| File name: | Supreme Bot.exe |
| Full analysis: | https://app.any.run/tasks/69acb7b6-76ce-4ad6-beab-d23b3d30363f |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2020, 13:27:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 821D763F7D693A5D53E23C20225FA856 |
| SHA1: | 76978C1AB51DA3E281A88E35D4CF31EB596DAEDB |
| SHA256: | 360075906350639FB94617E3129258AFC837563B4C2BF8BF79D863872B664378 |
| SSDEEP: | 196608:zMGMMEzczynb/2FUkLpwmJ8EHlfTCW6EWpgNs2It/+nvx1i4Q8xW/nQcjaU31EGq:gGBzynqUKpwCteW6EWpgZG8NQ8xWPrNS |
MALICIOUS
Loads dropped or rewritten executable
- Supreme Bot.exe (PID: 2128)
SUSPICIOUS
Drops a file with a compile date too recent
- Supreme Bot.exe (PID: 2960)
Executable content was dropped or overwritten
- Supreme Bot.exe (PID: 2960)
Application launched itself
- Supreme Bot.exe (PID: 2960)
Drops a file that was compiled in debug mode
- Supreme Bot.exe (PID: 2960)
Loads Python modules
- Supreme Bot.exe (PID: 2128)
INFO
Dropped object may contain Bitcoin addresses
- Supreme Bot.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:05 13:16:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128512 |
| InitializedDataSize: | 187904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7a6a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 05-Jan-2020 12:16:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Jan-2020 12:16:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F4D4 | 0x0001F600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6643 |
.rdata | 0x00021000 | 0x0000B19E | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.11204 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93811 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86299 |
.rsrc | 0x0003D000 | 0x00020724 | 0x00020800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.9762 |
.reloc | 0x0005E000 | 0x000017D4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65456 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.79908 | 90 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.29638 | 1035 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.24549 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.30908 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.3949 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.41294 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.83701 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
WS2_32.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
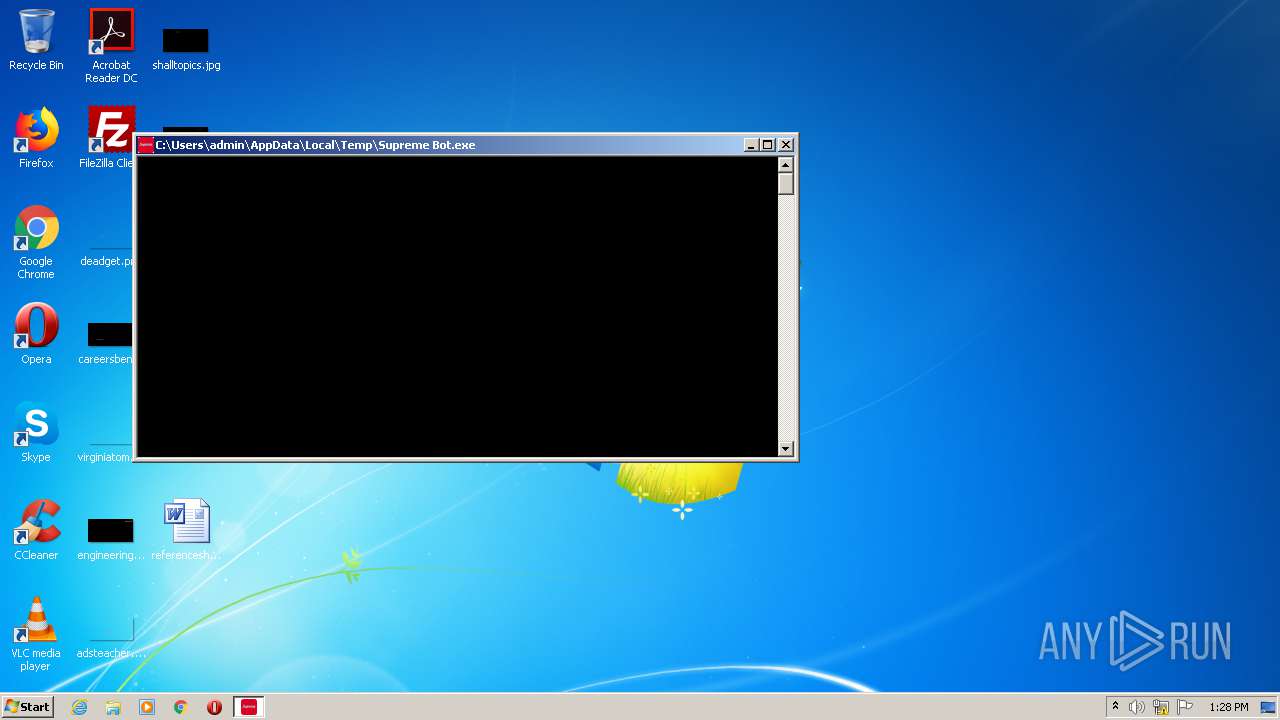
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | "C:\Users\admin\AppData\Local\Temp\Supreme Bot.exe" | C:\Users\admin\AppData\Local\Temp\Supreme Bot.exe | Supreme Bot.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\Supreme Bot.exe" | C:\Users\admin\AppData\Local\Temp\Supreme Bot.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
14
Read events
14
Write events
0
Delete events
0
Modification events
Executable files
66
Suspicious files
1
Text files
6
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_aes.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_ARC4.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_blowfish.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_chacha20.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_cast.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_cbc.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_ctr.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_des.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_Salsa20.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2960 | Supreme Bot.exe | C:\Users\admin\AppData\Local\Temp\_MEI29602\Cryptodome\Cipher\_raw_cfb.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2128 | Supreme Bot.exe | 66.171.248.178:443 | ipv4bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
2128 | Supreme Bot.exe | 195.201.248.89:443 | v2.api.iphub.info | Awanti Ltd. | RU | suspicious |
2128 | Supreme Bot.exe | 162.159.135.233:443 | discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipv4bot.whatismyipaddress.com |
| shared |
v2.api.iphub.info |
| suspicious |
discordapp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2128 | Supreme Bot.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
1 ETPRO signatures available at the full report