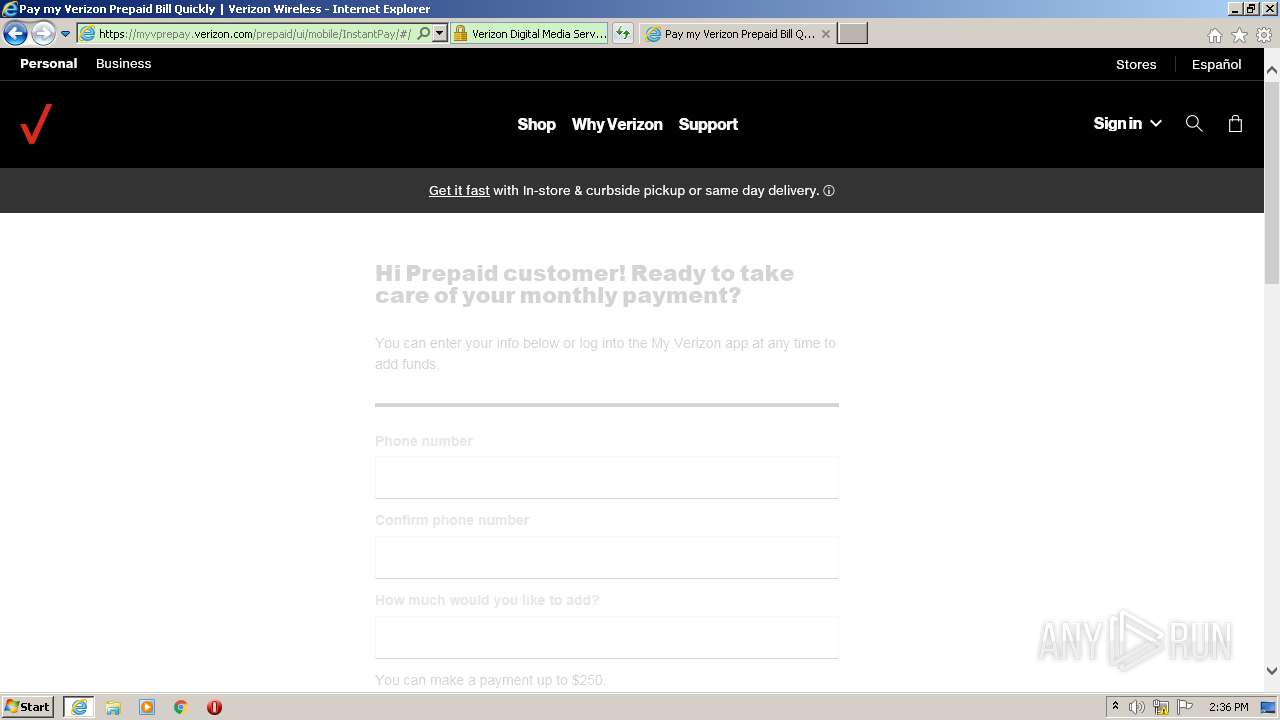
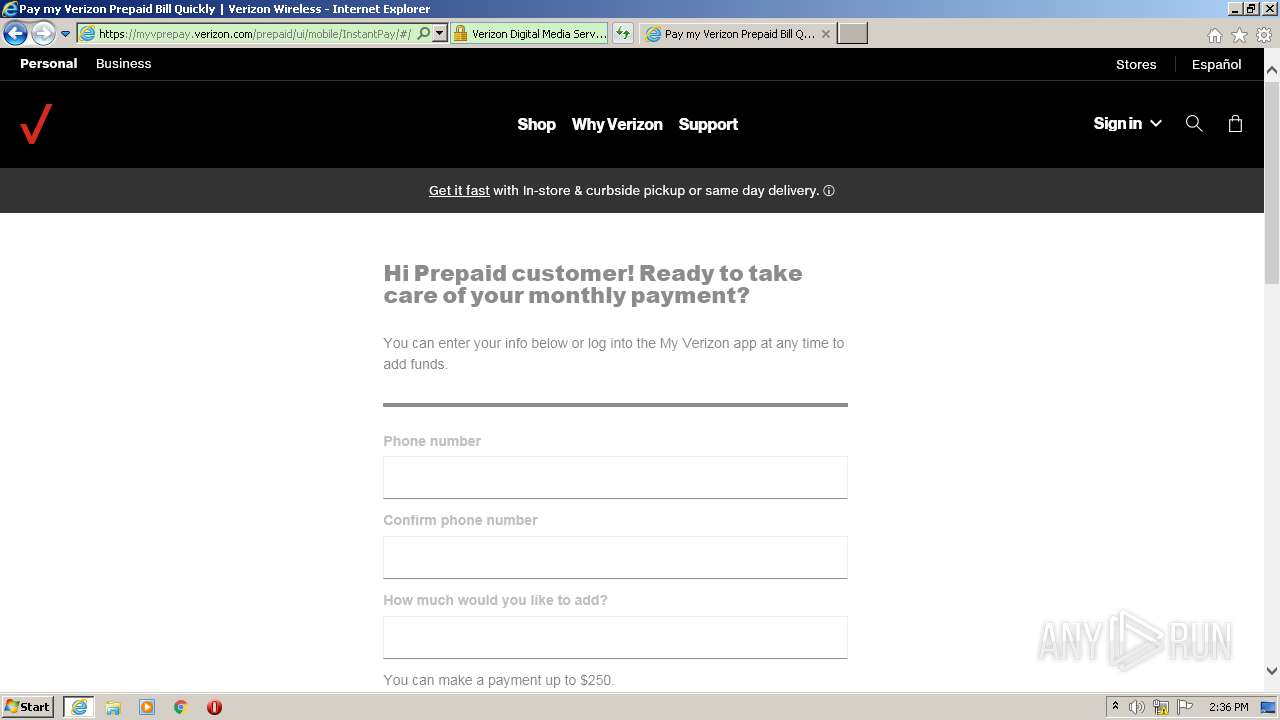
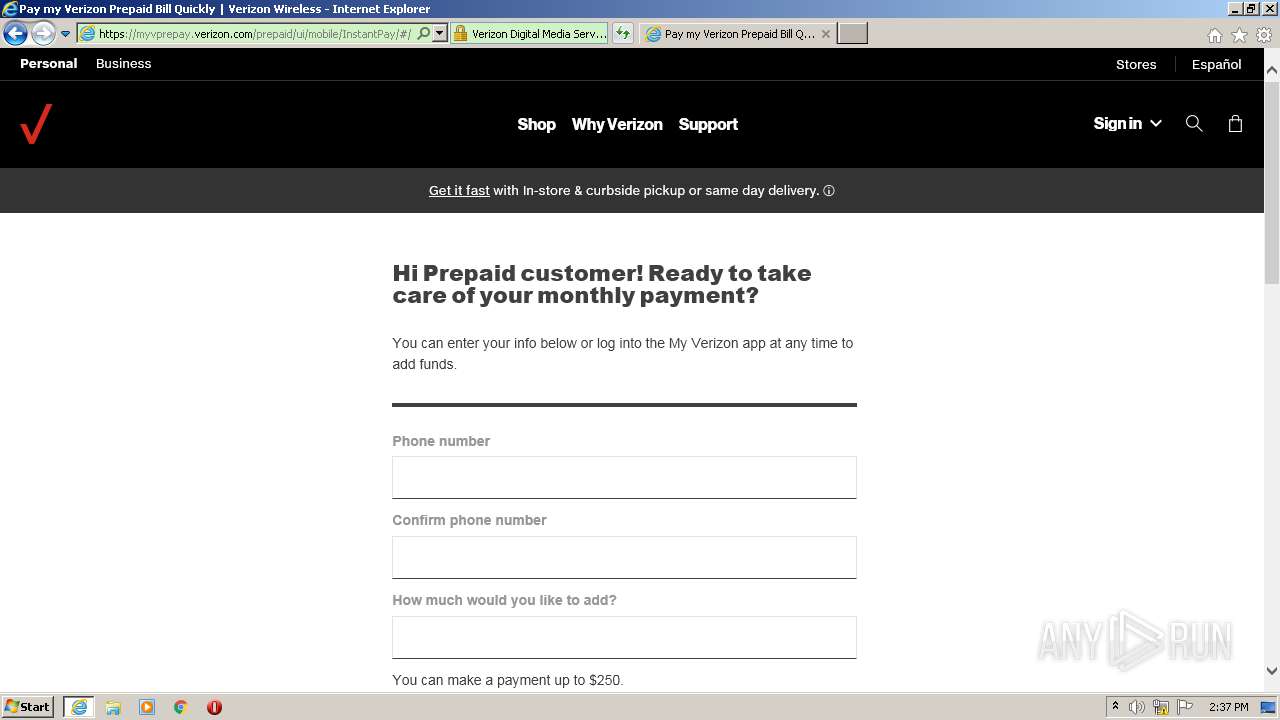
| URL: | https://visit.verizonwireless.com/MzI0LUJaRC0zNTAAAAF8R9-8RcLx34l0xMKvmU4byYrfl7zIWU7oUGGDjlQK4JybFR6FMjj2YomVds0i6Y8wioPkmW4= |
| Full analysis: | https://app.any.run/tasks/56fc4853-9004-47e1-ac73-2dfbfff86193 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2021, 13:34:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C26D1D6DA98C0EAA2207A22702DFACD8 |
| SHA1: | 7B074657115C8A8A288D740DA1085728D57E6D0A |
| SHA256: | 360E5FBBF200BF25DD170475553771D27A2DB2A807C323CC69CE8096DEF1AFBB |
| SSDEEP: | 3:N8ZMWFLfhWWLddx8l5jjuBh9J2j3wbIcMPL1:2ZMcLfnrSjw9JE3wbk5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes settings of System certificates
- iexplore.exe (PID: 2128)
Reads settings of System Certificates
- iexplore.exe (PID: 2128)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 612)
Changes internet zones settings
- iexplore.exe (PID: 2128)
Application launched itself
- iexplore.exe (PID: 2128)
Reads internet explorer settings
- iexplore.exe (PID: 612)
Creates files in the user directory
- iexplore.exe (PID: 2128)
- iexplore.exe (PID: 612)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://visit.verizonwireless.com/MzI0LUJaRC0zNTAAAAF8R9-8RcLx34l0xMKvmU4byYrfl7zIWU7oUGGDjlQK4JybFR6FMjj2YomVds0i6Y8wioPkmW4=" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
631
Read events
444
Write events
183
Delete events
4
Modification events
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3879000468 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30878642 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
196
Text files
263
Unknown types
113
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 612 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFC06.tmp | — | |
MD5:— | SHA256:— | |||
| 612 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFC07.tmp | — | |
MD5:— | SHA256:— | |||
| 612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BEU4BAEC.txt | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabFF61.tmp | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarFF62.tmp | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\0SW73U8W.txt | — | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6CF2.tmp | — | |
MD5:— | SHA256:— | |||
| 612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:— | SHA256:— | |||
| 2128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
266
DNS requests
96
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
612 | iexplore.exe | GET | 301 | 192.30.31.2:80 | http://www.verizonwireless.com/b2c/vzwfly?go=/ContactUsControllerServlet& | US | — | — | unknown |
2128 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
612 | iexplore.exe | GET | 200 | 68.232.35.163:80 | http://cache.vzw.com/stylesheets/accessible.css | US | text | 11.7 Kb | whitelisted |
612 | iexplore.exe | GET | 200 | 68.232.35.163:80 | http://cache.vzw.com/stylesheets/accessiblePrint.css | US | text | 1.12 Kb | whitelisted |
612 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
612 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
2128 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
612 | iexplore.exe | GET | 200 | 68.232.35.163:80 | http://cache.vzw.com/images_b2c/shared/nav/vzwlogo.gif | US | image | 2.80 Kb | whitelisted |
612 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
612 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
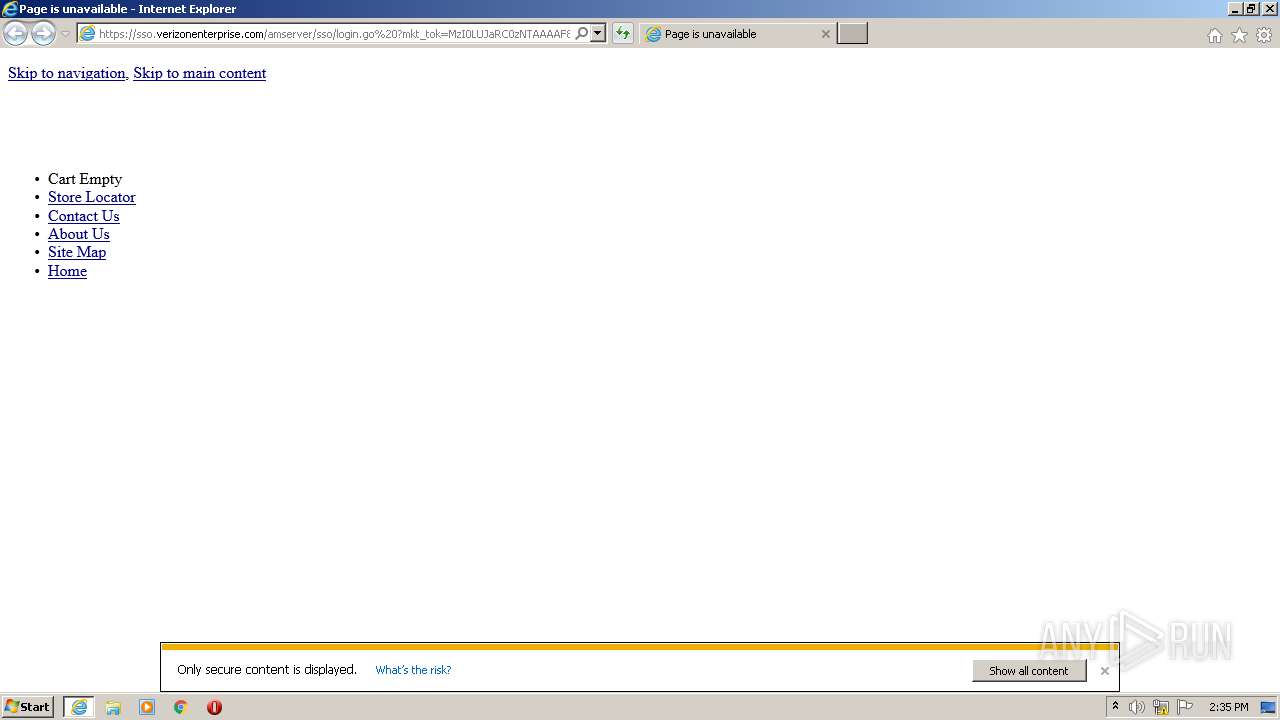
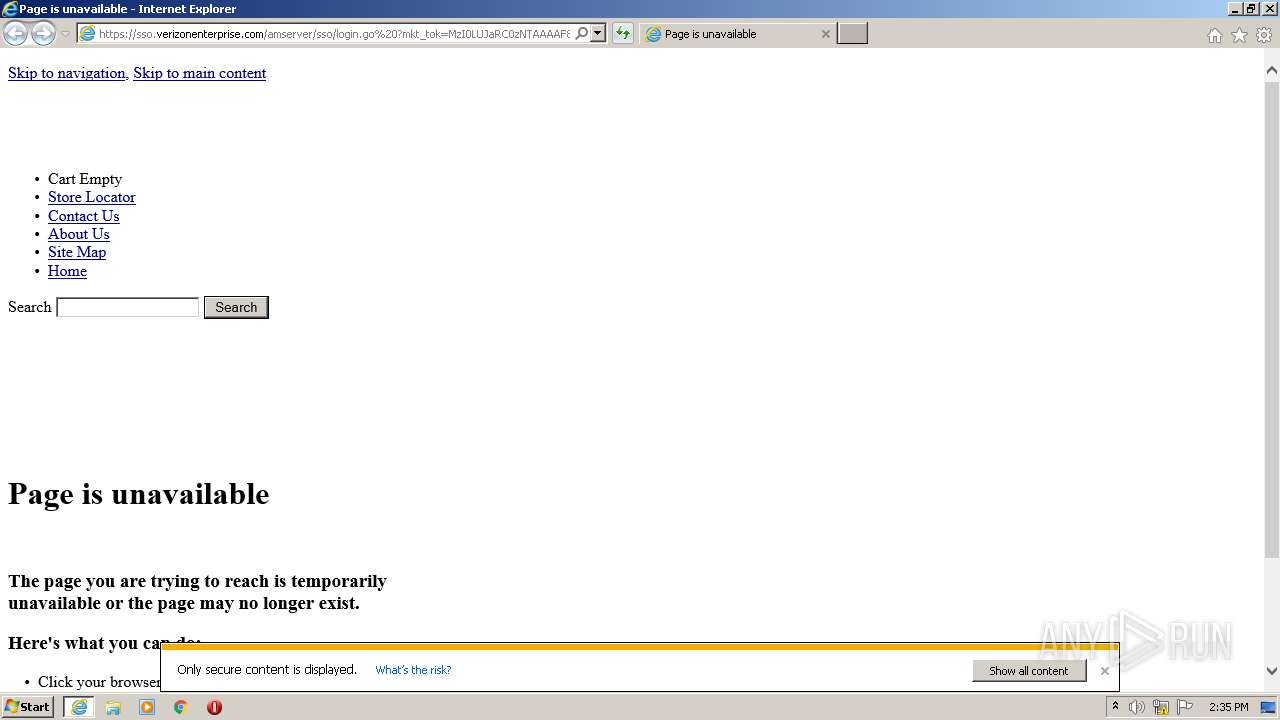
612 | iexplore.exe | 152.199.150.32:443 | sso.verizonenterprise.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
612 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
612 | iexplore.exe | 68.232.35.163:80 | cache.vzw.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2128 | iexplore.exe | 104.17.74.206:443 | visit.verizonwireless.com | Cloudflare Inc | US | shared |
2128 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2128 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2128 | iexplore.exe | 152.199.150.32:443 | sso.verizonenterprise.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
2128 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2128 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
612 | iexplore.exe | 192.30.31.2:80 | www.verizonwireless.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
visit.verizonwireless.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sso.verizonenterprise.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
cache.vzw.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
www.verizonwireless.com |
| unknown |
www.verizon.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |