| download: | /Da2dalus/The-MALWARE-Repo/blob/master/Virus/MadMan.exe |
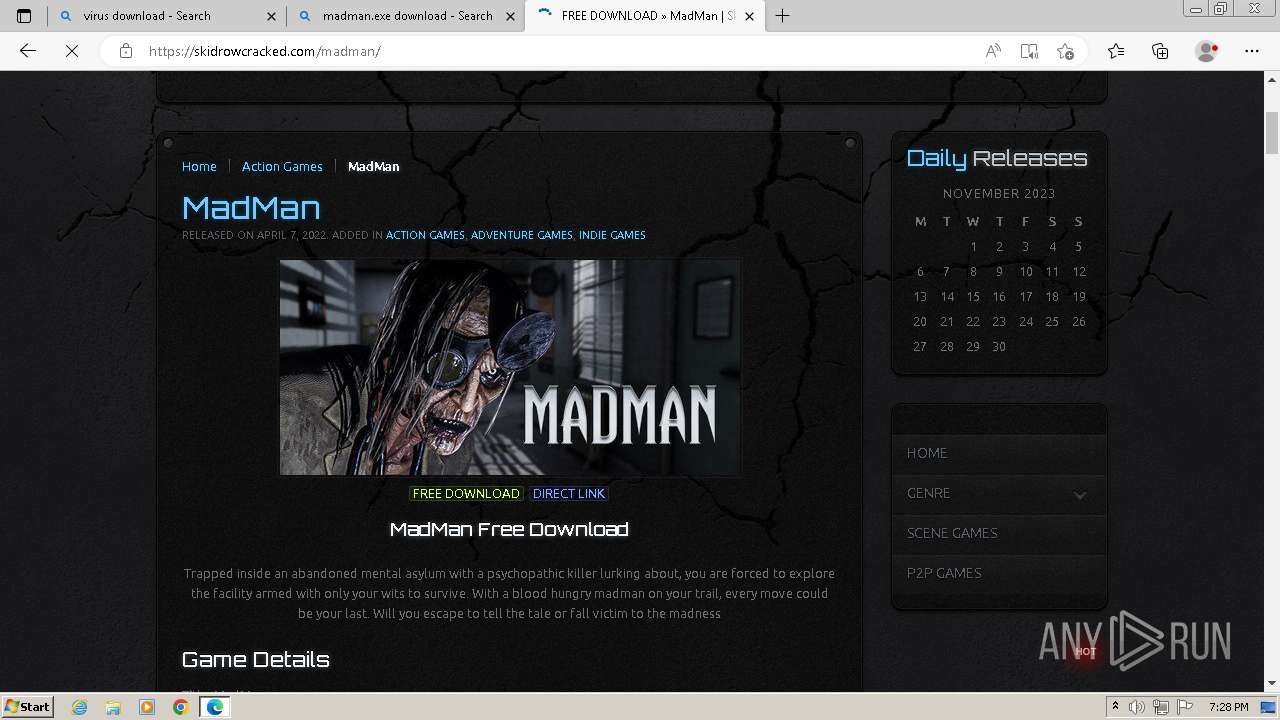
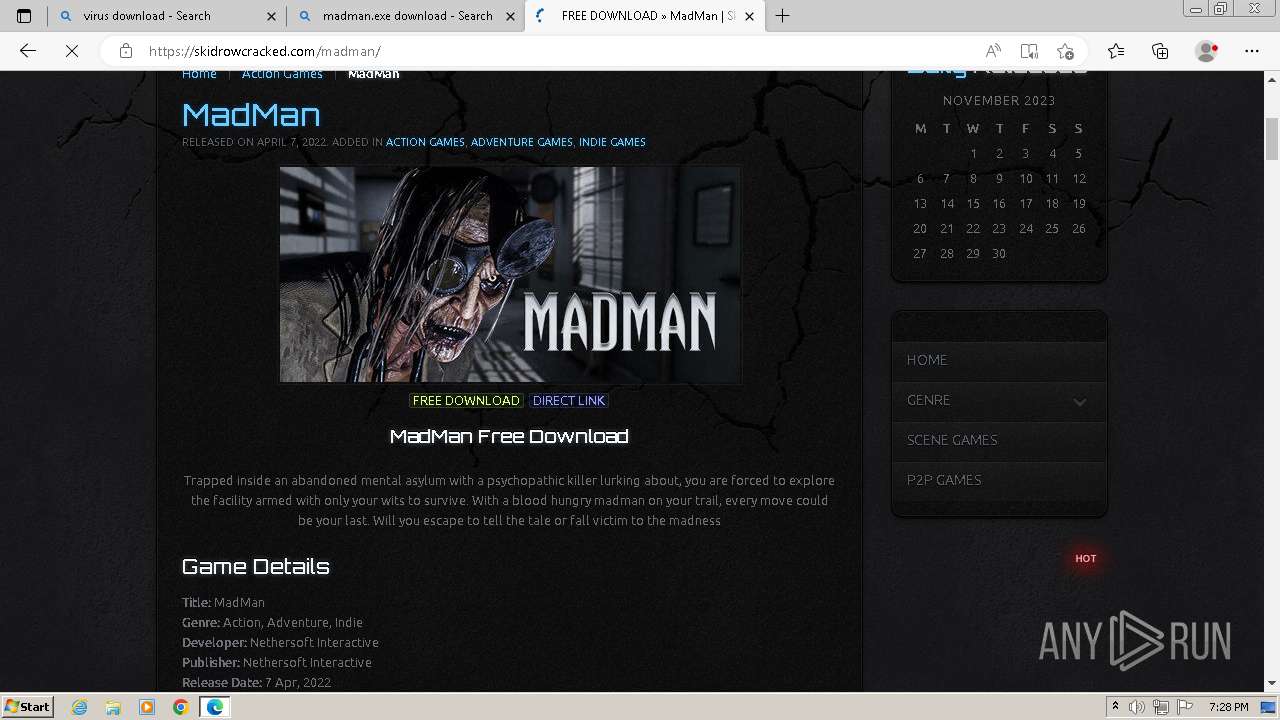
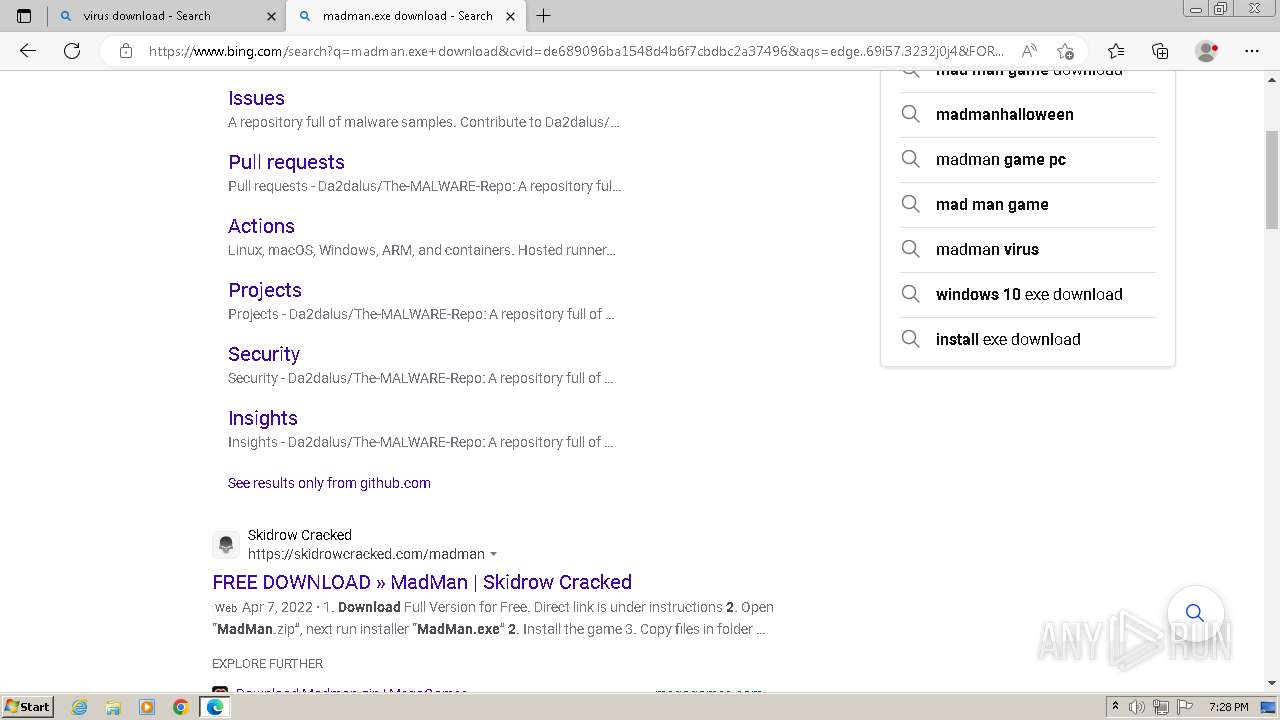
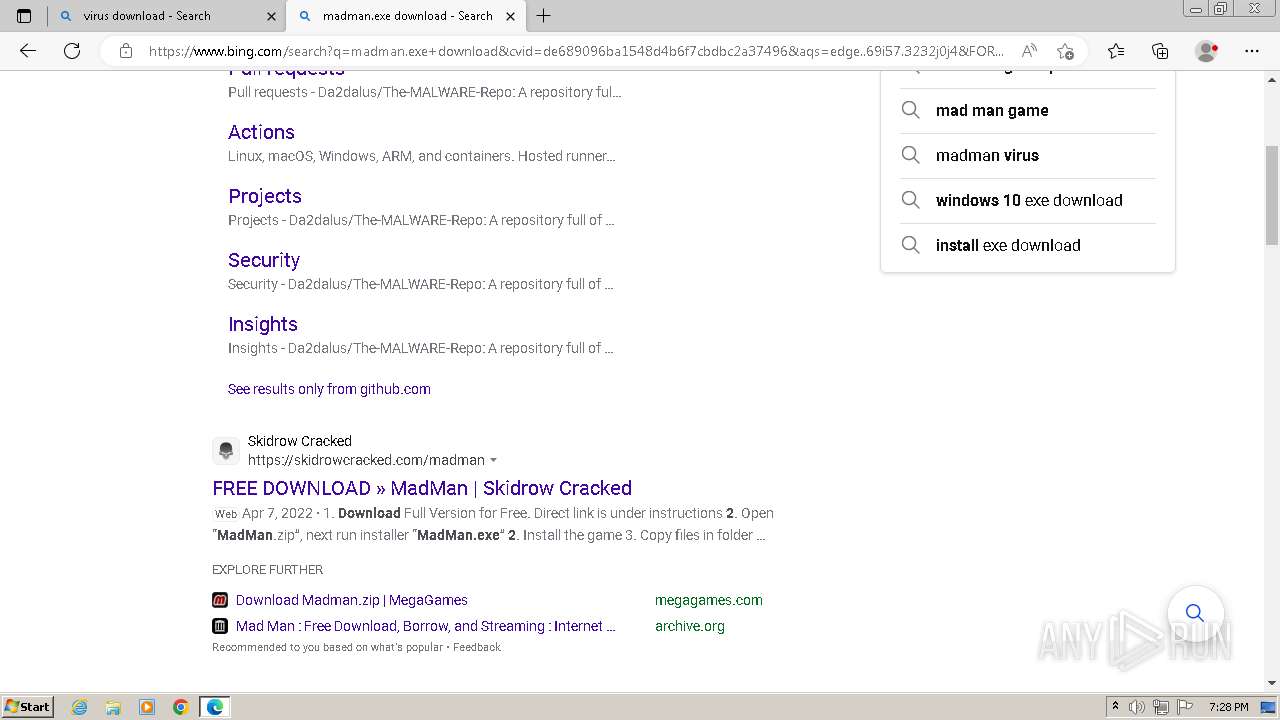
| Full analysis: | https://app.any.run/tasks/e6f8a524-20ab-4c70-a932-7ec71409f1df |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2023, 19:26:39 |
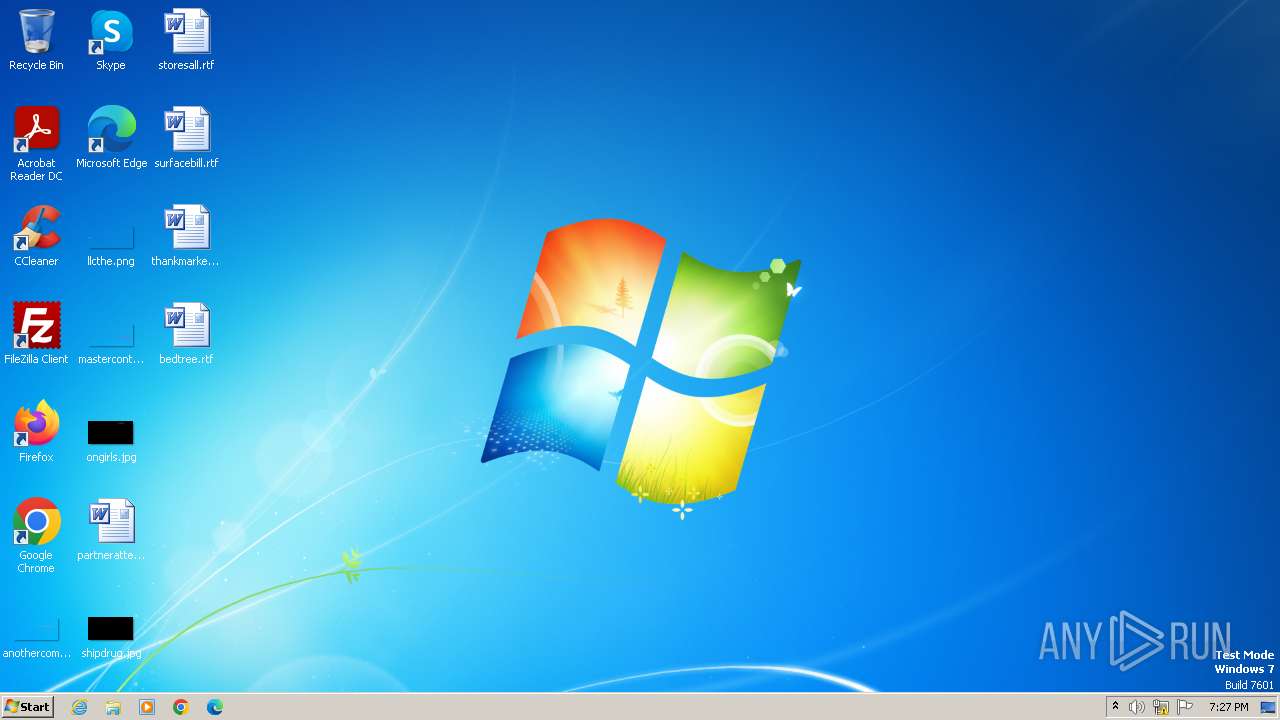
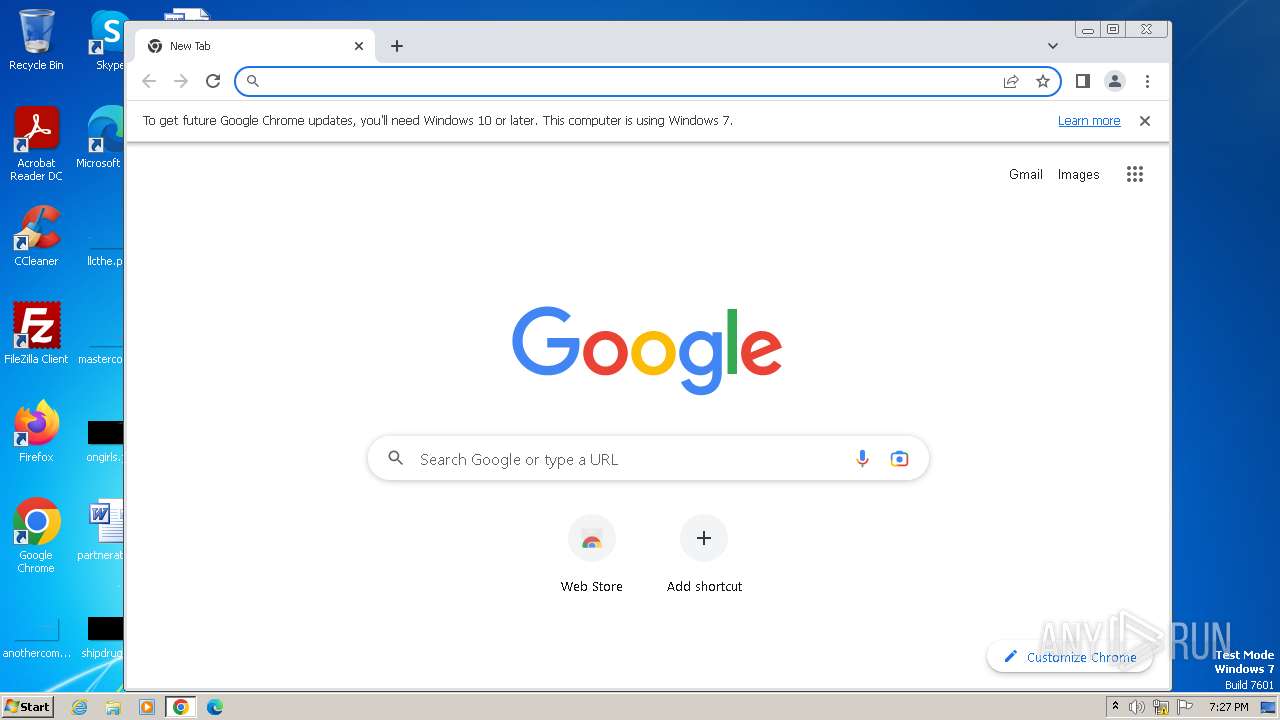
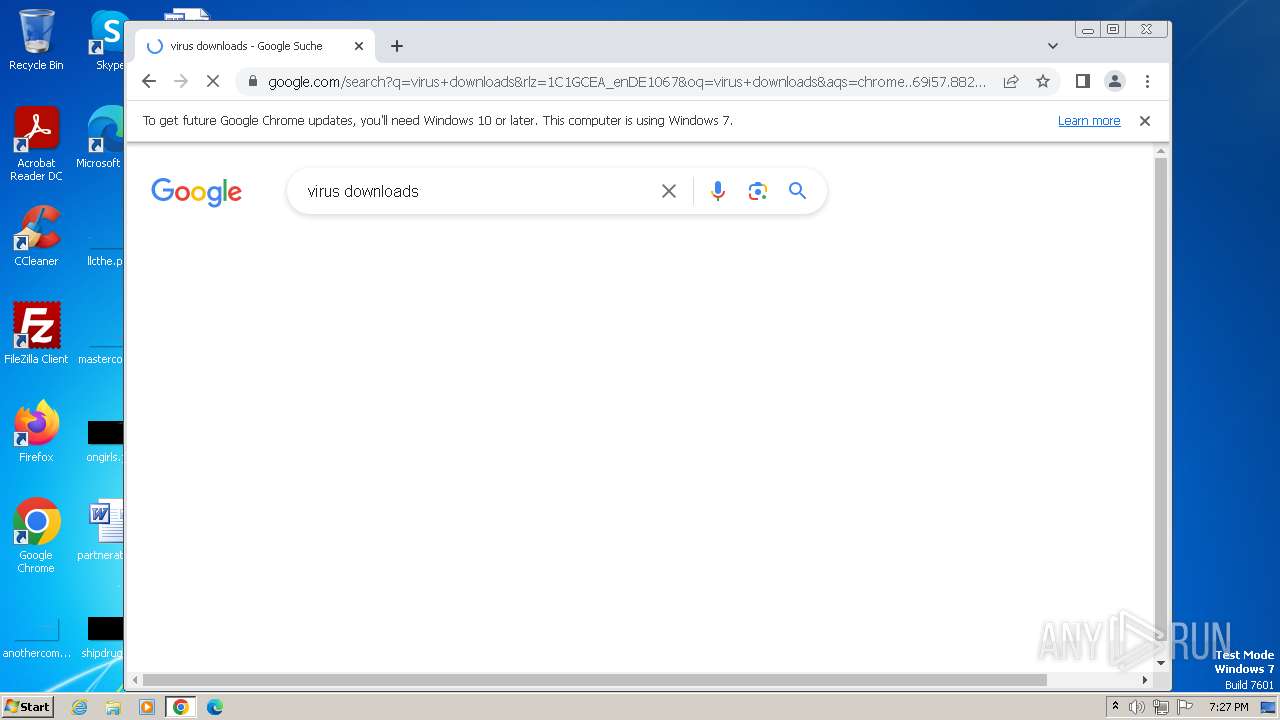
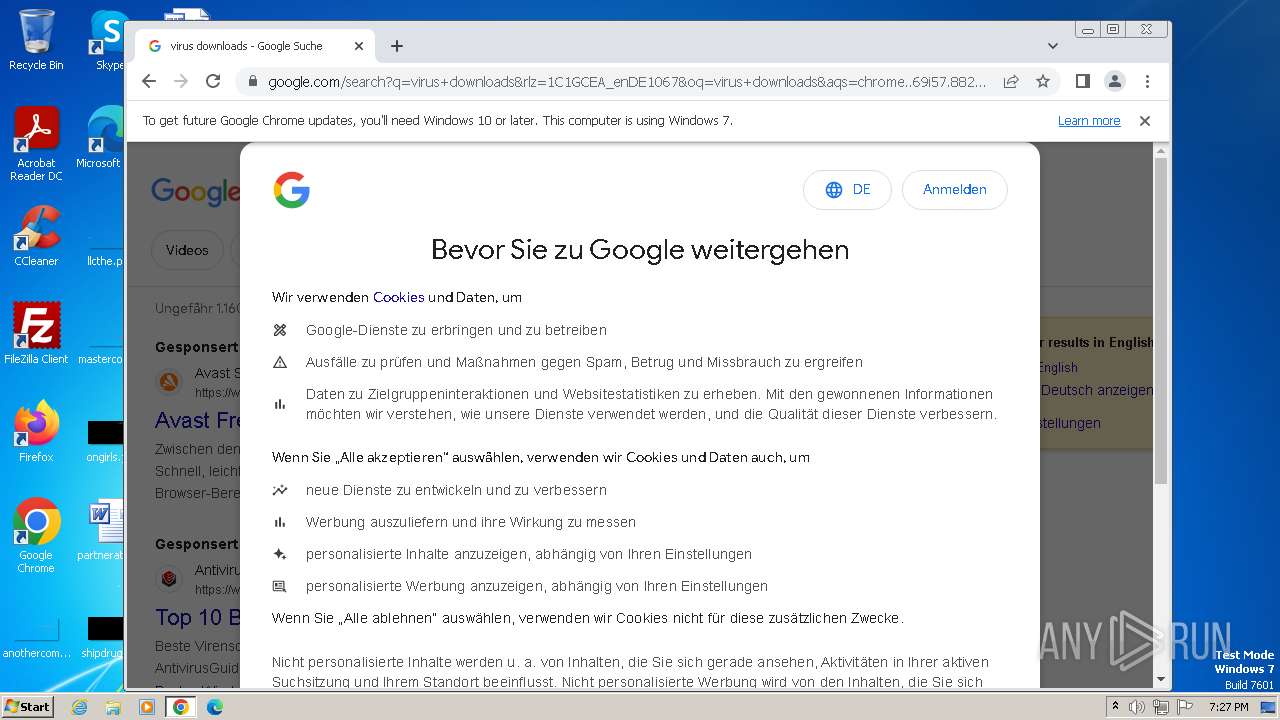
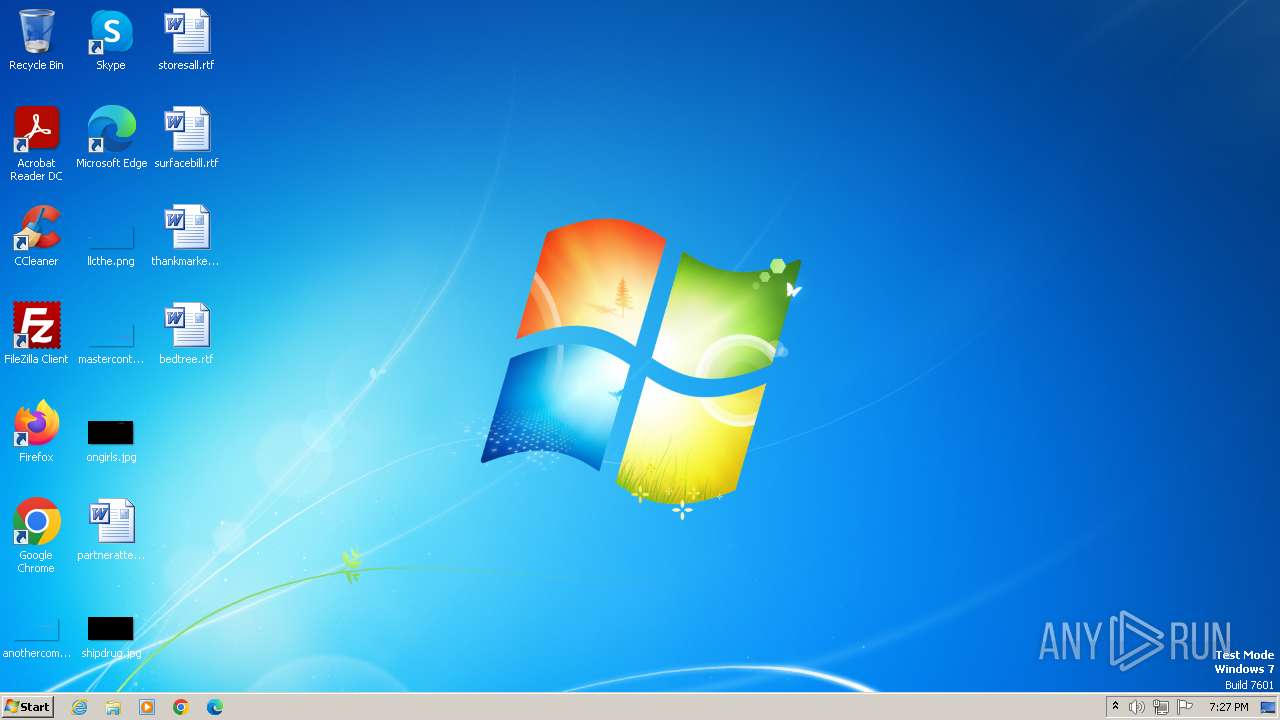
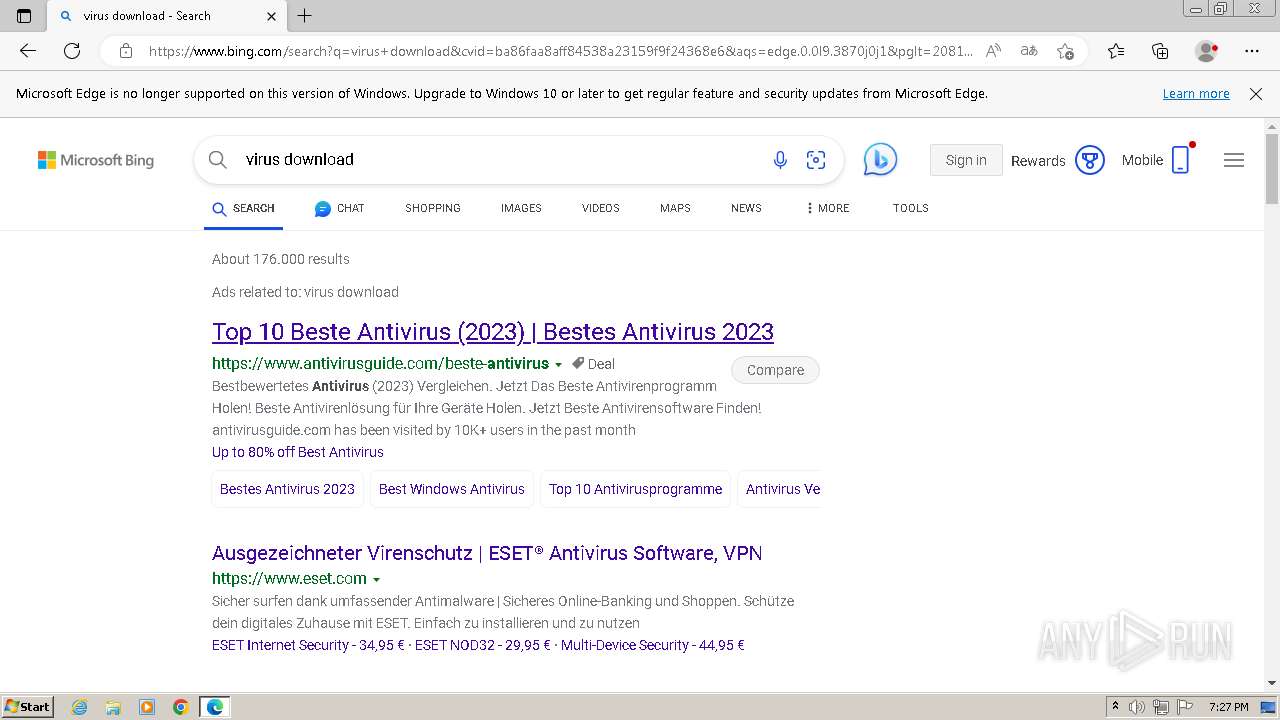
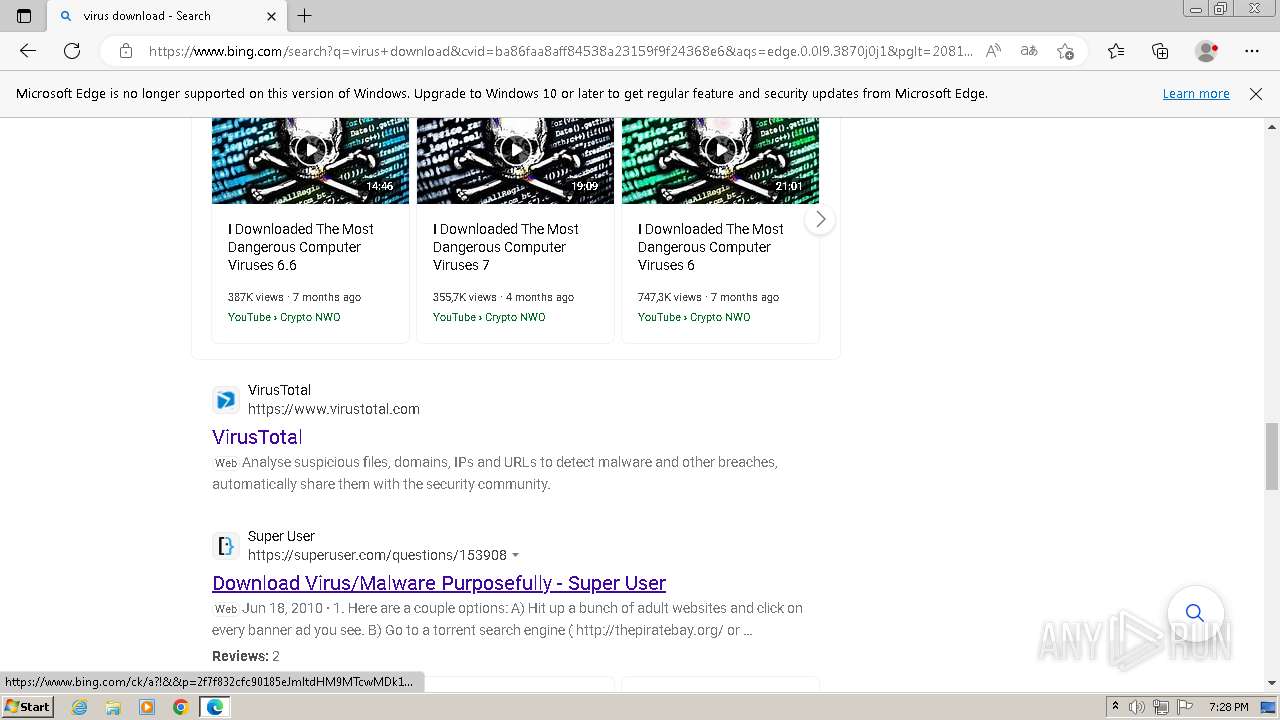
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/json |
| File info: | JSON data |
| MD5: | 85FB107992C4F0448E7475D29A63FEEB |
| SHA1: | 865CBB4EEE149F06426C39A89879C93C502CBC04 |
| SHA256: | 35FA6766A28C424DE42E613765AB9EB64E4D1EE481630522E237F5DEEC7AA5B8 |
| SSDEEP: | 96:Un1X/YZzX9bvbpNGZUxFtXtXbZZbVpbwk84qHntknRW9h2Aa1voQ5z69A:Un1X/8zX9bvbpN9xFtXtXbZZbVpbB8v4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
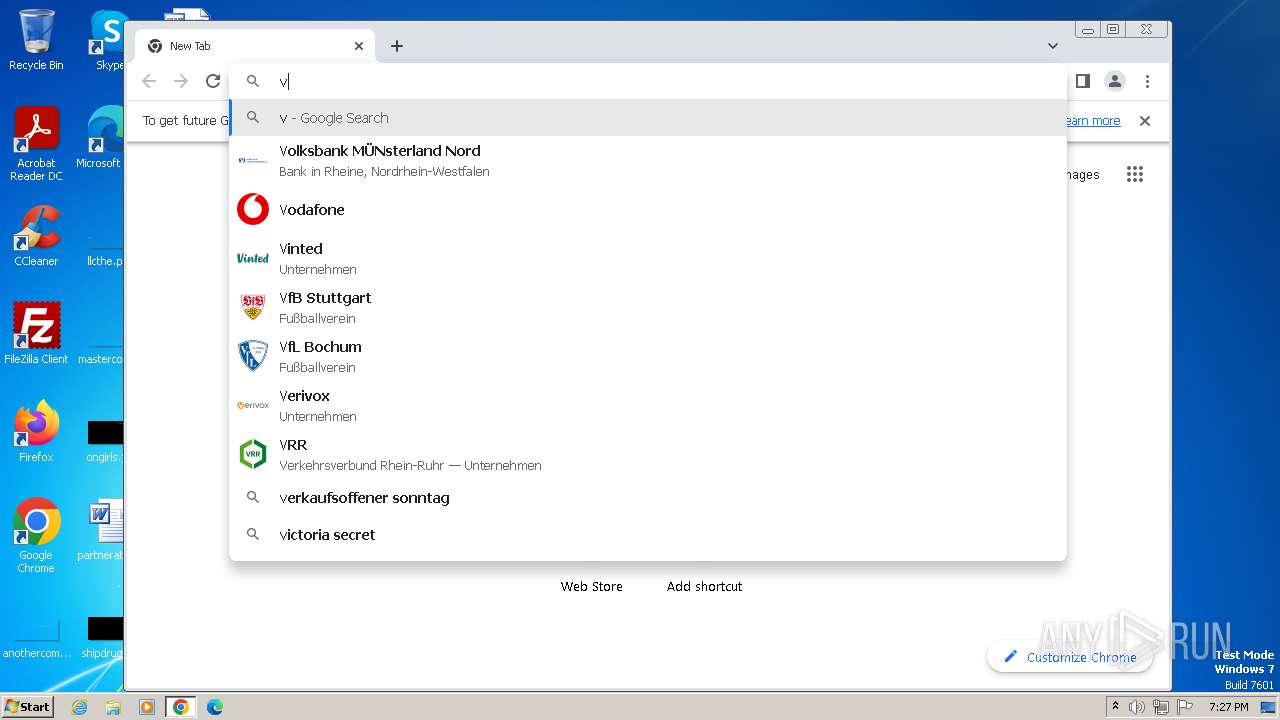
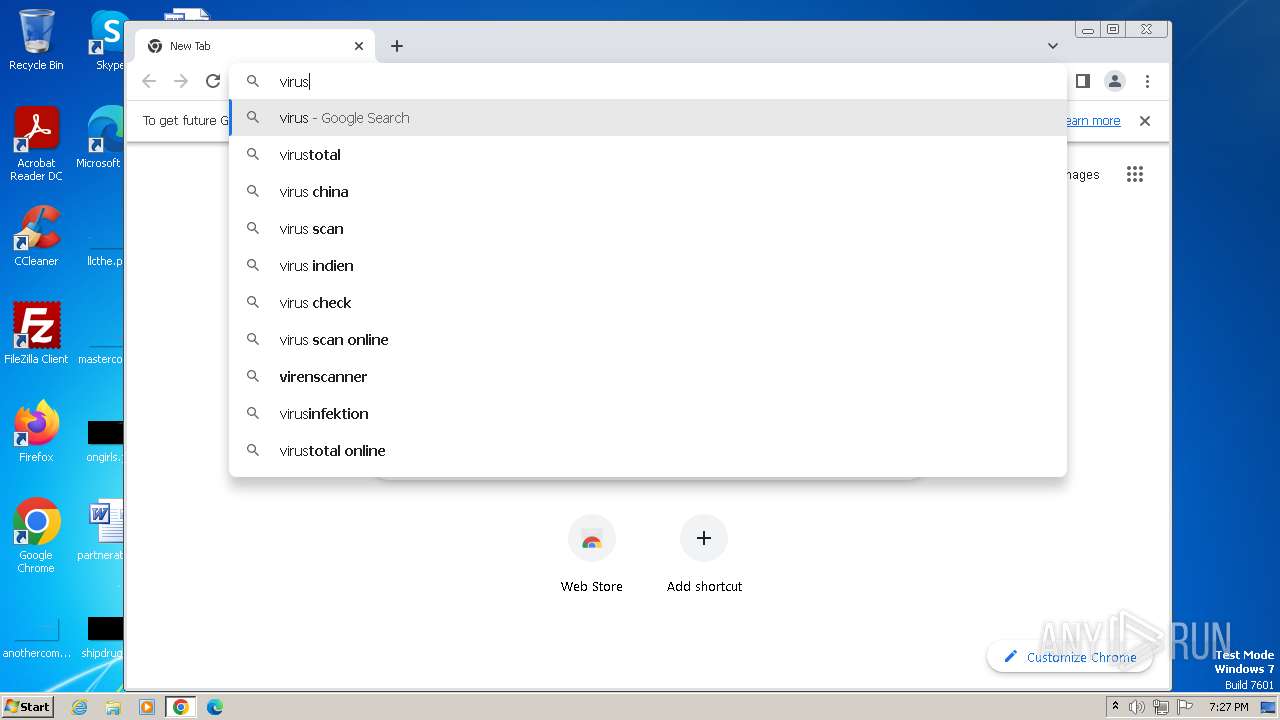
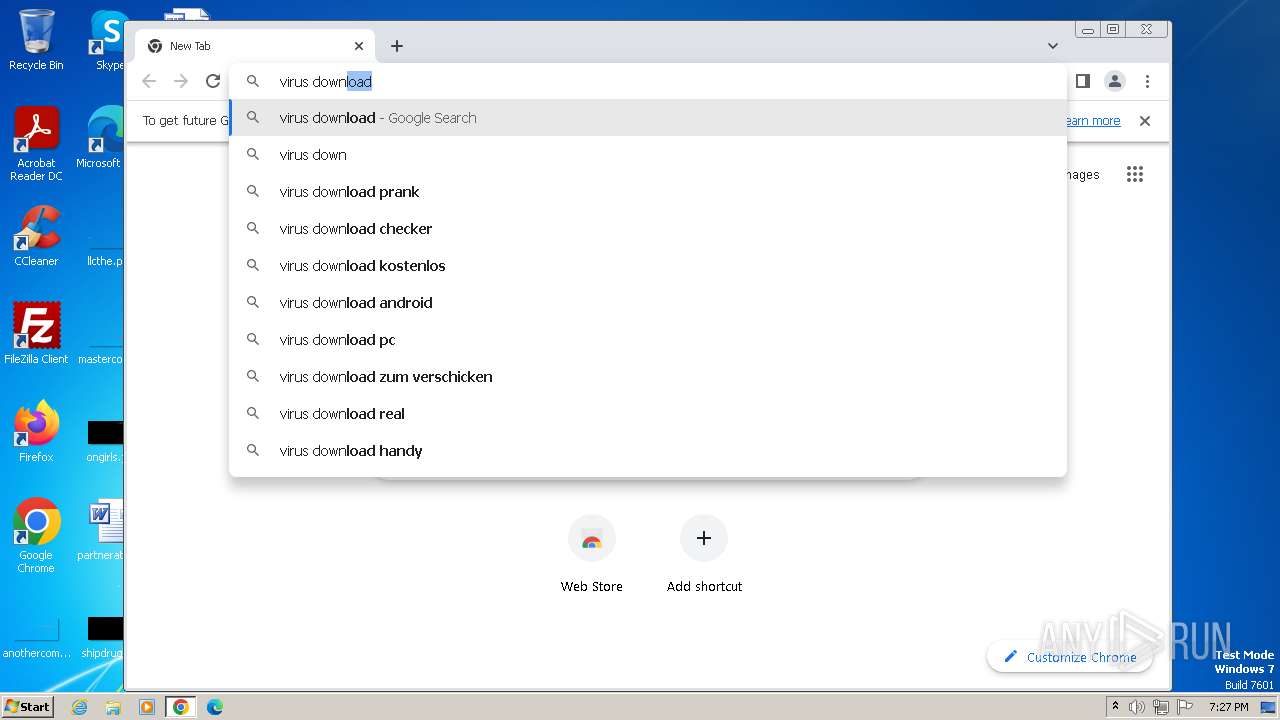
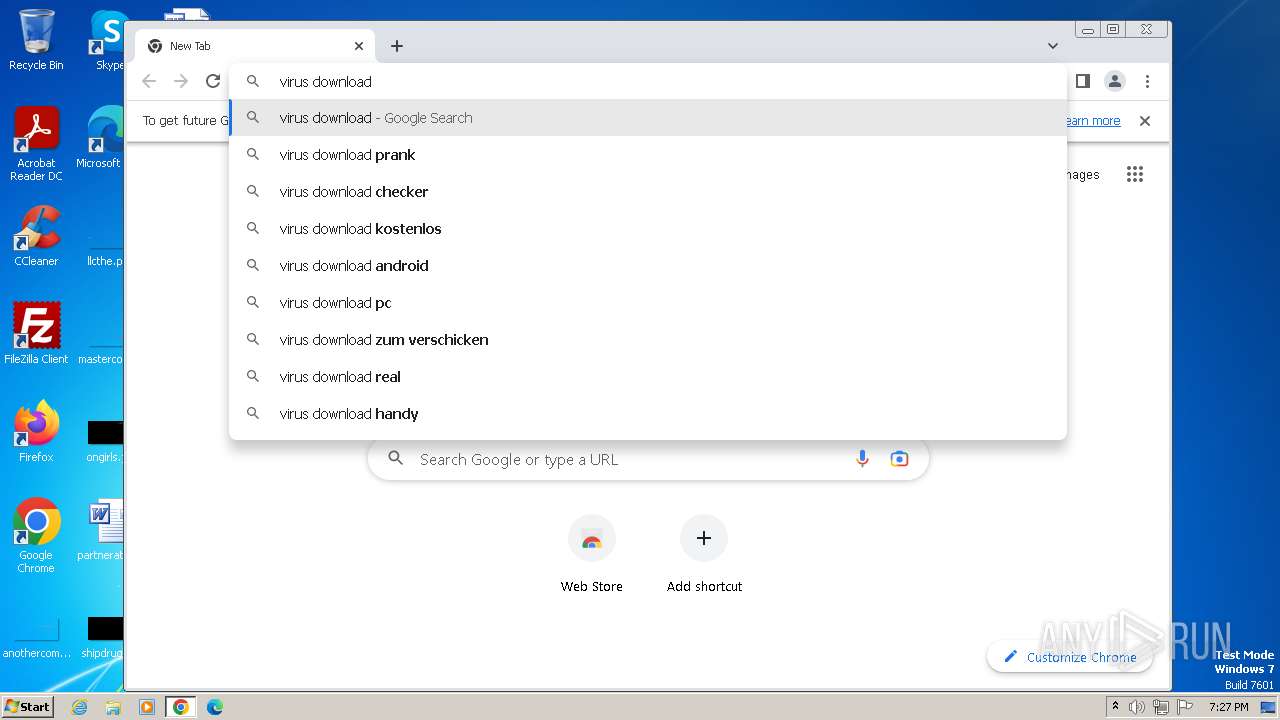
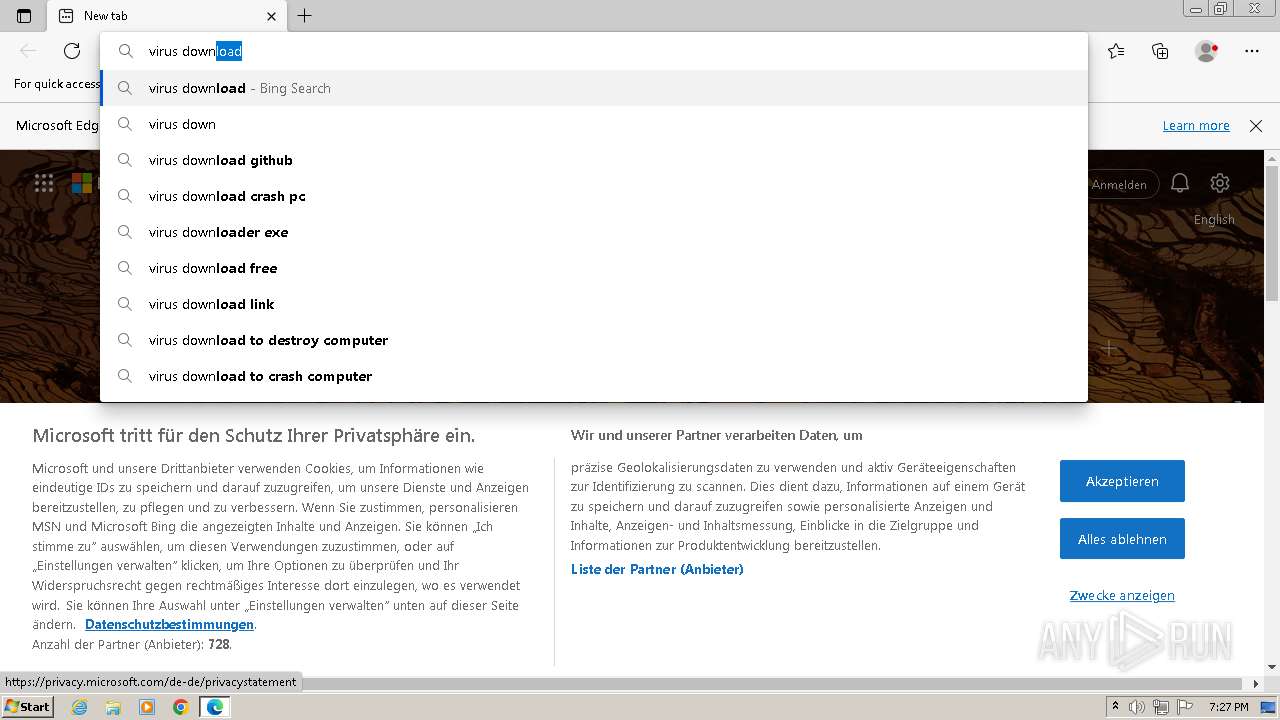
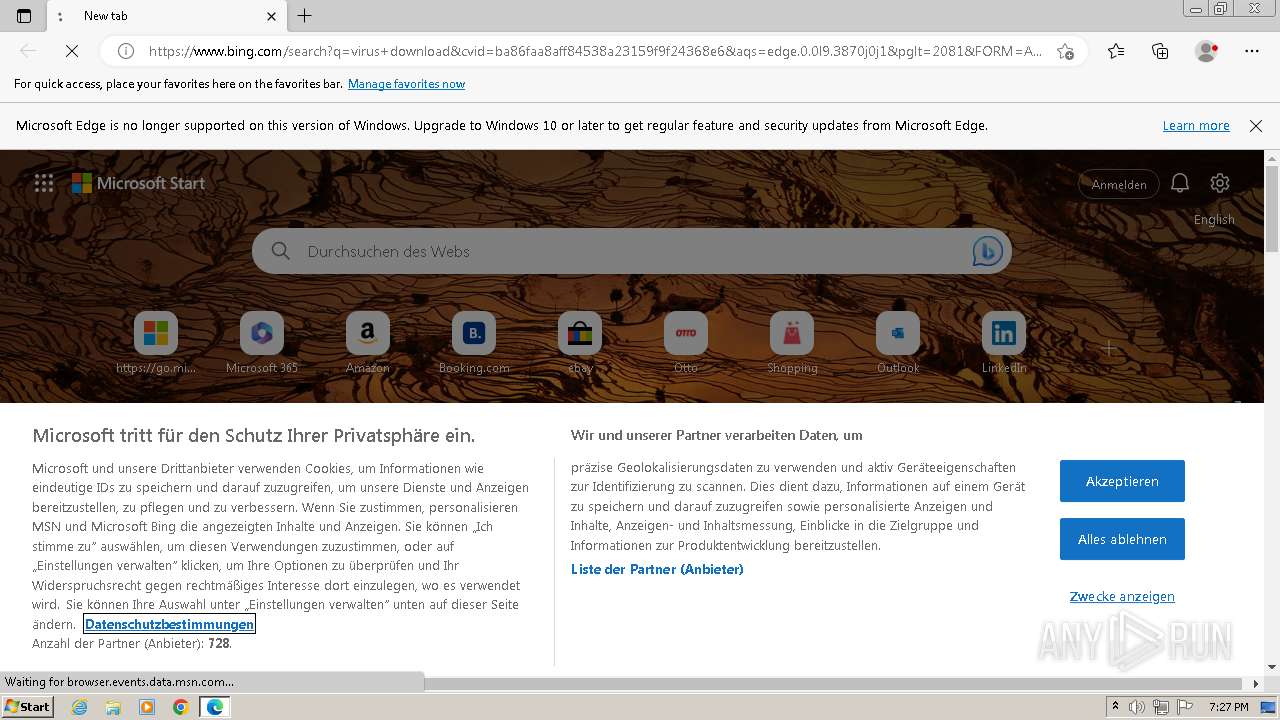
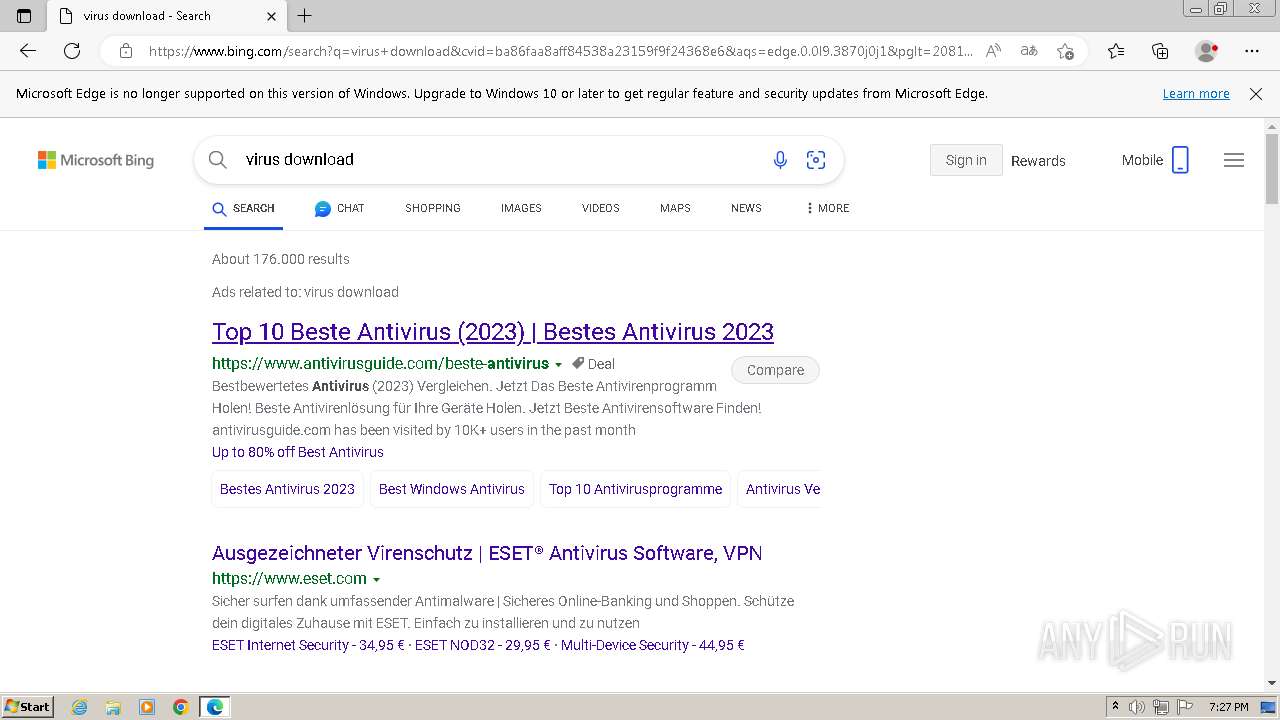
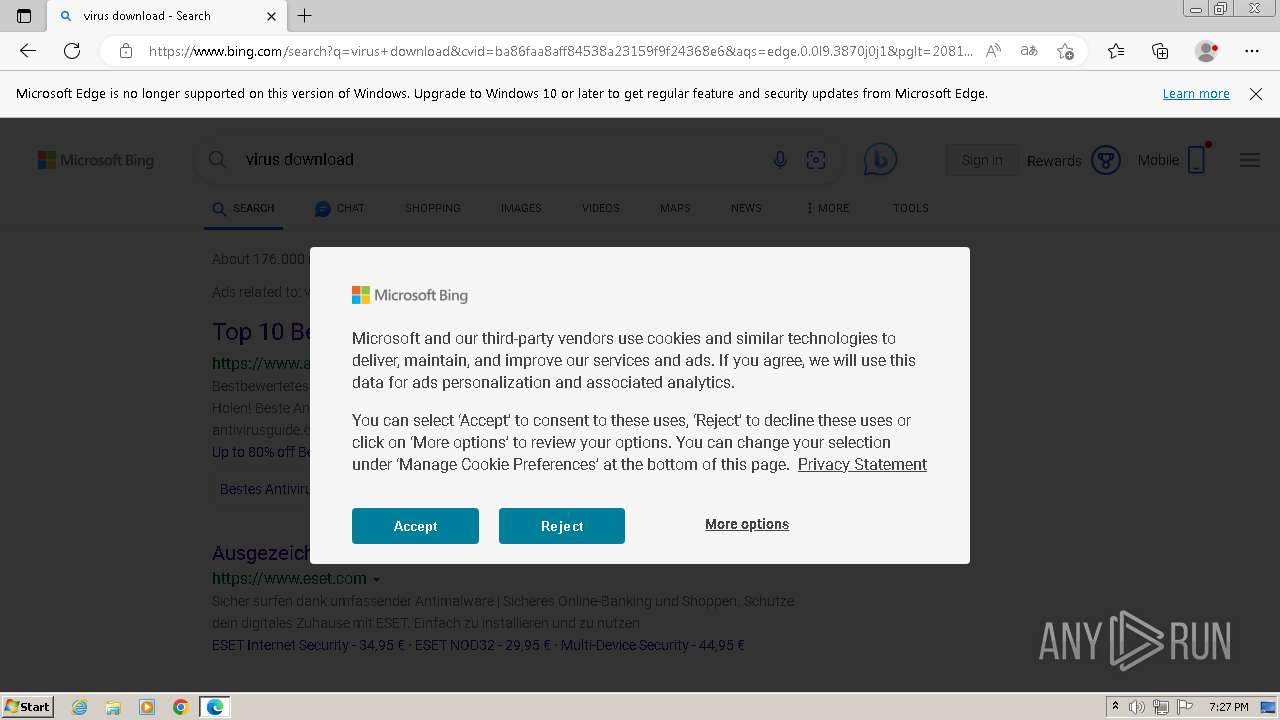
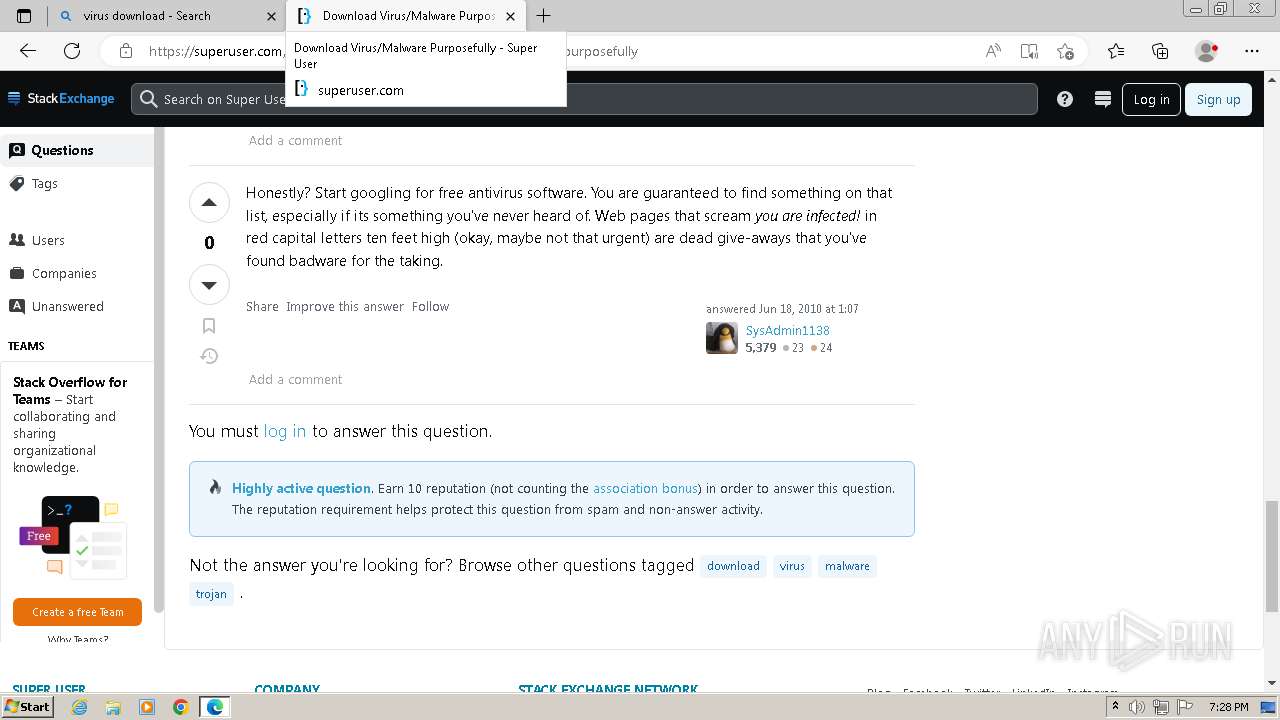
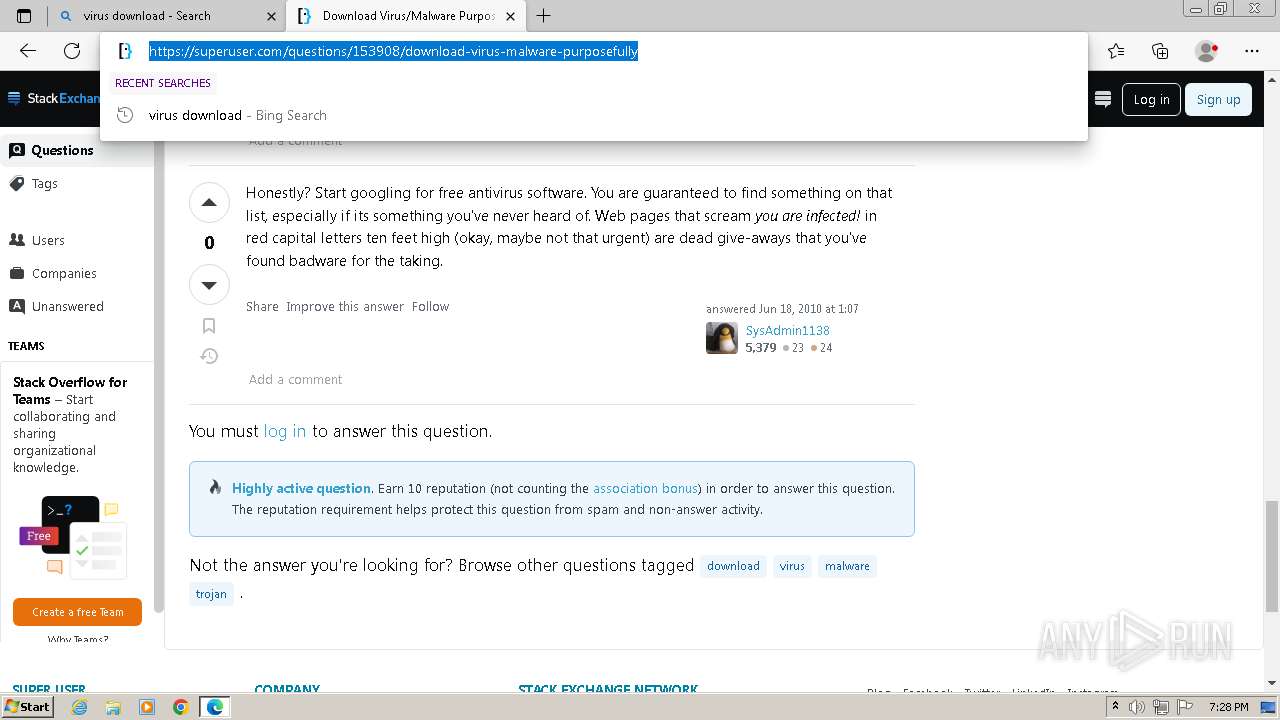
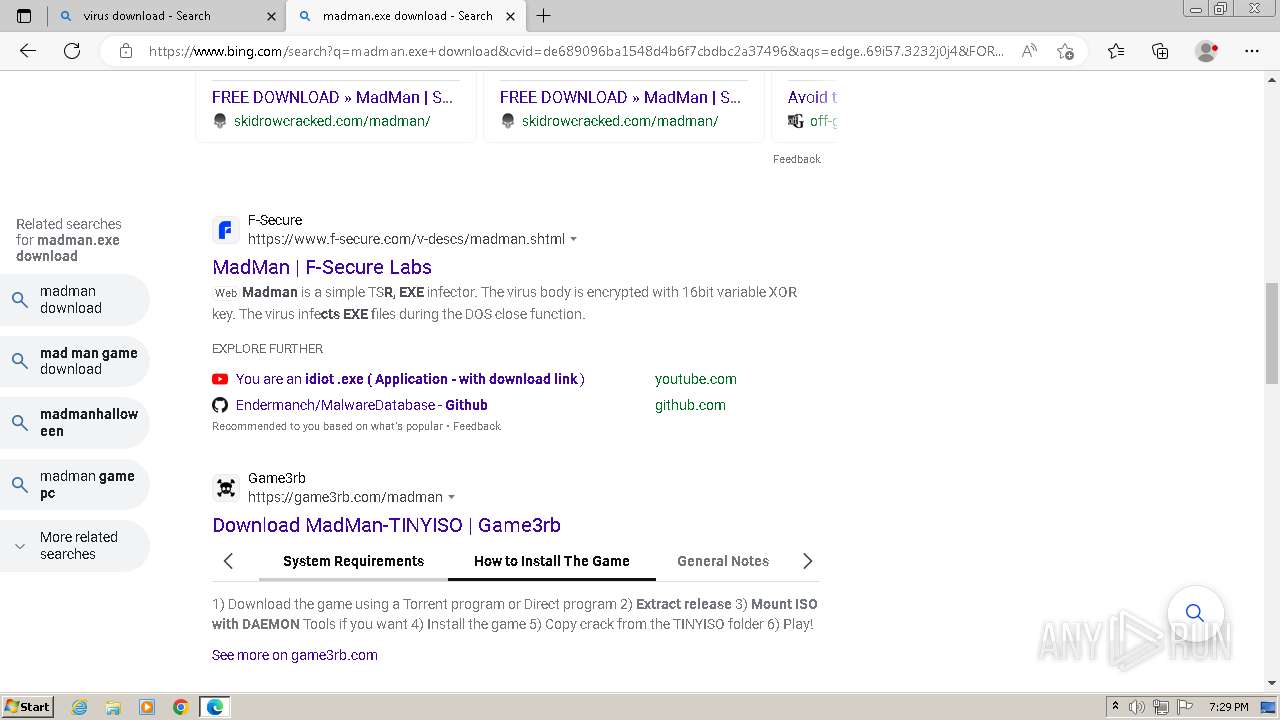
Application launched itself
- chrome.exe (PID: 3320)
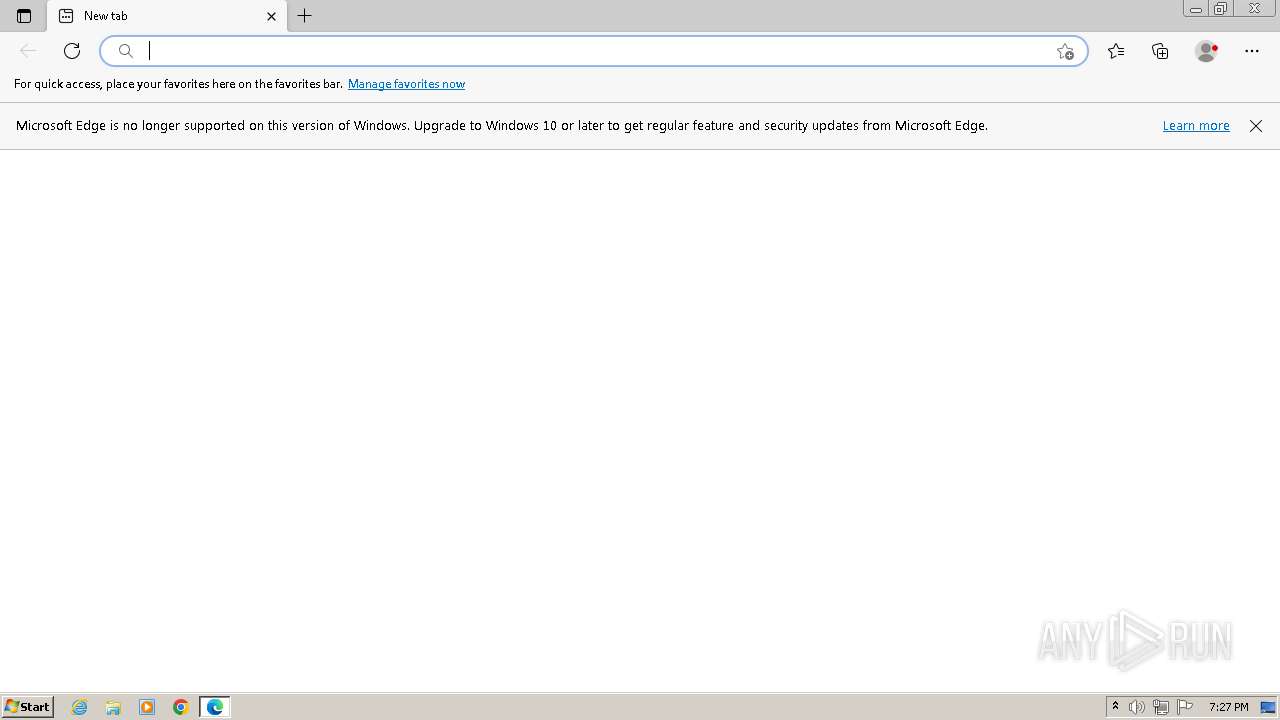
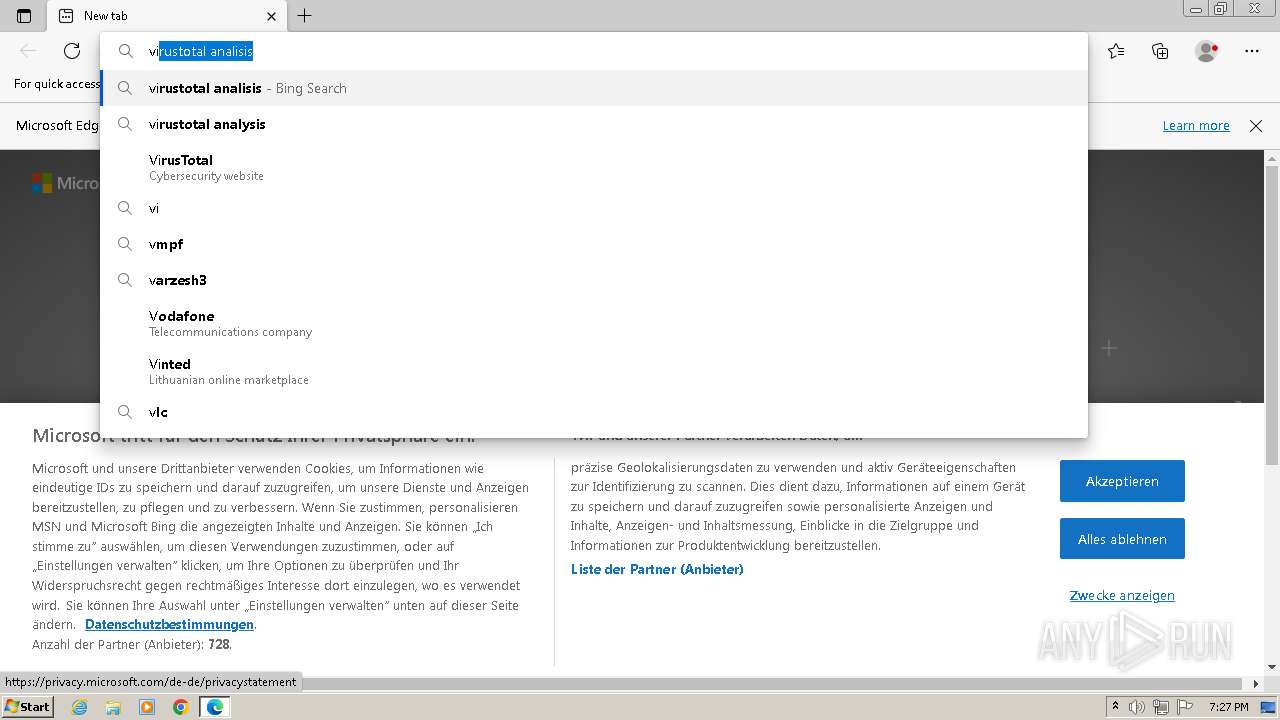
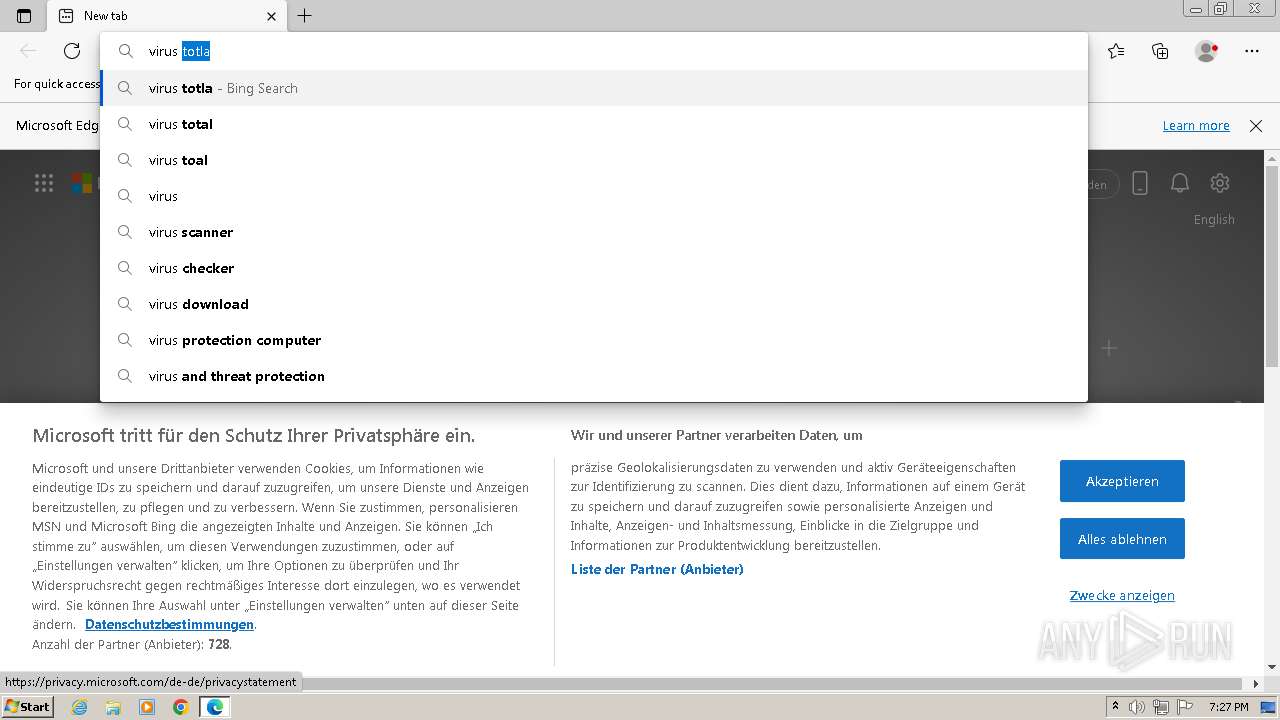
- msedge.exe (PID: 3704)
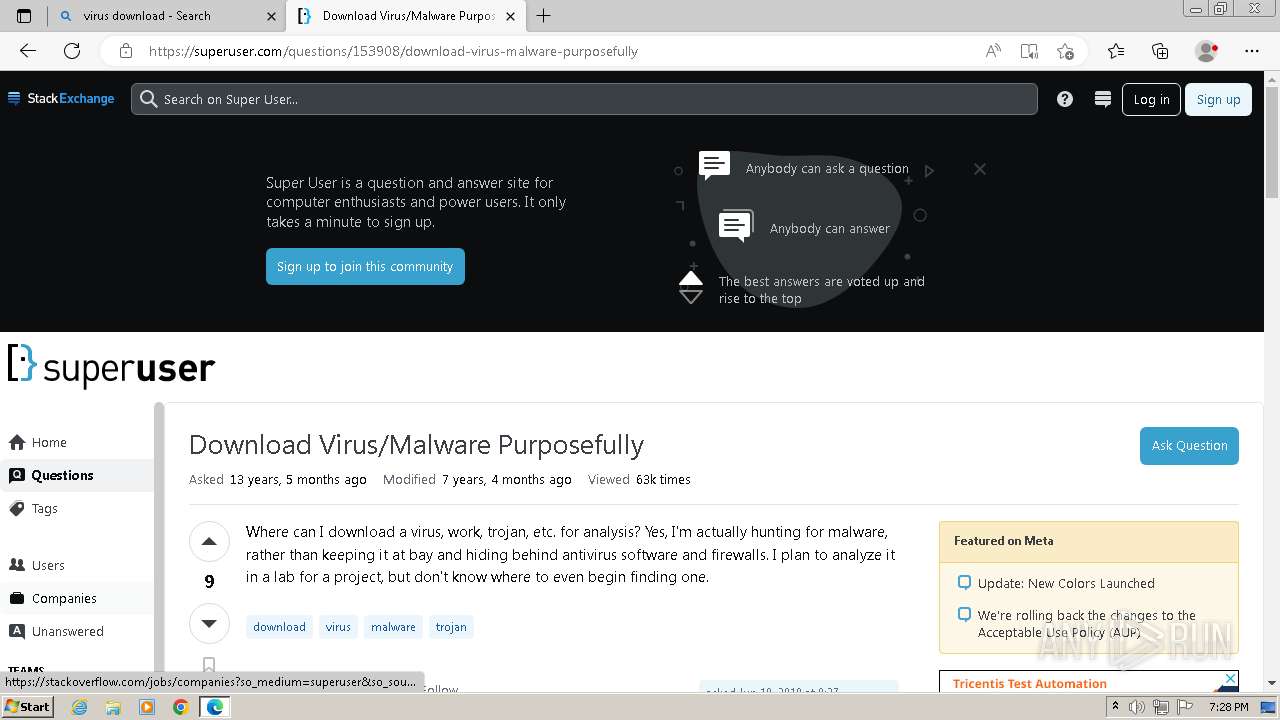
Manual execution by a user
- chrome.exe (PID: 3320)
- wmpnscfg.exe (PID: 3252)
- msedge.exe (PID: 3704)
Checks supported languages
- wmpnscfg.exe (PID: 3252)
Reads the computer name
- wmpnscfg.exe (PID: 3252)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
JSON
| PayloadAllShortcutsEnabled: | - |
|---|---|
| PayloadBlobCsv: | null |
| PayloadBlobCsvError: | null |
| PayloadBlobDependabotInfoConfigFilePath: | null |
| PayloadBlobDependabotInfoConfigurationNoticeDismissed: | null |
| PayloadBlobDependabotInfoCurrentUserCanAdminRepo: | - |
| PayloadBlobDependabotInfoDismissConfigurationNoticePath: | /settings/dismiss-notice/dependabot_configuration_notice |
| PayloadBlobDependabotInfoNetworkDependabotPath: | /Da2dalus/The-MALWARE-Repo/network/updates |
| PayloadBlobDependabotInfoRepoAlertsPath: | /Da2dalus/The-MALWARE-Repo/security/dependabot |
| PayloadBlobDependabotInfoRepoOwnerIsOrg: | - |
| PayloadBlobDependabotInfoRepoSecurityAndAnalysisPath: | /Da2dalus/The-MALWARE-Repo/settings/security_analysis |
| PayloadBlobDependabotInfoShowConfigurationBanner: | - |
| PayloadBlobDiscussionTemplate: | null |
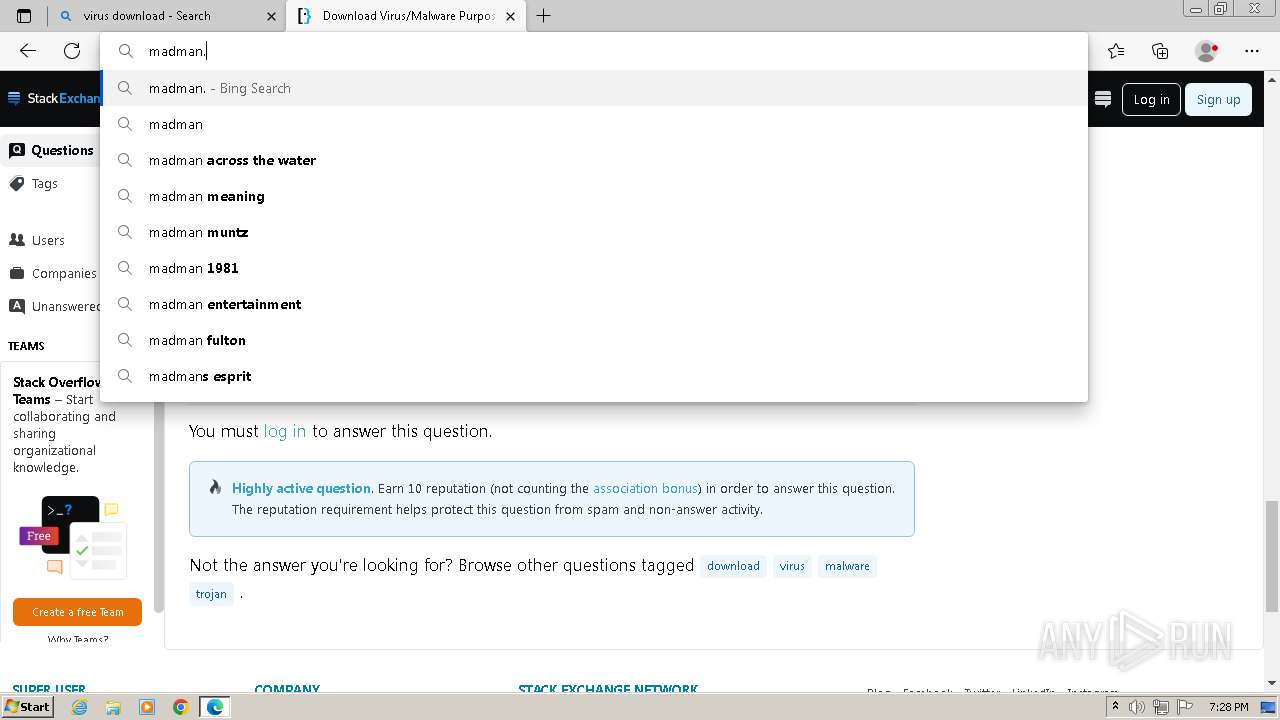
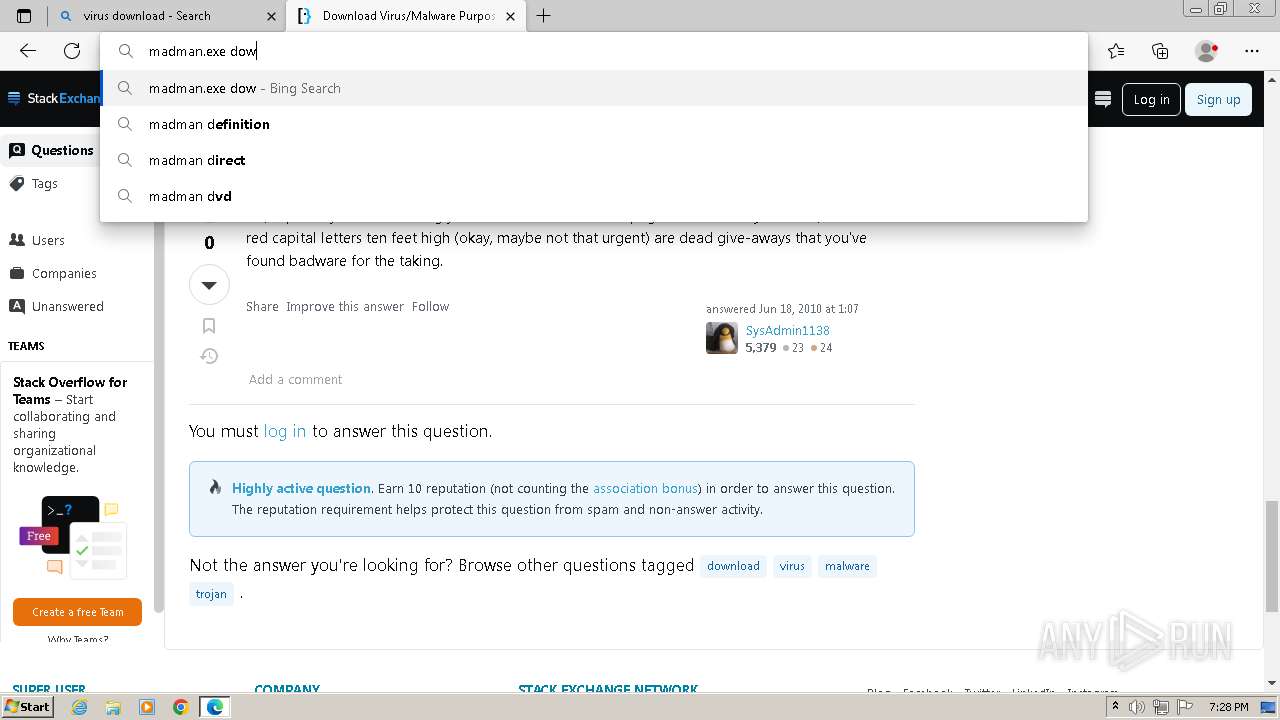
| PayloadBlobDisplayName: | MadMan.exe |
| PayloadBlobDisplayUrl: | https://github.com/Da2dalus/The-MALWARE-Repo/blob/master/Virus/MadMan.exe?raw=true |
| PayloadBlobHeaderInfoBlobSize: | 2.61 KB |
| PayloadBlobHeaderInfoDeleteInfoDeleteTooltip: | You must be signed in to make or propose changes |
| PayloadBlobHeaderInfoEditInfoEditTooltip: | You must be signed in to make or propose changes |
| PayloadBlobHeaderInfoGhDesktopPath: | https://desktop.github.com |
| PayloadBlobHeaderInfoGitLfsPath: | null |
| PayloadBlobHeaderInfoIsCSV: | - |
| PayloadBlobHeaderInfoIsRichtext: | - |
| PayloadBlobHeaderInfoLineInfoTruncatedLoc: | null |
| PayloadBlobHeaderInfoLineInfoTruncatedSloc: | null |
| PayloadBlobHeaderInfoMode: | file |
| PayloadBlobHeaderInfoOnBranch: | |
| PayloadBlobHeaderInfoShortPath: | a962bbb |
| PayloadBlobHeaderInfoSiteNavLoginPath: | /login?return_to=https%3A%2F%2Fgithub.com%2FDa2dalus%2FThe-MALWARE-Repo%2Fblob%2Fmaster%2FVirus%2FMadMan.exe |
| PayloadBlobHeaderInfoToc: | null |
| PayloadBlobImage: | - |
| PayloadBlobIsCodeownersFile: | null |
| PayloadBlobIsPlain: | - |
| PayloadBlobIsValidLegacyIssueTemplate: | - |
| PayloadBlobIssueTemplate: | null |
| PayloadBlobIssueTemplateHelpUrl: | https://docs.github.com/articles/about-issue-and-pull-request-templates |
| PayloadBlobLanguage: | null |
| PayloadBlobLanguageID: | null |
| PayloadBlobLarge: | - |
| PayloadBlobLoggedIn: | - |
| PayloadBlobNewDiscussionPath: | /Da2dalus/The-MALWARE-Repo/discussions/new |
| PayloadBlobNewIssuePath: | /Da2dalus/The-MALWARE-Repo/issues/new |
| PayloadBlobPlanSupportInfoRepoIsFork: | null |
| PayloadBlobPlanSupportInfoRepoOwnedByCurrentUser: | null |
| PayloadBlobPlanSupportInfoRequestFullPath: | /Da2dalus/The-MALWARE-Repo/blob/master/Virus/MadMan.exe |
| PayloadBlobPlanSupportInfoShowFreeOrgGatedFeatureMessage: | null |
| PayloadBlobPlanSupportInfoShowPlanSupportBanner: | null |
| PayloadBlobPlanSupportInfoUpgradeDataAttributes: | null |
| PayloadBlobPlanSupportInfoUpgradePath: | null |
| PayloadBlobPublishBannersInfoDismissActionNoticePath: | /settings/dismiss-notice/publish_action_from_dockerfile |
| PayloadBlobPublishBannersInfoDismissStackNoticePath: | /settings/dismiss-notice/publish_stack_from_file |
| PayloadBlobPublishBannersInfoReleasePath: | /Da2dalus/The-MALWARE-Repo/releases/new?marketplace=true |
| PayloadBlobPublishBannersInfoShowPublishActionBanner: | - |
| PayloadBlobPublishBannersInfoShowPublishStackBanner: | - |
| PayloadBlobRawBlobUrl: | https://github.com/Da2dalus/The-MALWARE-Repo/raw/master/Virus/MadMan.exe |
| PayloadBlobRawLines: | null |
| PayloadBlobRenderImageOrRaw: | |
| PayloadBlobRenderedFileInfo: | null |
| PayloadBlobRichText: | null |
| PayloadBlobShortPath: | null |
| PayloadBlobStylingDirectives: | null |
| PayloadBlobSymbols: | null |
| PayloadBlobTabSize: | 8 |
| PayloadBlobTopBannersInfoActionsOnboardingTip: | null |
| PayloadBlobTopBannersInfoCitationHelpUrl: | https://docs.github.com/en/github/creating-cloning-and-archiving-repositories/creating-a-repository-on-github/about-citation-files |
| PayloadBlobTopBannersInfoGlobalPreferredFundingPath: | null |
| PayloadBlobTopBannersInfoOverridingGlobalFundingFile: | - |
| PayloadBlobTopBannersInfoRepoName: | The-MALWARE-Repo |
| PayloadBlobTopBannersInfoRepoOwner: | Da2dalus |
| PayloadBlobTopBannersInfoShowDependabotConfigurationBanner: | - |
| PayloadBlobTopBannersInfoShowInvalidCitationWarning: | - |
| PayloadBlobTruncated: | - |
| PayloadBlobViewable: | - |
| PayloadBlobWorkflowRedirectUrl: | null |
| PayloadCopilotAccessAllowed: | - |
| PayloadCopilotInfo: | null |
| PayloadCsrf_tokensDa2dalusThe-MALWARE-RepobranchesPost: | Sq3eb9TTafXEIwFTX8Mh2hE7a9EvQhv8hbJlZZpA5OT2Pj3ujjmOaAnTh5W8qKahOPj-NtskhAopkZrSgmX5cQ |
| PayloadCsrf_tokensrepospreferencesPost: | Os5fZczGCvE_jlh-UZ-cXb5smjUw1yJk1AhBy1pVKpIDtFam4G3mj7Pq8YeP-IV9rl-je9dnpB4wQq5LfJwMPQ |
| PayloadCurrentUser: | null |
| PayloadFileTreeItemsContentType: |
|
| PayloadFileTreeItemsName: |
|
| PayloadFileTreeItemsPath: |
|
| PayloadFileTreeTotalCount: | 16 |
| PayloadFileTreeVirusItemsContentType: |
|
| PayloadFileTreeVirusItemsName: |
|
| PayloadFileTreeVirusItemsPath: |
|
| PayloadFileTreeVirusTotalCount: | 8 |
| PayloadFileTreeProcessingTime: | 5.025628 |
| PayloadPath: | Virus/MadMan.exe |
| PayloadReducedMotionEnabled: | null |
| PayloadRefInfoCanEdit: | - |
| PayloadRefInfoCurrentOid: | e8ddc517b4ecd80728e0acef1c558fad9a1c888a |
| PayloadRefInfoListCacheKey: | v0:1592036907.0 |
| PayloadRefInfoName: | master |
| PayloadRefInfoRefType: | branch |
| PayloadRepoCreatedAt: | 2020-06-13T08:28:25.000Z |
| PayloadRepoCurrentUserCanPush: | - |
| PayloadRepoDefaultBranch: | master |
| PayloadRepoId: | 271970028 |
| PayloadRepoIsEmpty: | - |
| PayloadRepoIsFork: | - |
| PayloadRepoIsOrgOwned: | - |
| PayloadRepoName: | The-MALWARE-Repo |
| PayloadRepoOwnerAvatar: | https://avatars.githubusercontent.com/u/63458929?v=4 |
| PayloadRepoOwnerLogin: | Da2dalus |
| PayloadRepoPrivate: | - |
| PayloadRepoPublic: | |
| PayloadSymbolsExpanded: | - |
| PayloadTreeExpanded: | |
| Title: | The-MALWARE-Repo/Virus/MadMan.exe at master · Da2dalus/The-MALWARE-Repo |
Total processes
88
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2328 --field-trial-handle=1216,i,11574460019094710710,1476180552849112950,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --mojo-platform-channel-handle=1184 --field-trial-handle=1216,i,11574460019094710710,1476180552849112950,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
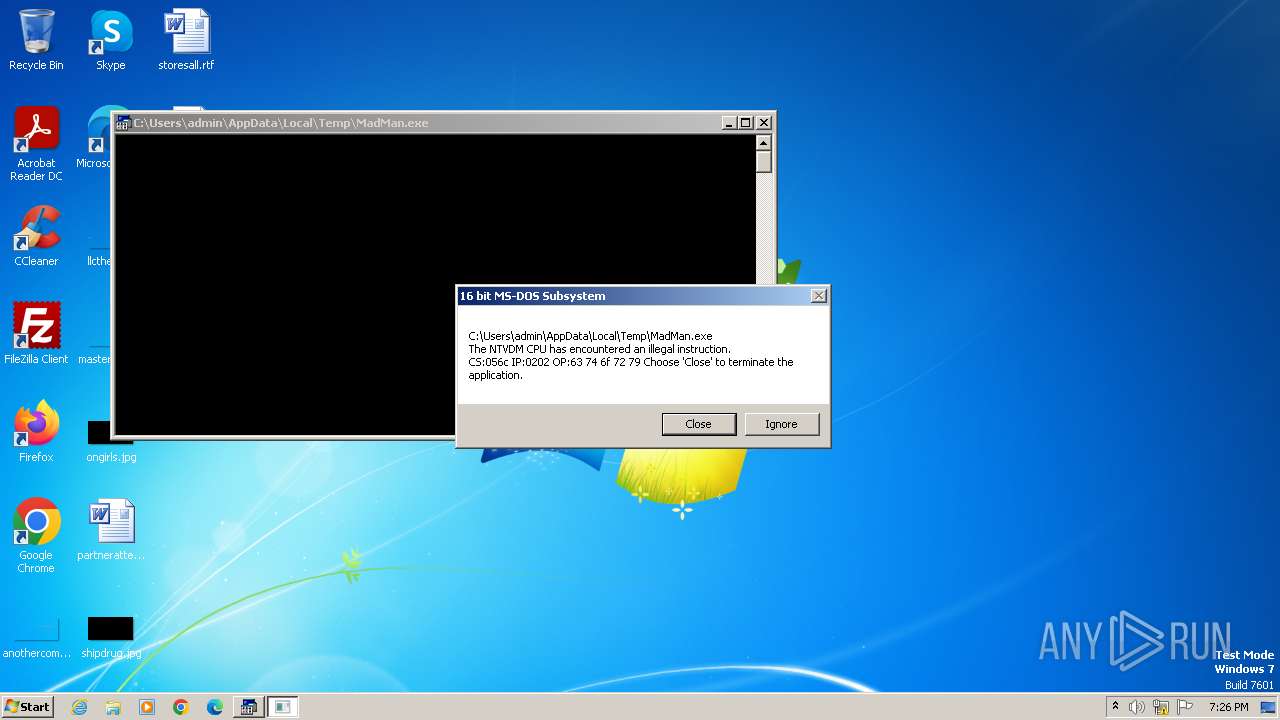
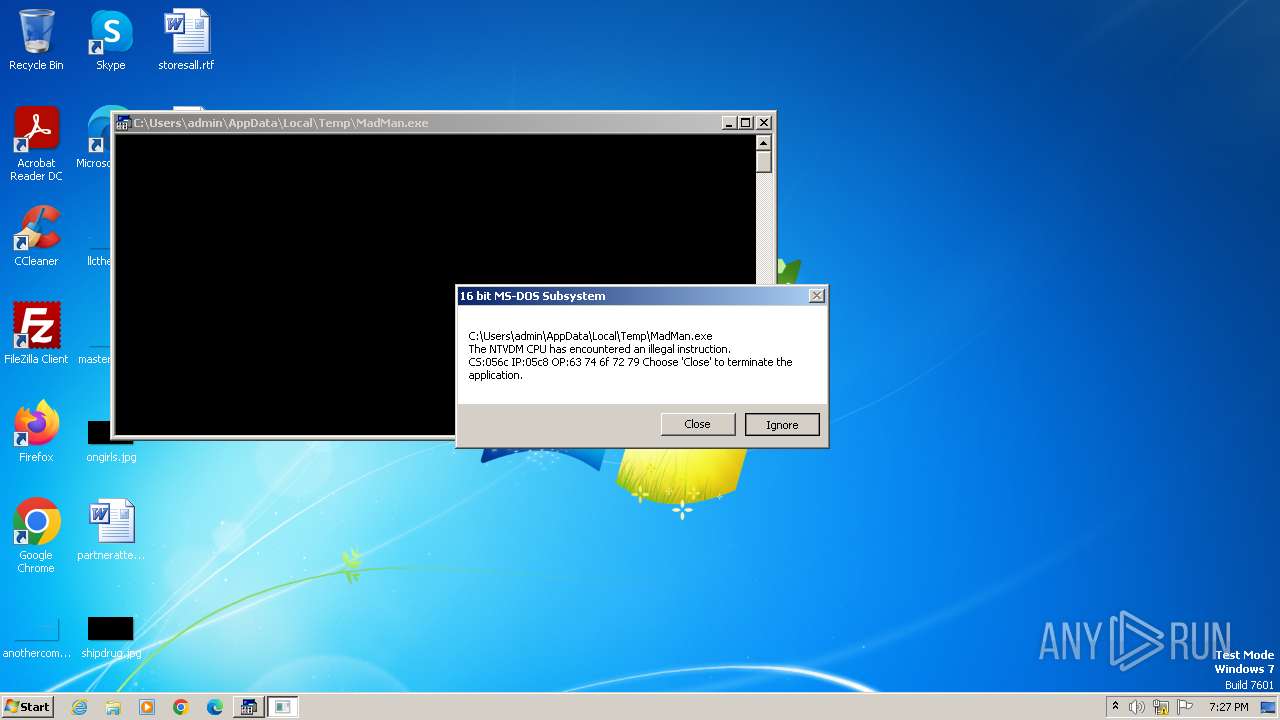
| 564 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\System32\ntvdm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=4460 --field-trial-handle=1216,i,11574460019094710710,1476180552849112950,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3644 --field-trial-handle=1216,i,11574460019094710710,1476180552849112950,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1316 --field-trial-handle=1148,i,4384702846549780841,2491397066019644174,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1132 --field-trial-handle=1148,i,4384702846549780841,2491397066019644174,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=4088 --field-trial-handle=1216,i,11574460019094710710,1476180552849112950,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6b738b38,0x6b738b48,0x6b738b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=3672 --field-trial-handle=1216,i,11574460019094710710,1476180552849112950,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
6 929
Read events
6 848
Write events
75
Delete events
6
Modification events
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
37
Suspicious files
1 244
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1c5645.TMP | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1c5636.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 564 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsD965.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1c573f.TMP | text | |
MD5:99EC94B2503FAD33EDAF99779EBA5BC8 | SHA256:DC554AB7EDCAD375F39ED106CA1EF9A89FB8D9063A4D08F377F2C80D66799D7E | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1c5839.TMP | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
112
DNS requests
177
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1128 | chrome.exe | 142.250.185.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3320 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
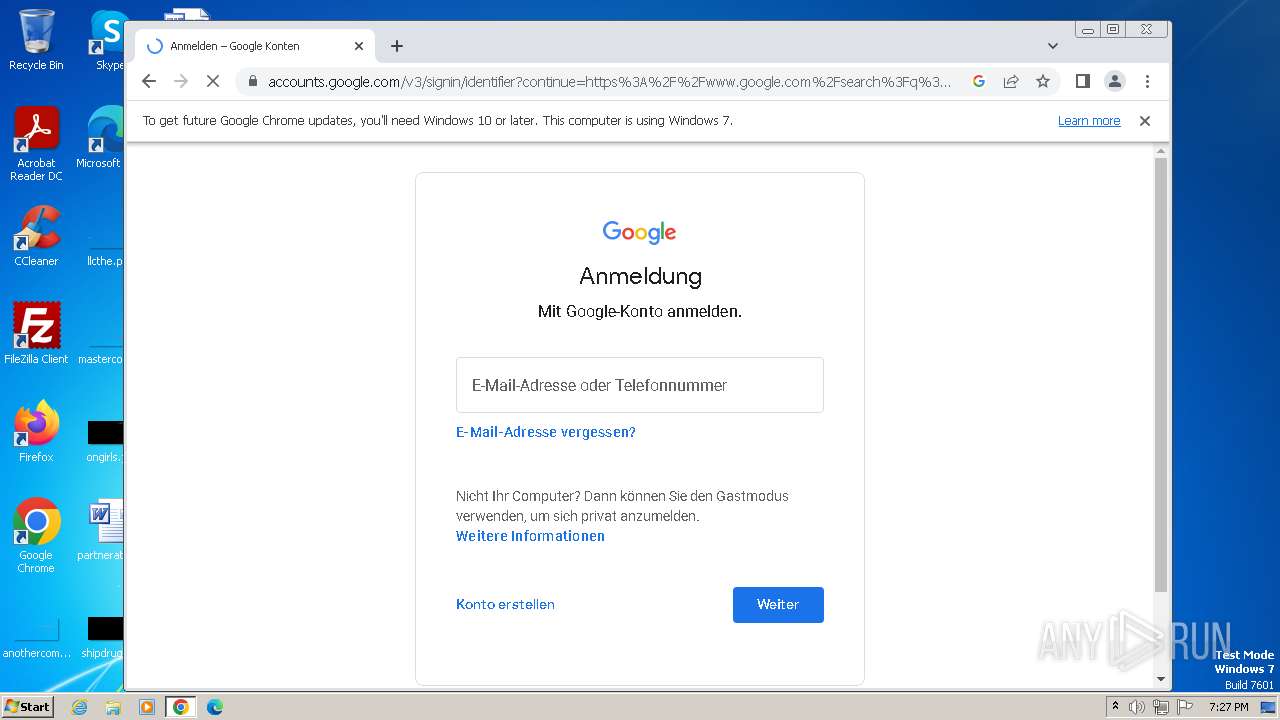
1128 | chrome.exe | 172.217.23.109:443 | accounts.google.com | GOOGLE | US | unknown |
1128 | chrome.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
1128 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |