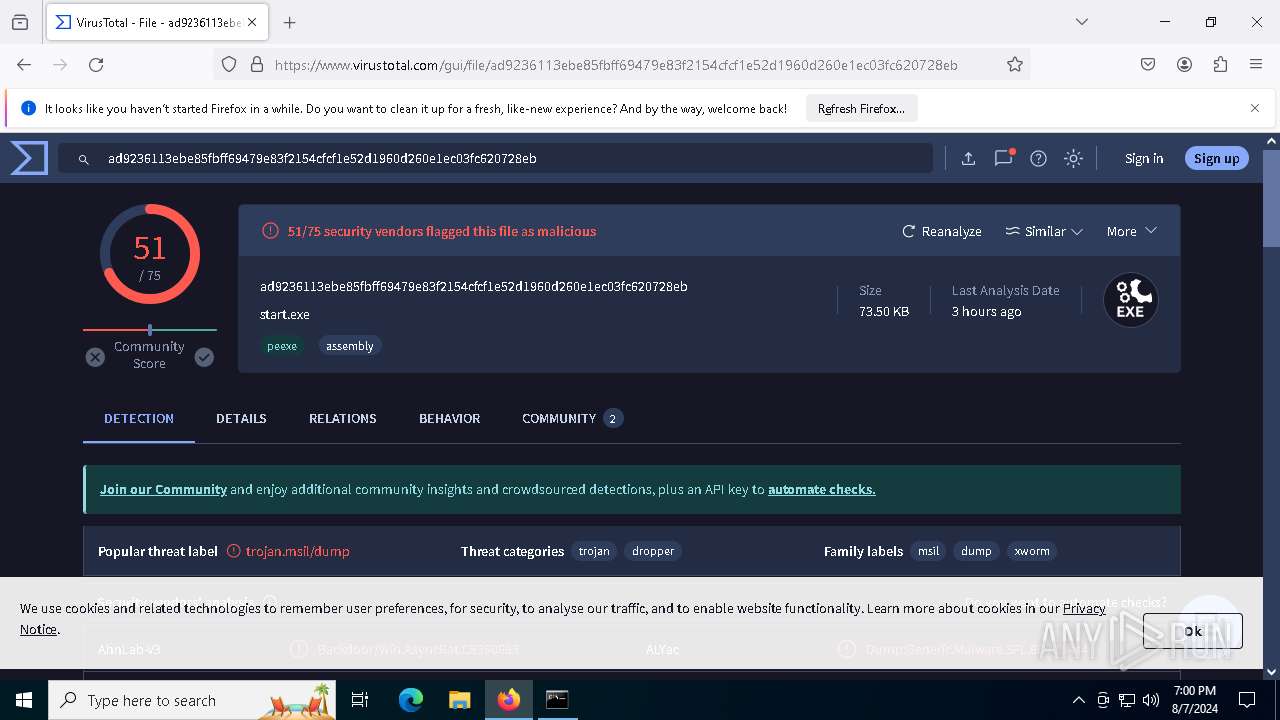
XWORM has been detected (YARA)
- start.exe (PID: 6508)
XWORM has been detected (SURICATA)
- start.exe (PID: 6508)
Connects to the CnC server
- start.exe (PID: 6508)
Actions looks like stealing of personal data
- start.exe (PID: 6508)
SUSPICIOUS
Reads the date of Windows installation
- infected.bin.exe (PID: 6392)
- start.exe (PID: 6508)
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
Reads security settings of Internet Explorer
- infected.bin.exe (PID: 6392)
- start.exe (PID: 6508)
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
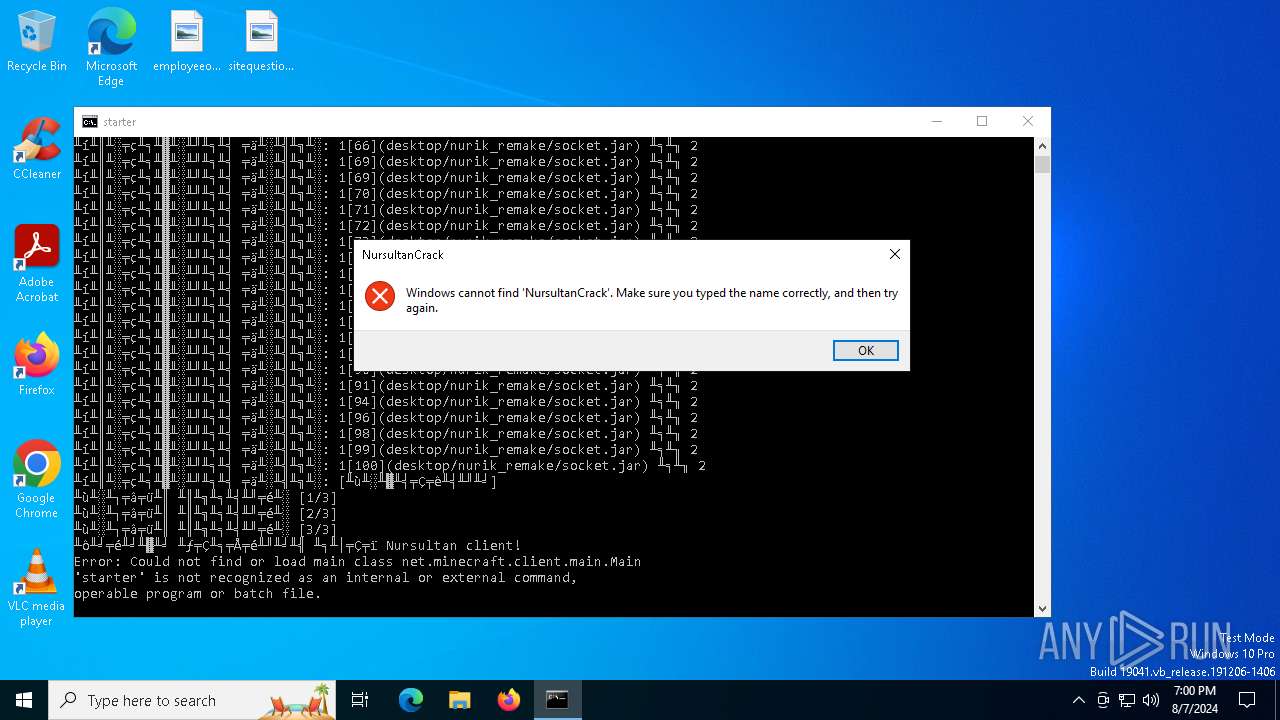
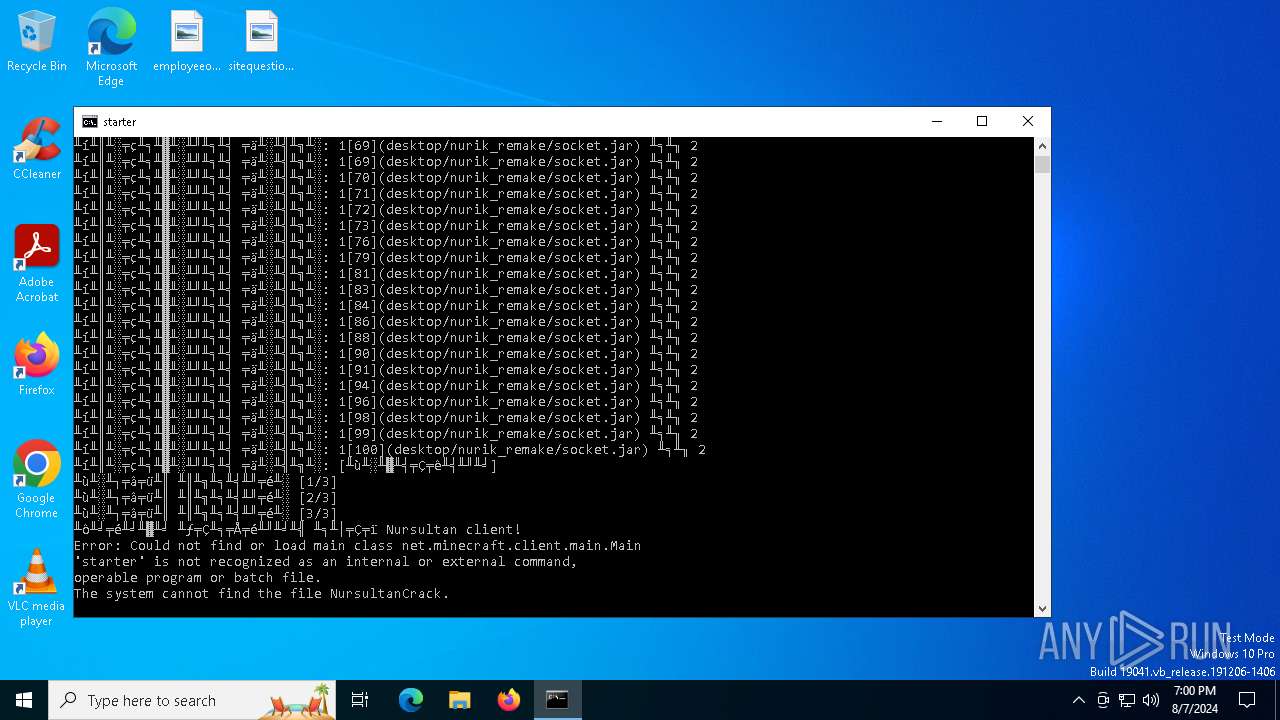
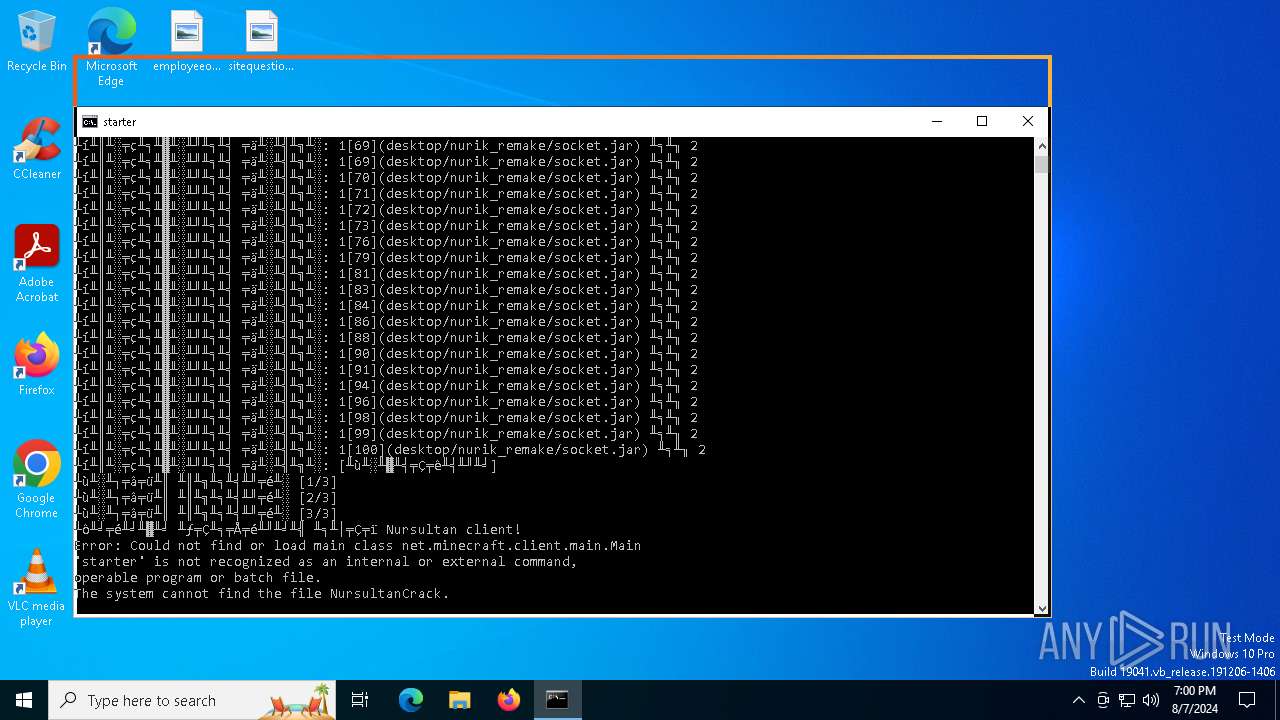
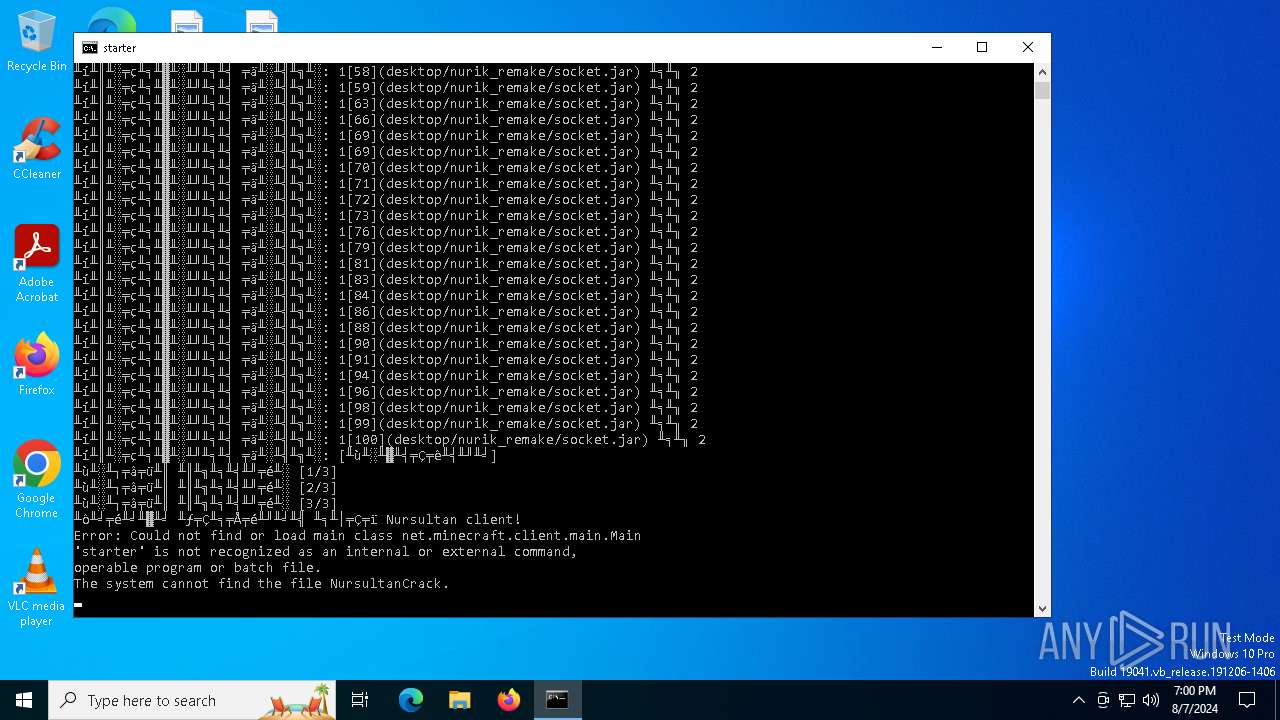
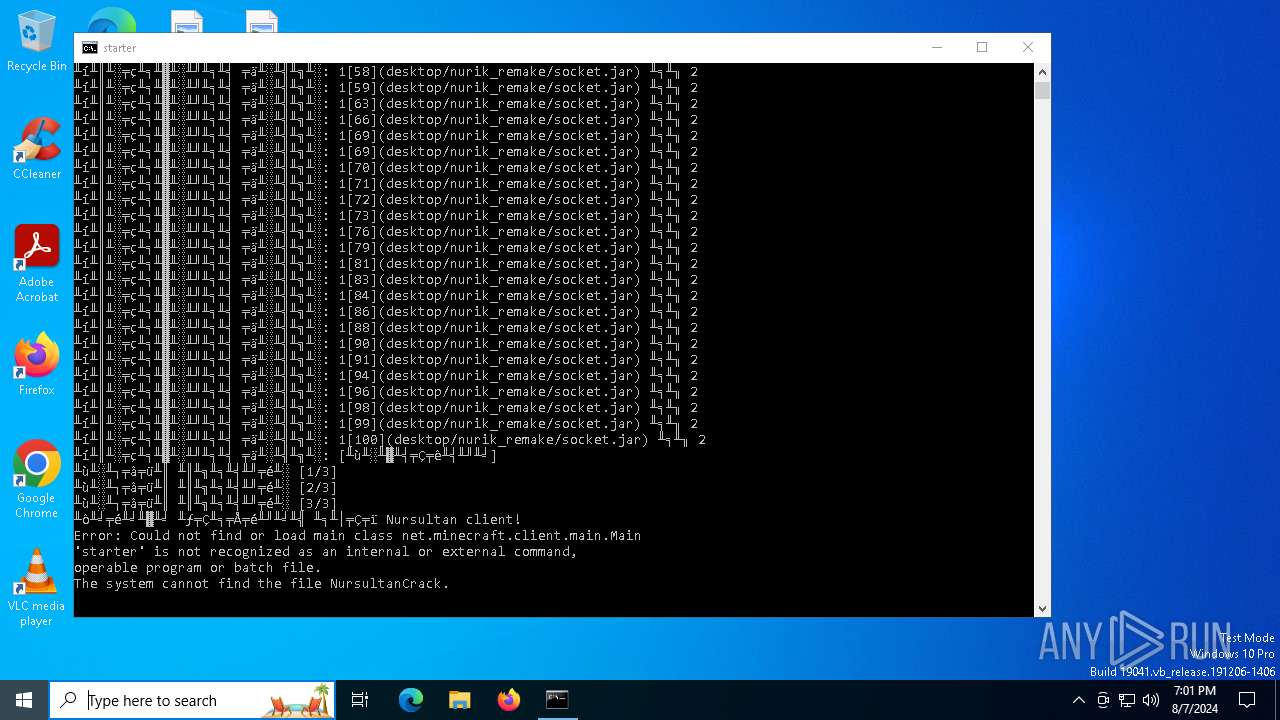
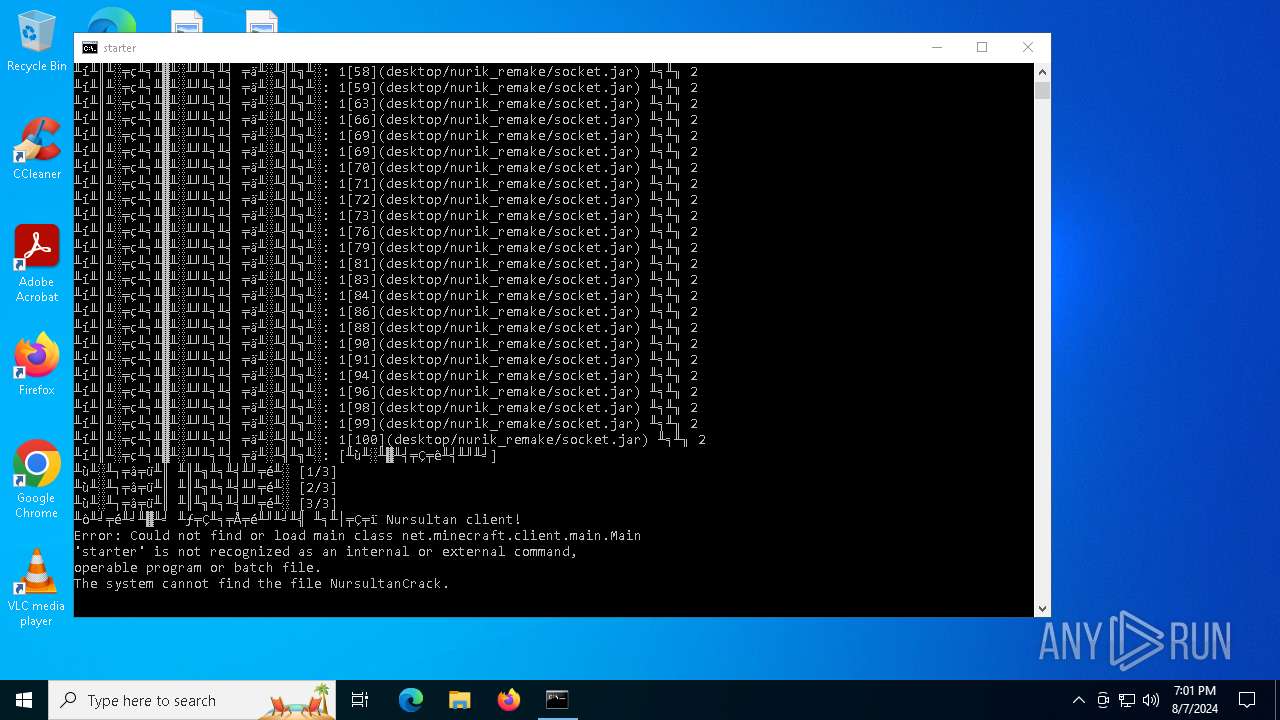
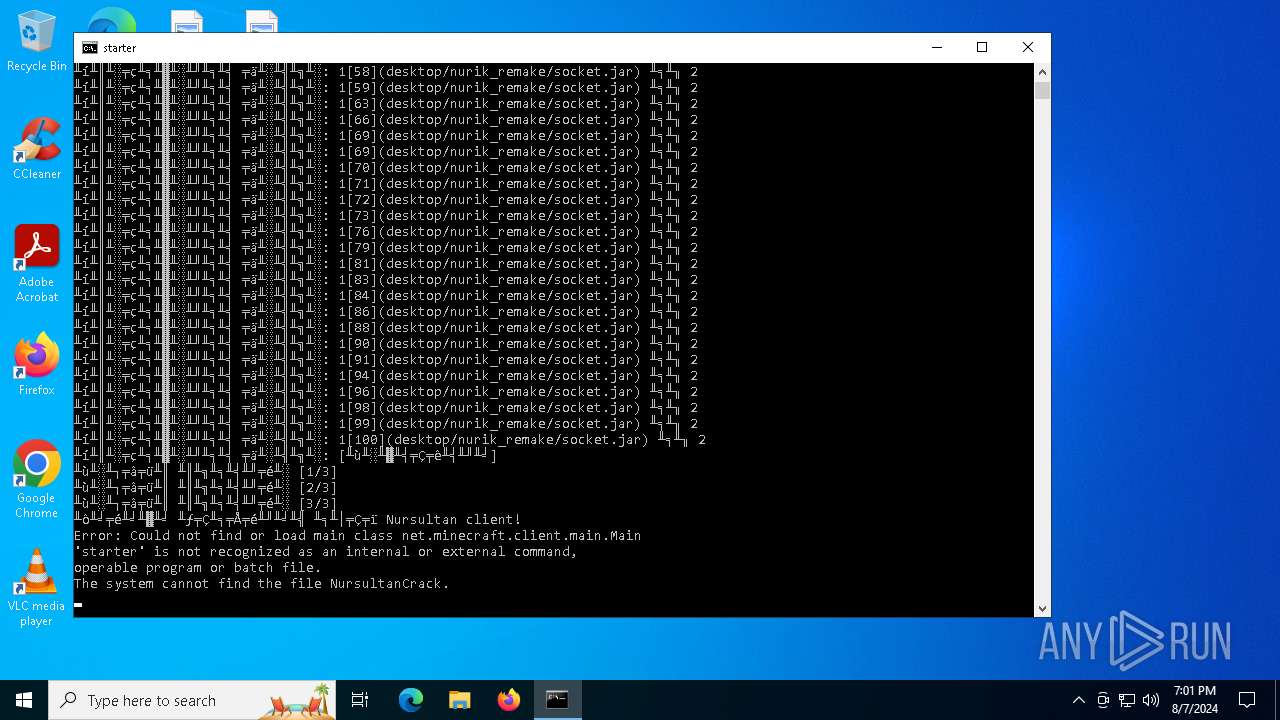
Starts CMD.EXE for commands execution
- infected.bin.exe (PID: 6392)
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
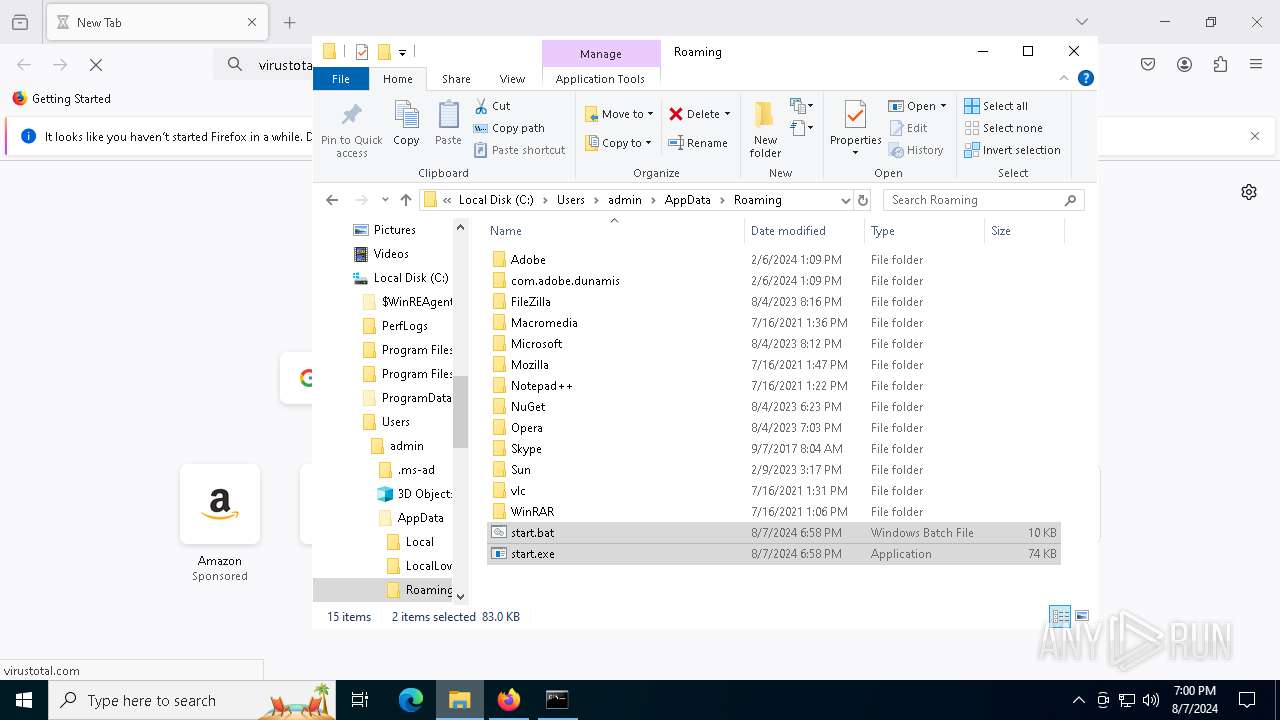
Executable content was dropped or overwritten
- infected.bin.exe (PID: 6392)
- start.exe (PID: 6508)
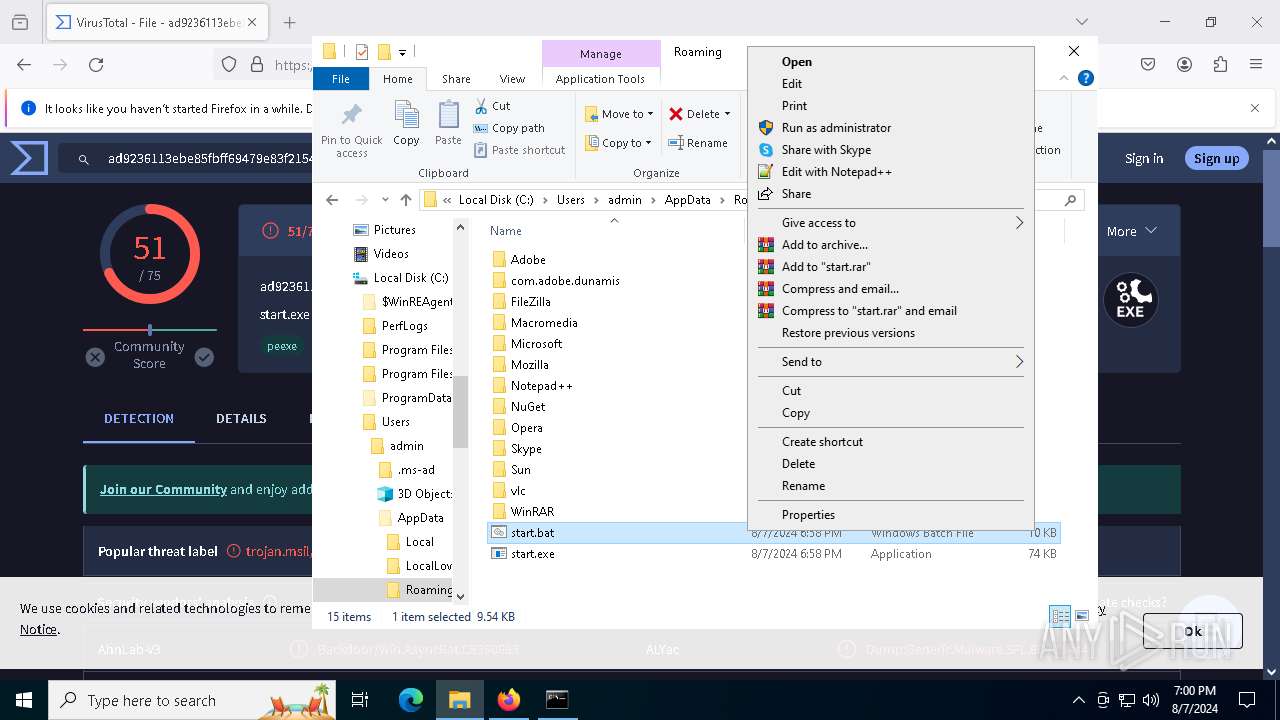
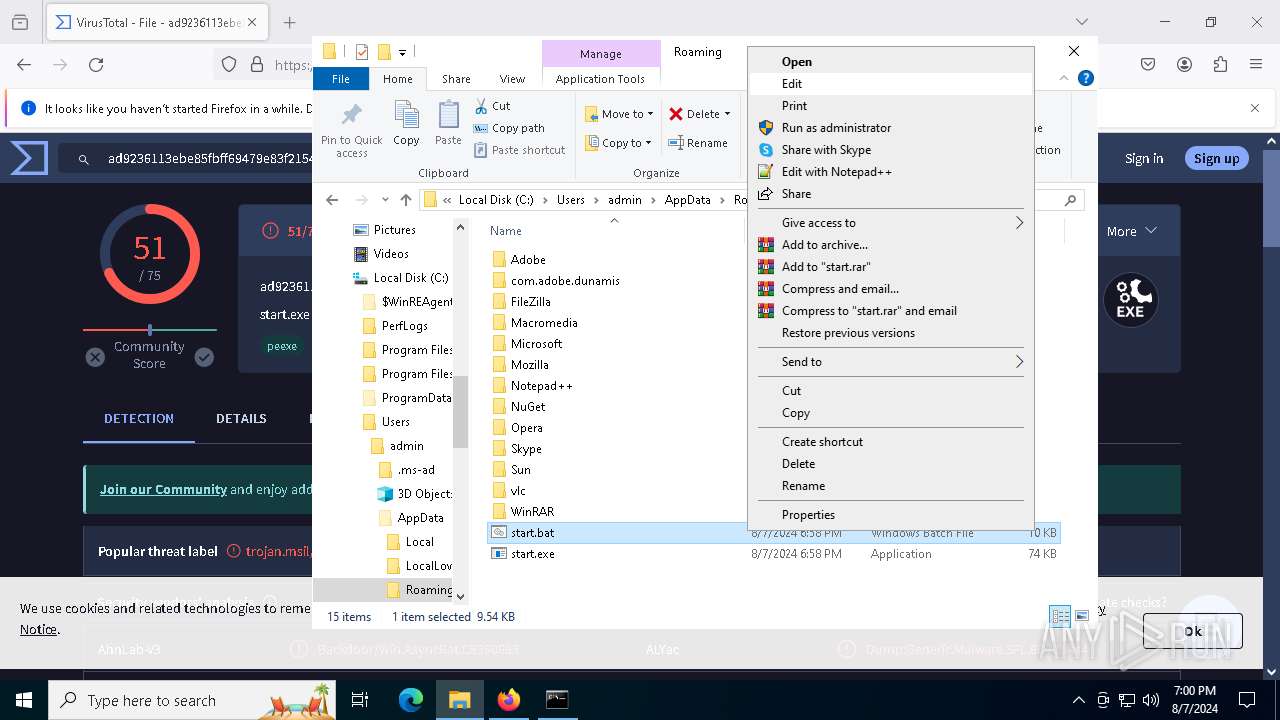
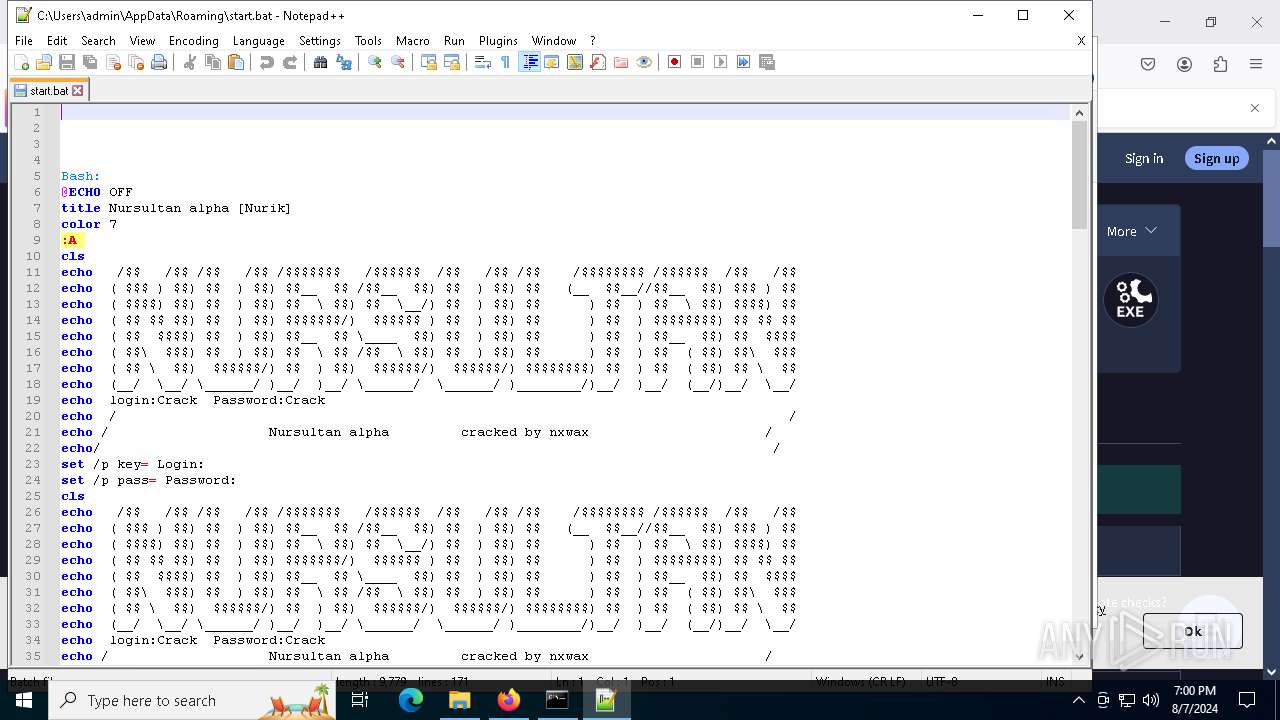
Executing commands from a ".bat" file
- infected.bin.exe (PID: 6392)
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
Connects to unusual port
- start.exe (PID: 6508)
Contacting a server suspected of hosting an CnC
- start.exe (PID: 6508)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5900)
- cmd.exe (PID: 6468)
Checks for external IP
- svchost.exe (PID: 2256)
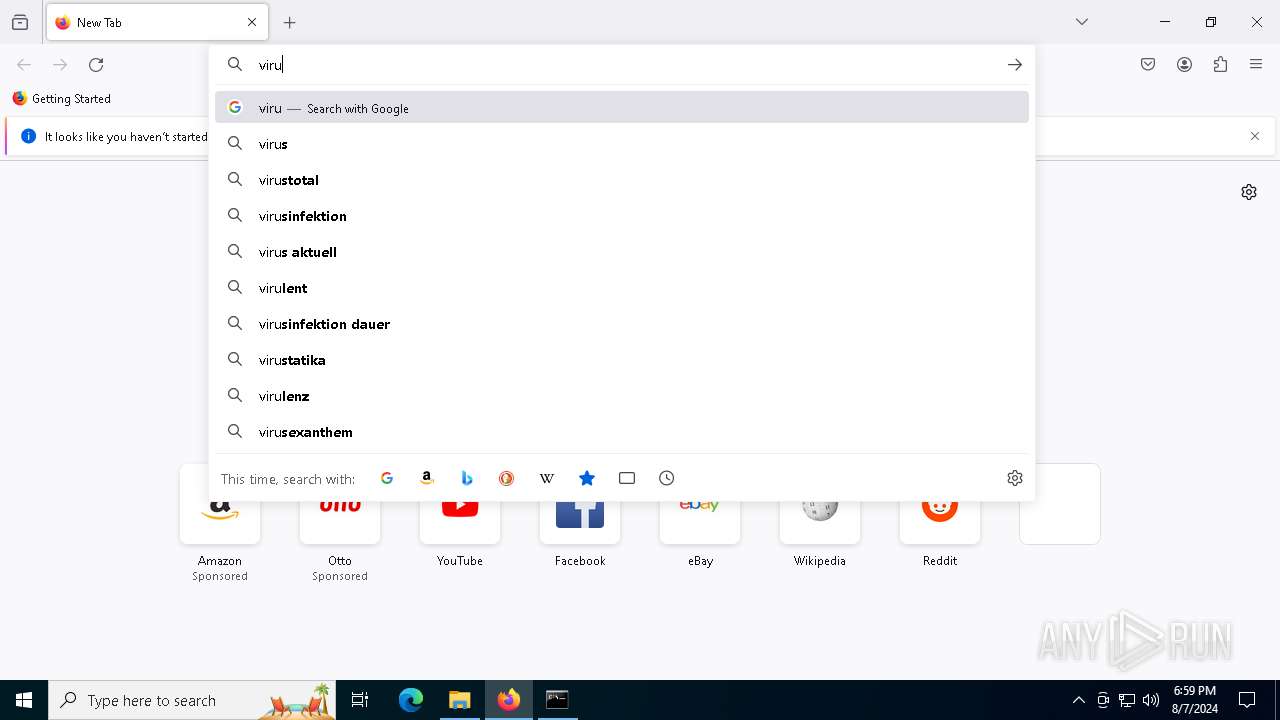
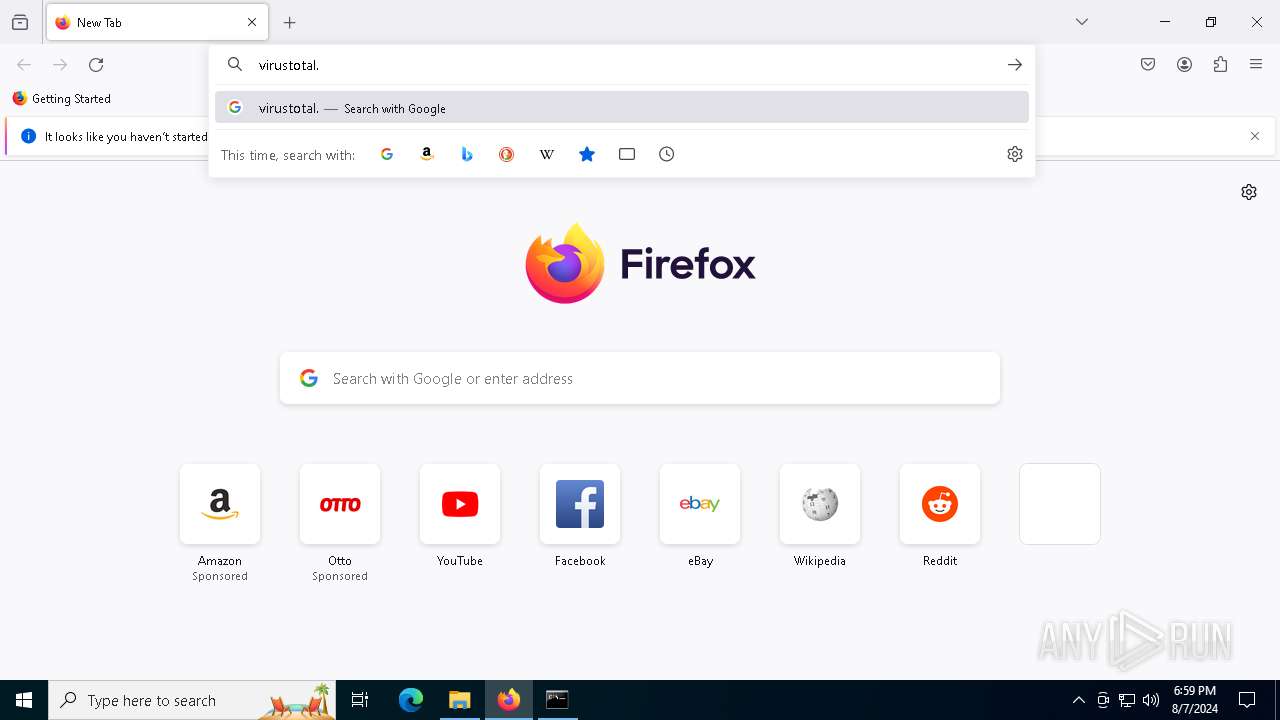
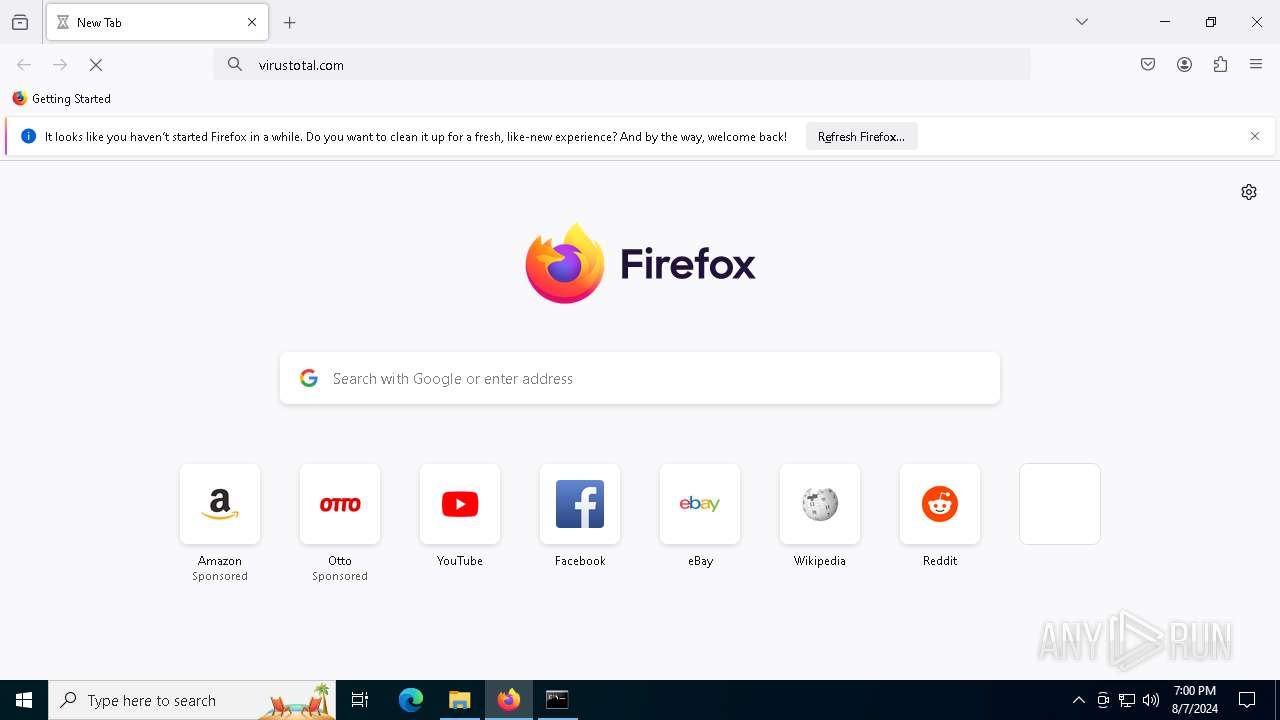
- start.exe (PID: 6508)
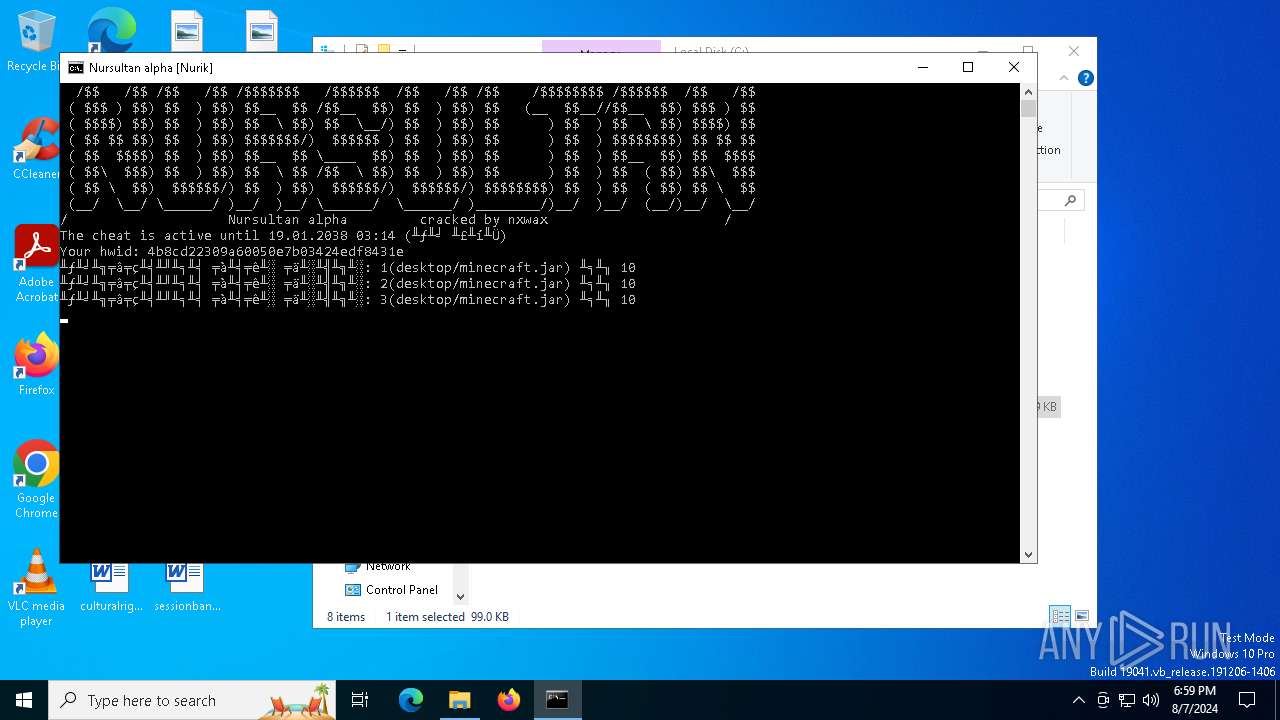
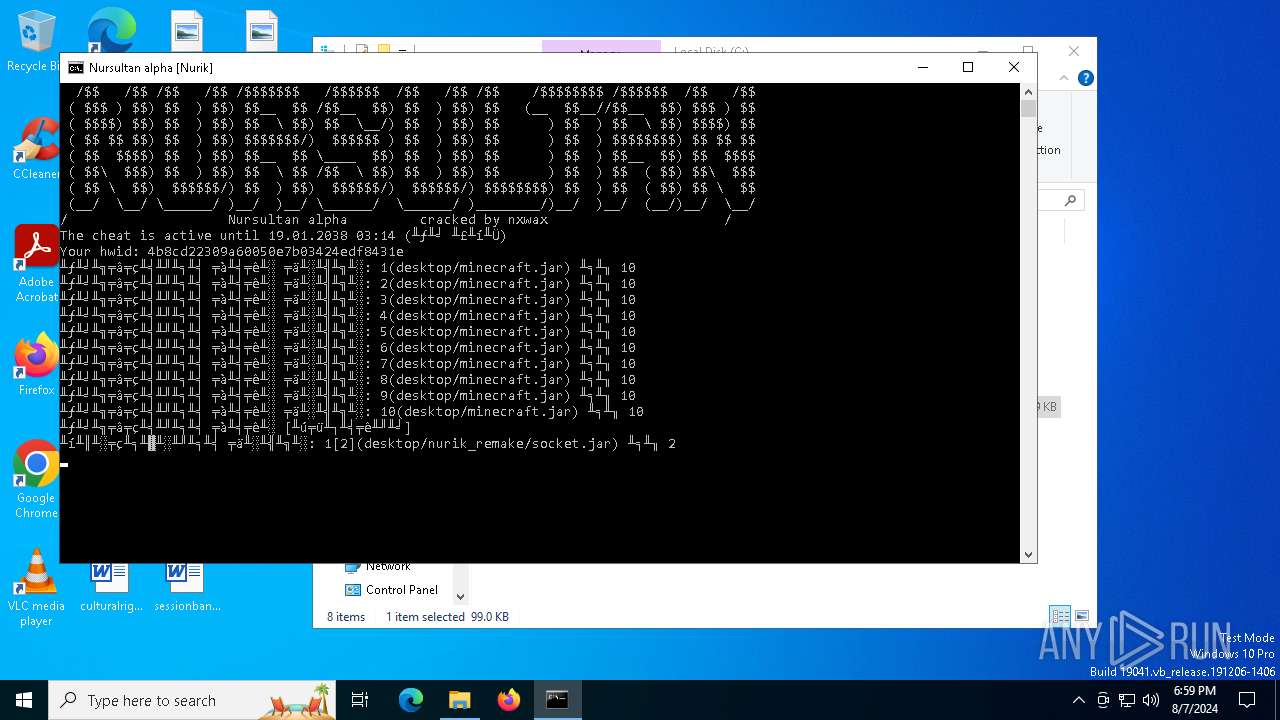
Checks for Java to be installed
- java.exe (PID: 5116)
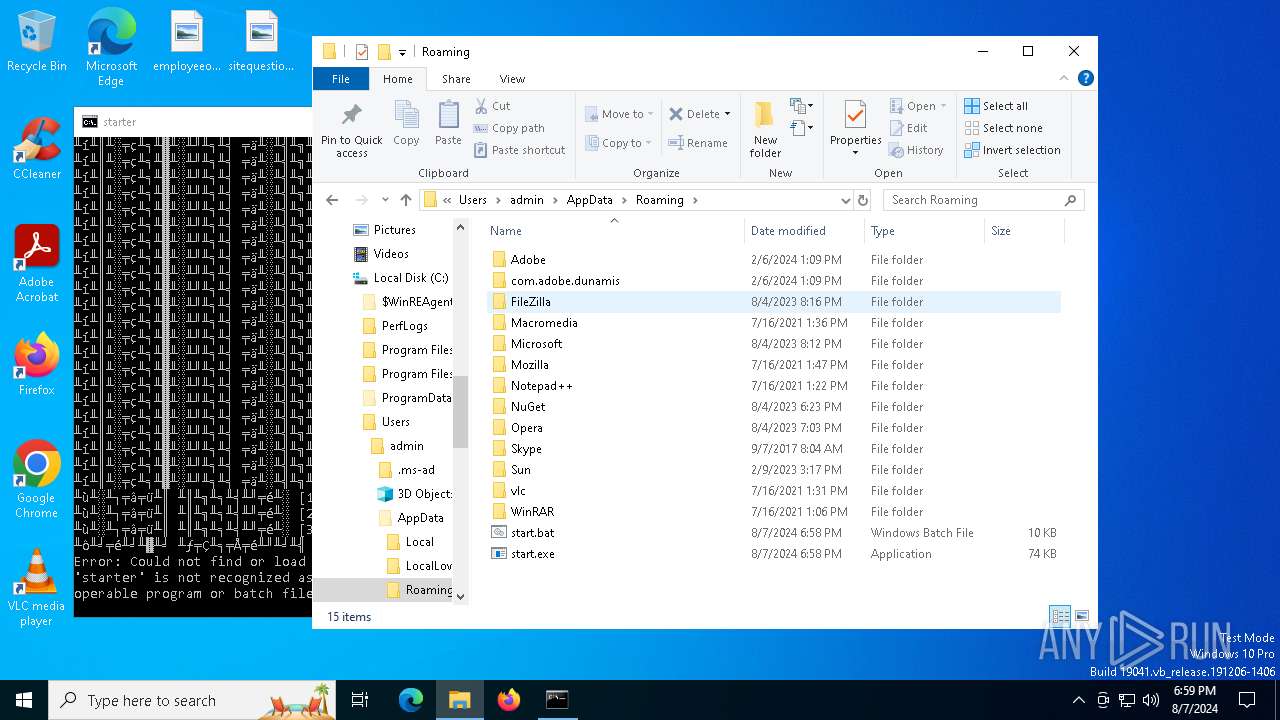
Loads DLL from Mozilla Firefox
- start.exe (PID: 6508)
INFO
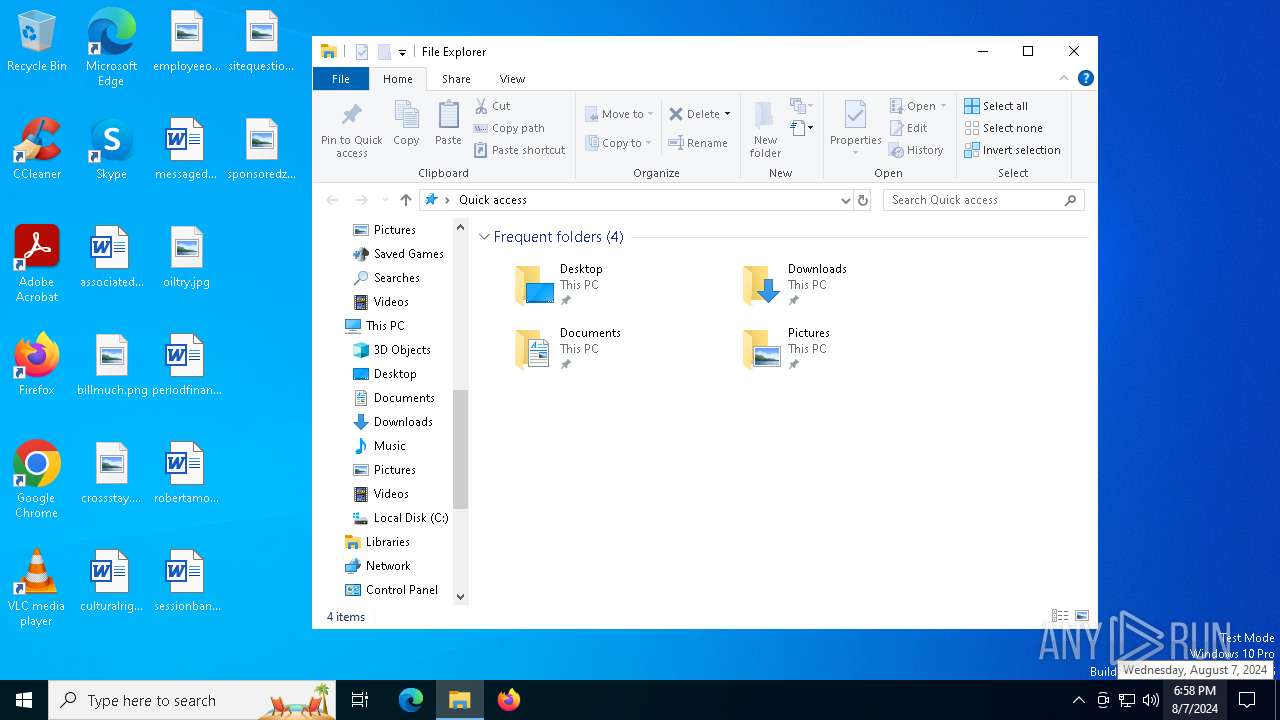
Creates files or folders in the user directory
- infected.bin.exe (PID: 6392)
- start.exe (PID: 6508)
Process checks computer location settings
- infected.bin.exe (PID: 6392)
- start.exe (PID: 6508)
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
Checks supported languages
- start.exe (PID: 6508)
- infected.bin.exe (PID: 6392)
- infected.bin.exe (PID: 3700)
- start.exe (PID: 5484)
- infected.bin.exe (PID: 3184)
- java.exe (PID: 5116)
- TextInputHost.exe (PID: 1360)
- start.exe (PID: 1420)
Reads the computer name
- start.exe (PID: 6508)
- infected.bin.exe (PID: 6392)
- infected.bin.exe (PID: 3700)
- start.exe (PID: 5484)
- infected.bin.exe (PID: 3184)
- TextInputHost.exe (PID: 1360)
- start.exe (PID: 1420)
Reads Environment values
- start.exe (PID: 6508)
Reads the machine GUID from the registry
- start.exe (PID: 6508)
- infected.bin.exe (PID: 6392)
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
- start.exe (PID: 5484)
- start.exe (PID: 1420)
Disables trace logs
- start.exe (PID: 6508)
Checks proxy server information
- start.exe (PID: 6508)
Creates files in the program directory
- start.exe (PID: 6508)
- java.exe (PID: 5116)
Reads the software policy settings
- start.exe (PID: 6508)
Create files in a temporary directory
- start.exe (PID: 6508)
- java.exe (PID: 5116)
Manual execution by a user
- infected.bin.exe (PID: 3700)
- infected.bin.exe (PID: 3184)
- firefox.exe (PID: 3520)
- notepad++.exe (PID: 7280)
- mmc.exe (PID: 8092)
- mmc.exe (PID: 8168)
Application launched itself
- firefox.exe (PID: 5032)
- firefox.exe (PID: 3520)
Reads Microsoft Office registry keys
- firefox.exe (PID: 5032)
Reads security settings of Internet Explorer
- mmc.exe (PID: 8168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
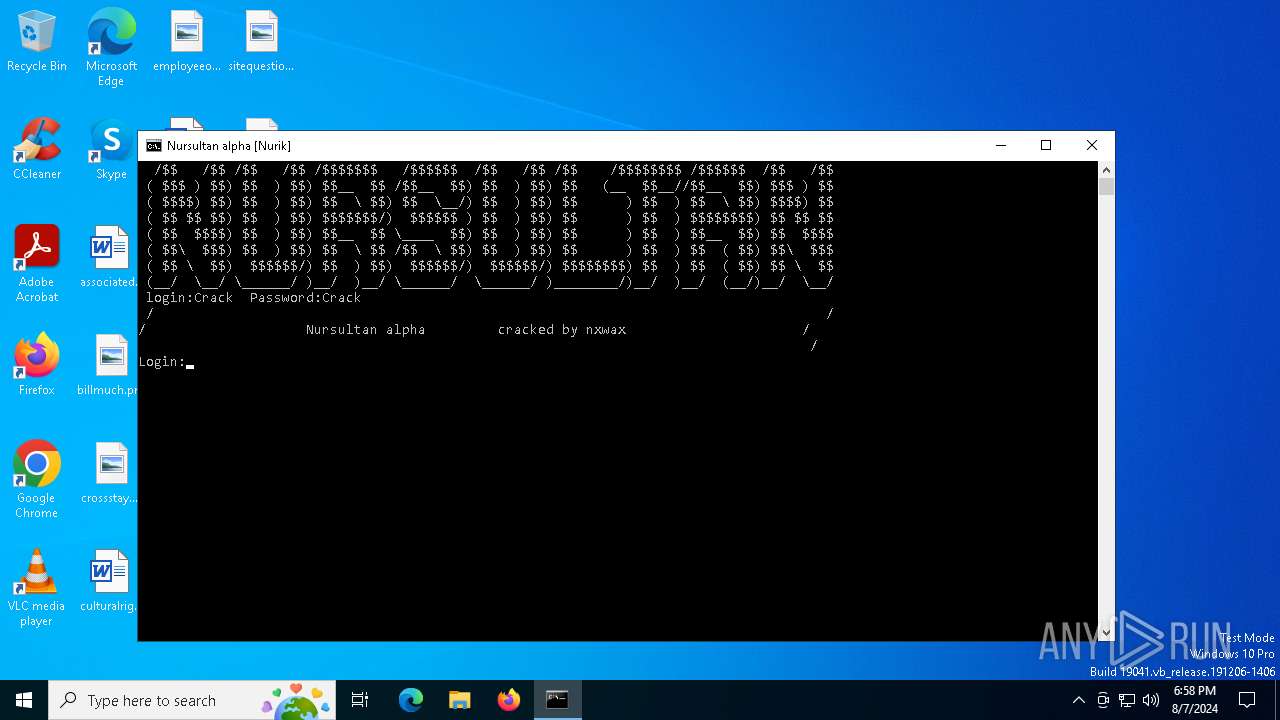
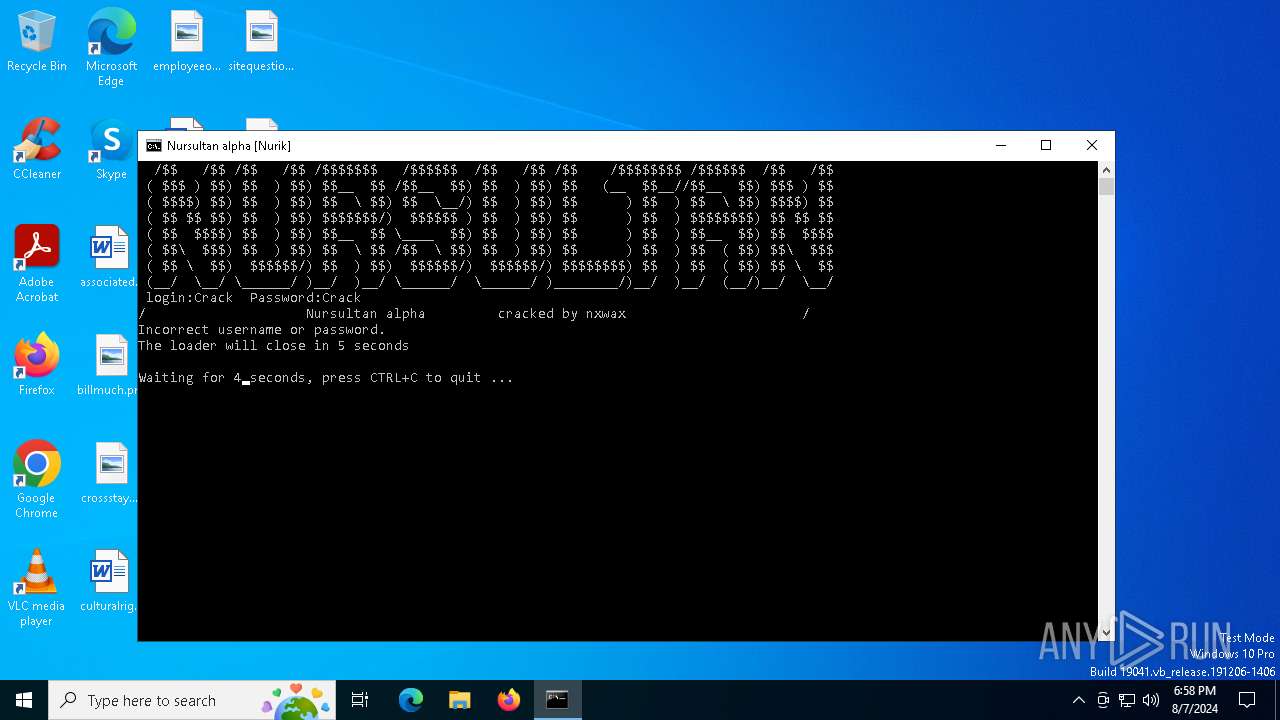
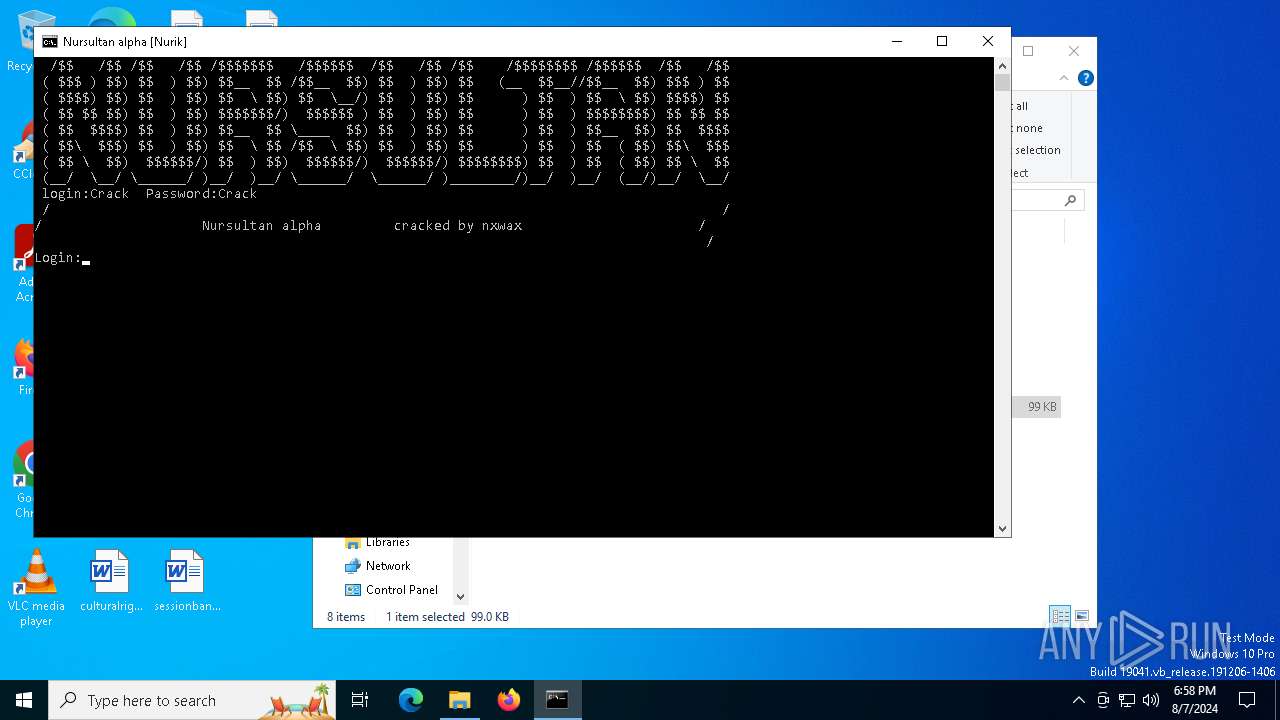
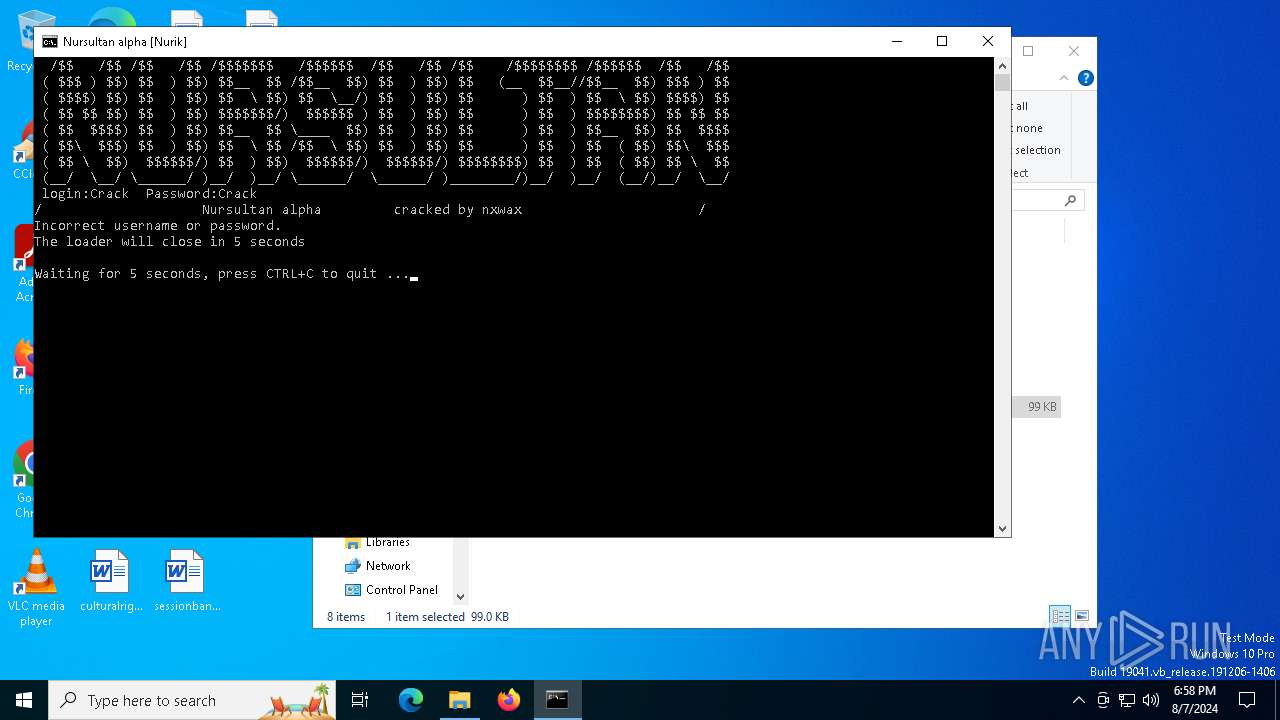
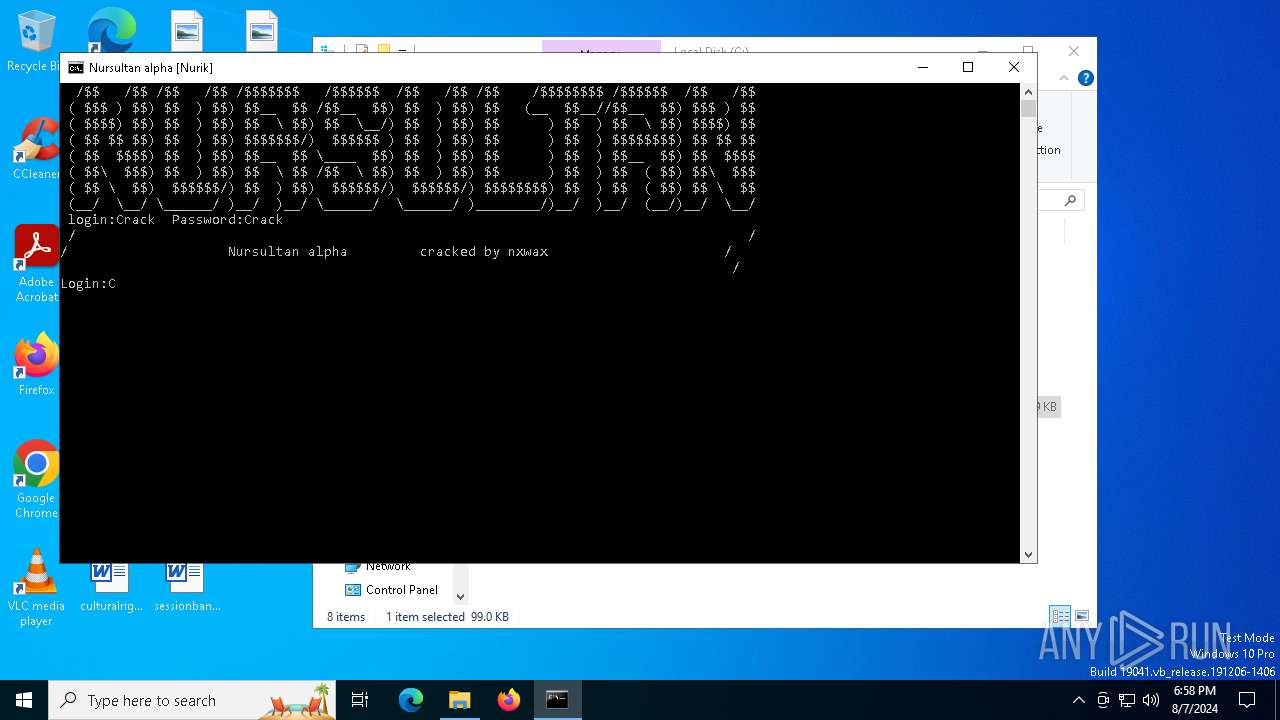
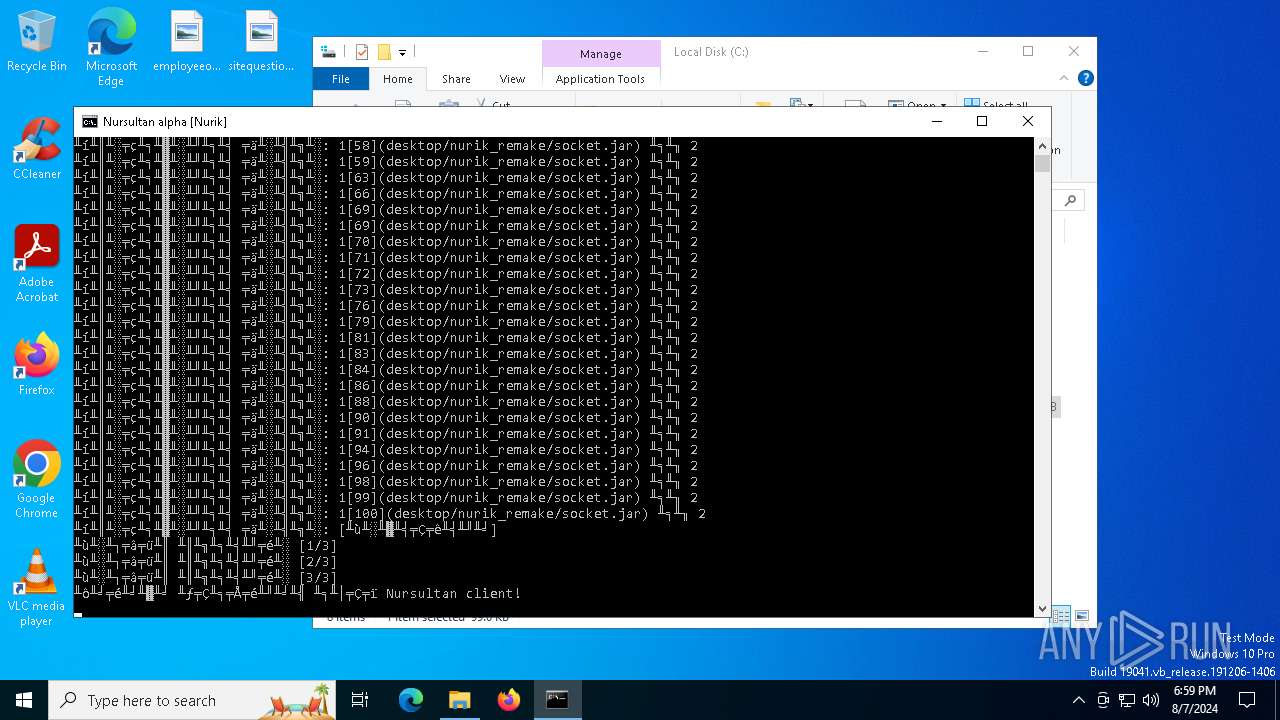
XWorm
(PID) Process(6508) start.exe
C2https://pastebin.com/raw/BdgsZDZW:<123456789>
Keys
AES<Xwormmm>
Options
Splitter3
Sleep timeMicrosoft Edge
USB drop nameUSB.exe
MutexJt3xVhX1JuppTtED
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:07 14:26:04+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 98816 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a11e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | start.exe |
| LegalCopyright: | |
| OriginalFileName: | start.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
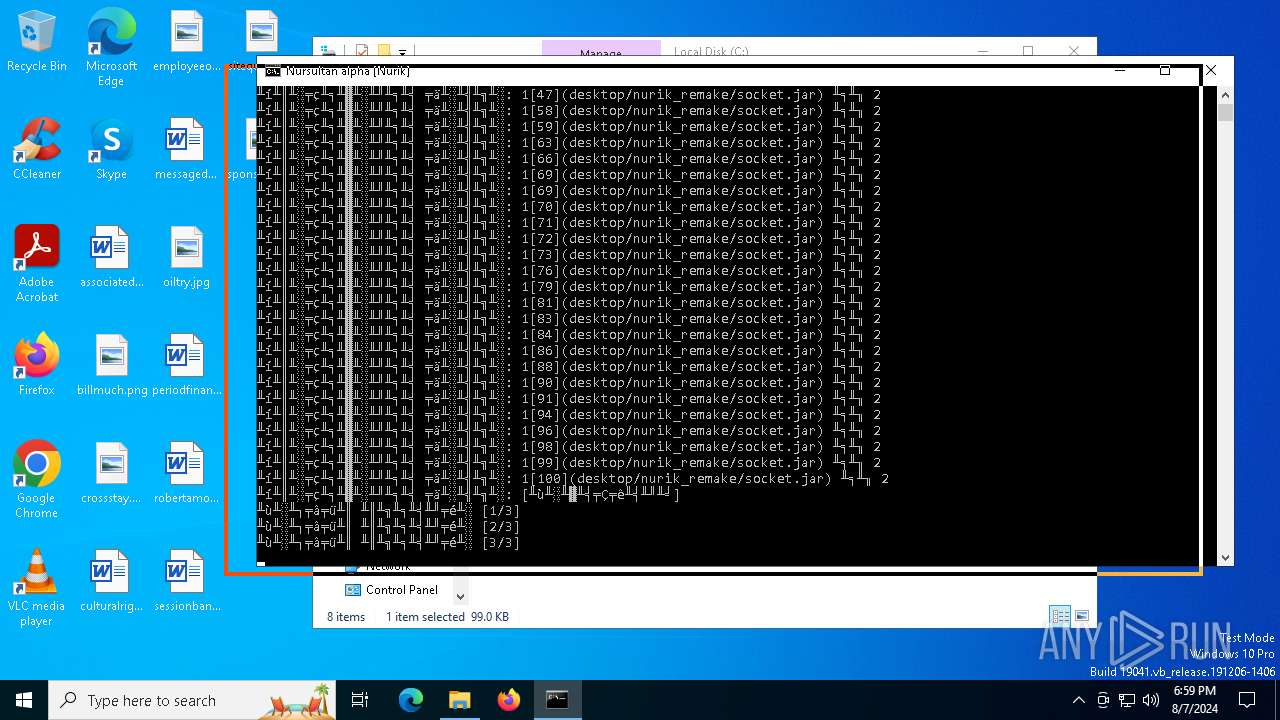
Total processes
219
Monitored processes
82
Malicious processes
3
Suspicious processes
2
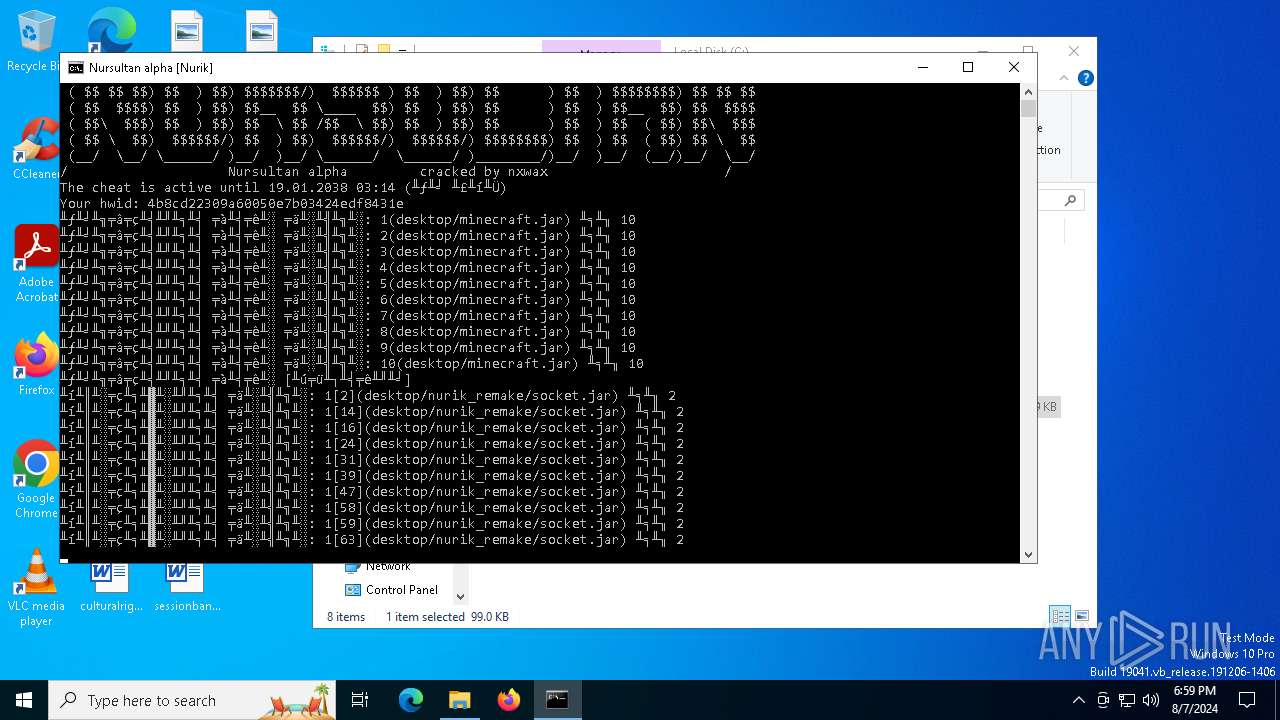
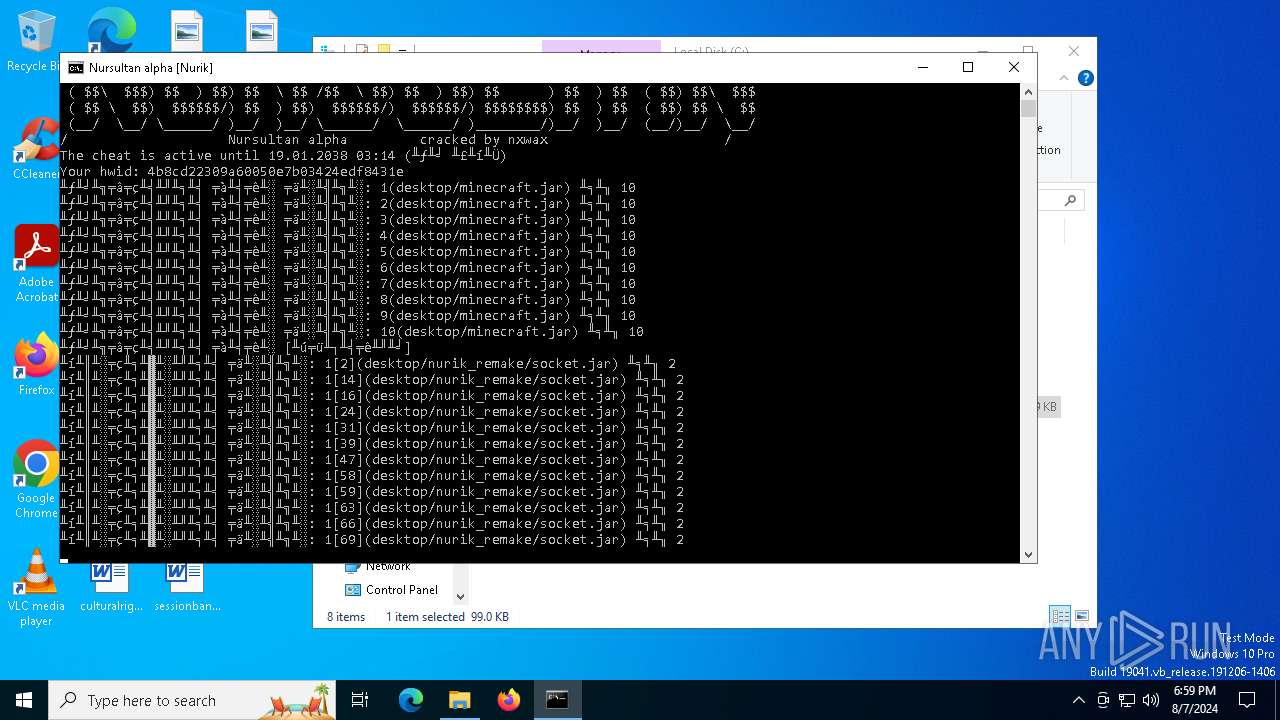
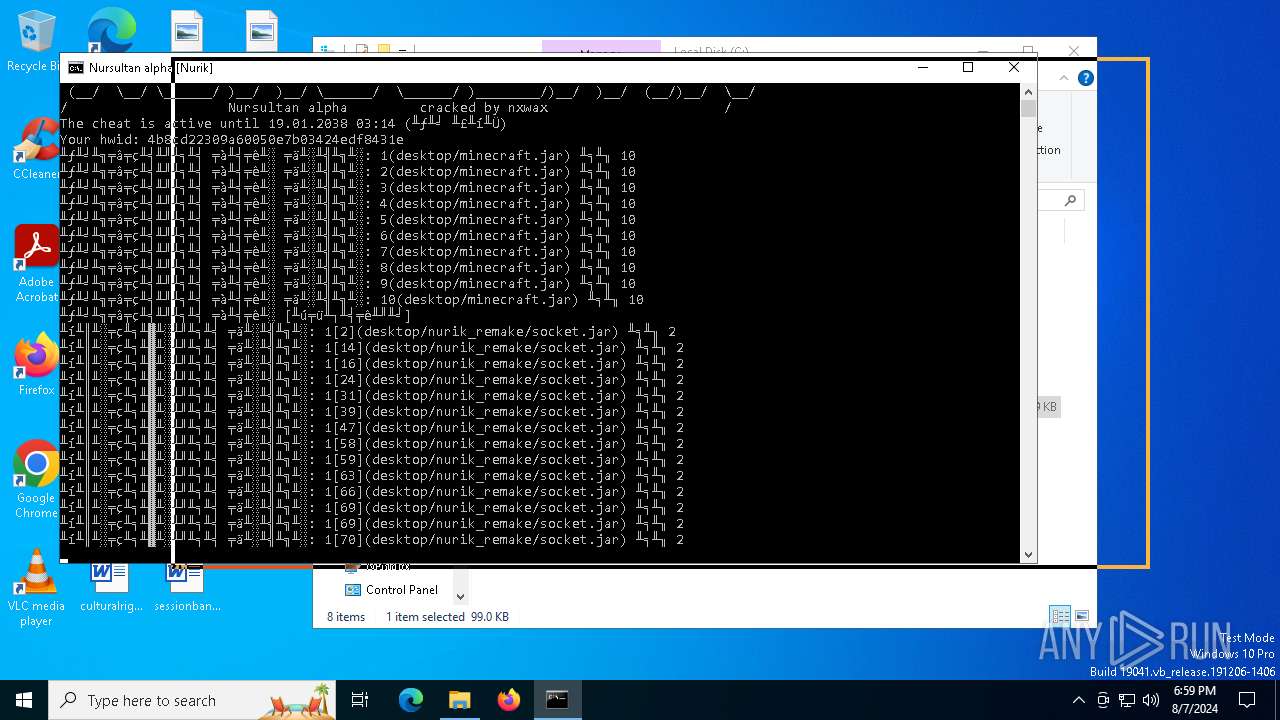
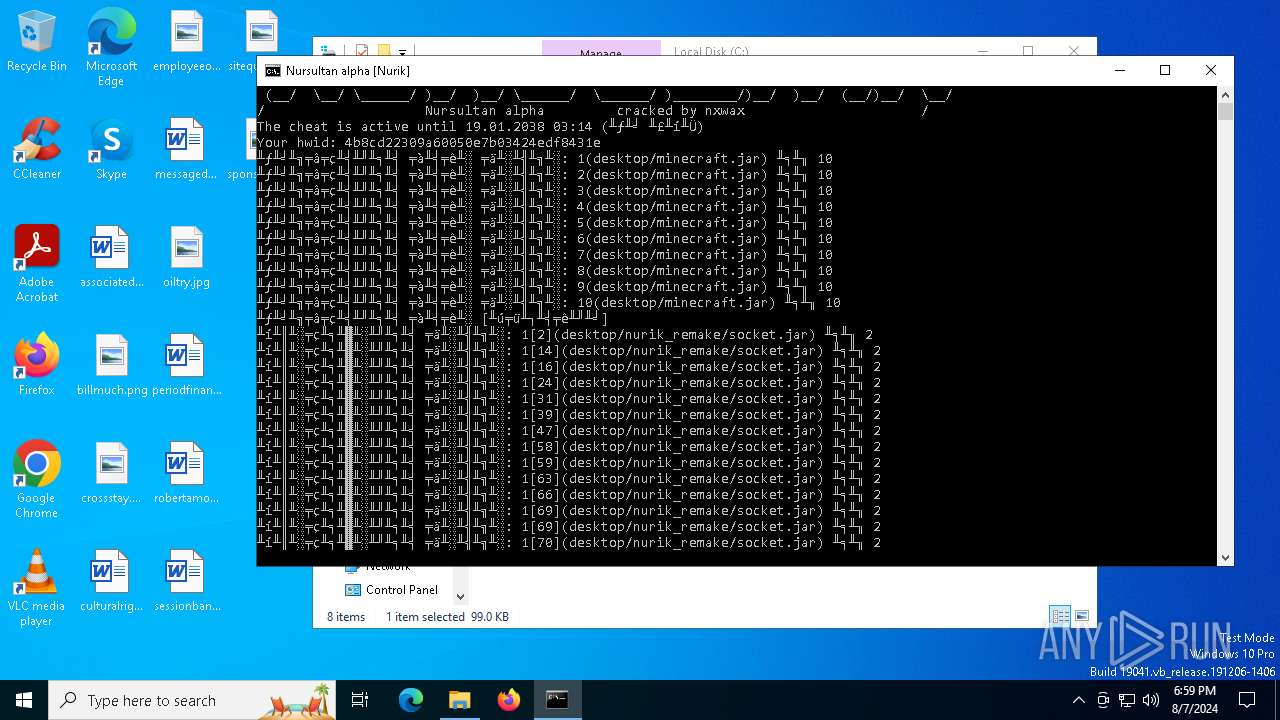
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | ping 1.1.1.2 -n 1 -w 2000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | ping 1.1.1.2 -n 3 -w 2000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\start.bat" " | C:\Windows\System32\cmd.exe | — | infected.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | ping 1.1.1.2 -n 2 -w 8000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1360 | ping 1.1.1.2 -n 1 -w 2000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1360 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 1420 | "C:\Users\admin\AppData\Roaming\start.exe" | C:\Users\admin\AppData\Roaming\start.exe | — | infected.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5676 -childID 5 -isForBrowser -prefsHandle 5696 -prefMapHandle 5684 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1444 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f34c8a20-5492-44ea-9b57-c1571a018569} 5032 "\\.\pipe\gecko-crash-server-pipe.5032" 21d08b1f690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6700 -childID 6 -isForBrowser -prefsHandle 6712 -prefMapHandle 5476 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1444 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {bd73f02c-fd99-4dec-948f-b874e73b446c} 5032 "\\.\pipe\gecko-crash-server-pipe.5032" 21d08b1fbd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 653
Read events
40 555
Write events
96
Delete events
2
Modification events
| (PID) Process: | (6392) infected.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6392) infected.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6392) infected.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6392) infected.bin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6508) start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\start_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6508) start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\start_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6508) start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\start_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6508) start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\start_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6508) start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\start_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6508) start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\start_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
2
Suspicious files
197
Text files
38
Unknown types
3
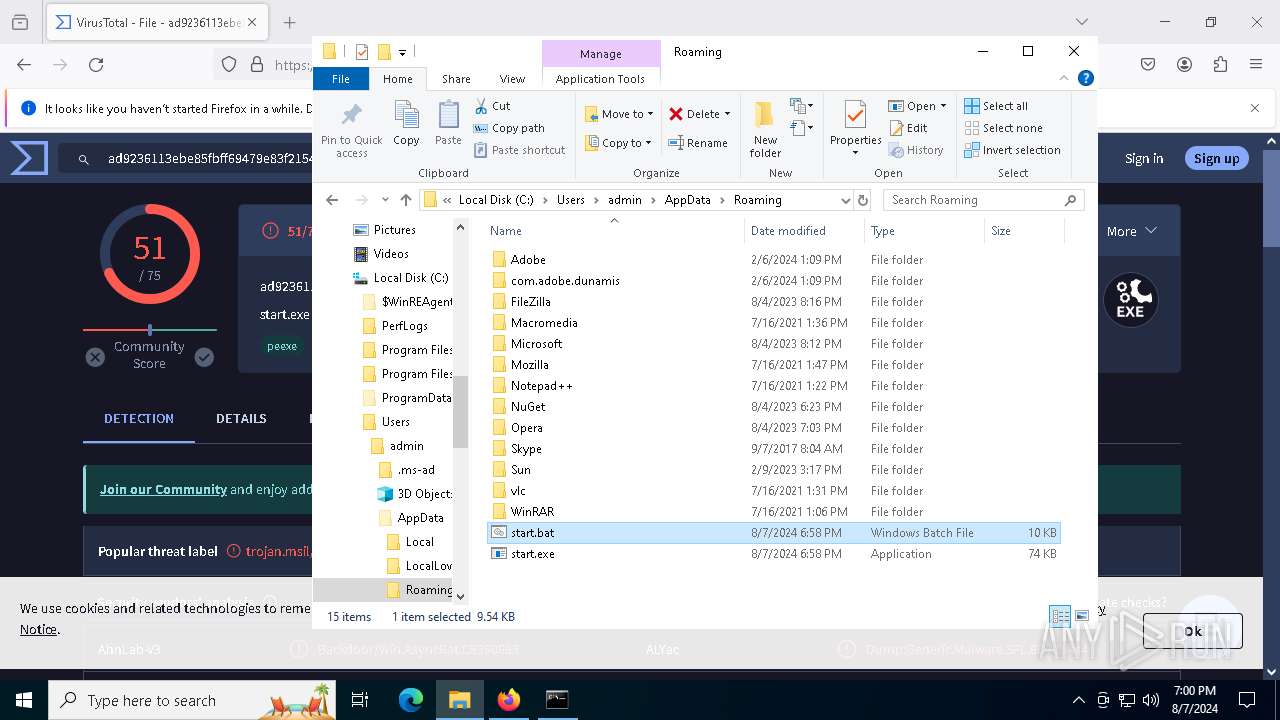
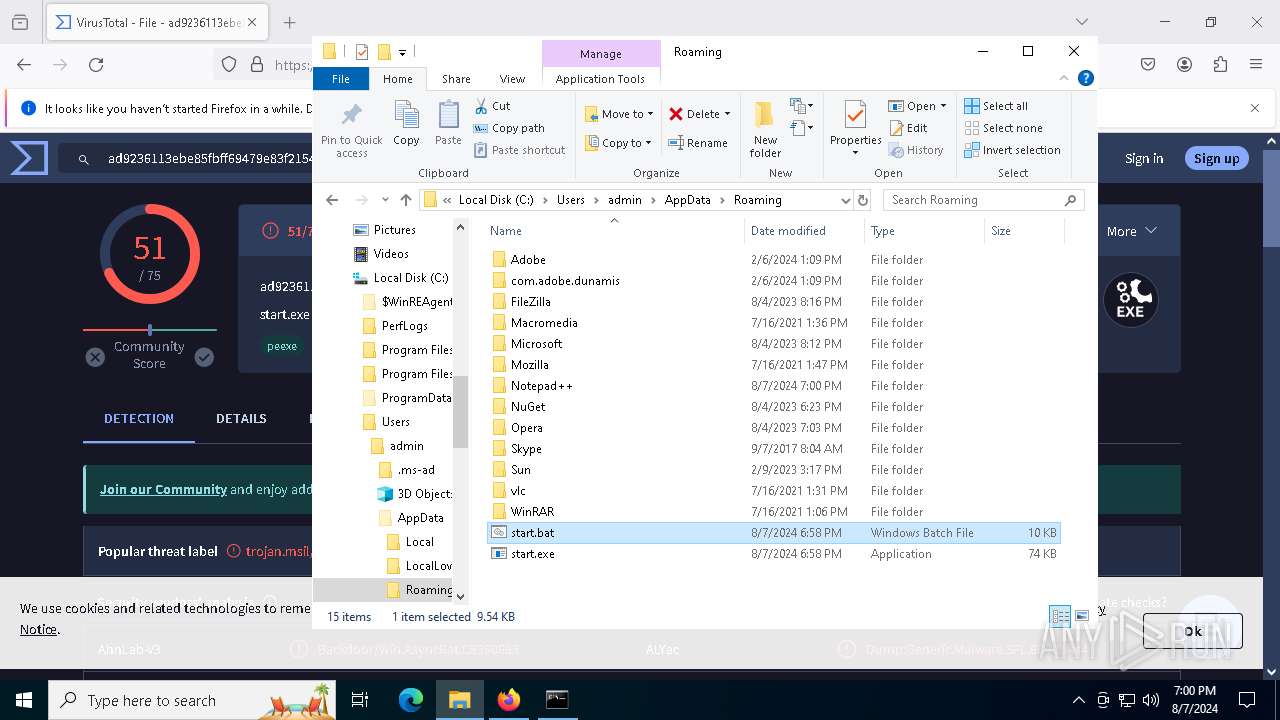
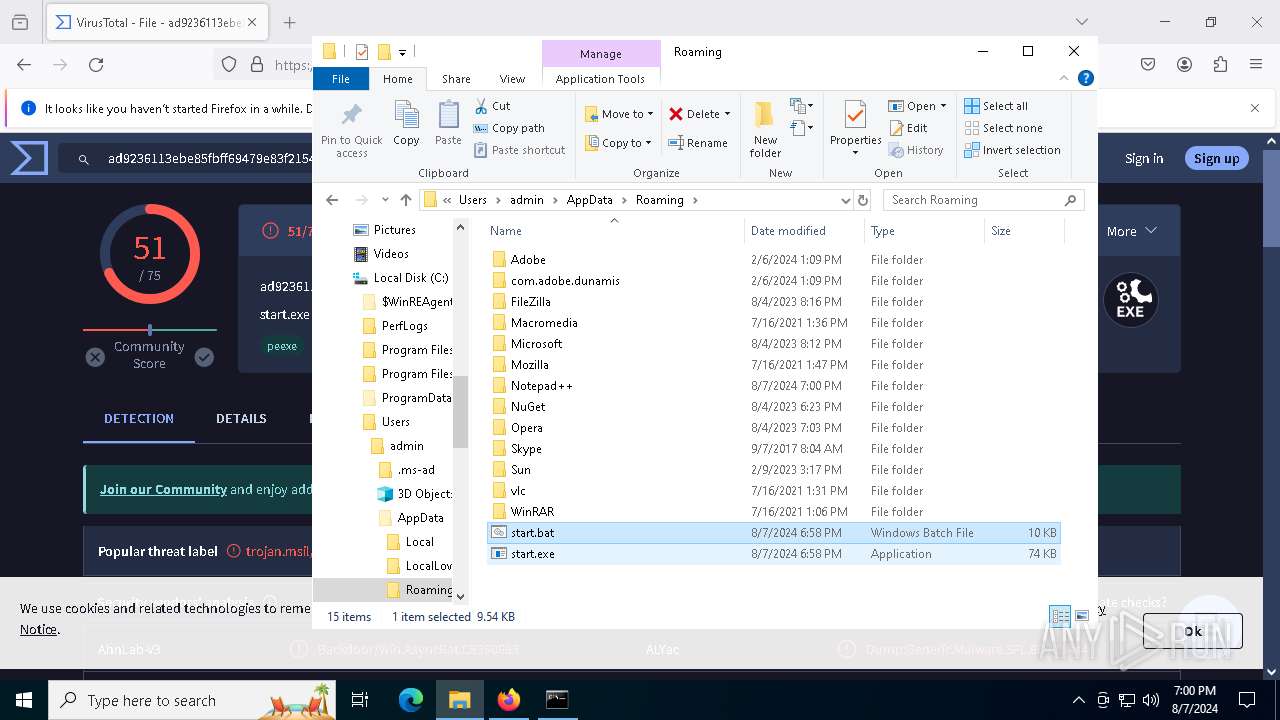
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
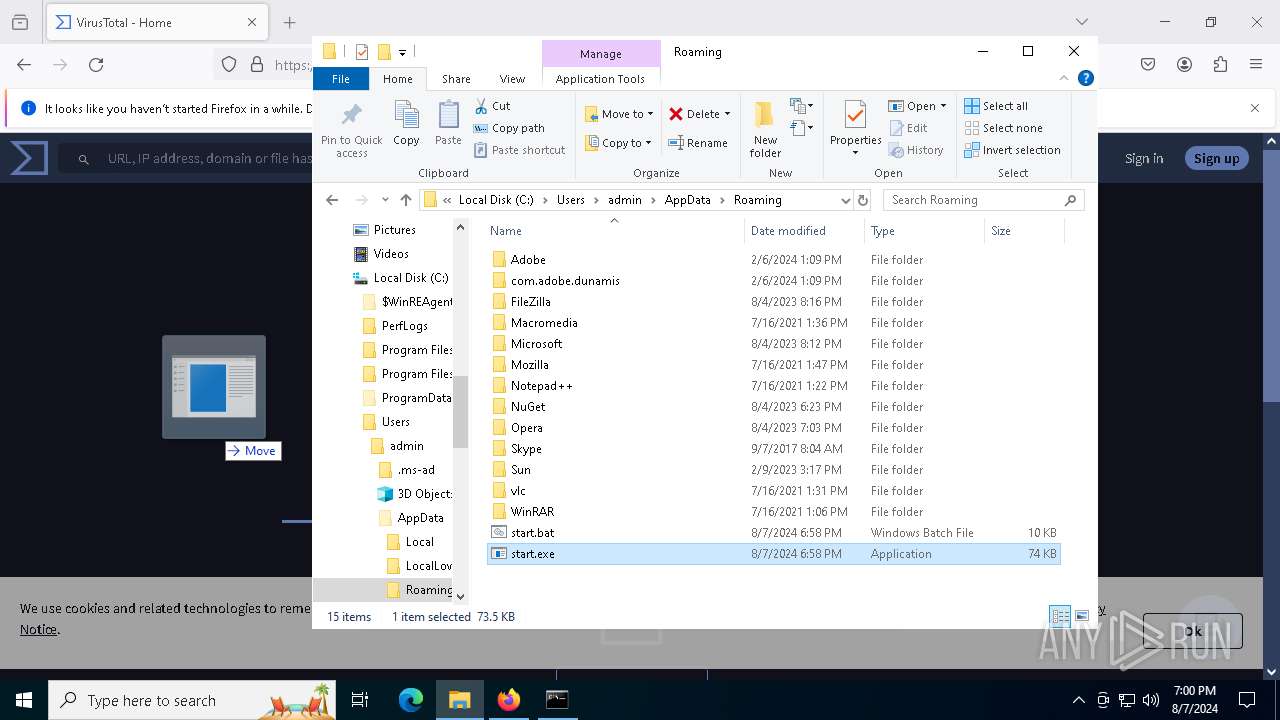
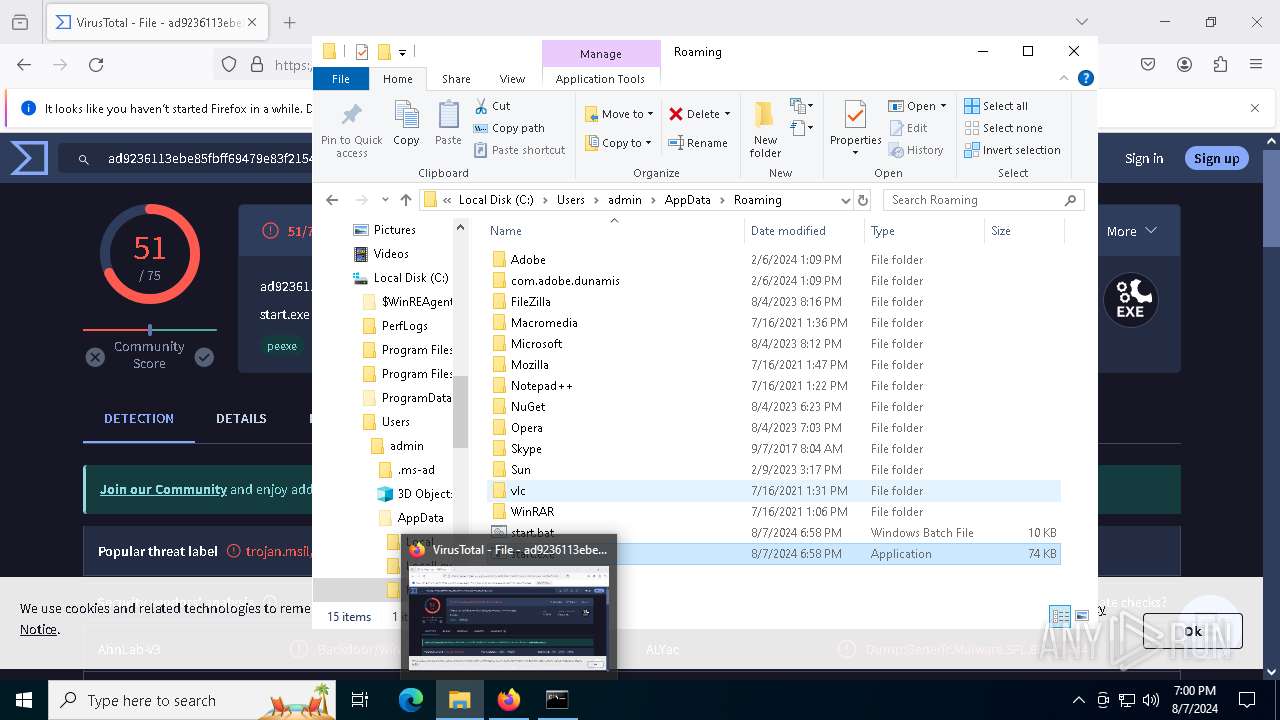
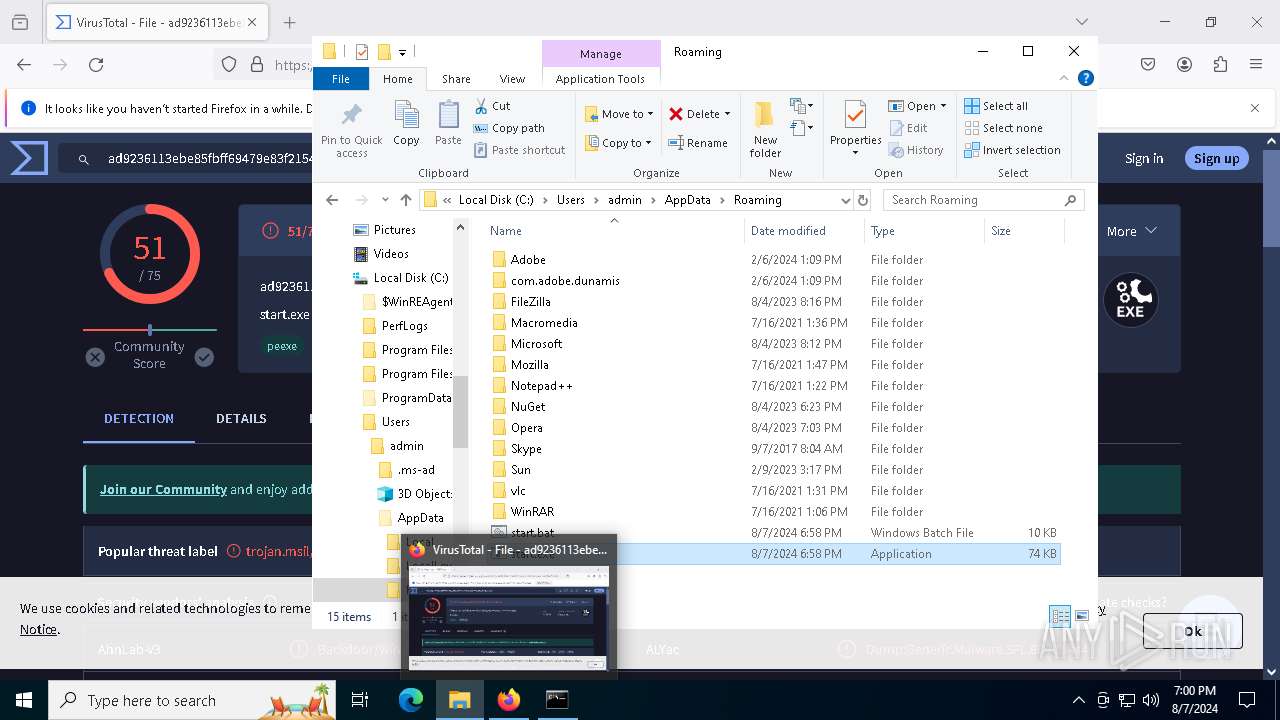
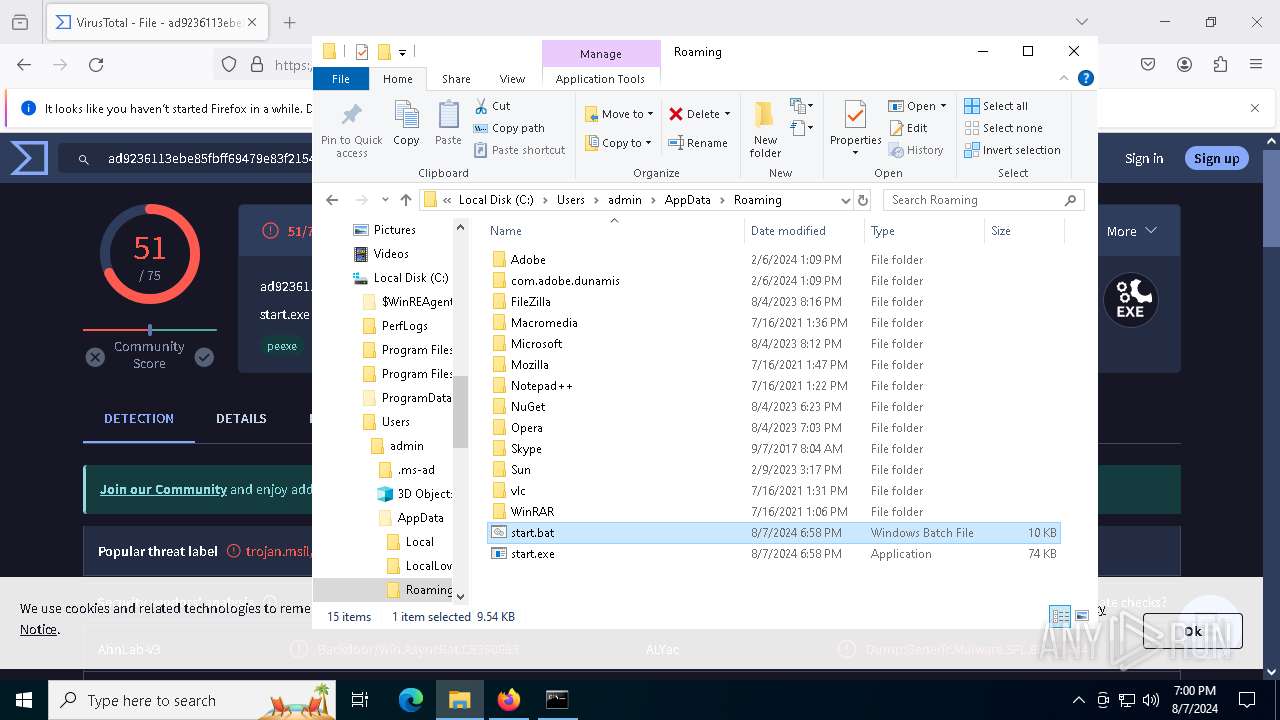
| 6392 | infected.bin.exe | C:\Users\admin\AppData\Roaming\start.bat | text | |
MD5:75E37FB1983DCAAD7E13FF86679E5F91 | SHA256:0840C10333359794796F1404BDE9A82D5705E7064A05785A0D891432FB4E471C | |||
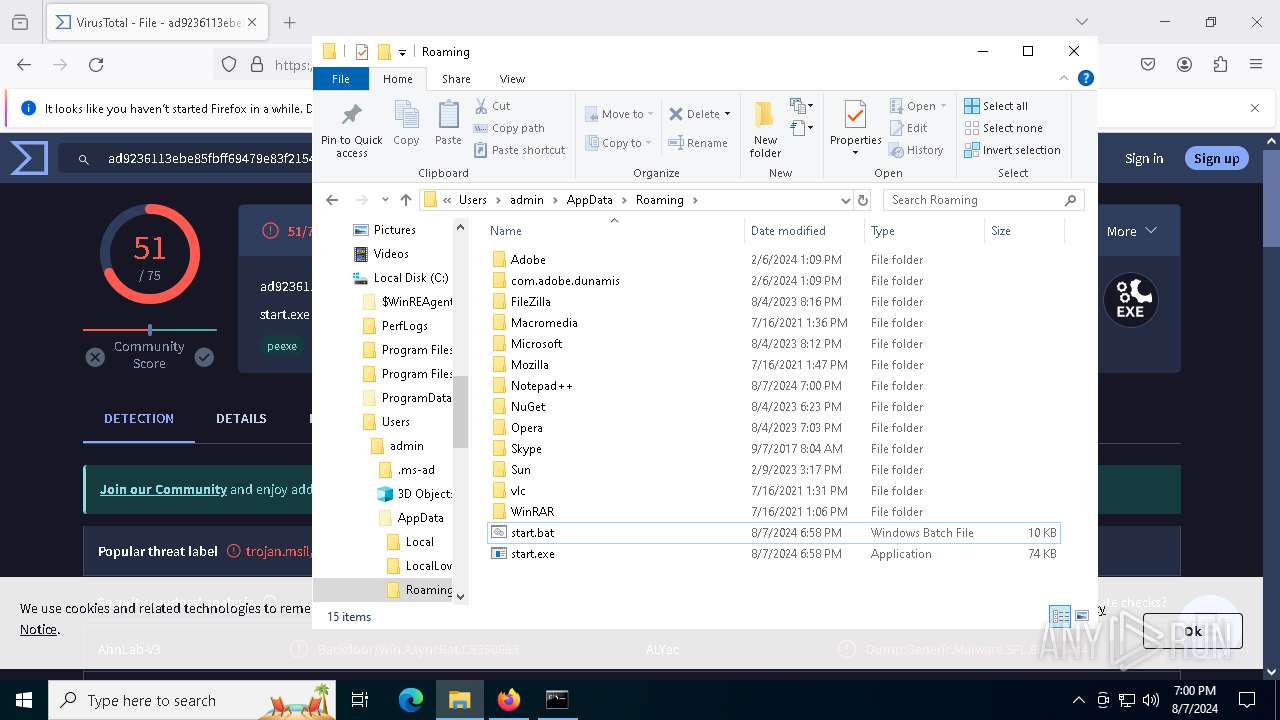
| 6508 | start.exe | C:\ProgramData\Microsoft Edge.exe | executable | |
MD5:671DA6E7194A84289B470B60B5B96AB7 | SHA256:AD9236113EBE85FBFF69479E83F2154CFCF1E52D1960D260E1EC03FC620728EB | |||
| 6508 | start.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Microsoft Edge.lnk | binary | |
MD5:ECF7C653F8E6C8EC9ADDF5405AF3734D | SHA256:EC8723470BD6F9EB35CDE313E4DD362E7A598409F8F894919655A76ECF4C266E | |||
| 6508 | start.exe | C:\Users\admin\AppData\Local\Temp\Log.tmp | text | |
MD5:38CC1188232B1D1FBA64CB76C9EEB4A9 | SHA256:47E8B1A07085634AD33D463756DDA26C534002C8D6B0CA41E0D74C825E0A047D | |||
| 6392 | infected.bin.exe | C:\Users\admin\AppData\Roaming\start.exe | executable | |
MD5:671DA6E7194A84289B470B60B5B96AB7 | SHA256:AD9236113EBE85FBFF69479E83F2154CFCF1E52D1960D260E1EC03FC620728EB | |||
| 5032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5116 | java.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:FA78C42F1E374602E6103067FEA79CDC | SHA256:FB99CF87A26827157389CB49201E702C0365448F6AE2B48A184D0C3C0FBA1EA5 | |||
| 5032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
129
DNS requests
150
Threats
59
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6508 | start.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6488 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6456 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5032 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5032 | firefox.exe | POST | 200 | 216.58.206.67:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
5032 | firefox.exe | POST | 200 | 2.16.202.99:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
5032 | firefox.exe | POST | 200 | 2.16.202.99:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3028 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2632 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6508 | start.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6508 | start.exe | 104.20.3.235:443 | pastebin.com | CLOUDFLARENET | — | unknown |
3028 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6508 | start.exe | 147.185.221.21:55542 | later-tale.gl.at.ply.gg | PLAYIT-GG | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ip-api.com |
| shared |
pastebin.com |
| shared |
later-tale.gl.at.ply.gg |
| malicious |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6508 | start.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6508 | start.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2256 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
6508 | start.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |
52 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|